| File name: | tb_free.exe |
| Full analysis: | https://app.any.run/tasks/b625ad6c-68a3-497a-a091-6ba7a152185a |
| Verdict: | No threats detected |
| Analysis date: | June 12, 2019, 09:52:50 |
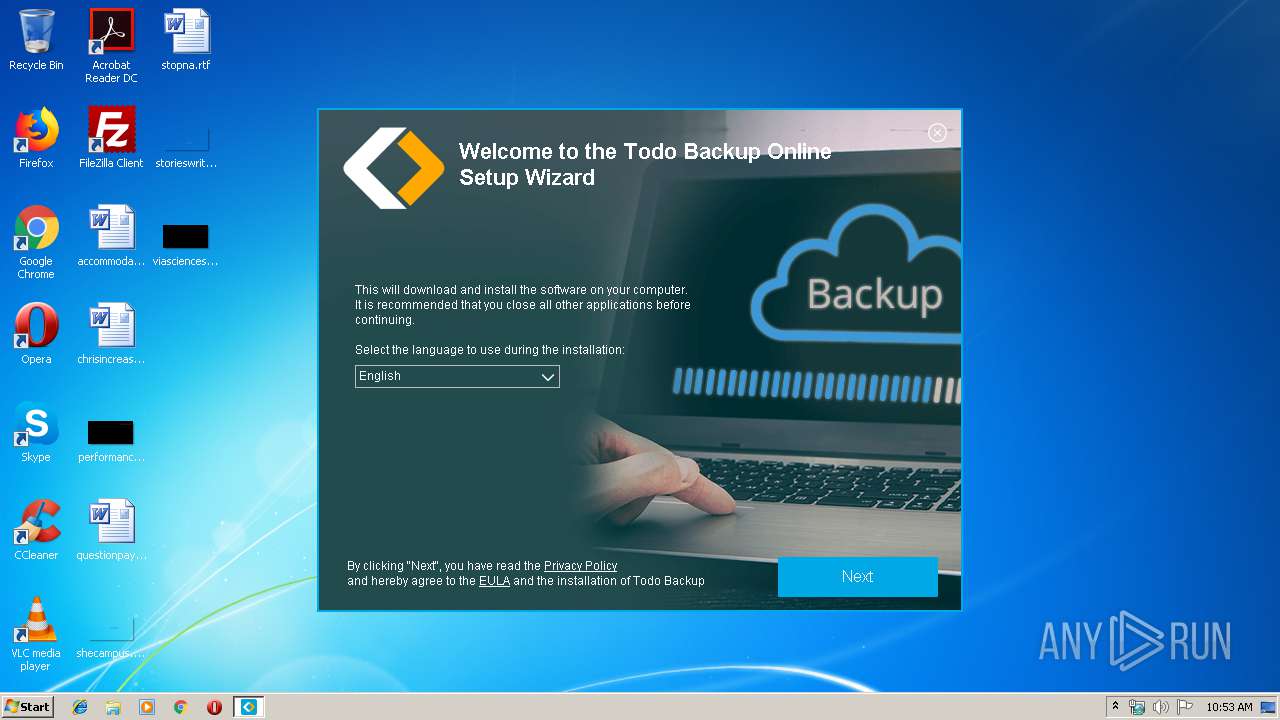
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9FD541513FD673DD939335A7D962F245 |
| SHA1: | 030FF95F70EEB7B15F6940C1396007DDF161D53F |
| SHA256: | A920374ACC358A3D1549A5CD47A6616AB6423E24F6EAD71EE05A5B0064964076 |
| SSDEEP: | 49152:1oXbVnMZ5MsGgrHVXjbFGFQnWDC7o4dhTQTSE48R/7RQRp:1oRMMOFG2W5qTQGwh7E |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Windows Product ID
- tb_free.exe (PID: 2872)
Reads the machine GUID from the registry
- tb_free.exe (PID: 2872)
Application launched itself
- tb_free.exe (PID: 3020)
Reads Environment values
- tb_free.exe (PID: 2872)
Reads CPU info
- tb_free.exe (PID: 2872)
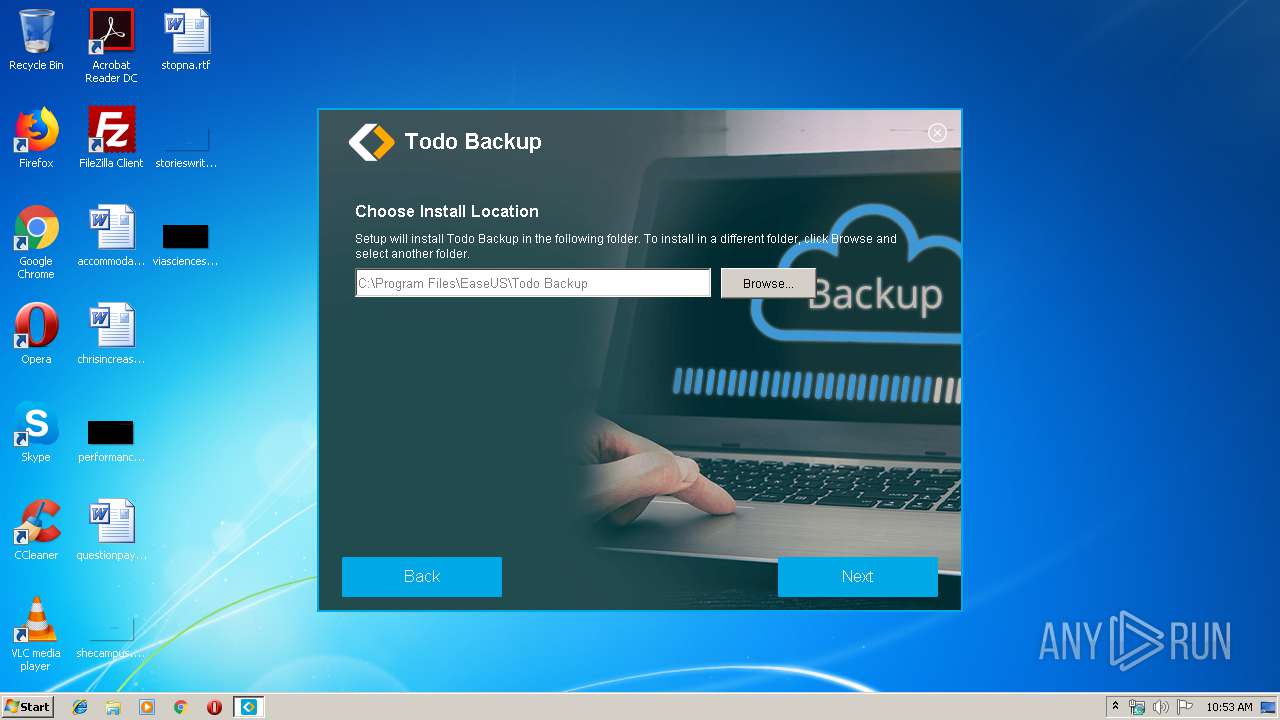
Creates files in the program directory
- tb_free.exe (PID: 2872)
Reads internet explorer settings
- tb_free.exe (PID: 2872)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 514048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c40 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.6.2.5 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Tunugupah Setup |
| FileVersion: | 4.6.2.5 |
| LegalCopyright: | File fast |
| ProductName: | Tunugupah |
| ProductVersion: | 5.4.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Tunugupah Setup |
| FileVersion: | 4.6.2.5 |
| LegalCopyright: | File fast |
| ProductName: | Tunugupah |
| ProductVersion: | 5.4.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009364 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59587 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.7391 |
BSS | 0x0000C000 | 0x00000E88 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x0007C700 | 0x0007C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.03766 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05007 | 1376 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 5.41663 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.10139 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.78195 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 4.7492 | 152104 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 2.21627 | 270376 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2872 | "C:\Users\admin\AppData\Local\Temp\tb_free.exe" /RSF /ppn:YyhwYgxaFRAiP211FM5W /mnl | C:\Users\admin\AppData\Local\Temp\tb_free.exe | tb_free.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Tunugupah Setup Exit code: 0 Version: 4.6.2.5 Modules
| |||||||||||||||
| 3020 | "C:\Users\admin\AppData\Local\Temp\tb_free.exe" | C:\Users\admin\AppData\Local\Temp\tb_free.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Tunugupah Setup Exit code: 0 Version: 4.6.2.5 Modules
| |||||||||||||||
Total events
828
Read events
796
Write events
32
Delete events
0
Modification events
| (PID) Process: | (3020) tb_free.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3020) tb_free.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2872) tb_free.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2872) tb_free.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2872) tb_free.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2872) tb_free.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\tb_free_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2872) tb_free.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\tb_free_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2872) tb_free.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\tb_free_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2872) tb_free.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\tb_free_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2872) tb_free.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\tb_free_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
4
Text files
63
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | tb_free.exe | C:\Users\admin\AppData\Local\Temp\0014F720.log | — | |
MD5:— | SHA256:— | |||
| 2872 | tb_free.exe | C:\Users\admin\AppData\Local\Temp\inH137398452647\css\main.css | text | |
MD5:— | SHA256:— | |||
| 2872 | tb_free.exe | C:\Users\admin\AppData\Local\Temp\inH137398452647\css\ie6_main.scss | text | |
MD5:— | SHA256:— | |||
| 2872 | tb_free.exe | C:\Users\admin\AppData\Local\Temp\inH137398452647\css\ie6_main.css | text | |
MD5:— | SHA256:— | |||
| 2872 | tb_free.exe | C:\Users\admin\AppData\Local\Temp\inH137398452647\css\main.scss | text | |
MD5:— | SHA256:— | |||
| 2872 | tb_free.exe | C:\Users\admin\AppData\Local\Temp\inH137398452647\css\helpers\_border-radius.scss | text | |
MD5:6BDF3FD89410E39D33F8137E04AD4A16 | SHA256:2C6B98CB19C3E3A0E37472767C53DF213243AE92BC80EF9A7F5BAA17F7B6FA31 | |||
| 2872 | tb_free.exe | C:\Users\admin\AppData\Local\Temp\inH137398452647\css\helpers\_align.scss | text | |
MD5:BBBBD243F9525ACC7DC6077010627409 | SHA256:1F11B5F53E0AA7DA1A1559A1A5CDD52BF03119EA74E5091462461C550E9288DB | |||
| 2872 | tb_free.exe | C:\Users\admin\AppData\Local\Temp\inH137398452647\form.bmp.Mask | binary | |
MD5:D2FC989F9C2043CD32332EC0FAD69C70 | SHA256:27DD029405CBFB0C3BF8BAC517BE5DB9AA83E981B1DC2BD5C5D6C549FA514101 | |||
| 2872 | tb_free.exe | C:\Users\admin\AppData\Local\Temp\inH137398452647\css\_helpers.scss | text | |
MD5:5F158DBBD9FC4594A2F6C13854501916 | SHA256:BF12B79F67F1CB9988797F7D81F6F504C8DFE0F0435482E64819A140DBC8DA14 | |||
| 2872 | tb_free.exe | C:\Users\admin\AppData\Local\Temp\inH137398452647\css\helpers\_border.scss | text | |
MD5:681FB7EB197E8E7EBD89F828D1181FD6 | SHA256:51E8AFA69ED6D92EB82F71939B0B8FD34EF23FAECEE457698238E5A4F28DF984 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
30
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
ww2.cenecraye.com |
| unknown |
vpn.cenecraye.com |
| unknown |
portal.cenecraye.com |
| unknown |
support.cenecraye.com |
| unknown |
remote.cenecraye.com |
| unknown |