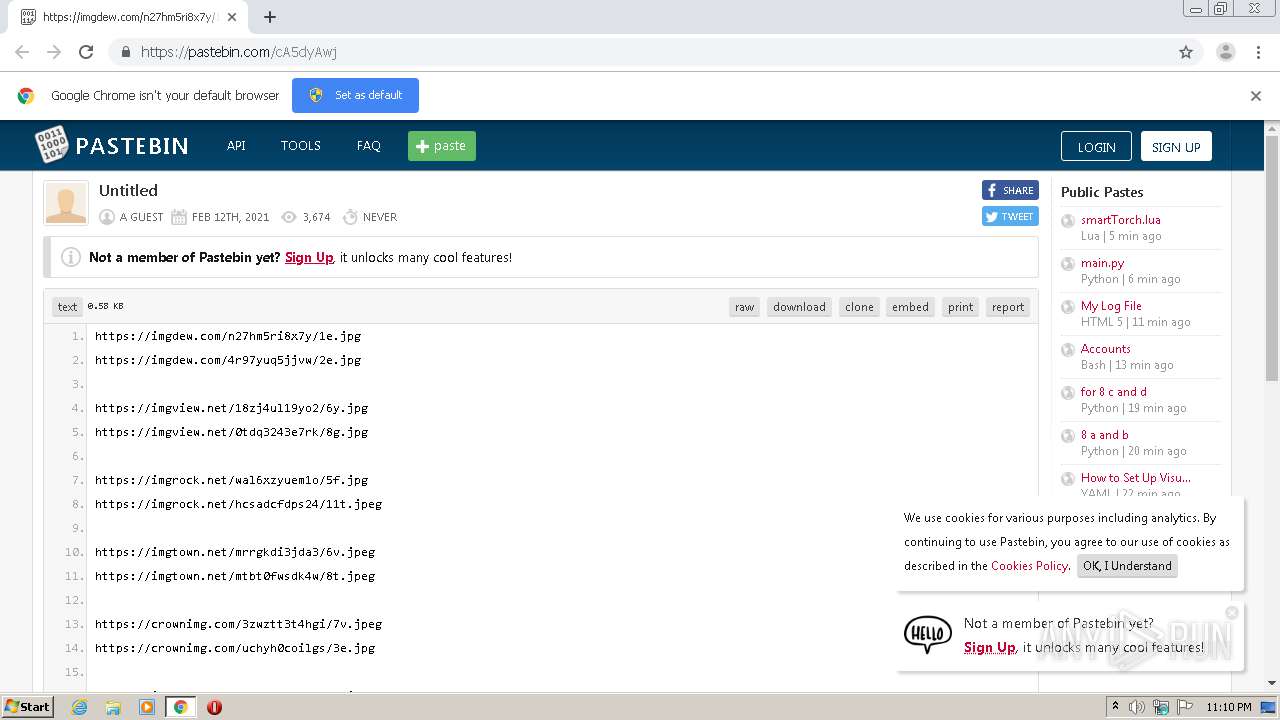
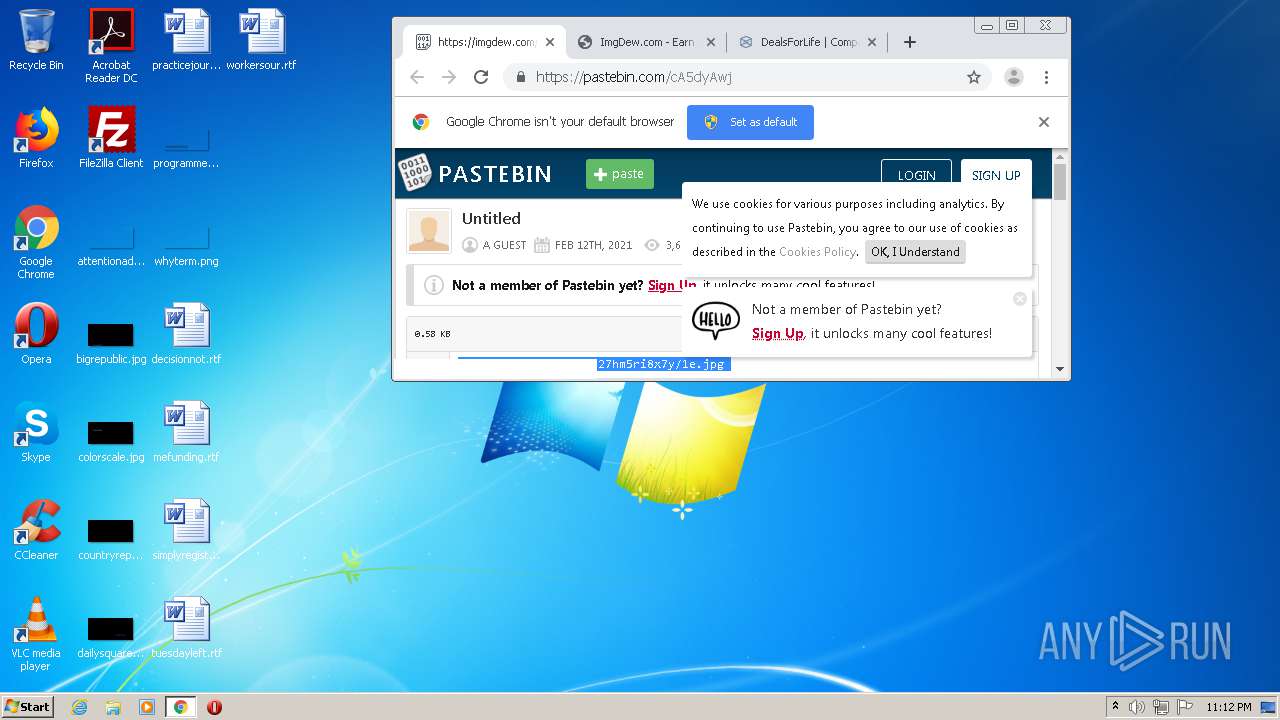
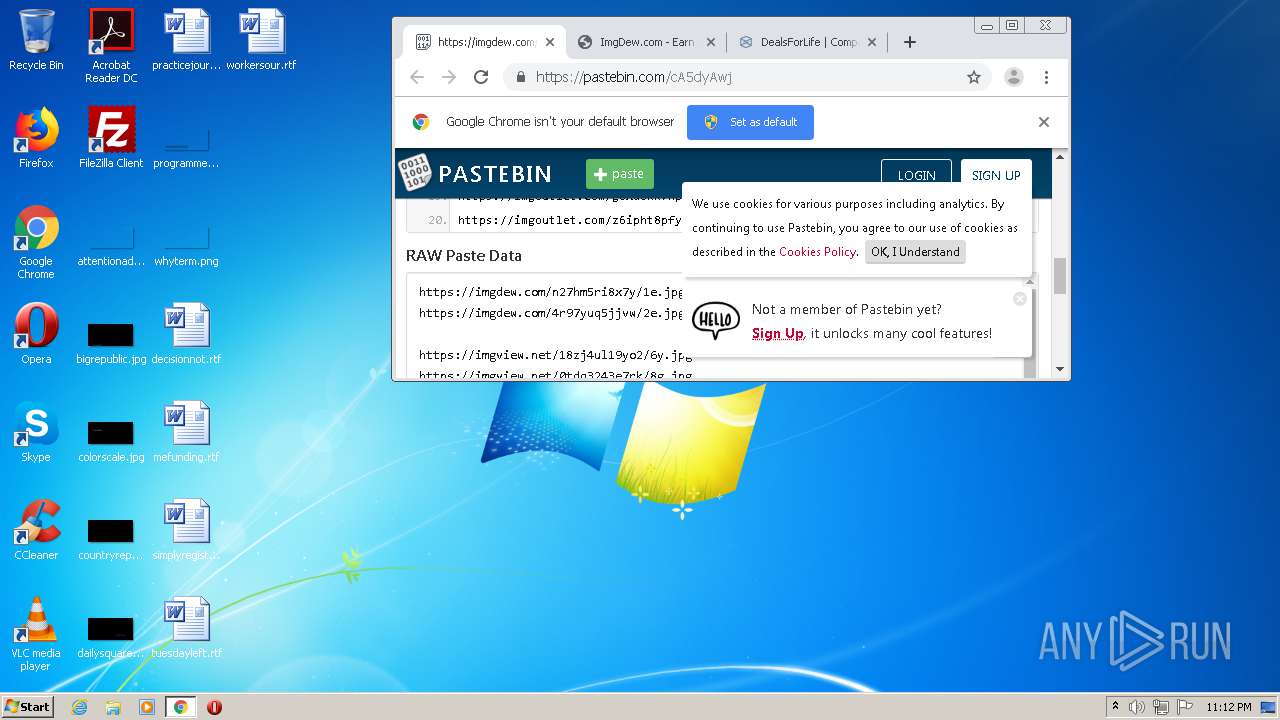
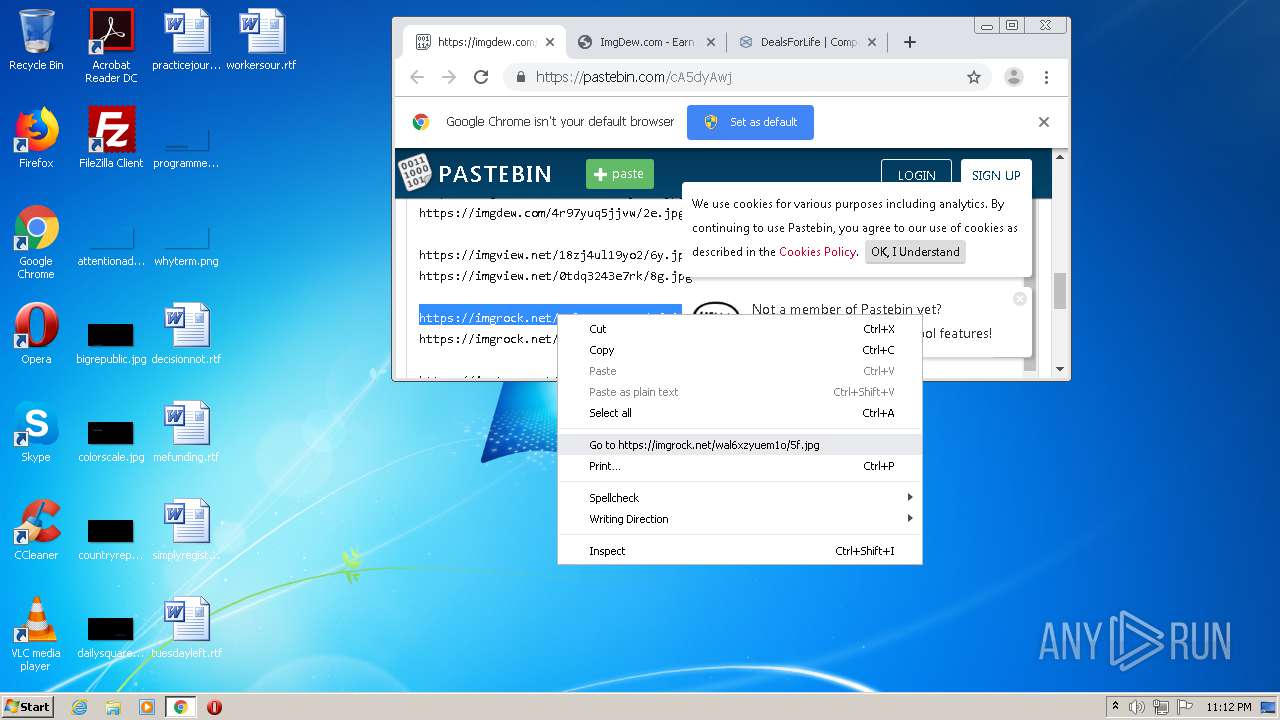
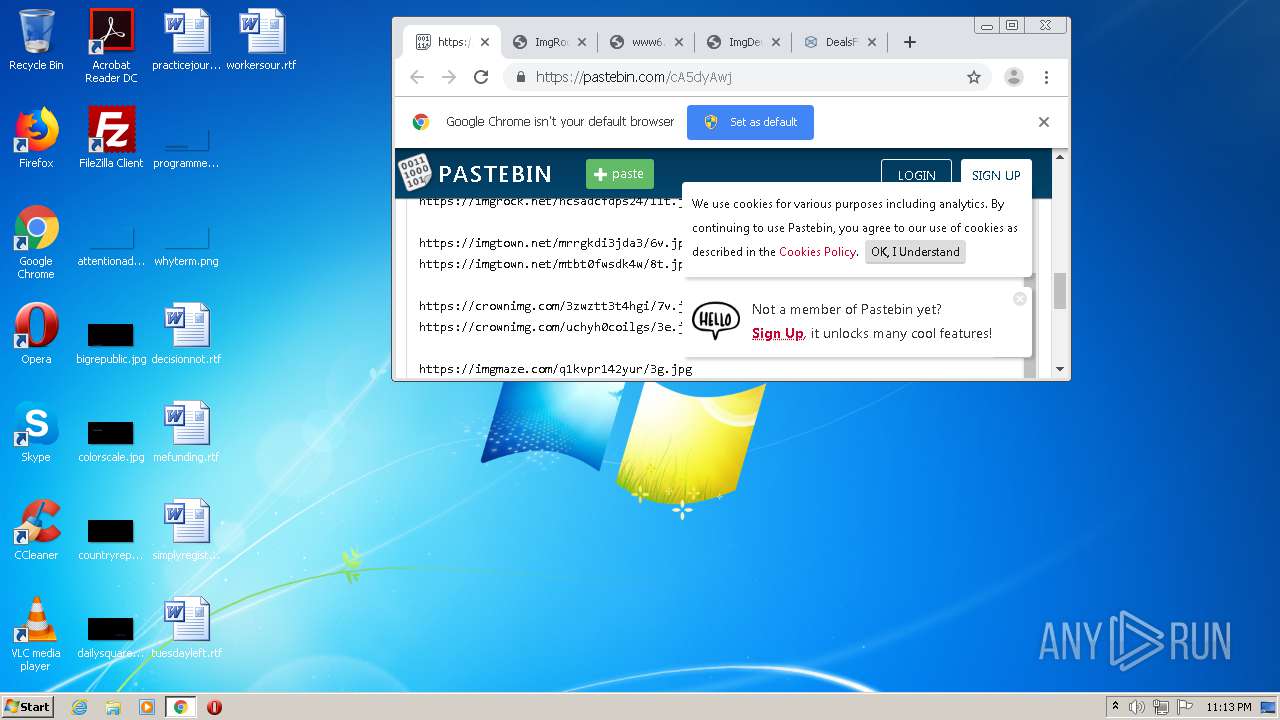
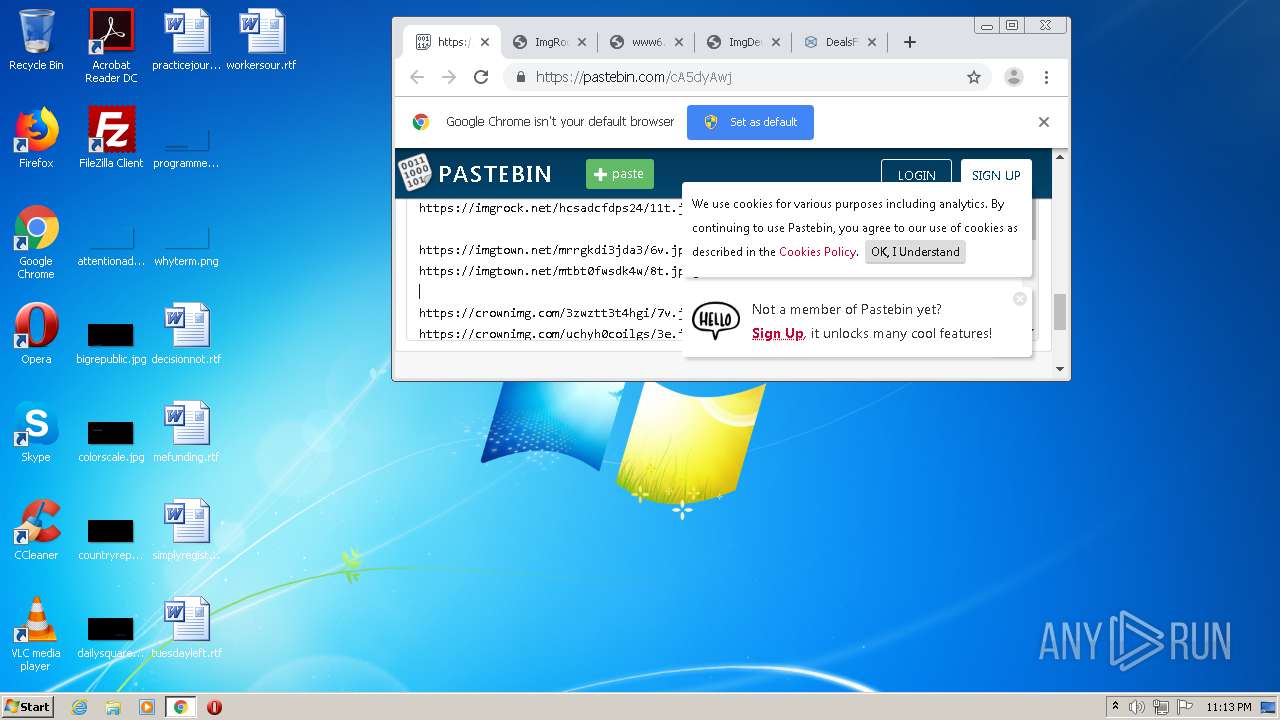
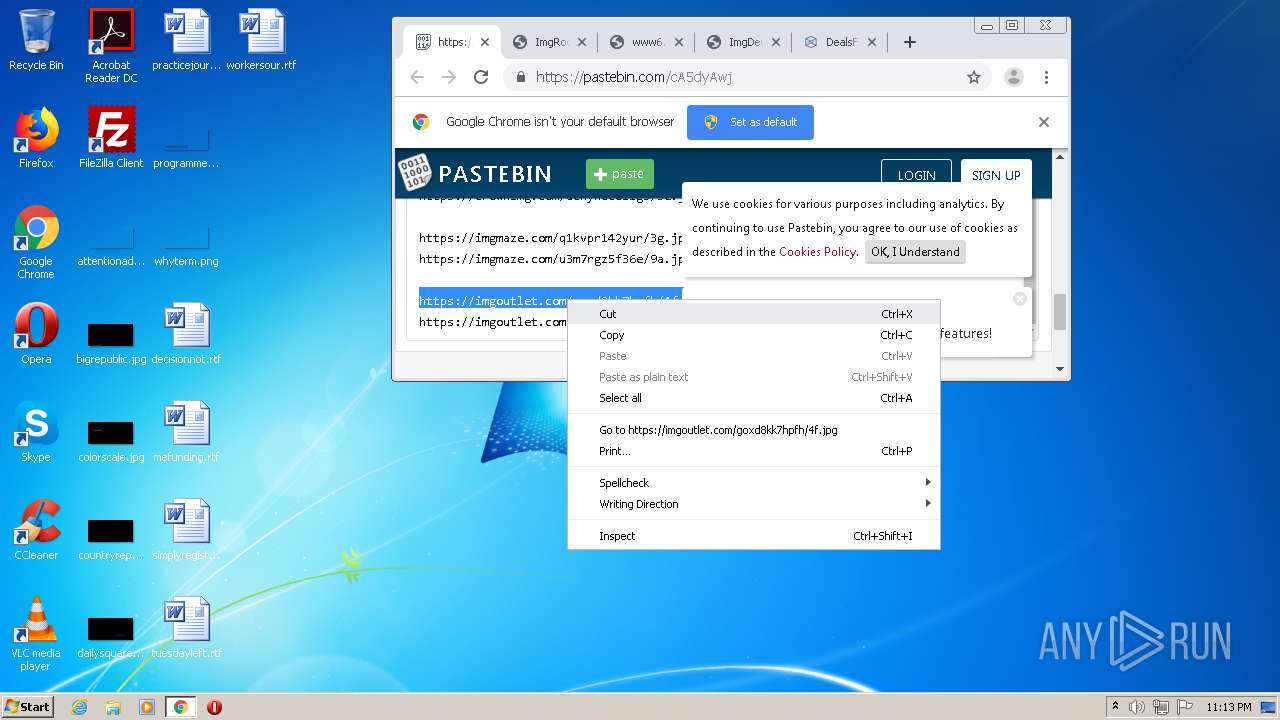
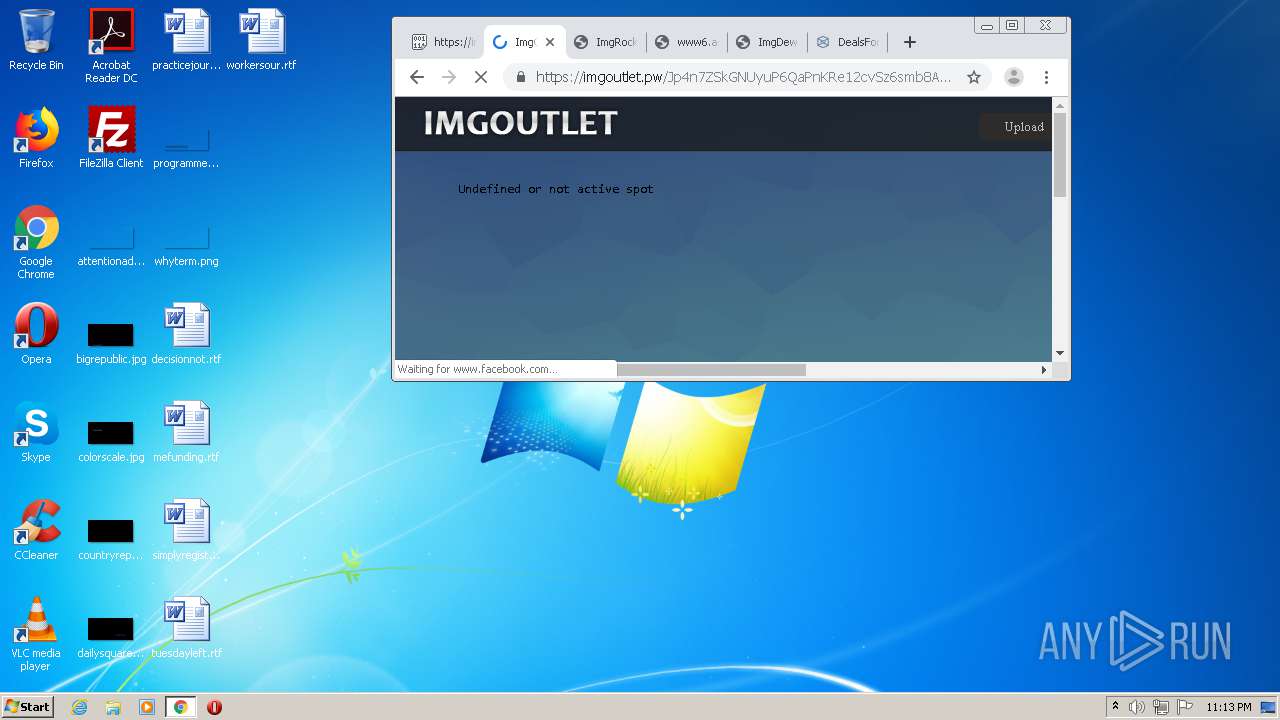
| URL: | https://www.pastebin.com/cA5dyAwj |
| Full analysis: | https://app.any.run/tasks/f1337950-f608-4f0d-b4c1-67cf6e1b0f0b |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2021, 23:10:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5308D3E8C8B393EFFC588B24926FBBC0 |
| SHA1: | A5214AE125482B355F911BF1287633045460FA3F |
| SHA256: | A8EFC20AF13B4655D591F8F9DE351112620AD175F31B3AFCFF1CC12A5C6878D9 |
| SSDEEP: | 3:N8DSLvAsLZ2/cbP:2OL70/cbP |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 1348)
- chrome.exe (PID: 3452)
Application launched itself
- chrome.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
39
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,14203180879581755505,1674787844535333249,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2457357782076694115 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2128 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,14203180879581755505,1674787844535333249,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6531056311511453226 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,14203180879581755505,1674787844535333249,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6231572267522312756 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://www.pastebin.com/cA5dyAwj" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,14203180879581755505,1674787844535333249,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10229430995238363920 --mojo-platform-channel-handle=3924 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,14203180879581755505,1674787844535333249,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9673878632514433419 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,14203180879581755505,1674787844535333249,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12462928141693812879 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,14203180879581755505,1674787844535333249,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16511455221905840634 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,14203180879581755505,1674787844535333249,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16245001250341390086 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
657
Read events
572
Write events
82
Delete events
3
Modification events
| (PID) Process: | (1348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1348-13257645042486125 |
Value: 259 | |||
| (PID) Process: | (1348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1348) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
145
Text files
147
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60270AF3-544.pma | — | |
MD5:— | SHA256:— | |||
| 1348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d120fd5c-229a-43c6-8004-abd3e4166d13.tmp | — | |
MD5:— | SHA256:— | |||
| 1348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12a0bc.TMP | text | |
MD5:— | SHA256:— | |||
| 1348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF12a0bc.TMP | text | |
MD5:— | SHA256:— | |||
| 1348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF12a10b.TMP | text | |
MD5:— | SHA256:— | |||
| 1348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF12a2ff.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
202
DNS requests
99
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
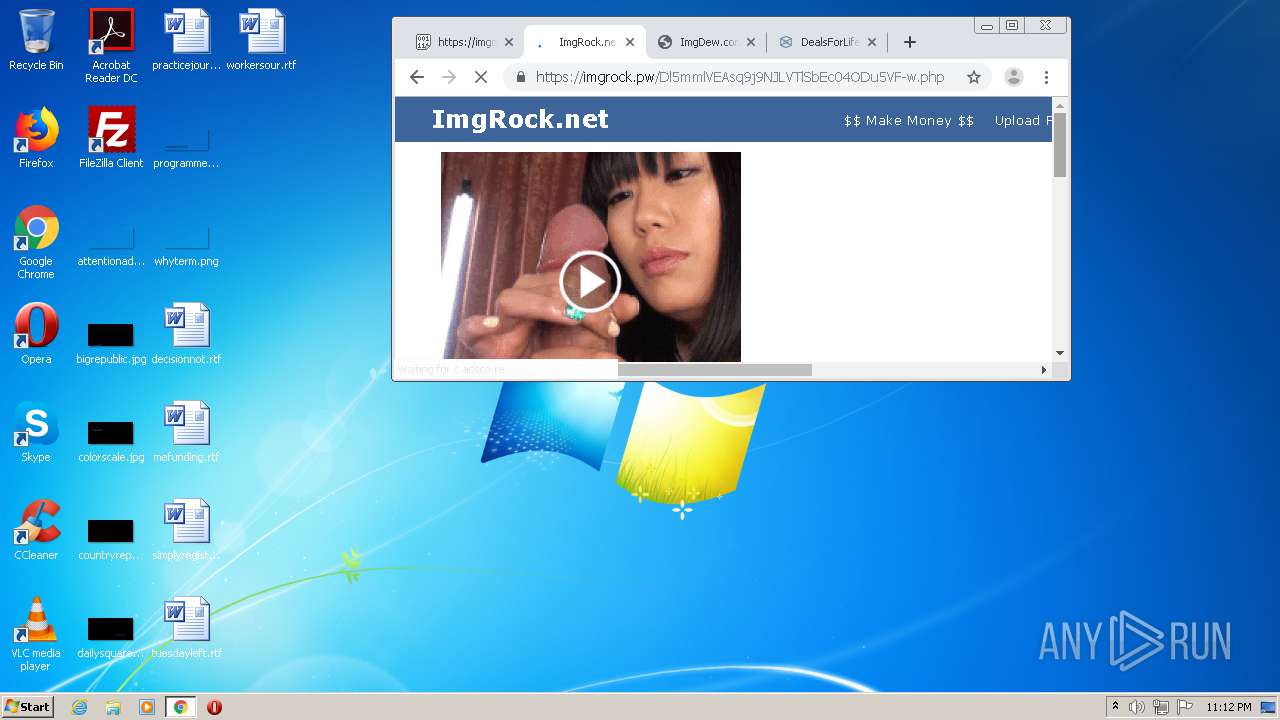
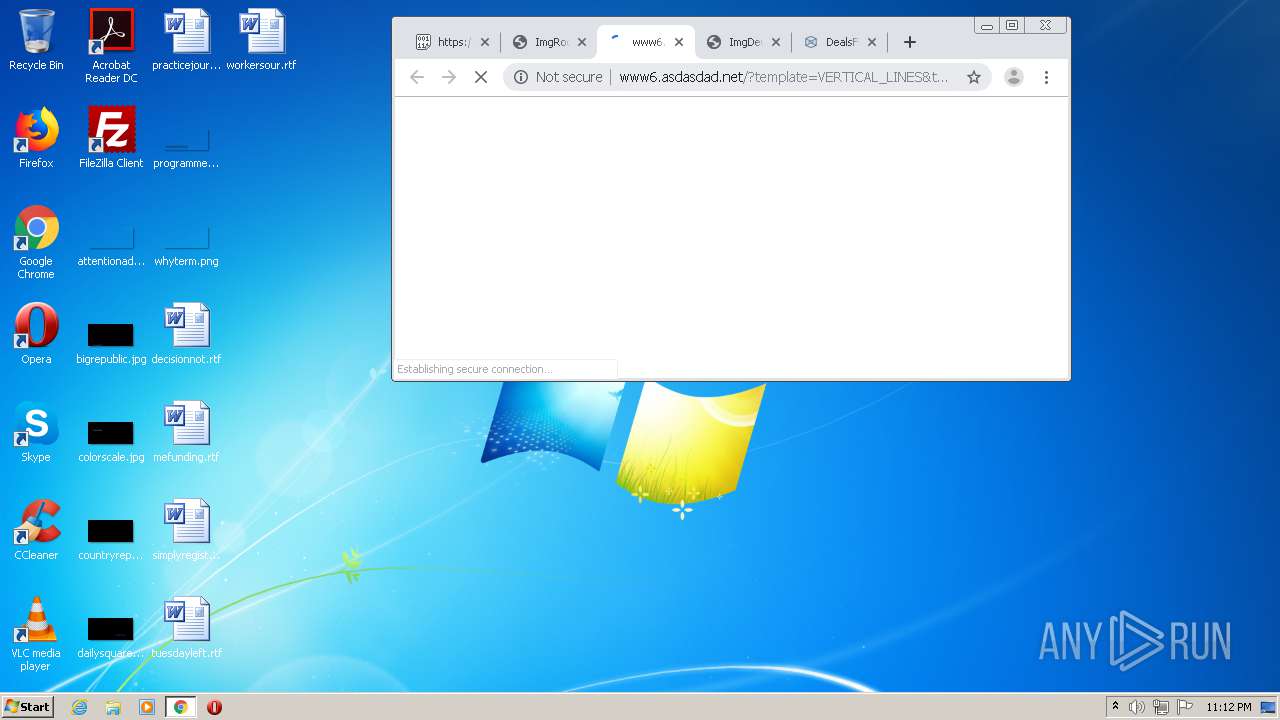
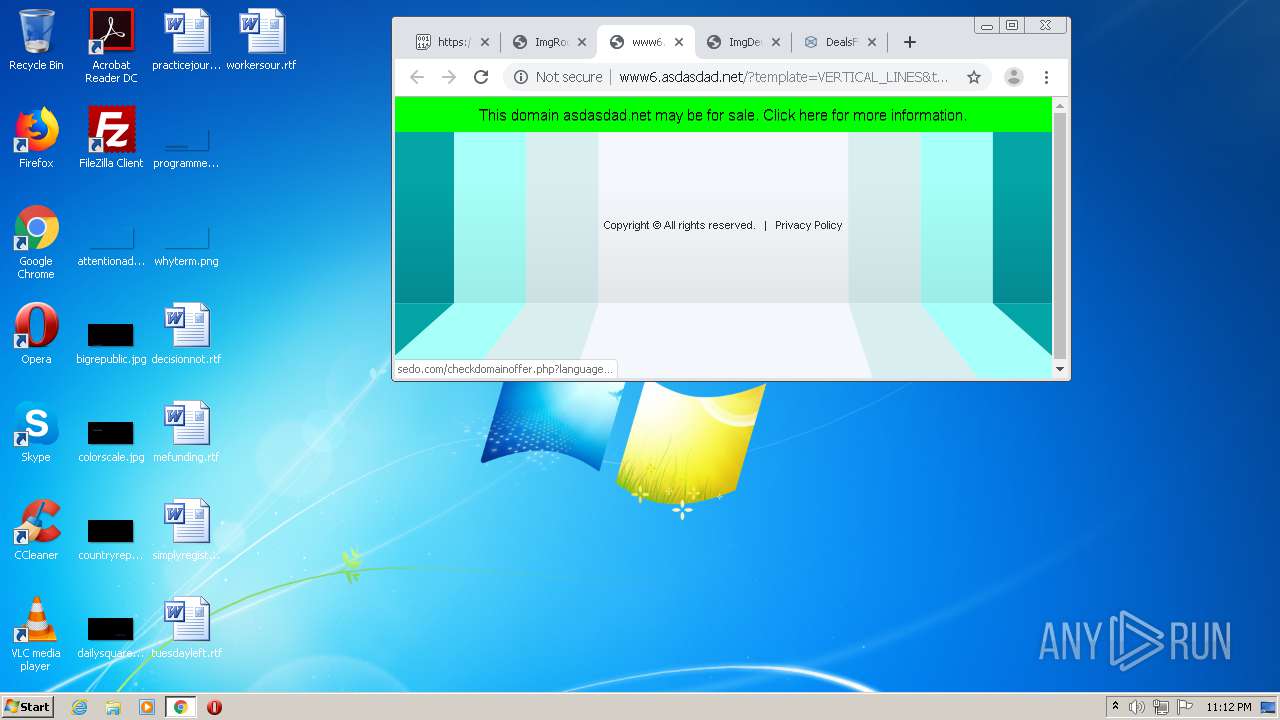
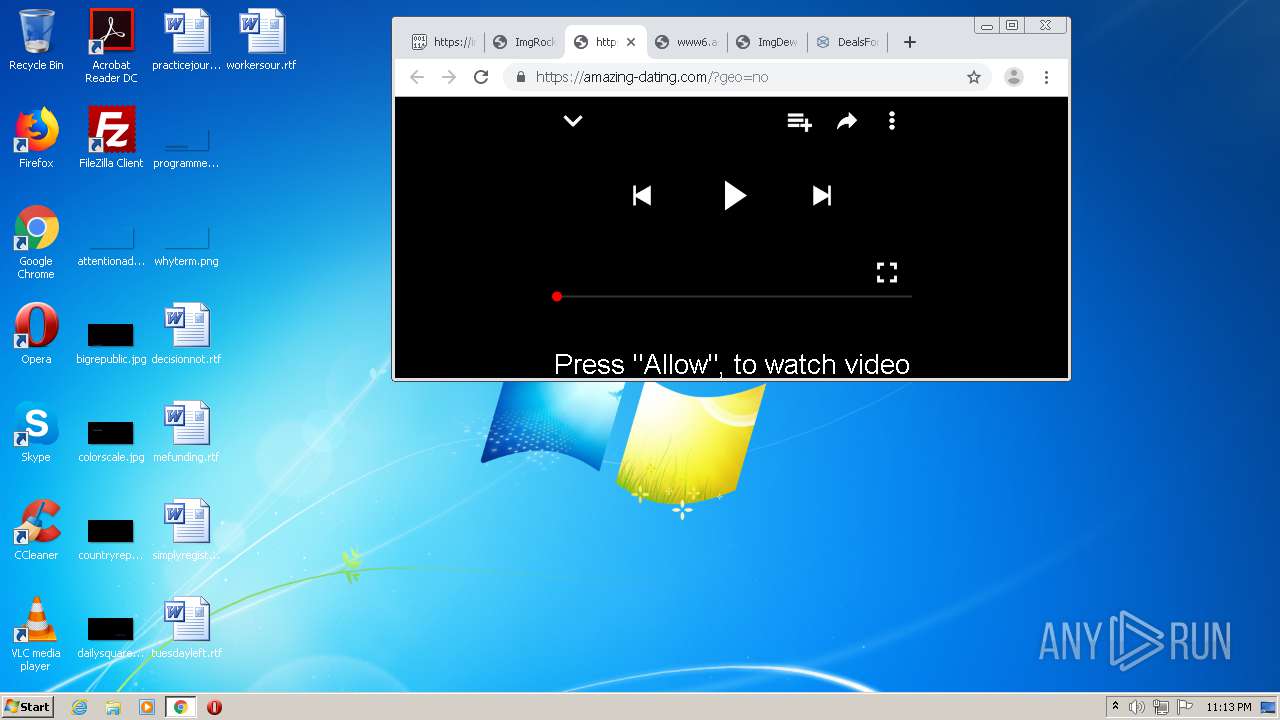
3452 | chrome.exe | GET | 403 | 192.243.59.12:80 | http://terraclicks.com/anonymous/ | US | — | — | whitelisted |
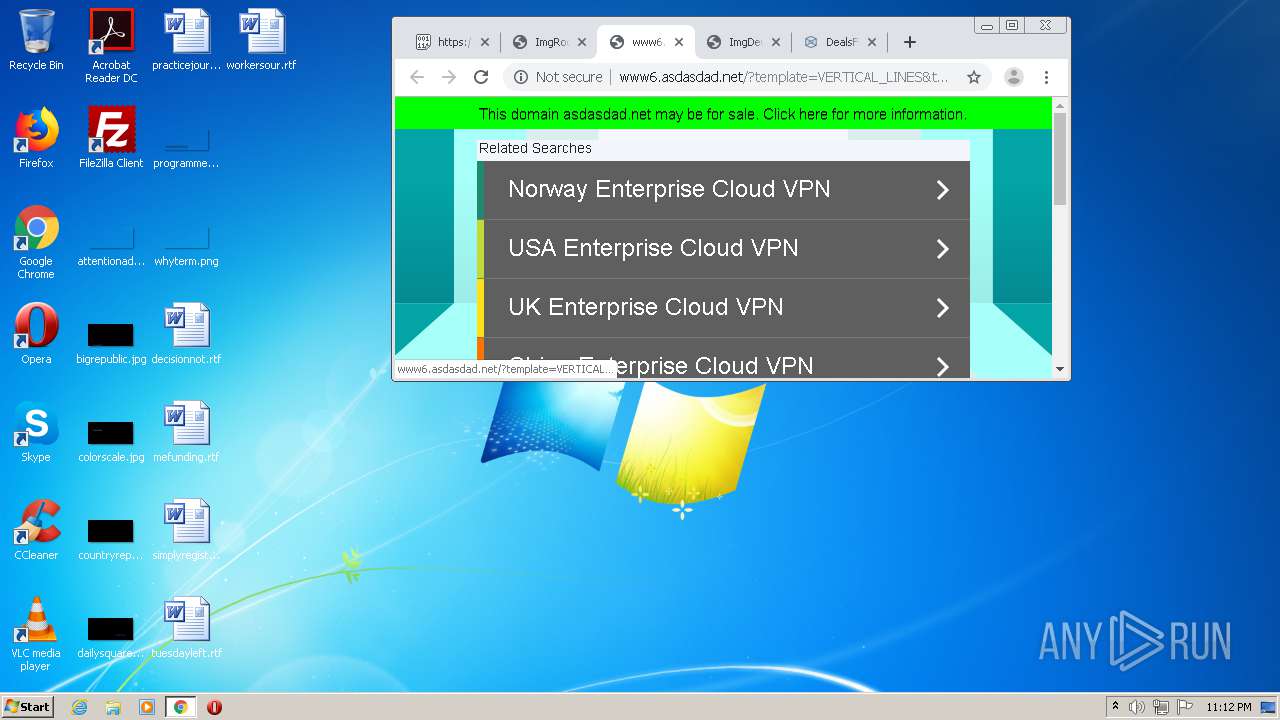
3452 | chrome.exe | GET | 200 | 35.186.238.101:80 | http://www6.asdasdad.net/?template=VERTICAL_LINES&tdfs=1&s_token=1613171571.0015158733&uuid=1613171571.0015158733&term=Norway%20Enterprise%20Cloud%20VPN&term=USA%20Enterprise%20Cloud%20VPN&term=UK%20Enterprise%20Cloud%20VPN&term=China%20Enterprise%20Cloud%20VPN&term=Korea%20Enterprise%20Cloud%20VPN&term=Australia%20Enterprise%20Cloud%20VPN&term=Japan%20Enterprise%20Cloud%20VPN&term=Hong%20Kong%20Enterprise%20Cloud%20VPN&term=Russia%20Enterprise%20Cloud%20VPN&term=Taiwan%20Enterprise%20Cloud%20VPN&backfill=0 | US | html | 2.46 Kb | whitelisted |
3452 | chrome.exe | GET | 200 | 45.33.2.79:80 | http://asdasdad.net/ | US | html | 1.53 Kb | malicious |
3452 | chrome.exe | GET | 200 | 45.33.2.79:80 | http://asdasdad.net/mtm/async/.eJyrViotylSyUtJX0lFKLEovBjKBrKLUtNSi1CIIJyO_uCQ-LzE3FchNLE4BoRS9vNQSpVoAK6oTBA:1lAhcJ:2mxj6GTIbHfQNPQK6upEEYLdRjo/1 | US | text | 512 b | malicious |
3452 | chrome.exe | GET | 200 | 45.33.2.79:80 | http://asdasdad.net/favicon.ico | US | image | 43 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
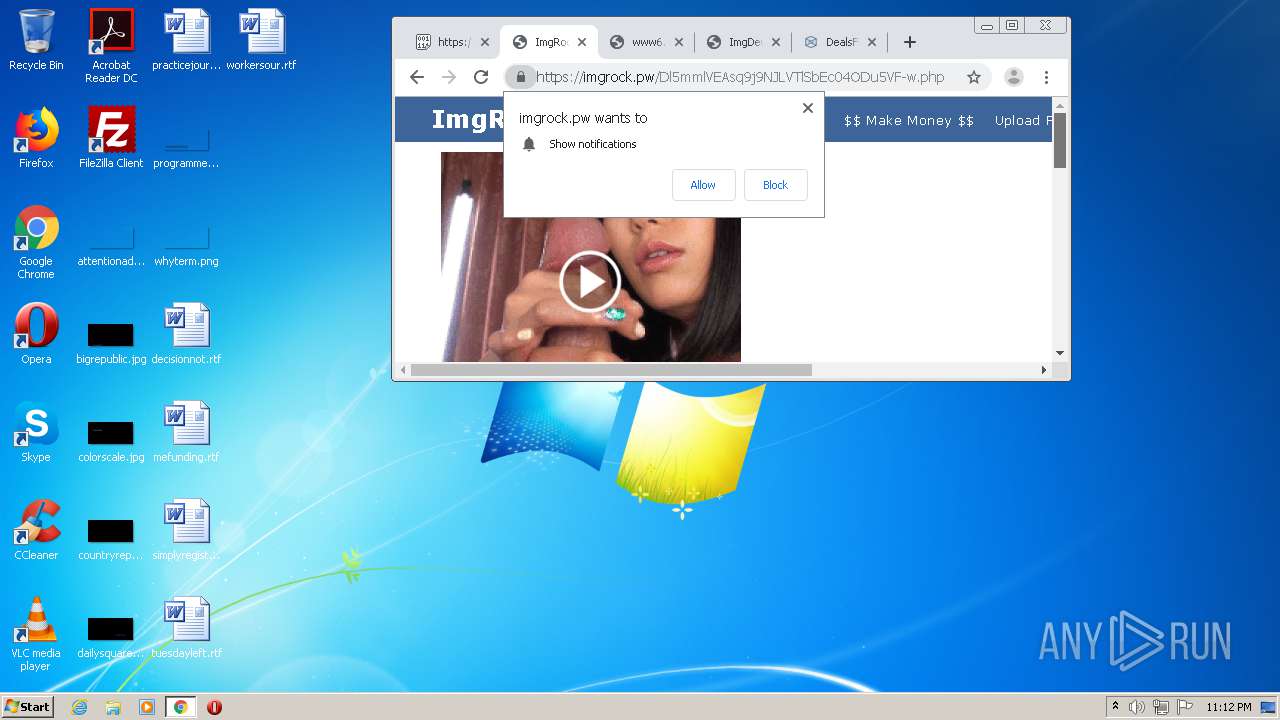
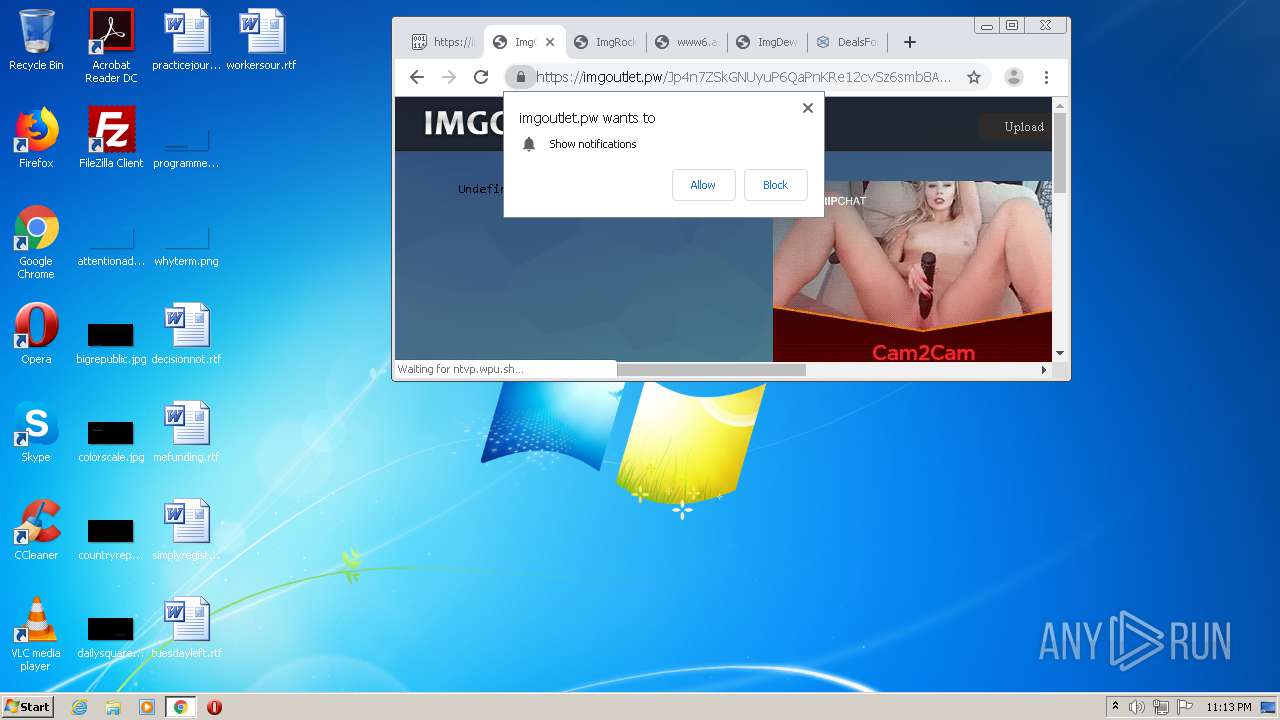
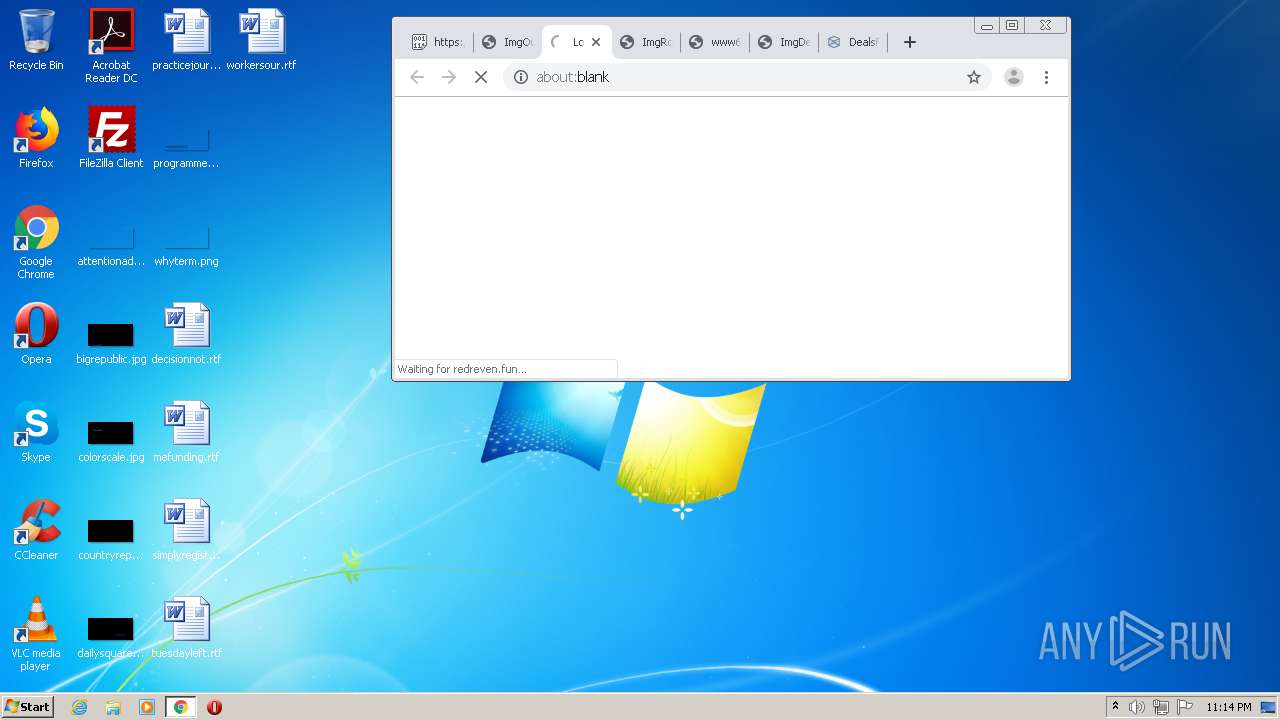
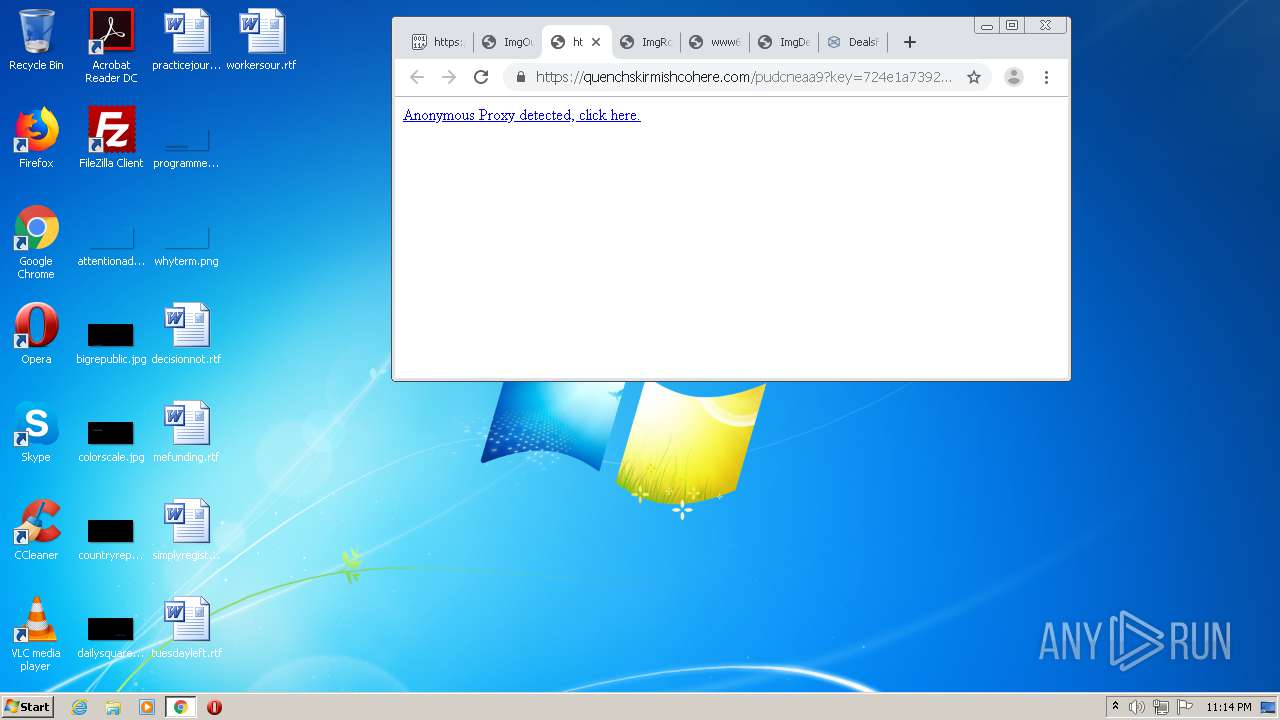
3452 | chrome.exe | 65.9.69.29:443 | hinksdeba.top | AT&T Services, Inc. | US | unknown |
3452 | chrome.exe | 172.64.132.18:443 | freychang.fun | Cloudflare Inc | US | unknown |
3452 | chrome.exe | 185.60.216.35:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
3452 | chrome.exe | 195.181.175.48:443 | www.blockadsnot.com | Datacamp Limited | DE | suspicious |
3452 | chrome.exe | 104.23.98.190:443 | www.pastebin.com | Cloudflare Inc | US | malicious |
3452 | chrome.exe | 172.217.17.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 216.58.212.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 142.250.179.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 172.217.20.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 74.125.143.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.pastebin.com |
| shared |
accounts.google.com |
| shared |
pastebin.com |
| malicious |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
clients1.google.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
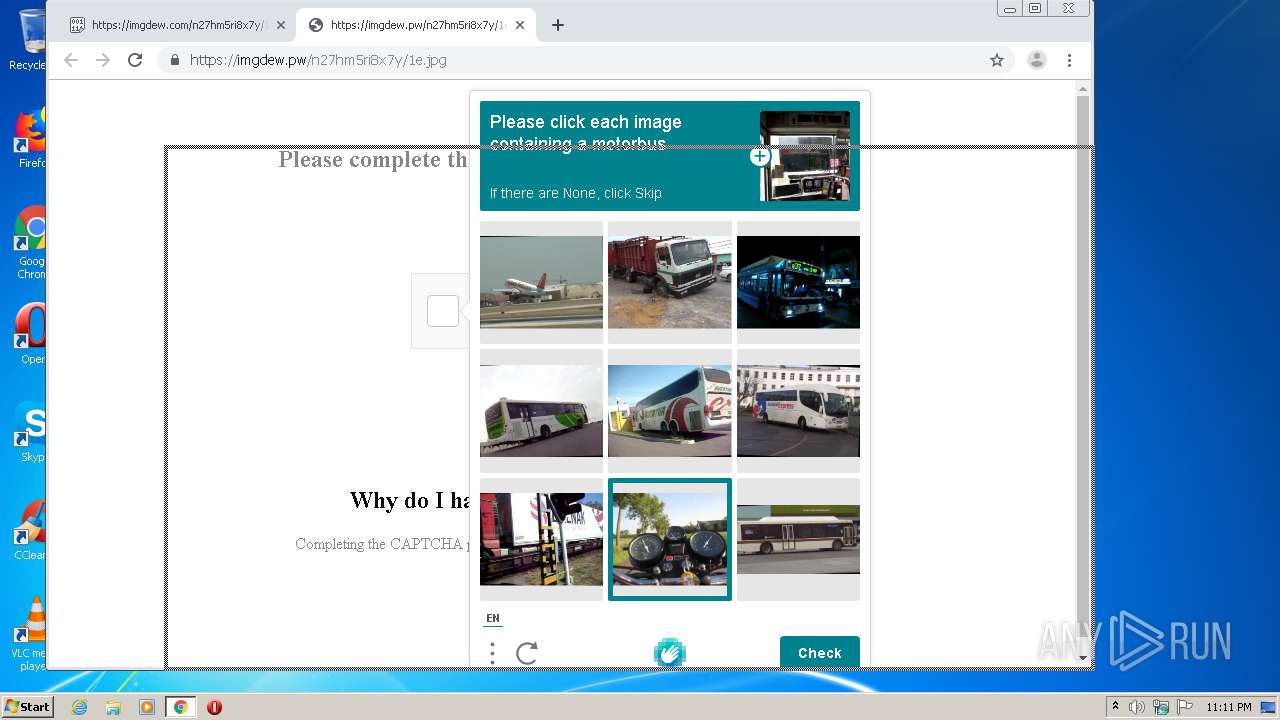
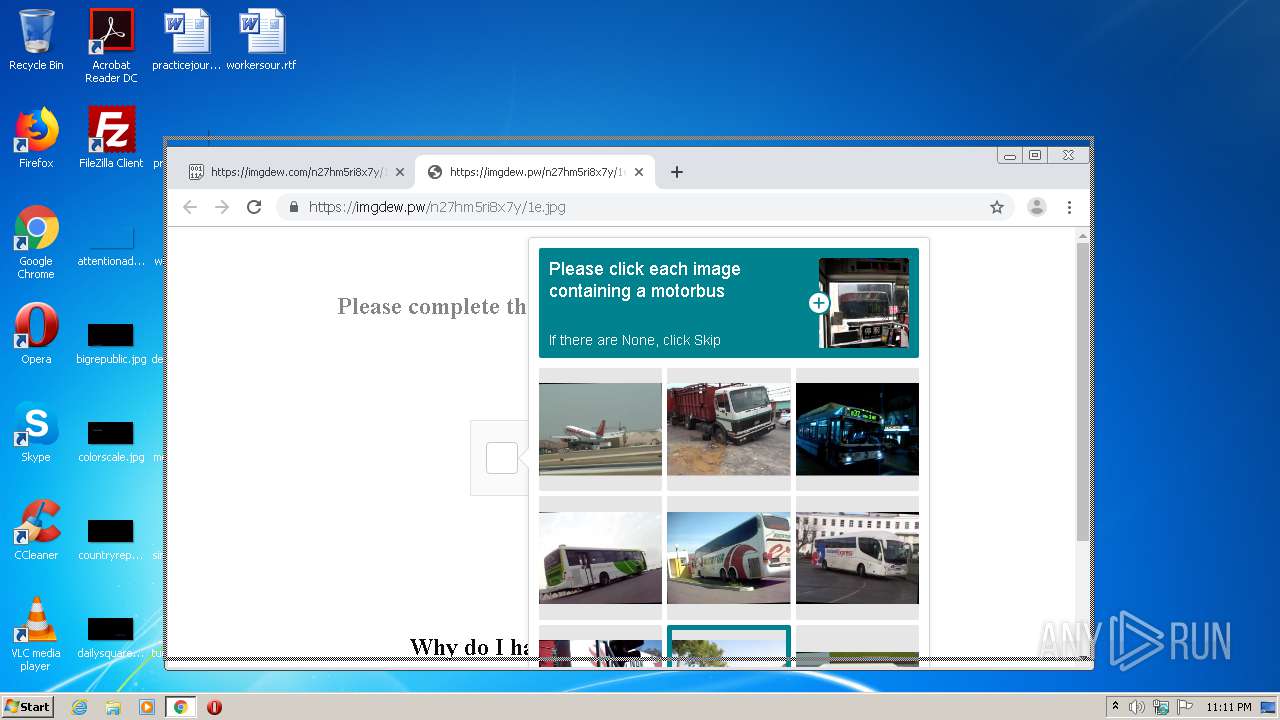
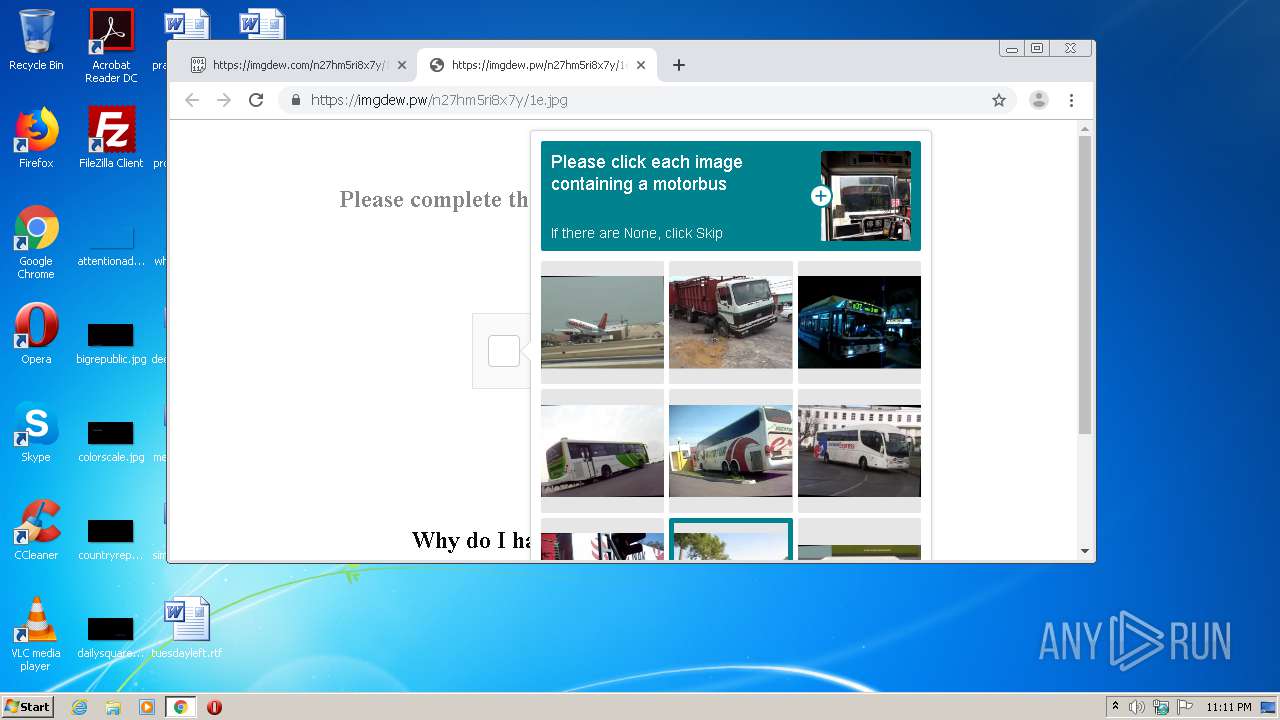
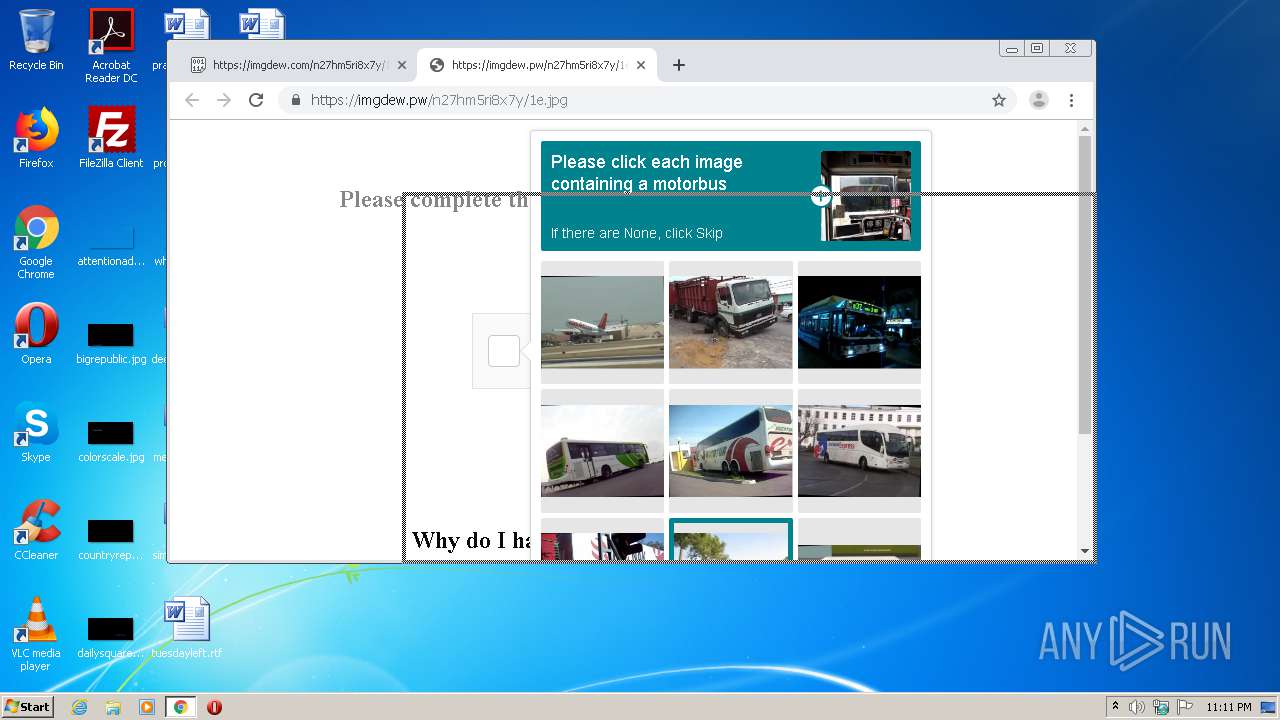
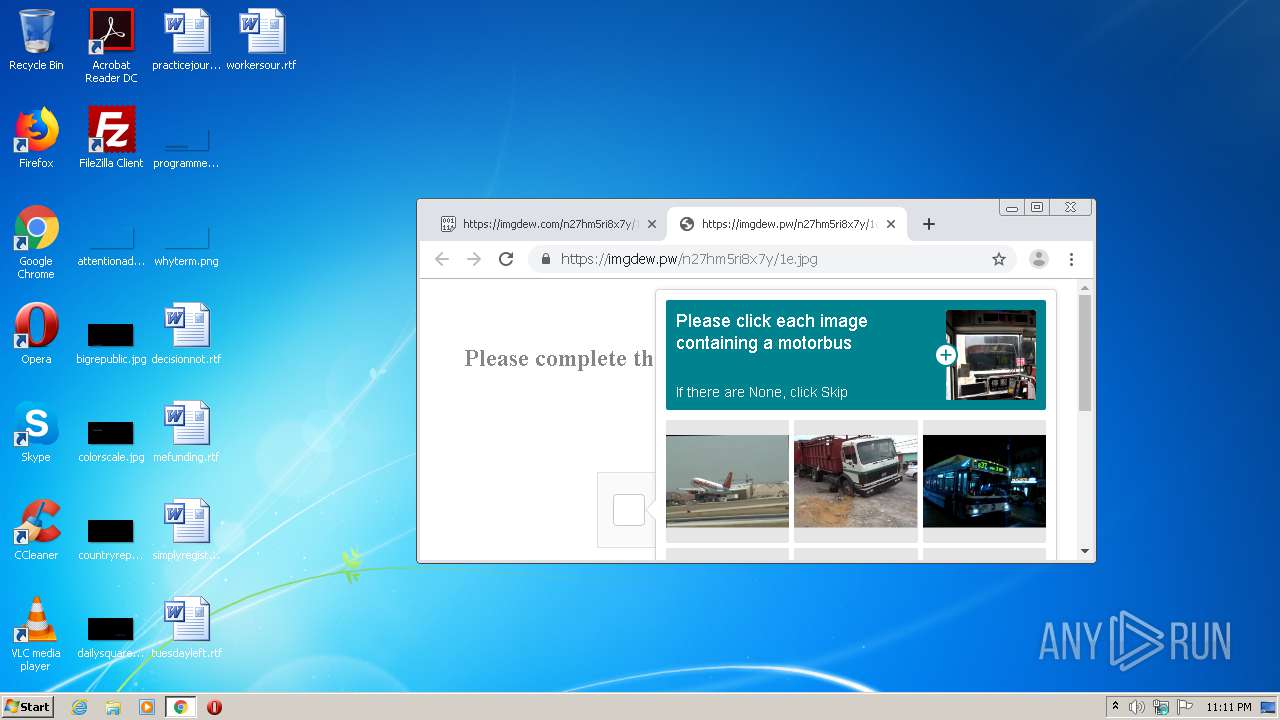
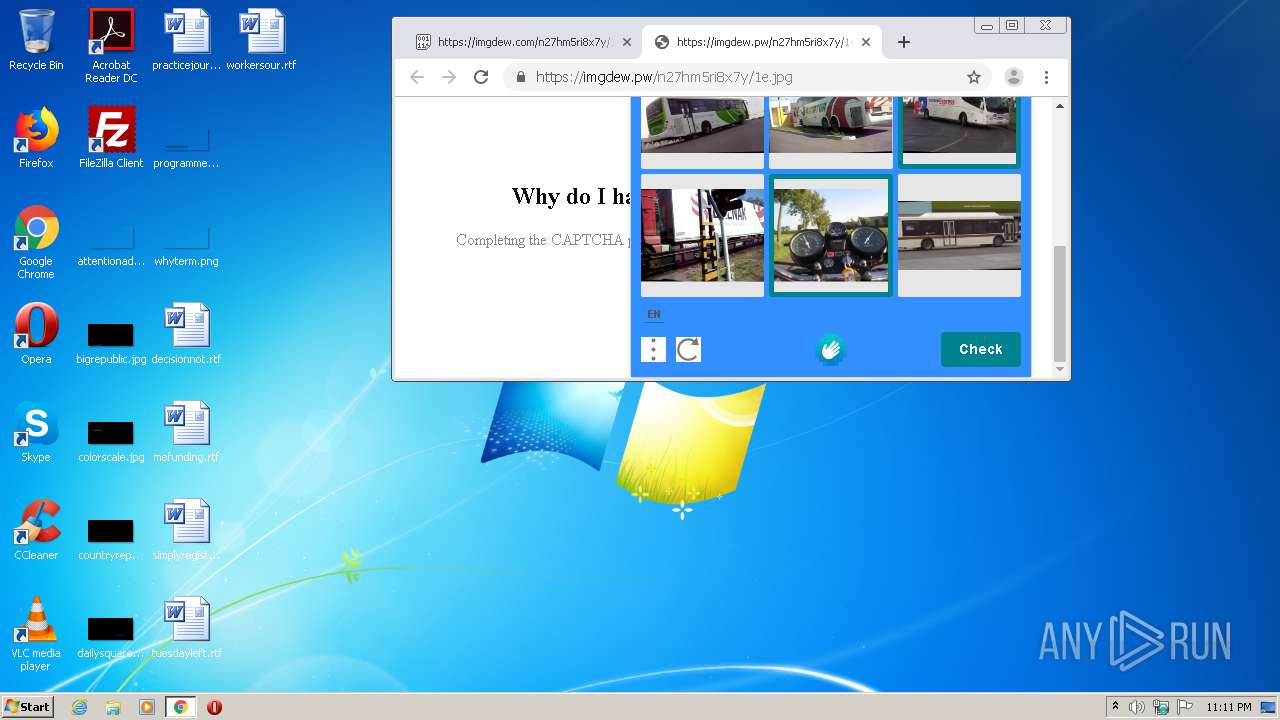
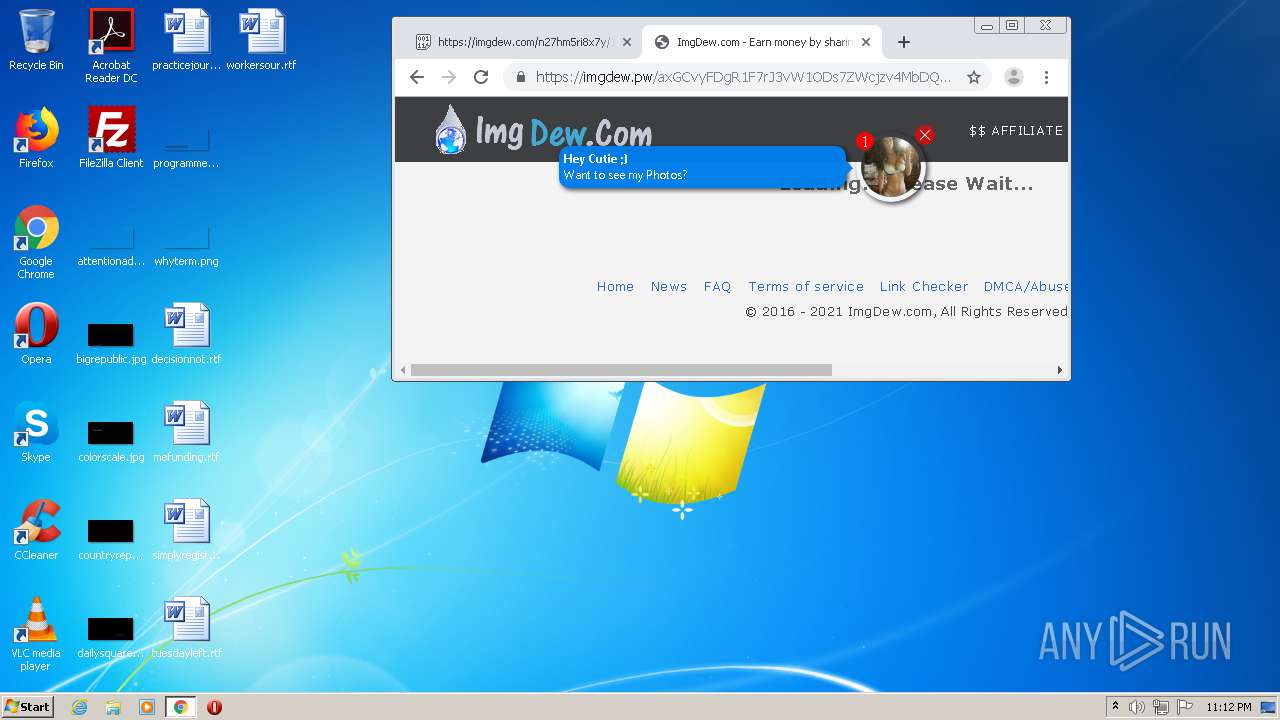
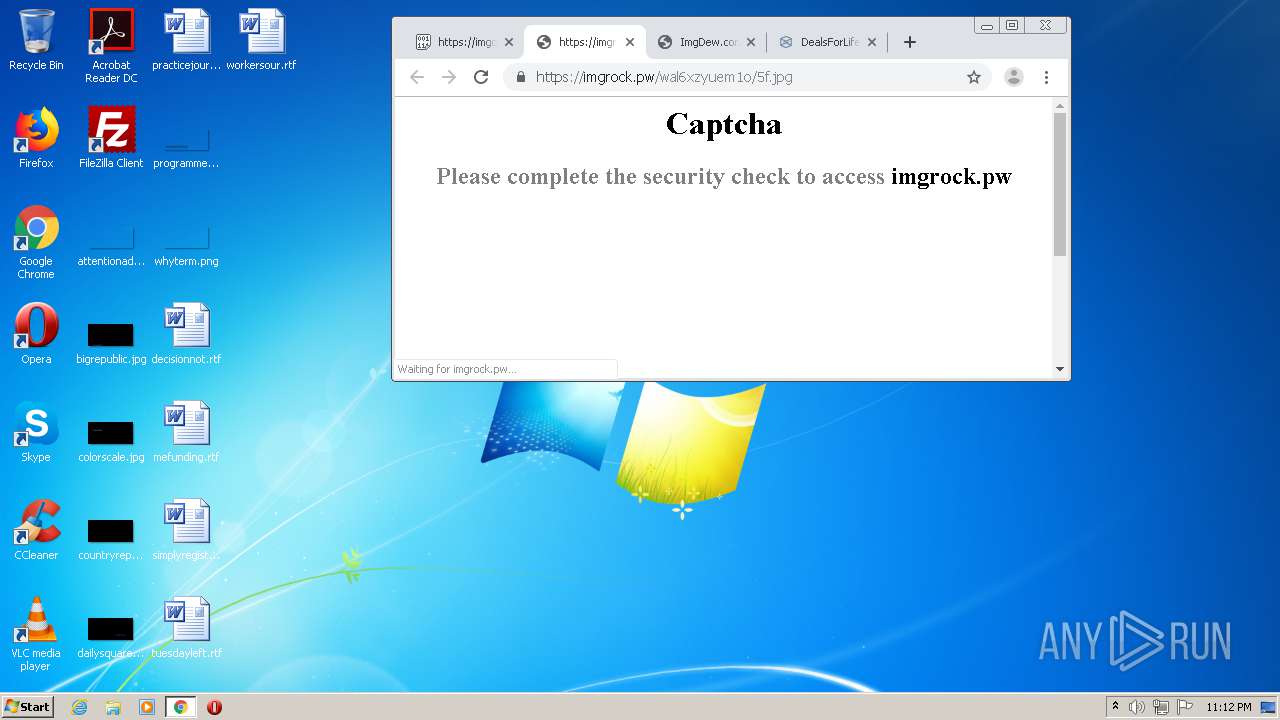
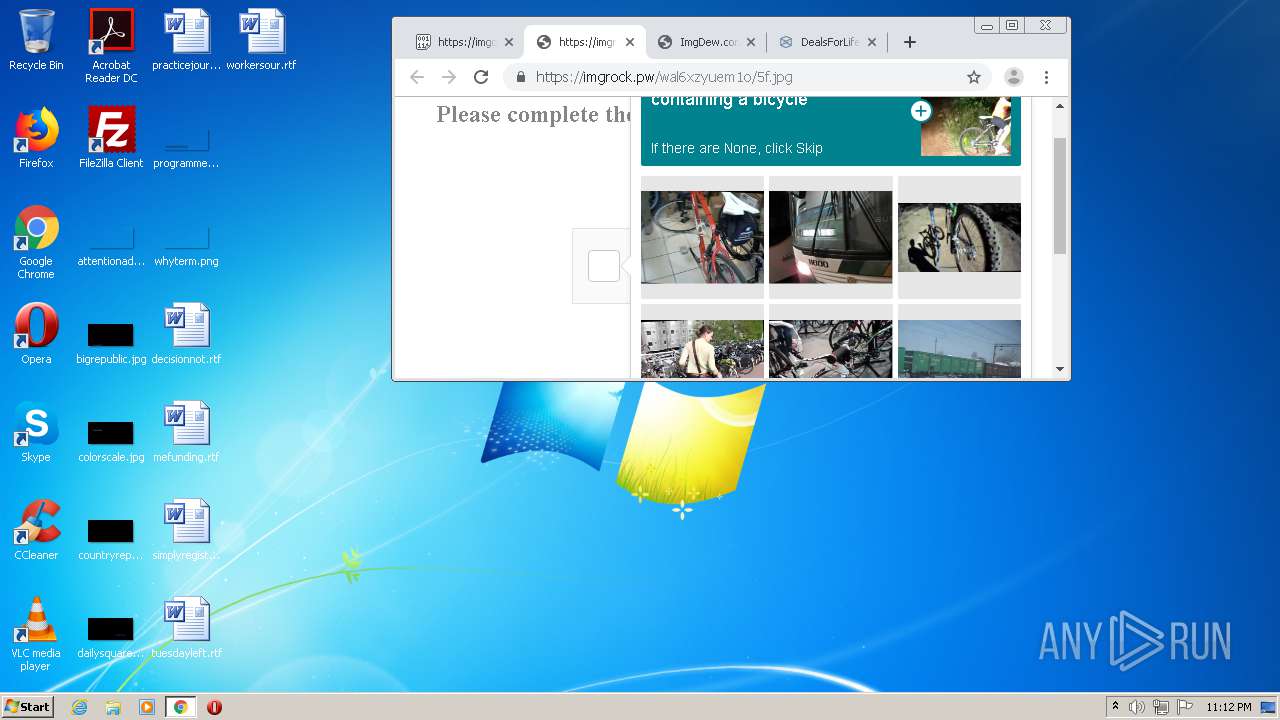
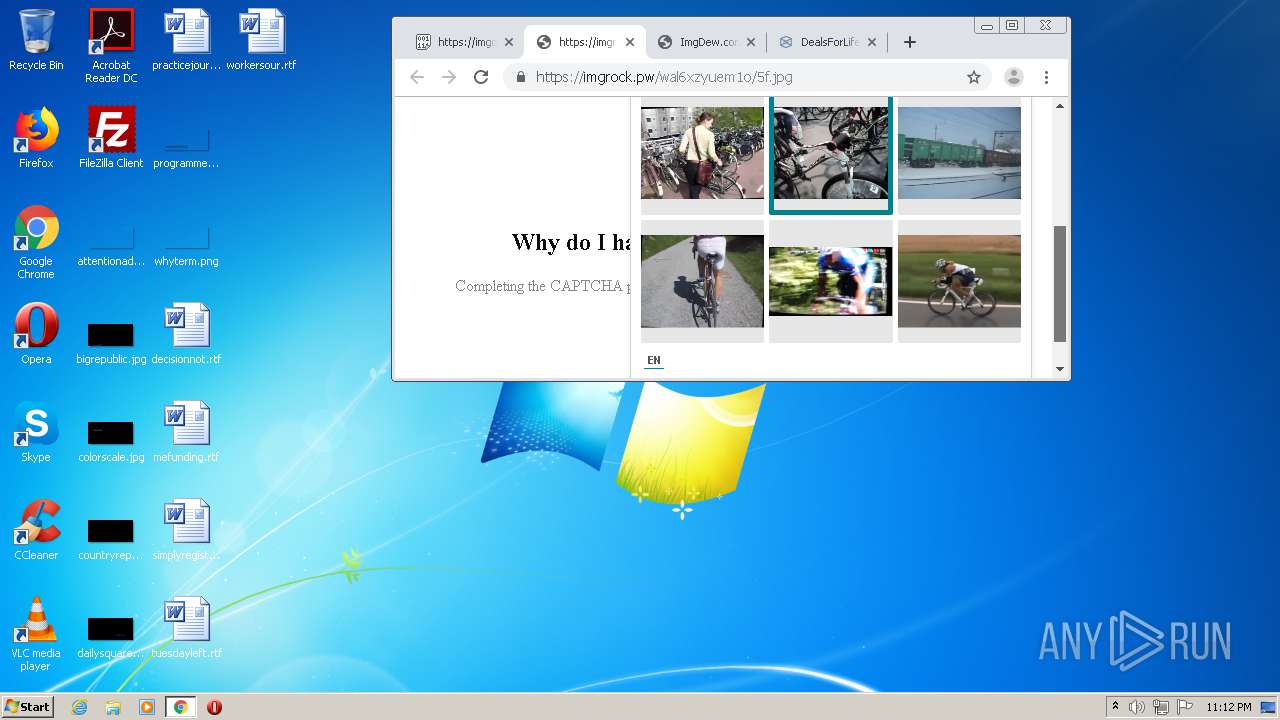
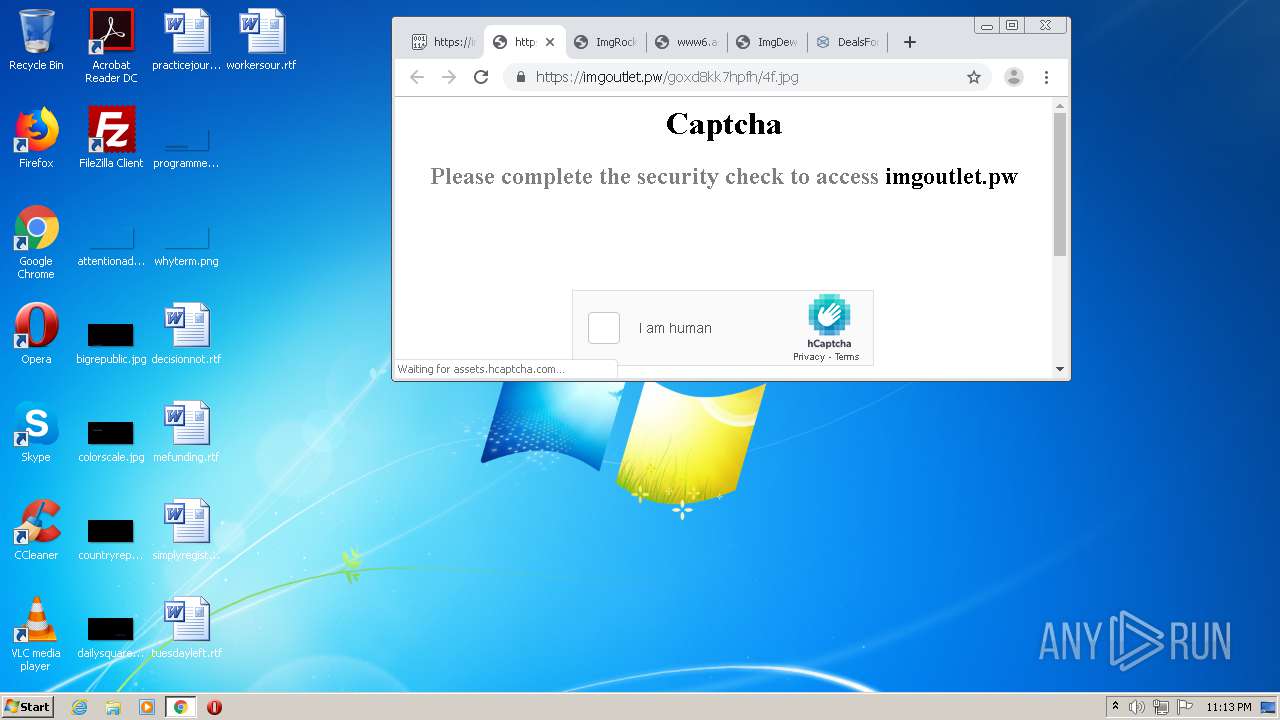
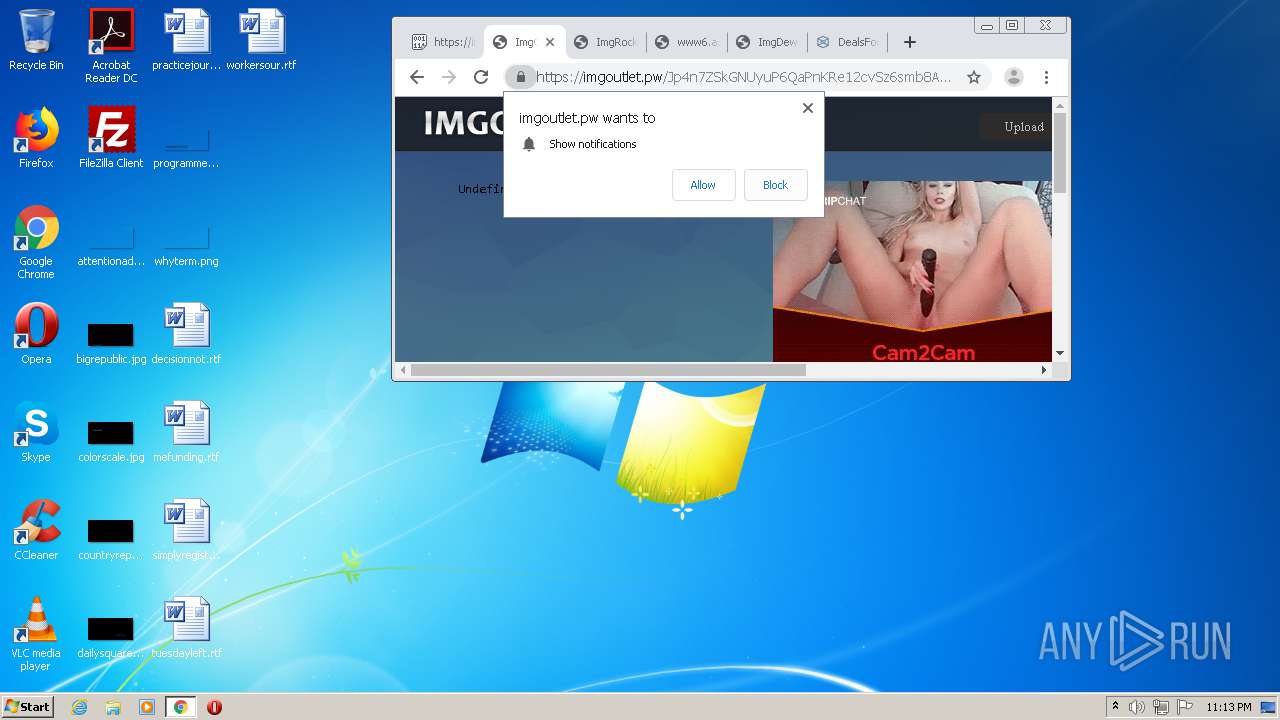
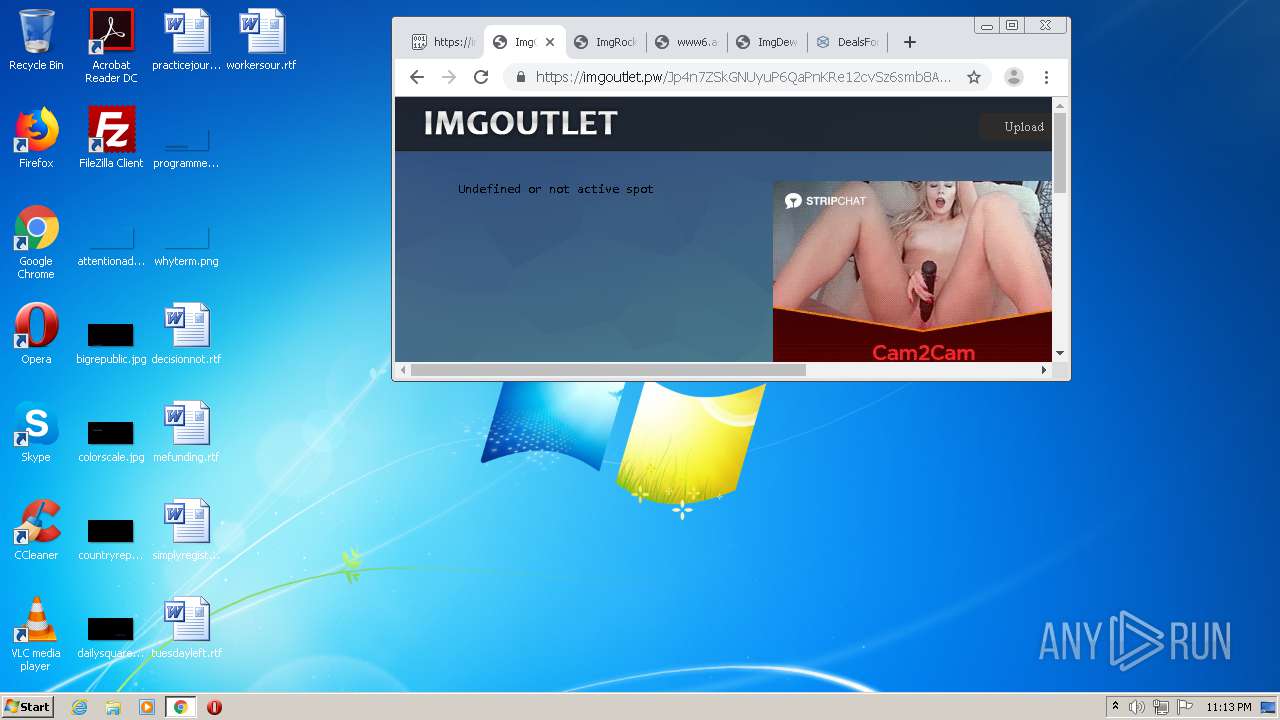
imgdew.com |
| unknown |
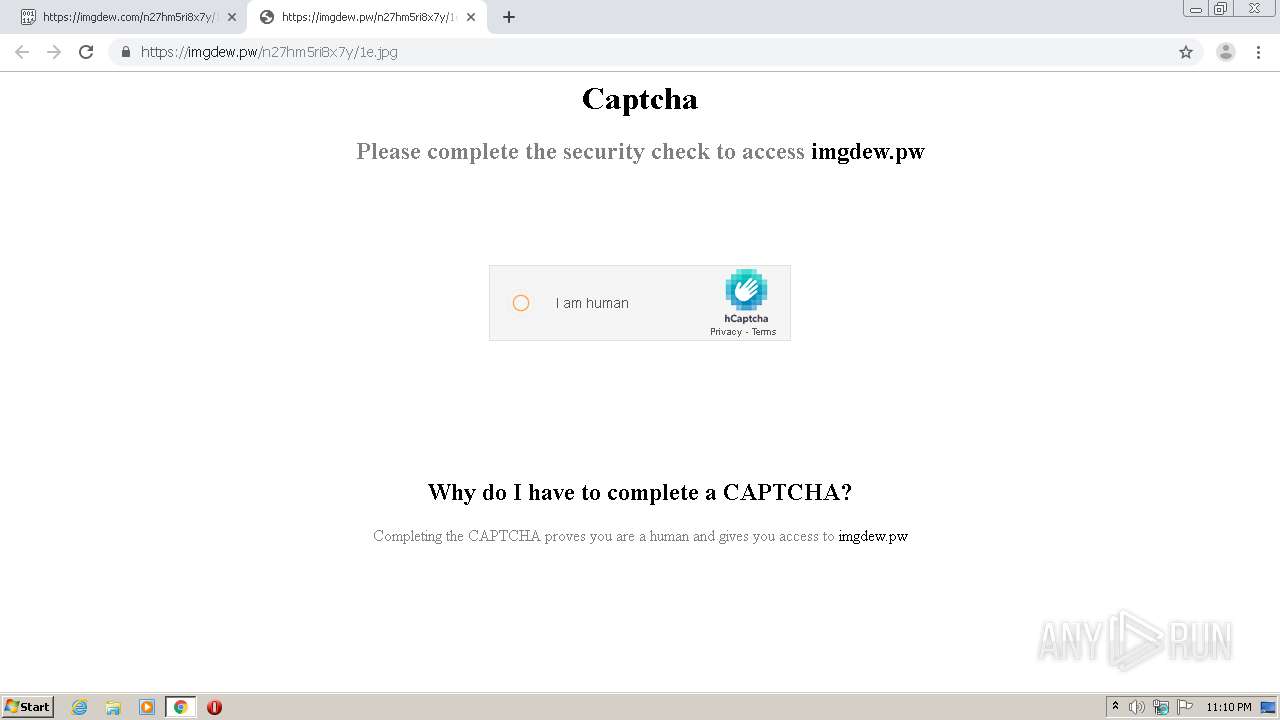
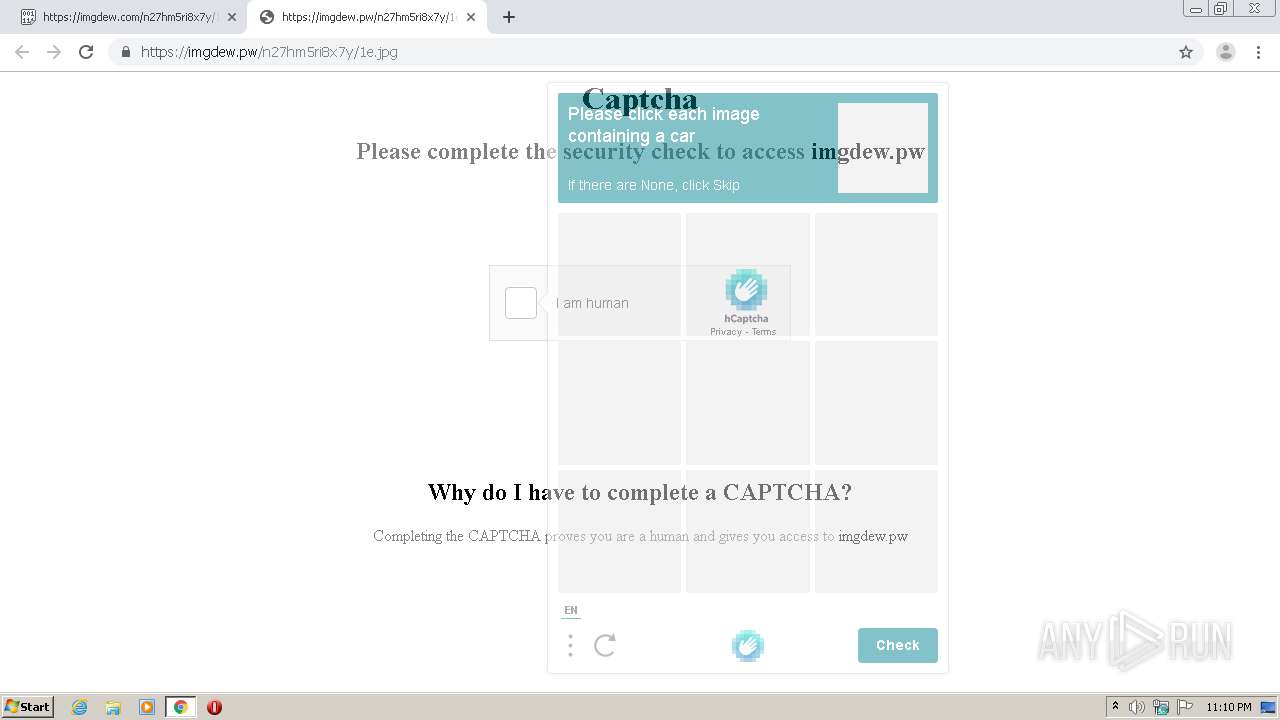
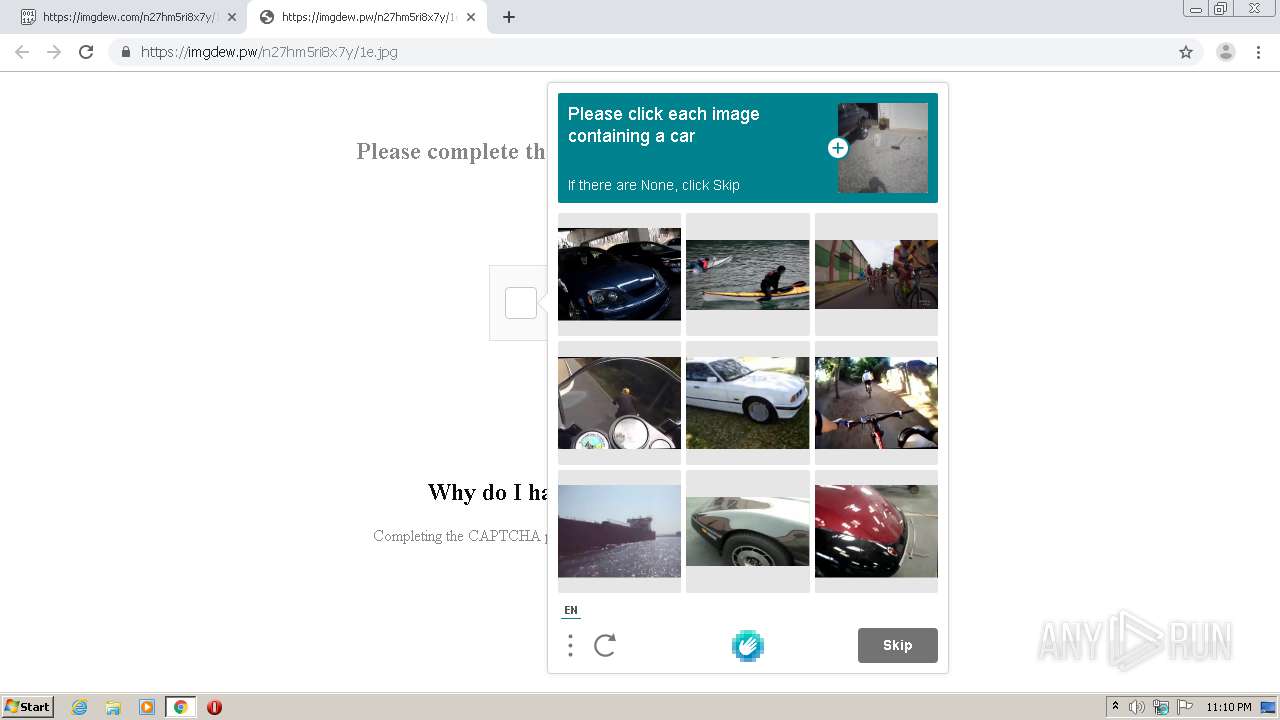
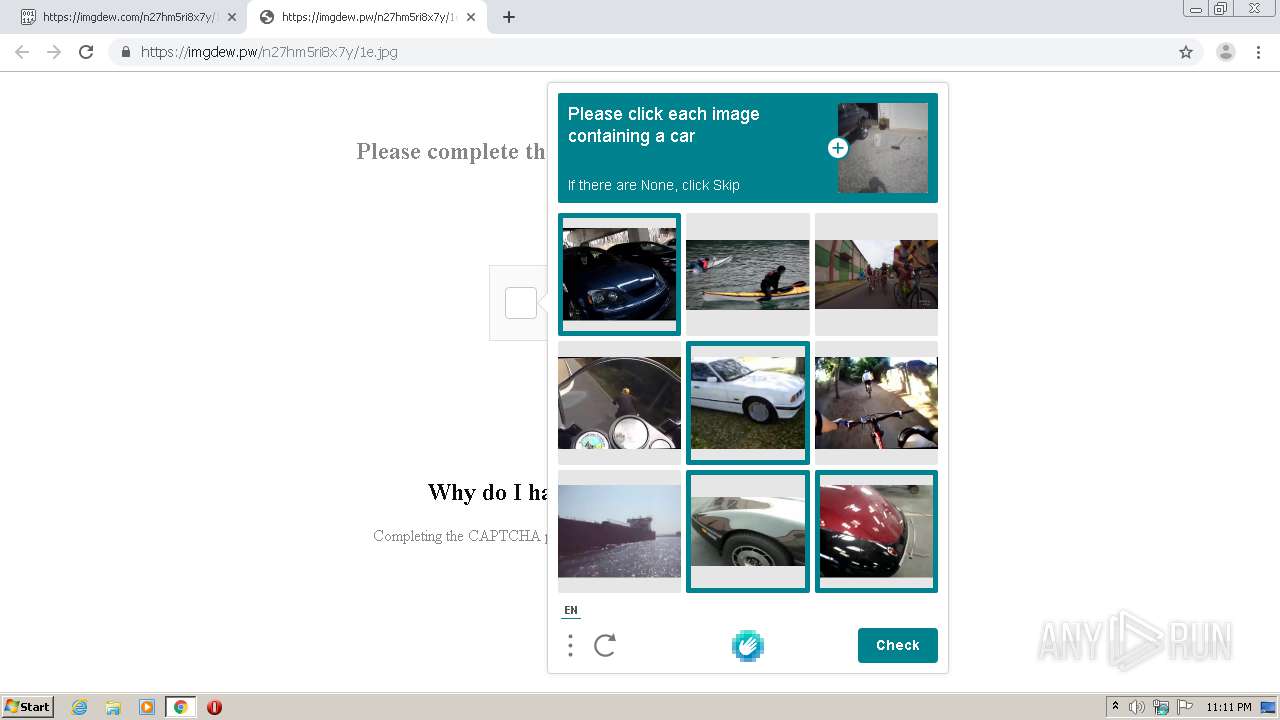
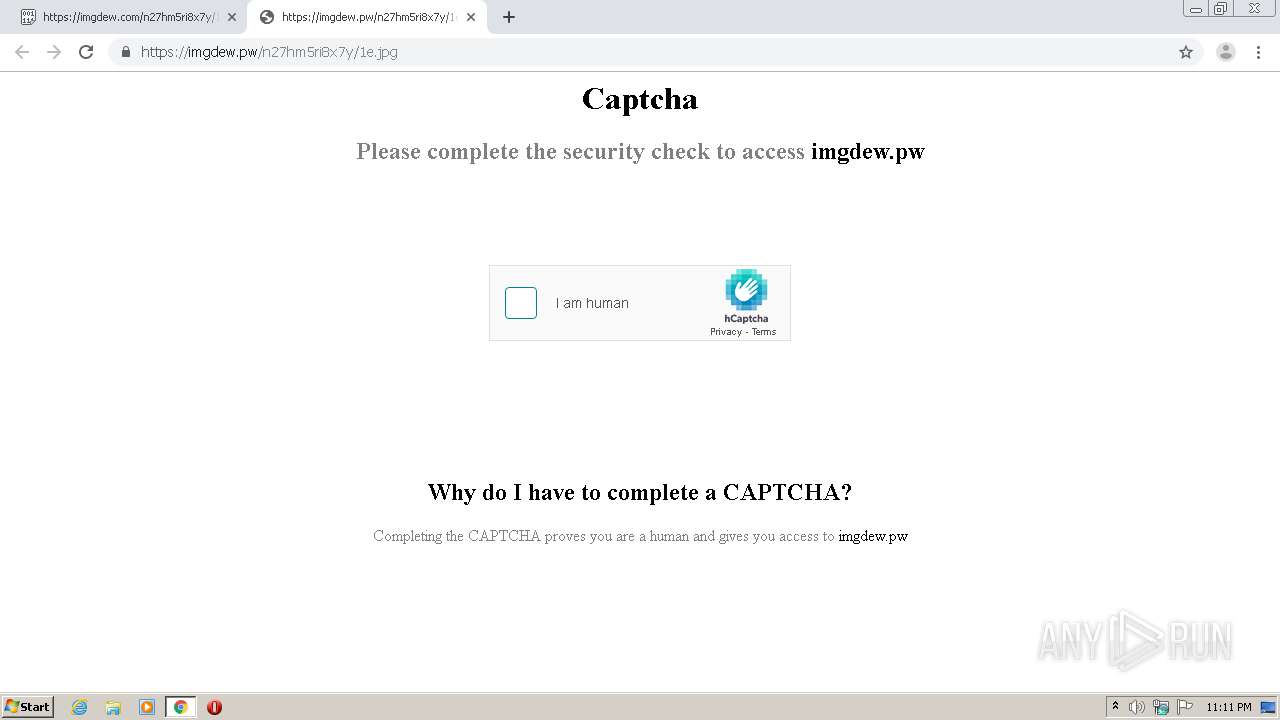
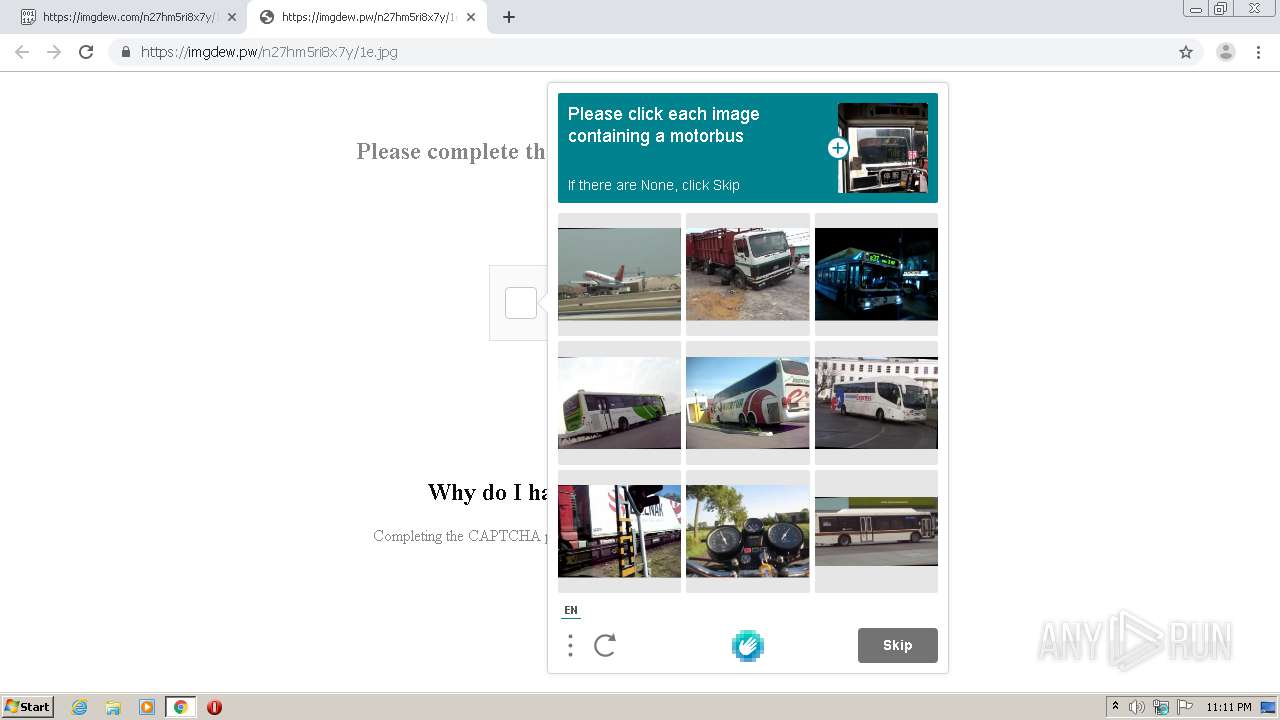
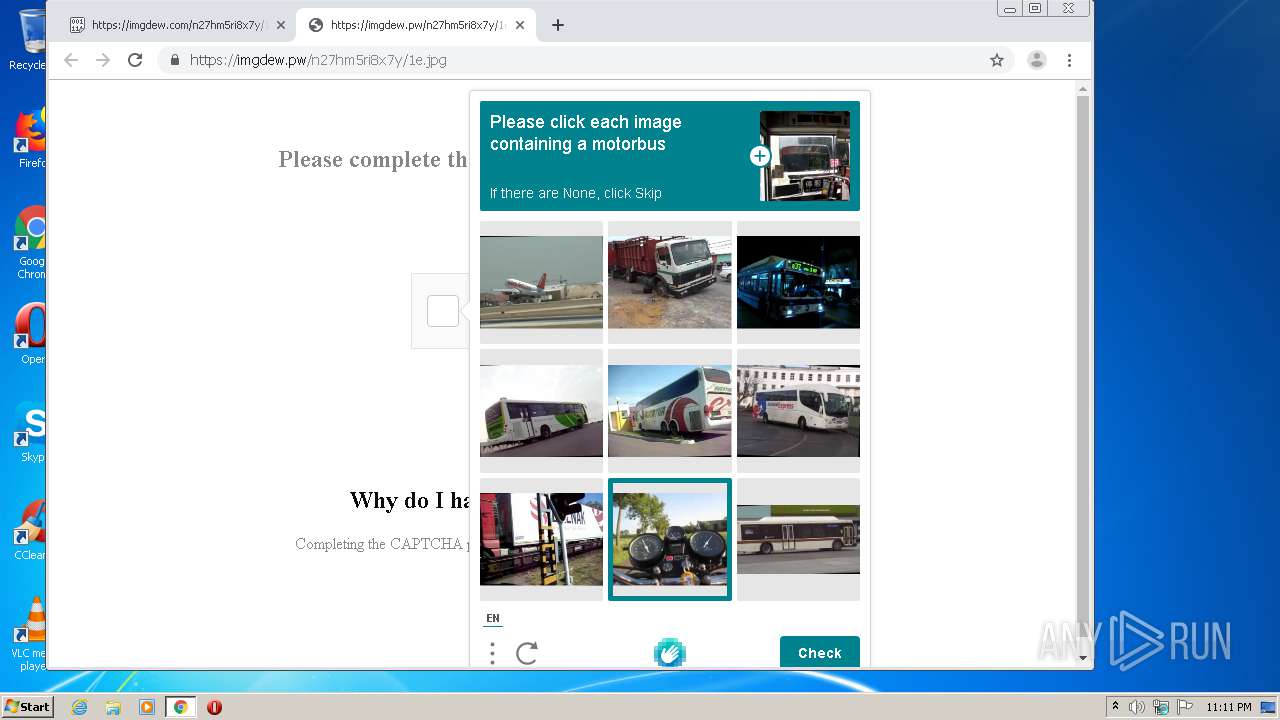
imgdew.pw |
| whitelisted |
hcaptcha.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
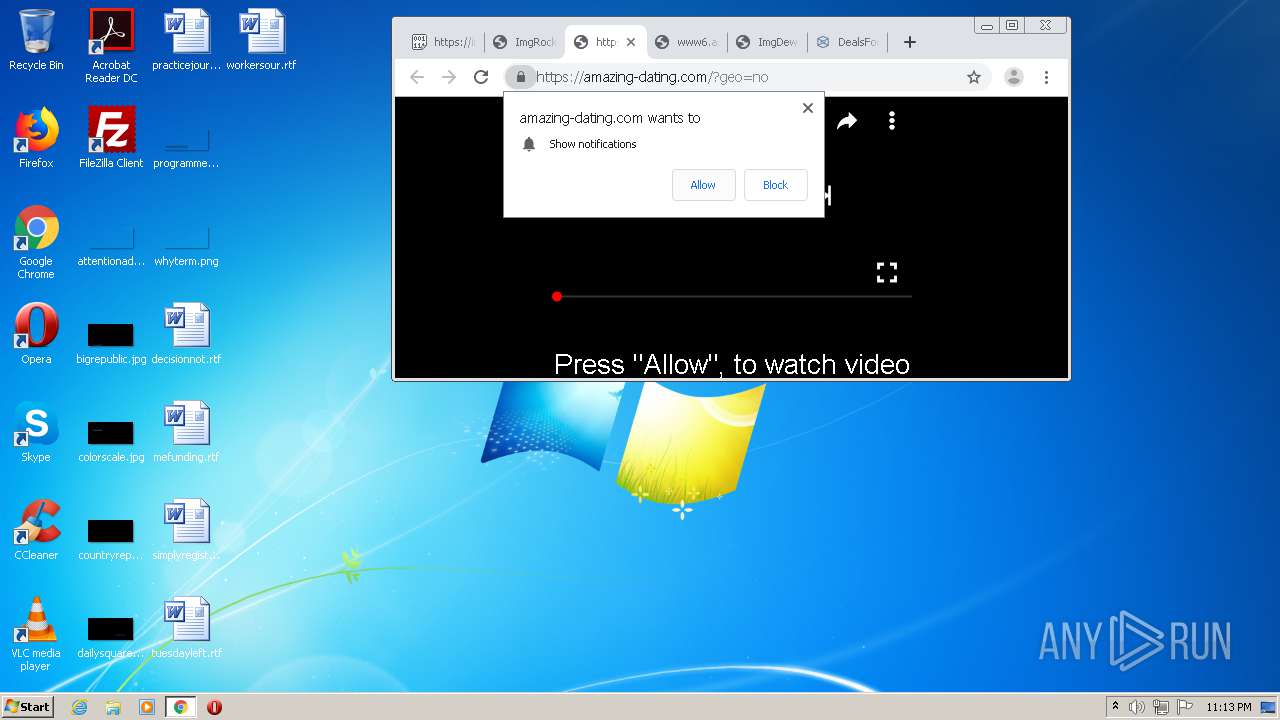
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3452 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3452 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |