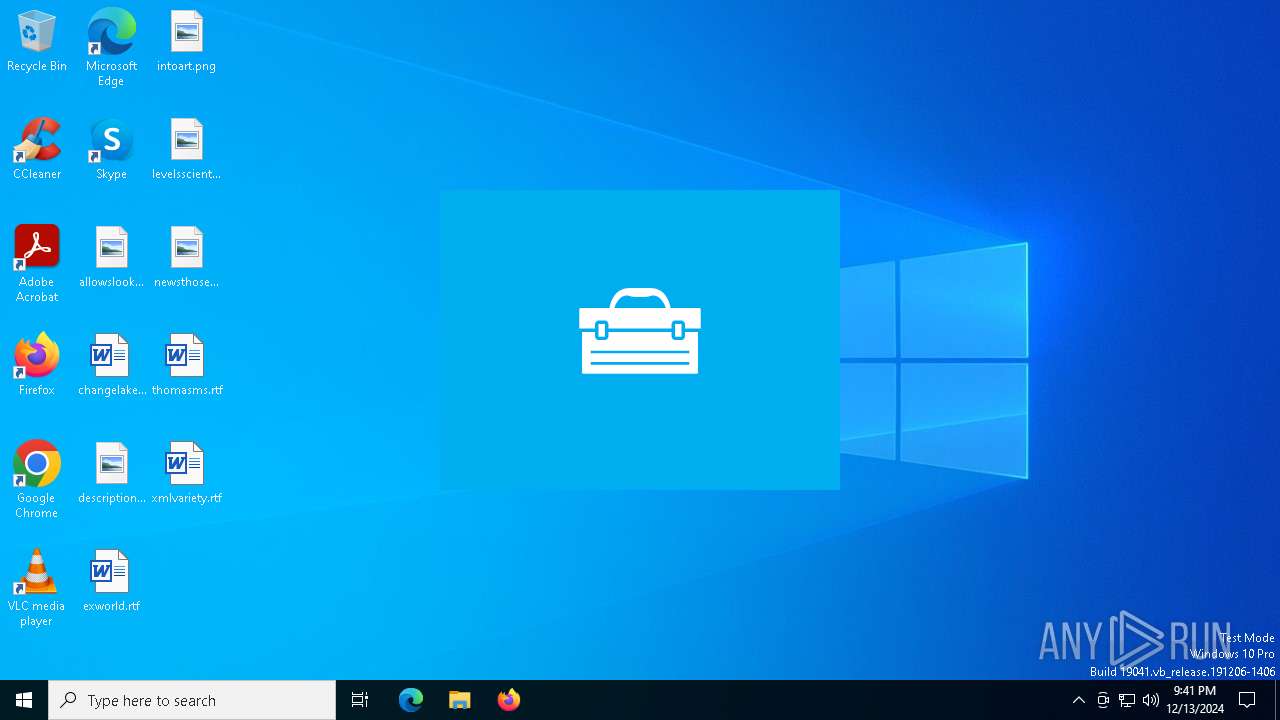
| File name: | winsdksetup (3).exe |
| Full analysis: | https://app.any.run/tasks/204f5c69-76d0-49ad-9c80-9e3f19f61f53 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 21:40:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | 93A956CB0A05A0EB38BB056F7B5864F2 |
| SHA1: | 6D1F7F638FFDEC8420B655E0A15278348AF0984B |
| SHA256: | A8E6B6CC2DCEC9FDD4C35553A4CBF288C9CE5E4761D7A2762F06A3A95F1E530D |
| SSDEEP: | 49152:uhX/IZU5KMMfpxNS0Jsta6d3yhaDzpYV/53eYeDvw10oGoTJyzRJdb4VLqgAbo4u:uhn5KMMfpxNLs53SaD9Y153ebzw1qzRM |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts a Microsoft application from unusual location
- winsdksetup (3).exe (PID: 4052)
- winsdksetup (3).exe (PID: 4628)
Executable content was dropped or overwritten
- winsdksetup (3).exe (PID: 4052)
- winsdksetup (3).exe (PID: 4628)
Process drops legitimate windows executable
- winsdksetup (3).exe (PID: 4052)
- winsdksetup (3).exe (PID: 4628)
Starts itself from another location
- winsdksetup (3).exe (PID: 4052)
The process creates files with name similar to system file names
- winsdksetup (3).exe (PID: 4628)
Searches for installed software
- winsdksetup (3).exe (PID: 4628)
INFO
Checks supported languages
- winsdksetup (3).exe (PID: 4052)
- winsdksetup (3).exe (PID: 4628)
Create files in a temporary directory
- winsdksetup (3).exe (PID: 4052)
- winsdksetup (3).exe (PID: 4628)
The sample compiled with english language support
- winsdksetup (3).exe (PID: 4052)
- winsdksetup (3).exe (PID: 4628)
Reads the machine GUID from the registry
- winsdksetup (3).exe (PID: 4628)
Creates files in the program directory
- winsdksetup (3).exe (PID: 4628)
Reads the computer name
- winsdksetup (3).exe (PID: 4628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:19 20:27:03+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 323072 |
| InitializedDataSize: | 409088 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31c20 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.1.26100.1742 |
| ProductVersionNumber: | 10.1.26100.1742 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
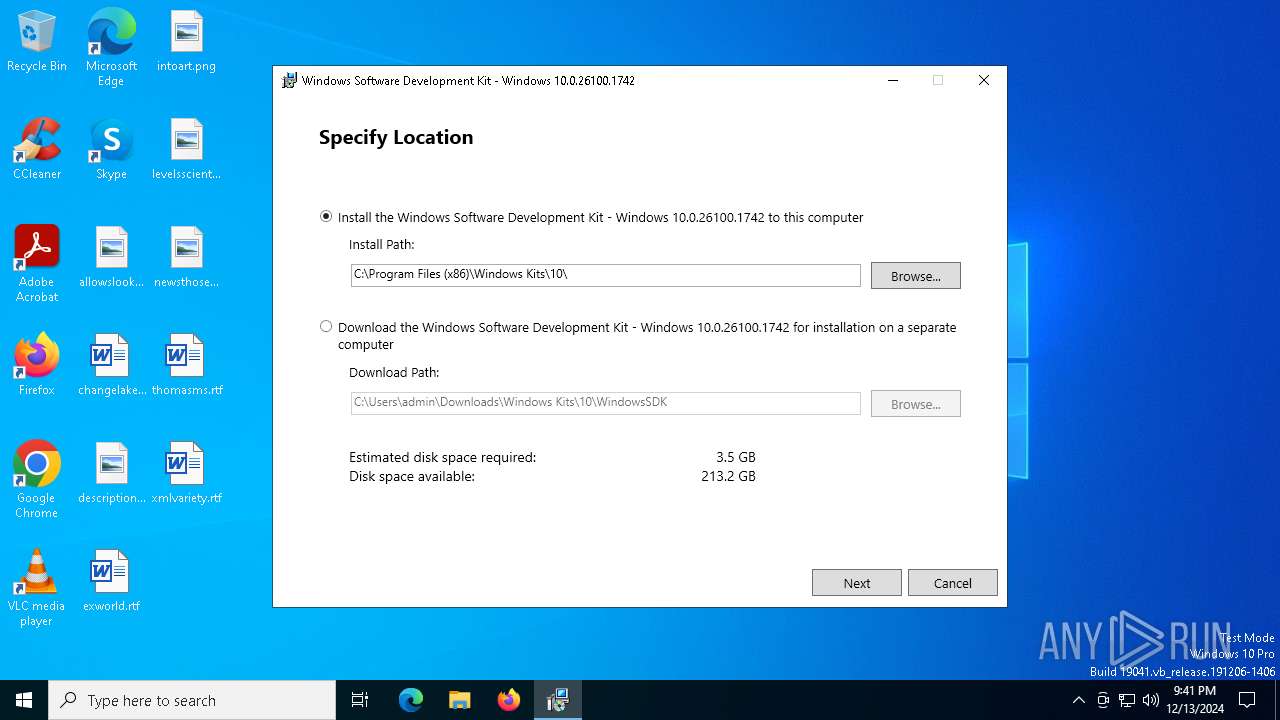
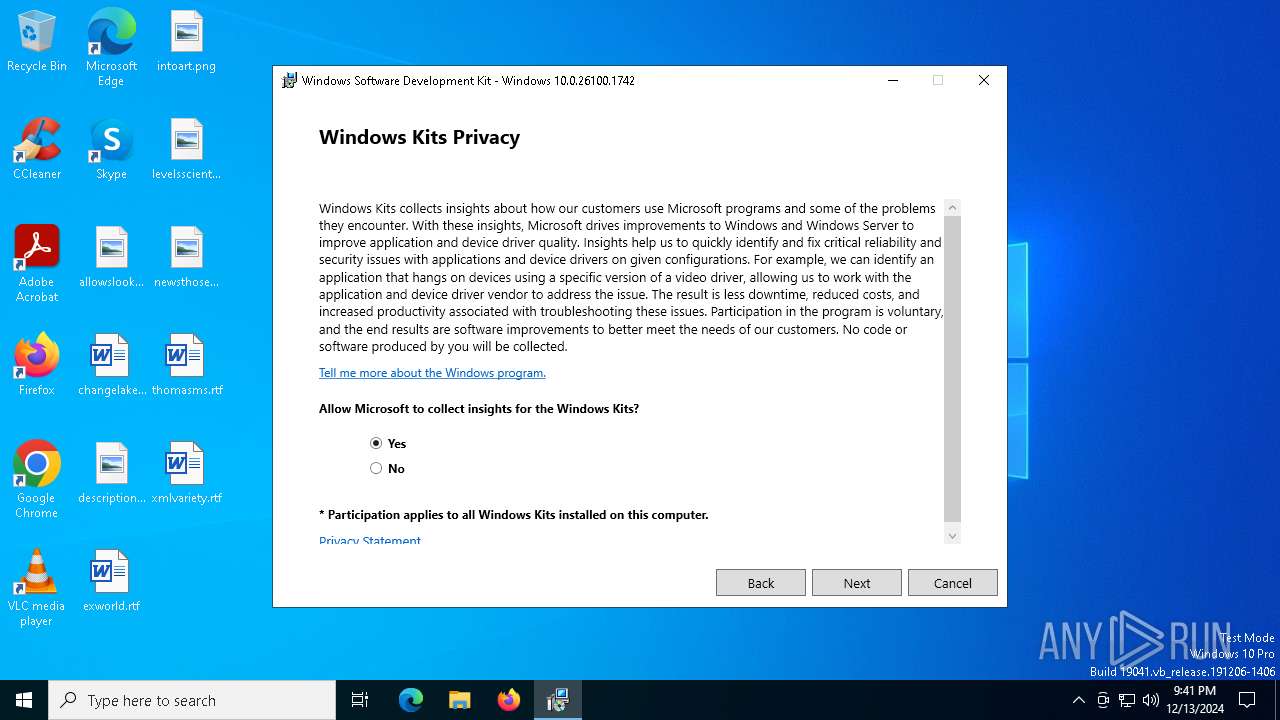
| FileDescription: | Windows Software Development Kit - Windows 10.0.26100.1742 |
| FileVersion: | 10.1.26100.1742 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | winsdksetup.exe |
| ProductName: | Windows Software Development Kit - Windows 10.0.26100.1742 |
| ProductVersion: | 10.1.26100.1742 |
Total processes
128
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4052 | "C:\Users\admin\AppData\Local\Temp\winsdksetup (3).exe" | C:\Users\admin\AppData\Local\Temp\winsdksetup (3).exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Software Development Kit - Windows 10.0.26100.1742 Version: 10.1.26100.1742 Modules
| |||||||||||||||
| 4628 | "C:\Users\admin\AppData\Local\Temp\{2C4E5F55-28B7-4BF3-9425-671741680C99}\.cr\winsdksetup (3).exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\winsdksetup (3).exe" -burn.filehandle.attached=752 -burn.filehandle.self=580 | C:\Users\admin\AppData\Local\Temp\{2C4E5F55-28B7-4BF3-9425-671741680C99}\.cr\winsdksetup (3).exe | winsdksetup (3).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Software Development Kit - Windows 10.0.26100.1742 Version: 10.1.26100.1742 Modules
| |||||||||||||||
Total events
688
Read events
688
Write events
0
Delete events
0
Modification events
Executable files
8
Suspicious files
0
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4628 | winsdksetup (3).exe | C:\Users\admin\AppData\Local\Temp\{373AA998-1A21-4096-A221-9C87257A617A}\.ba\Microsoft.Bootstrapper.dll | executable | |
MD5:F4DEAD1DD23EE0A6443CDDA932DF8D82 | SHA256:21E65BE8E066BC929D348A55E92B69AF1D394F448265691B7A4A87D0C971CD67 | |||
| 4628 | winsdksetup (3).exe | C:\Users\admin\AppData\Local\Temp\{373AA998-1A21-4096-A221-9C87257A617A}\.ba\license.rtf | text | |
MD5:1A940E6727738BA3C966BB15370541C8 | SHA256:0F4A26AC9DC50066F8A1BFEAAF3F092D1B9E4791DF5487B9F3C31E7C3DC4D7F5 | |||
| 4628 | winsdksetup (3).exe | C:\Users\admin\AppData\Local\Temp\{373AA998-1A21-4096-A221-9C87257A617A}\.ba\BootstrapperCore.dll | executable | |
MD5:312AC5D4DED277394F0C59C944B1E2CD | SHA256:D2E9E09B96EE9A23DBFD993EC7A1F1FC3936171EDE97650993E626C08DB1DC8D | |||
| 4628 | winsdksetup (3).exe | C:\Users\admin\AppData\Local\Temp\{373AA998-1A21-4096-A221-9C87257A617A}\.ba\mbahost.dll | executable | |
MD5:47C2DD7E9F97A0453ED2F8656B2BC939 | SHA256:30A94CE6FCD03F1320396EC2B92D4EF661B60BFADB5AC428E4B075AE593B4057 | |||
| 4628 | winsdksetup (3).exe | C:\Users\admin\AppData\Local\Temp\{373AA998-1A21-4096-A221-9C87257A617A}\.ba\BootstrapperCore.config | xml | |
MD5:57AA0F7B5F6F076454F075A88BCC0CC9 | SHA256:361079F9F118E11EA3F05D75FD3874664C94334F453177242C8E32F0881A3527 | |||
| 4628 | winsdksetup (3).exe | C:\Users\admin\AppData\Local\Temp\{373AA998-1A21-4096-A221-9C87257A617A}\.ba\NetfxLicense.rtf | text | |
MD5:EC356D9BB20437848228F5C480FD111C | SHA256:48AE54DD5A7DCA60DE835C384648433099C702BAB71EB3339D88B96424DB500E | |||
| 4628 | winsdksetup (3).exe | C:\Users\admin\AppData\Local\Temp\{373AA998-1A21-4096-A221-9C87257A617A}\.ba\Microsoft.Diagnostics.Tracing.EventSource.dll | executable | |
MD5:AD9250C9725E55E11729256336ACCD56 | SHA256:F9836C19B55583433141CBC1AE4542E65919ABB0753E806B29740A732526B685 | |||
| 4052 | winsdksetup (3).exe | C:\Users\admin\AppData\Local\Temp\{2C4E5F55-28B7-4BF3-9425-671741680C99}\.cr\winsdksetup (3).exe | executable | |
MD5:93A956CB0A05A0EB38BB056F7B5864F2 | SHA256:A8E6B6CC2DCEC9FDD4C35553A4CBF288C9CE5E4761D7A2762F06A3A95F1E530D | |||
| 4628 | winsdksetup (3).exe | C:\Users\admin\AppData\Local\Temp\{373AA998-1A21-4096-A221-9C87257A617A}\.ba\mbapreq.png | image | |
MD5:A356956FD269567B8F4612A33802637B | SHA256:A401A225ADDAF89110B4B0F6E8CF94779E7C0640BCDD2D670FFCF05AAB0DAD03 | |||
| 4628 | winsdksetup (3).exe | C:\Users\admin\AppData\Local\Temp\{373AA998-1A21-4096-A221-9C87257A617A}\.ba\mbapreq.thm | xml | |
MD5:9F63155A23573D3E522CD28E982658B1 | SHA256:DF05AC2A44327303B718B9FC05D306047EC387EE551664B8EB9B3E48DF24B5F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
33
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2220 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6984 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6984 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
3040 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |