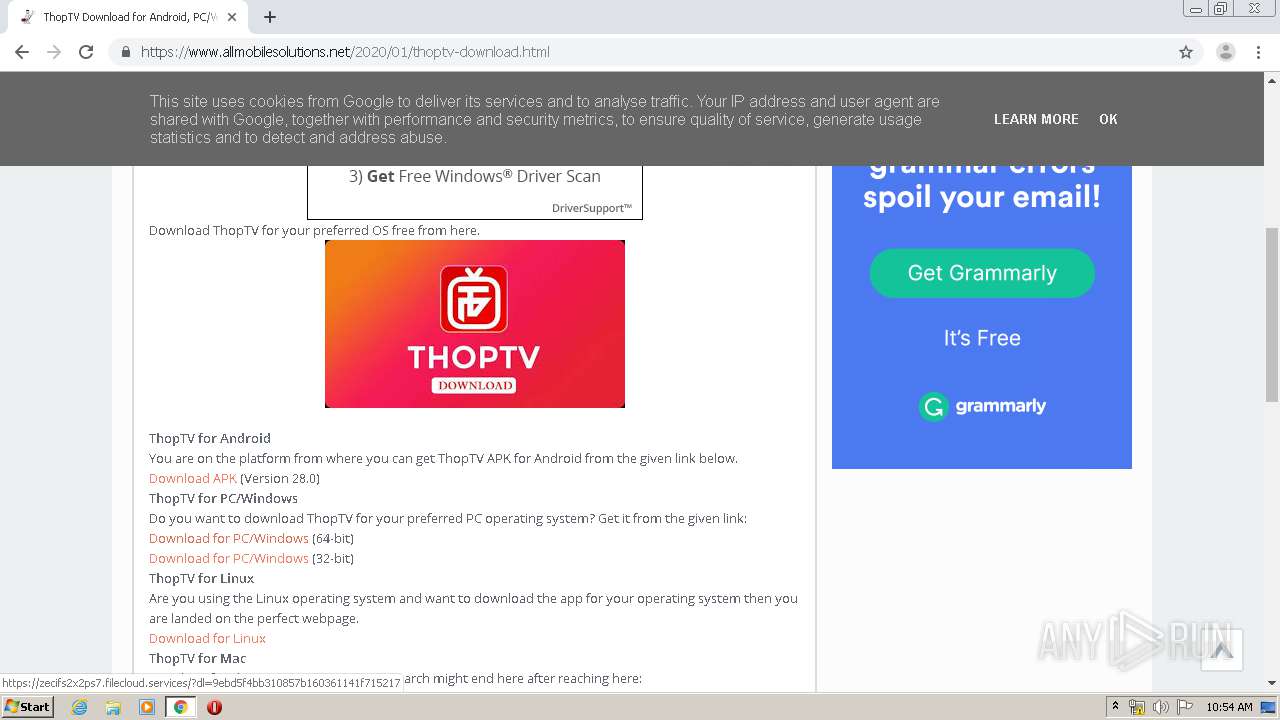
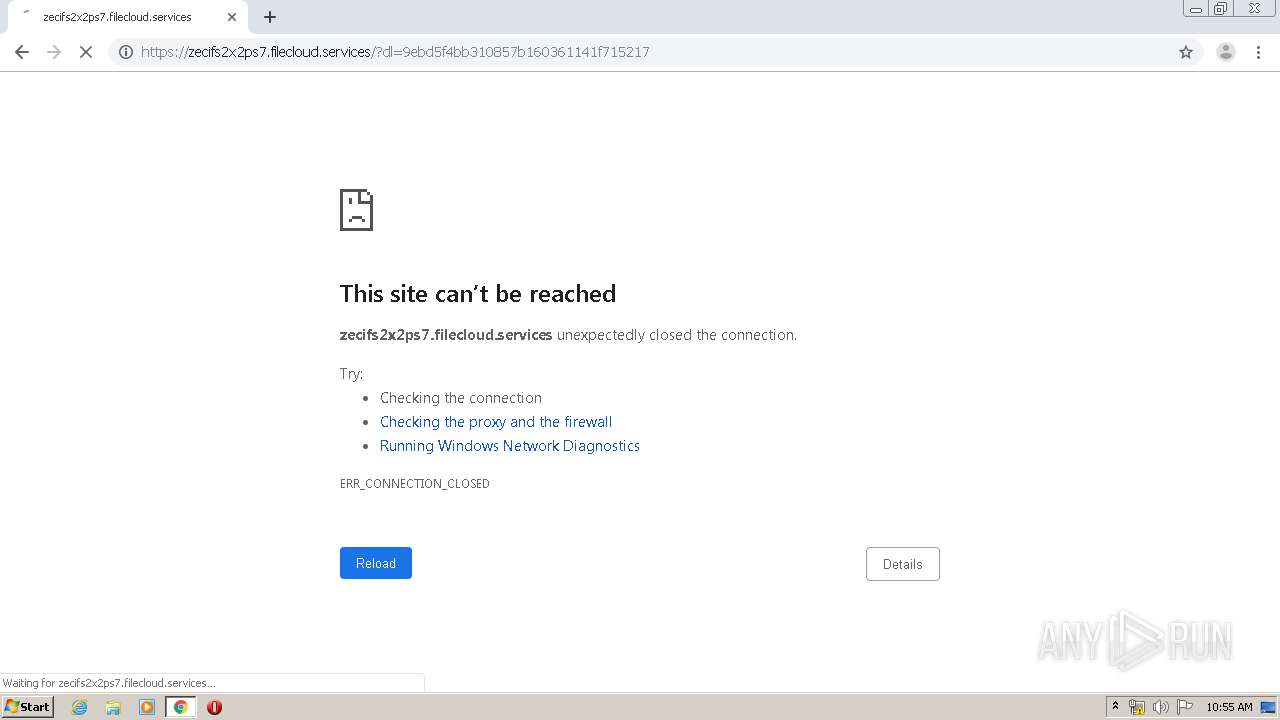
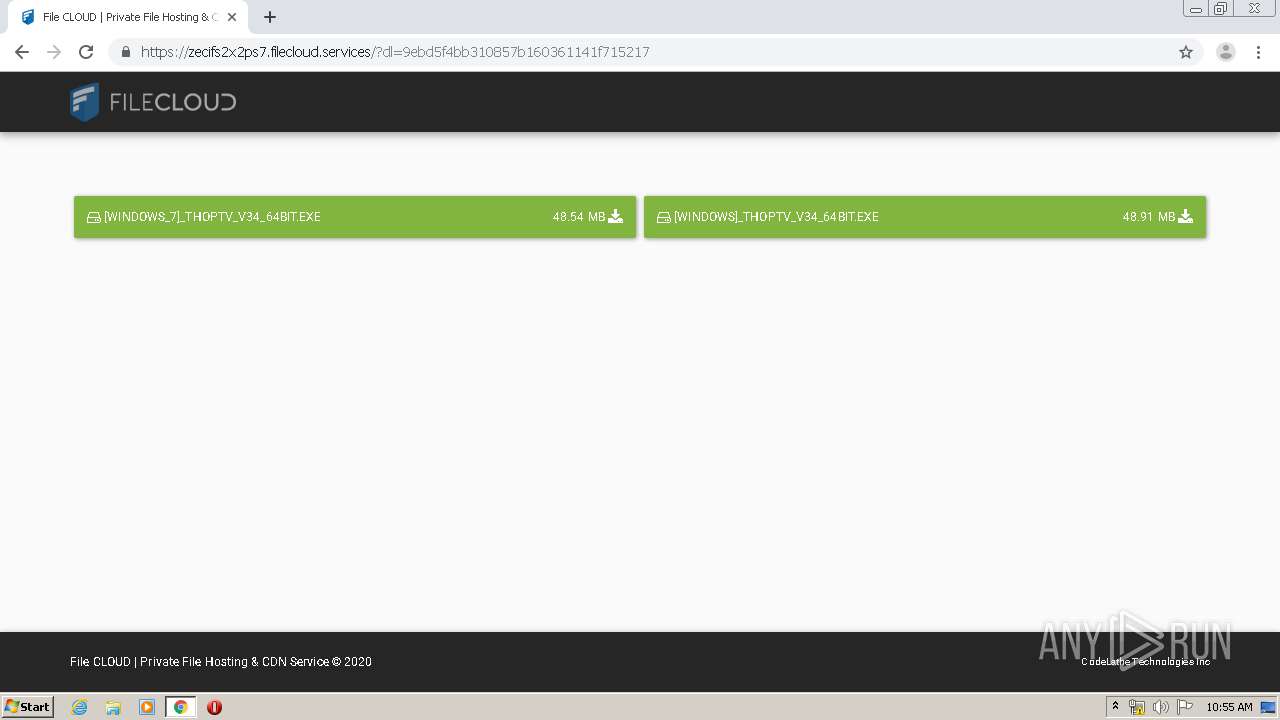
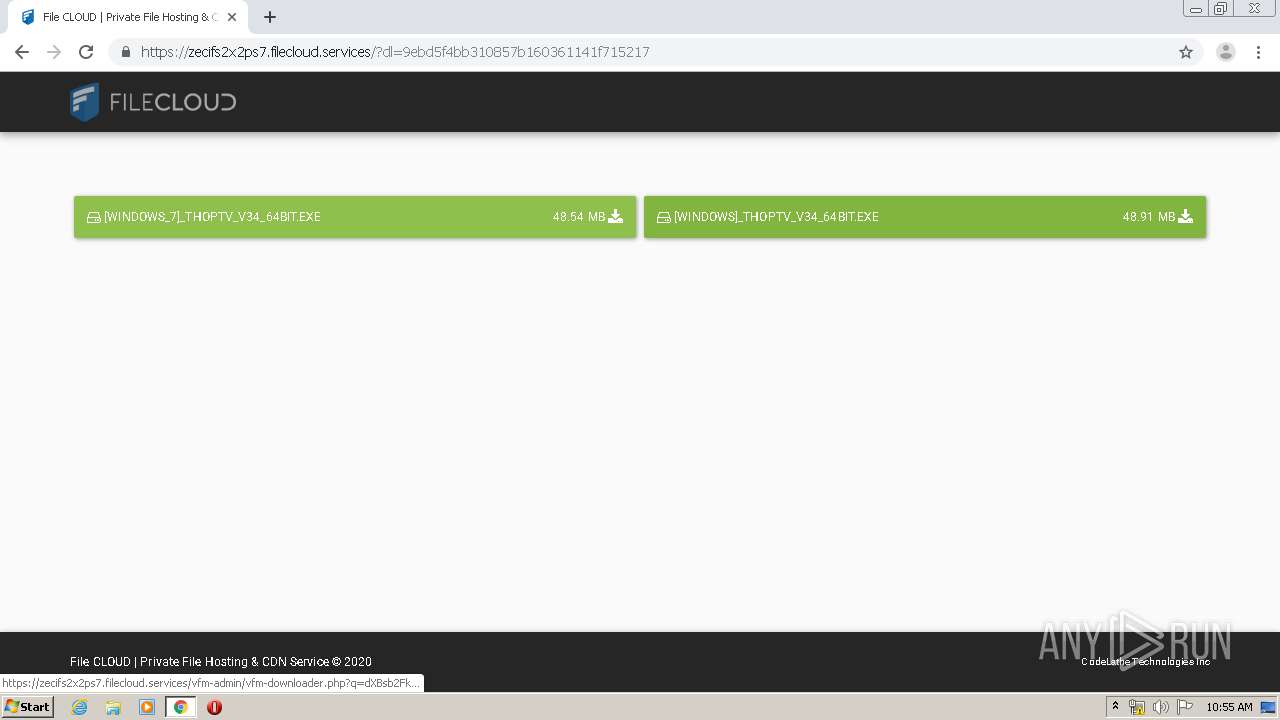
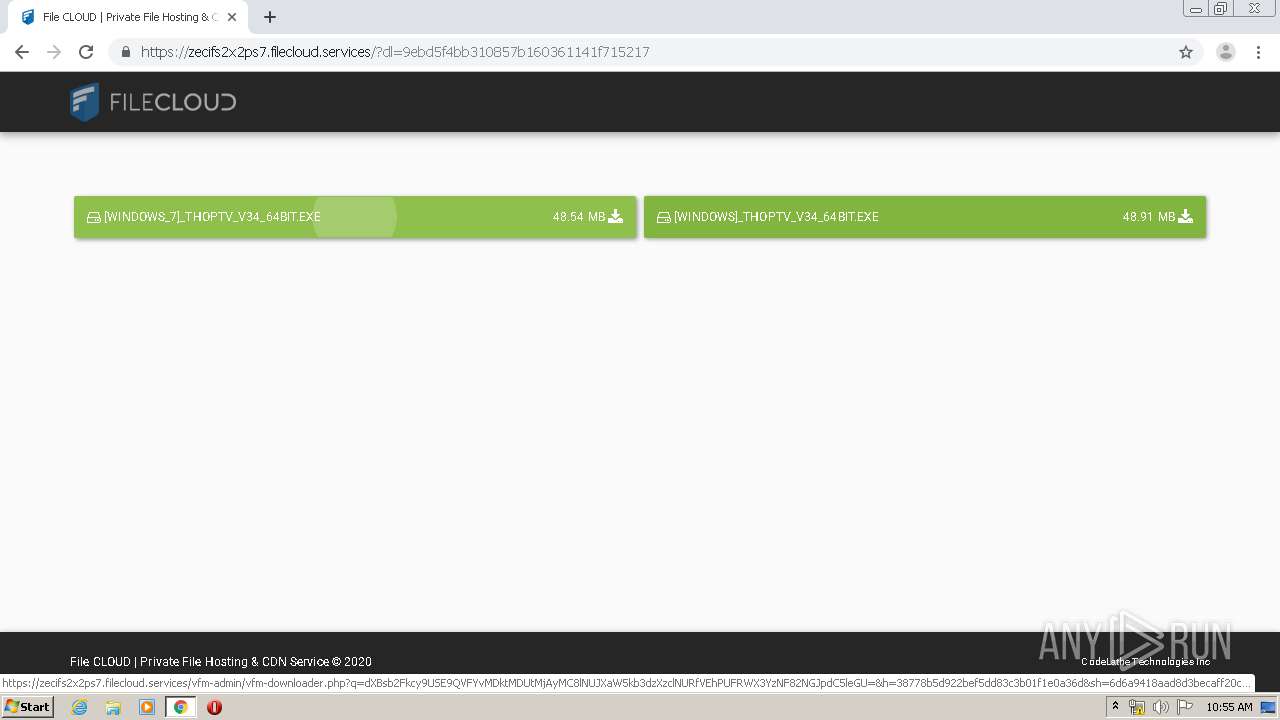
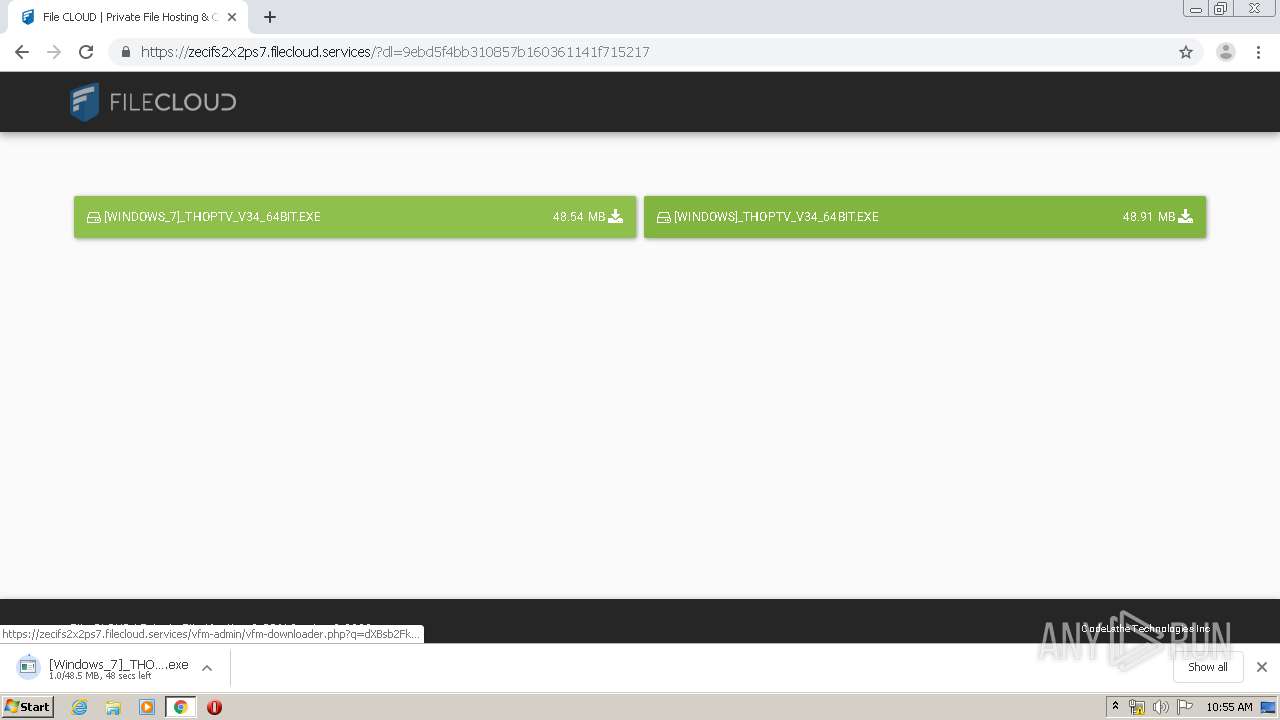
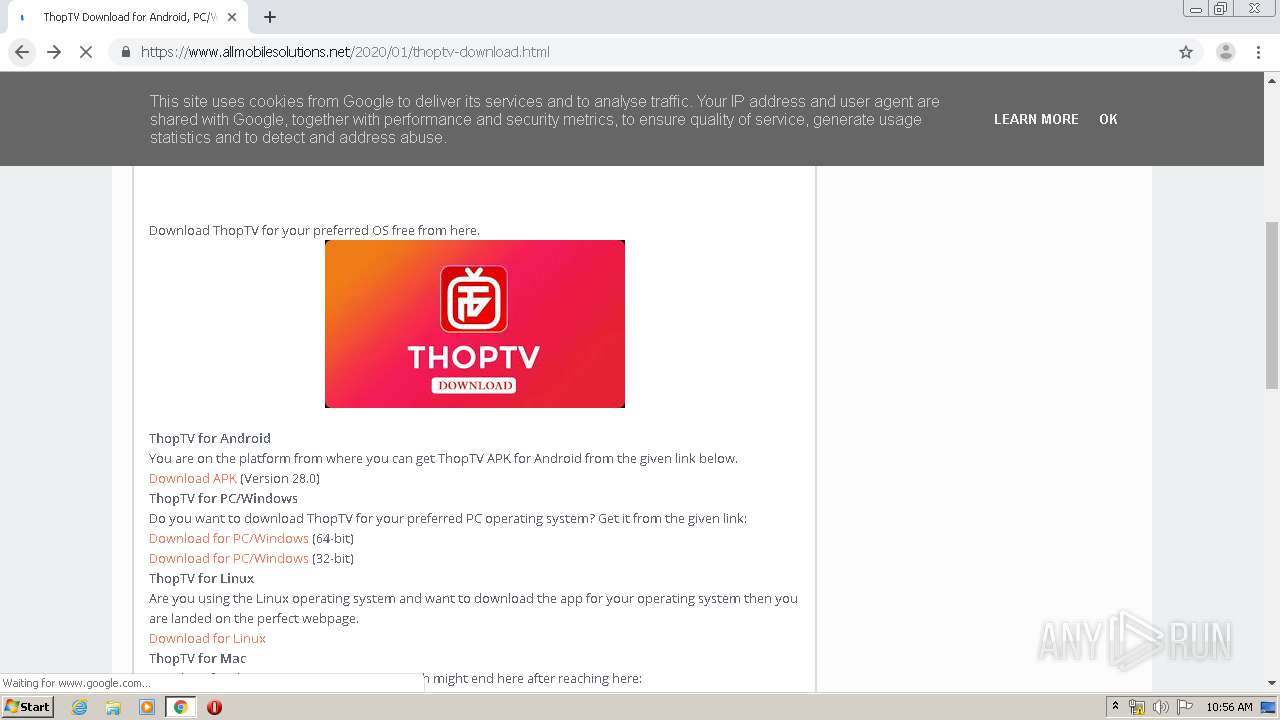
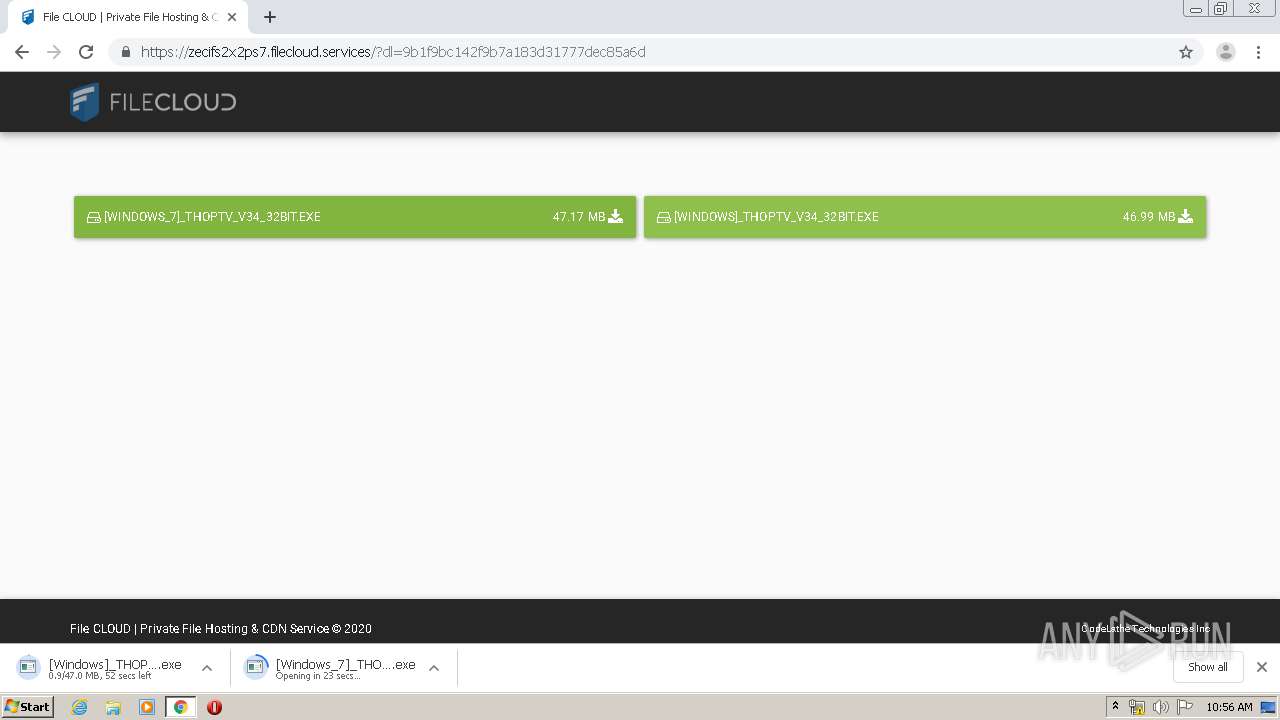
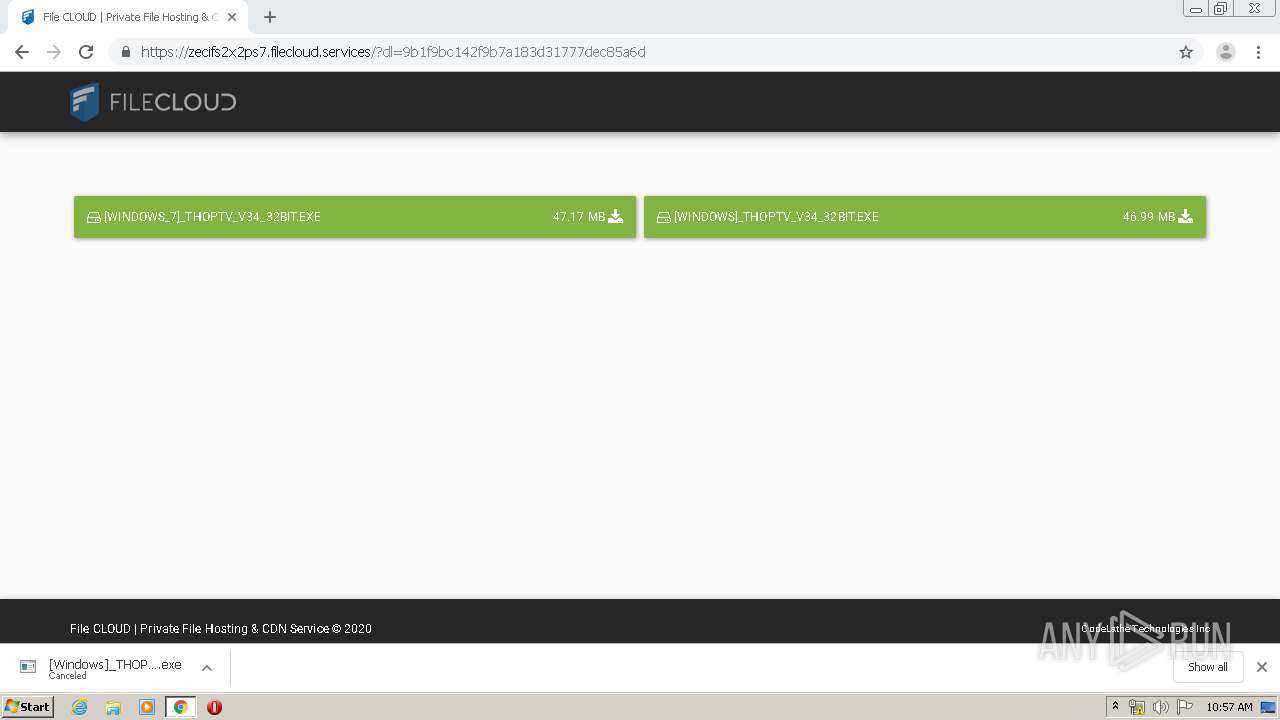
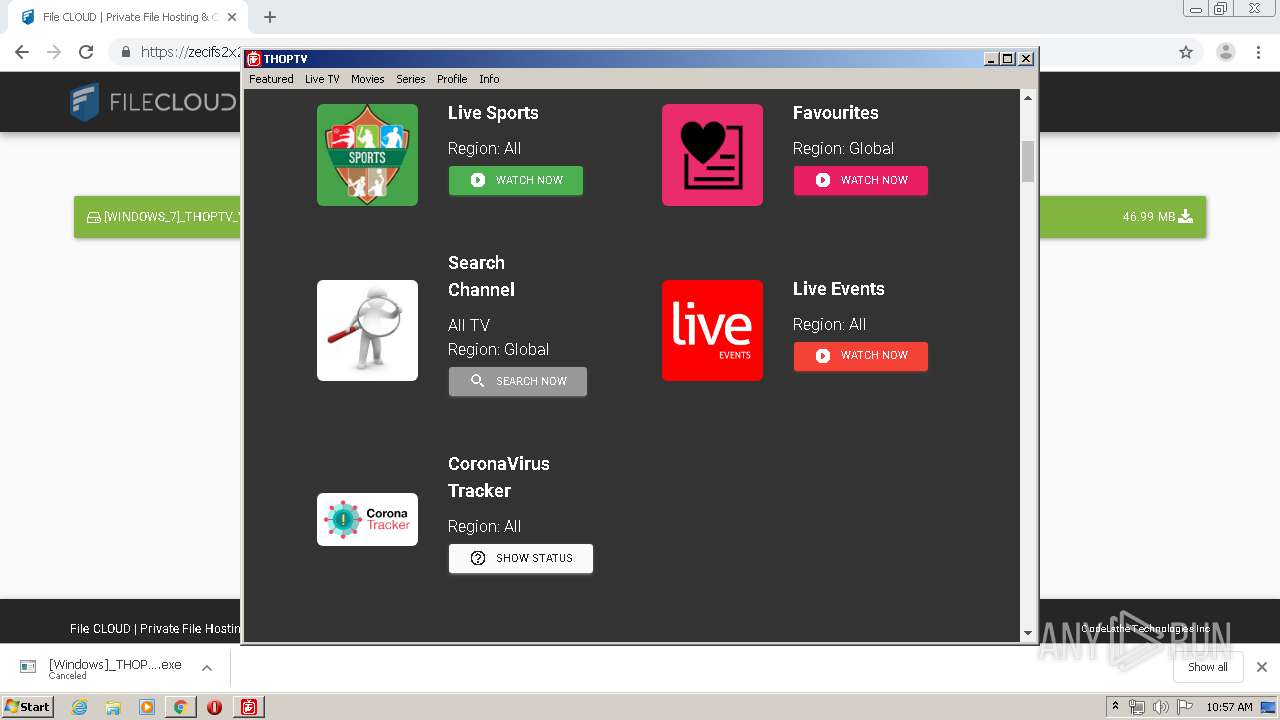
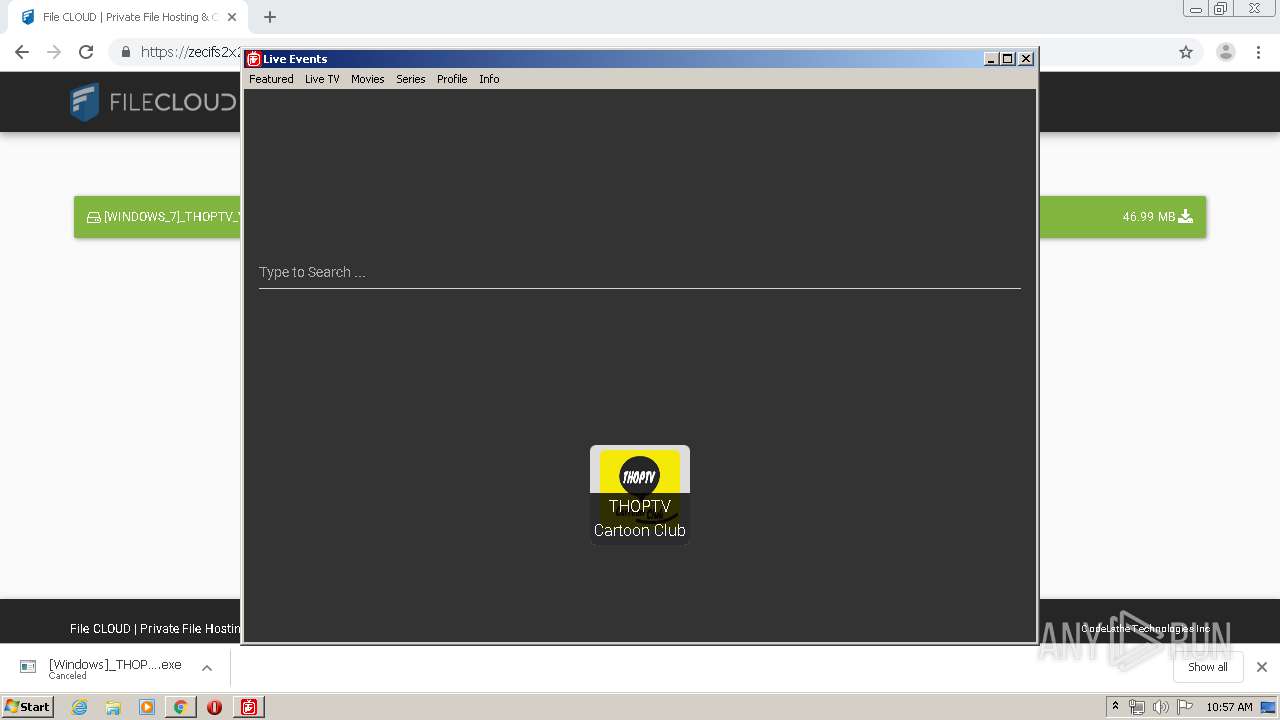
| URL: | https://thoptv.download |
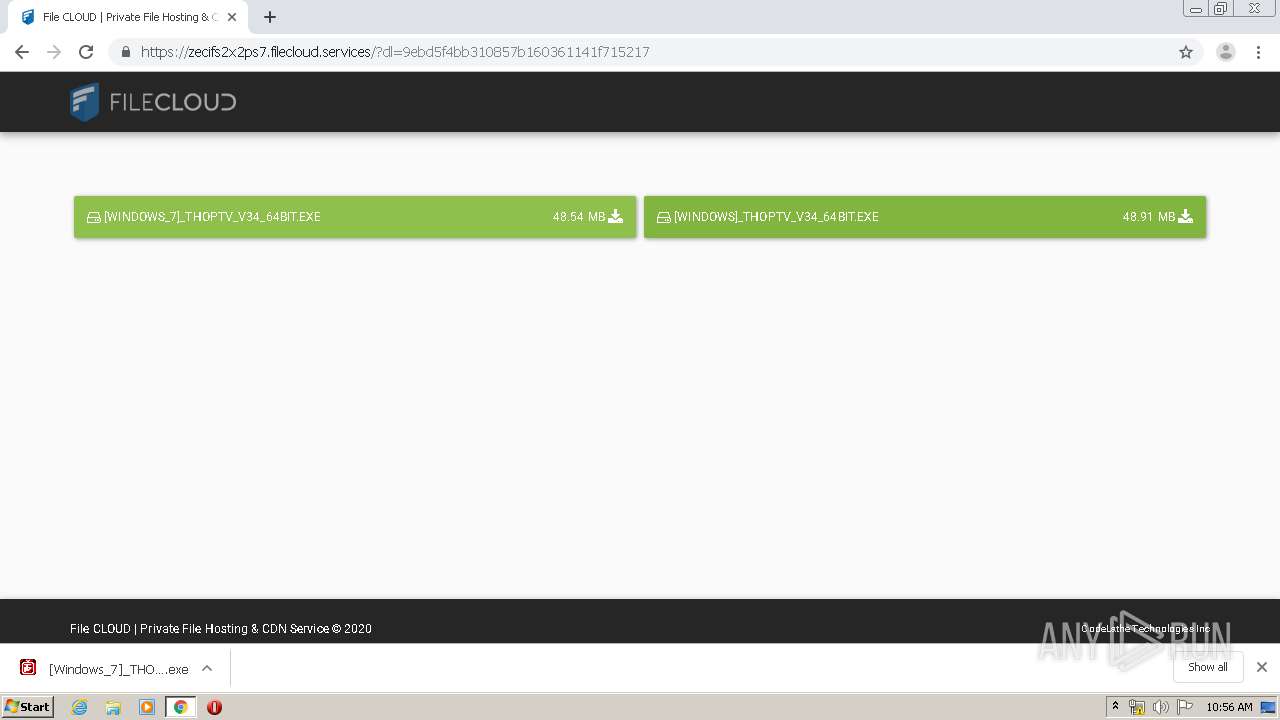
| Full analysis: | https://app.any.run/tasks/bd29fb32-5191-42e6-b72e-4ee44c69c7df |
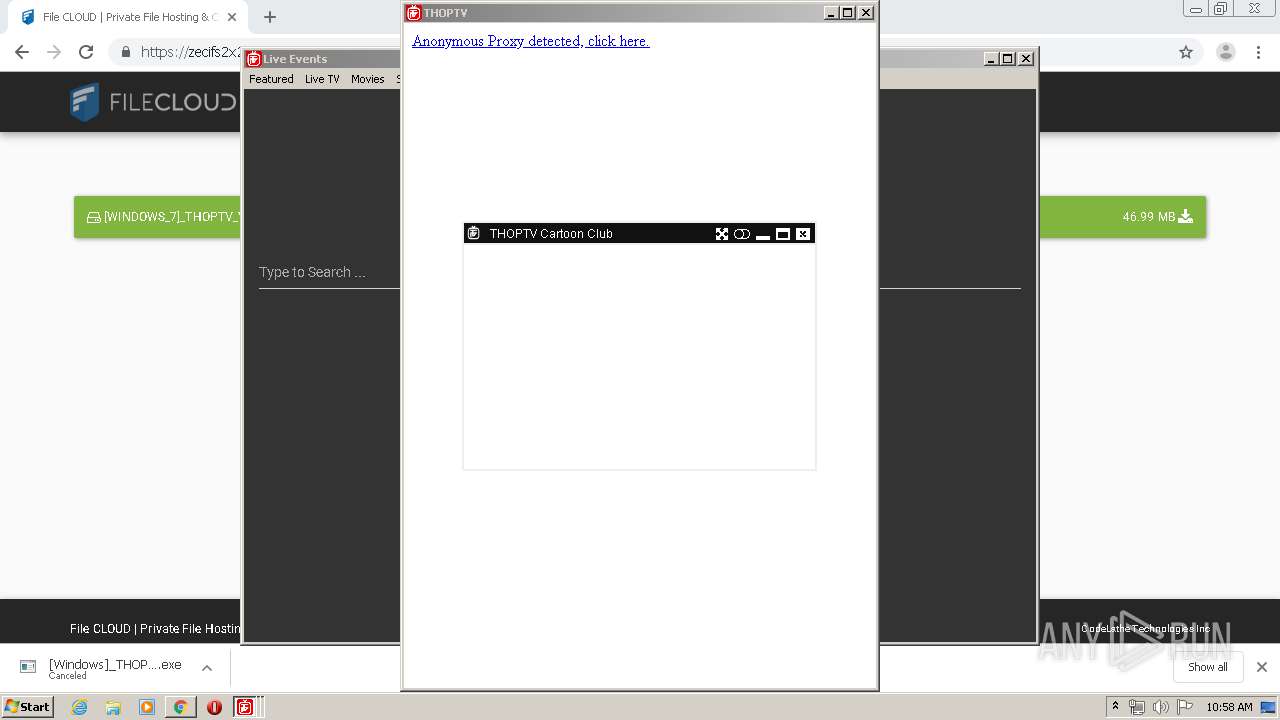
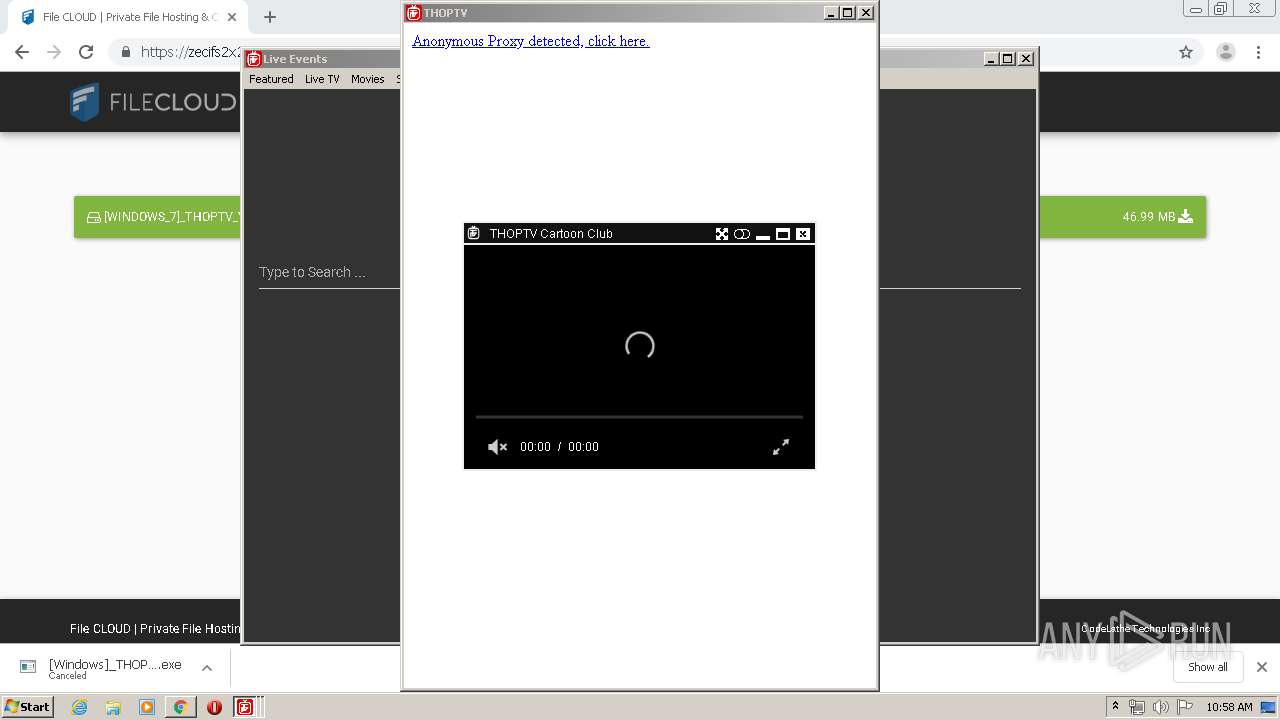
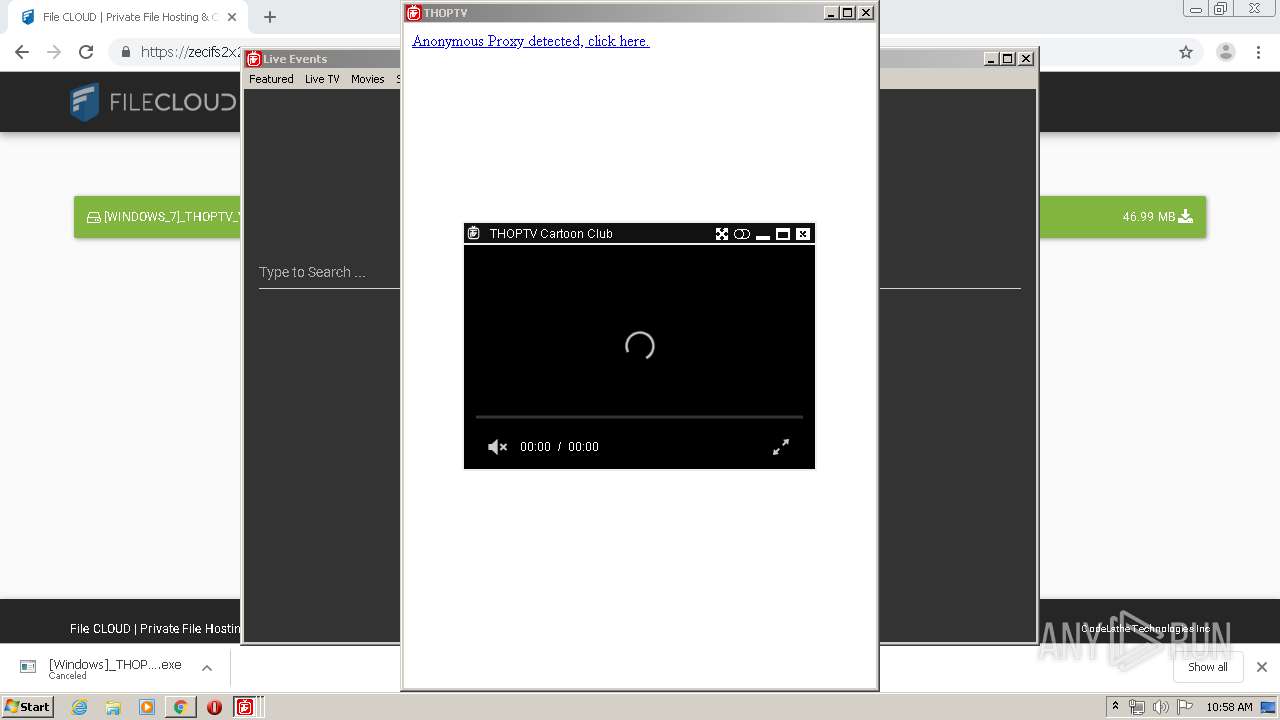
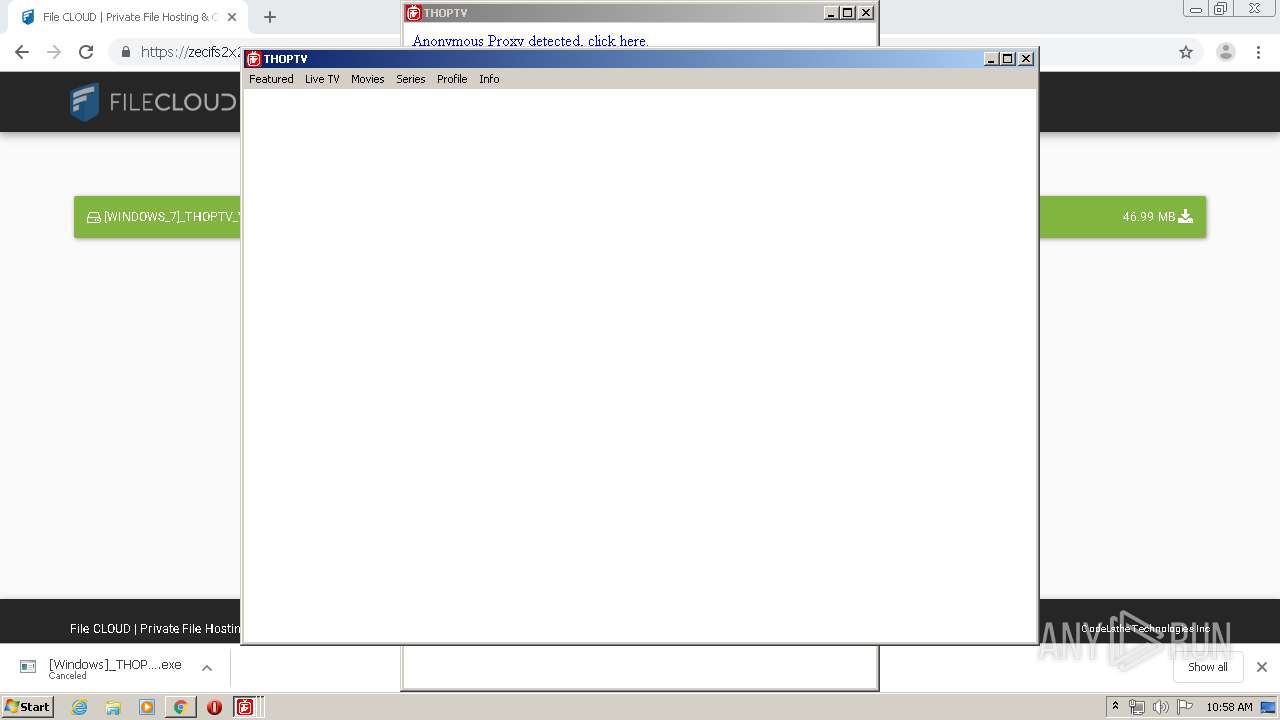
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2020, 09:53:03 |
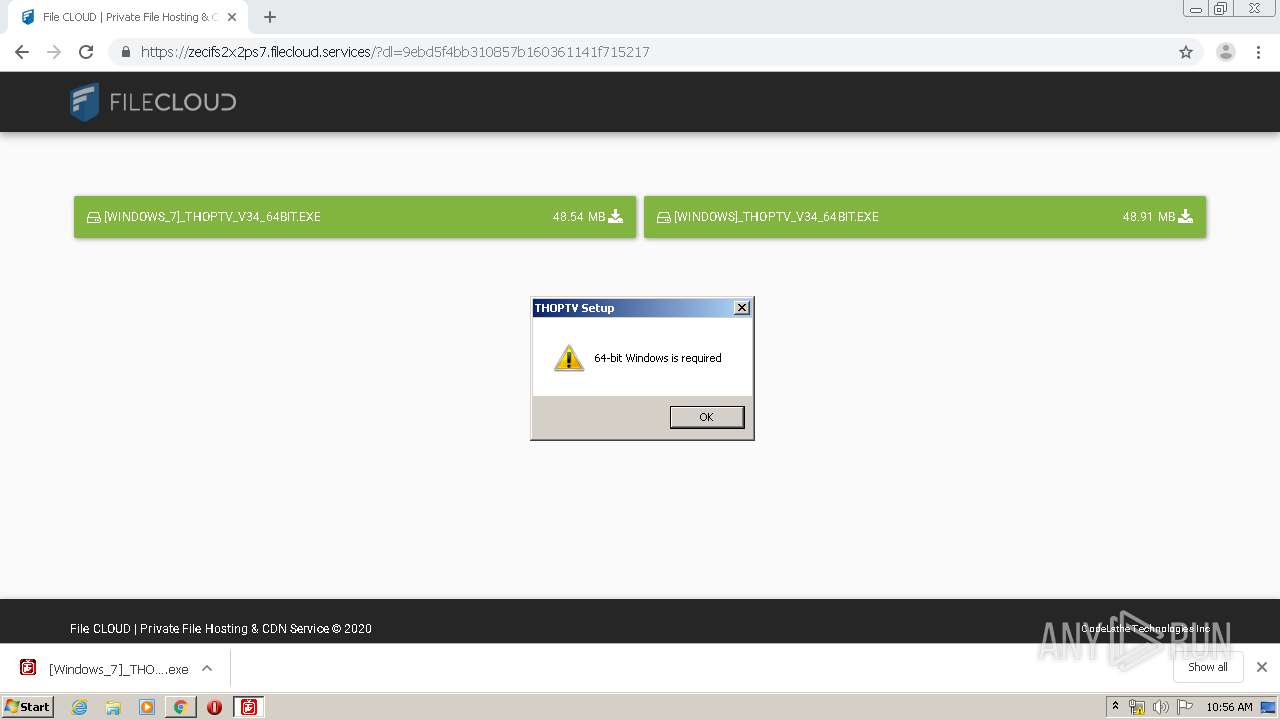
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BFA93474BFB436E96FE838502DB7BD24 |
| SHA1: | A1E6BFE020642110335BA1088D7718DBDB1D969E |
| SHA256: | A8DBDDEA8BE94C7A6FE8E80B57CF79A6D2C24557897E09B54DE3B5031C16445D |
| SSDEEP: | 3:N8FKbDLEo:2Uz |
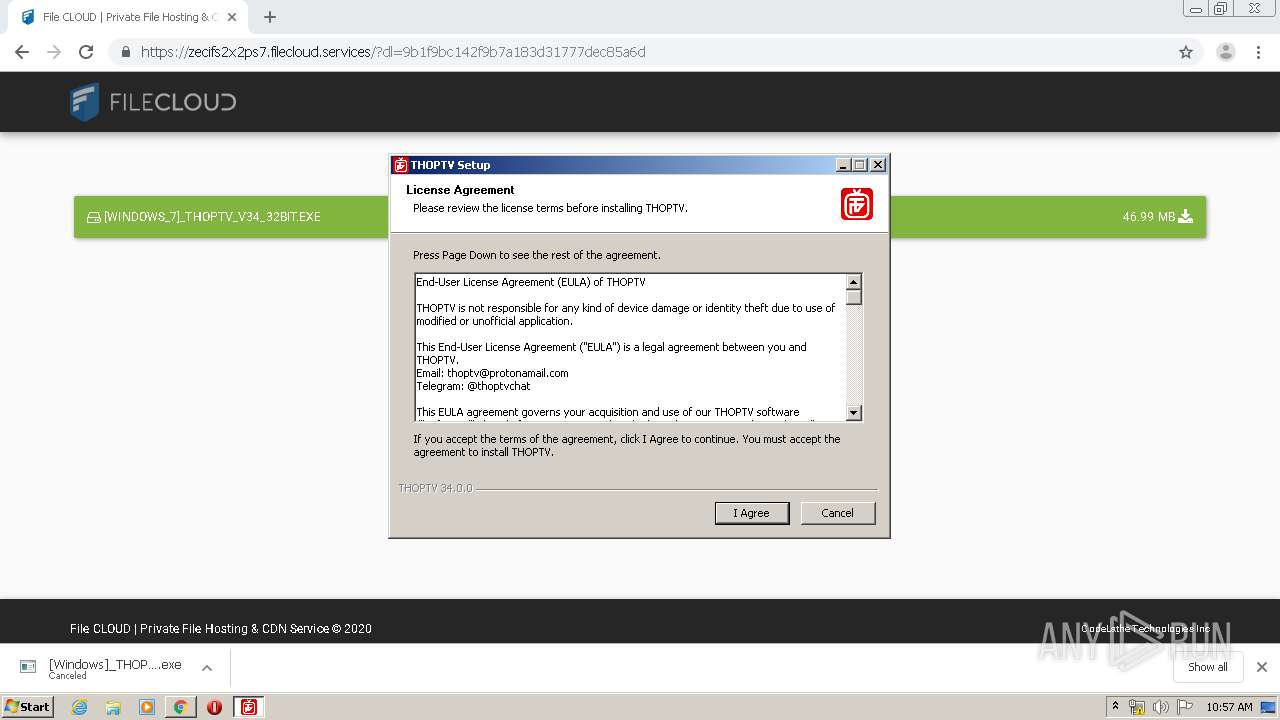
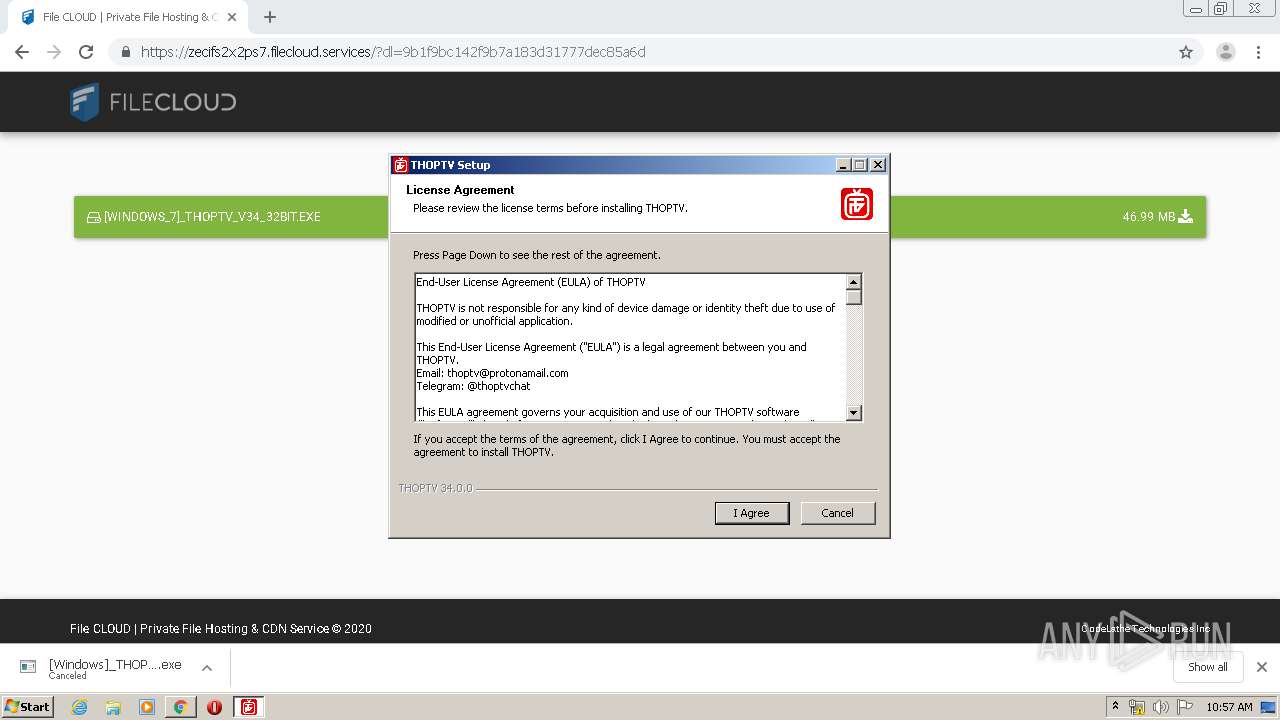
MALICIOUS
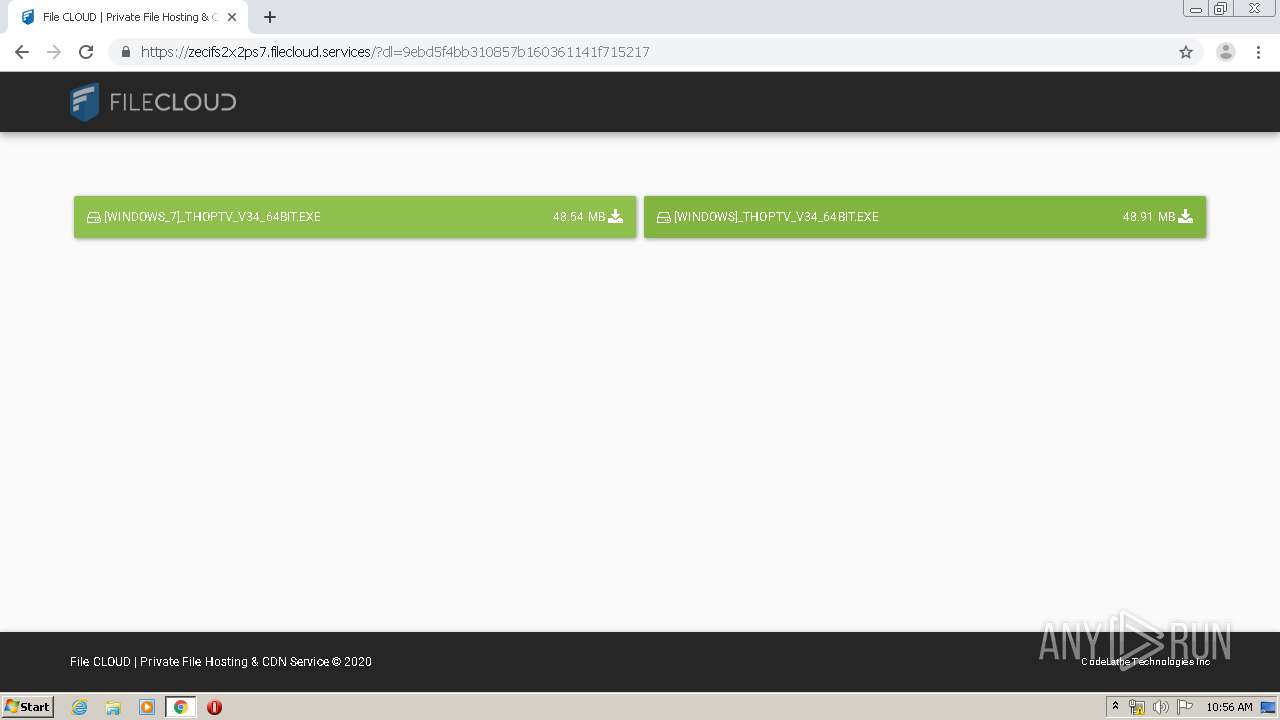
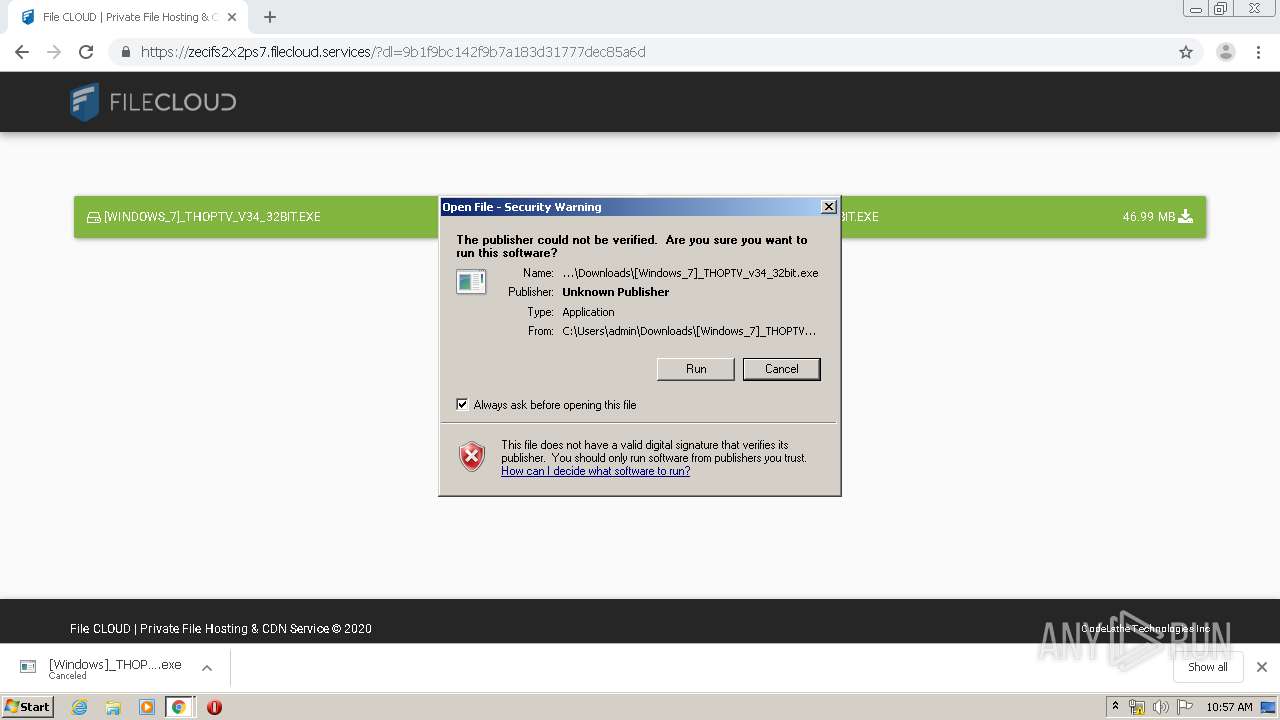
Application was dropped or rewritten from another process
- [Windows_7]_THOPTV_v34_32bit.exe (PID: 2836)
- [Windows_7]_THOPTV_v34_64bit.exe (PID: 2896)
- [Windows_7]_THOPTV_v34_32bit.exe (PID: 1328)
Loads dropped or rewritten executable
- [Windows_7]_THOPTV_v34_64bit.exe (PID: 2896)
- [Windows_7]_THOPTV_v34_32bit.exe (PID: 2836)
- [Windows_7]_THOPTV_v34_32bit.exe (PID: 1328)
- THOPTV.exe (PID: 4032)
- THOPTV.exe (PID: 3100)
- THOPTV.exe (PID: 180)
- THOPTV.exe (PID: 3844)
- THOPTV.exe (PID: 608)
- THOPTV.exe (PID: 3740)
- THOPTV.exe (PID: 3016)
- THOPTV.exe (PID: 3332)
- THOPTV.exe (PID: 2140)
- THOPTV.exe (PID: 2648)
- THOPTV.exe (PID: 3776)
- THOPTV.exe (PID: 1636)
- THOPTV.exe (PID: 3956)
- THOPTV.exe (PID: 912)
- THOPTV.exe (PID: 4076)
- THOPTV.exe (PID: 3804)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2720)
Executable content was dropped or overwritten
- [Windows_7]_THOPTV_v34_32bit.exe (PID: 2836)
- [Windows_7]_THOPTV_v34_64bit.exe (PID: 2896)
- chrome.exe (PID: 2720)
- [Windows_7]_THOPTV_v34_32bit.exe (PID: 1328)
Application launched itself
- [Windows_7]_THOPTV_v34_32bit.exe (PID: 2836)
- THOPTV.exe (PID: 4032)
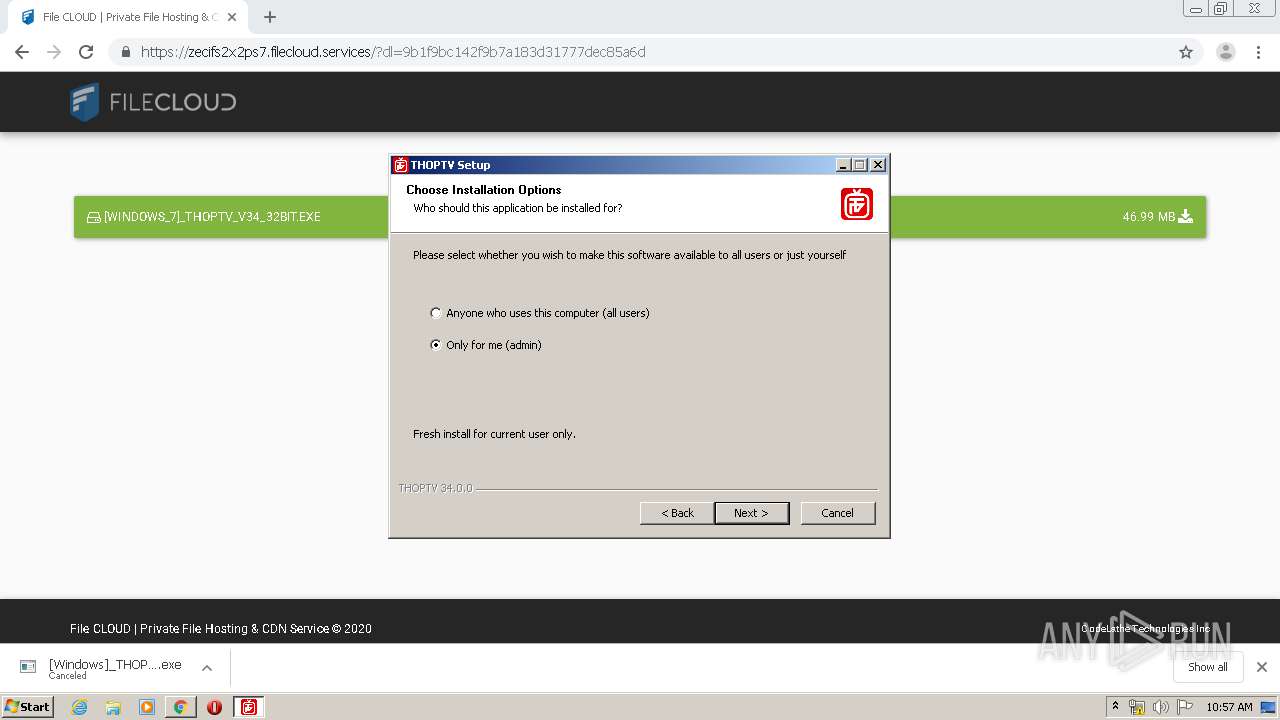
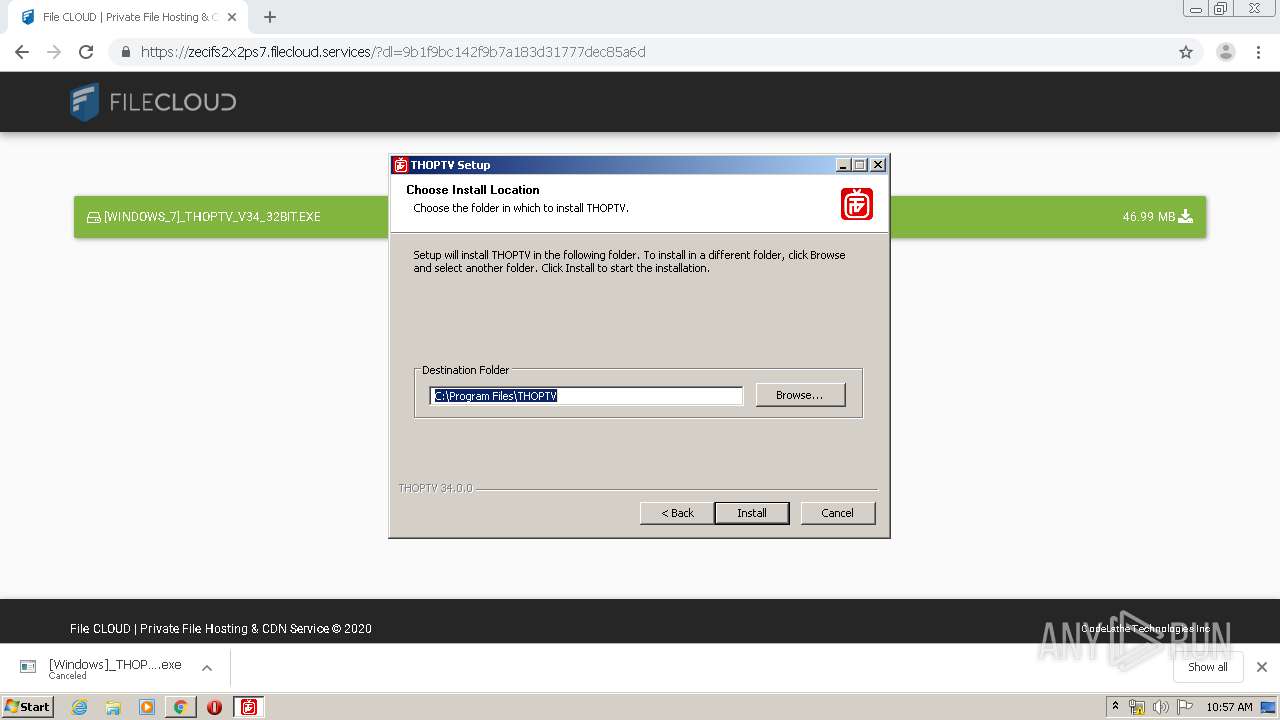
Creates a software uninstall entry
- [Windows_7]_THOPTV_v34_32bit.exe (PID: 1328)
Creates files in the program directory
- [Windows_7]_THOPTV_v34_32bit.exe (PID: 1328)
Starts CMD.EXE for commands execution
- THOPTV.exe (PID: 4032)
Creates files in the user directory
- THOPTV.exe (PID: 4032)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2844)
INFO
Reads the hosts file
- chrome.exe (PID: 2720)
- chrome.exe (PID: 3140)
- THOPTV.exe (PID: 4032)
Reads Internet Cache Settings
- chrome.exe (PID: 2720)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2720)
Application launched itself
- chrome.exe (PID: 2720)
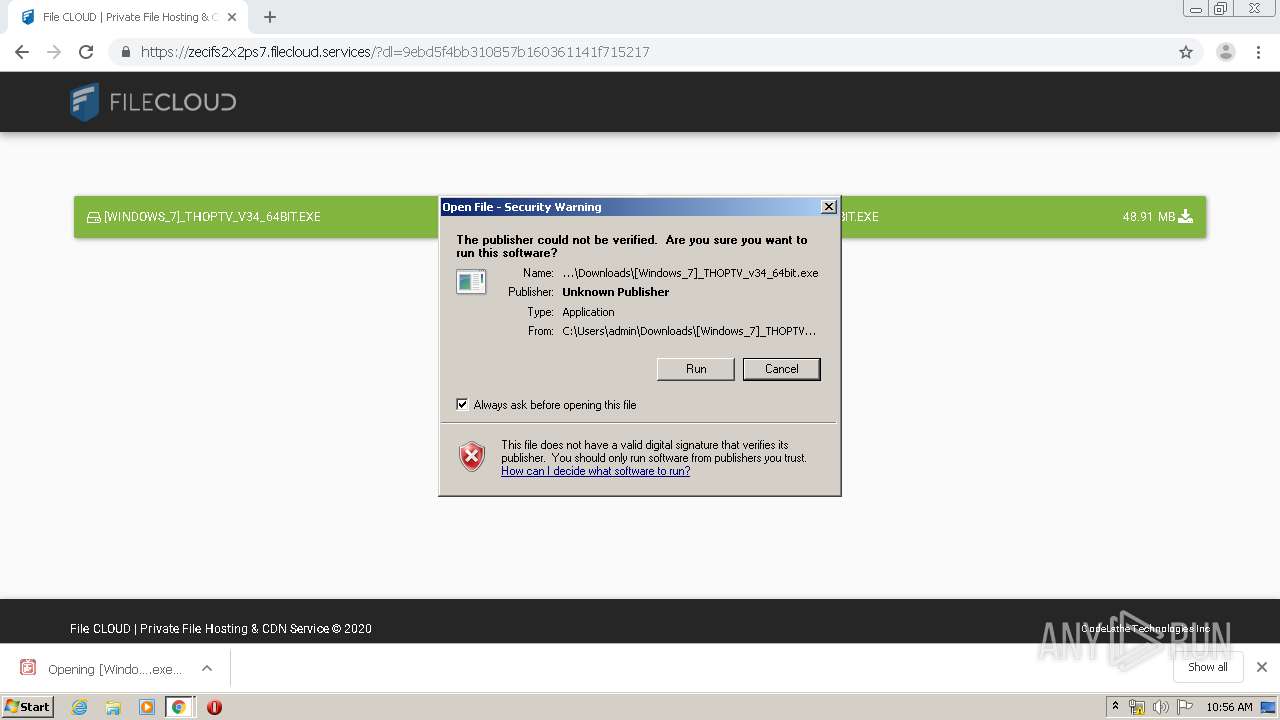
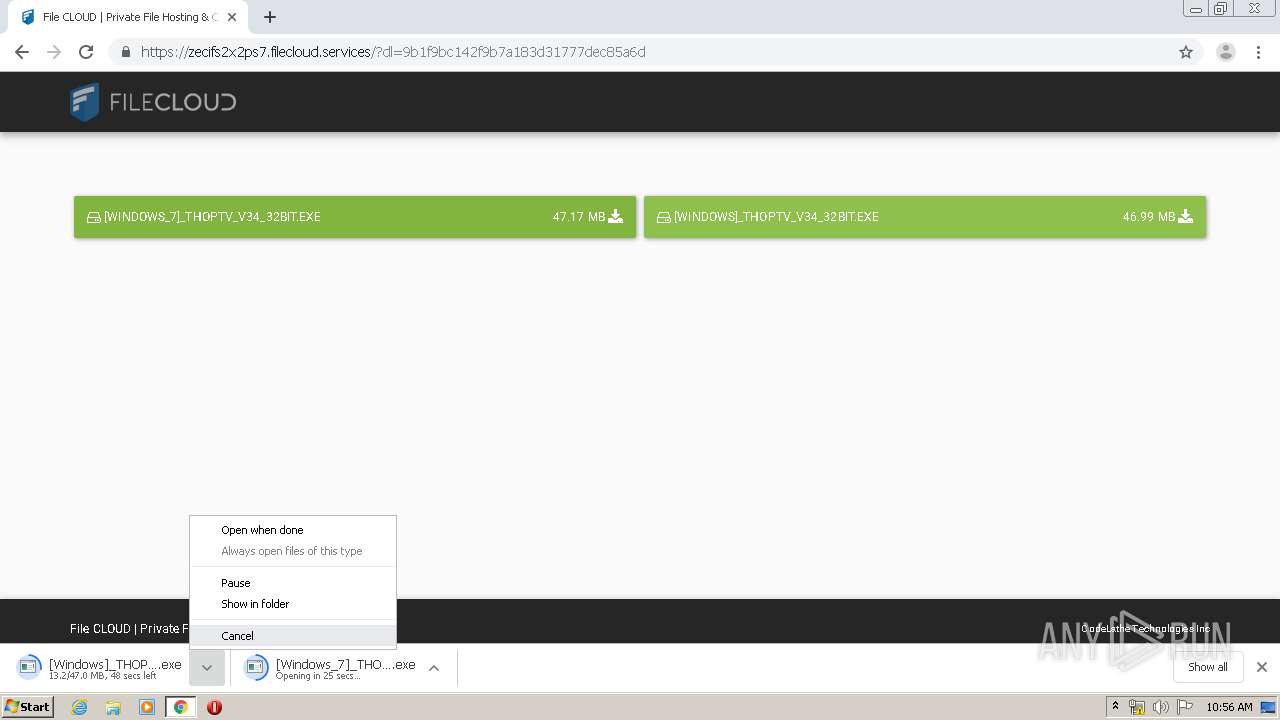
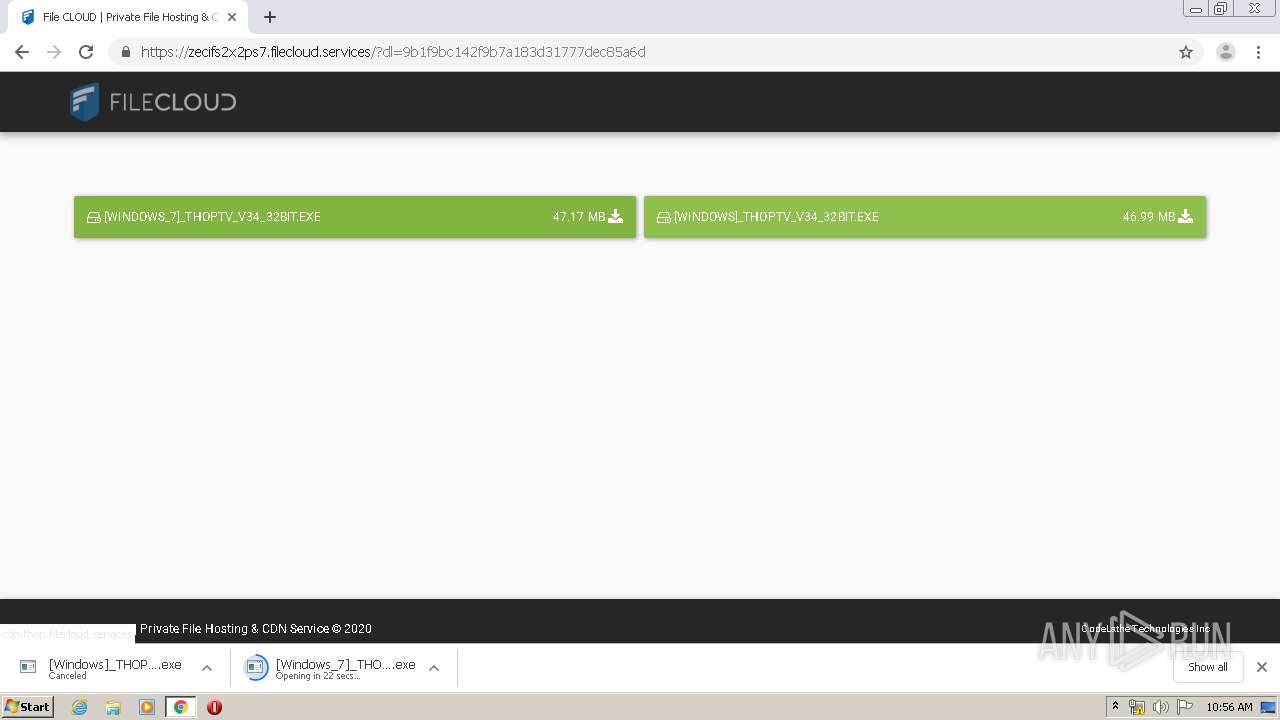
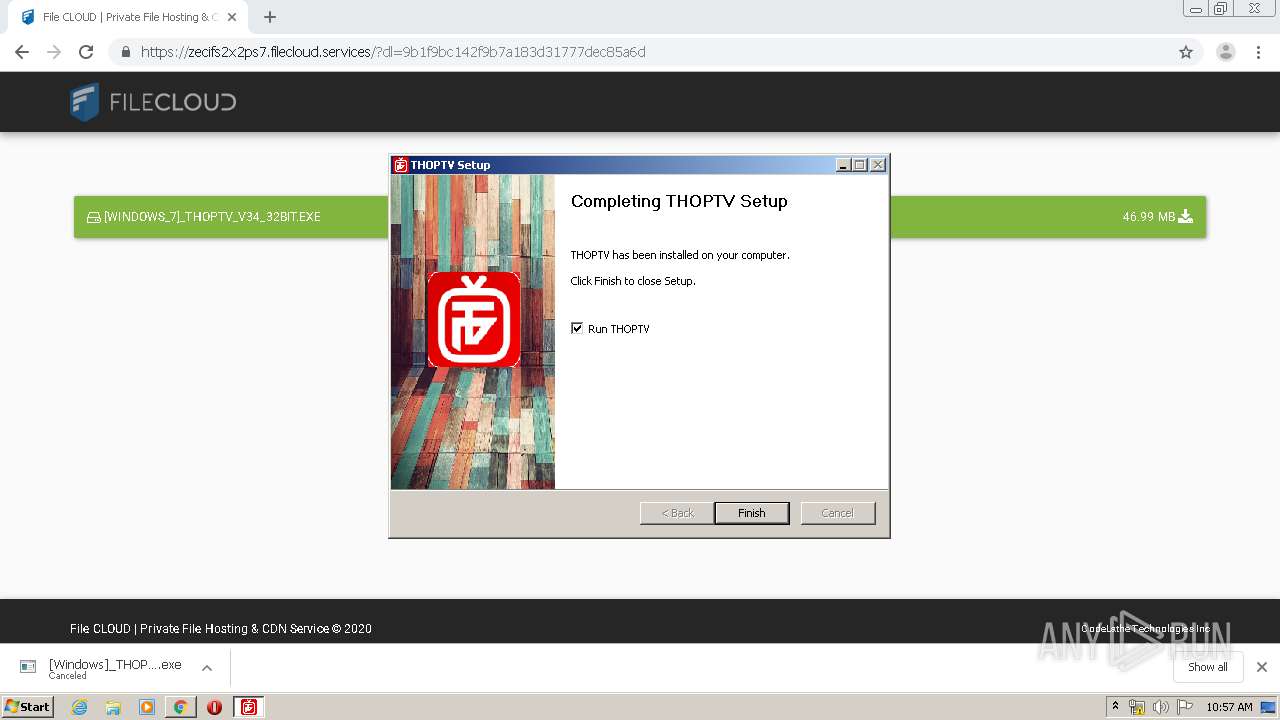
Manual execution by user
- THOPTV.exe (PID: 4032)
Reads settings of System Certificates
- chrome.exe (PID: 3140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
118
Monitored processes
70
Malicious processes
5
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\THOPTV\THOPTV.exe" --type=renderer --no-sandbox --enable-features=SharedArrayBuffer --disable-gpu-compositing --service-pipe-token=9327927393987575513 --lang=en-US --app-path="C:\Program Files\THOPTV\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --background-color=#fff --guest-instance-id=1 --enable-blink-features --disable-blink-features --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9327927393987575513 --renderer-client-id=7 --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\THOPTV\THOPTV.exe | — | THOPTV.exe | |||||||||||
User: admin Company: Thopster Athen Integrity Level: MEDIUM Description: THOPTV Exit code: 0 Version: 34.0.0 Modules
| |||||||||||||||
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,14254457422872372749,1003518120104931550,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9405236992000252200 --mojo-platform-channel-handle=3900 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,14254457422872372749,1003518120104931550,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18235010778120831608 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,14254457422872372749,1003518120104931550,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9631005039999301019 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4560 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=976,14254457422872372749,1003518120104931550,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12822702734431930817 --mojo-platform-channel-handle=3676 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 608 | "C:\Program Files\THOPTV\THOPTV.exe" --type=renderer --no-sandbox --enable-features=SharedArrayBuffer --disable-gpu-compositing --service-pipe-token=13110184413988353415 --lang=en-US --app-path="C:\Program Files\THOPTV\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --background-color=#fff --guest-instance-id=1 --enable-blink-features --disable-blink-features --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13110184413988353415 --renderer-client-id=9 --mojo-platform-channel-handle=2012 /prefetch:1 | C:\Program Files\THOPTV\THOPTV.exe | — | THOPTV.exe | |||||||||||
User: admin Company: Thopster Athen Integrity Level: MEDIUM Description: THOPTV Exit code: 0 Version: 34.0.0 Modules
| |||||||||||||||
| 912 | "C:\Program Files\THOPTV\THOPTV.exe" --type=gpu-process --enable-features=SharedArrayBuffer --disable-gpu-sandbox --no-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=4980946378247039369 --mojo-platform-channel-handle=2648 /prefetch:2 | C:\Program Files\THOPTV\THOPTV.exe | — | THOPTV.exe | |||||||||||
User: admin Company: Thopster Athen Integrity Level: MEDIUM Description: THOPTV Exit code: 0 Version: 34.0.0 Modules
| |||||||||||||||
| 1328 | "C:\Users\admin\Downloads\[Windows_7]_THOPTV_v34_32bit.exe" /UAC:A0218 /NCRC | C:\Users\admin\Downloads\[Windows_7]_THOPTV_v34_32bit.exe | [Windows_7]_THOPTV_v34_32bit.exe | ||||||||||||
User: admin Company: Thopster Athen Integrity Level: HIGH Description: Watch free Live TV and Movies and VOD for free Exit code: 0 Version: 34.0.0 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,14254457422872372749,1003518120104931550,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14425066356079375670 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,14254457422872372749,1003518120104931550,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12012804415611250800 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4668 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 496
Read events
2 338
Write events
153
Delete events
5
Modification events
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3200) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2720-13234355598758375 |
Value: 259 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
30
Suspicious files
175
Text files
240
Unknown types
73
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EC3AC8F-AA0.pma | — | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\309f50f7-5679-4fa8-b09c-786b8bed6814.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa87454.TMP | text | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa87415.TMP | text | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa87425.TMP | text | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa87415.TMP | text | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa875cb.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
97
DNS requests
67
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4032 | THOPTV.exe | GET | 403 | 198.134.112.244:80 | http://terraclicks.com/anonymous/ | US | — | — | whitelisted |
3140 | chrome.exe | GET | 200 | 74.125.4.216:80 | http://r2---sn-aigzrney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.217.117.48&mm=28&mn=sn-aigzrney&ms=nvh&mt=1589881932&mv=m&mvi=1&pl=25&shardbypass=yes | US | crx | 816 Kb | whitelisted |
3140 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
3140 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
3140 | chrome.exe | GET | 200 | 74.125.4.166:80 | http://r1---sn-aigzrne7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.217.117.48&mm=28&mn=sn-aigzrne7&ms=nvh&mt=1589881932&mv=m&mvi=0&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3140 | chrome.exe | 172.217.21.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3140 | chrome.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
3140 | chrome.exe | 13.226.159.129:443 | buttons-config.sharethis.com | — | US | unknown |
3140 | chrome.exe | 13.226.159.88:443 | c.sharethis.mgr.consensu.org | — | US | unknown |
3140 | chrome.exe | 172.217.23.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
3140 | chrome.exe | 18.195.176.77:443 | l.sharethis.com | Amazon.com, Inc. | DE | unknown |
3140 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3140 | chrome.exe | 74.125.4.166:80 | r1---sn-aigzrne7.gvt1.com | Google Inc. | US | whitelisted |
3140 | chrome.exe | 172.217.16.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3140 | chrome.exe | 172.217.16.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
thoptv.download |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| malicious |
platform-api.sharethis.com |
| whitelisted |
s.w.org |
| whitelisted |
stats.wp.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
buttons-config.sharethis.com |
| shared |
c.sharethis.mgr.consensu.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M2 |
4032 | THOPTV.exe | Potentially Bad Traffic | ET INFO Suspicious TLS SNI Request for Possible COVID-19 Domain M2 |
4032 | THOPTV.exe | Potentially Bad Traffic | ET INFO Possible COVID-19 Domain in SSL Certificate M1 |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |