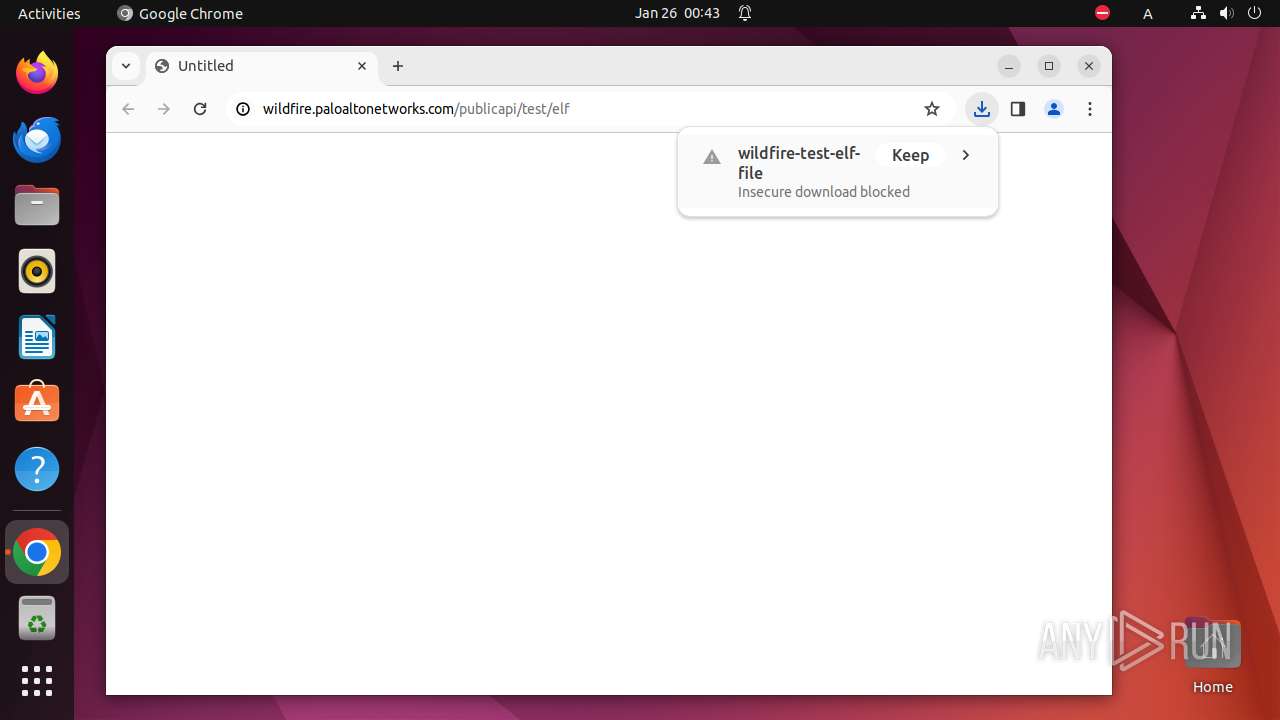
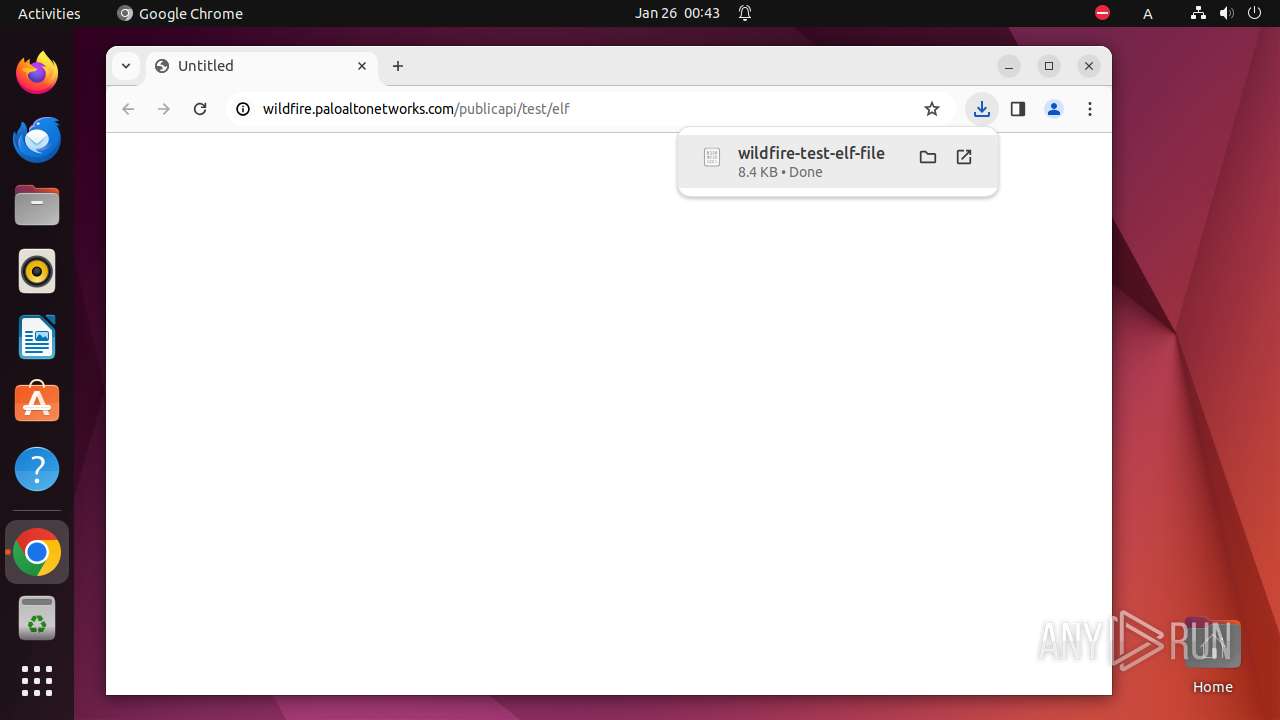
| URL: | http://wildfire.paloaltonetworks.com/publicapi/test/elf |
| Full analysis: | https://app.any.run/tasks/6172e8c4-4e2c-4890-bdfe-5cfcb515f3ca |
| Verdict: | Malicious activity |
| Analysis date: | January 26, 2024, 00:43:43 |
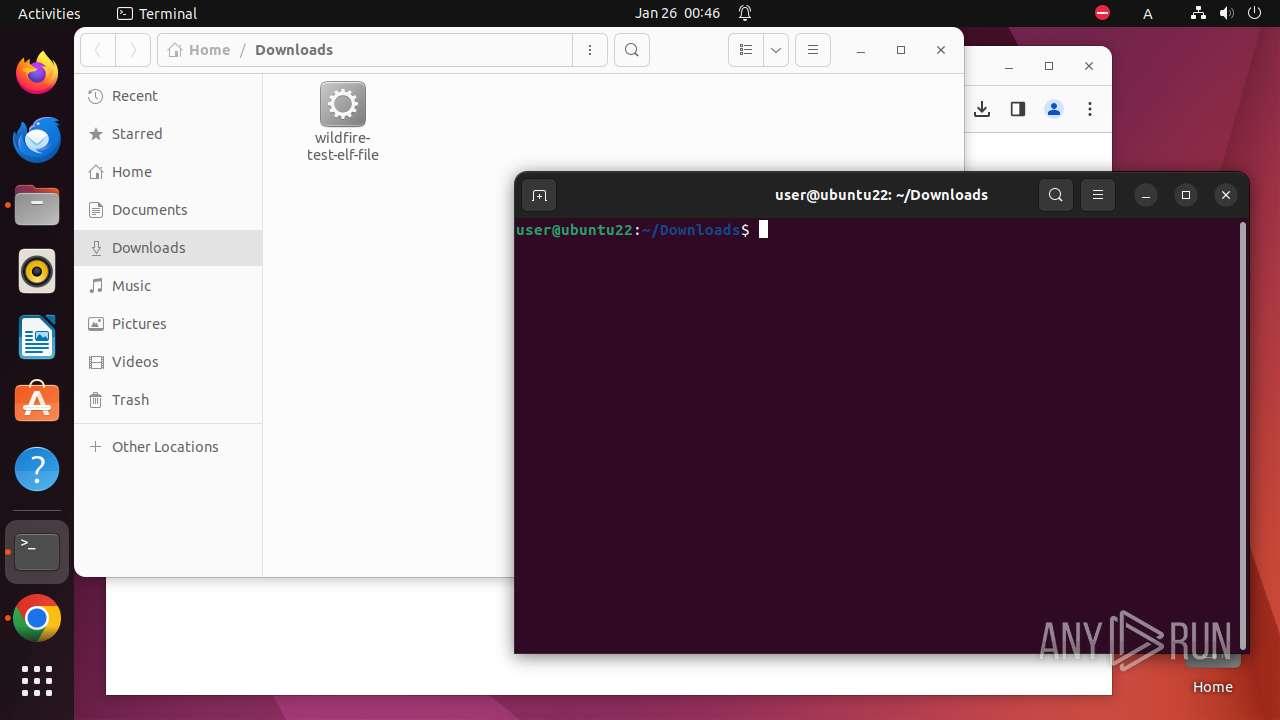
| OS: | Ubuntu 22.04.2 |
| MD5: | BE62A59AE0494194F1CE02FC3D02D061 |
| SHA1: | 69BFDD186E9F2C2A1A27AAE229208D90DC69625E |
| SHA256: | A8D8A3358E688593016F9EE621AF770A22D268252D8C2DB00F01ADDA074EAAFD |
| SSDEEP: | 3:N1KJMPQXMEfQ0JsK3VQHJkVMKRn:CC+9sKKHJk7 |
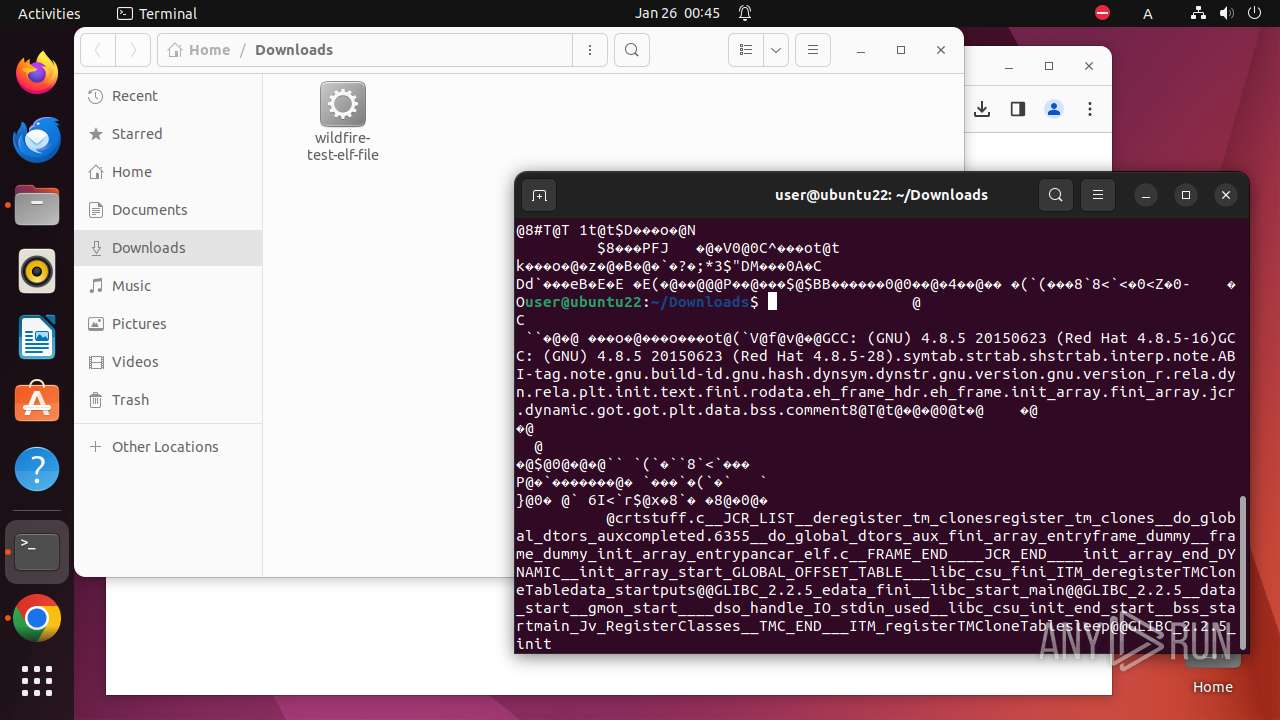
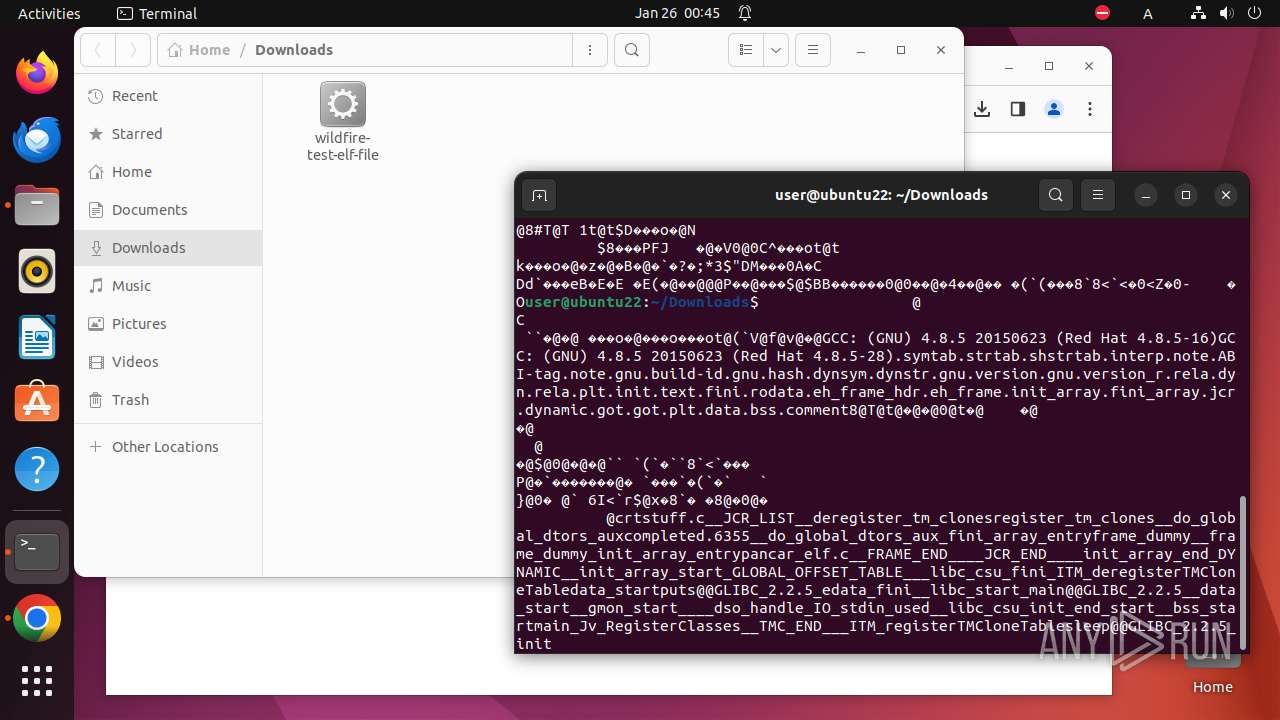
MALICIOUS
No malicious indicators.SUSPICIOUS
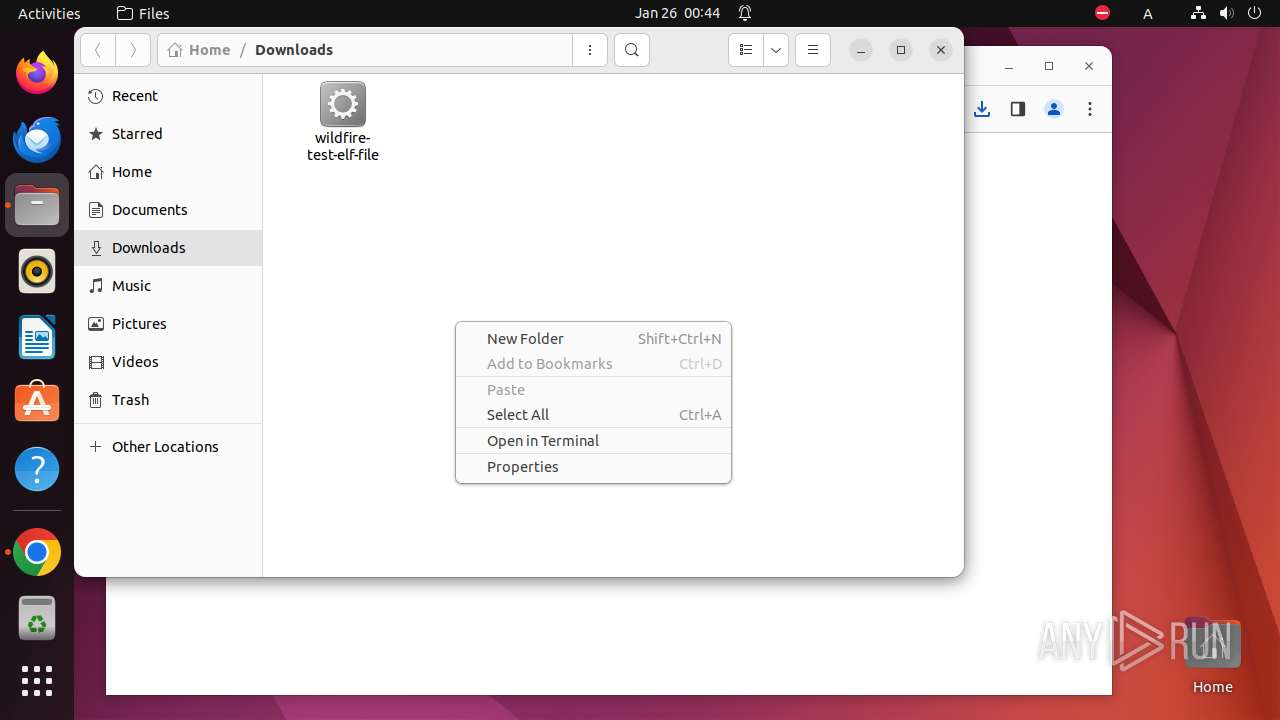
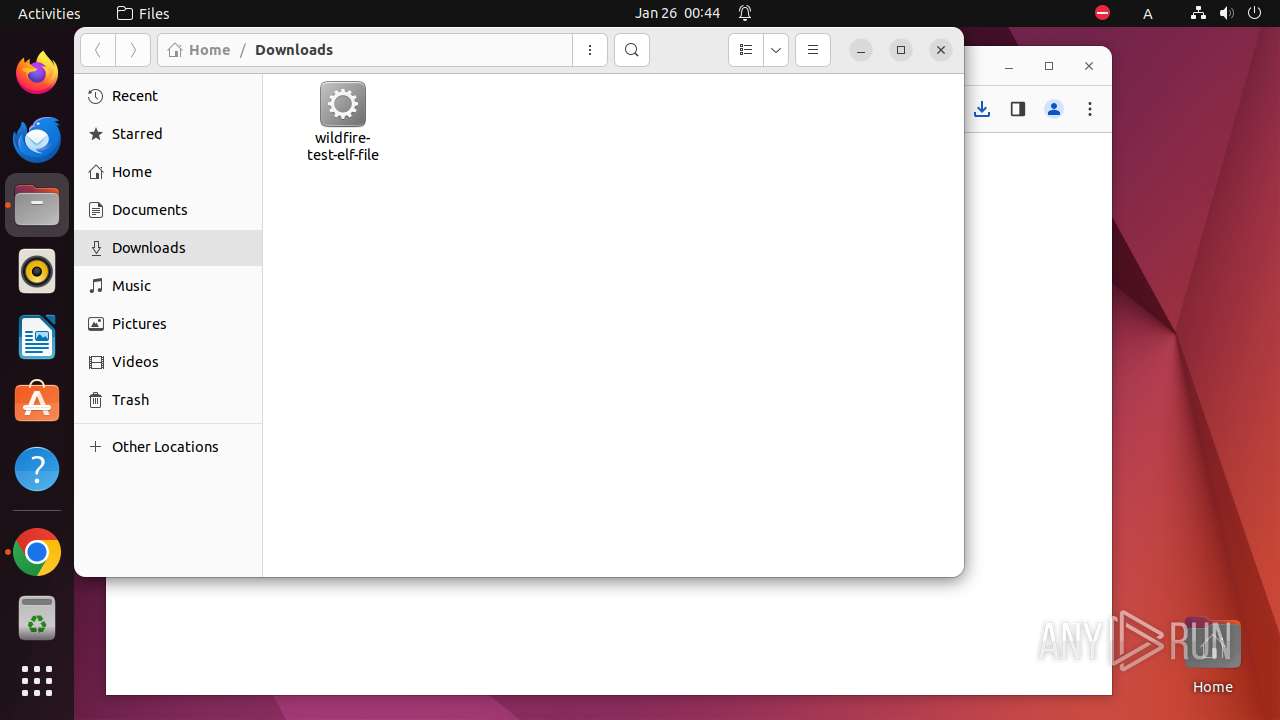
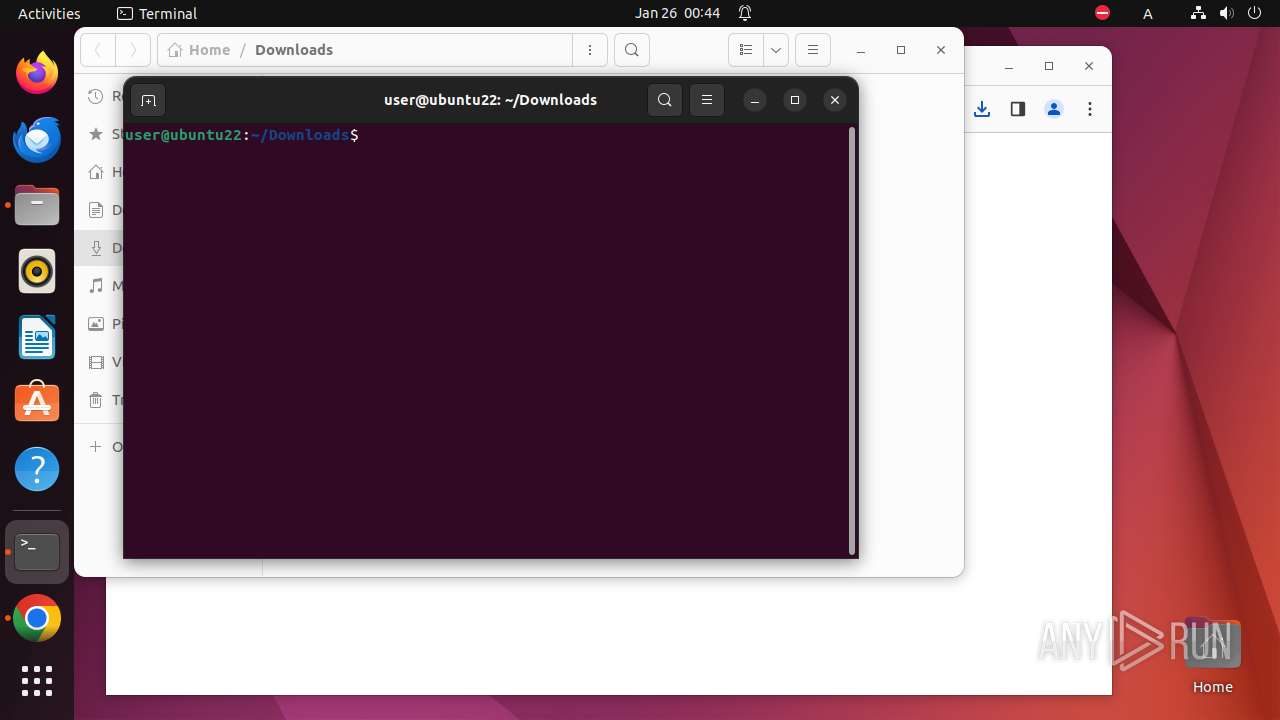
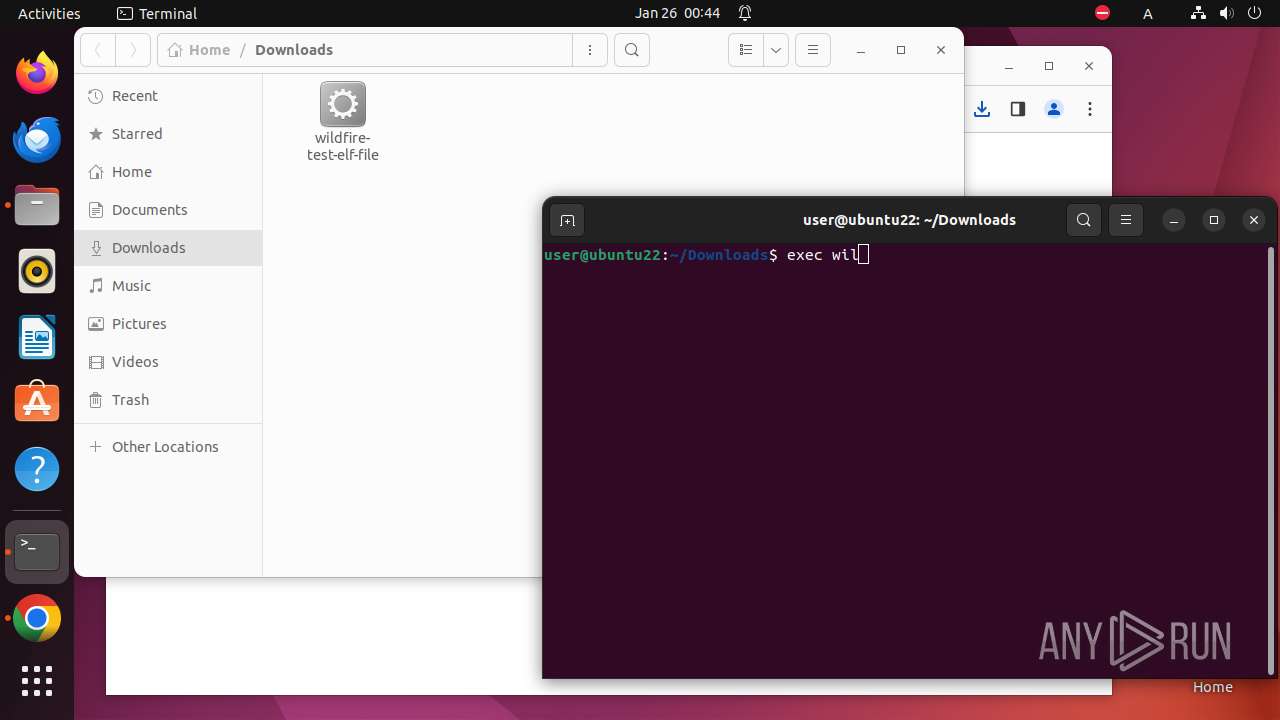
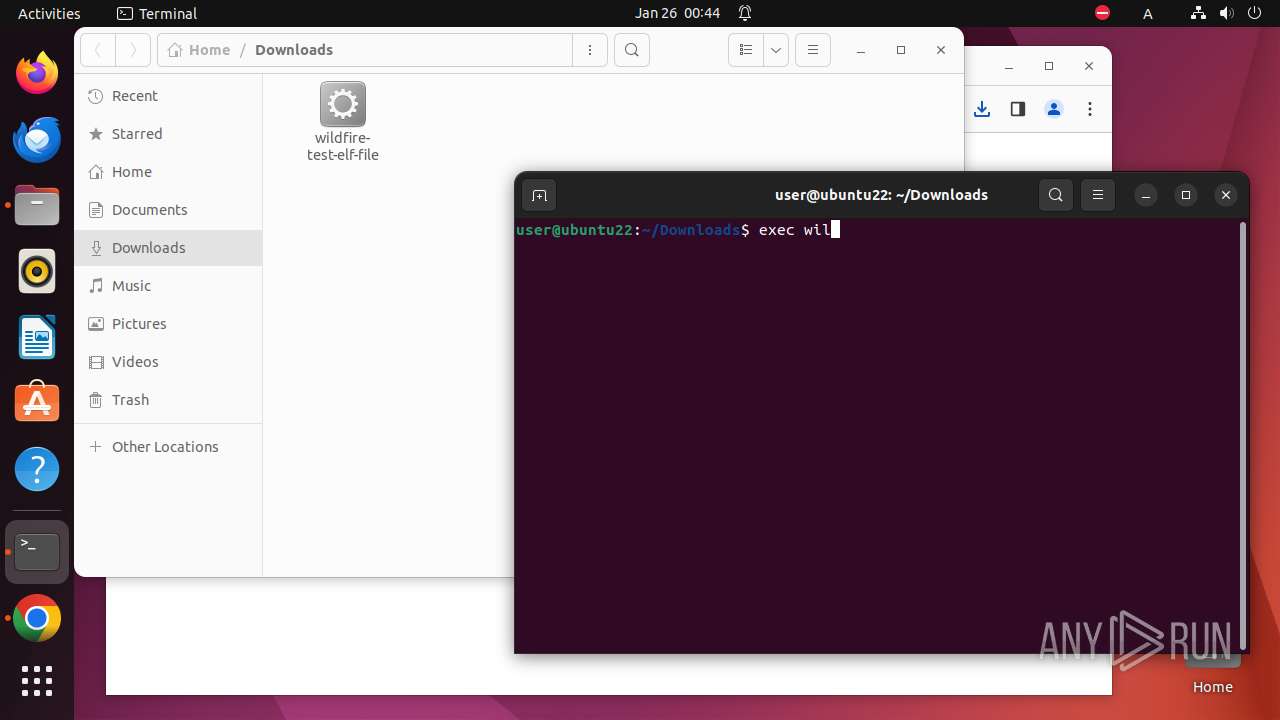
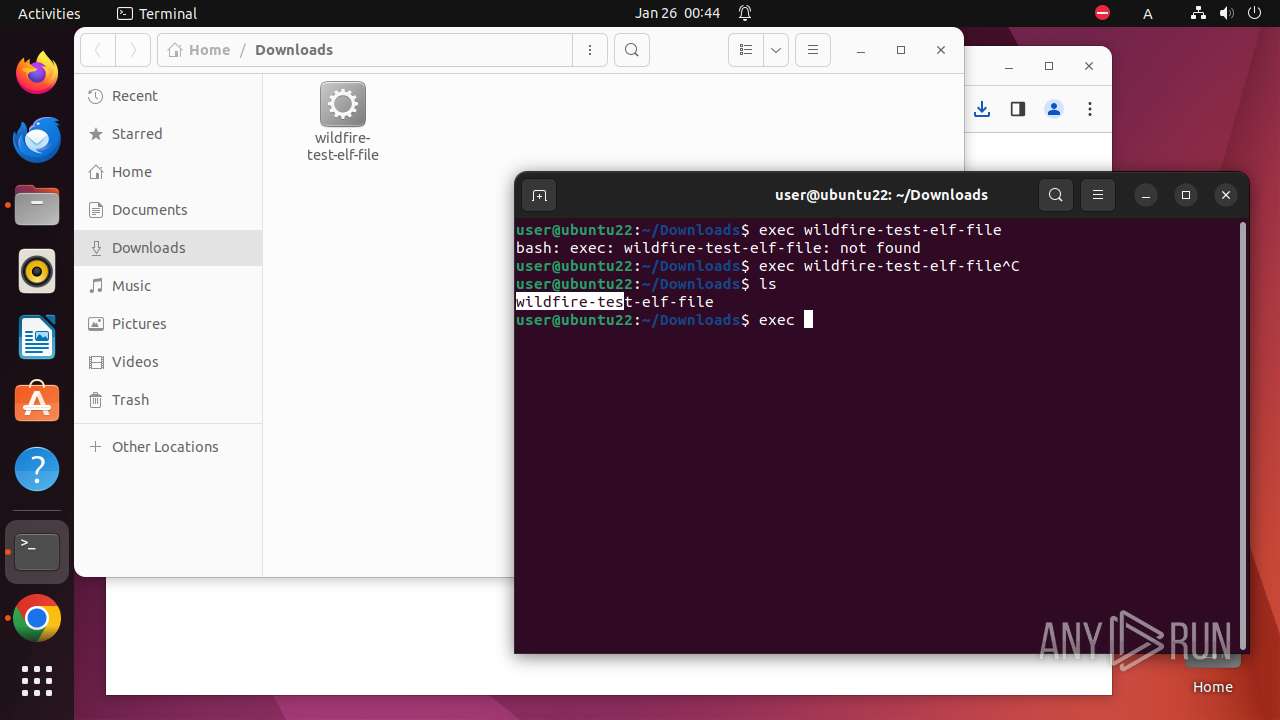
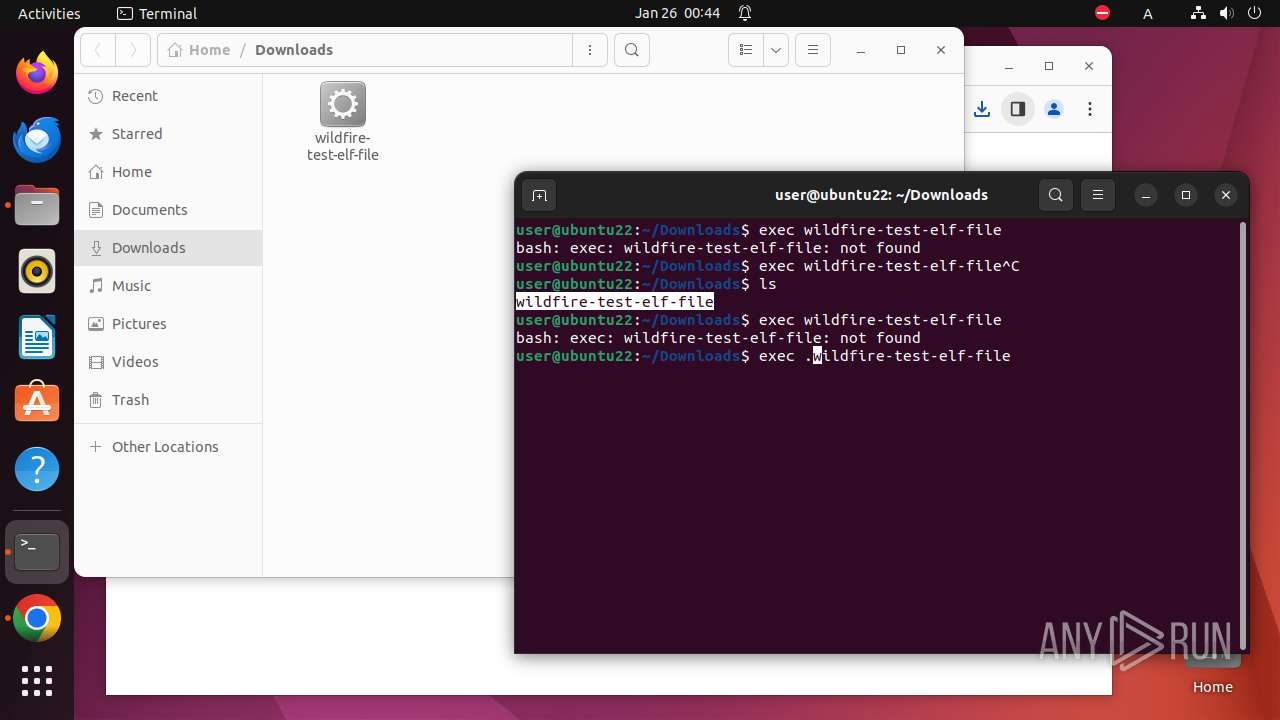
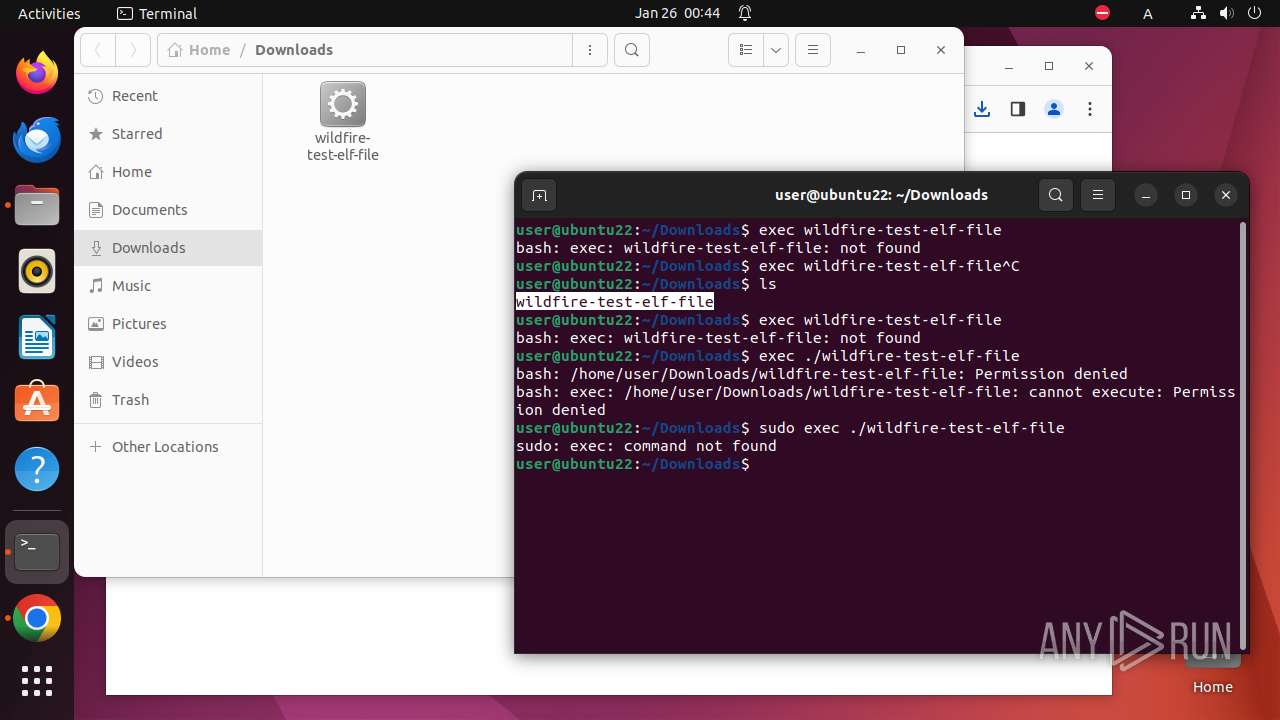
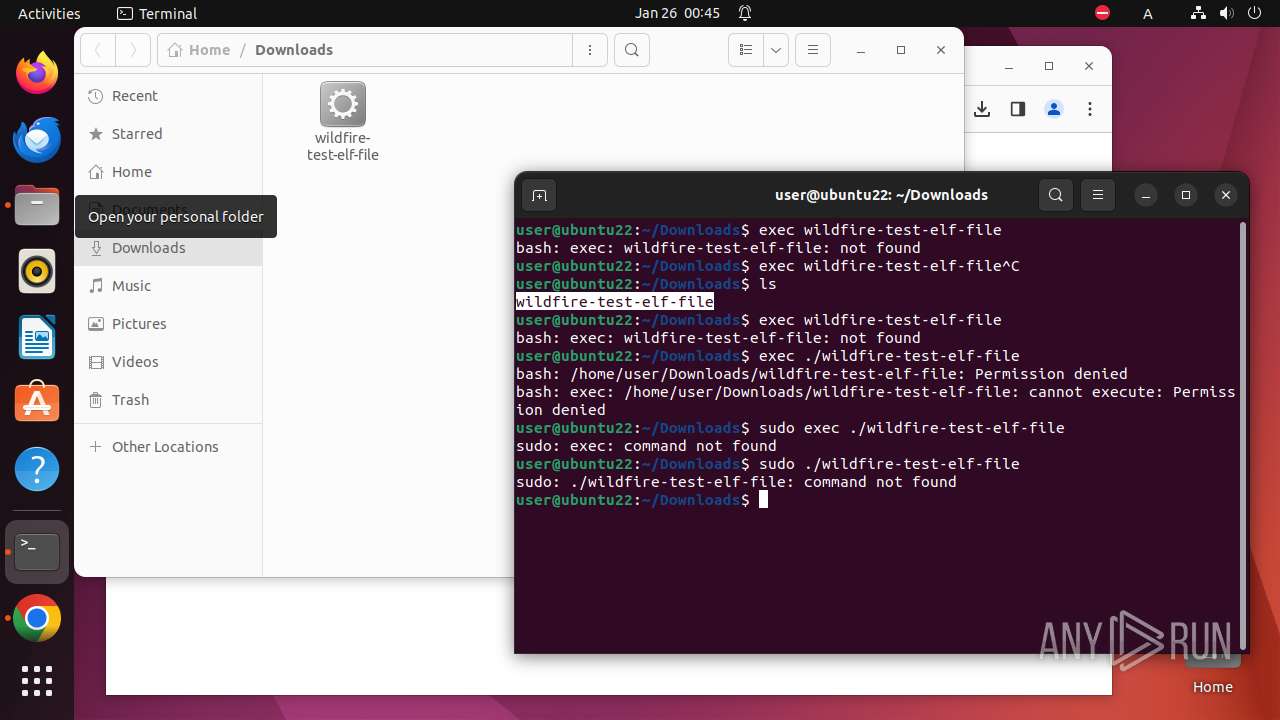
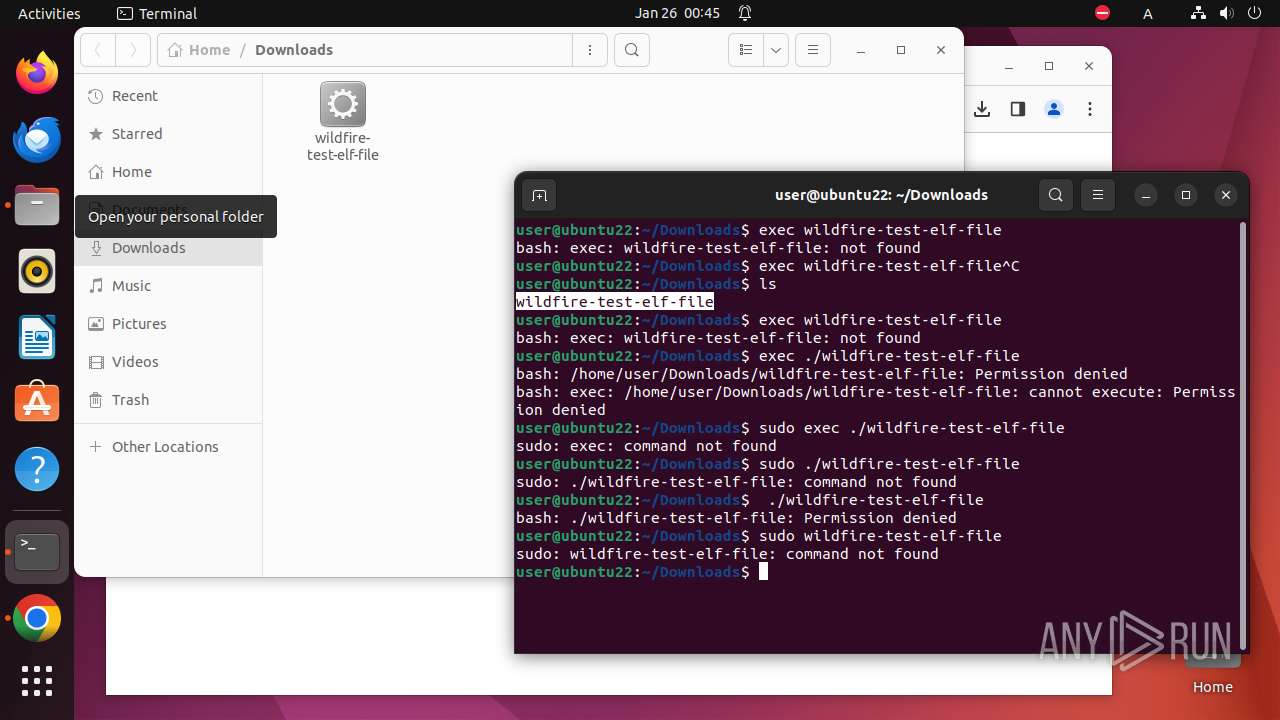
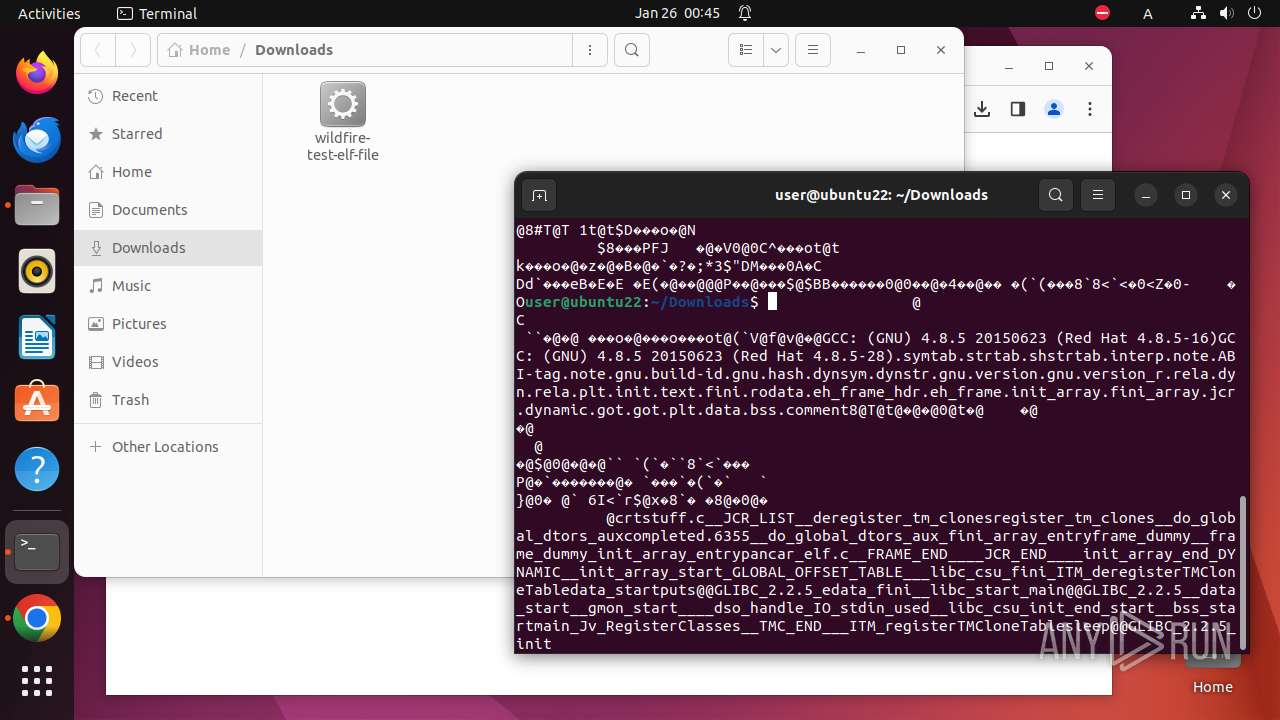
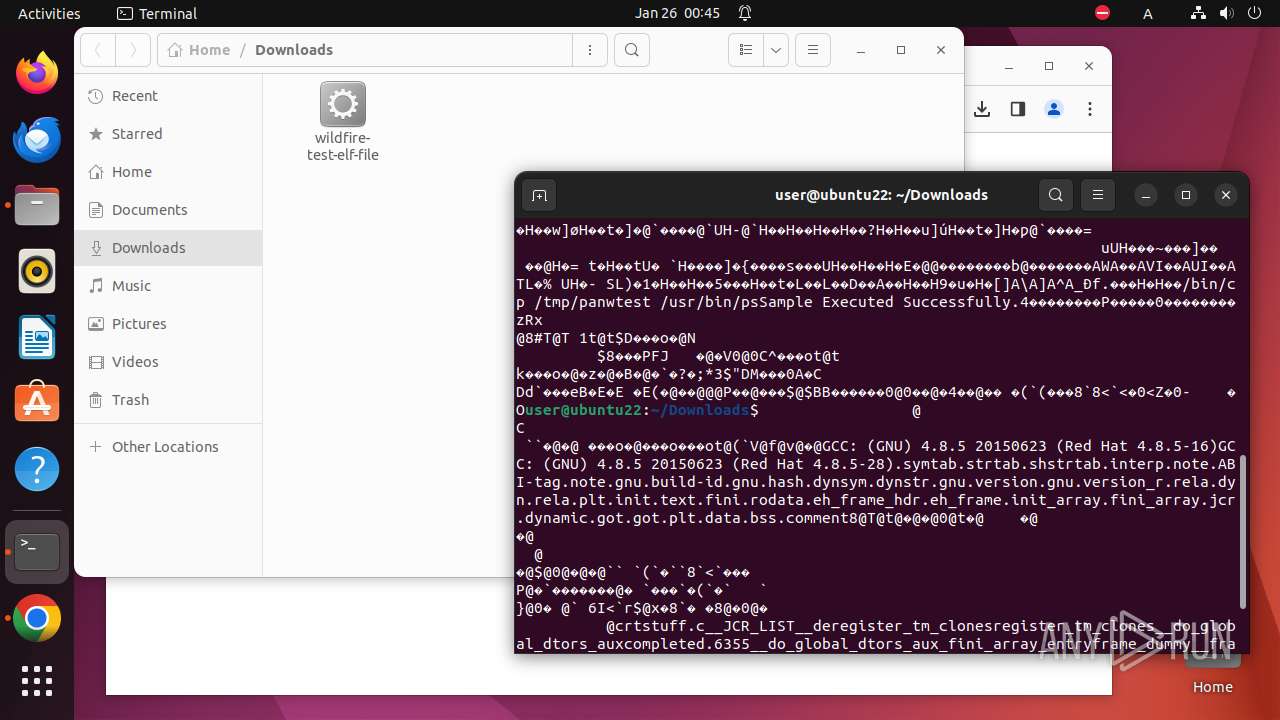
Executes commands using command-line interpreter
- sudo (PID: 6849)
- gnome-terminal-server (PID: 7052)
Reads passwd file
- chrome (PID: 6850)
- bash (PID: 7070)
- nautilus (PID: 7031)
Checks timezone
- nautilus (PID: 7031)
- chrome (PID: 6850)
Check the Environment Variables Related to System Identification (os-release)
- chrome (PID: 6850)
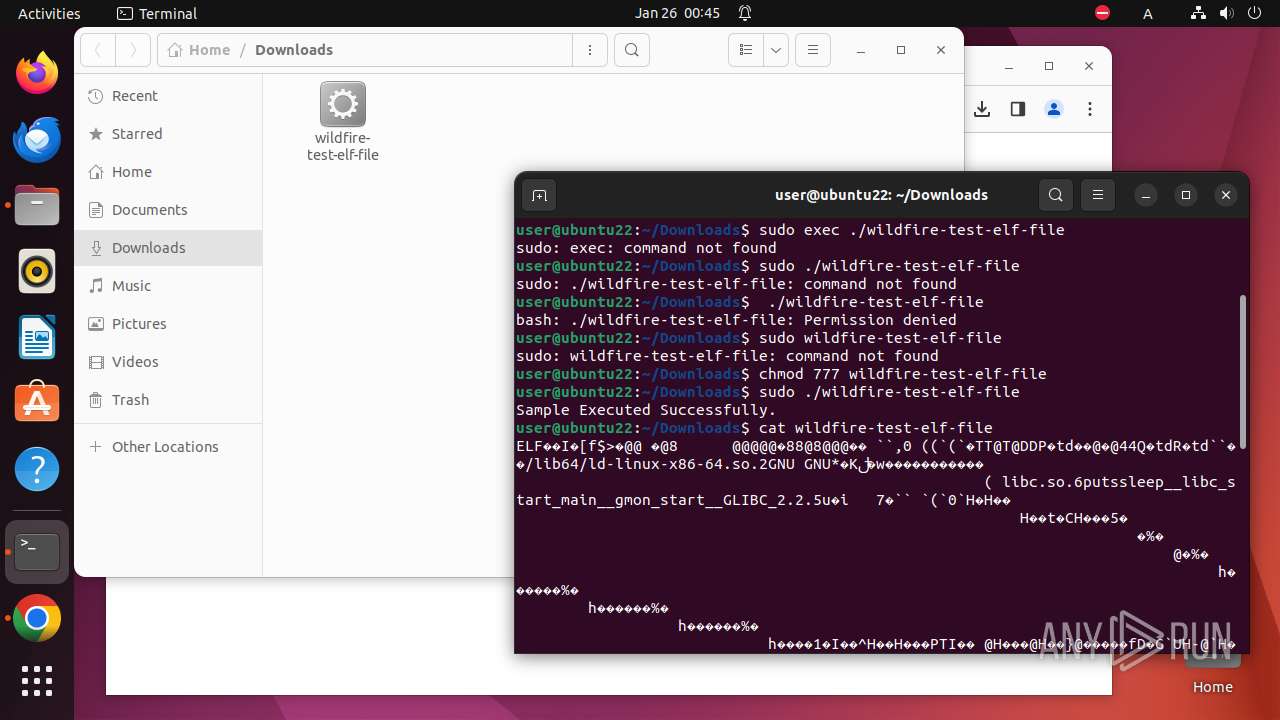
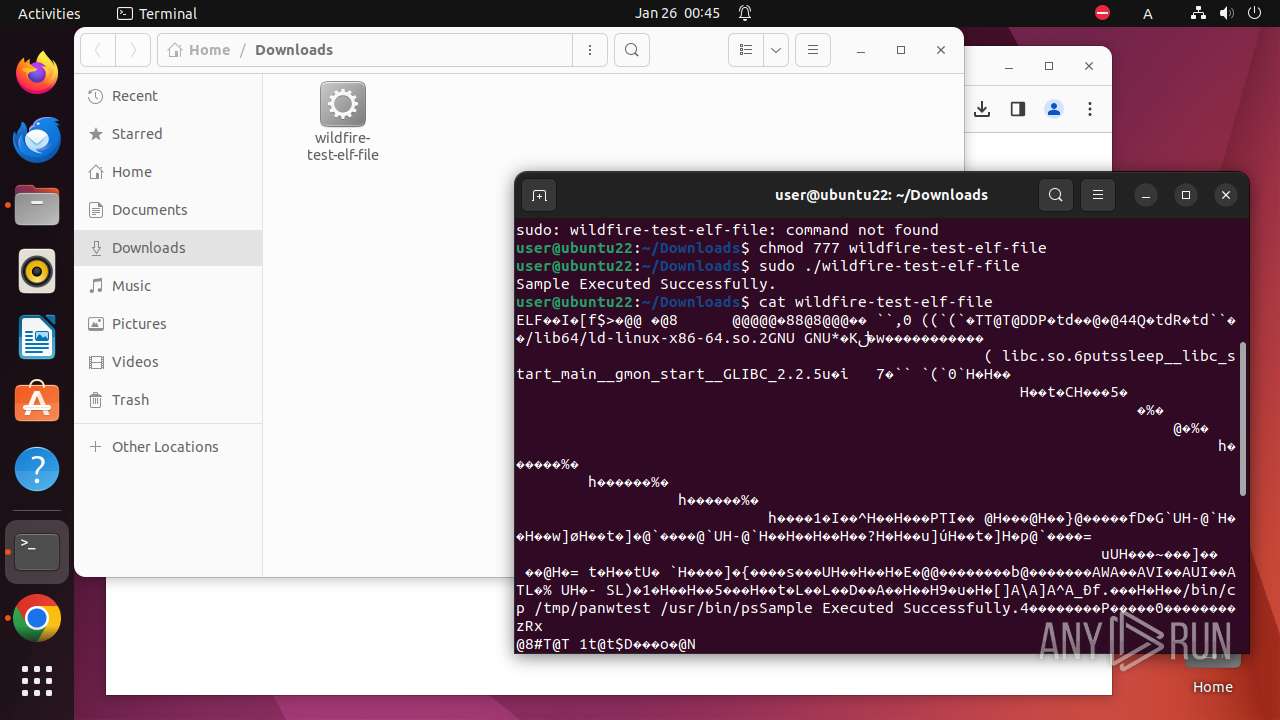
Changes file or directory permissions
- bash (PID: 7070)
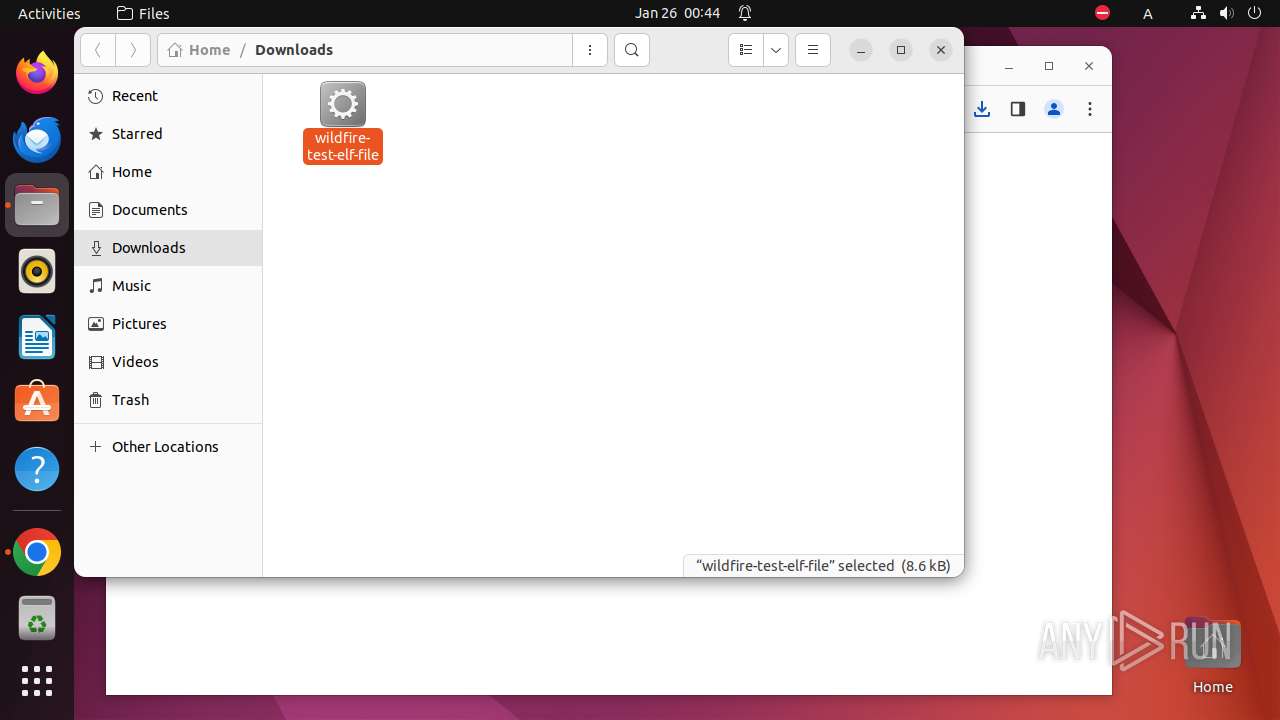
Creates files in the user directory
- chrome (PID: 6850)
Reads information about logins, logouts, and login attempts
- bash (PID: 7070)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
307
Monitored processes
88
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 6848 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome \"http://wildfire\.paloaltonetworks\.com/publicapi/test/elf\" " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6849 | sudo -iu user google-chrome http://wildfire.paloaltonetworks.com/publicapi/test/elf | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6850 | /usr/bin/google-chrome http://wildfire.paloaltonetworks.com/publicapi/test/elf | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6851 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6852 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6853 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6854 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6855 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6856 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6857 | "/opt/google/chrome/chrome http://wildfire\.paloaltonetworks\.com/publicapi/test/e" | /opt/google/chrome/chrome | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6850 | chrome | /6850/fd/63 | — | |
MD5:— | SHA256:— | |||
| 6850 | chrome | /home/user/.config/google-chrome/BrowserMetrics/BrowserMetrics-65B30048-1AC2.pma | — | |
MD5:— | SHA256:— | |||
| 6850 | chrome | /home/user/.config/google-chrome/Default/chrome_cart_db/LOG | — | |
MD5:— | SHA256:— | |||
| 6850 | chrome | /home/user/.config/google-chrome/Default/coupon_db/LOG | — | |
MD5:— | SHA256:— | |||
| 6850 | chrome | /home/user/.config/google-chrome/Default/LOG | — | |
MD5:— | SHA256:— | |||
| 6850 | chrome | /home/user/.config/google-chrome/Default/PersistentOriginTrials/LOG | — | |
MD5:— | SHA256:— | |||
| 6850 | chrome | /home/user/.config/google-chrome/Default/Local Storage/leveldb/LOG | — | |
MD5:— | SHA256:— | |||
| 6850 | chrome | /.com.google.Chrome.Ggl3kp | — | |
MD5:— | SHA256:— | |||
| 6850 | chrome | /.com.google.Chrome.iogHAK | — | |
MD5:— | SHA256:— | |||
| 6850 | chrome | /home/user/.config/google-chrome/Default/Session Storage/LOG | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
22
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/jflhchccmppkfebkiaminageehmchikm/1.0ab4082a6c03f6150b423a6773f3f740e8098369aa616a68c04c2f0fecc94d2c/1.8a794d870fcd9f730f9ab279e2c72be078de8cf10243f7092181a7a412af6c7a/1bd4975a0b373f929ef3d512c571f7b45fc571a3ae480ddc24f355cb97db6900.puff | unknown | binary | 8.55 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/bxsxfoovuyw4eyyjoshgwgad5u_2024.1.24.0/niikhdgajlphfehepabhhblakbdgeefj_2024.01.24.00_all_acssagqjupmbpecp3w63slfvx7qa.crx3 | unknown | binary | 5.48 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/hfnkpimlhhgieaddgfemjhofmfblmnib/1.d9a6a83725530083e464be150a6ba6d9ee1ba65e3317f7d4b338ad70c8c56780/1.70f09e0a653ea31af7453dc2a5ca85655e727beb924726f38d1703dba8e26eb5/3ce0f16bbbe9cc92dff251fd7c0ea0586b750d88834bfc7edcdc123d1b81a318.puff | unknown | binary | 2.24 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/efniojlnjndmcbiieegkicadnoecjjef/1.c704c4804edba71e46592283238d0edf83ce69f38d63f3b0fa47bdc76084a63c/1.6fcc02a365d39485c49c9da8679a9fd979832315b2d47ff7f0ab395b10e303bd/45684b588524e44a98e130f8b5f5289ae6bb89ea165f6968d1dba18bfb3cce8a.puff | unknown | binary | 2.89 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 216.58.206.35:443 | update.googleapis.com | — | — | unknown |
— | — | 173.194.76.84:443 | accounts.google.com | — | — | unknown |
— | — | 142.250.185.99:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
— | — | 35.204.106.198:80 | wildfire.paloaltonetworks.com | GOOGLE-CLOUD-PLATFORM | NL | unknown |
— | — | 35.204.106.198:443 | wildfire.paloaltonetworks.com | GOOGLE-CLOUD-PLATFORM | NL | unknown |
— | — | 142.250.185.164:443 | www.google.com | — | — | unknown |
— | — | 142.250.181.238:443 | sb-ssl.google.com | GOOGLE | US | unknown |
— | — | 142.250.185.170:443 | optimizationguide-pa.googleapis.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
wildfire.paloaltonetworks.com |
| unknown |
update.googleapis.com |
| whitelisted |
94.100.168.192.in-addr.arpa |
| unknown |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
sb-ssl.l.google.com |
| unknown |
optimizationguide-pa.googleapis.com |
| whitelisted |
connectivity-check.ubuntu.com |
| unknown |