| File name: | F-M-E.exe |
| Full analysis: | https://app.any.run/tasks/bd62bb3f-c7d8-4452-bed5-7ef292c1b879 |
| Verdict: | Malicious activity |
| Analysis date: | November 06, 2023, 15:19:10 |
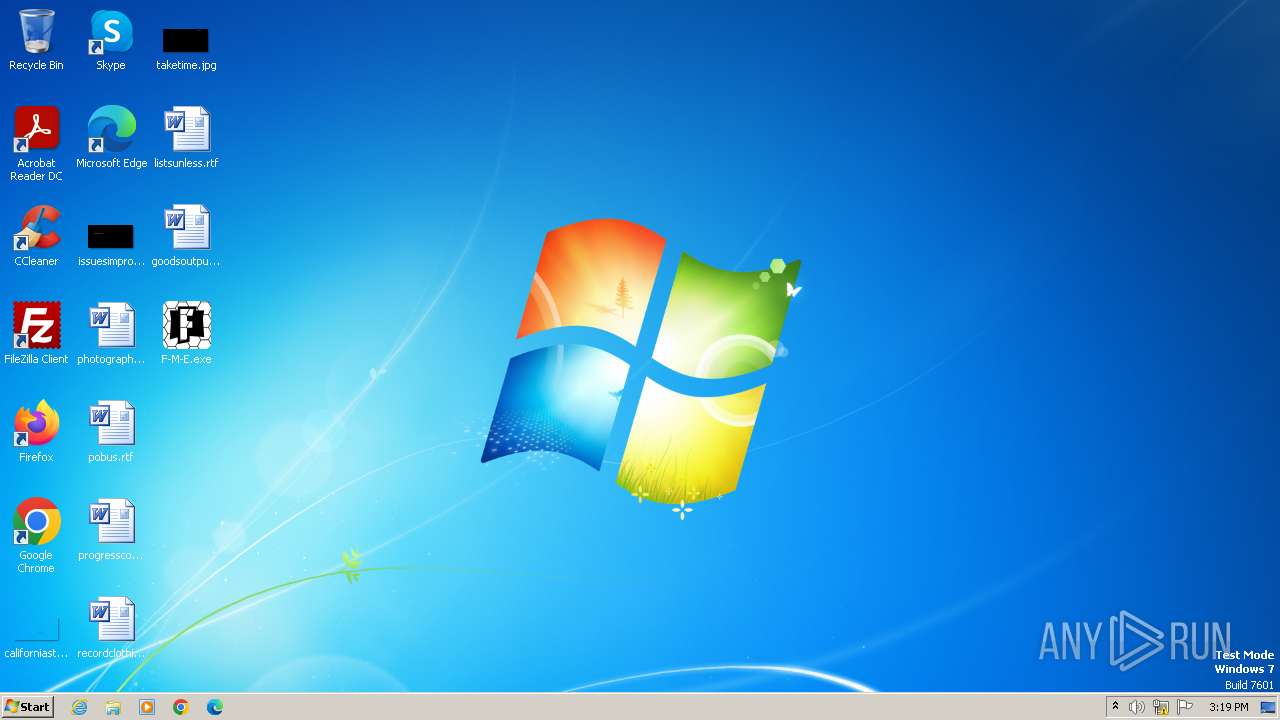
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4EF695F7BE20D8D41A0C597C2D23F9F8 |
| SHA1: | DB7A120B7A9011D172AD789D91FE065F85422AA1 |
| SHA256: | A8C9A71B36BDA8212AB96657EA566E1DF217B09090D75F8F736D0C34A4B6E8C9 |
| SSDEEP: | 49152:OwUtZYu8qyjLJATzoYqDnM7bJKLlJ7PwHZC3gBb8+kw2aDtuKs2Lzex7SWZb/CEa:OwU/YTRLJAT0jMZKBJ7PCIl+7JtPs2LL |
MALICIOUS
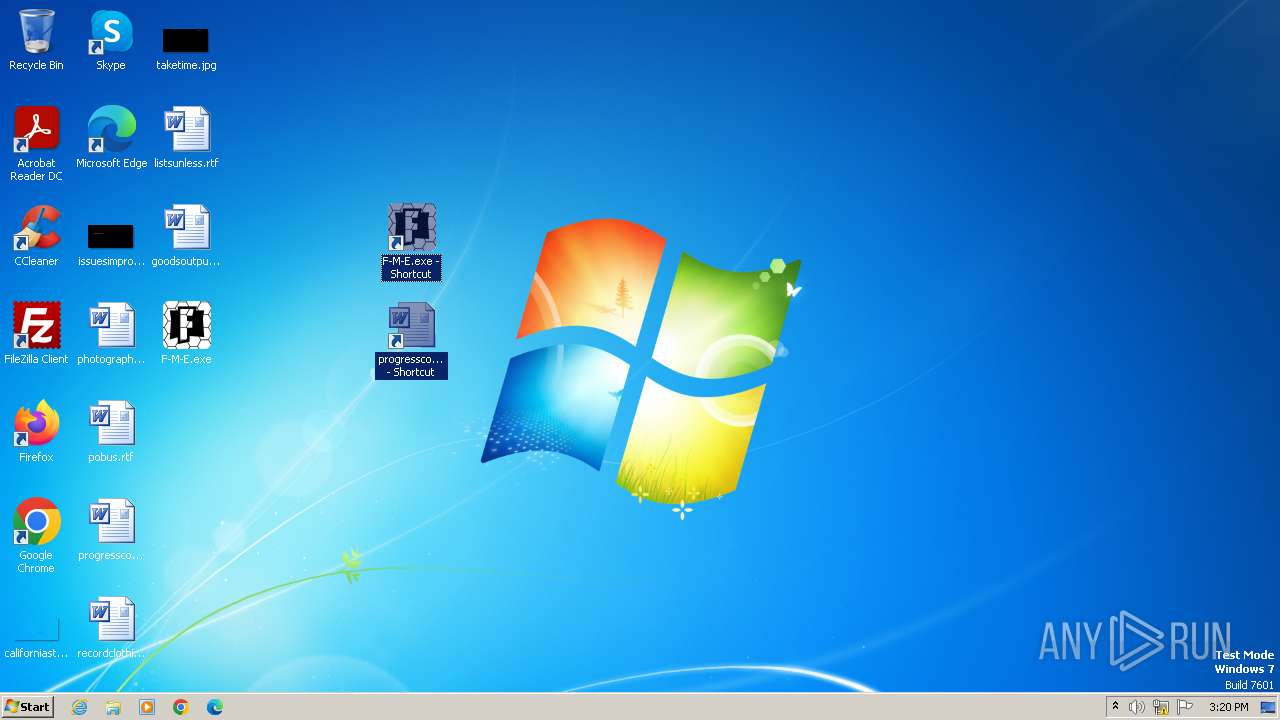
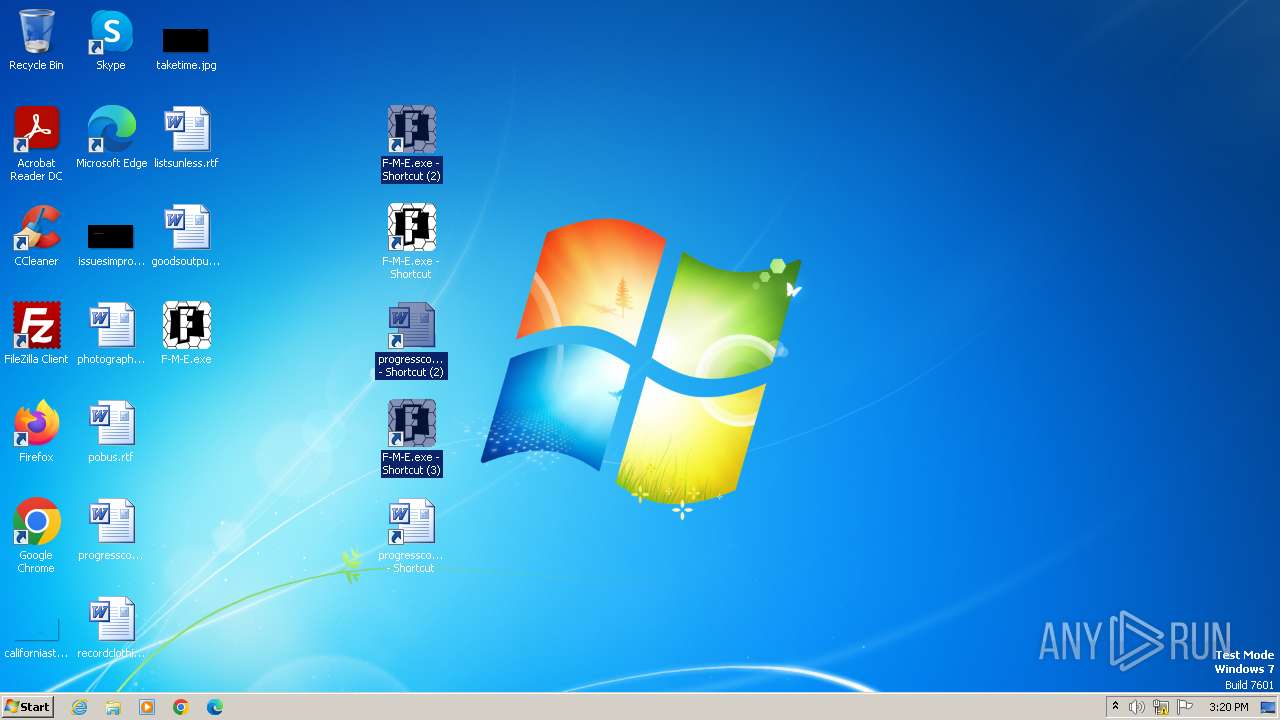
Drops the executable file immediately after the start
- F-M-E.exe (PID: 3484)
- u0Y4DfNbjZAQ4PNg6NB5.exe (PID: 3656)
- F-M-E.exe (PID: 4020)
- u0Y4DfNbjZAQ4PNg6NB5.exe (PID: 4068)
SUSPICIOUS
Reads the Internet Settings
- F-M-E.exe (PID: 3484)
- F-M-E.exe (PID: 4020)
- WMIC.exe (PID: 4056)
- WMIC.exe (PID: 3468)
Drops 7-zip archiver for unpacking
- xcopy.exe (PID: 3688)
- F-M-E.exe (PID: 3484)
- F-M-E.exe (PID: 4020)
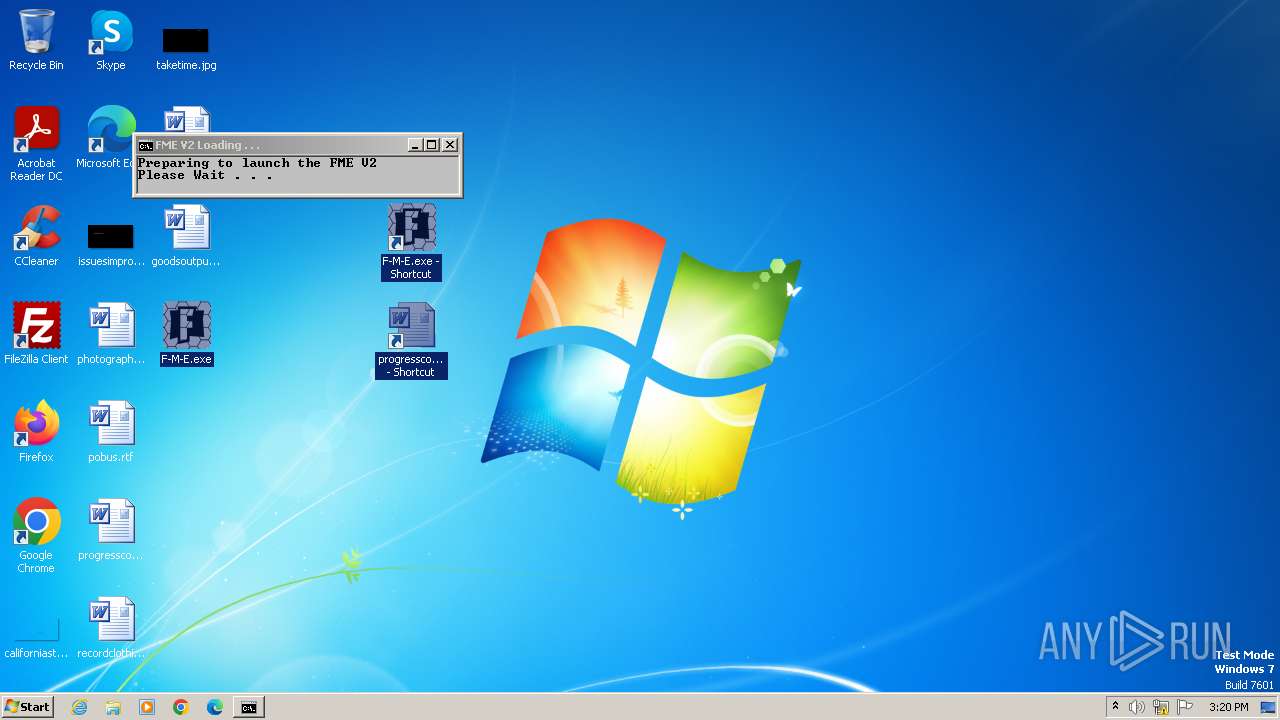
Starts CMD.EXE for commands execution
- F-M-E.exe (PID: 3484)
- F-M-E.exe (PID: 4020)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 3164)
Executing commands from a ".bat" file
- F-M-E.exe (PID: 3484)
- cmd.exe (PID: 3164)
- F-M-E.exe (PID: 4020)
- cmd.exe (PID: 3976)
Application launched itself
- cmd.exe (PID: 3164)
- cmd.exe (PID: 3976)
Uses WMIC.EXE to obtain data on processes
- cmd.exe (PID: 2424)
- cmd.exe (PID: 3956)
Get information on the list of running processes
- cmd.exe (PID: 3164)
- cmd.exe (PID: 3976)
INFO
Create files in a temporary directory
- F-M-E.exe (PID: 3484)
- u0Y4DfNbjZAQ4PNg6NB5.exe (PID: 3656)
- F-M-E.exe (PID: 4020)
- xcopy.exe (PID: 3684)
- u0Y4DfNbjZAQ4PNg6NB5.exe (PID: 4068)
- xcopy.exe (PID: 3688)
Checks supported languages
- F-M-E.exe (PID: 3484)
- mode.com (PID: 3508)
- F-M-E.exe (PID: 4020)
- mode.com (PID: 4076)
- u0Y4DfNbjZAQ4PNg6NB5.exe (PID: 4068)
- u0Y4DfNbjZAQ4PNg6NB5.exe (PID: 3656)
Reads the computer name
- F-M-E.exe (PID: 3484)
- F-M-E.exe (PID: 4020)
- u0Y4DfNbjZAQ4PNg6NB5.exe (PID: 3656)
- u0Y4DfNbjZAQ4PNg6NB5.exe (PID: 4068)
Manual execution by a user
- F-M-E.exe (PID: 4020)
Drops the executable file immediately after the start
- xcopy.exe (PID: 3688)
The executable file from the user directory is run by the CMD process
- u0Y4DfNbjZAQ4PNg6NB5.exe (PID: 4068)
- u0Y4DfNbjZAQ4PNg6NB5.exe (PID: 3656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:21 17:00:00+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 104448 |
| InitializedDataSize: | 50688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1910c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.0.0.0 |
| ProductVersionNumber: | 19.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Fortnite Macros Editor |
| FileDescription: | FME |
| FileVersion: | 1 |
| InternalName: | FME.sfx |
| LegalCopyright: | Copyright (c) 2019-2022 FME |
| OriginalFileName: | FME.exe |
| ProductName: | FME |
| ProductVersion: | 1 |
Total processes
57
Monitored processes
18
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2424 | C:\Windows\system32\cmd.exe /c wmic process where "name='cmd.exe' and commandline like '%run.bat%'" get processid | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3164 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\7zSC9D9D646\run.bat" x -pZhd2kZSak8js u0Y4DfNbjZAQ4PNg6NB5 -o. -y AsDxzcDAzSDzdD 862536370979602452" | C:\Windows\System32\cmd.exe | — | F-M-E.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3468 | wmic process where "name='cmd.exe' and commandline like '%run.bat%'" get processid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3484 | "C:\Users\admin\Desktop\F-M-E.exe" | C:\Users\admin\Desktop\F-M-E.exe | — | explorer.exe | |||||||||||
User: admin Company: Fortnite Macros Editor Integrity Level: MEDIUM Description: FME Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3488 | find /i "name.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3508 | mode con: cols=40 lines=3 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3516 | tasklist /fi "imagename eq name.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3592 | find /i "name.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3656 | u0Y4DfNbjZAQ4PNg6NB5.exe x -pZhd2kZSak8js u0Y4DfNbjZAQ4PNg6NB5 -o. -y | C:\Users\admin\AppData\Local\Temp\u0Y4DfNbjZAQ4PNg6NB5.exe | — | cmd.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Reduced Standalone Console Exit code: 0 Version: 23.01 Modules
| |||||||||||||||
| 3676 | tasklist /fi "imagename eq name.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 810
Read events
1 794
Write events
16
Delete events
0
Modification events
| (PID) Process: | (3484) F-M-E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3484) F-M-E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3484) F-M-E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3484) F-M-E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4020) F-M-E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4020) F-M-E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4020) F-M-E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4020) F-M-E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
5
Suspicious files
2
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3656 | u0Y4DfNbjZAQ4PNg6NB5.exe | C:\Users\admin\AppData\Local\Temp\AsDxzcDAzSDzdD | — | |
MD5:— | SHA256:— | |||
| 4068 | u0Y4DfNbjZAQ4PNg6NB5.exe | C:\Users\admin\AppData\Local\Temp\AsDxzcDAzSDzdD | — | |
MD5:— | SHA256:— | |||
| 3688 | xcopy.exe | C:\Users\admin\AppData\Local\Temp\u0Y4DfNbjZAQ4PNg6NB5 | — | |
MD5:F795A689FAE22D85A663A0CEC6B04EDD | SHA256:630BADF7CCAC90BFC0A38D823154A816C1838D2F72B13F6486C89AC506BE331C | |||
| 3656 | u0Y4DfNbjZAQ4PNg6NB5.exe | C:\Users\admin\AppData\Local\Temp\name.exe | executable | |
MD5:7A906783000136E751744C80048600E7 | SHA256:83B9A6831948CF3217D05461269D937E53DB02391B3F30EBD25283272001174D | |||
| 3688 | xcopy.exe | C:\Users\admin\AppData\Local\Temp\u0Y4DfNbjZAQ4PNg6NB5.exe | executable | |
MD5:1F7B03F055CDFBFE54F6AE96E52119D6 | SHA256:40BC7B7150E23880FD35FF98301D7D1A8FD28A047E07EC1B9D7C1680806828EE | |||
| 3484 | F-M-E.exe | C:\Users\admin\AppData\Local\Temp\7zSC9D9D646\u0Y4DfNbjZAQ4PNg6NB5 | compressed | |
MD5:F795A689FAE22D85A663A0CEC6B04EDD | SHA256:630BADF7CCAC90BFC0A38D823154A816C1838D2F72B13F6486C89AC506BE331C | |||
| 3684 | xcopy.exe | C:\Users\admin\AppData\Local\Temp\run.bat | text | |
MD5:B4226B490A1D93CF99C2C9CBC7C0DAC2 | SHA256:643A6A83E0E87EDC5296CD499D3DC4E562E02B32B5C510E311073BDF35521347 | |||
| 3688 | xcopy.exe | C:\Users\admin\AppData\Local\Temp\run.bat | text | |
MD5:B4226B490A1D93CF99C2C9CBC7C0DAC2 | SHA256:643A6A83E0E87EDC5296CD499D3DC4E562E02B32B5C510E311073BDF35521347 | |||
| 4068 | u0Y4DfNbjZAQ4PNg6NB5.exe | C:\Users\admin\AppData\Local\Temp\name.exe | executable | |
MD5:7A906783000136E751744C80048600E7 | SHA256:83B9A6831948CF3217D05461269D937E53DB02391B3F30EBD25283272001174D | |||
| 4020 | F-M-E.exe | C:\Users\admin\AppData\Local\Temp\7zS4BF75277\u0Y4DfNbjZAQ4PNg6NB5 | compressed | |
MD5:F795A689FAE22D85A663A0CEC6B04EDD | SHA256:630BADF7CCAC90BFC0A38D823154A816C1838D2F72B13F6486C89AC506BE331C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
10
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
868 | svchost.exe | 95.101.148.135:80 | — | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
armmf.adobe.com |
| unknown |
dns.msftncsi.com |
| unknown |