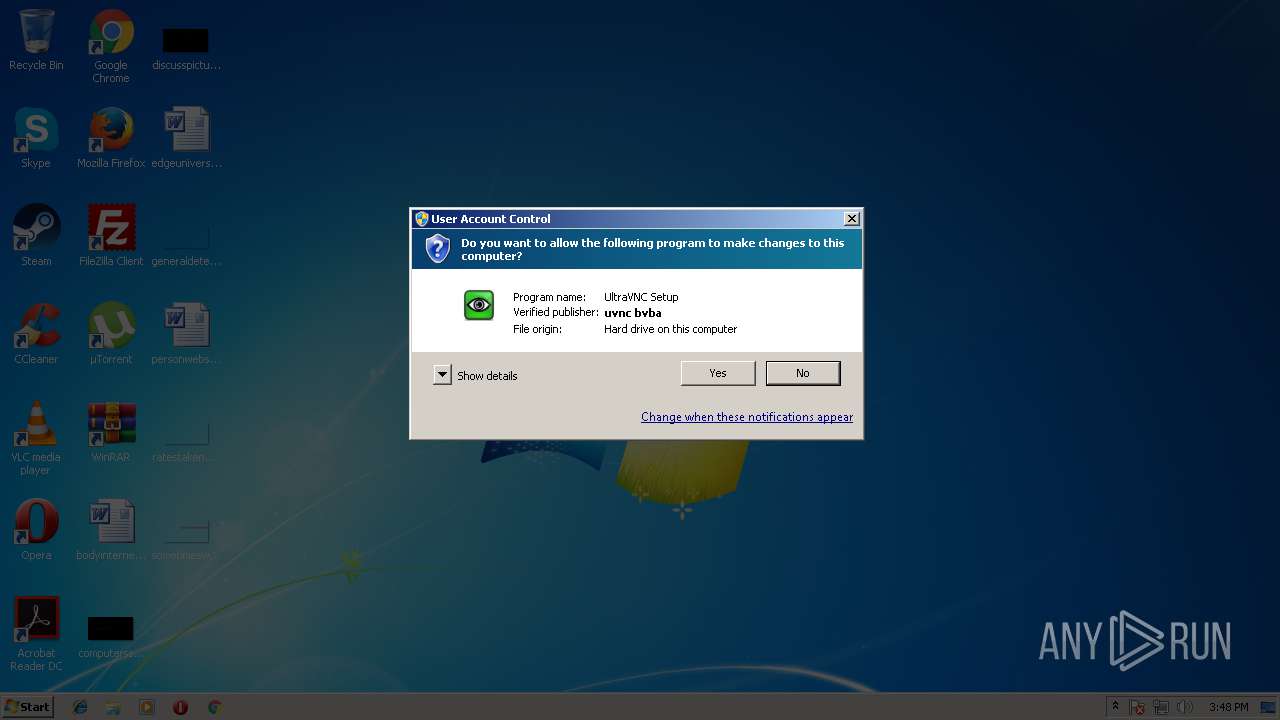
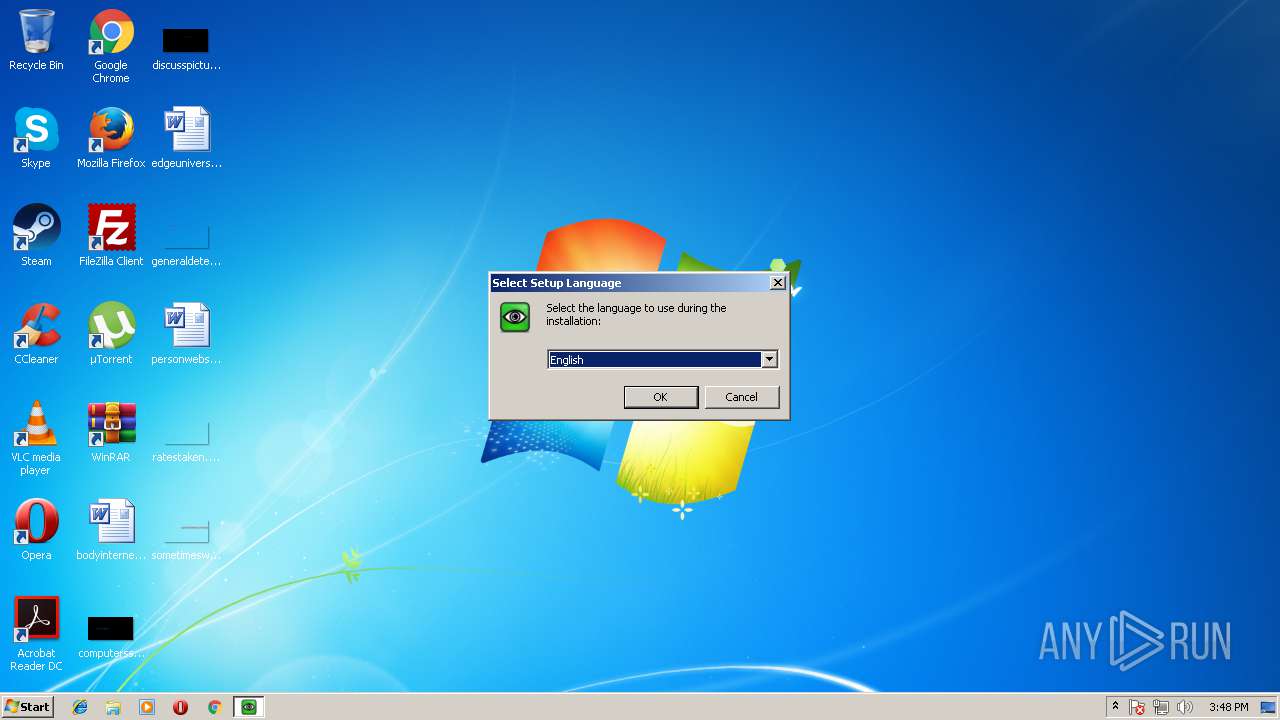
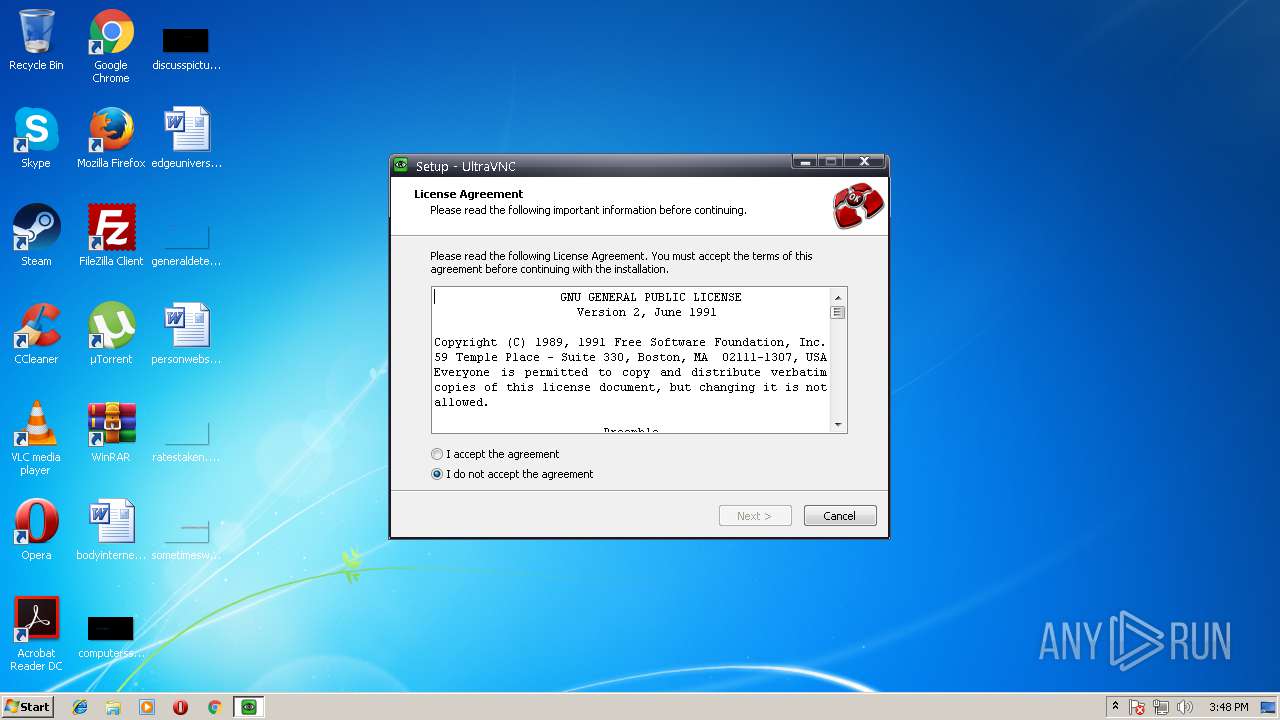
| File name: | UltraVNC_1_2_22_X86_Setup.exe |
| Full analysis: | https://app.any.run/tasks/b65688a4-463c-4e4b-9d9c-a72e5632642e |
| Verdict: | Malicious activity |
| Analysis date: | August 23, 2018, 14:47:31 |
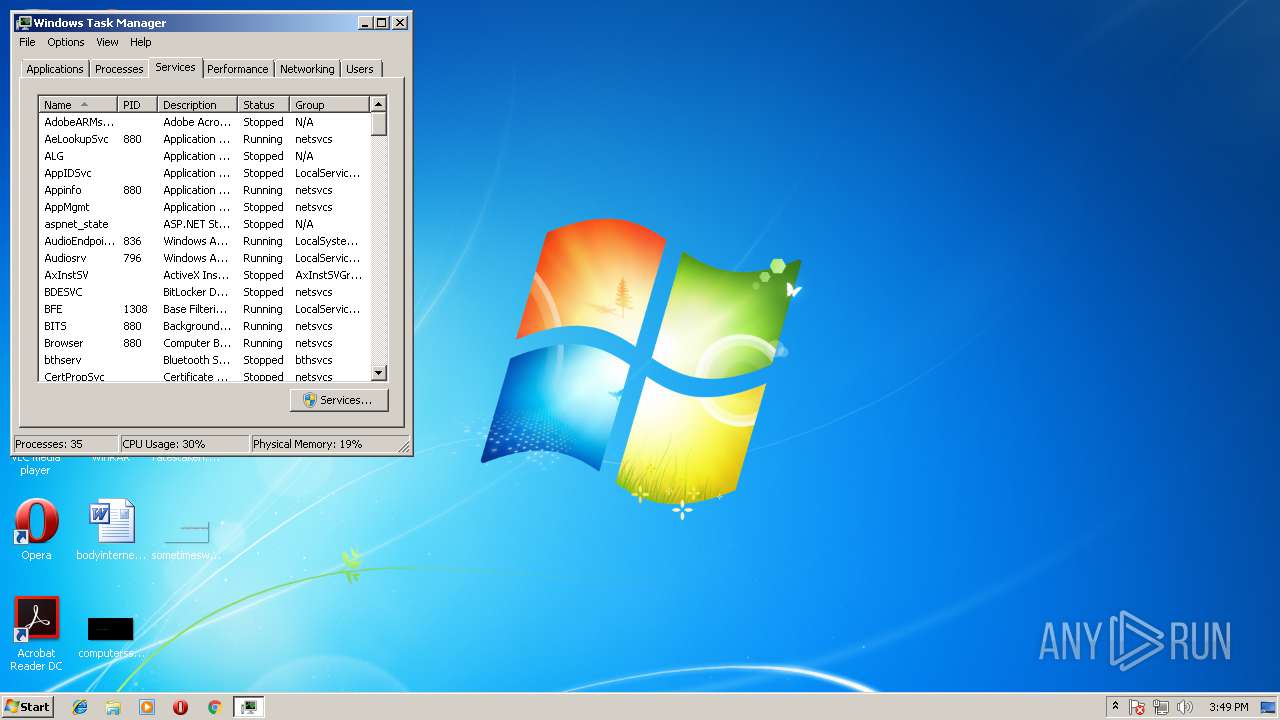
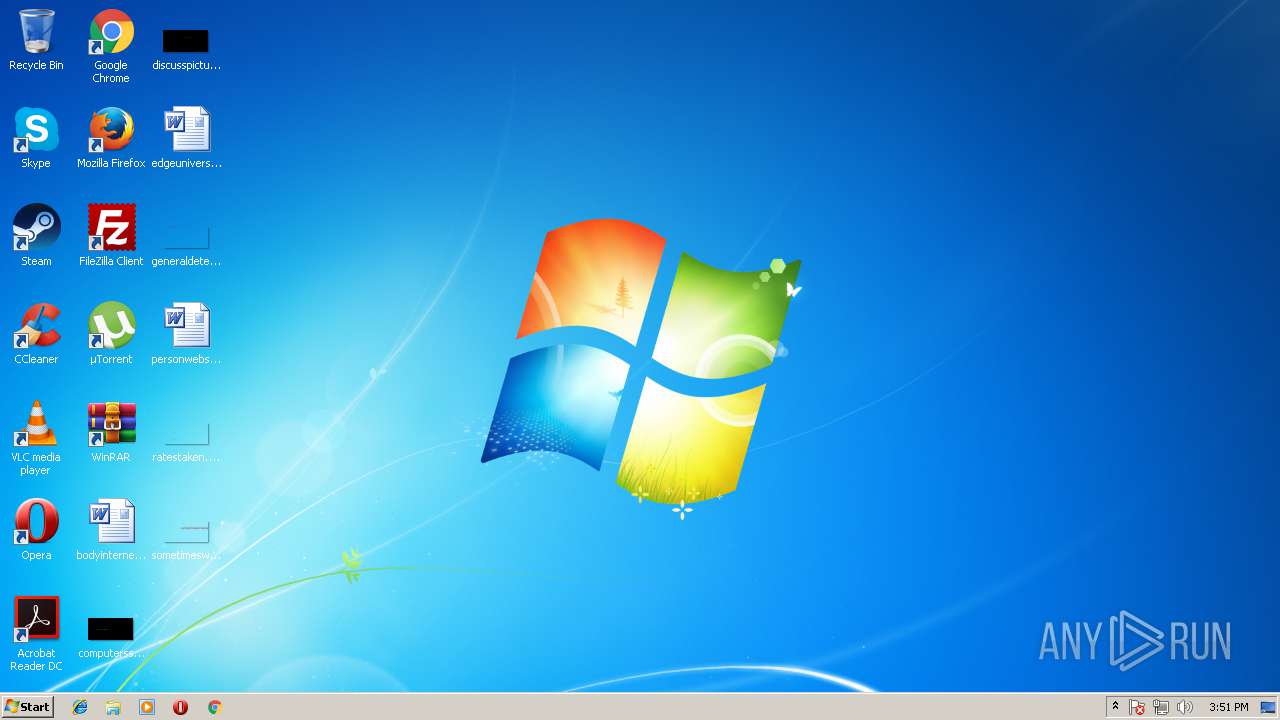
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5F5357C762045E192138C77F77C1FC66 |
| SHA1: | 9F61FCD32EE1781F7102DAE0397FD46D9F09D35F |
| SHA256: | A8BFBB9E2514E9DCB438FC7740E1A6D6055EDE0EEA6ED9A13386523F568B8B4E |
| SSDEEP: | 49152:R75tM5lYmO+X5TAju29INW+4Weij8ka2XEpWBxzPYyqO46R8EhEpqsRk0Tk:p5rD+X5cpXcjO20pAxzZ74EhEgsRM |
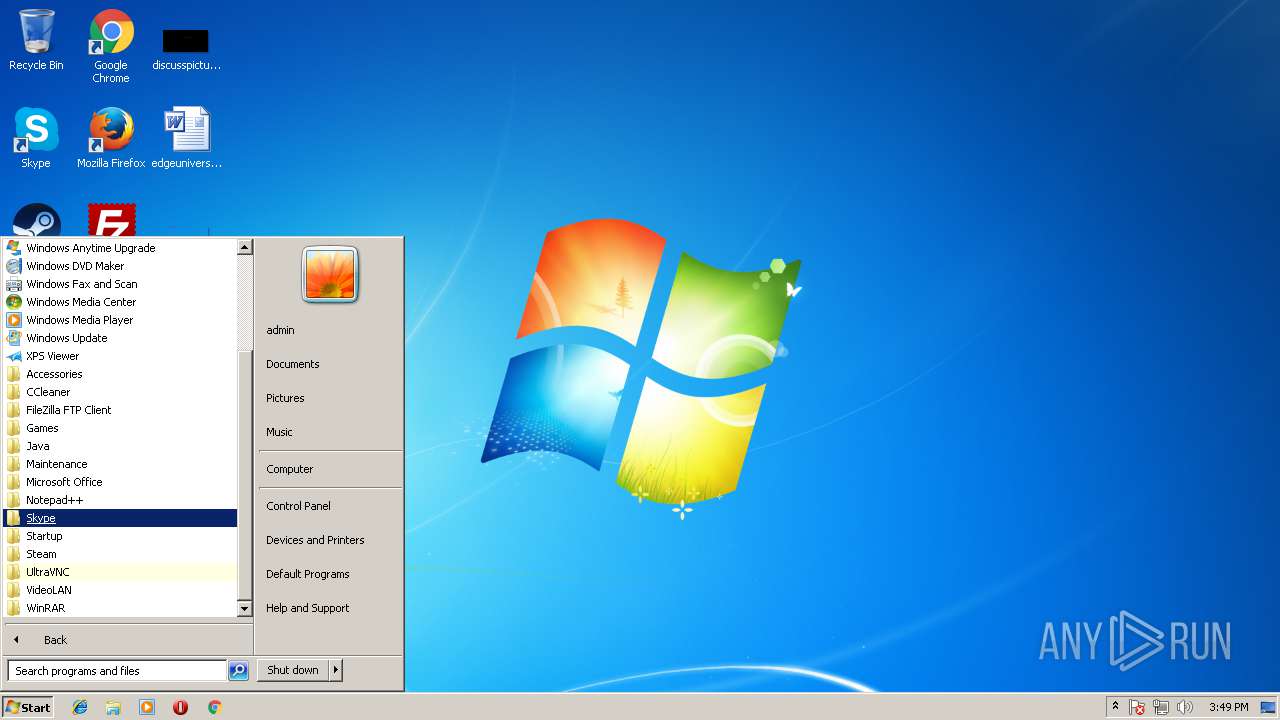
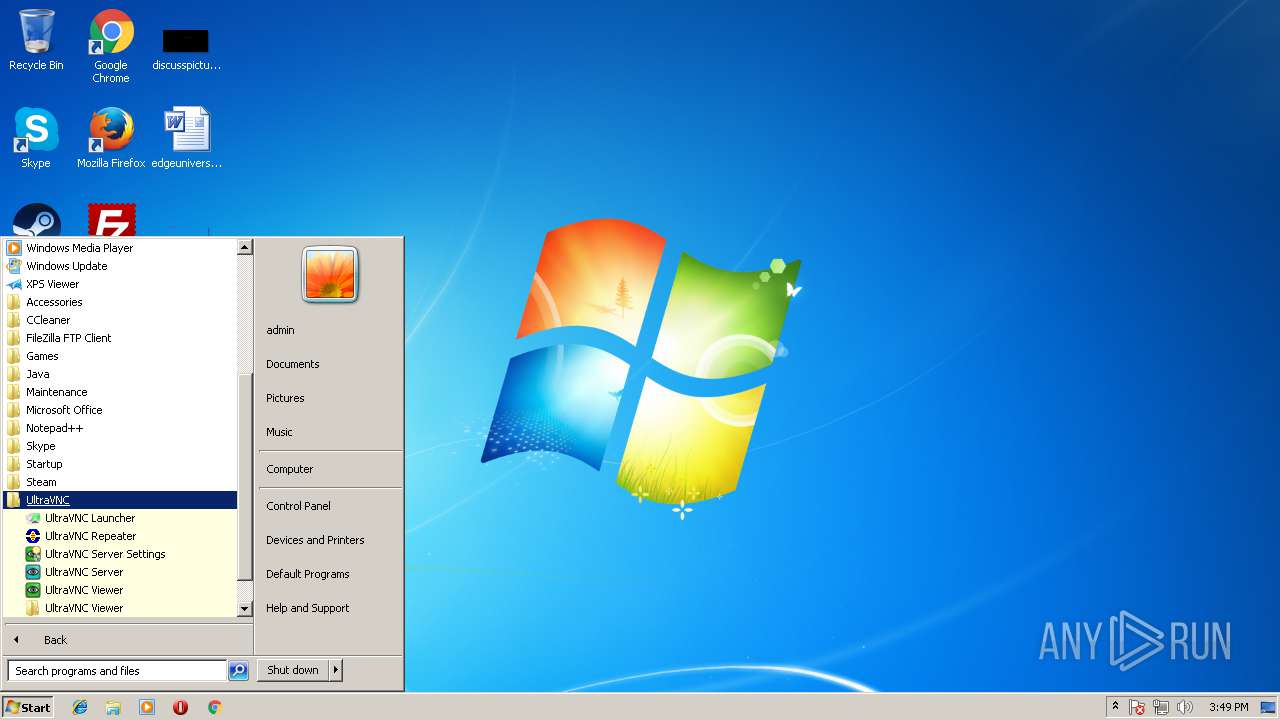
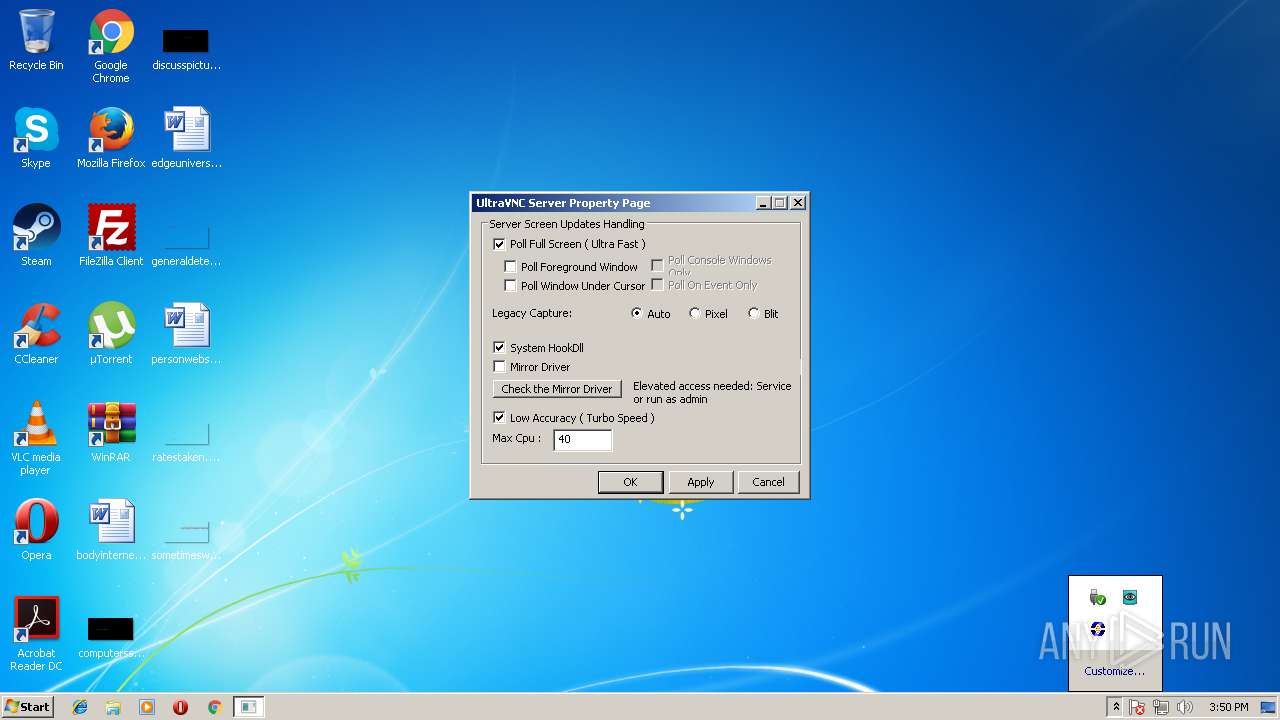
MALICIOUS
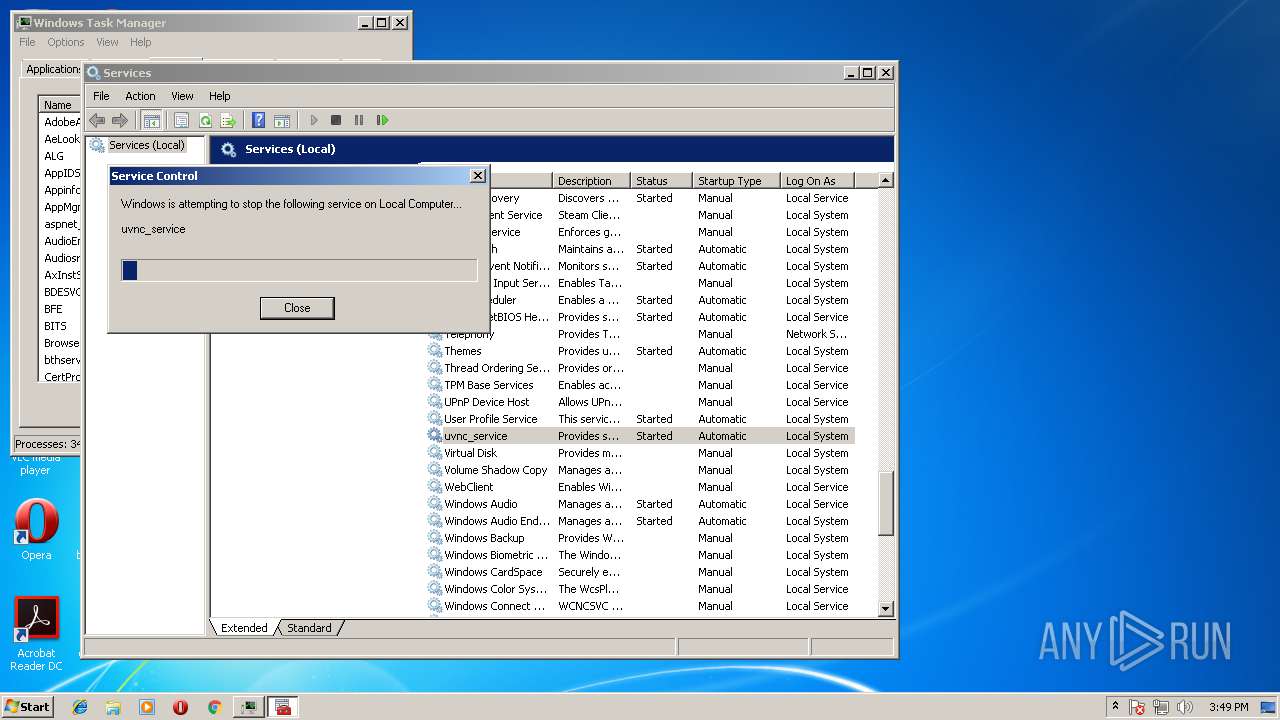
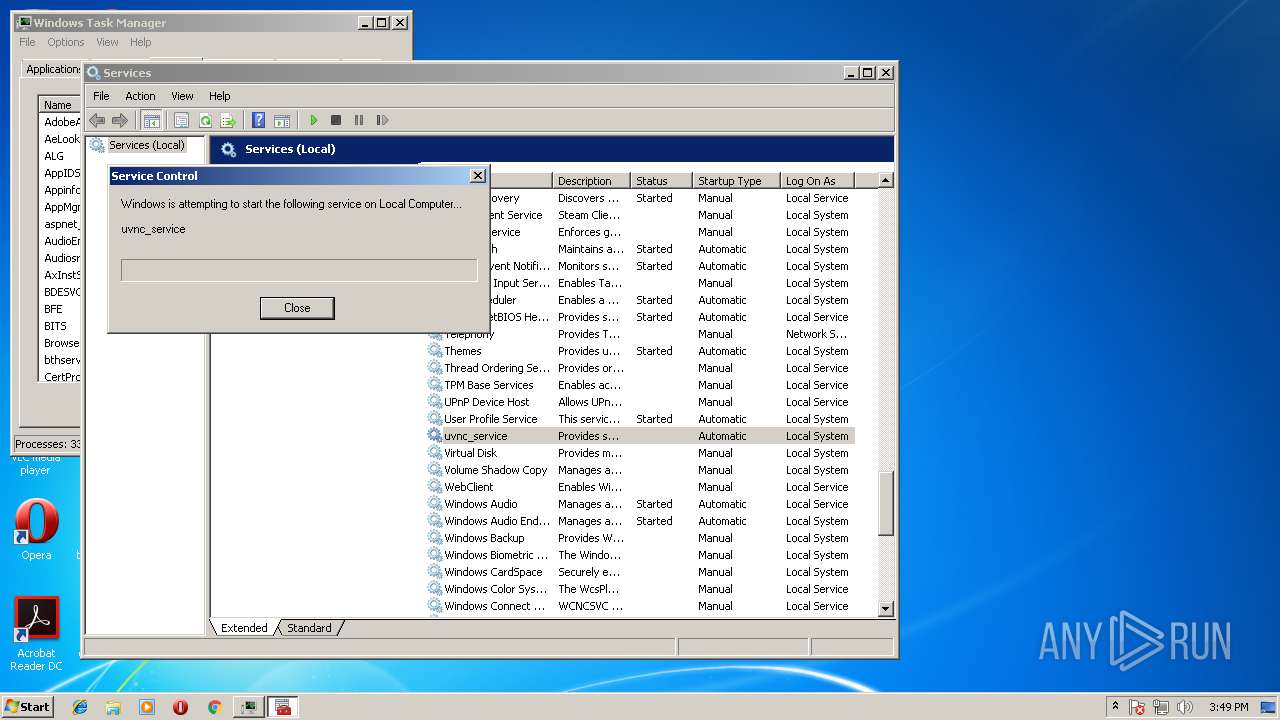
Starts NET.EXE for service management
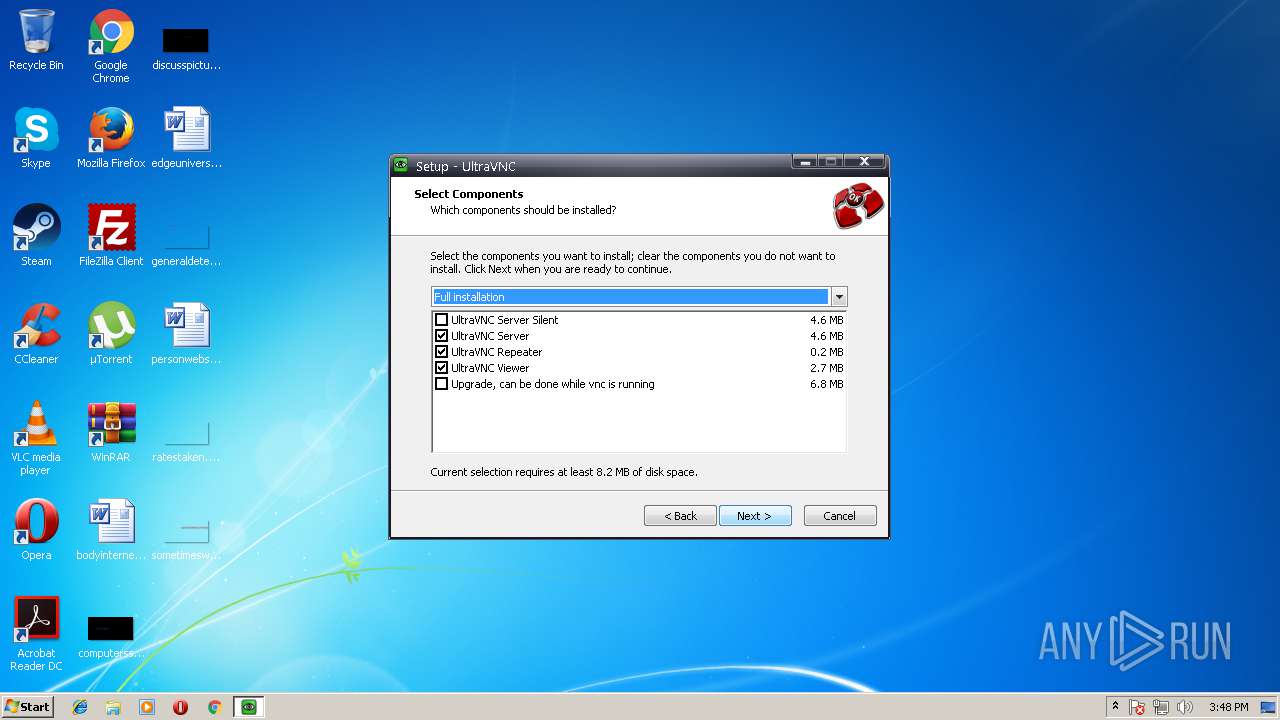
- WinVNC.exe (PID: 3152)
- UltraVNC_1_2_22_X86_Setup.tmp (PID: 3856)
Application was dropped or rewritten from another process
- WinVNC.exe (PID: 3152)
- setpasswd.exe (PID: 3092)
- WinVNC.exe (PID: 1068)
- setcad.exe (PID: 3376)
- WinVNC.exe (PID: 3812)
- repeater.exe (PID: 2180)
- WinVNC.exe (PID: 3440)
- WinVNC.exe (PID: 2860)
- winvnc.exe (PID: 3732)
- WinVNC.exe (PID: 3880)
- WinVNC.exe (PID: 344)
- vncviewer.exe (PID: 1552)
- WinVNC.exe (PID: 2988)
- WinVNC.exe (PID: 2432)
- WinVNC.exe (PID: 3628)
Loads dropped or rewritten executable
- WinVNC.exe (PID: 2860)
- explorer.exe (PID: 1380)
- repeater.exe (PID: 2180)
- vncviewer.exe (PID: 1552)
SUSPICIOUS
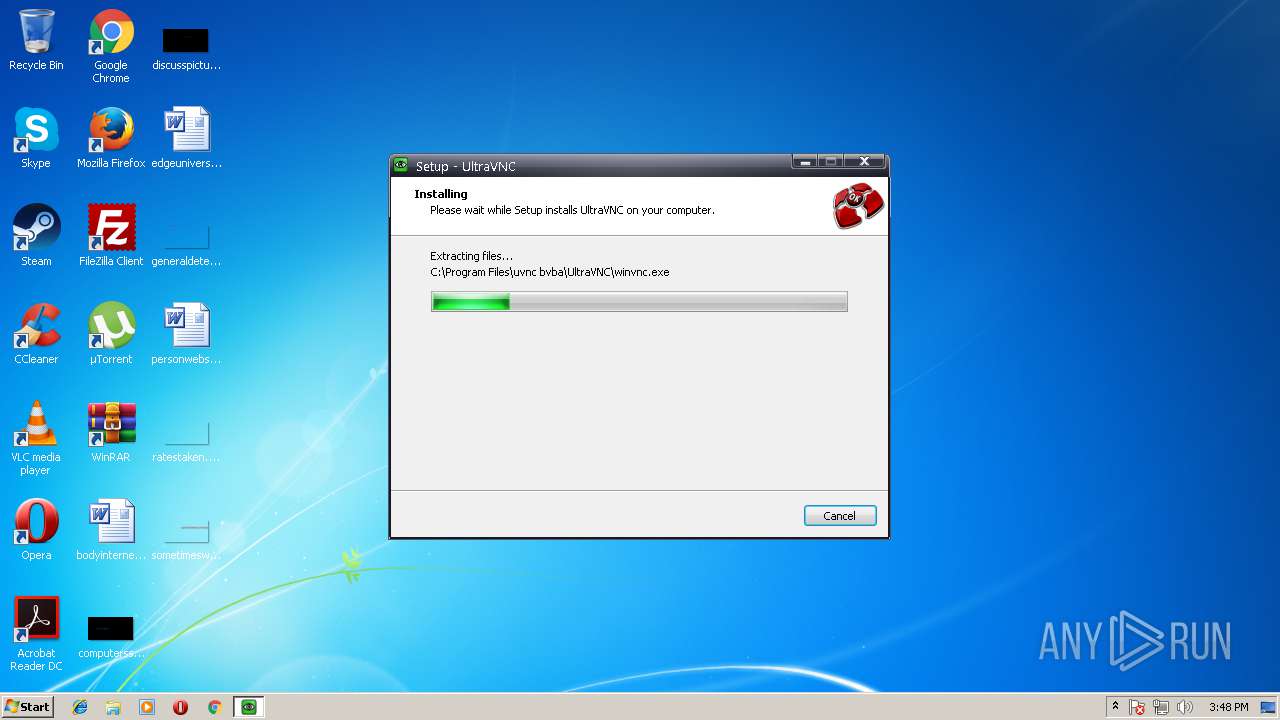
Executable content was dropped or overwritten
- UltraVNC_1_2_22_X86_Setup.exe (PID: 3520)
- UltraVNC_1_2_22_X86_Setup.exe (PID: 3724)
- UltraVNC_1_2_22_X86_Setup.tmp (PID: 3856)
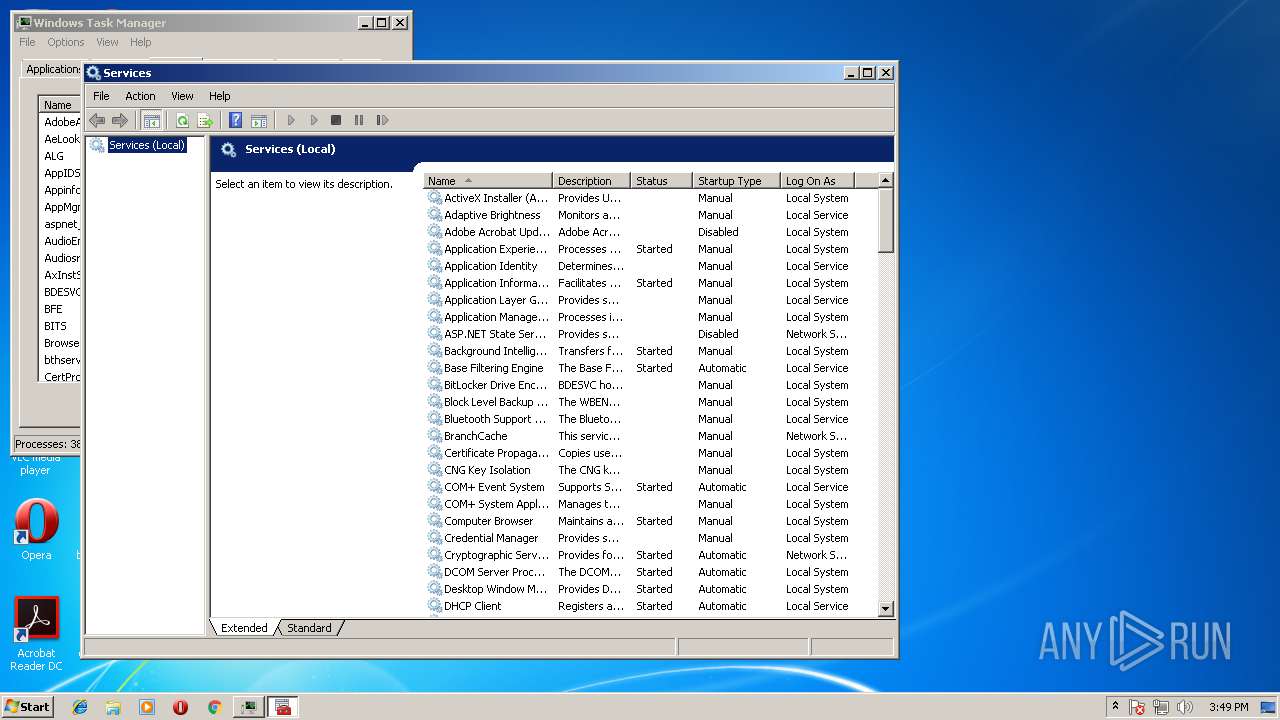
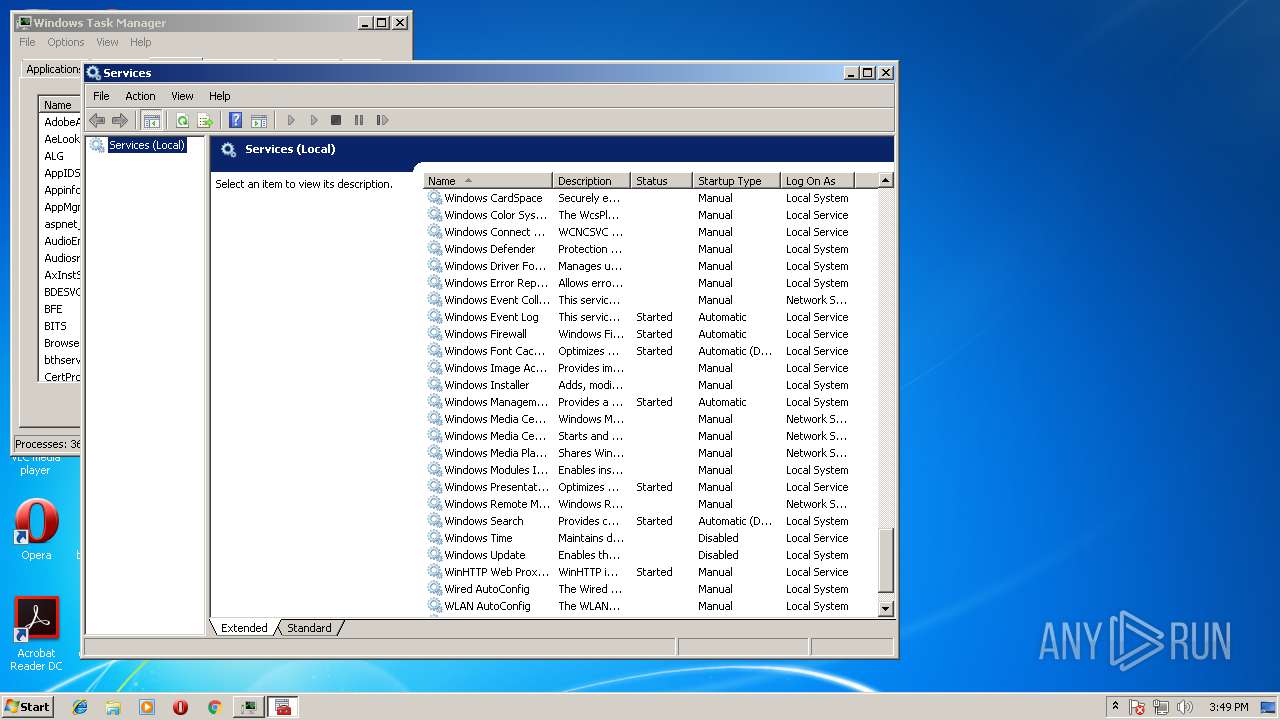
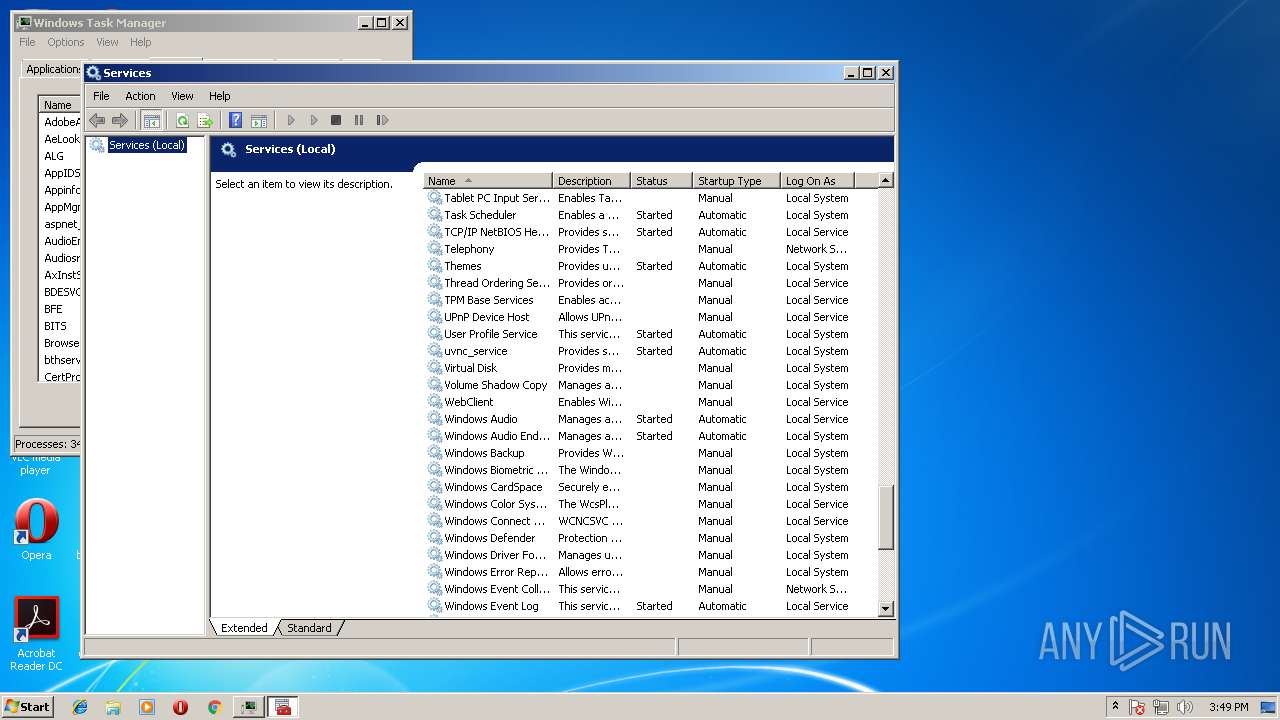
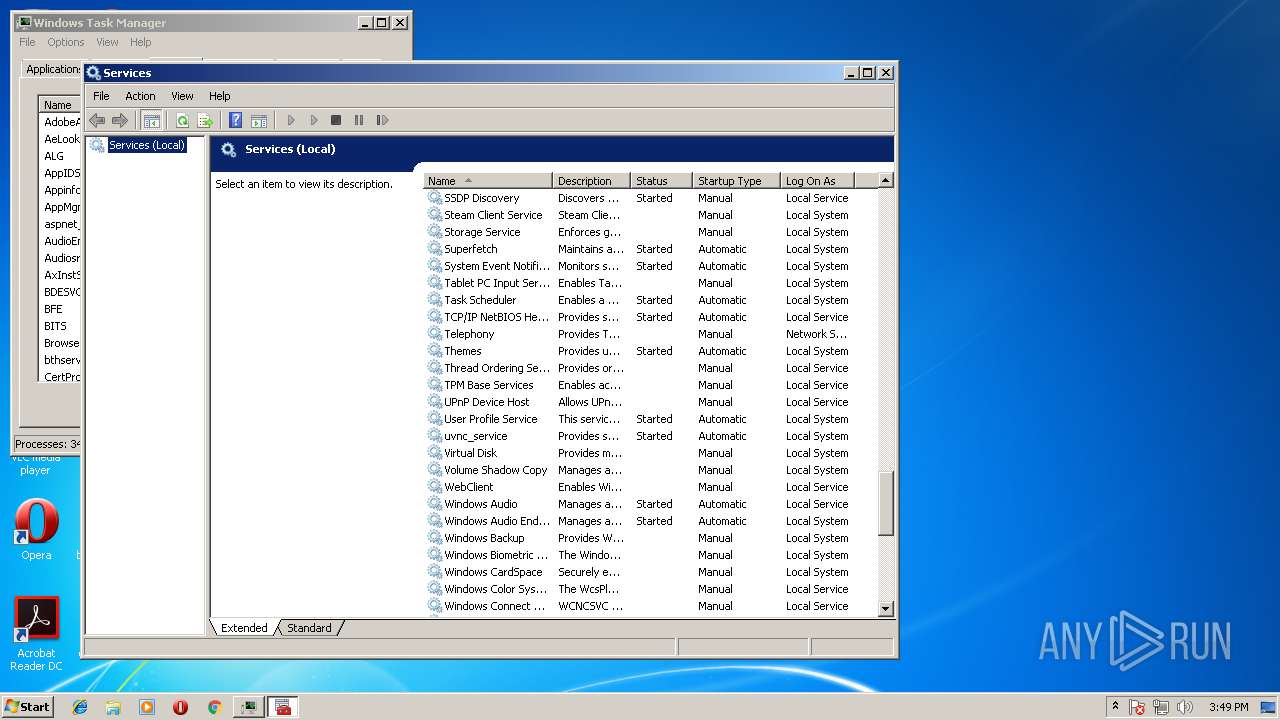
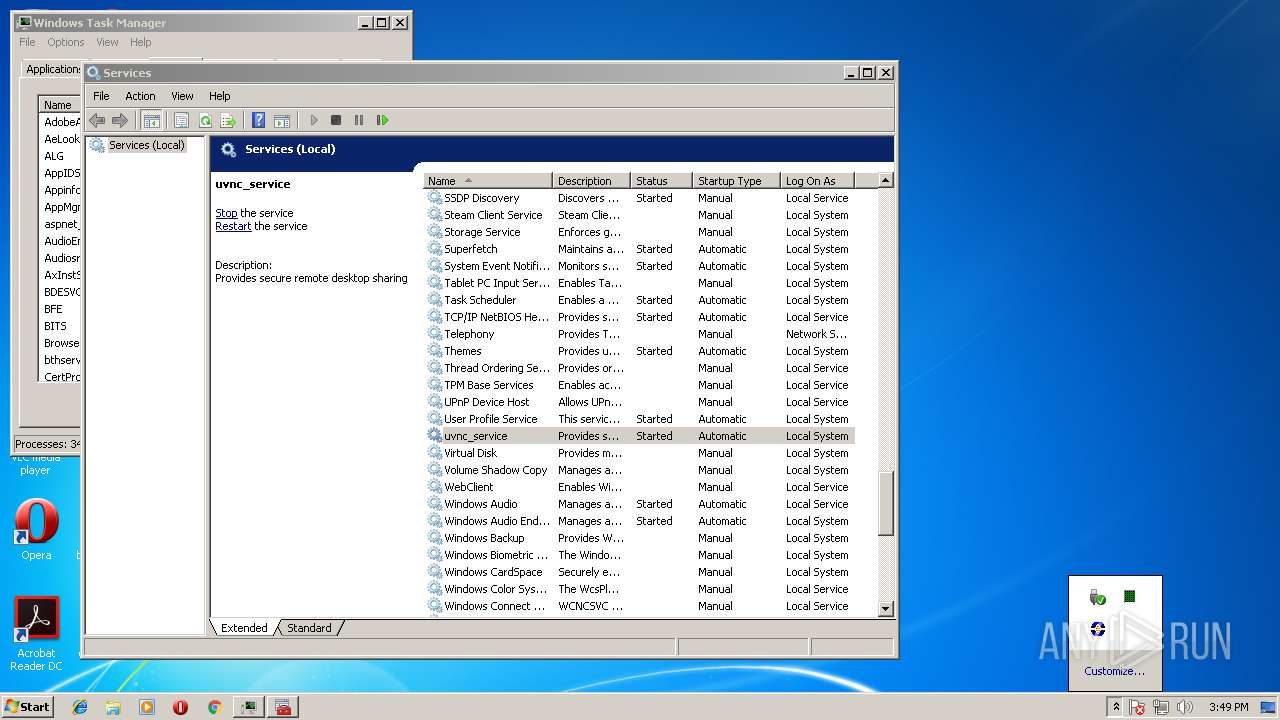
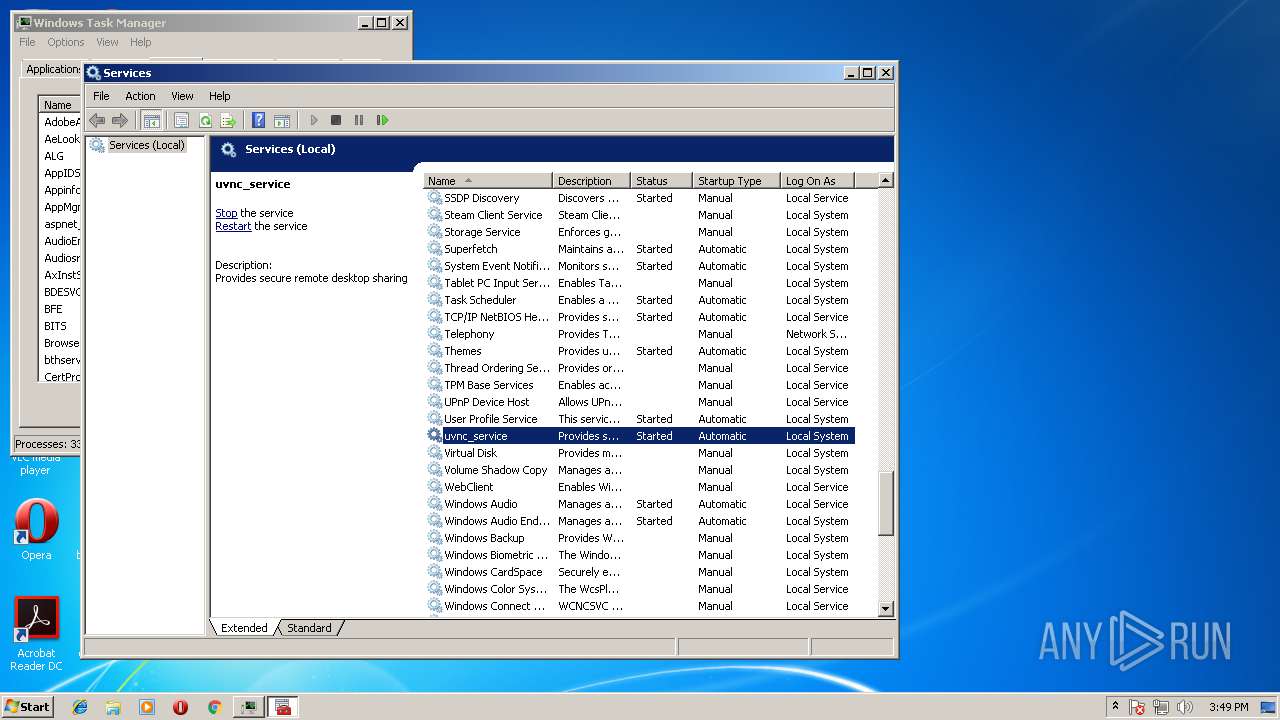
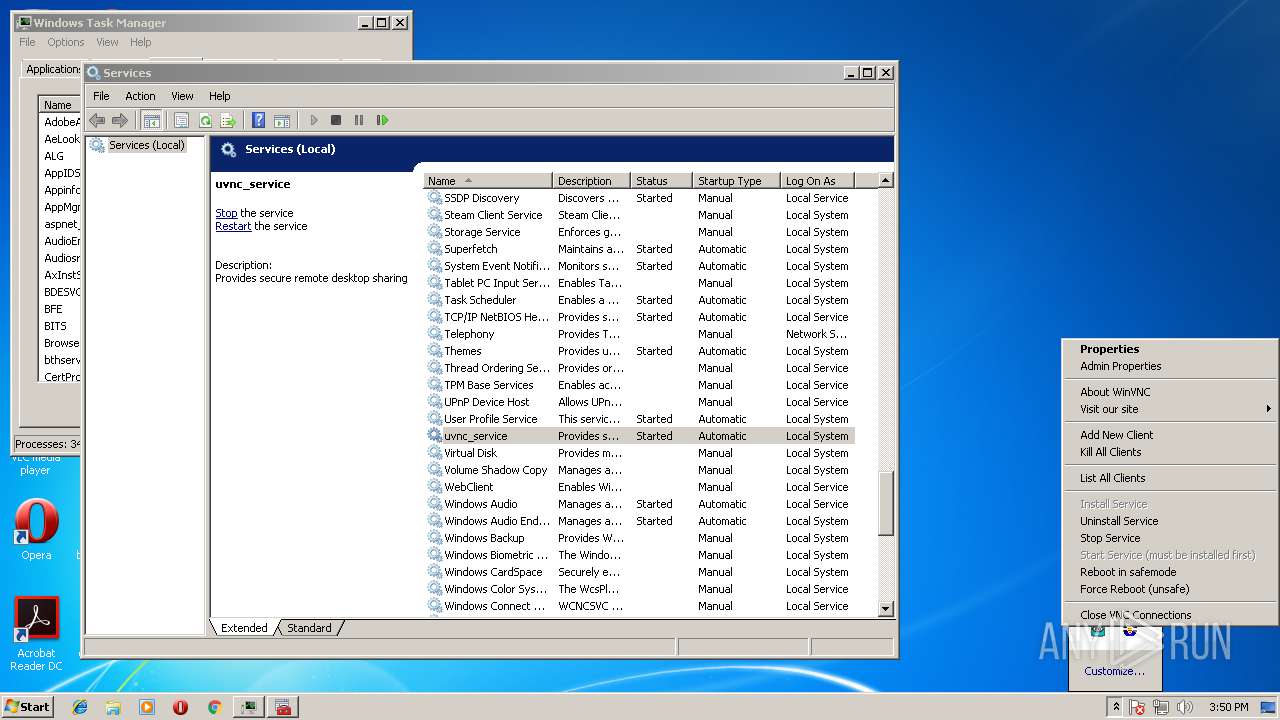
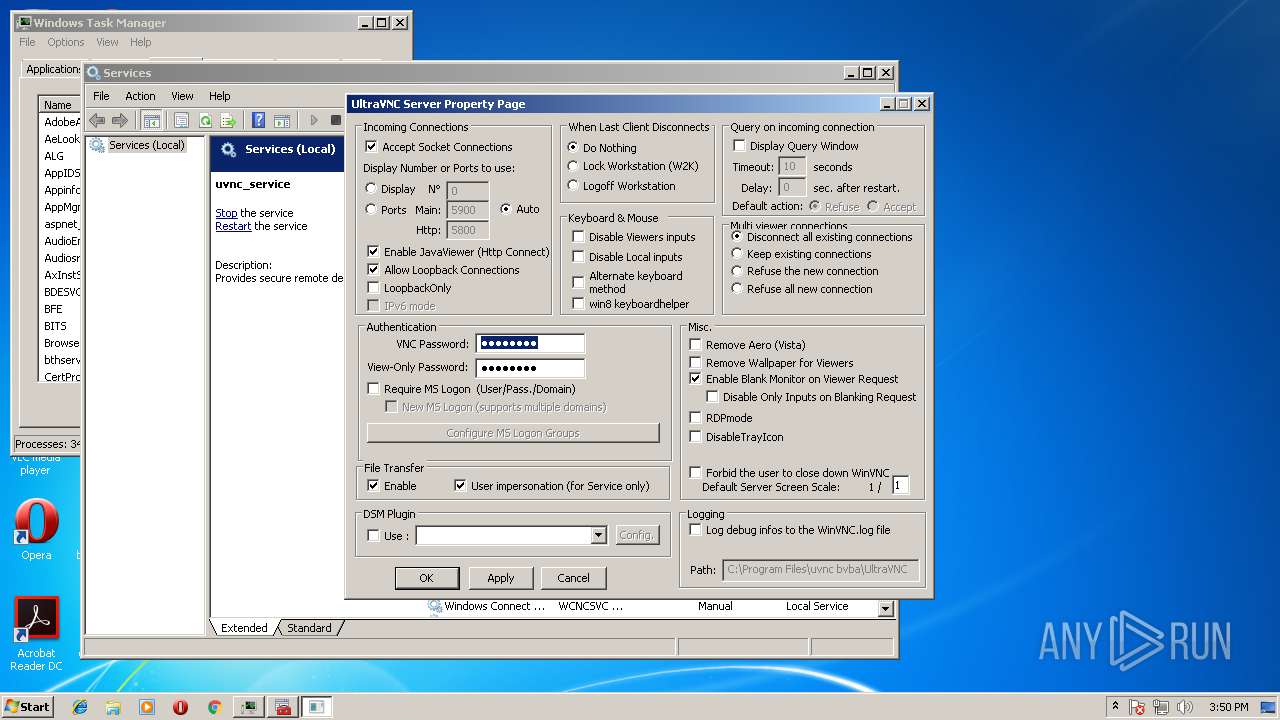
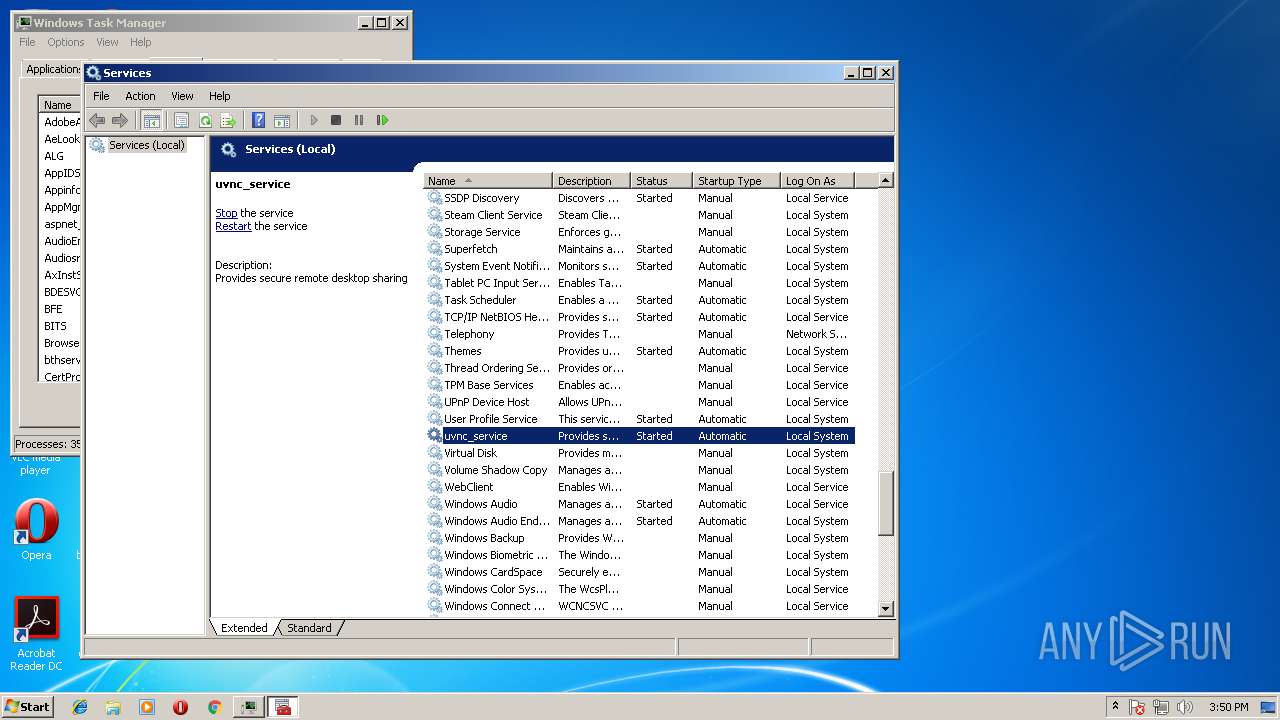
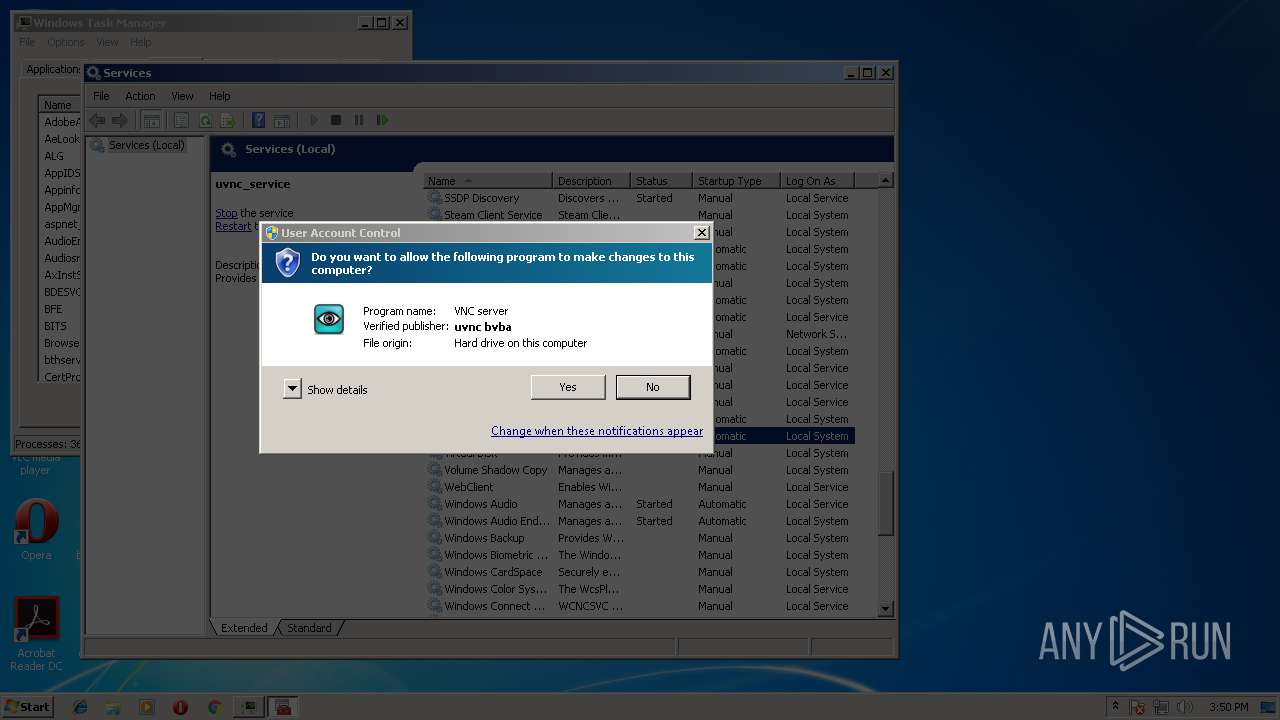
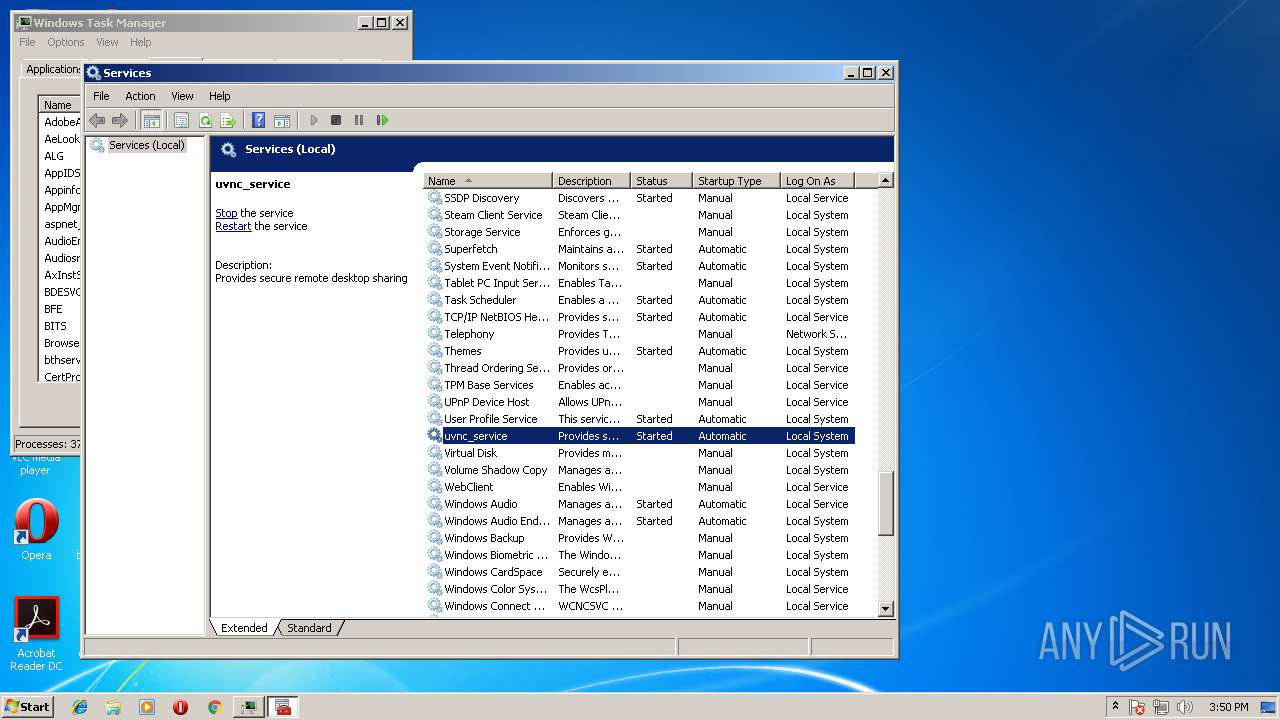
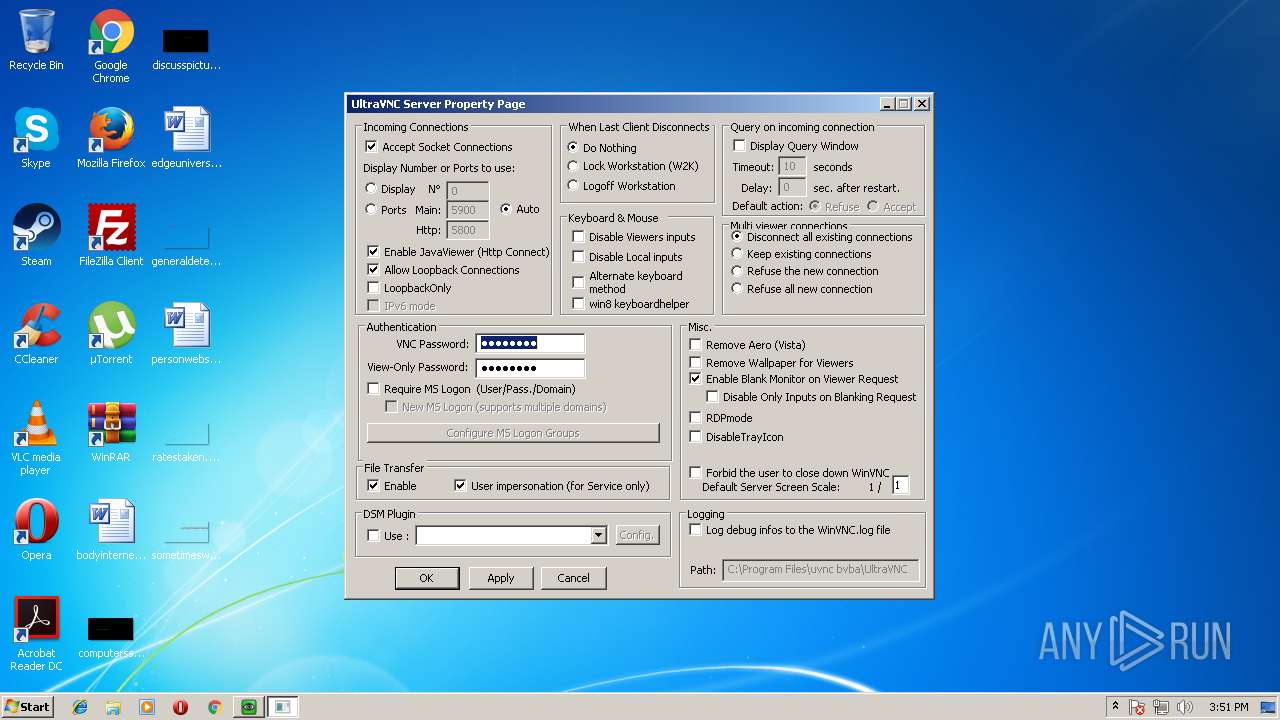
Creates or modifies windows services
- WinVNC.exe (PID: 3152)
- WinVNC.exe (PID: 2860)
Uses NETSH.EXE for network configuration
- UltraVNC_1_2_22_X86_Setup.tmp (PID: 3856)
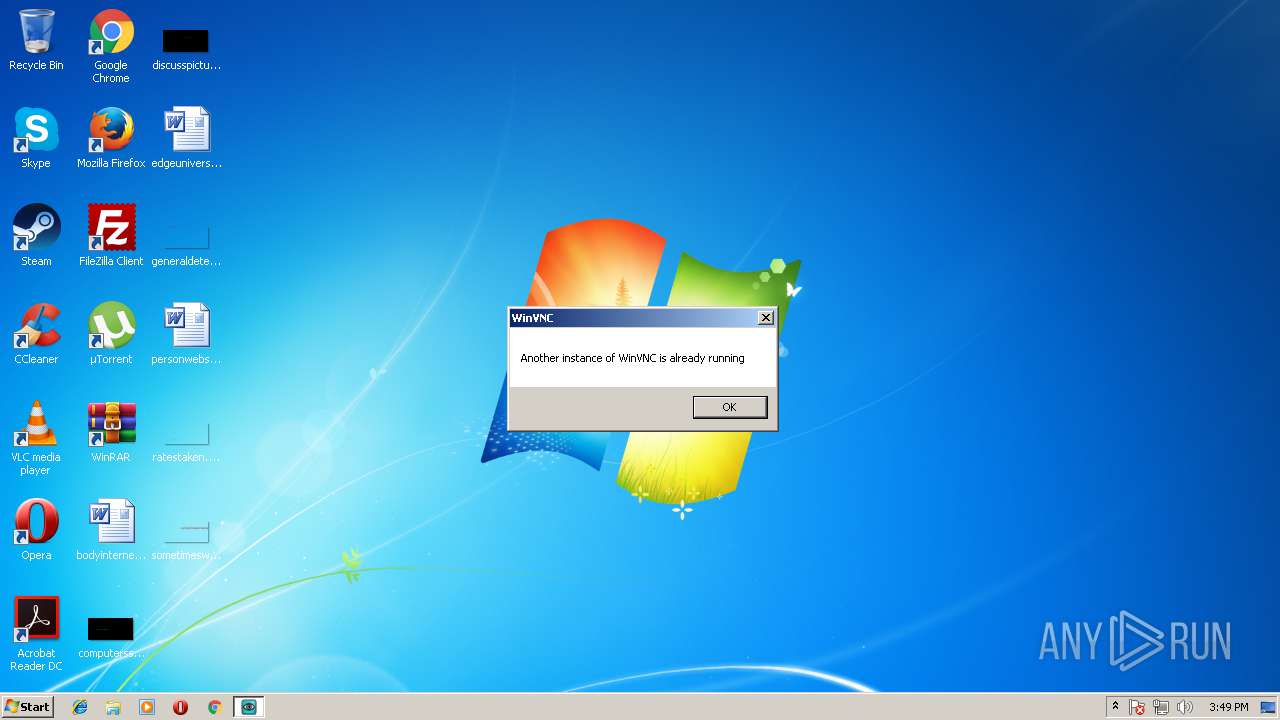
Application launched itself
- WinVNC.exe (PID: 1068)
- WinVNC.exe (PID: 3880)
- WinVNC.exe (PID: 2860)
- WinVNC.exe (PID: 3628)
- WinVNC.exe (PID: 2988)
Reads internet explorer settings
- mmc.exe (PID: 1640)
Creates files in the Windows directory
- WinVNC.exe (PID: 2860)
Removes files from Windows directory
- WinVNC.exe (PID: 344)
- WinVNC.exe (PID: 2432)
Creates files in the user directory
- vncviewer.exe (PID: 1552)
Creates files in the program directory
- WinVNC.exe (PID: 2860)
INFO
Application was dropped or rewritten from another process
- UltraVNC_1_2_22_X86_Setup.tmp (PID: 3080)
- UltraVNC_1_2_22_X86_Setup.tmp (PID: 3856)
Dropped object may contain URL's
- UltraVNC_1_2_22_X86_Setup.exe (PID: 3520)
- UltraVNC_1_2_22_X86_Setup.exe (PID: 3724)
- UltraVNC_1_2_22_X86_Setup.tmp (PID: 3856)
Loads dropped or rewritten executable
- UltraVNC_1_2_22_X86_Setup.tmp (PID: 3856)
Creates files in the program directory
- UltraVNC_1_2_22_X86_Setup.tmp (PID: 3856)
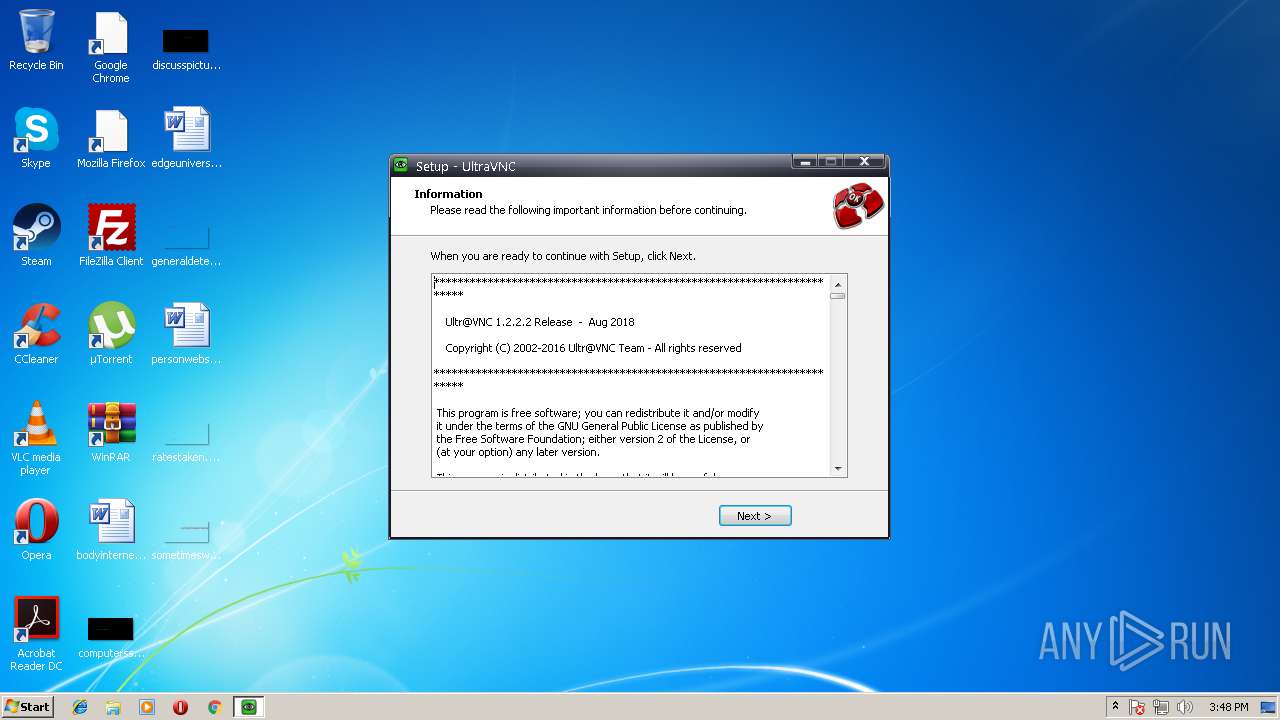
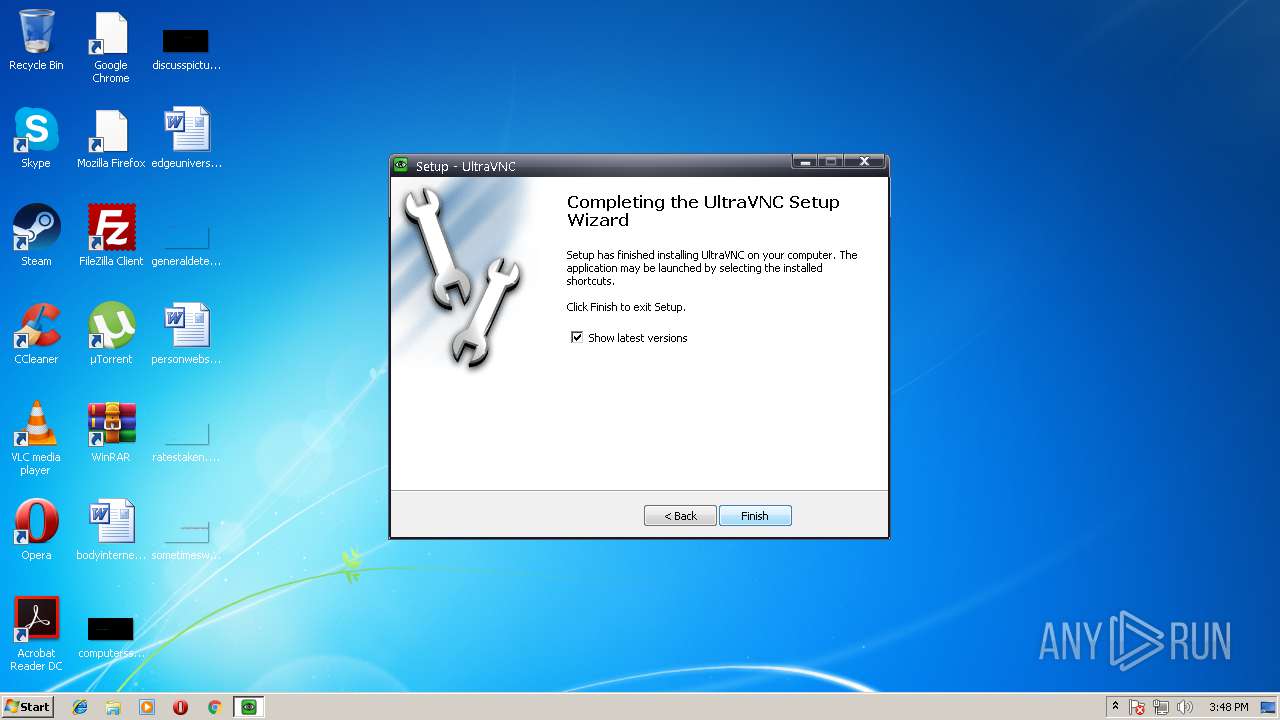
Creates a software uninstall entry
- UltraVNC_1_2_22_X86_Setup.tmp (PID: 3856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41472 |
| InitializedDataSize: | 308224 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa98 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
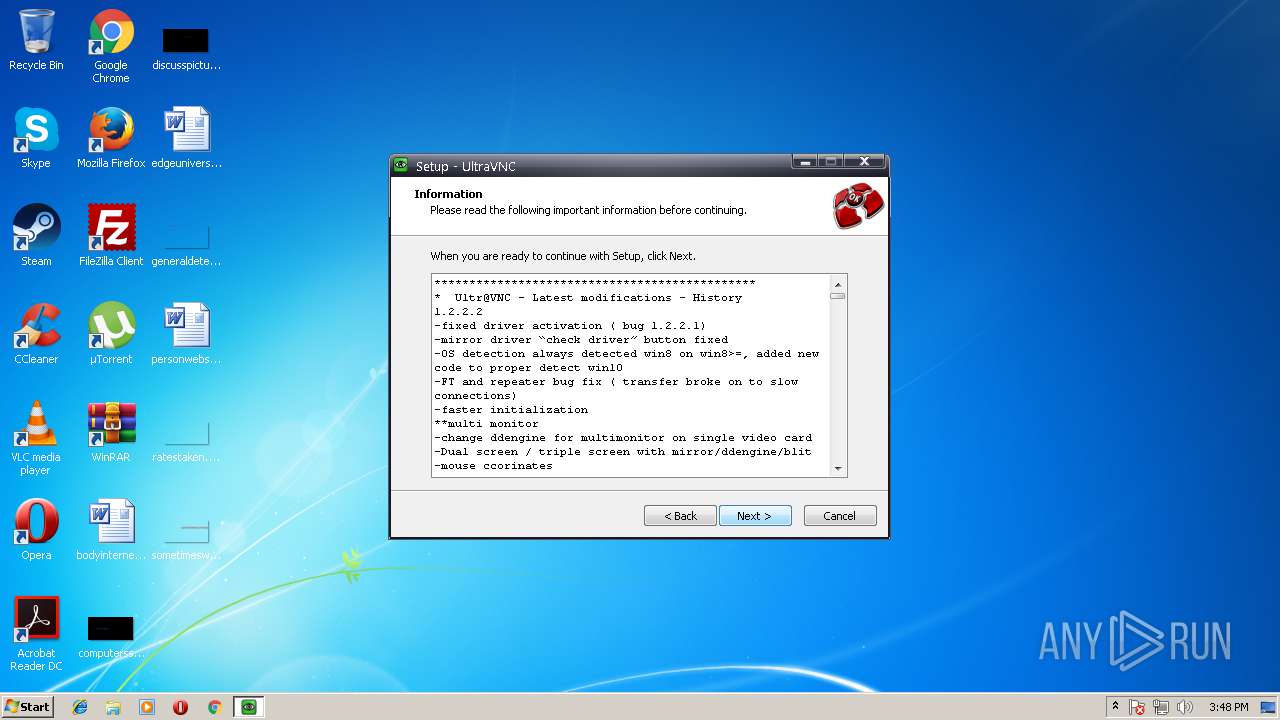
| FileVersionNumber: | 1.2.2.2 |
| ProductVersionNumber: | 1.2.2.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
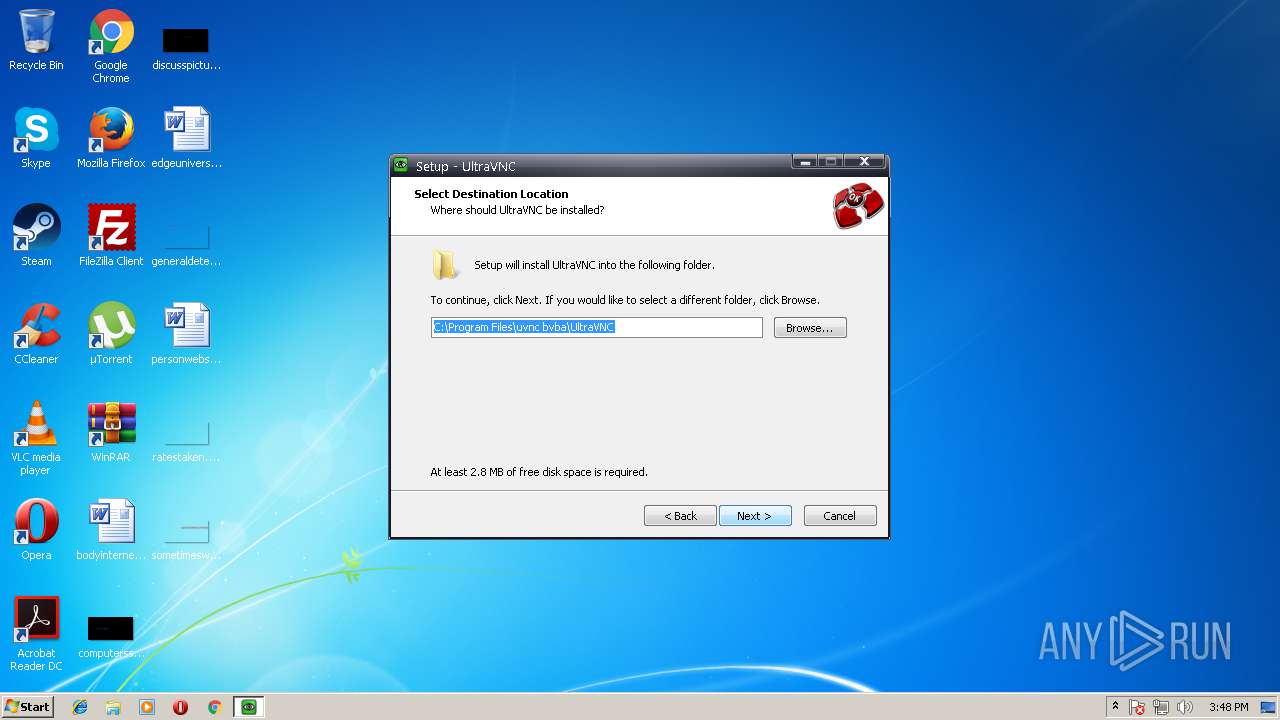
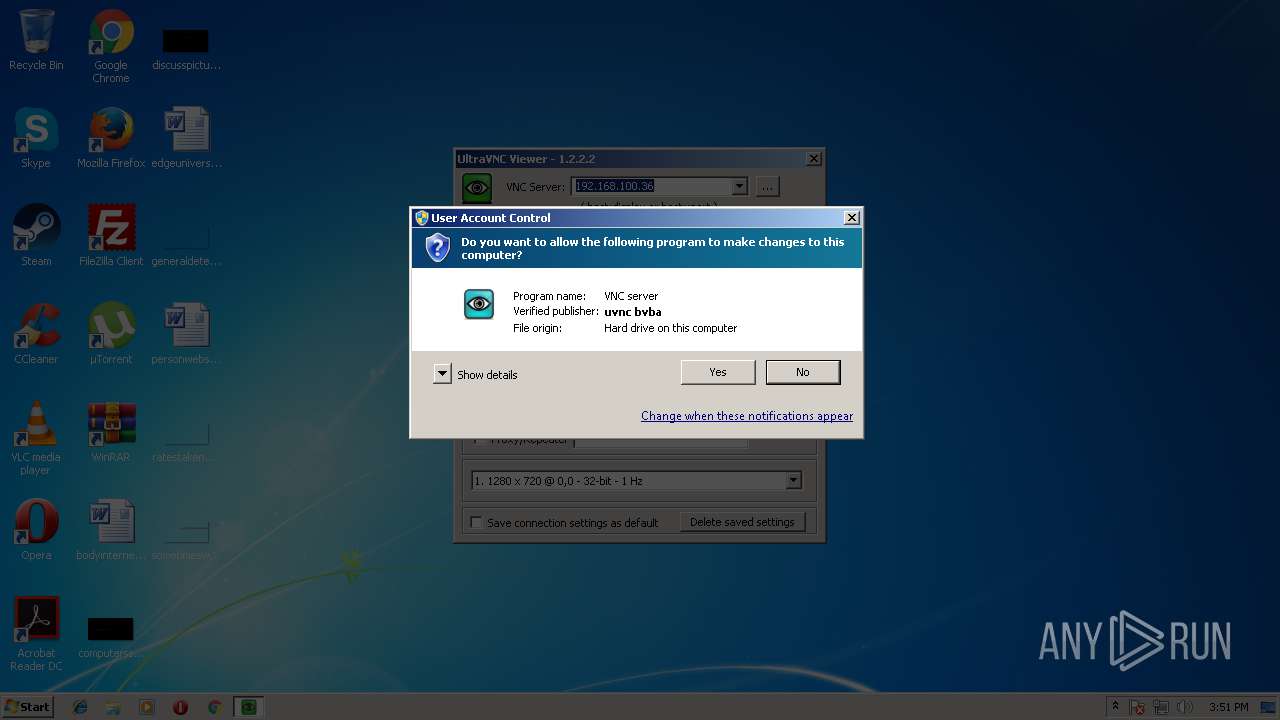
| CompanyName: | uvnc bvba |
| FileDescription: | UltraVNC Setup |
| FileVersion: | 1.2.2.2 |
| LegalCopyright: | UltraVnc Team |
| ProductName: | UltraVnc |
| ProductVersion: | 1.2.2.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | uvnc bvba |
| FileDescription: | UltraVNC Setup |
| FileVersion: | 1.2.2.2 |
| LegalCopyright: | UltraVnc Team |
| ProductName: | UltraVnc |
| ProductVersion: | 1.2.2.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A1D0 | 0x0000A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64375 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74012 |
BSS | 0x0000D000 | 0x00000E94 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000097C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x0000091C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x0004A298 | 0x0004A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.15292 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.34562 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.80291 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.16391 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.90207 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 6.31237 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 6.47782 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 6.44659 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 6.40578 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
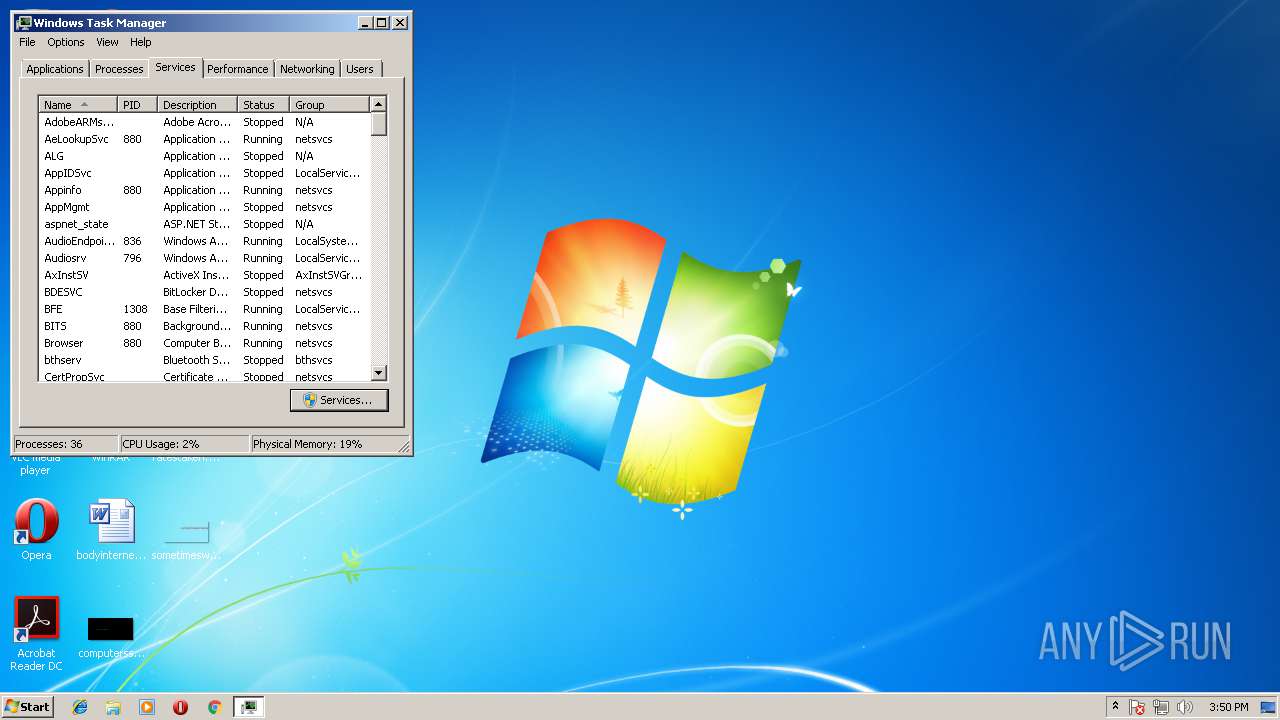
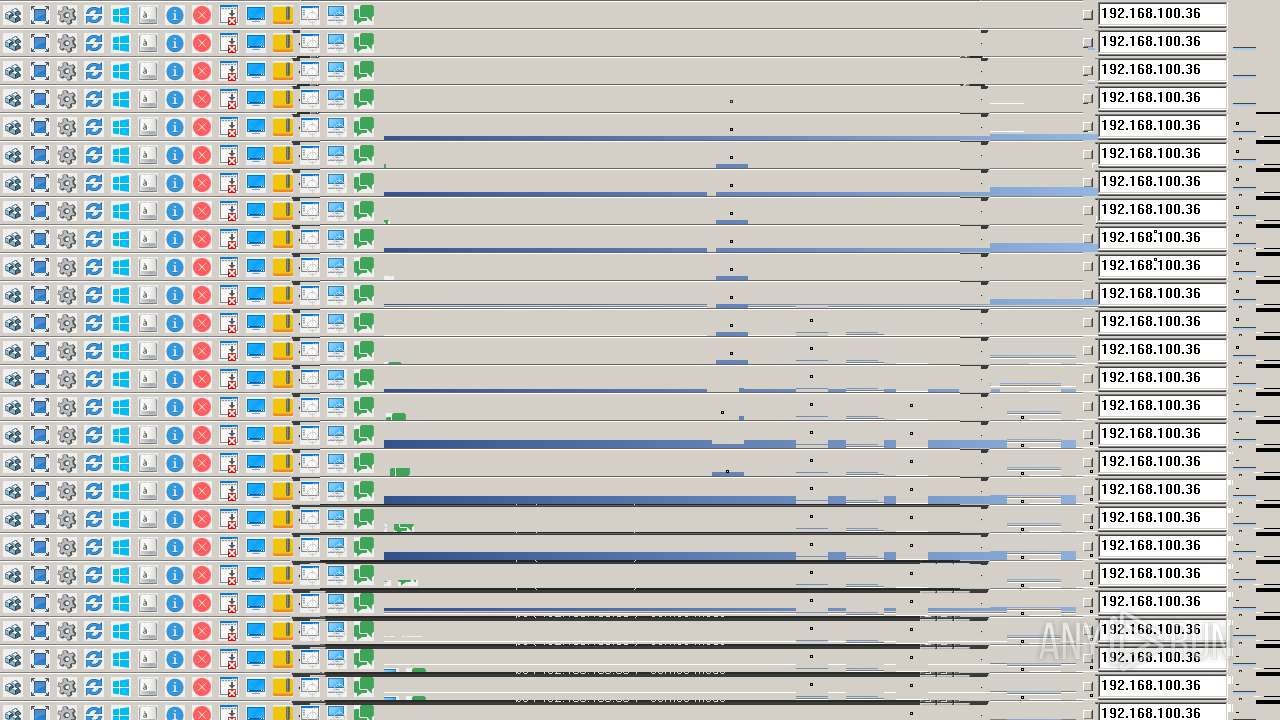
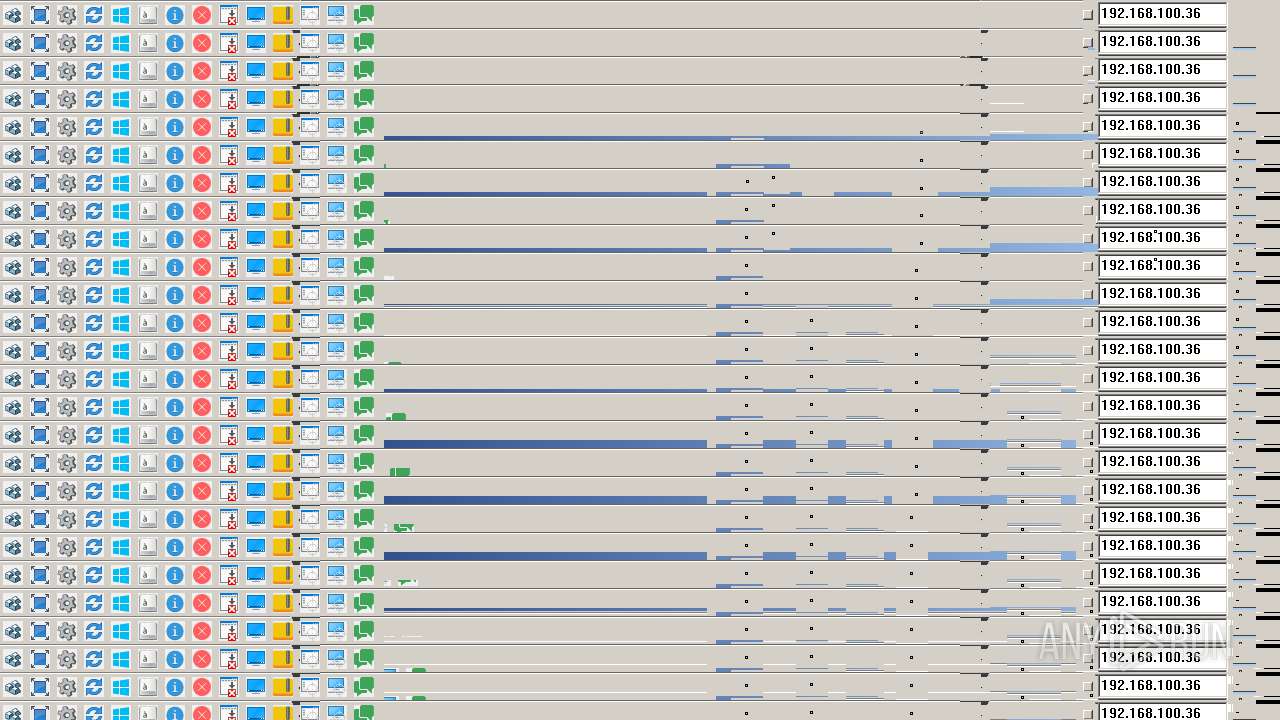
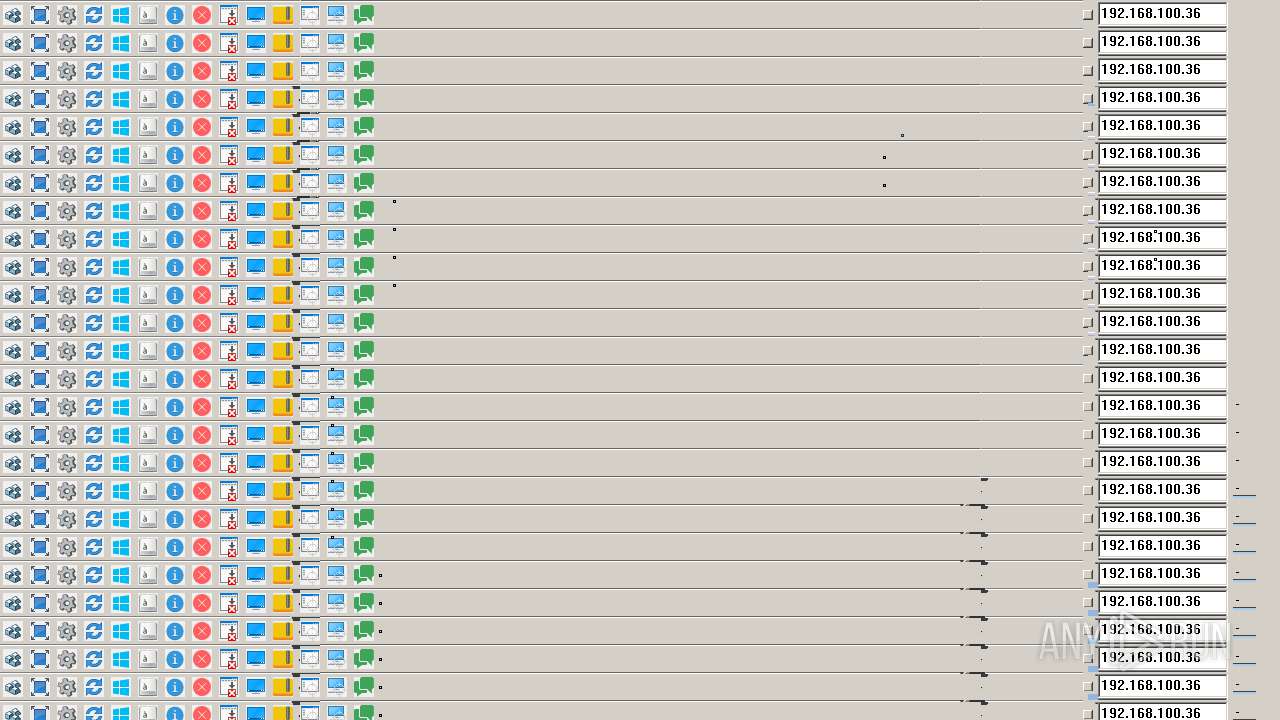
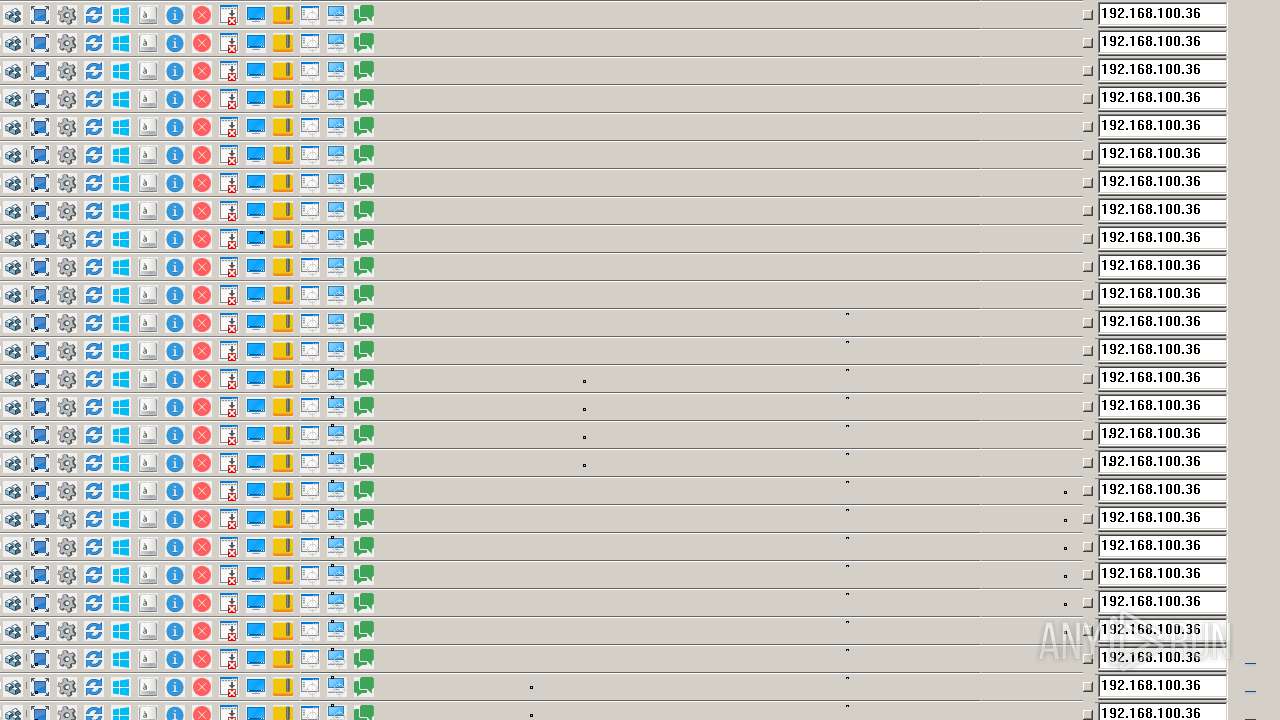
Total processes
85
Monitored processes
34
Malicious processes
7
Suspicious processes
8
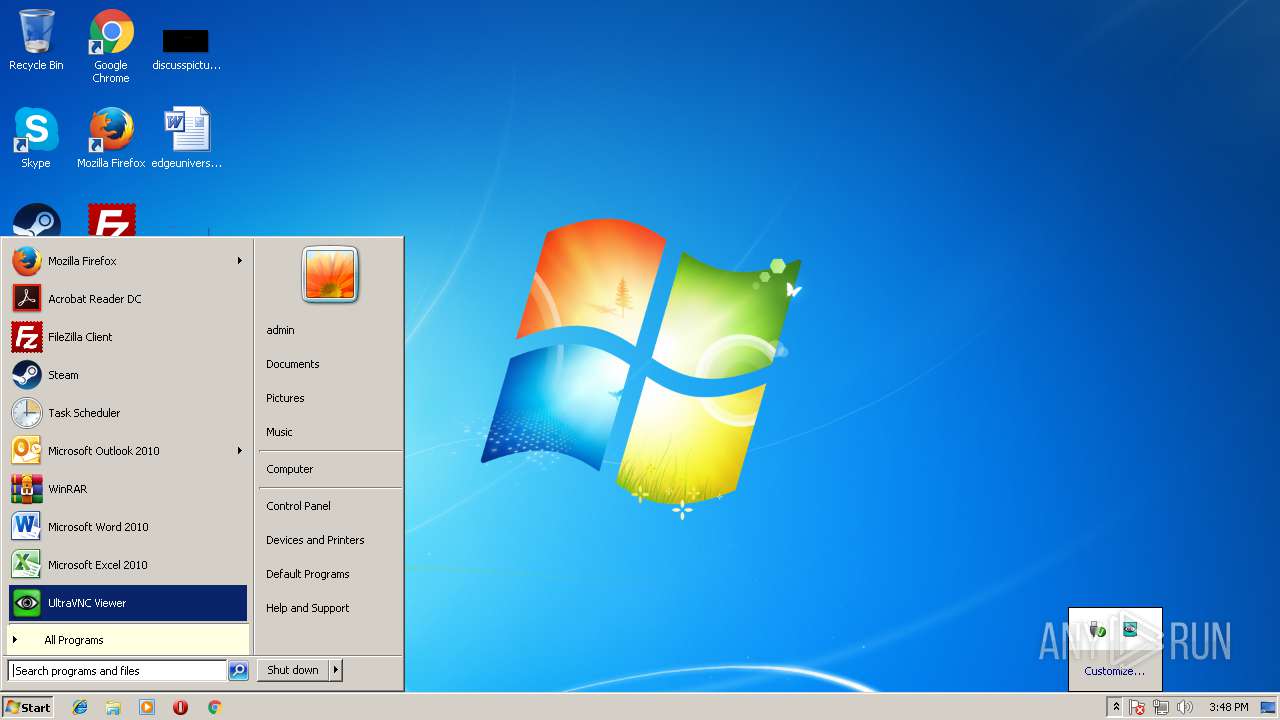
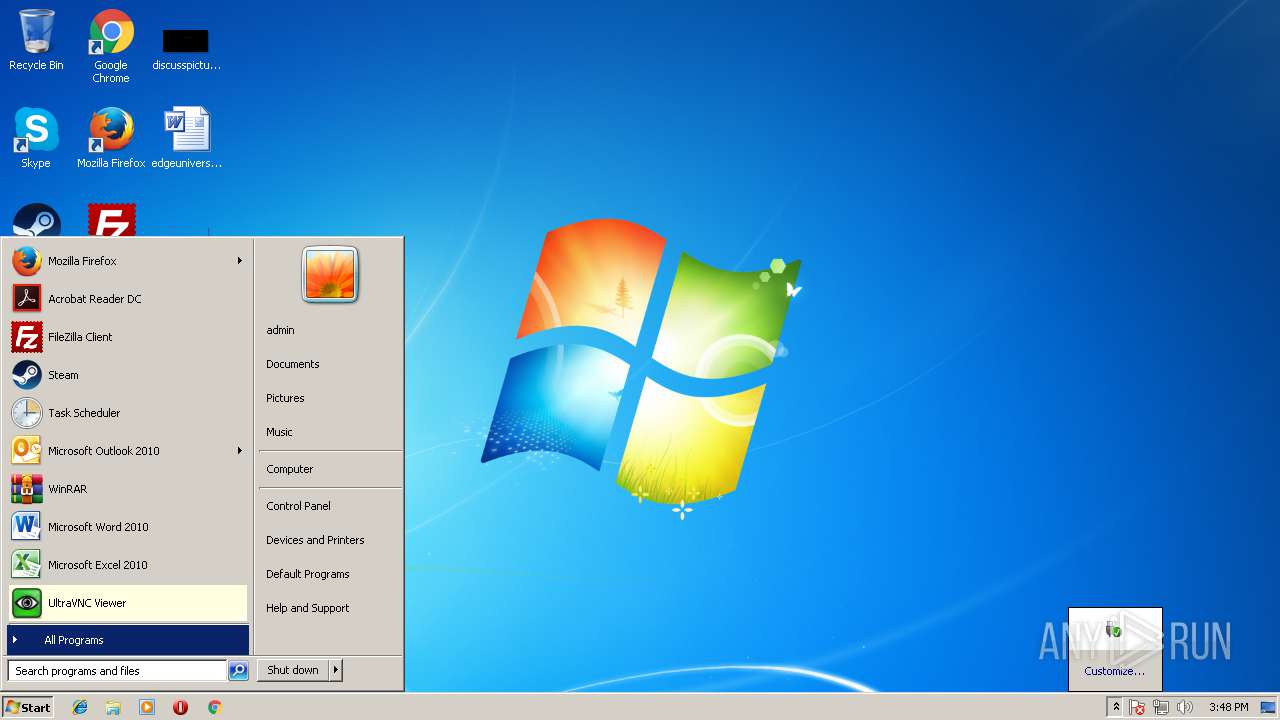
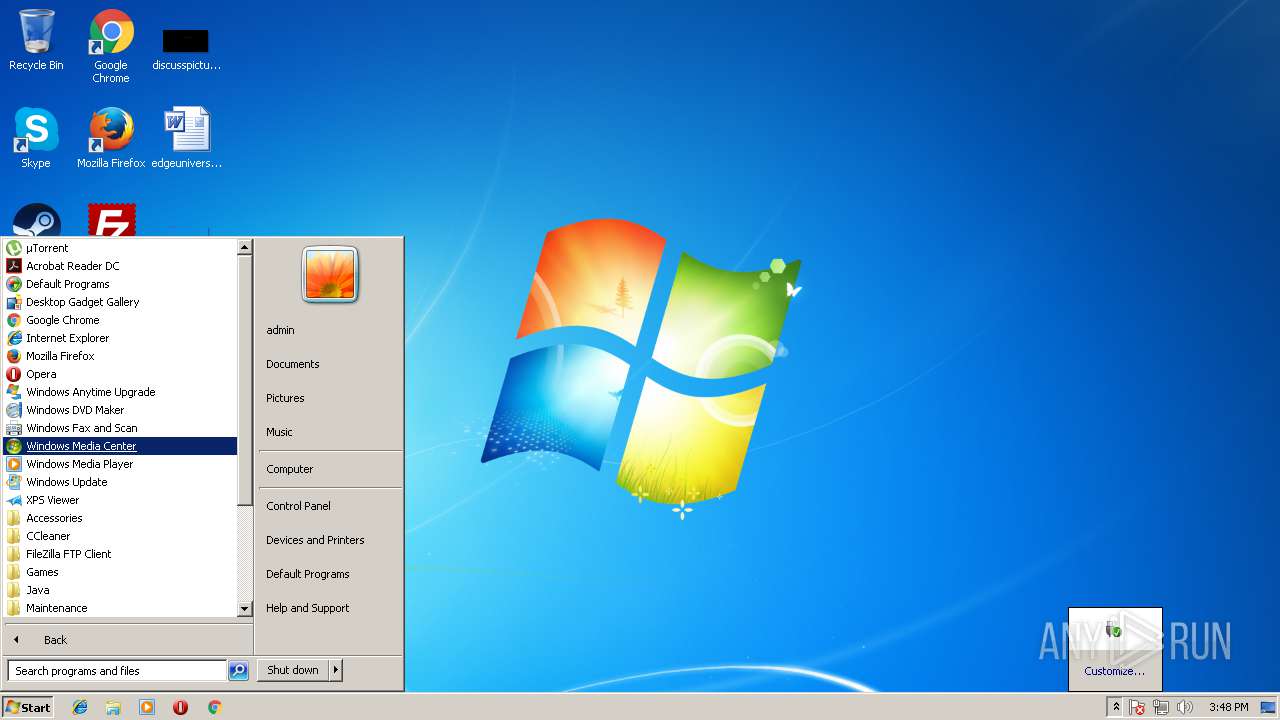
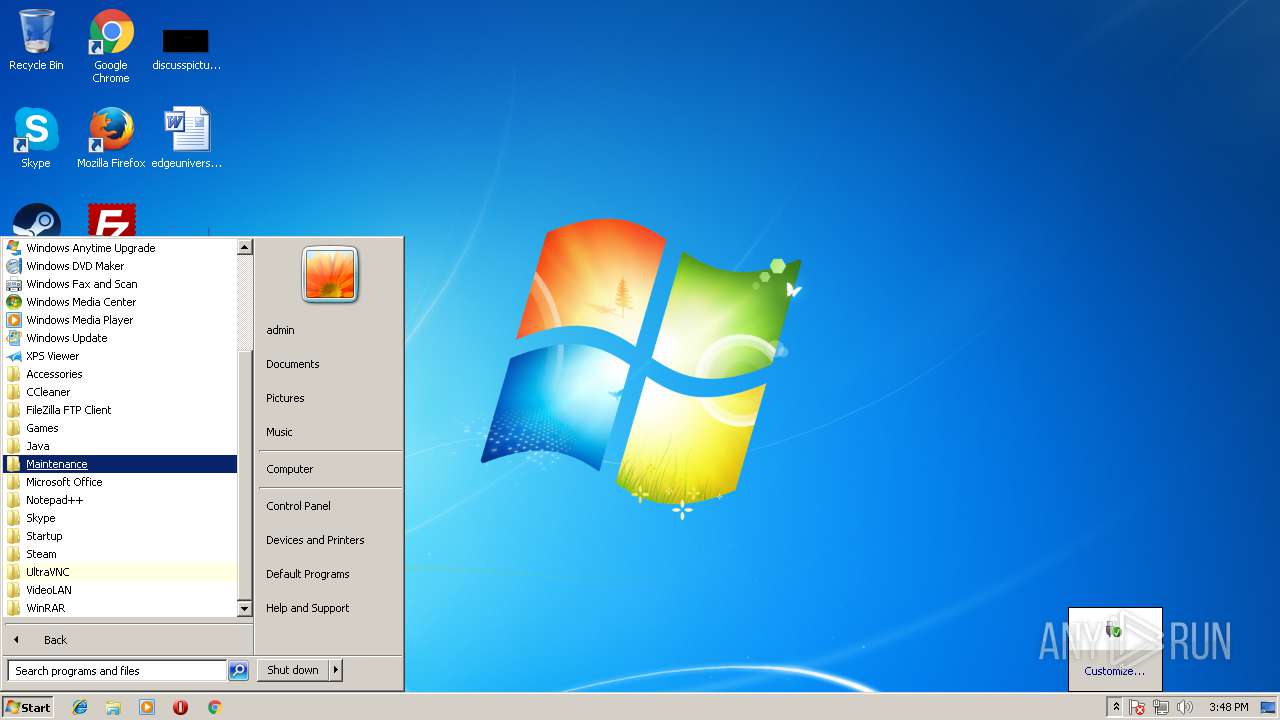
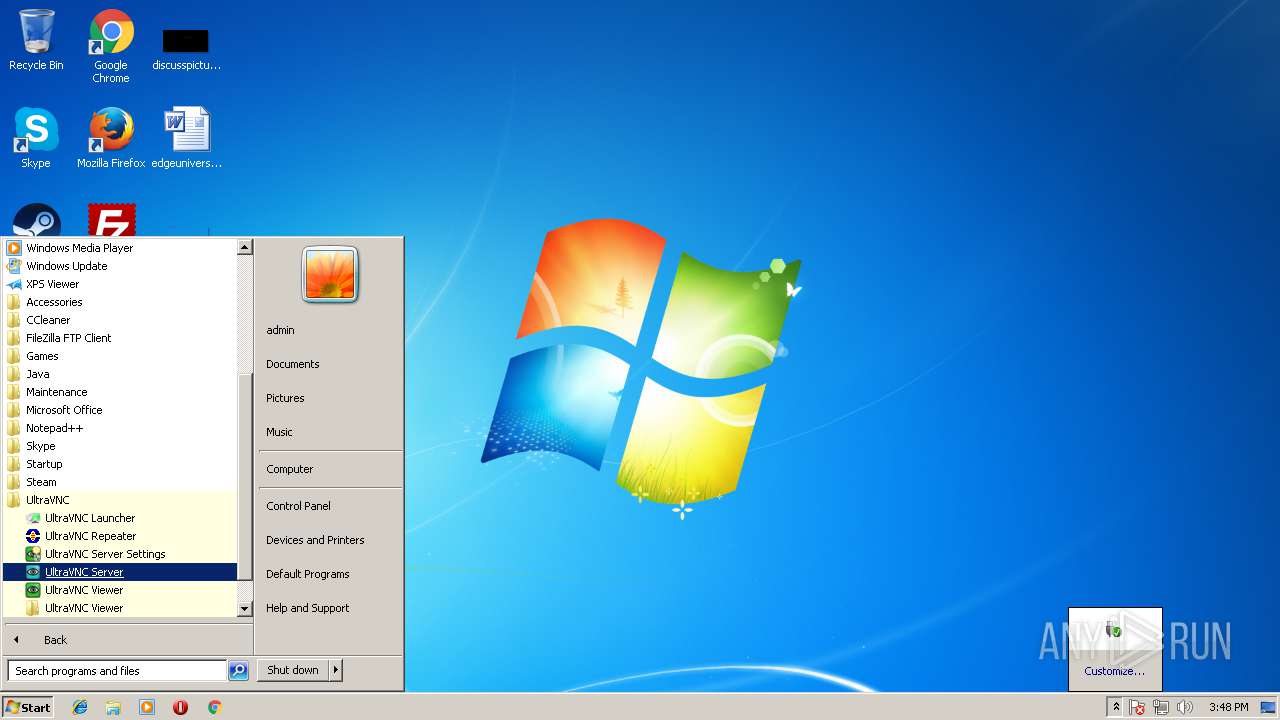
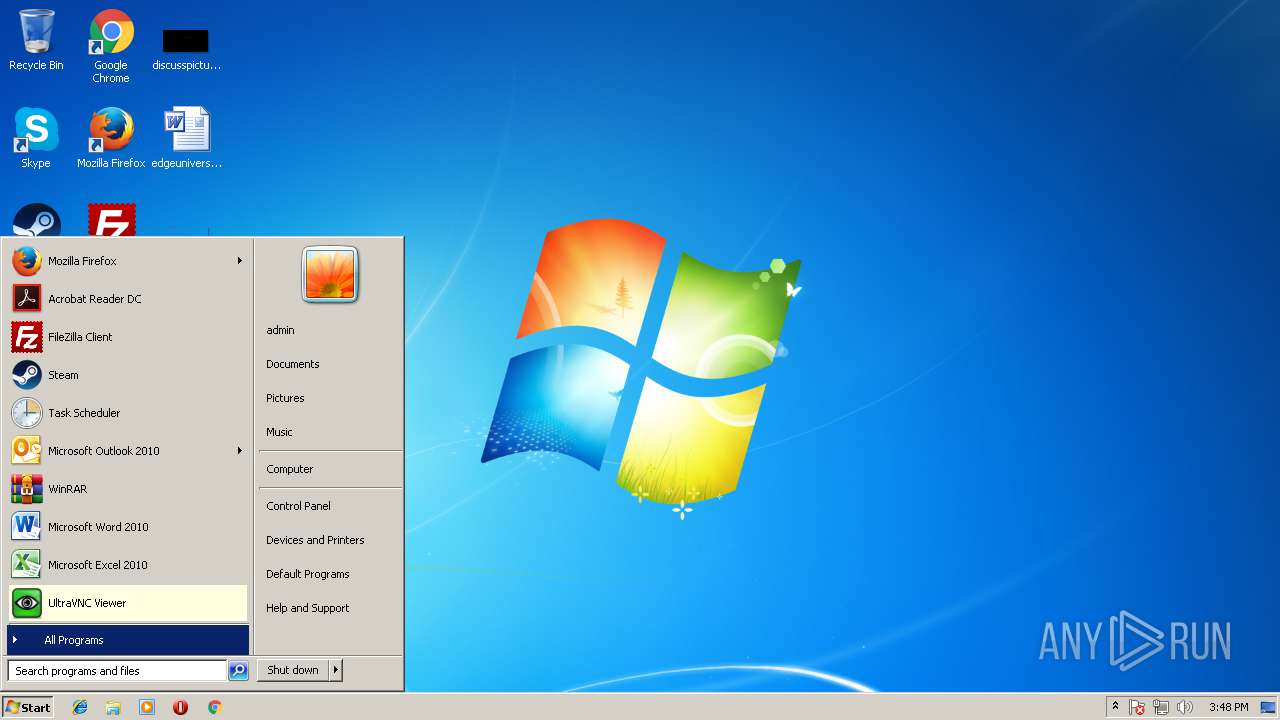
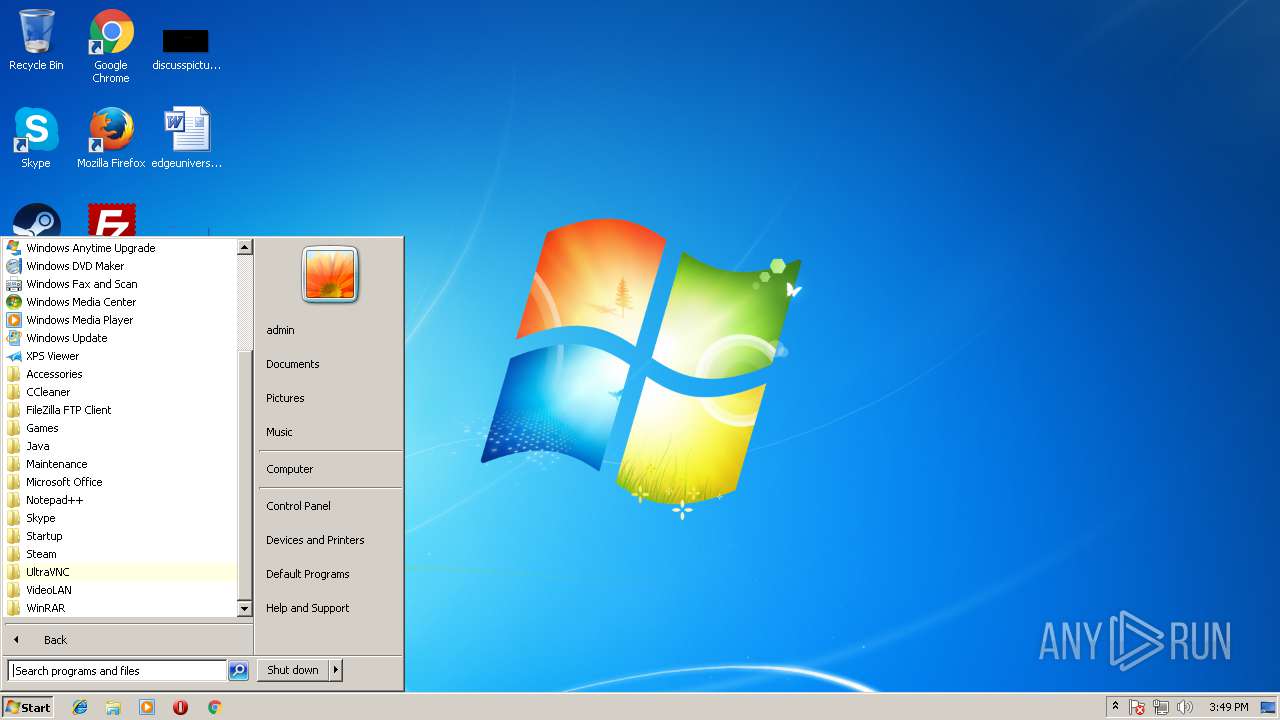
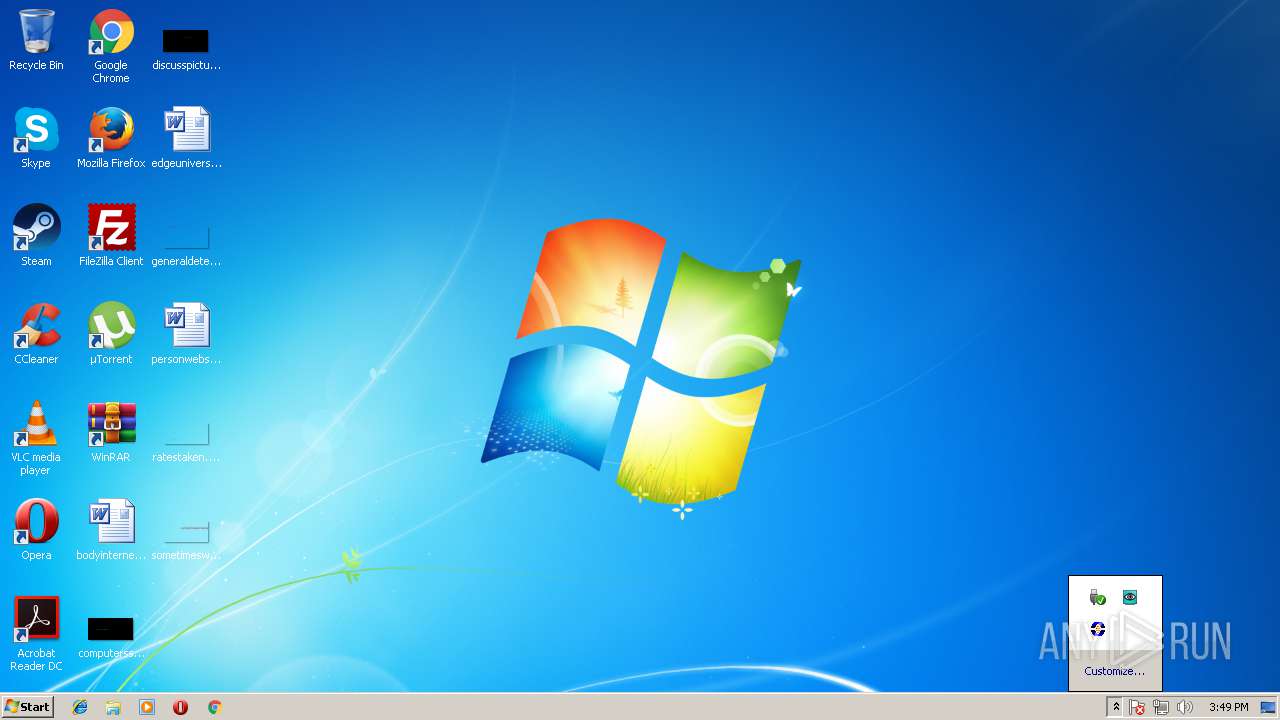
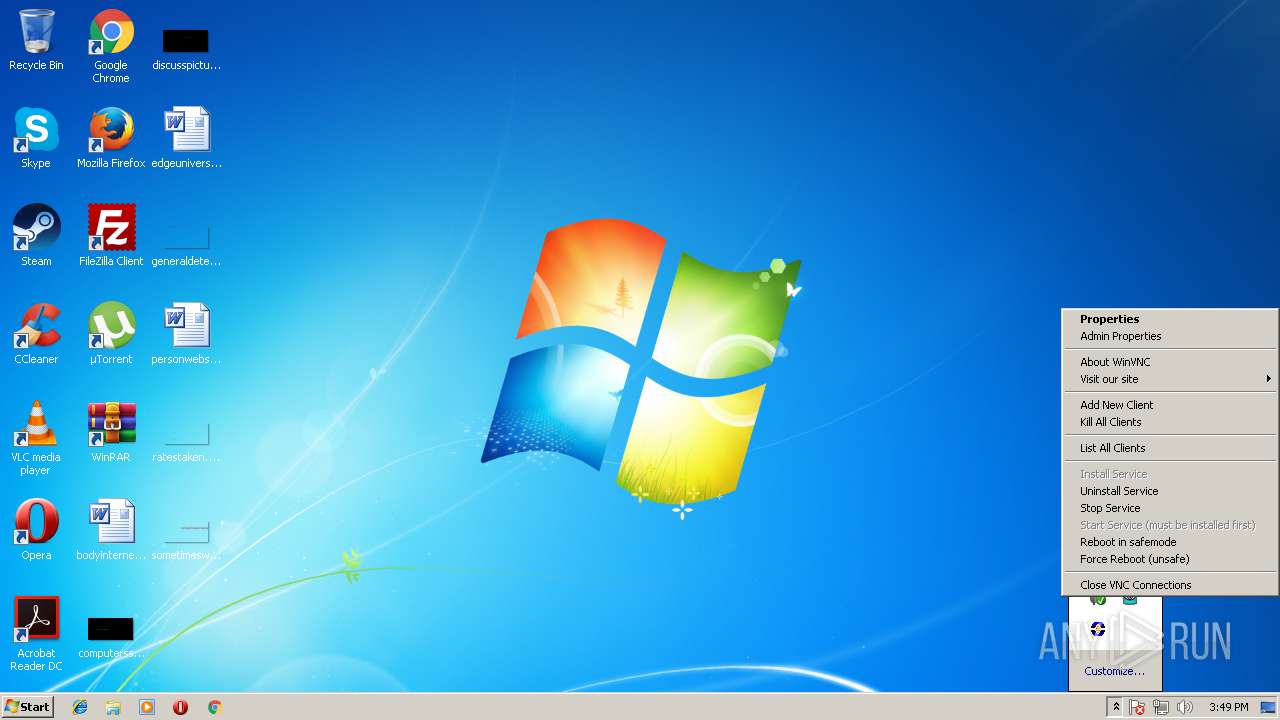
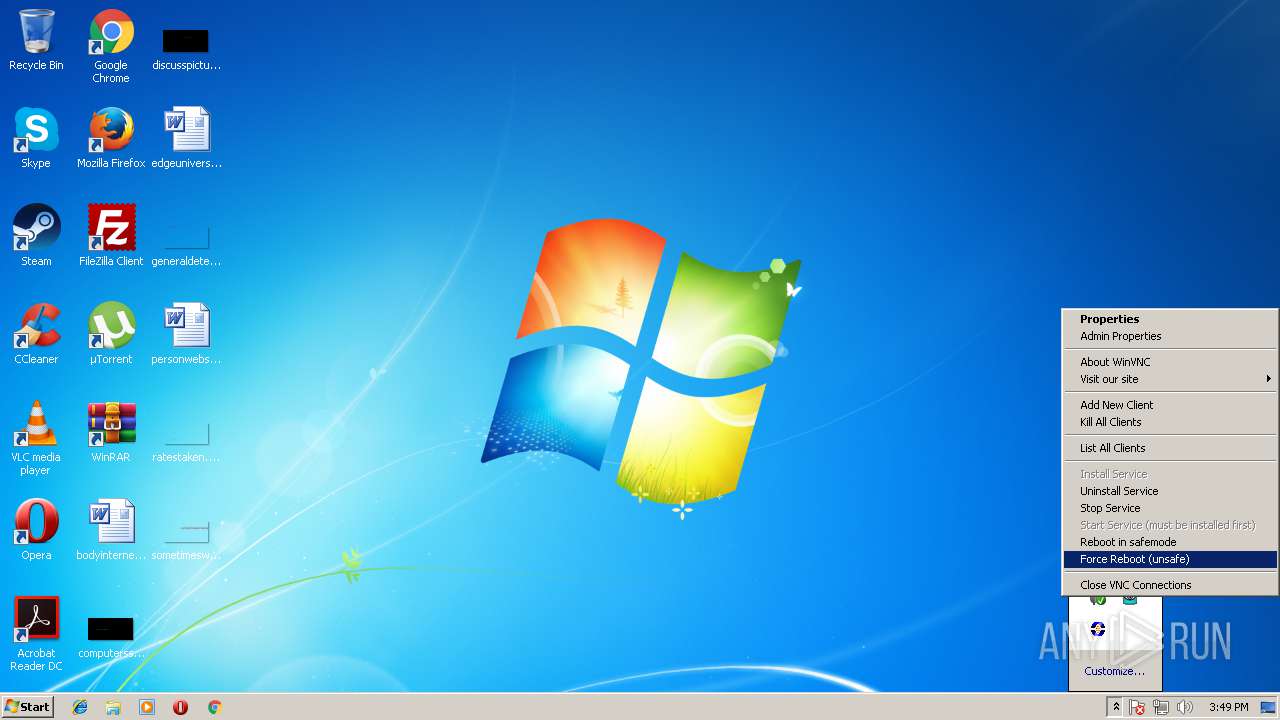
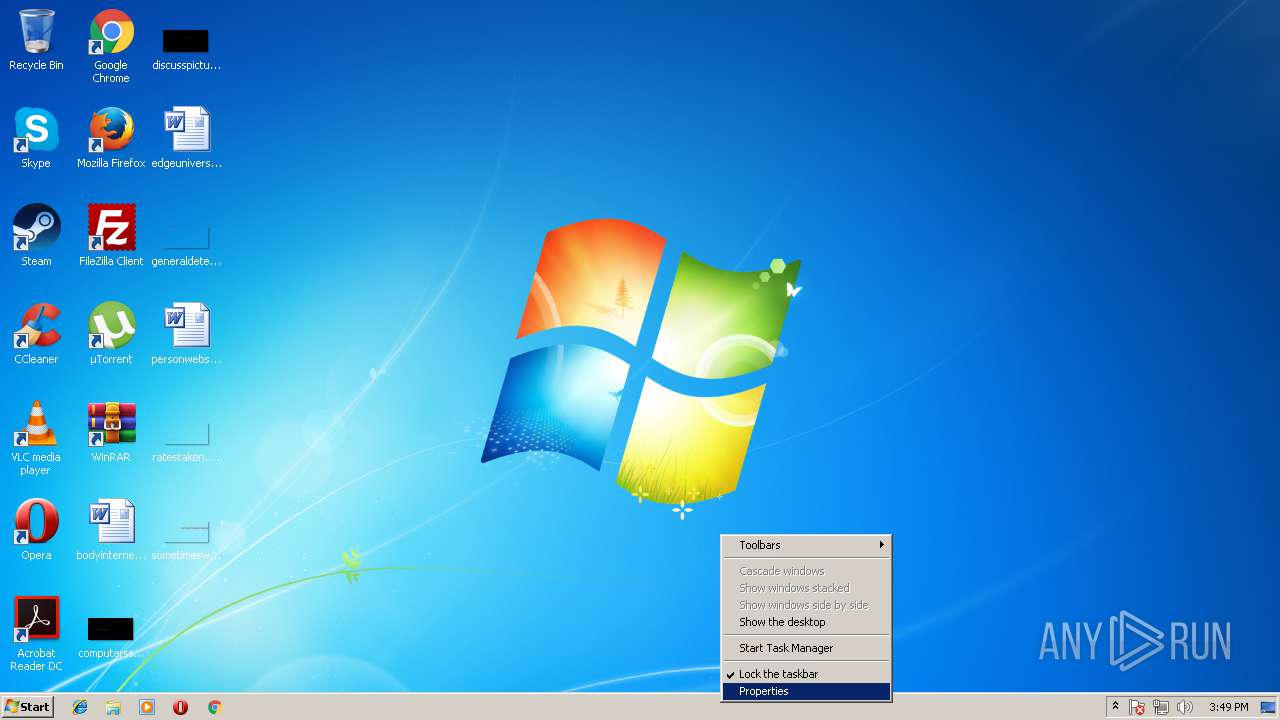
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | "C:\Program Files\uvnc bvba\UltraVNC\WinVNC.exe" -settings:c:\windows\temp\ultravnc.ini | C:\Program Files\uvnc bvba\UltraVNC\WinVNC.exe | WinVNC.exe | ||||||||||||
User: admin Company: UltraVNC Integrity Level: HIGH Description: VNC server Exit code: 0 Version: 1.2.2.2 Modules
| |||||||||||||||
| 868 | "C:\Windows\system32\netsh" firewall add portopening TCP 5900 vnc5900 | C:\Windows\system32\netsh.exe | — | UltraVNC_1_2_22_X86_Setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1032 | C:\Windows\system32\net1 start uvnc_service | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1068 | "C:\Program Files\uvnc bvba\UltraVNC\WinVNC.exe" -service | C:\Program Files\uvnc bvba\UltraVNC\WinVNC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: UltraVNC Integrity Level: SYSTEM Description: VNC server Exit code: 0 Version: 1.2.2.2 Modules
| |||||||||||||||
| 1380 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
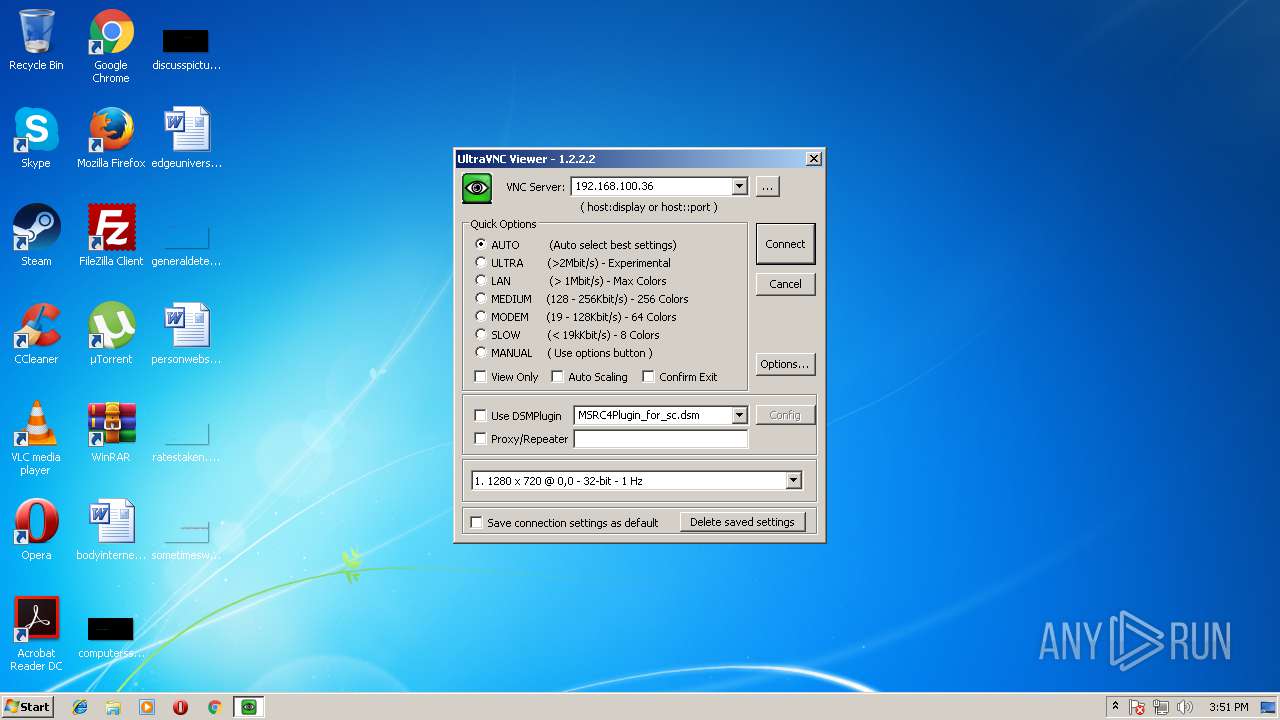
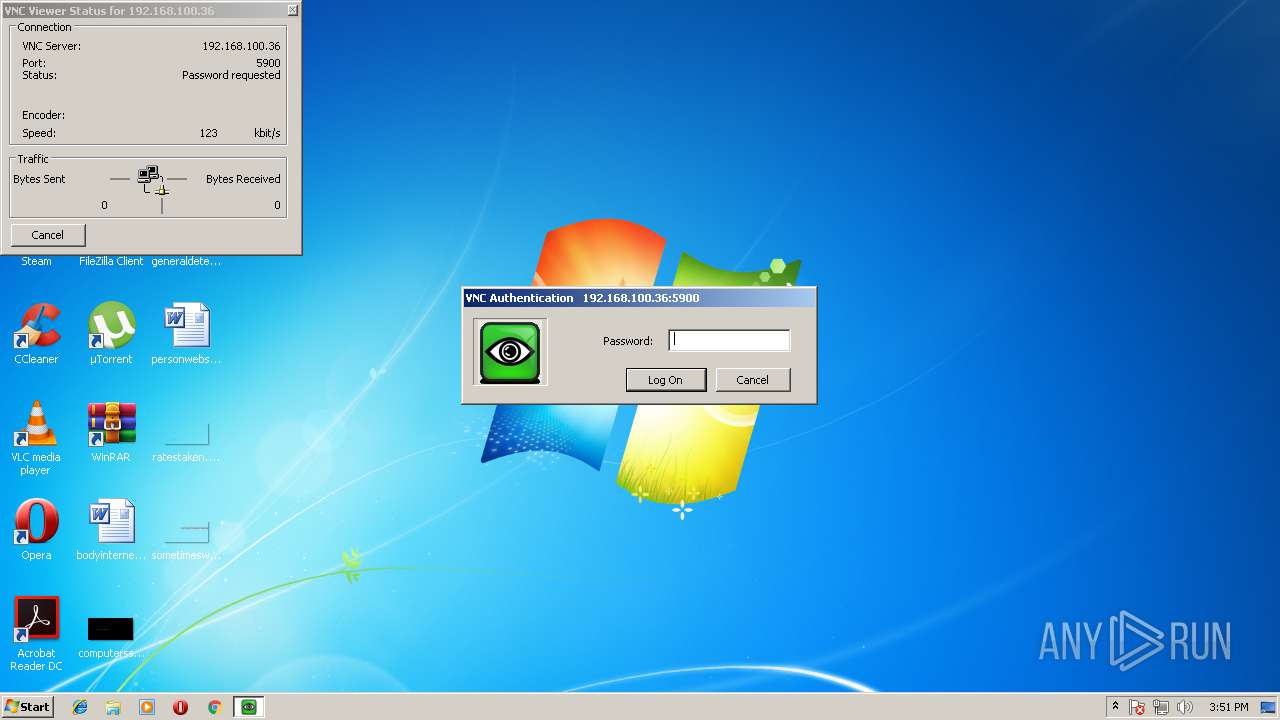
| 1552 | "C:\Program Files\uvnc bvba\UltraVNC\vncviewer.exe" | C:\Program Files\uvnc bvba\UltraVNC\vncviewer.exe | explorer.exe | ||||||||||||
User: admin Company: UltraVNC Integrity Level: MEDIUM Description: VNCViewer Exit code: 0 Version: 1.2.2.2 Modules
| |||||||||||||||
| 1640 | "C:\Windows\system32\mmc.exe" "C:\Windows\System32\services.msc" | C:\Windows\system32\mmc.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1680 | rundll32.exe C:\Windows\system32\hotplug.dll,HotPlugSafeRemovalNotification \\.\pipe\PNP_HotPlug_Pipe_1.{a7e6f783-fad2-4ef0-86c4-49e51ac462b5} | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2096 | "C:\Windows\system32\netsh" firewall add portopening TCP 5800 vnc5800 | C:\Windows\system32\netsh.exe | — | UltraVNC_1_2_22_X86_Setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2180 | "C:\Program Files\uvnc bvba\UltraVNC\repeater.exe" | C:\Program Files\uvnc bvba\UltraVNC\repeater.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: distributer Exit code: 0 Version: 1.4.0.0 Modules
| |||||||||||||||
Total events
3 926
Read events
3 400
Write events
513
Delete events
13
Modification events
| (PID) Process: | (3856) UltraVNC_1_2_22_X86_Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 100F0000D7BD784CF03AD401 | |||
| (PID) Process: | (3856) UltraVNC_1_2_22_X86_Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: E22086491CDA2A426BD805D1028A6EF71CAF90FB6D1F2BF9F42CD6E93E746811 | |||
| (PID) Process: | (3856) UltraVNC_1_2_22_X86_Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3856) UltraVNC_1_2_22_X86_Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\uvnc bvba\UltraVNC\repeater.exe | |||
| (PID) Process: | (3856) UltraVNC_1_2_22_X86_Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 035C8445D543773F2E6C68BE8268FF060DEDB3F5976AC4CF05D9EA72621D8735 | |||
| (PID) Process: | (3376) setcad.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | SoftwareSASGeneration |
Value: 1 | |||
| (PID) Process: | (3856) UltraVNC_1_2_22_X86_Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Ultravnc2_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.9 (a) | |||
| (PID) Process: | (3856) UltraVNC_1_2_22_X86_Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Ultravnc2_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\uvnc bvba\UltraVNC | |||
| (PID) Process: | (3856) UltraVNC_1_2_22_X86_Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Ultravnc2_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\uvnc bvba\UltraVNC\ | |||
| (PID) Process: | (3856) UltraVNC_1_2_22_X86_Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Ultravnc2_is1 |
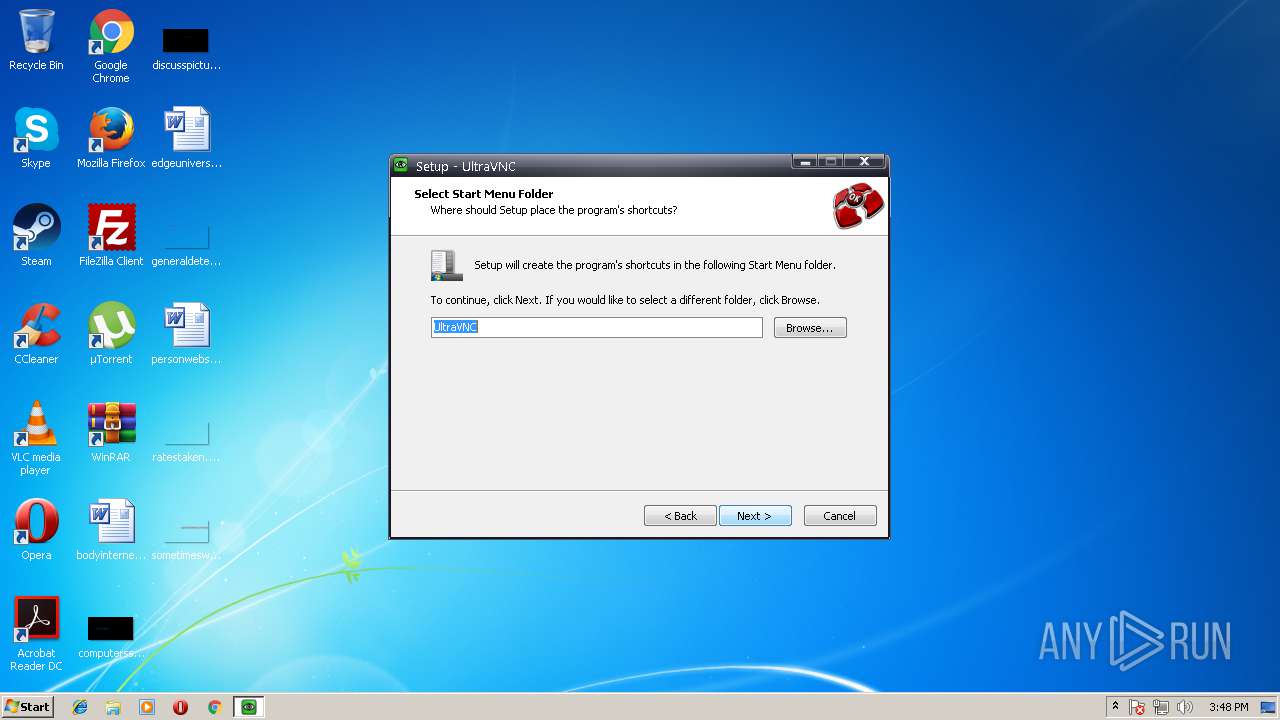
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: UltraVNC | |||
Executable files
29
Suspicious files
2
Text files
272
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3856 | UltraVNC_1_2_22_X86_Setup.tmp | C:\Program Files\uvnc bvba\UltraVNC\is-0OPVU.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | UltraVNC_1_2_22_X86_Setup.tmp | C:\Program Files\uvnc bvba\UltraVNC\is-4IHHK.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | UltraVNC_1_2_22_X86_Setup.tmp | C:\Program Files\uvnc bvba\UltraVNC\is-SV9QC.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | UltraVNC_1_2_22_X86_Setup.tmp | C:\Program Files\uvnc bvba\UltraVNC\is-8JNN8.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | UltraVNC_1_2_22_X86_Setup.tmp | C:\Program Files\uvnc bvba\UltraVNC\is-KQBTU.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | UltraVNC_1_2_22_X86_Setup.tmp | C:\Program Files\uvnc bvba\UltraVNC\is-KS2EL.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | UltraVNC_1_2_22_X86_Setup.tmp | C:\Program Files\uvnc bvba\UltraVNC\is-OUIEH.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | UltraVNC_1_2_22_X86_Setup.tmp | C:\Program Files\uvnc bvba\UltraVNC\is-G17B3.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | UltraVNC_1_2_22_X86_Setup.tmp | C:\Program Files\uvnc bvba\UltraVNC\is-72GC7.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | UltraVNC_1_2_22_X86_Setup.tmp | C:\Program Files\uvnc bvba\UltraVNC\is-378D1.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
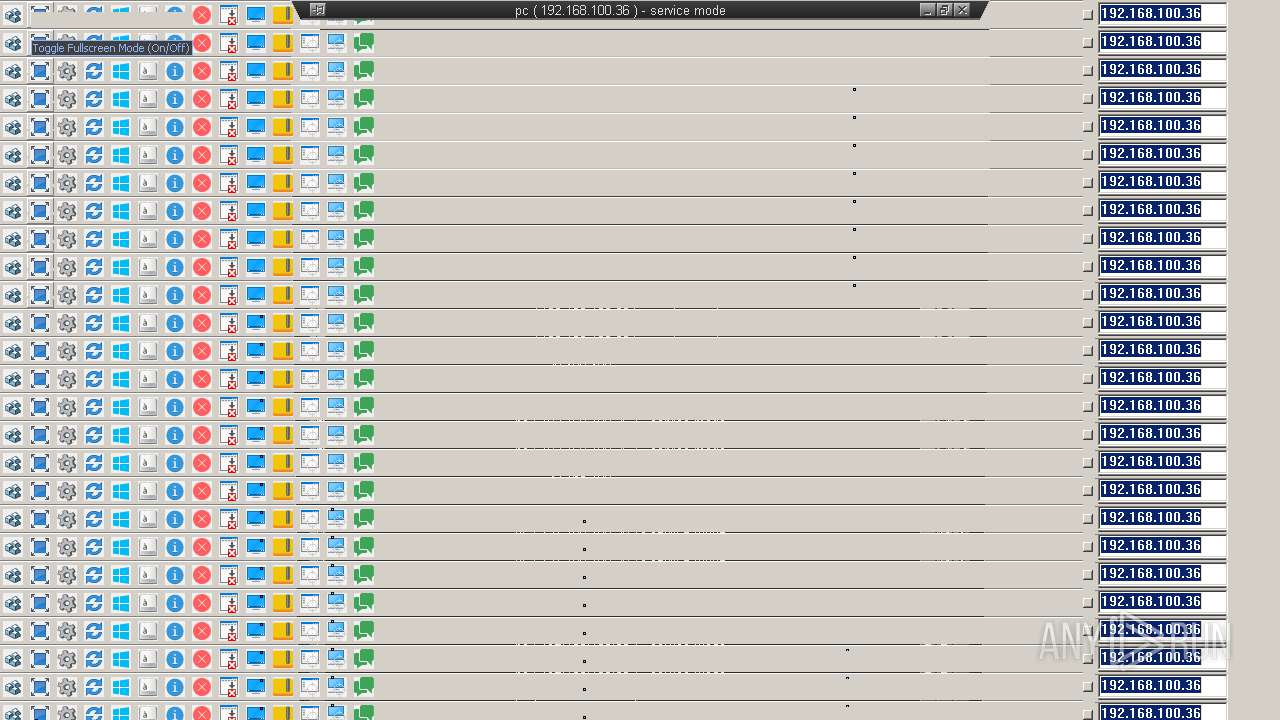
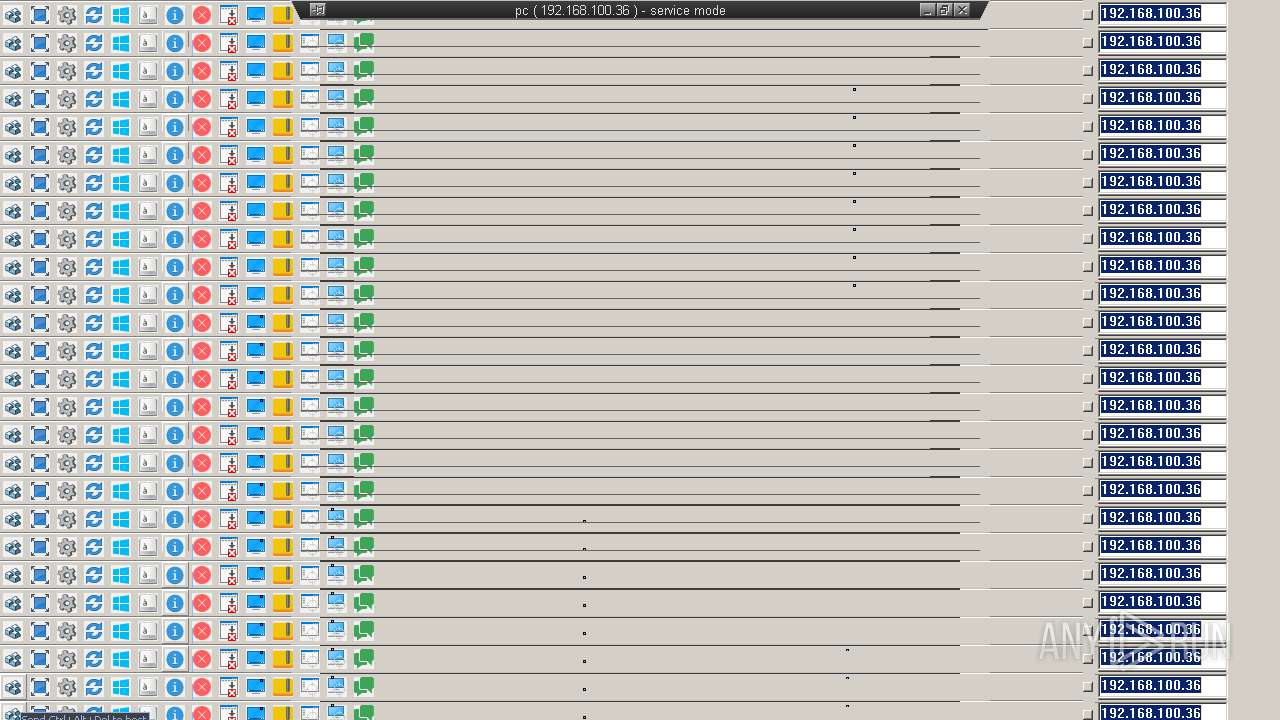
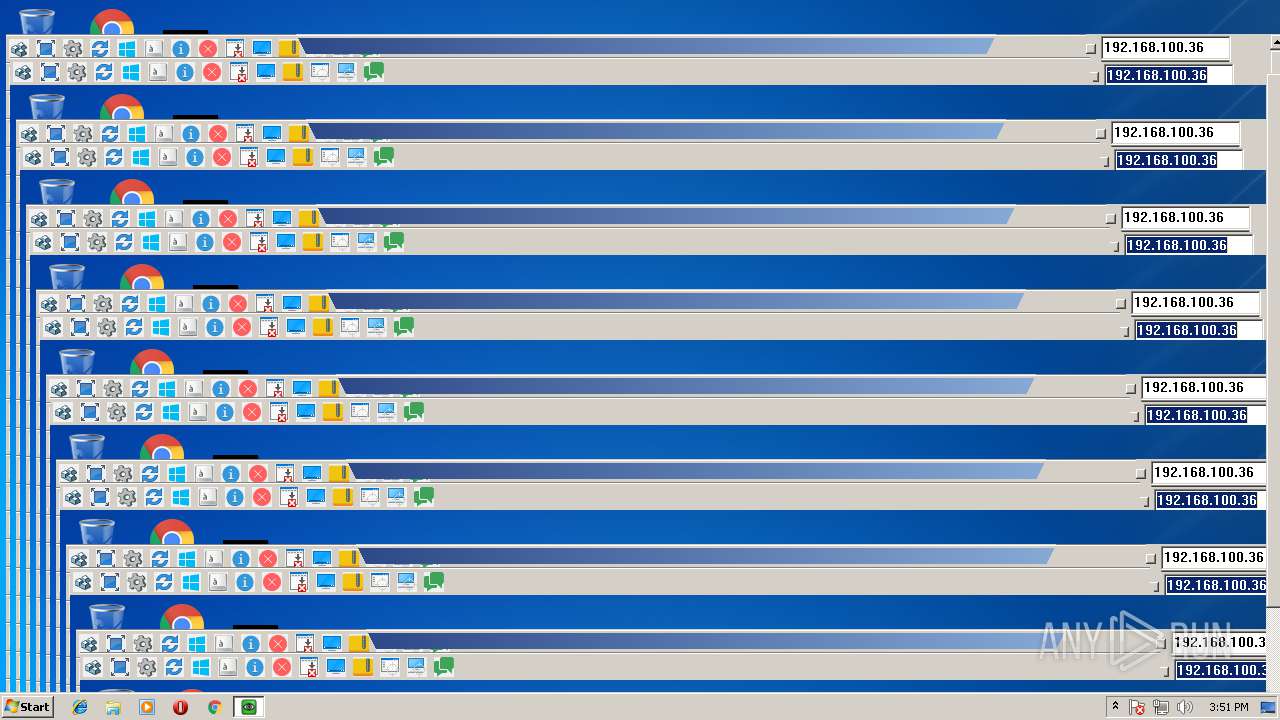
Process | Message |
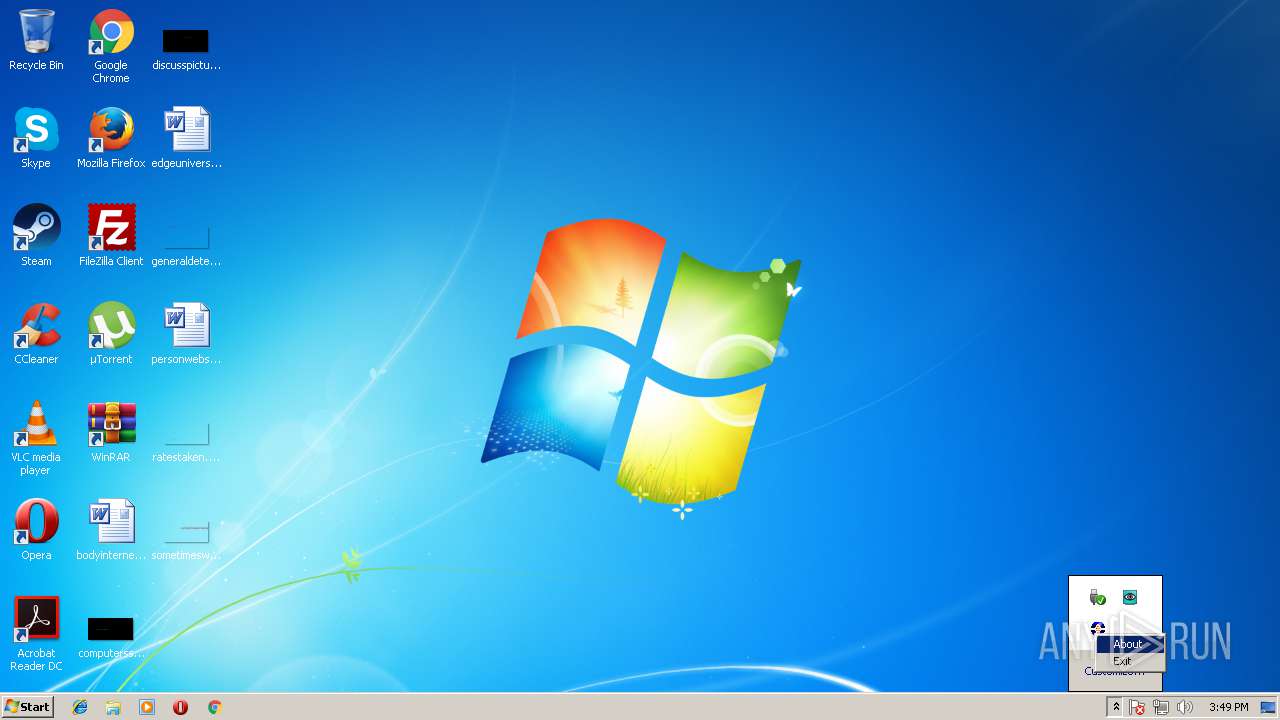
|---|---|
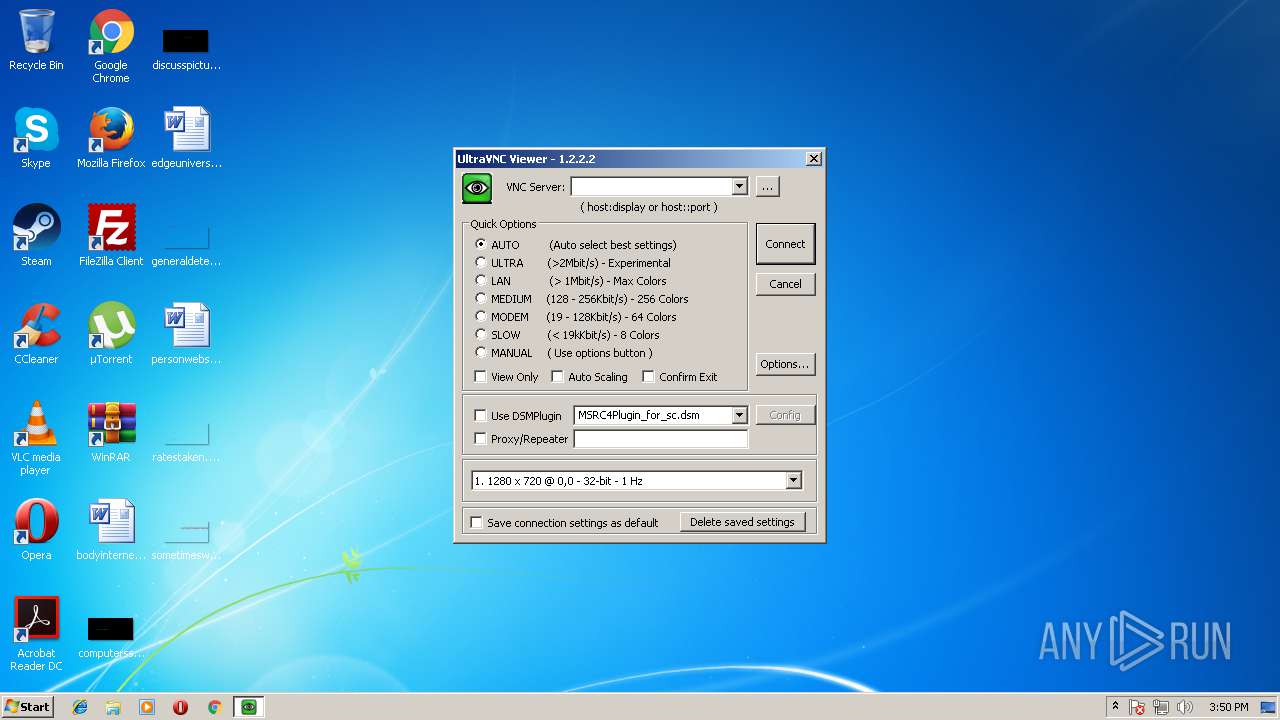
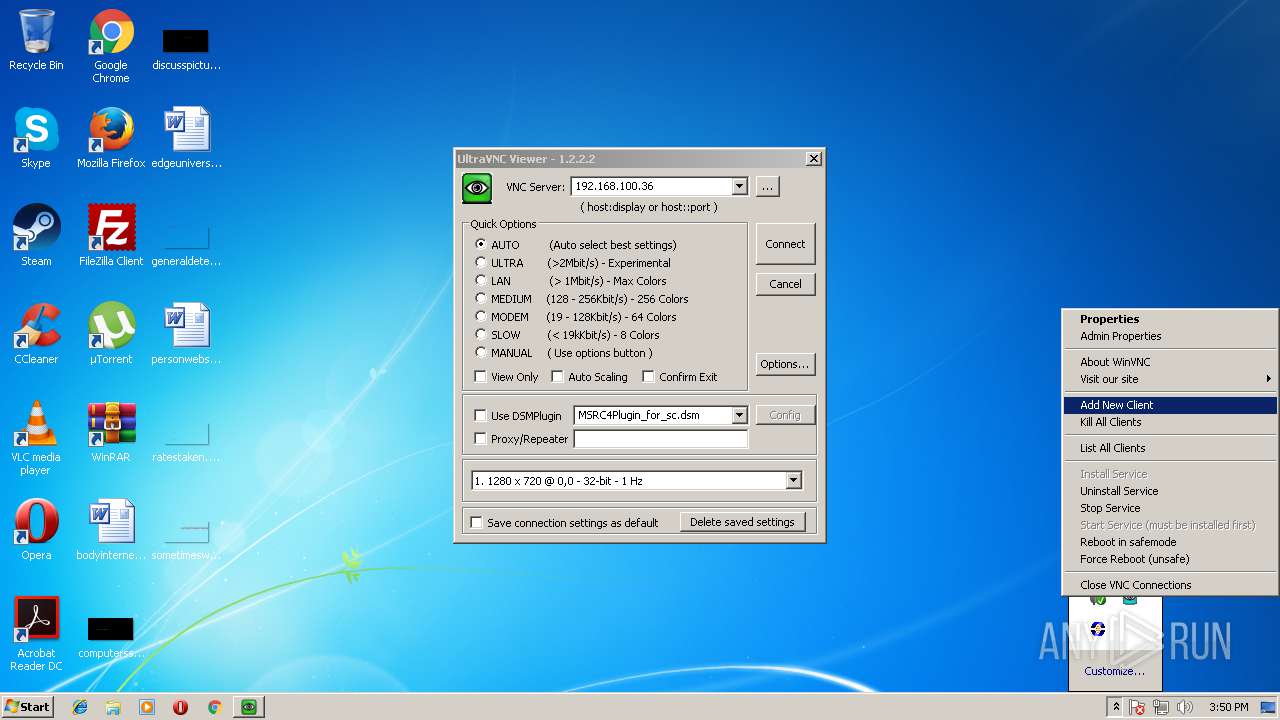
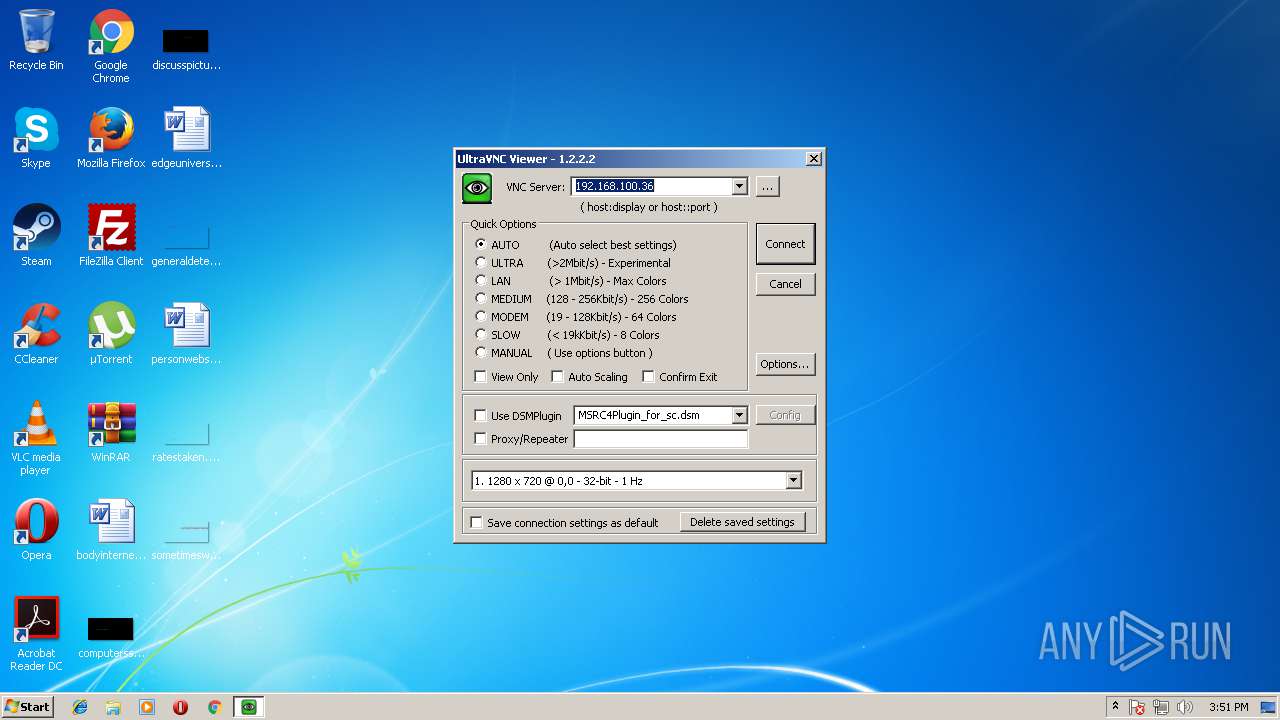
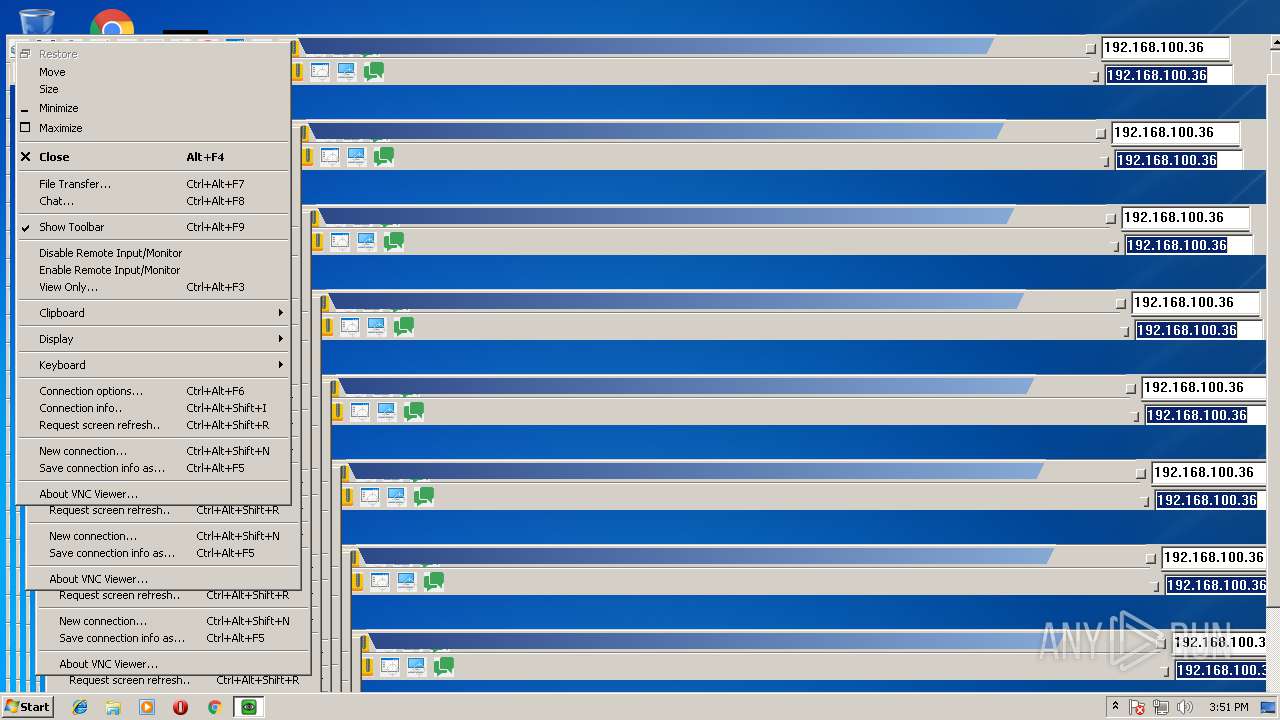
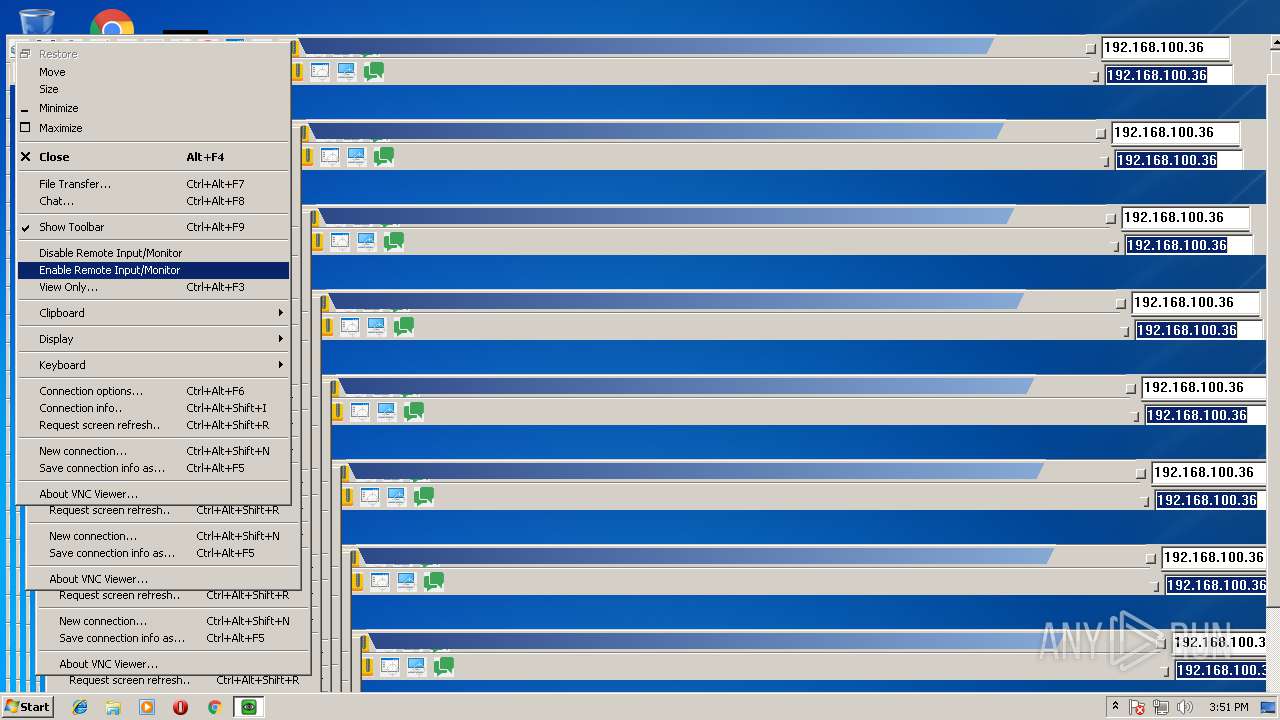
vncviewer.exe | Connected to 192.168.100.36 port 5900
|
vncviewer.exe | DSMPlugin not enabled
|
vncviewer.exe | RFB server supports protocol version 3.8
|
vncviewer.exe | Connected to RFB server, using protocol version 3.8
|
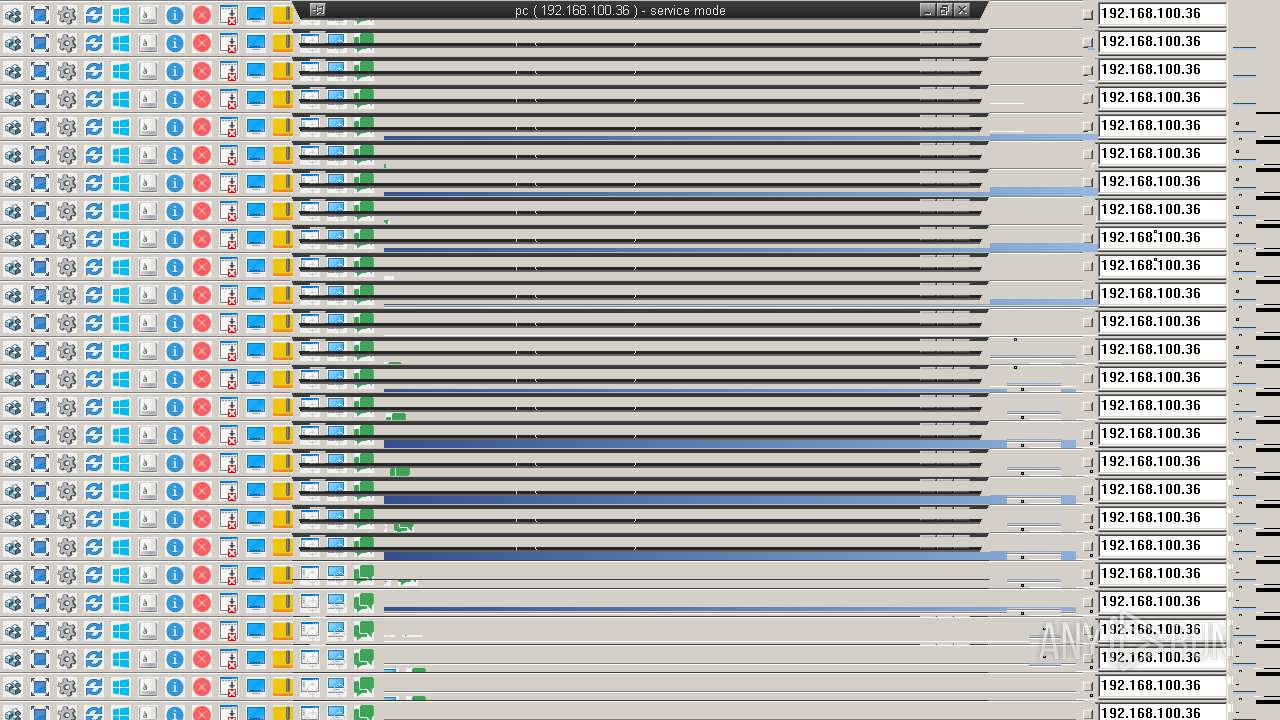
vncviewer.exe | VNC authentication succeeded
|
vncviewer.exe | Desktop name "pc ( 192.168.100.36 ) - service mode "
|
WinVNC.exe | SetHook |
vncviewer.exe | rdr::Exception (1): rdr::SystemException: read: Unknown error (10004)
|