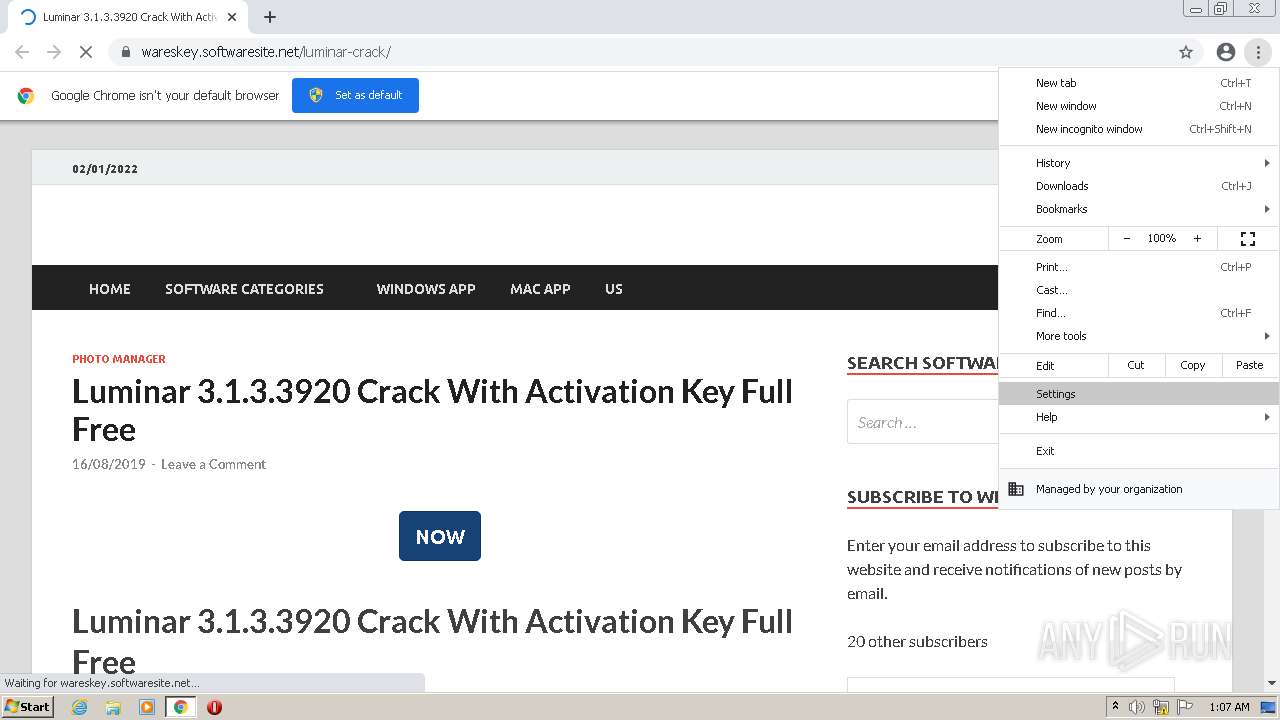
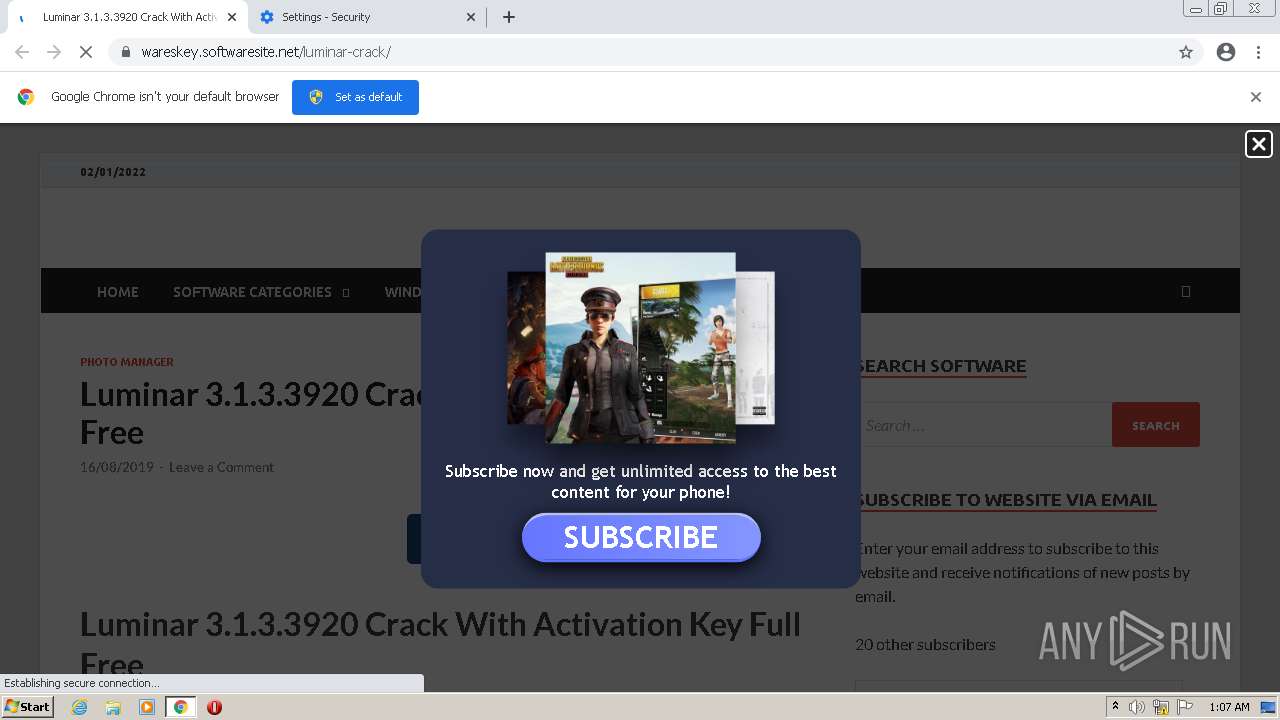
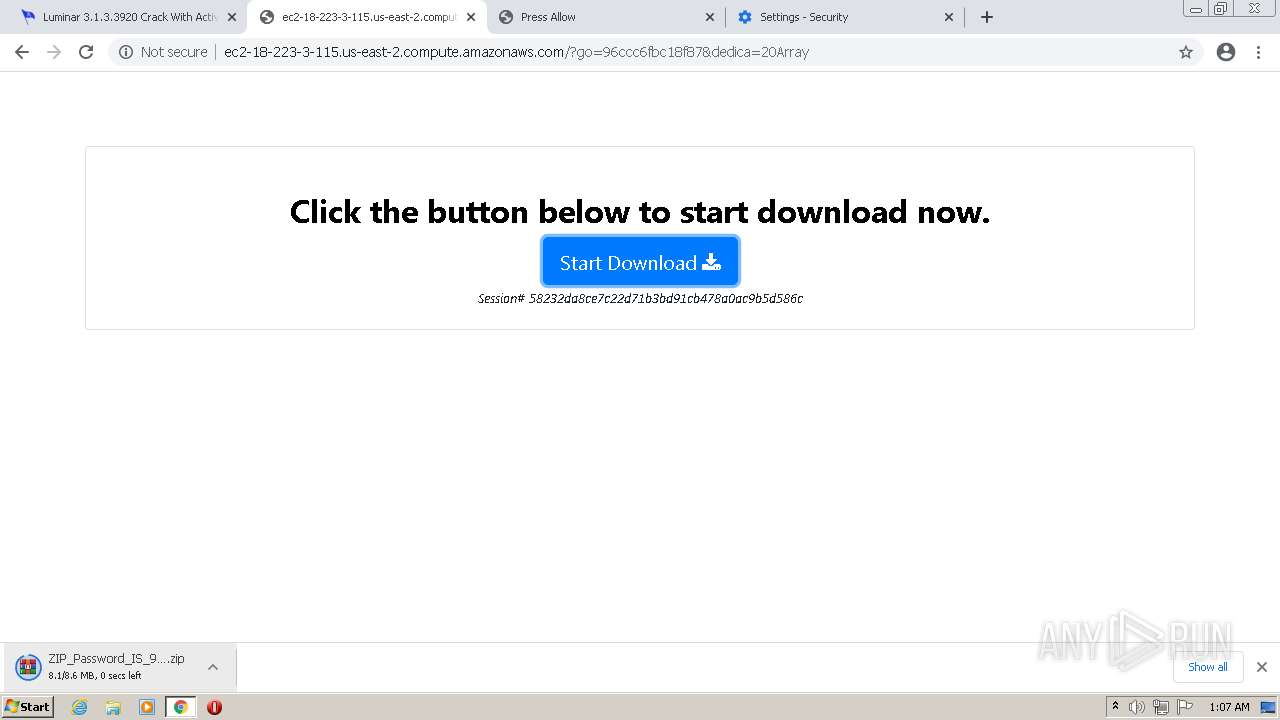
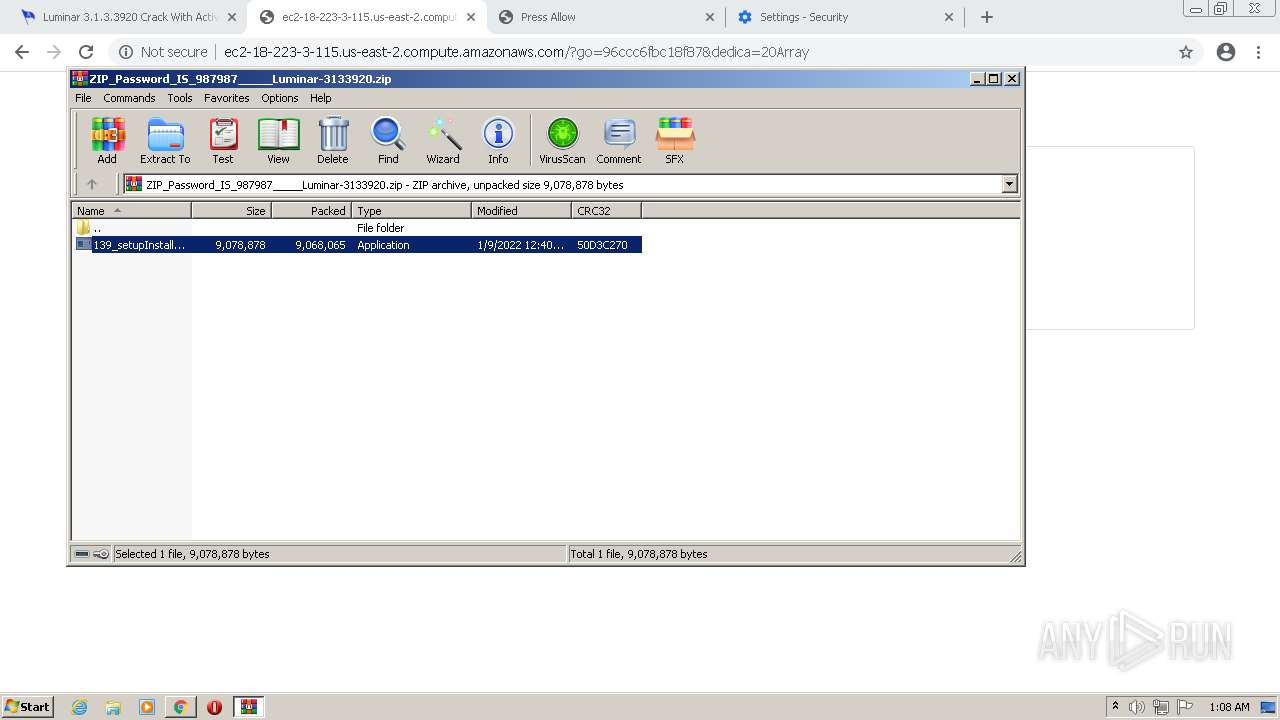
| URL: | https://wareskey.softwaresite.net/luminar-crack/ |
| Full analysis: | https://app.any.run/tasks/99d14158-e5c8-48d9-997e-9efe3752b68e |
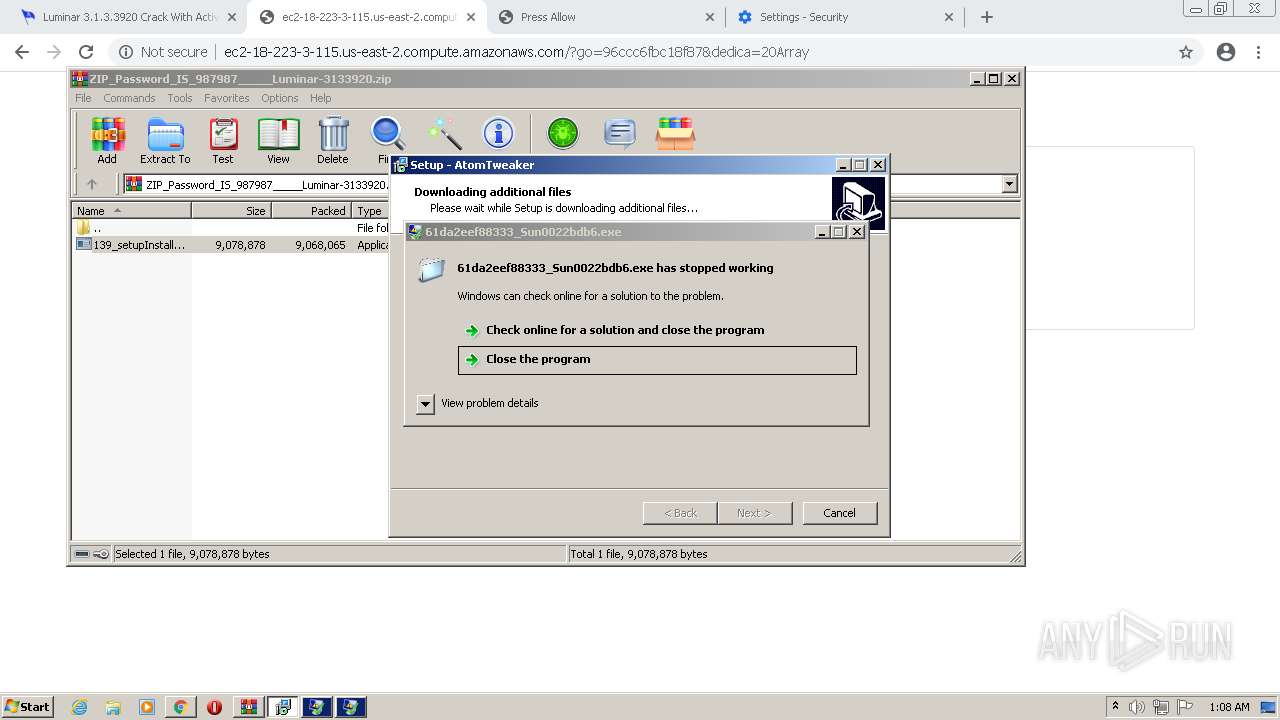
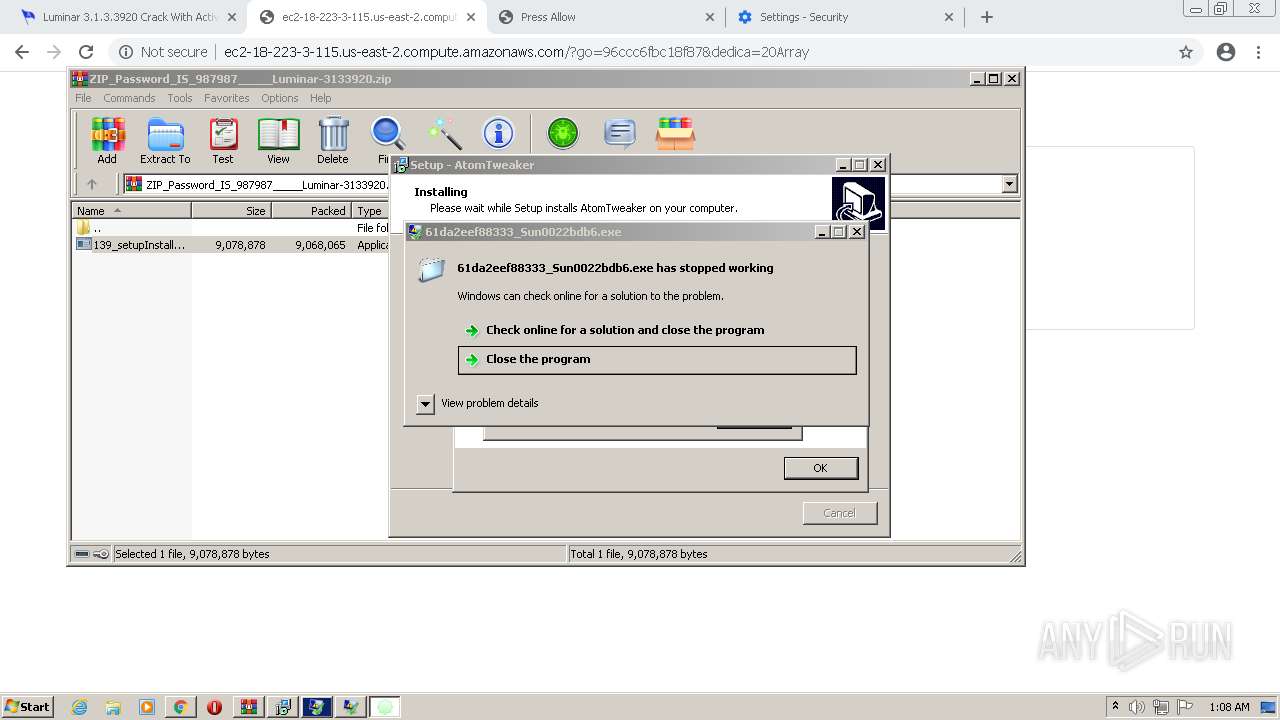
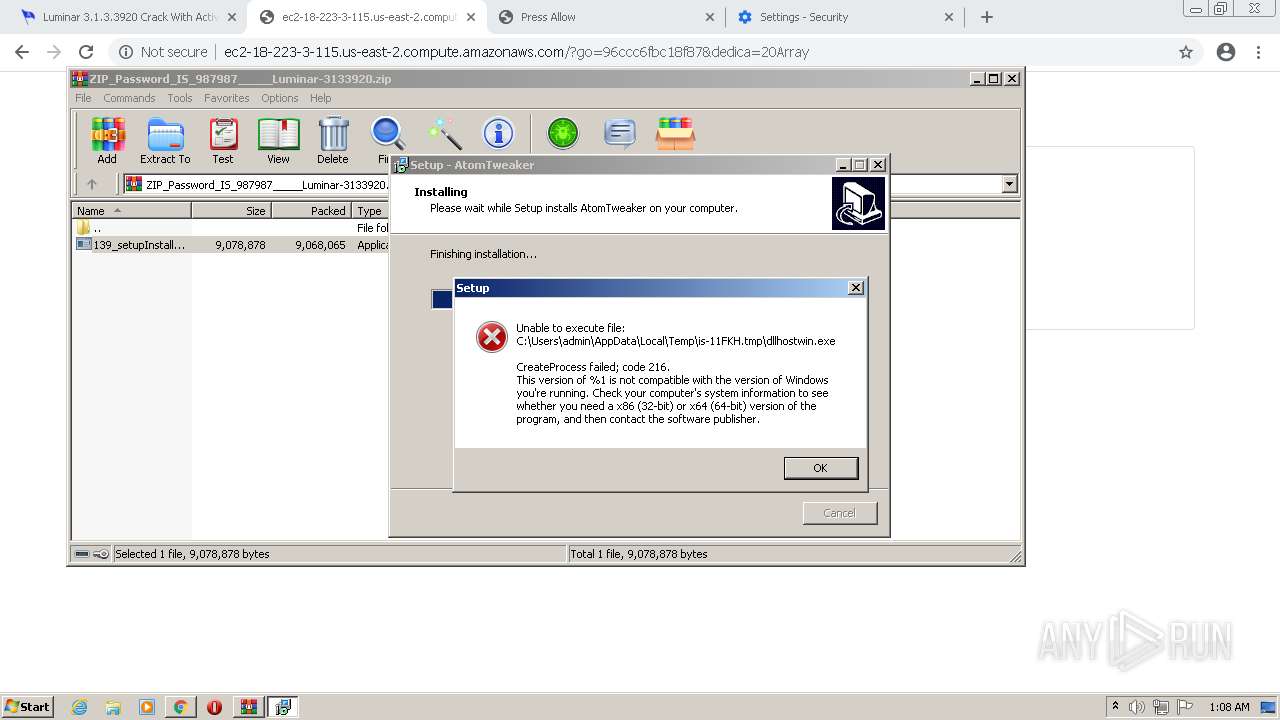
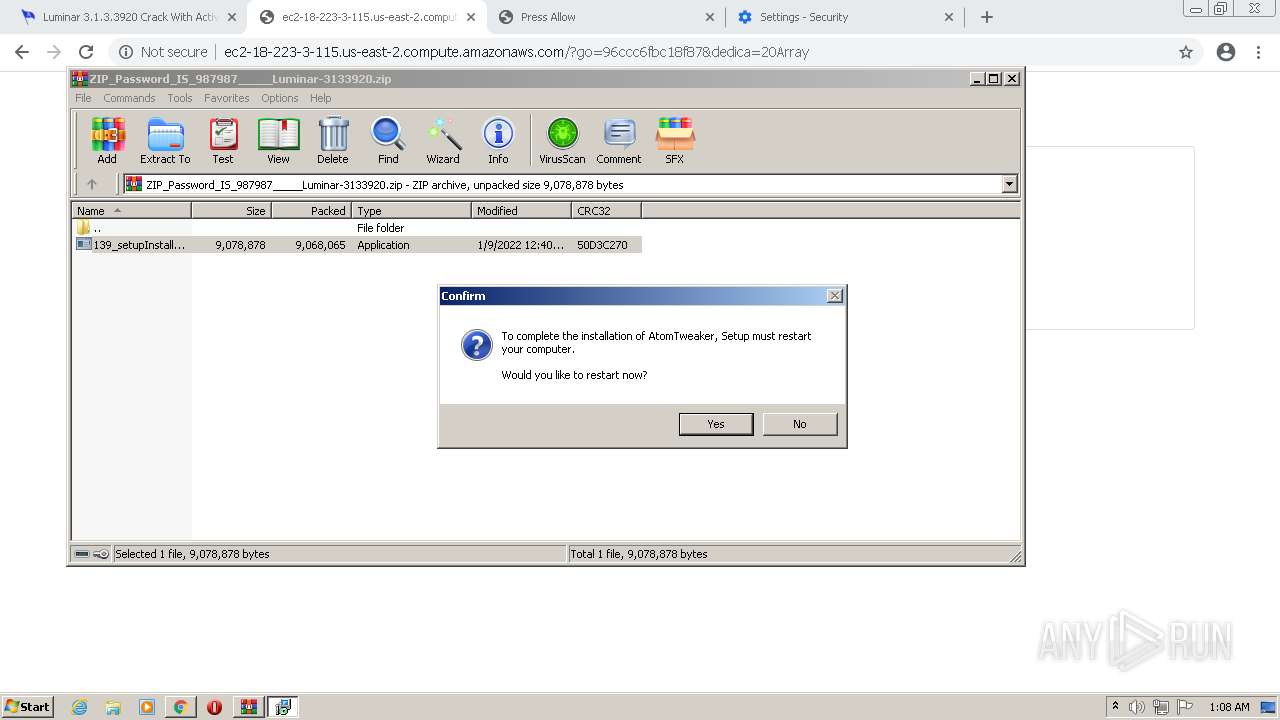
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | January 09, 2022, 01:07:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
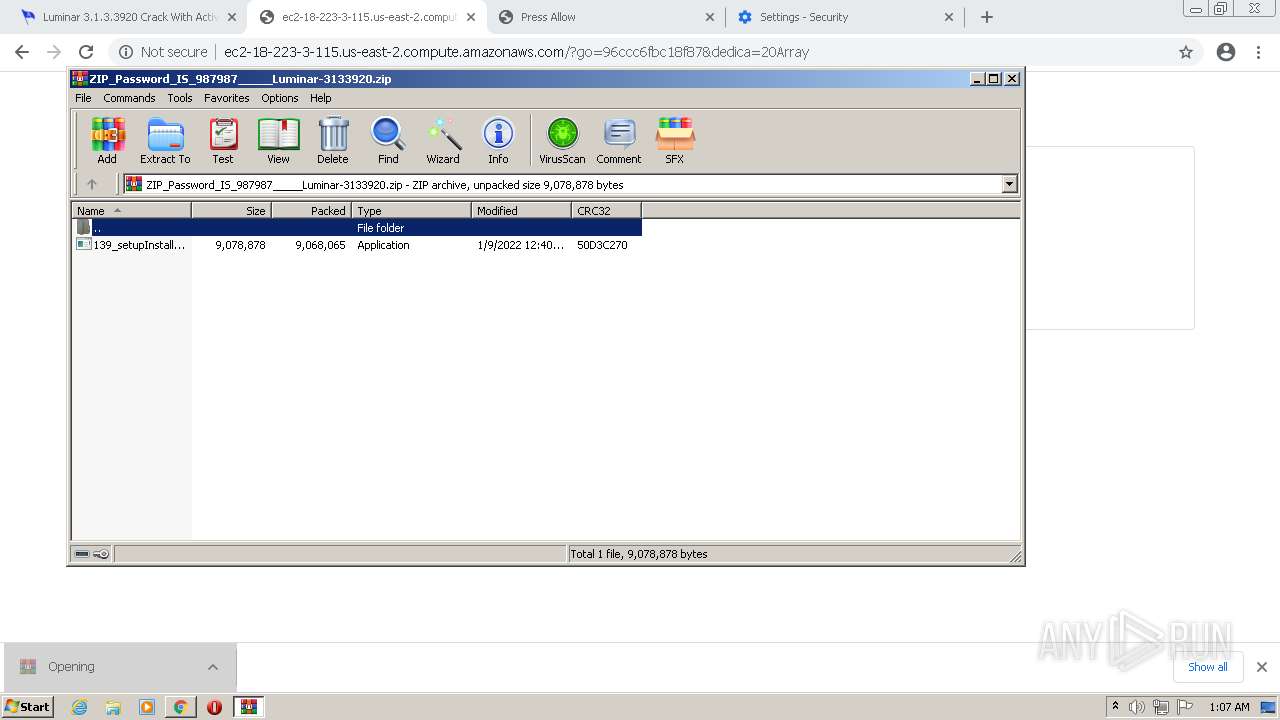
| MD5: | BFF02BAFB6526FFDCCBD9D80A8ABA546 |
| SHA1: | F43D278740768358E65277C4A9CD013B9016341A |
| SHA256: | A8BB72428337E14331707B1B8ADC9A7EF652867D63B64605022B4EBE55693FF0 |
| SSDEEP: | 3:N8VDAAEECexL2XN:2EELNwN |
MALICIOUS
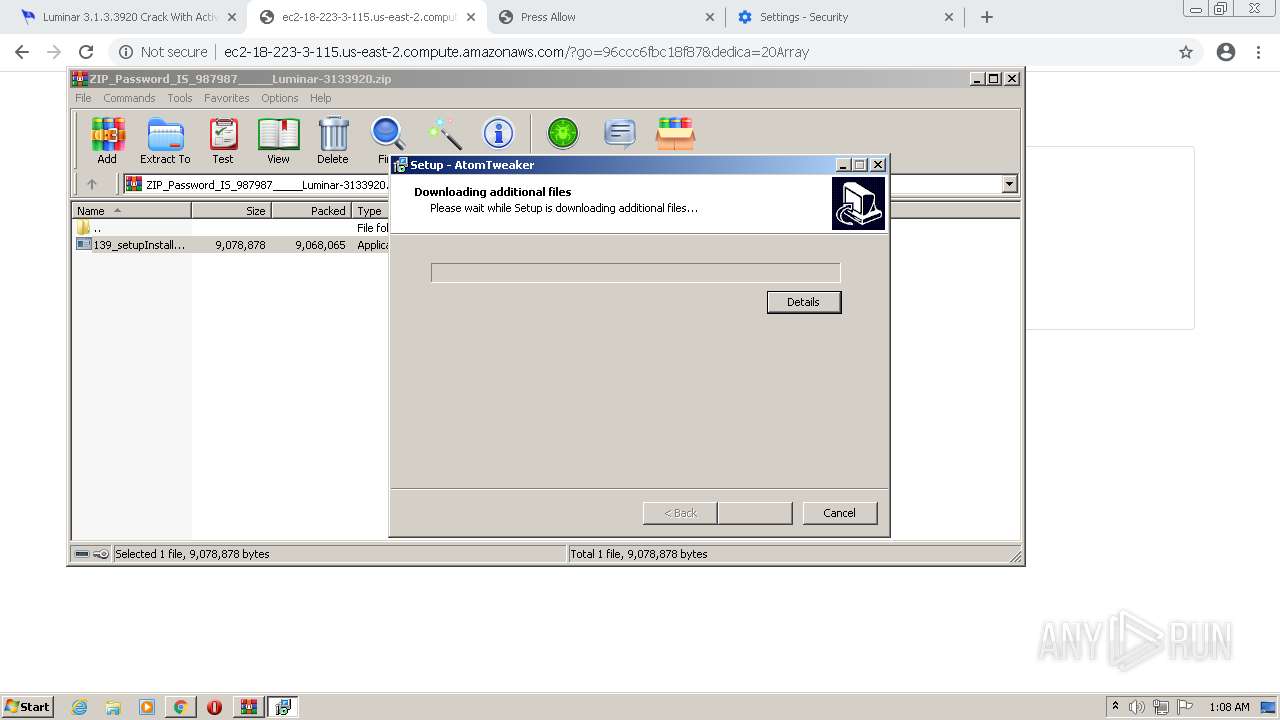
Application was dropped or rewritten from another process
- 139_setupInstaller.exe (PID: 3804)
- setup_installer.exe (PID: 696)
- 61da2ee31ae42_Sun0059a4c0a47.exe (PID: 3496)
- 61da2ee267552_Sun00dbc51a61.exe (PID: 3364)
- 139_setupInstaller.exe (PID: 2172)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 2508)
- 61da2eedb3053_Sun00e80628.exe (PID: 1820)
- 61da2ee31ae42_Sun0059a4c0a47.exe (PID: 5956)
- 61da2ee911f5e_Sun0034f7697f.exe (PID: 3916)
- 61da2ef065ec0_Sun00935fdf6e.exe (PID: 3092)
- 61da2ef2767d7_Sun00d5c0fc069f.exe (PID: 424)
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- setup_install.exe (PID: 1948)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 2972)
- 61da2eee7b42e_Sun007615f757ff.exe (PID: 4848)
- 61da2eef88333_Sun0022bdb6.exe (PID: 4960)
- 61da2eee7b42e_Sun007615f757ff.exe (PID: 5628)
- 61da2ee7bed2e_Sun0006d4e5.exe (PID: 3472)
- 61da2eec8c0b0_Sun000e19af4.exe (PID: 4924)
- 61da2ee267552_Sun00dbc51a61.exe (PID: 4920)
- 61da2eeb98df8_Sun00bd121dfc.exe (PID: 5052)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 5180)
- 1881.tmp.exe (PID: 5308)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 460)
- 1D37.tmp.exe (PID: 3464)
- 4420263701.exe (PID: 3572)
- gP9G4hoQrkhHXGnUvMcK5ro9.exe (PID: 3696)
- 5396712929.exe (PID: 4144)
- anytimepc.exe (PID: 4472)
- myslanewfile.exe (PID: 532)
- Q8tZ9DQWhatOWX4X814XpfQJ.exe (PID: 4828)
- File.exe (PID: 3316)
- TYIU7z3qlzxBdwW2VK_Dxnmo.exe (PID: 2908)
- TYIU7z3qlzxBdwW2VK_Dxnmo.exe (PID: 5988)
- W8qKY42BC_9QKHU7wDi_b32g.exe (PID: 5204)
- Q7Fy6EJgJFk2D4AxrK8Hc0NL.exe (PID: 5216)
- wW9FzscnVHF80slCHphthsyR.exe (PID: 4280)
- c39904ff-91e0-4ea1-9dd1-09411552aee1.exe (PID: 284)
- 7902785479027854.exe (PID: 4544)
- 66139841-4090-468e-9913-fbadb8a51bd1.exe (PID: 4208)
- LzmwAqmV.exe (PID: 5884)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 4228)
- db6b8c06-2204-471c-9f8c-2b03ae94ac92.exe (PID: 5368)
- DpEditor.exe (PID: 472)
- 7252757.exe (PID: 2288)
- 1855194.exe (PID: 3360)
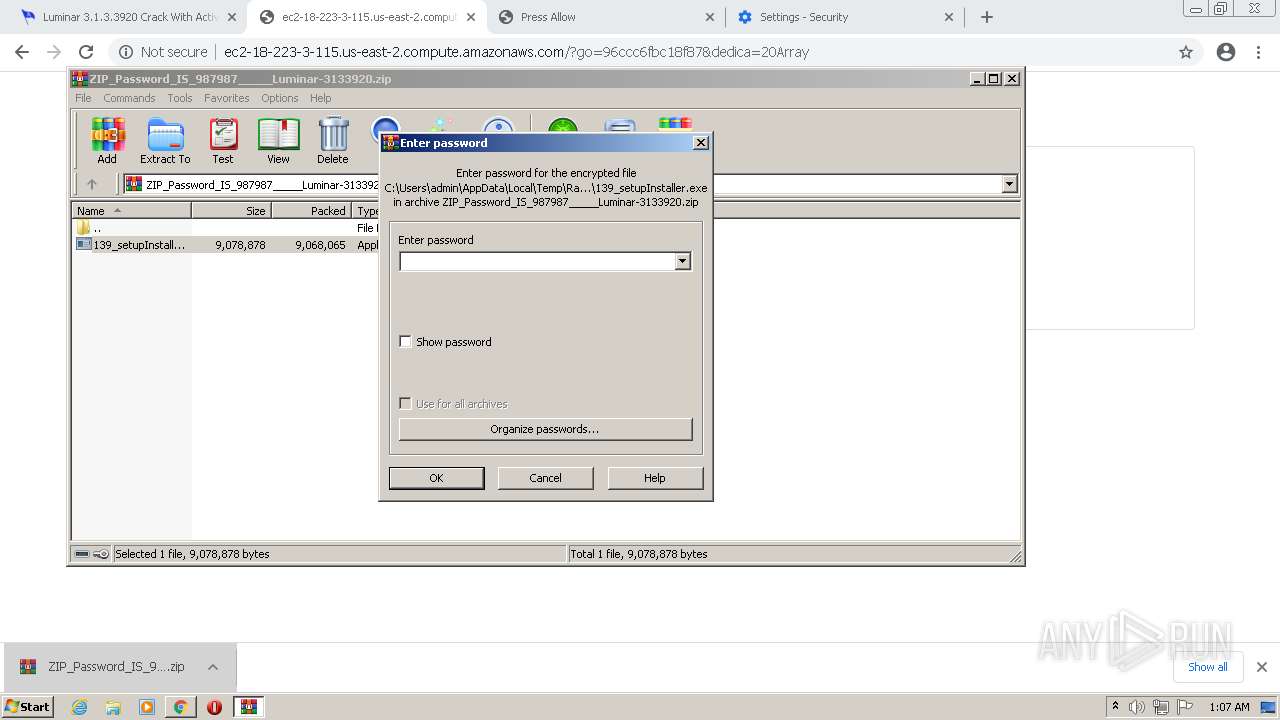
Drops executable file immediately after starts
- setup_installer.exe (PID: 696)
- 61da2ee267552_Sun00dbc51a61.exe (PID: 3364)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3464)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
- LzmwAqmV.exe (PID: 5884)
- gP9G4hoQrkhHXGnUvMcK5ro9.exe (PID: 3696)
- LzmwAqmV.exe (PID: 2068)
- Q7Fy6EJgJFk2D4AxrK8Hc0NL.exe (PID: 5216)
- 66139841-4090-468e-9913-fbadb8a51bd1.exe (PID: 4208)
- Routes License Agreement.exe (PID: 5248)
Executes PowerShell scripts
- cmd.exe (PID: 3696)
- cmd.exe (PID: 2540)
Loads dropped or rewritten executable
- setup_install.exe (PID: 1948)
- rundll32.exe (PID: 4168)
- LzmwAqmV.exe (PID: 2068)
- rundll32.exe (PID: 6028)
- 4420263701.exe (PID: 3572)
- Routes License Agreement.exe (PID: 5248)
Changes settings of System certificates
- 61da2ee31ae42_Sun0059a4c0a47.exe (PID: 5956)
- 61da2ef065ec0_Sun00935fdf6e.exe (PID: 3092)
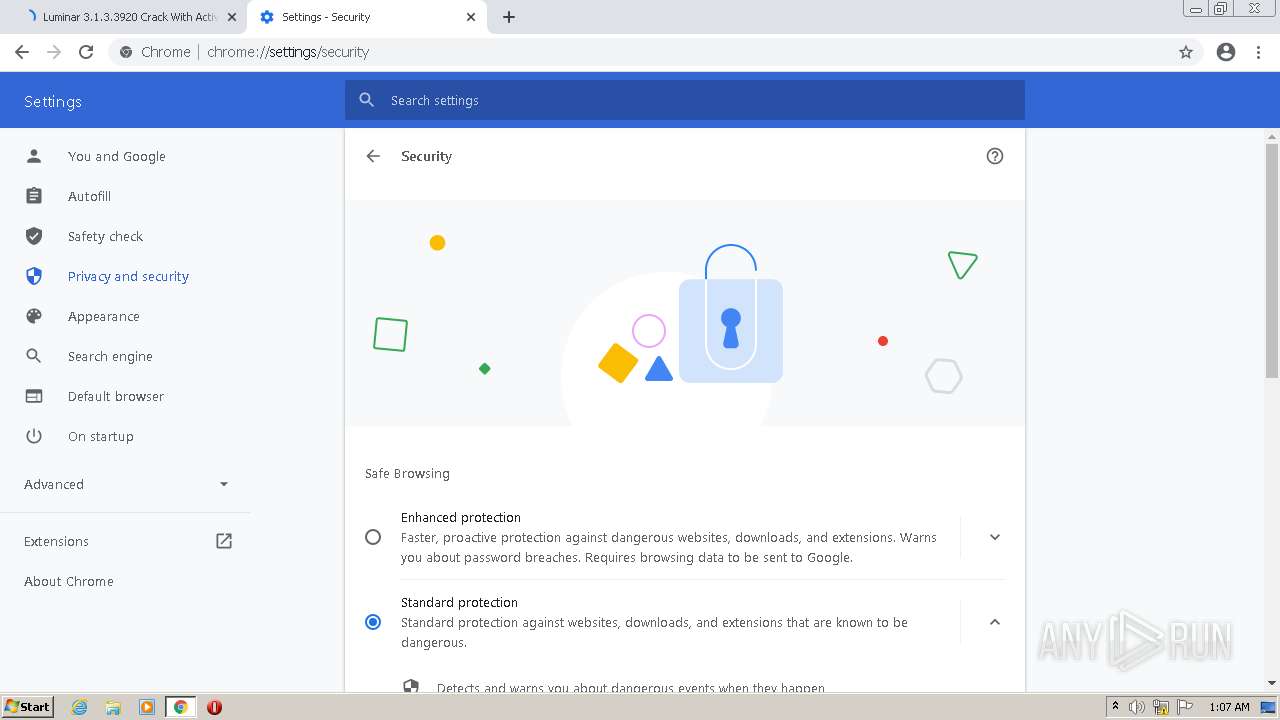
Steals credentials from Web Browsers
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- myslanewfile.exe (PID: 532)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 460)
- 4420263701.exe (PID: 3572)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 4228)
Actions looks like stealing of personal data
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- myslanewfile.exe (PID: 532)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 460)
- c39904ff-91e0-4ea1-9dd1-09411552aee1.exe (PID: 284)
- 4420263701.exe (PID: 3572)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 4228)
Registers / Runs the DLL via REGSVR32.EXE
- 61da2ee7bed2e_Sun0006d4e5.exe (PID: 3472)
Stealing of credential data
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- 4420263701.exe (PID: 3572)
Application was injected by another process
- svchost.exe (PID: 860)
Runs injected code in another process
- rundll32.exe (PID: 4168)
- rundll32.exe (PID: 6028)
Disables Windows Defender
- 61da2ef065ec0_Sun00935fdf6e.exe (PID: 3092)
Writes to a start menu file
- 1D37.tmp.exe (PID: 3464)
Connects to CnC server
- 61da2eeb98df8_Sun00bd121dfc.exe (PID: 5052)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 460)
- myslanewfile.exe (PID: 532)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 4228)
REDLINE was detected
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 460)
- myslanewfile.exe (PID: 532)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 4228)
Changes the autorun value in the registry
- 66139841-4090-468e-9913-fbadb8a51bd1.exe (PID: 4208)
VIDAR was detected
- 4420263701.exe (PID: 3572)
SUSPICIOUS
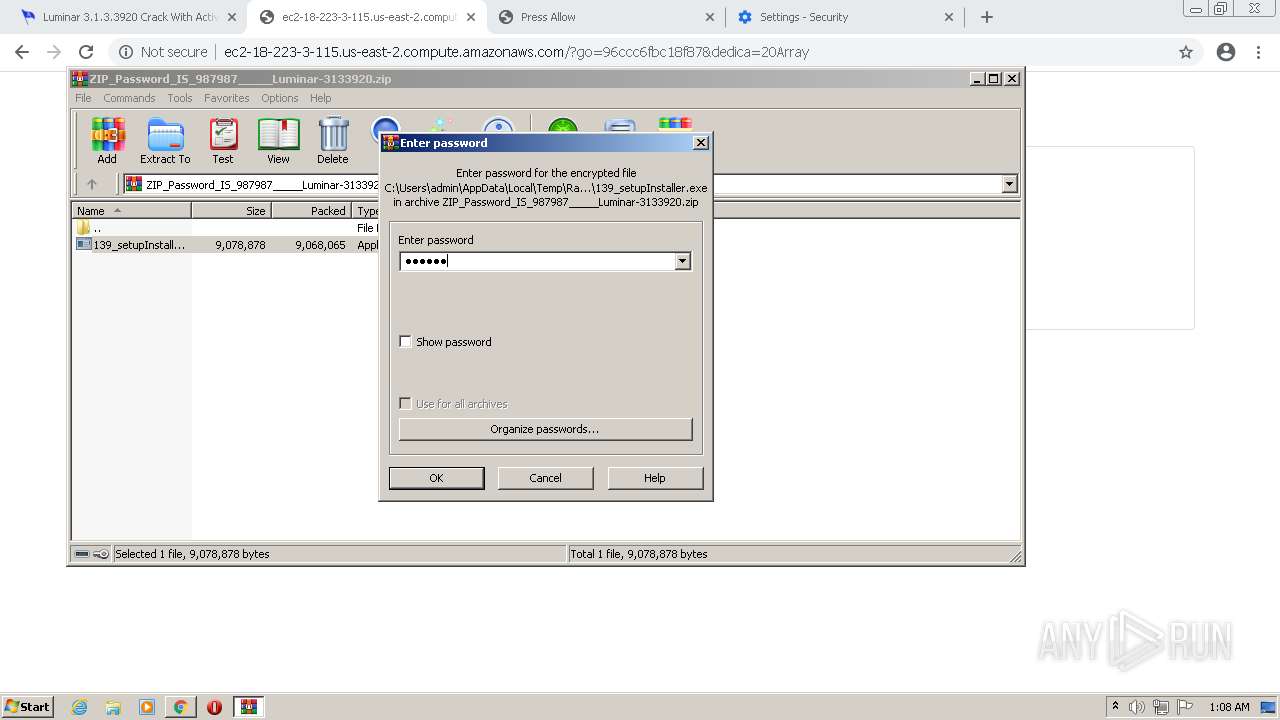
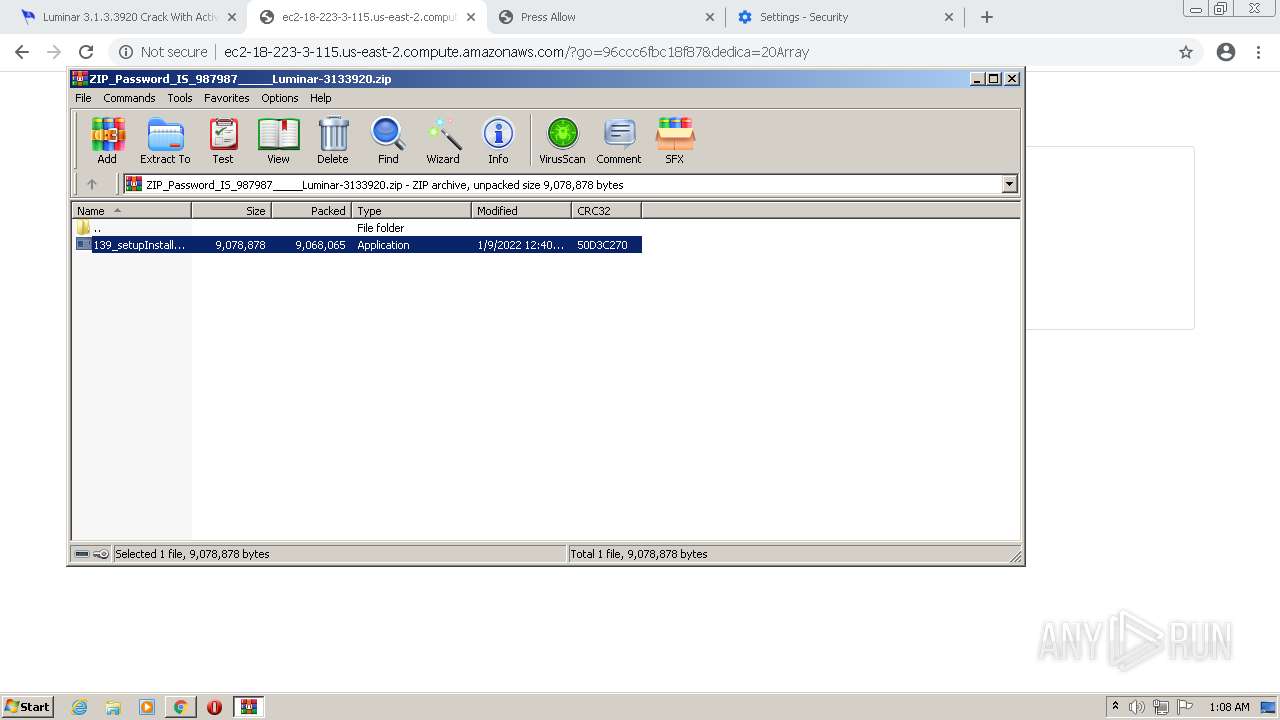
Checks supported languages
- WinRAR.exe (PID: 2672)
- 139_setupInstaller.exe (PID: 3804)
- setup_installer.exe (PID: 696)
- setup_install.exe (PID: 1948)
- cmd.exe (PID: 2540)
- cmd.exe (PID: 976)
- cmd.exe (PID: 3696)
- powershell.exe (PID: 2904)
- 61da2ee267552_Sun00dbc51a61.exe (PID: 3364)
- cmd.exe (PID: 2256)
- powershell.exe (PID: 2888)
- cmd.exe (PID: 1980)
- cmd.exe (PID: 3480)
- 61da2ee31ae42_Sun0059a4c0a47.exe (PID: 3496)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 2884)
- 61da2eedb3053_Sun00e80628.exe (PID: 1820)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 2508)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 2972)
- cmd.exe (PID: 2496)
- cmd.exe (PID: 1056)
- cmd.exe (PID: 3512)
- cmd.exe (PID: 3508)
- cmd.exe (PID: 1368)
- 61da2ee7bed2e_Sun0006d4e5.exe (PID: 3472)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3464)
- 61da2eec8c0b0_Sun000e19af4.exe (PID: 4924)
- 61da2eef88333_Sun0022bdb6.exe (PID: 4960)
- 61da2ee31ae42_Sun0059a4c0a47.exe (PID: 5956)
- powershell.exe (PID: 5148)
- cmd.exe (PID: 2344)
- cmd.exe (PID: 320)
- 61da2ef065ec0_Sun00935fdf6e.exe (PID: 3092)
- cmd.exe (PID: 1496)
- 61da2ef2767d7_Sun00d5c0fc069f.exe (PID: 424)
- 61da2ee911f5e_Sun0034f7697f.exe (PID: 3916)
- cmd.exe (PID: 916)
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- 61da2eee7b42e_Sun007615f757ff.exe (PID: 5628)
- 61da2eeb98df8_Sun00bd121dfc.exe (PID: 5052)
- 61da2eee7b42e_Sun007615f757ff.exe (PID: 4848)
- 61da2ee267552_Sun00dbc51a61.exe (PID: 4920)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
- 1881.tmp.exe (PID: 5308)
- LzmwAqmV.exe (PID: 5884)
- 1D37.tmp.exe (PID: 3464)
- anytimepc.exe (PID: 4472)
- myslanewfile.exe (PID: 532)
- cmd.exe (PID: 4912)
- gP9G4hoQrkhHXGnUvMcK5ro9.exe (PID: 3696)
- 4420263701.exe (PID: 3572)
- cmd.exe (PID: 3500)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 460)
- LzmwAqmV.exe (PID: 2068)
- cmd.exe (PID: 2820)
- 5396712929.exe (PID: 4144)
- Q8tZ9DQWhatOWX4X814XpfQJ.exe (PID: 4828)
- TYIU7z3qlzxBdwW2VK_Dxnmo.exe (PID: 5988)
- TYIU7z3qlzxBdwW2VK_Dxnmo.exe (PID: 2908)
- svchost.exe (PID: 860)
- File.exe (PID: 3316)
- cmd.exe (PID: 5916)
- wW9FzscnVHF80slCHphthsyR.exe (PID: 4280)
- cmd.exe (PID: 4756)
- W8qKY42BC_9QKHU7wDi_b32g.exe (PID: 5204)
- Q7Fy6EJgJFk2D4AxrK8Hc0NL.exe (PID: 5216)
- c39904ff-91e0-4ea1-9dd1-09411552aee1.exe (PID: 284)
- 66139841-4090-468e-9913-fbadb8a51bd1.exe (PID: 4208)
- 7902785479027854.exe (PID: 4544)
- db6b8c06-2204-471c-9f8c-2b03ae94ac92.exe (PID: 5368)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 4228)
- 7252757.exe (PID: 2288)
- DpEditor.exe (PID: 472)
- cmd.exe (PID: 5336)
- 1855194.exe (PID: 3360)
- Routes License Agreement.exe (PID: 5248)
Reads the computer name
- WinRAR.exe (PID: 2672)
- 139_setupInstaller.exe (PID: 3804)
- setup_installer.exe (PID: 696)
- powershell.exe (PID: 2904)
- powershell.exe (PID: 2888)
- setup_install.exe (PID: 1948)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 2508)
- 61da2ee7bed2e_Sun0006d4e5.exe (PID: 3472)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 2972)
- 61da2eedb3053_Sun00e80628.exe (PID: 1820)
- 61da2ee31ae42_Sun0059a4c0a47.exe (PID: 3496)
- 61da2eef88333_Sun0022bdb6.exe (PID: 4960)
- powershell.exe (PID: 5148)
- 61da2ee31ae42_Sun0059a4c0a47.exe (PID: 5956)
- 61da2eec8c0b0_Sun000e19af4.exe (PID: 4924)
- 61da2ee911f5e_Sun0034f7697f.exe (PID: 3916)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3464)
- 61da2eee7b42e_Sun007615f757ff.exe (PID: 5628)
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- 61da2ef065ec0_Sun00935fdf6e.exe (PID: 3092)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
- 61da2eeb98df8_Sun00bd121dfc.exe (PID: 5052)
- LzmwAqmV.exe (PID: 5884)
- 1881.tmp.exe (PID: 5308)
- anytimepc.exe (PID: 4472)
- myslanewfile.exe (PID: 532)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 460)
- LzmwAqmV.exe (PID: 2068)
- TYIU7z3qlzxBdwW2VK_Dxnmo.exe (PID: 2908)
- TYIU7z3qlzxBdwW2VK_Dxnmo.exe (PID: 5988)
- wW9FzscnVHF80slCHphthsyR.exe (PID: 4280)
- Q8tZ9DQWhatOWX4X814XpfQJ.exe (PID: 4828)
- W8qKY42BC_9QKHU7wDi_b32g.exe (PID: 5204)
- 4420263701.exe (PID: 3572)
- Q7Fy6EJgJFk2D4AxrK8Hc0NL.exe (PID: 5216)
- c39904ff-91e0-4ea1-9dd1-09411552aee1.exe (PID: 284)
- 66139841-4090-468e-9913-fbadb8a51bd1.exe (PID: 4208)
- 7902785479027854.exe (PID: 4544)
- db6b8c06-2204-471c-9f8c-2b03ae94ac92.exe (PID: 5368)
- 7252757.exe (PID: 2288)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 4228)
- 1855194.exe (PID: 3360)
- Routes License Agreement.exe (PID: 5248)
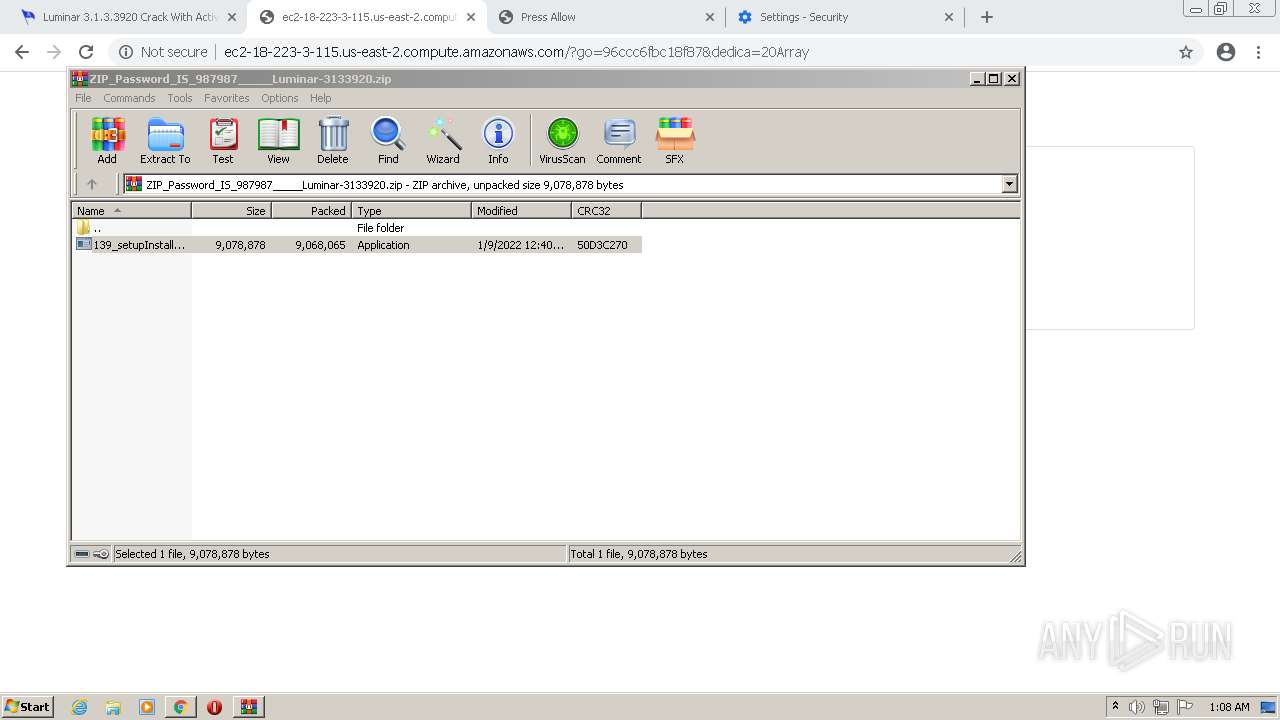
Executable content was dropped or overwritten
- 139_setupInstaller.exe (PID: 3804)
- WinRAR.exe (PID: 2672)
- setup_installer.exe (PID: 696)
- 61da2ee267552_Sun00dbc51a61.exe (PID: 3364)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3464)
- 61da2ee267552_Sun00dbc51a61.exe (PID: 4920)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
- 61da2ee31ae42_Sun0059a4c0a47.exe (PID: 5956)
- 61da2eedb3053_Sun00e80628.exe (PID: 1820)
- 61da2ee911f5e_Sun0034f7697f.exe (PID: 3916)
- 61da2eeb98df8_Sun00bd121dfc.exe (PID: 5052)
- gP9G4hoQrkhHXGnUvMcK5ro9.exe (PID: 3696)
- 61da2ef065ec0_Sun00935fdf6e.exe (PID: 3092)
- 1D37.tmp.exe (PID: 3464)
- LzmwAqmV.exe (PID: 2068)
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- Q7Fy6EJgJFk2D4AxrK8Hc0NL.exe (PID: 5216)
- wW9FzscnVHF80slCHphthsyR.exe (PID: 4280)
- LzmwAqmV.exe (PID: 5884)
- 66139841-4090-468e-9913-fbadb8a51bd1.exe (PID: 4208)
- 4420263701.exe (PID: 3572)
- TYIU7z3qlzxBdwW2VK_Dxnmo.exe (PID: 5988)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 2508)
- db6b8c06-2204-471c-9f8c-2b03ae94ac92.exe (PID: 5368)
- File.exe (PID: 3316)
- 61da2eec8c0b0_Sun000e19af4.exe (PID: 4924)
- Routes License Agreement.exe (PID: 5248)
Drops a file with too old compile date
- setup_installer.exe (PID: 696)
- 61da2ee267552_Sun00dbc51a61.exe (PID: 3364)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3464)
- 61da2ee267552_Sun00dbc51a61.exe (PID: 4920)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
- 61da2eeb98df8_Sun00bd121dfc.exe (PID: 5052)
Drops a file with a compile date too recent
- setup_installer.exe (PID: 696)
- 61da2ee31ae42_Sun0059a4c0a47.exe (PID: 5956)
- 61da2eedb3053_Sun00e80628.exe (PID: 1820)
- 61da2ee911f5e_Sun0034f7697f.exe (PID: 3916)
- LzmwAqmV.exe (PID: 5884)
- 61da2ef065ec0_Sun00935fdf6e.exe (PID: 3092)
- Q7Fy6EJgJFk2D4AxrK8Hc0NL.exe (PID: 5216)
- wW9FzscnVHF80slCHphthsyR.exe (PID: 4280)
- 66139841-4090-468e-9913-fbadb8a51bd1.exe (PID: 4208)
- TYIU7z3qlzxBdwW2VK_Dxnmo.exe (PID: 5988)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 2508)
- 61da2eec8c0b0_Sun000e19af4.exe (PID: 4924)
- Routes License Agreement.exe (PID: 5248)
Drops a file that was compiled in debug mode
- setup_installer.exe (PID: 696)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3464)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
- LzmwAqmV.exe (PID: 5884)
- 61da2ee911f5e_Sun0034f7697f.exe (PID: 3916)
- 1D37.tmp.exe (PID: 3464)
- 61da2ef065ec0_Sun00935fdf6e.exe (PID: 3092)
- Q7Fy6EJgJFk2D4AxrK8Hc0NL.exe (PID: 5216)
- 4420263701.exe (PID: 3572)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 2508)
- db6b8c06-2204-471c-9f8c-2b03ae94ac92.exe (PID: 5368)
- Routes License Agreement.exe (PID: 5248)
Starts CMD.EXE for commands execution
- setup_install.exe (PID: 1948)
- 61da2ee911f5e_Sun0034f7697f.exe (PID: 3916)
- 61da2eeb98df8_Sun00bd121dfc.exe (PID: 5052)
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- Q8tZ9DQWhatOWX4X814XpfQJ.exe (PID: 4828)
- 4420263701.exe (PID: 3572)
Reads Environment values
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 2508)
- 61da2eedb3053_Sun00e80628.exe (PID: 1820)
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- 1881.tmp.exe (PID: 5308)
- anytimepc.exe (PID: 4472)
- myslanewfile.exe (PID: 532)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 460)
- wW9FzscnVHF80slCHphthsyR.exe (PID: 4280)
- c39904ff-91e0-4ea1-9dd1-09411552aee1.exe (PID: 284)
- db6b8c06-2204-471c-9f8c-2b03ae94ac92.exe (PID: 5368)
- 4420263701.exe (PID: 3572)
- 61da2eec8c0b0_Sun000e19af4.exe (PID: 4924)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 4228)
Executes PowerShell scripts
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 2508)
Application launched itself
- 61da2ee31ae42_Sun0059a4c0a47.exe (PID: 3496)
- 61da2eee7b42e_Sun007615f757ff.exe (PID: 4848)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 2972)
- TYIU7z3qlzxBdwW2VK_Dxnmo.exe (PID: 2908)
Reads the Windows organization settings
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3464)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
Reads Windows owner or organization settings
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3464)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
Reads CPU info
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- 4420263701.exe (PID: 3572)
Adds / modifies Windows certificates
- 61da2ee31ae42_Sun0059a4c0a47.exe (PID: 5956)
- 61da2ef065ec0_Sun00935fdf6e.exe (PID: 3092)
Reads the cookies of Mozilla Firefox
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- myslanewfile.exe (PID: 532)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 460)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 4228)
Creates files in the user directory
- 61da2ee911f5e_Sun0034f7697f.exe (PID: 3916)
- 1D37.tmp.exe (PID: 3464)
- 66139841-4090-468e-9913-fbadb8a51bd1.exe (PID: 4208)
- db6b8c06-2204-471c-9f8c-2b03ae94ac92.exe (PID: 5368)
- File.exe (PID: 3316)
- Routes License Agreement.exe (PID: 5248)
Executed via WMI
- rundll32.exe (PID: 4168)
- rundll32.exe (PID: 6028)
Searches for installed software
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 460)
- myslanewfile.exe (PID: 532)
- c39904ff-91e0-4ea1-9dd1-09411552aee1.exe (PID: 284)
- 4420263701.exe (PID: 3572)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 4228)
Starts CMD.EXE for self-deleting
- 61da2ee911f5e_Sun0034f7697f.exe (PID: 3916)
- 61da2ee3eb808_Sun00e9d2f77.exe (PID: 1904)
- 4420263701.exe (PID: 3572)
Creates a directory in Program Files
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
Reads mouse settings
- 5396712929.exe (PID: 4144)
Checks for external IP
- 61da2ef065ec0_Sun00935fdf6e.exe (PID: 3092)
Reads the cookies of Google Chrome
- 61da2eea12110_Sun00793d9cfe20.exe (PID: 460)
- myslanewfile.exe (PID: 532)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 4228)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 4756)
- cmd.exe (PID: 5336)
Starts itself from another location
- 66139841-4090-468e-9913-fbadb8a51bd1.exe (PID: 4208)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 2508)
- File.exe (PID: 3316)
Creates files in the program directory
- 4420263701.exe (PID: 3572)
- 61da2eec8c0b0_Sun000e19af4.exe (PID: 4924)
Reads default file associations for system extensions
- 7252757.exe (PID: 2288)
Uses RUNDLL32.EXE to load library
- control.exe (PID: 4252)
INFO
Application launched itself
- chrome.exe (PID: 3160)
Checks supported languages
- chrome.exe (PID: 2564)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 2468)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 344)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3336)
- chrome.exe (PID: 904)
- chrome.exe (PID: 396)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 1836)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 388)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 2144)
- chrome.exe (PID: 3004)
- regsvr32.exe (PID: 5420)
- rundll32.exe (PID: 4168)
- PING.EXE (PID: 5092)
- chrome.exe (PID: 2540)
- timeout.exe (PID: 2460)
- taskkill.exe (PID: 4748)
- rundll32.exe (PID: 6028)
- taskkill.exe (PID: 2420)
- timeout.exe (PID: 4992)
- control.exe (PID: 4252)
- chrome.exe (PID: 4844)
- rundll32.exe (PID: 388)
Reads the hosts file
- chrome.exe (PID: 3160)
- chrome.exe (PID: 2072)
Reads the computer name
- chrome.exe (PID: 4052)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 388)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 3004)
- rundll32.exe (PID: 4168)
- PING.EXE (PID: 5092)
- chrome.exe (PID: 2540)
- taskkill.exe (PID: 4748)
- rundll32.exe (PID: 6028)
- taskkill.exe (PID: 2420)
- control.exe (PID: 4252)
Reads settings of System Certificates
- chrome.exe (PID: 2072)
- 61da2ee31ae42_Sun0059a4c0a47.exe (PID: 5956)
- 61da2ee911f5e_Sun0034f7697f.exe (PID: 3916)
- 61da2eef88333_Sun0022bdb6.exe (PID: 4960)
- powershell.exe (PID: 2888)
- powershell.exe (PID: 2904)
- 61da2ef065ec0_Sun00935fdf6e.exe (PID: 3092)
- 61da2eedb3053_Sun00e80628.exe (PID: 1820)
- anytimepc.exe (PID: 4472)
- LzmwAqmV.exe (PID: 2068)
- TYIU7z3qlzxBdwW2VK_Dxnmo.exe (PID: 5988)
- wW9FzscnVHF80slCHphthsyR.exe (PID: 4280)
- 4420263701.exe (PID: 3572)
- db6b8c06-2204-471c-9f8c-2b03ae94ac92.exe (PID: 5368)
- c39904ff-91e0-4ea1-9dd1-09411552aee1.exe (PID: 284)
- 61da2eea58c05_Sun006b9a97ec1.exe (PID: 2508)
- 61da2eec8c0b0_Sun000e19af4.exe (PID: 4924)
Reads the date of Windows installation
- chrome.exe (PID: 3004)
Checks Windows Trust Settings
- powershell.exe (PID: 2888)
- powershell.exe (PID: 2904)
- powershell.exe (PID: 5148)
- 61da2eef88333_Sun0022bdb6.exe (PID: 4960)
- 61da2ee911f5e_Sun0034f7697f.exe (PID: 3916)
- 61da2ef065ec0_Sun00935fdf6e.exe (PID: 3092)
- LzmwAqmV.exe (PID: 2068)
- 4420263701.exe (PID: 3572)
Loads dropped or rewritten executable
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3464)
Application was dropped or rewritten from another process
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3464)
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
Creates files in the program directory
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
Creates a software uninstall entry
- 61da2ee267552_Sun00dbc51a61.tmp (PID: 3652)
Dropped object may contain Bitcoin addresses
- 4420263701.exe (PID: 3572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
165
Monitored processes
110
Malicious processes
41
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Users\admin\AppData\Local\c39904ff-91e0-4ea1-9dd1-09411552aee1.exe" | C:\Users\admin\AppData\Local\c39904ff-91e0-4ea1-9dd1-09411552aee1.exe | wW9FzscnVHF80slCHphthsyR.exe | ||||||||||||
User: admin Company: gsdufsdfhw Integrity Level: HIGH Description: gsdufsdfhw Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 320 | C:\Windows\system32\cmd.exe /c 61da2ee3eb808_Sun00e9d2f77.exe | C:\Windows\system32\cmd.exe | — | setup_install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,6310239344549221109,16280871944150092008,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,6310239344549221109,16280871944150092008,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4736 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 388 | "C:\Windows\system32\rundll32.exe" Shell32.dll,Control_RunDLL "C:\Users\admin\AppData\Local\Temp\P6GJMOn6.cpl", | C:\Windows\system32\rundll32.exe | — | control.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,6310239344549221109,16280871944150092008,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --disable-client-side-phishing-detection --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 424 | 61da2ef2767d7_Sun00d5c0fc069f.exe | C:\Users\admin\AppData\Local\Temp\7zS8B29BBE1\61da2ef2767d7_Sun00d5c0fc069f.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 460 | C:\Users\admin\AppData\Local\Temp\7zS8B29BBE1\61da2eea12110_Sun00793d9cfe20.exe | C:\Users\admin\AppData\Local\Temp\7zS8B29BBE1\61da2eea12110_Sun00793d9cfe20.exe | 61da2eea12110_Sun00793d9cfe20.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 472 | "C:\Users\admin\AppData\Roaming\NCH Software\DrawPad\DpEditor.exe" | C:\Users\admin\AppData\Roaming\NCH Software\DrawPad\DpEditor.exe | — | File.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 532 | "C:\Users\admin\AppData\Local\Temp\myslanewfile.exe" | C:\Users\admin\AppData\Local\Temp\myslanewfile.exe | LzmwAqmV.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
103 830
Read events
102 626
Write events
1 171
Delete events
33
Modification events
| (PID) Process: | (3160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3160) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
102
Suspicious files
64
Text files
126
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61DA353C-C58.pma | — | |
MD5:— | SHA256:— | |||
| 3160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ebe0cf9c-8a11-4a7f-8822-f27546284d43.tmp | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF112d56.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF112e7f.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 3160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
85
TCP/UDP connections
168
DNS requests
103
Threats
180
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
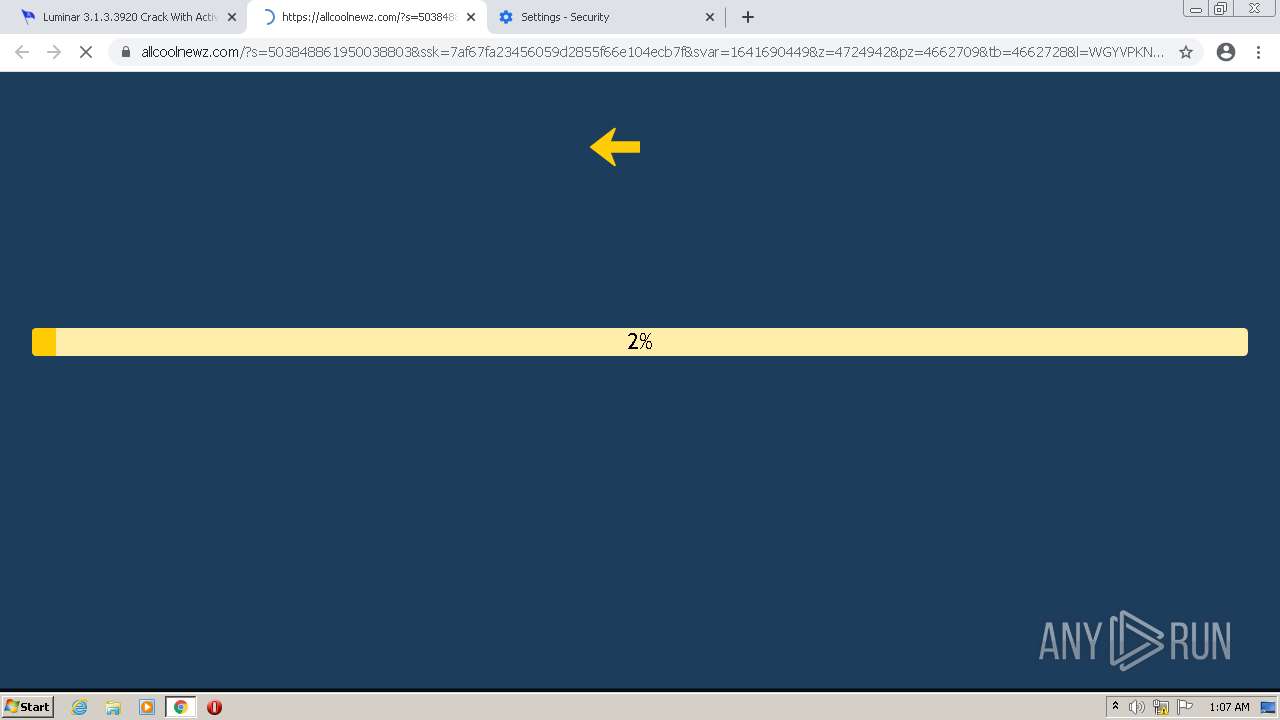
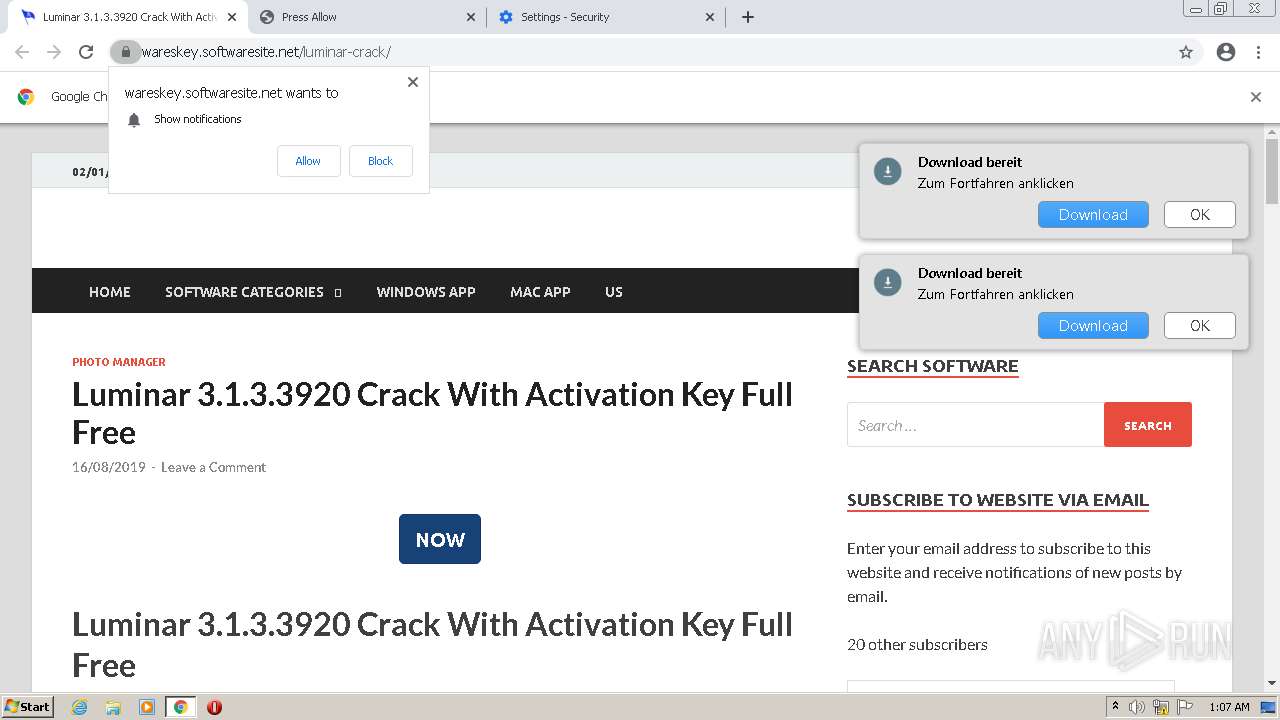
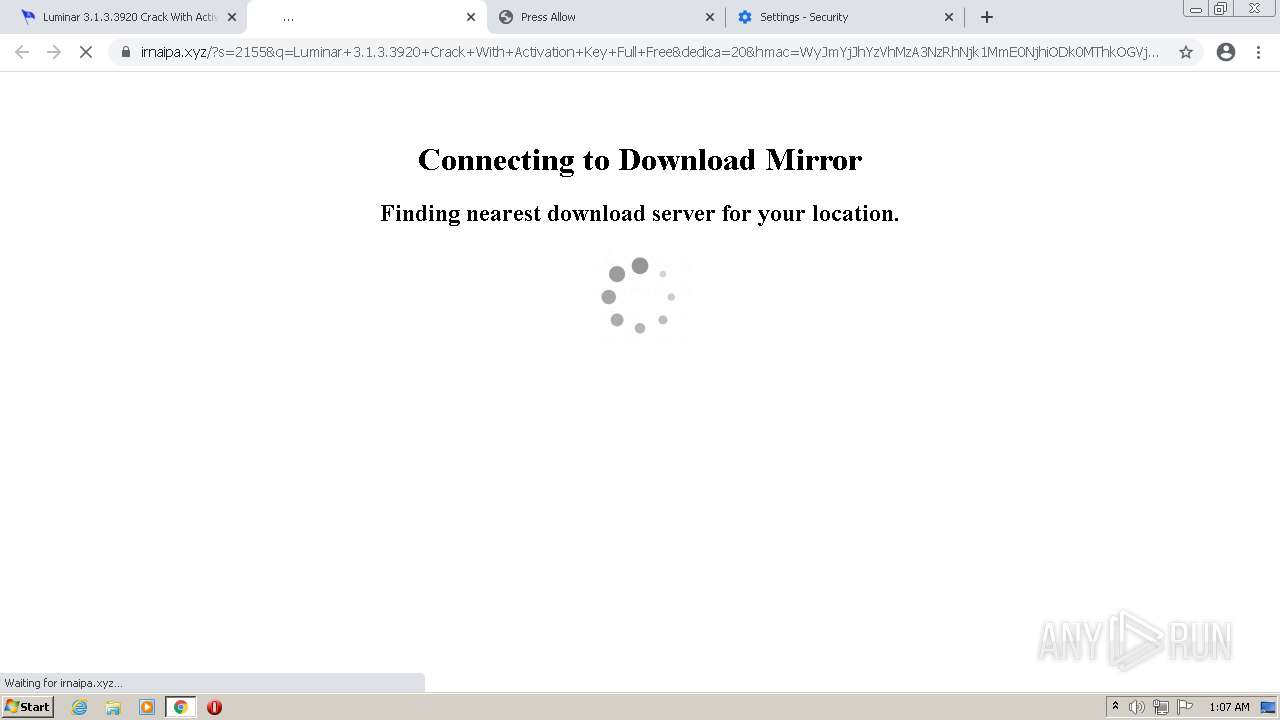
2072 | chrome.exe | GET | 301 | 104.21.14.19:80 | http://irnaipa.xyz/?s=2155&q=Luminar+3.1.3.3920+Crack+With+Activation+Key+Full+Free&dedica=20&hmac=WyJmYjJhYzVhMzA3NzRhNjk1MmE0NjhiODk0MThkOGVjNjY4MGY5NGYzIiwiOTA1MWVjNDlmYjg1NmNjZDQwNTk2Mjk0NmRmOGQ1YmNmNDU0YjJmYSIsImQ2ZTgxZjI5Mzc1MDFhNGY1NjgzOWU0MmIzOWMzMmQ1ZTg3NTFkOTgiLCJlZWZjNTU5ZWUzNjdjZDA1NzRiMzRjZTEyNDIzMjBhZjNkZmQ3MmY1IiwiZmMzZTdlZTA4ODcyZmZiNWE4ZjgzMjMxMGQxNGYwOWVmYzkzZjUyNyIsIjdlNzAwZTg5MTI1M2Y2ZGExMWI5NjMwZGE0ODAzNGJkNmU4NDljNGYiLCI4OWI1NWQ5ZjViZTJhNTk1ODRiMTVlMzFlYTdiNzVjNjVlZDk1N2EyIiwiMGMxNWYzN2UyODFhZjc2OTRhNDEwYTJmM2RmZjlmYzc0MjI2NzcxNiIsImJkZmY0NmZkYWU1ZmZlNTcwNDgxMDBlYTc5YTBmNTVkOTFmNjNhYTEiLCJkZTA5M2JjNDNjYTNhNDE2NzQ0ZTI4ZjQwMjZjZWJiOWViMjYxMTE1IiwiYTUxZjczMjg0ODBlNjkxMWVmZjcyYTA0ZTJjNmEzNjgwYmUxMTliNCJd | US | — | — | malicious |
5628 | 61da2eee7b42e_Sun007615f757ff.exe | GET | — | 37.220.10.229:80 | http://ad-postback.biz/stats/1.php?pub=/mixtwo&badparam=NOPE | GB | — | — | malicious |
2072 | chrome.exe | GET | 302 | 18.223.3.115:80 | http://ec2-18-223-3-115.us-east-2.compute.amazonaws.com/?dedica=20Array&m=2155&q=Luminar%203.1.3.3920%20Crack%20With%20Activation%20Key%20Full%20Free&tron=MjBiMGVmMDkxNmVmYjNiOGNmYzAyMWE3YmZjYjdiZjMyZTQ5OTRhMQ== | US | html | 19.0 Kb | shared |
3092 | 61da2ef065ec0_Sun00935fdf6e.exe | GET | 200 | 2.56.59.42:80 | http://2.56.59.42/base/api/statistics.php | unknown | binary | 94 b | malicious |
3092 | 61da2ef065ec0_Sun00935fdf6e.exe | GET | 200 | 45.144.225.57:80 | http://45.144.225.57/server.txt | unknown | text | 15 b | malicious |
3092 | 61da2ef065ec0_Sun00935fdf6e.exe | GET | 400 | 212.193.30.45:80 | http://212.193.30.45/proxies.txt | RU | html | 301 b | malicious |
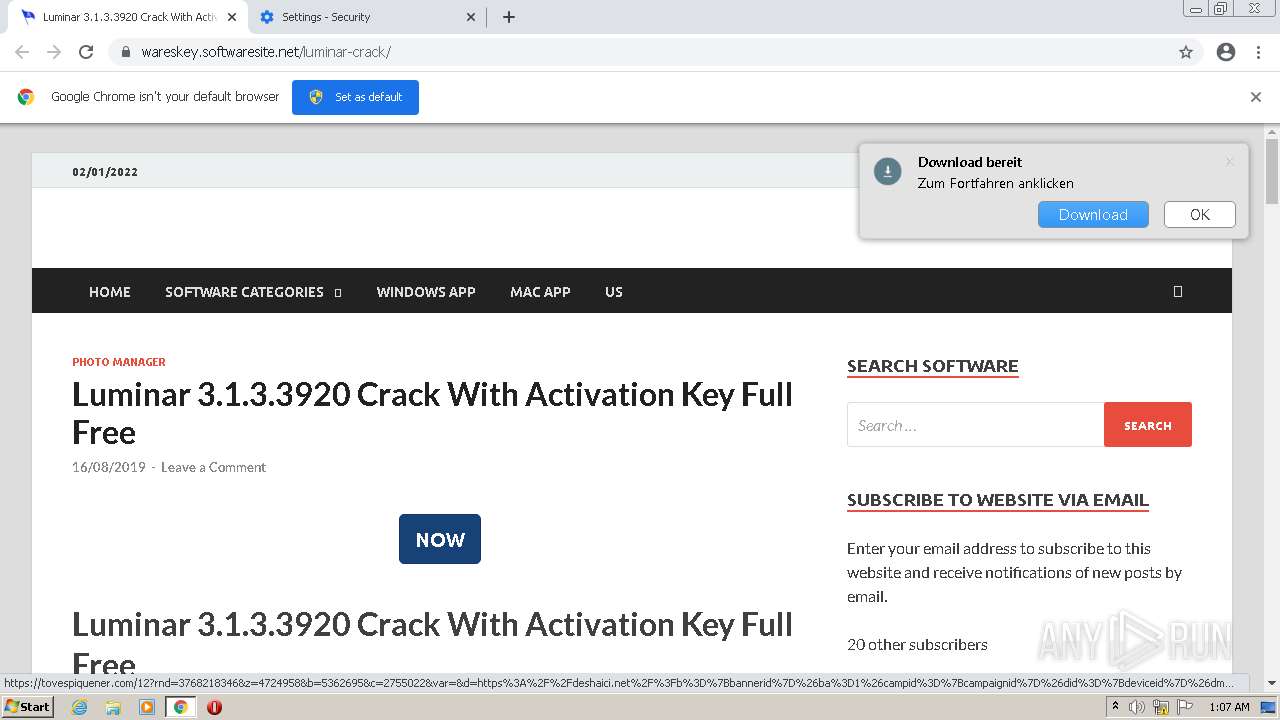
2072 | chrome.exe | POST | 200 | 18.223.3.115:80 | http://ec2-18-223-3-115.us-east-2.compute.amazonaws.com/?verify-id=2155&verify-hash=9d985188444175d30c709f634f65967f67f1ae22&verify-msch=THVtaW5hciAzLjEuMy4zOTIwIENyYWNrIFdpdGggQWN0aXZhdGlvbiBLZXkgRnVsbCBGcmVl&download=1&xtrans=MTM4 | US | compressed | 8.65 Mb | shared |
5052 | 61da2eeb98df8_Sun00bd121dfc.exe | GET | 200 | 45.144.2.131:80 | http://artmy.top/check.php?source=MIX1h1 | unknown | text | 31 b | malicious |
2072 | chrome.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?53fbf5961b2de4ae | US | compressed | 59.9 Kb | whitelisted |
2072 | chrome.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d78974334a2a783e | US | compressed | 59.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2072 | chrome.exe | 142.250.185.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2072 | chrome.exe | 172.67.213.2:443 | wareskey.softwaresite.net | — | US | suspicious |
2072 | chrome.exe | 104.21.71.210:443 | hastrenmon.xyz | Cloudflare Inc | US | malicious |
2072 | chrome.exe | 142.250.185.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2072 | chrome.exe | 172.67.39.148:443 | static.addtoany.com | — | US | unknown |
2072 | chrome.exe | 142.250.185.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2072 | chrome.exe | 142.250.184.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2072 | chrome.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
2072 | chrome.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
2072 | chrome.exe | 139.45.197.250:443 | itweepinbelltor.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
wareskey.softwaresite.net |
| malicious |
accounts.google.com |
| shared |
c0.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
hastrenmon.xyz |
| malicious |
i0.wp.com |
| whitelisted |
i1.wp.com |
| whitelisted |
i2.wp.com |
| whitelisted |
s.w.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2072 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
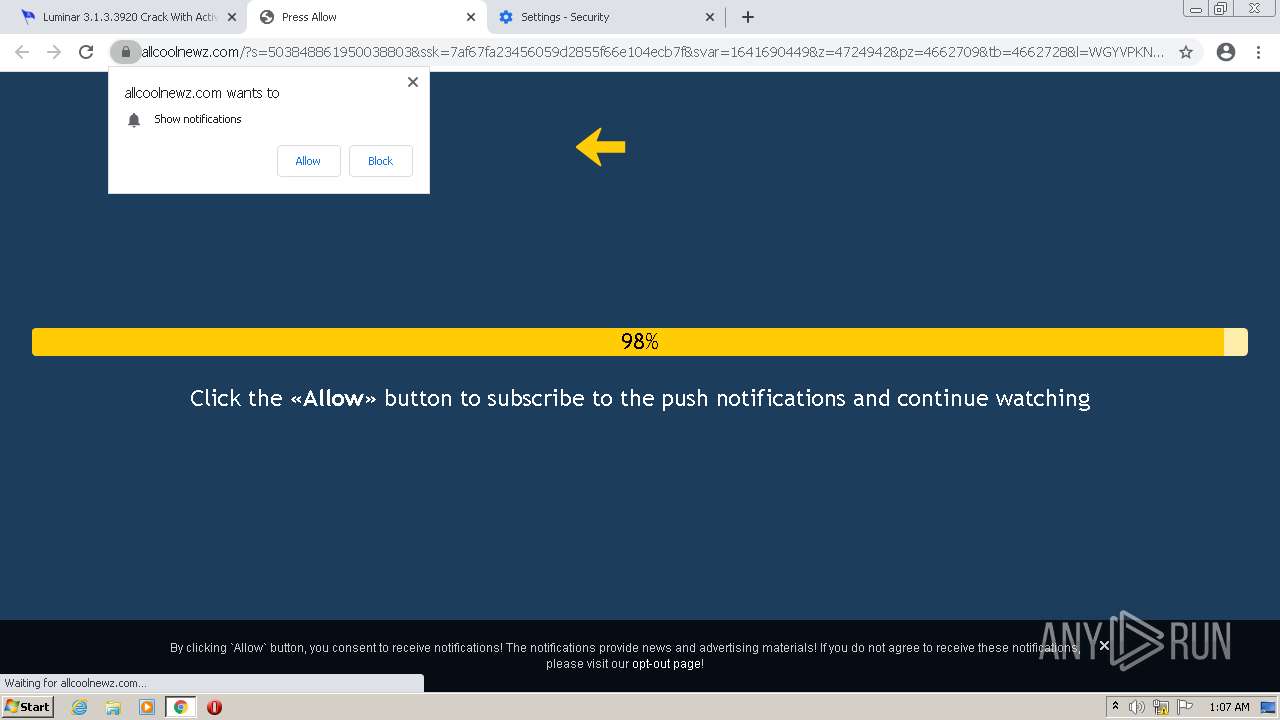
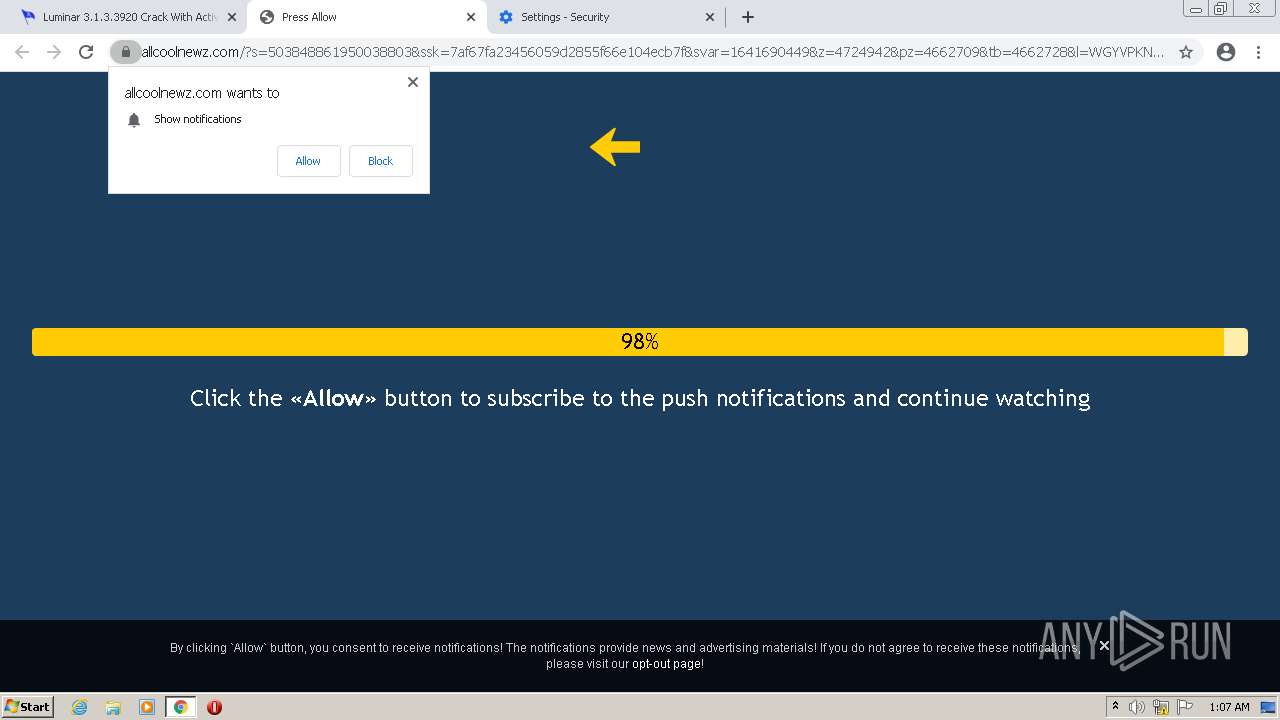
2072 | chrome.exe | A Network Trojan was detected | ET TROJAN Fake Software Download Redirect Leading to Malware M3 |
2072 | chrome.exe | A Network Trojan was detected | AV TROJAN Malware Dropper As a Service Download Request |
2072 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2072 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2072 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2072 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
1948 | setup_install.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
77 ETPRO signatures available at the full report