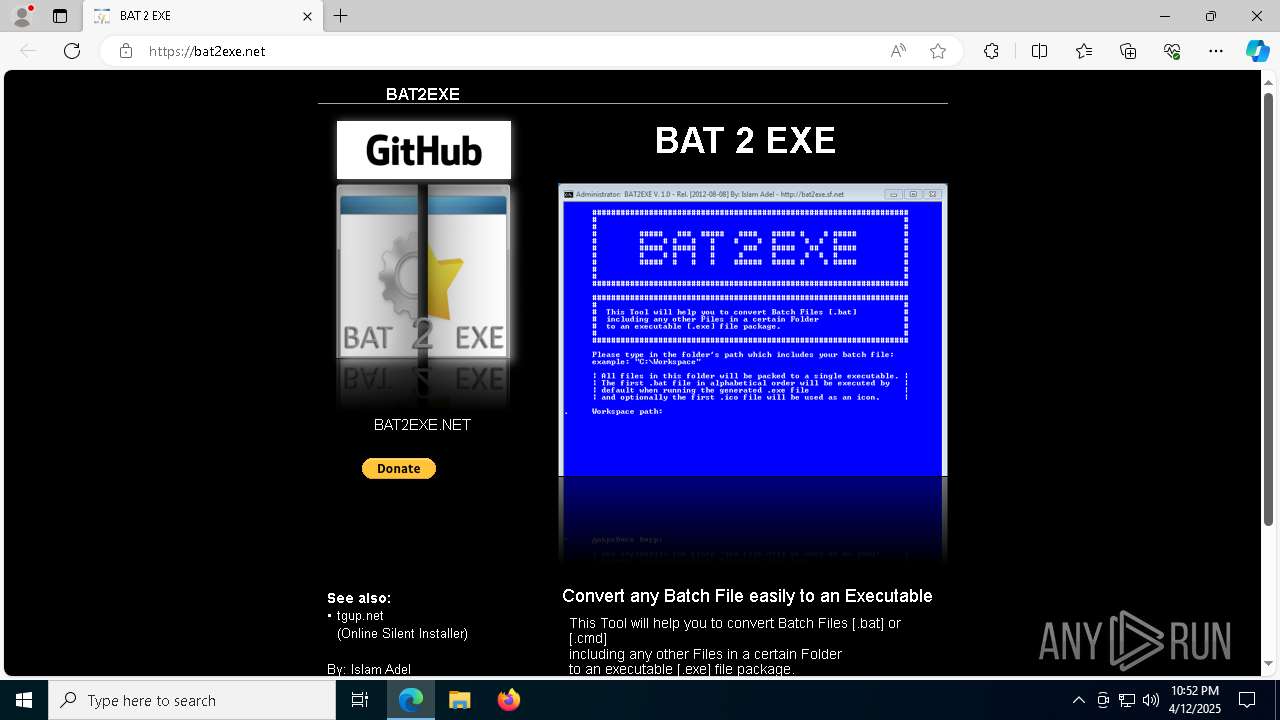
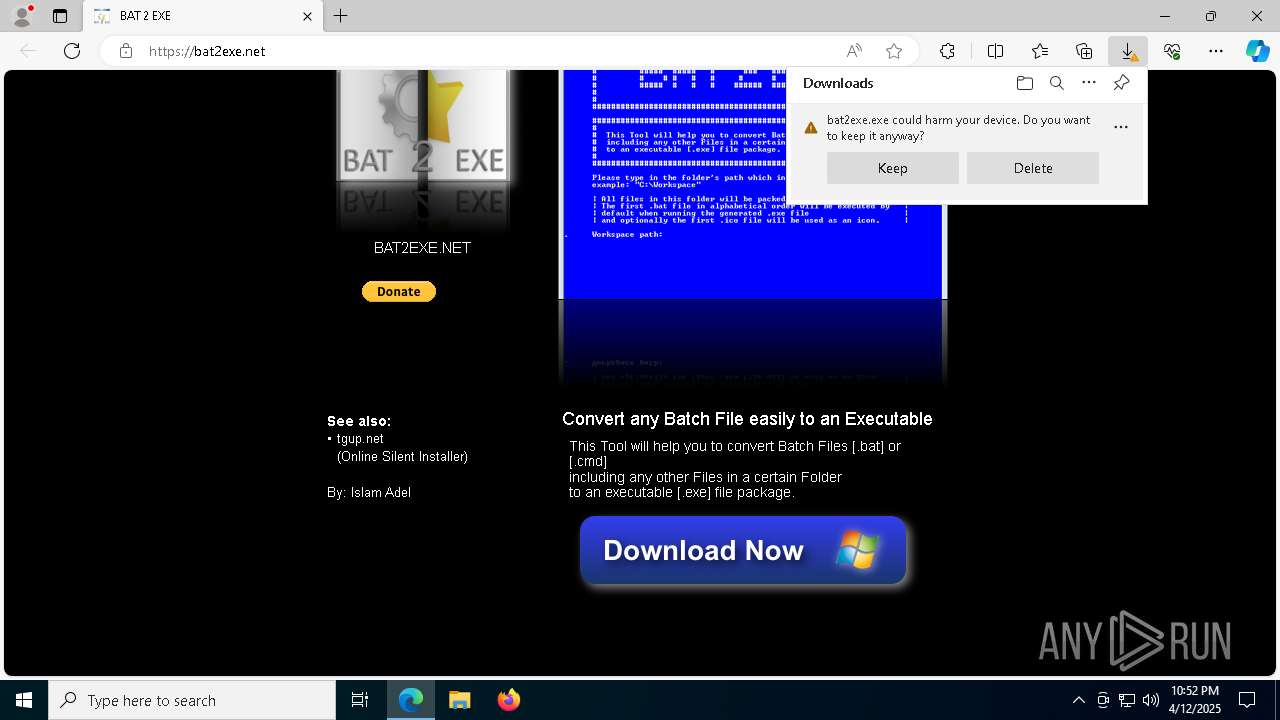
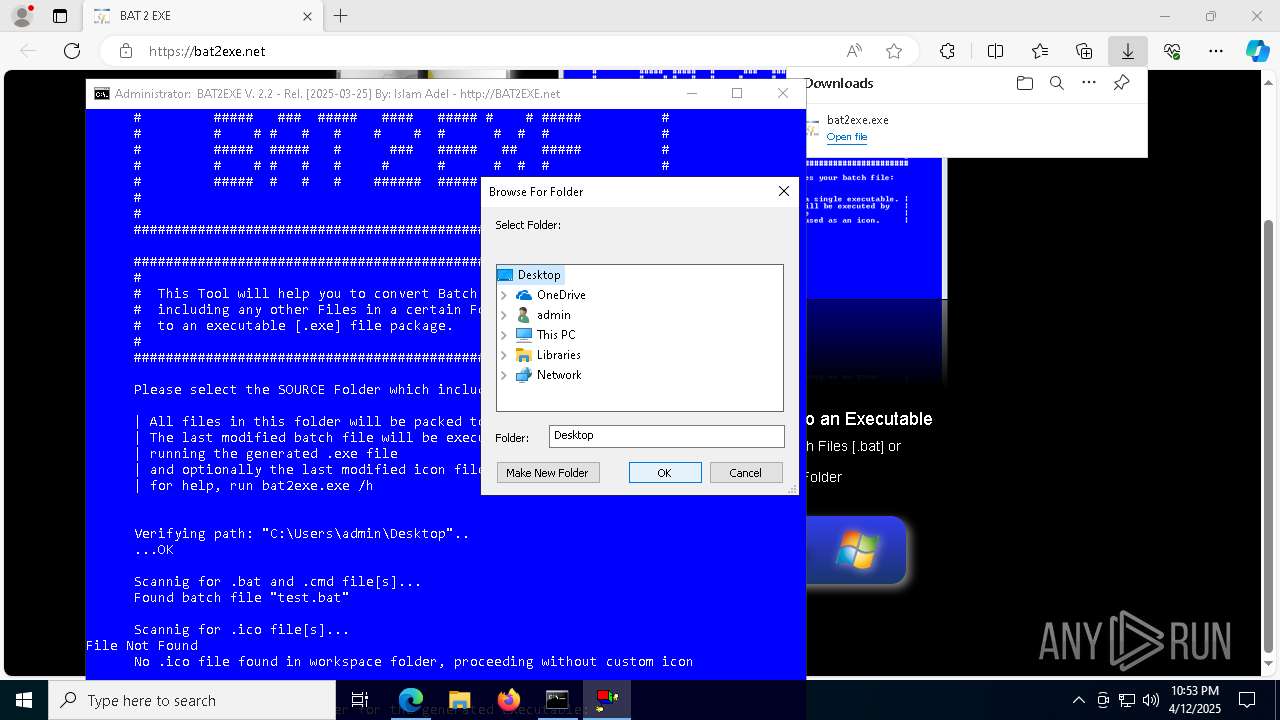
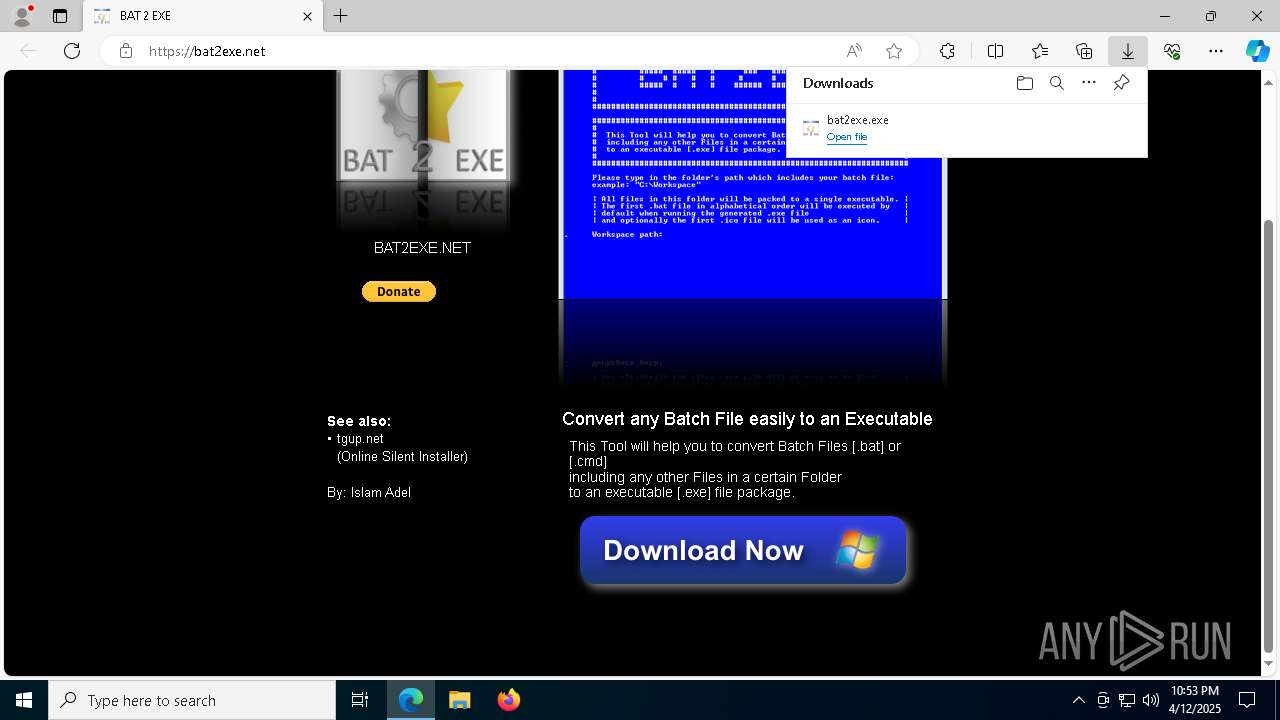
| URL: | https://bat2exe.net/ |
| Full analysis: | https://app.any.run/tasks/5c4652e8-6ae6-44e7-a4a4-c436d29419df |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2025, 22:52:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | A1883A2039E0050DCC50B013C10630B1 |
| SHA1: | EDCAB4FAD6DFD2E72F2F1A2B11072C399CB49C0E |
| SHA256: | A8B975F67D1D4AA130970B20DC00E3FD9764CBBB3FDB36A36E05AACFC2C2A477 |
| SSDEEP: | 3:N8LuX:2LC |
MALICIOUS
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 7204)
- cmd.exe (PID: 3124)
SUSPICIOUS
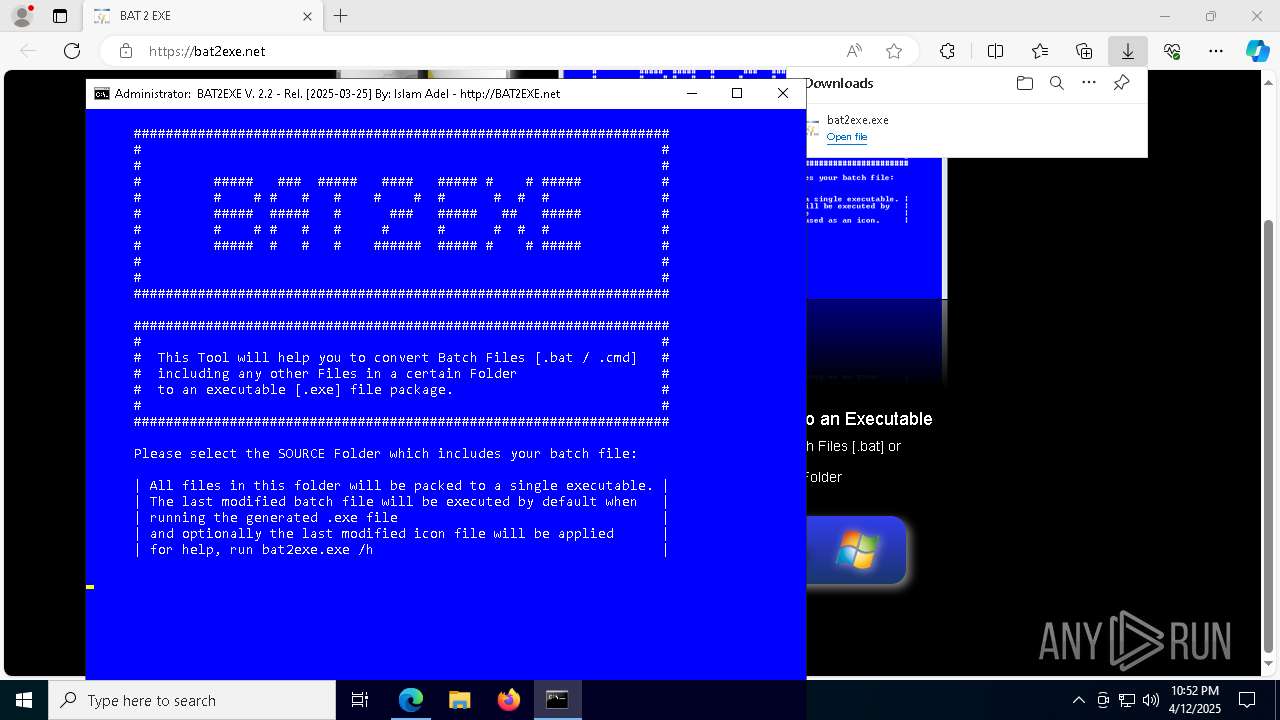
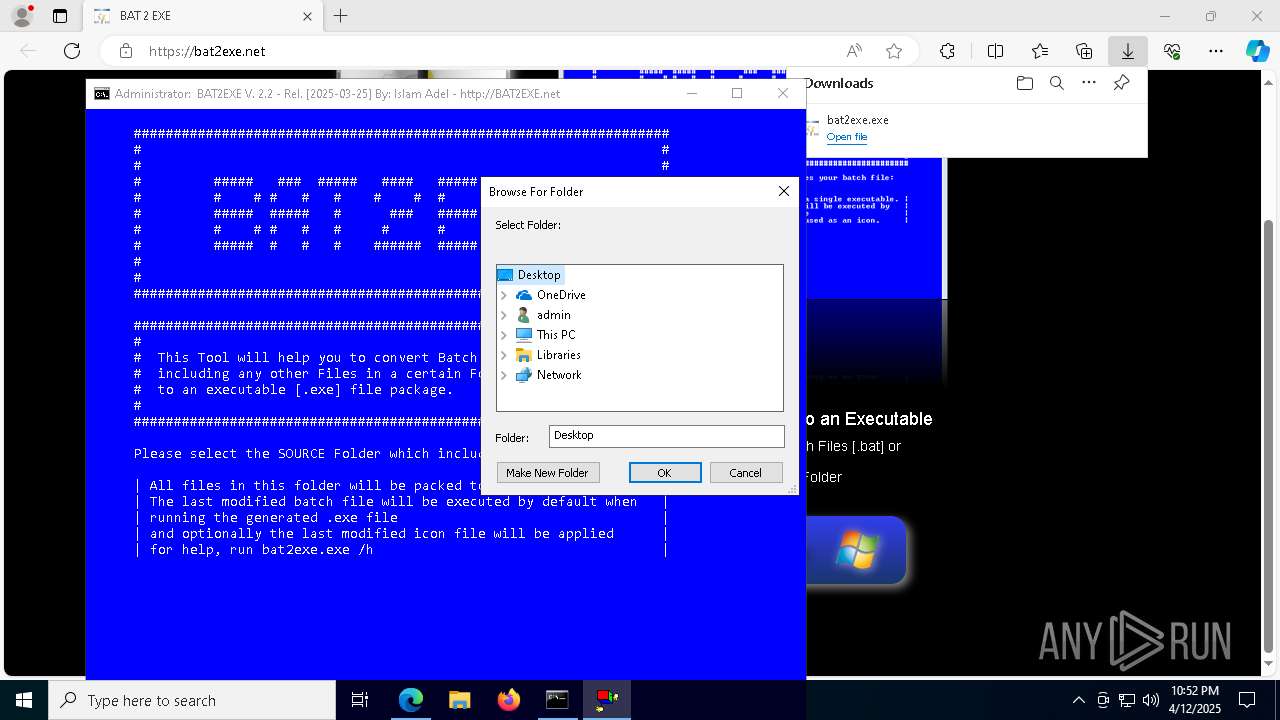
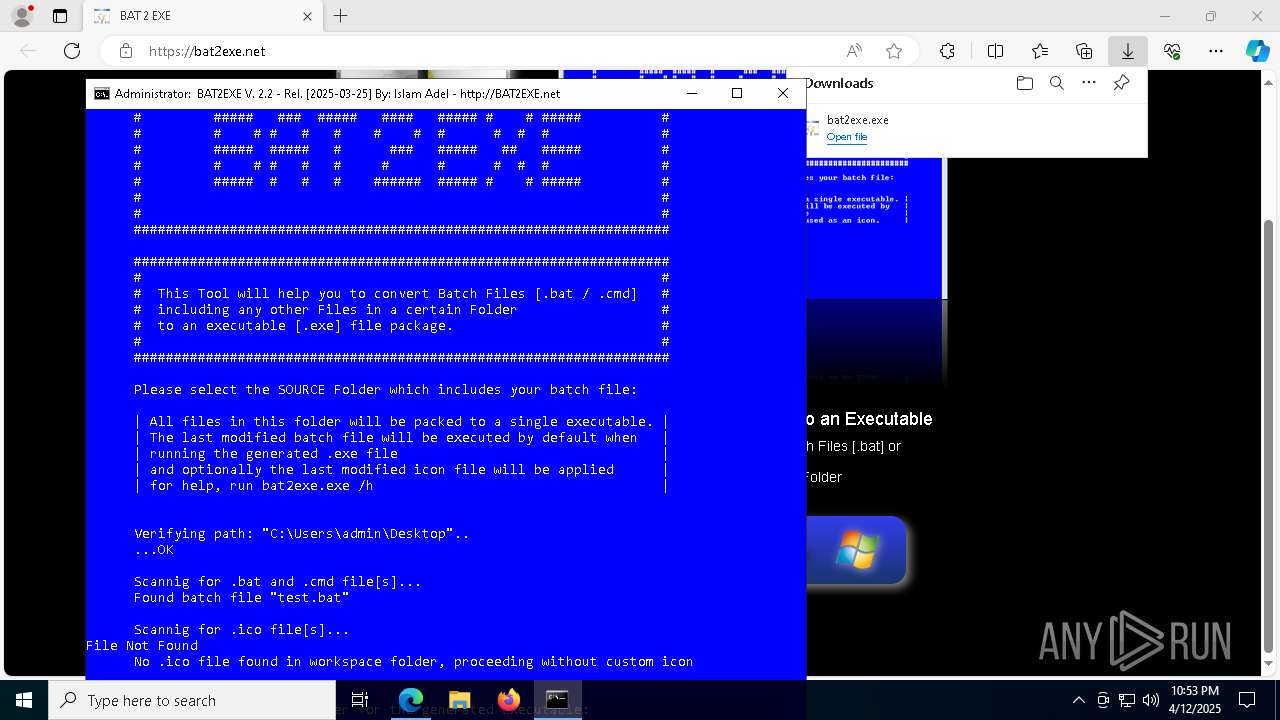
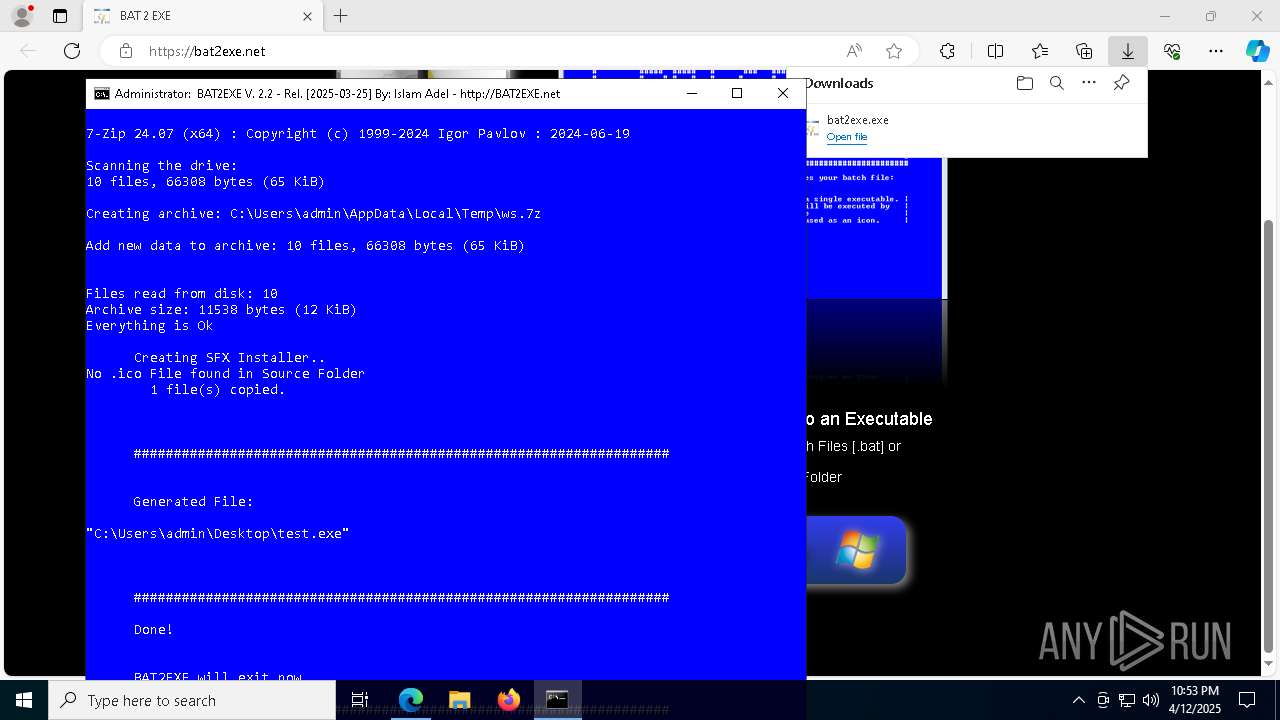
Drops 7-zip archiver for unpacking
- msedge.exe (PID: 7476)
- bat2exe.exe (PID: 4448)
- msedge.exe (PID: 7836)
Executable content was dropped or overwritten
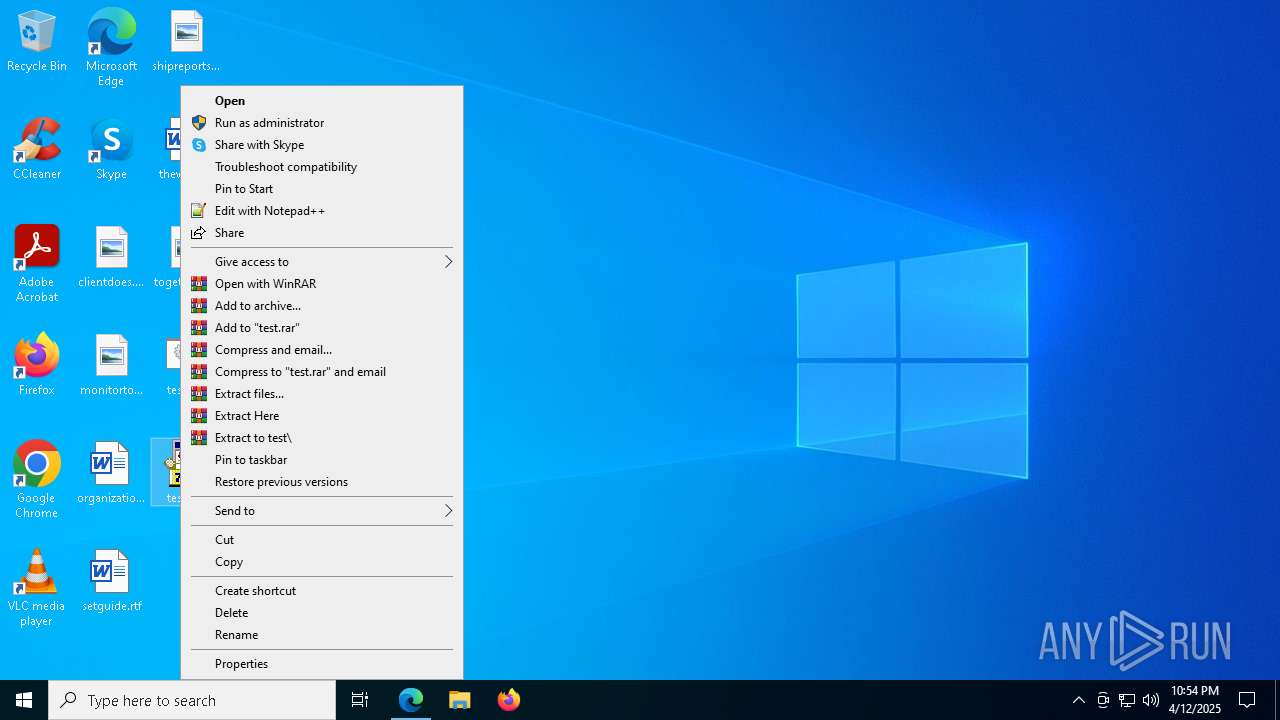
- bat2exe.exe (PID: 4448)
- cmd.exe (PID: 2800)
Reads security settings of Internet Explorer
- bat2exe.exe (PID: 4448)
- test.exe (PID: 6808)
- test.exe (PID: 7796)
Application launched itself
- cmd.exe (PID: 2800)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 4892)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2800)
- bat2exe.exe (PID: 4448)
- test.exe (PID: 6808)
- wscript.exe (PID: 8140)
- cmd.exe (PID: 2064)
- test.exe (PID: 7796)
- cmd.exe (PID: 4892)
- wscript.exe (PID: 5624)
- wscript.exe (PID: 2392)
- wscript.exe (PID: 4736)
The process executes VB scripts
- cmd.exe (PID: 4200)
- cmd.exe (PID: 5800)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 4892)
- cmd.exe (PID: 3124)
Executing commands from ".cmd" file
- cmd.exe (PID: 2800)
- bat2exe.exe (PID: 4448)
The process checks if it is being run in the virtual environment
- cmd.exe (PID: 2800)
Executing commands from a ".bat" file
- cmd.exe (PID: 2800)
- test.exe (PID: 6808)
- wscript.exe (PID: 8140)
- wscript.exe (PID: 4736)
- test.exe (PID: 7796)
- wscript.exe (PID: 5624)
- wscript.exe (PID: 2392)
The executable file from the user directory is run by the CMD process
- 7z.exe (PID: 5384)
Write to the desktop.ini file (may be used to cloak folders)
- test.exe (PID: 6808)
- test.exe (PID: 7796)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 2064)
- cmd.exe (PID: 4892)
- net.exe (PID: 924)
- net.exe (PID: 5024)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2064)
- cmd.exe (PID: 4892)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7204)
- cmd.exe (PID: 3124)
Runs shell command (SCRIPT)
- wscript.exe (PID: 4736)
- wscript.exe (PID: 5624)
- wscript.exe (PID: 2392)
- wscript.exe (PID: 8140)
INFO
Application launched itself
- msedge.exe (PID: 7476)
Reads Environment values
- identity_helper.exe (PID: 7284)
Reads the computer name
- identity_helper.exe (PID: 7284)
- bat2exe.exe (PID: 4448)
- 7z.exe (PID: 5384)
- test.exe (PID: 6808)
- test.exe (PID: 7796)
Executable content was dropped or overwritten
- msedge.exe (PID: 7476)
- msedge.exe (PID: 7836)
- msedge.exe (PID: 4528)
Autorun file from Downloads
- msedge.exe (PID: 5352)
- msedge.exe (PID: 7476)
The sample compiled with english language support
- msedge.exe (PID: 7836)
- msedge.exe (PID: 7476)
- bat2exe.exe (PID: 4448)
- msedge.exe (PID: 4528)
Checks supported languages
- identity_helper.exe (PID: 7284)
- bat2exe.exe (PID: 4448)
- mode.com (PID: 4120)
- 7z.exe (PID: 5384)
- test.exe (PID: 6808)
- test.exe (PID: 7796)
- mode.com (PID: 3300)
- mode.com (PID: 7332)
Create files in a temporary directory
- bat2exe.exe (PID: 4448)
- 7z.exe (PID: 5384)
- test.exe (PID: 6808)
- test.exe (PID: 7796)
Process checks computer location settings
- bat2exe.exe (PID: 4448)
- test.exe (PID: 6808)
- test.exe (PID: 7796)
Reads security settings of Internet Explorer
- cscript.exe (PID: 5392)
- cscript.exe (PID: 668)
Starts MODE.COM to configure console settings
- mode.com (PID: 4120)
- mode.com (PID: 7332)
- mode.com (PID: 3300)
Reads the software policy settings
- slui.exe (PID: 7856)
- slui.exe (PID: 7176)
Manual execution by a user
- test.exe (PID: 4024)
- test.exe (PID: 6808)
- test.exe (PID: 7796)
Checks proxy server information
- slui.exe (PID: 7176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
235
Monitored processes
98
Malicious processes
7
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | cscript //nologo bin\browse.vbs | C:\Windows\SysWOW64\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6852 --field-trial-handle=2456,i,509424847786540048,9569226579167482186,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Windows\System32\cmd.exe" /c "C:\Users\admin\AppData\Roaming\appdiagnostics\config.bat" | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | NET SESSION | C:\Windows\SysWOW64\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6520 --field-trial-handle=2456,i,509424847786540048,9569226579167482186,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 976 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5808 --field-trial-handle=2456,i,509424847786540048,9569226579167482186,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1600 | C:\WINDOWS\system32\net1 SESSION | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | C:\WINDOWS\system32\cmd.exe /c dir /b /OD "C:\Users\admin\Desktop\*.ico" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 376
Read events
12 352
Write events
24
Delete events
0
Modification events
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BFC668F432912F00 | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 92E7A2F432912F00 | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262926 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {481CC303-BD2A-4B2E-B125-3FDF46572C30} | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262926 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F5AD6C28-1D79-416C-94A0-57066FC24214} | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262926 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E0E33A77-48F6-4F18-83A4-EDCF55FED257} | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
23
Suspicious files
446
Text files
99
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bb43.TMP | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bb43.TMP | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bb43.TMP | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bb53.TMP | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF10bba1.TMP | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
66
DNS requests
71
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6252 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b649b6c2-4484-495a-96f2-2fd1ee2b66ca?P1=1744953275&P2=404&P3=2&P4=aYUYv%2f2xIqL8VJFIhSnf4toB6MCMu7uEQdLnU%2fGxJ6NDZh%2bPv3wKEI7hVorgtoeAu8qbuYZlYusDaLcNaABOuA%3d%3d | unknown | — | — | whitelisted |
6252 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744953266&P2=404&P3=2&P4=Sz7vituz1o%2b7JW5T32aIwEJSTPWKUGorDp0Rxf7QriBMfXOMODmi%2fddkvaQtM0R0Np3wbEUHvnjEeIRmro%2b6Qg%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6652 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6252 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744953266&P2=404&P3=2&P4=Sz7vituz1o%2b7JW5T32aIwEJSTPWKUGorDp0Rxf7QriBMfXOMODmi%2fddkvaQtM0R0Np3wbEUHvnjEeIRmro%2b6Qg%3d%3d | unknown | — | — | whitelisted |
6252 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744953266&P2=404&P3=2&P4=Sz7vituz1o%2b7JW5T32aIwEJSTPWKUGorDp0Rxf7QriBMfXOMODmi%2fddkvaQtM0R0Np3wbEUHvnjEeIRmro%2b6Qg%3d%3d | unknown | — | — | whitelisted |
6252 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744953266&P2=404&P3=2&P4=Sz7vituz1o%2b7JW5T32aIwEJSTPWKUGorDp0Rxf7QriBMfXOMODmi%2fddkvaQtM0R0Np3wbEUHvnjEeIRmro%2b6Qg%3d%3d | unknown | — | — | whitelisted |
6252 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744953266&P2=404&P3=2&P4=Sz7vituz1o%2b7JW5T32aIwEJSTPWKUGorDp0Rxf7QriBMfXOMODmi%2fddkvaQtM0R0Np3wbEUHvnjEeIRmro%2b6Qg%3d%3d | unknown | — | — | whitelisted |
6252 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744953266&P2=404&P3=2&P4=Sz7vituz1o%2b7JW5T32aIwEJSTPWKUGorDp0Rxf7QriBMfXOMODmi%2fddkvaQtM0R0Np3wbEUHvnjEeIRmro%2b6Qg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6632 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7836 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7476 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7836 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7836 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
bat2exe.net |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |