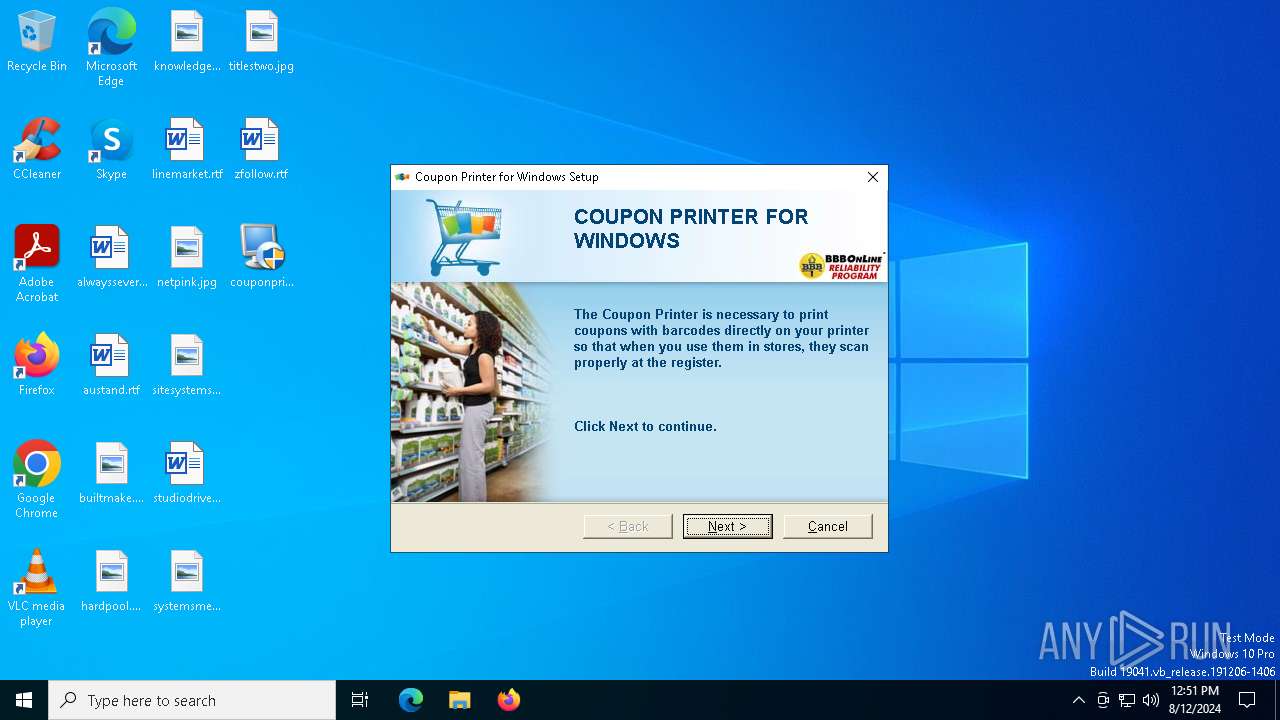
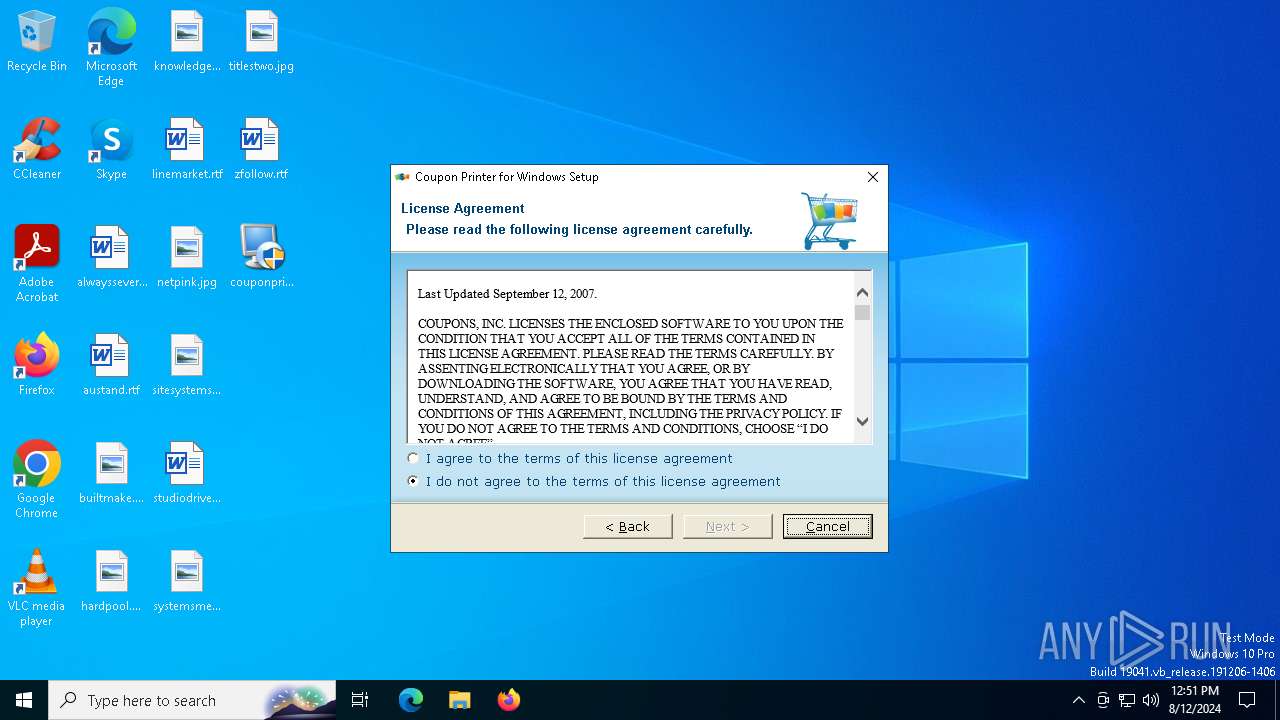
| File name: | couponprinter.exe |
| Full analysis: | https://app.any.run/tasks/7db2e69f-1de5-4660-aa1e-130f1a9be290 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2024, 12:51:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 82C2AF1B8F4DDE40301EF803C3E641A7 |
| SHA1: | 41390113AB2C111B2E898AEDBD307841617670B5 |
| SHA256: | A8A7F0E587402A8D2F84E02E6080F8D9C40DDCF69A87AE2679FEEBD12A2E10DC |
| SSDEEP: | 49152:cNx9dGS3VNdslS/QZKcC6pkjpONtgRTELDWJ2BdNFt+05+40i6IsJY9CMijIRlxO:cH9X3zyZpCPjrRT6iGNX+05+ri6IsGgb |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- couponprinter.exe (PID: 6976)
- irsetup.exe (PID: 7036)
Drops the executable file immediately after the start
- couponprinter.exe (PID: 6976)
- irsetup.exe (PID: 7036)
Reads security settings of Internet Explorer
- couponprinter.exe (PID: 6976)
- irsetup.exe (PID: 7036)
Reads the date of Windows installation
- couponprinter.exe (PID: 6976)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 7036)
Reads Microsoft Outlook installation path
- irsetup.exe (PID: 7036)
Reads Internet Explorer settings
- irsetup.exe (PID: 7036)
Read disk information to detect sandboxing environments
- irsetup.exe (PID: 7036)
Creates/Modifies COM task schedule object
- irsetup.exe (PID: 7036)
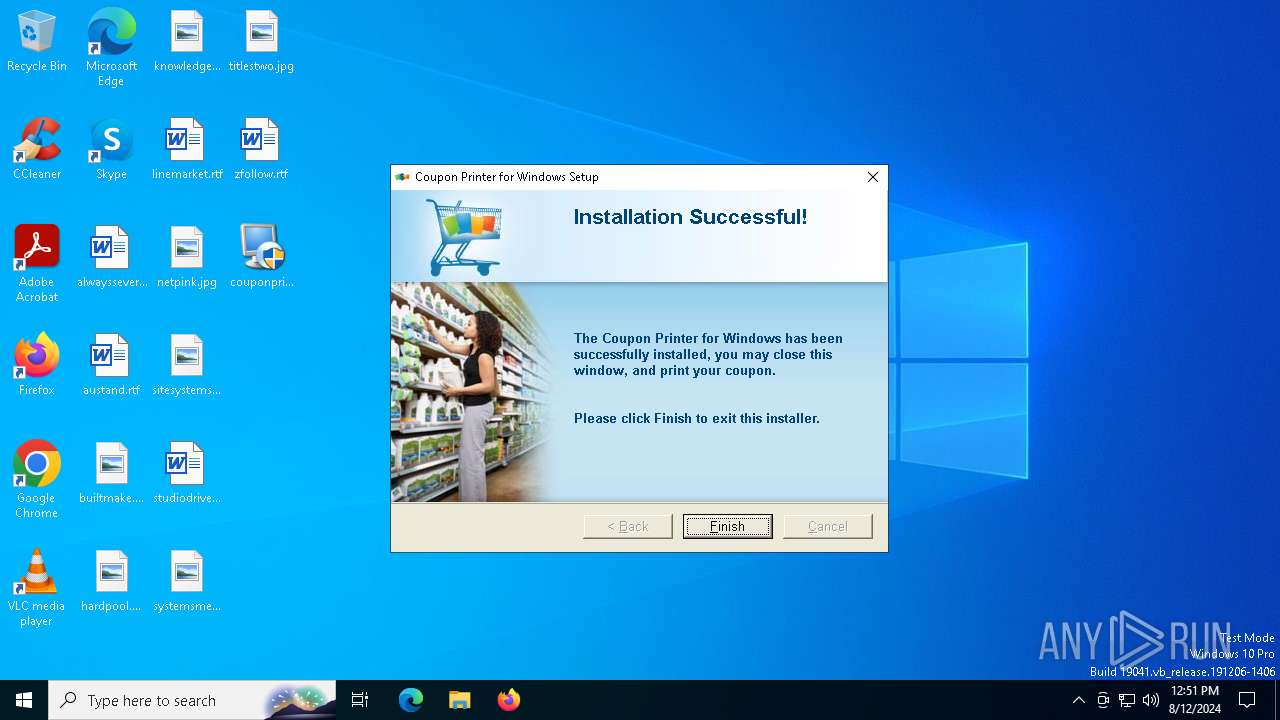
Creates a software uninstall entry
- irsetup.exe (PID: 7036)
INFO
Create files in a temporary directory
- couponprinter.exe (PID: 6976)
- irsetup.exe (PID: 7036)
Checks supported languages
- couponprinter.exe (PID: 6976)
- irsetup.exe (PID: 7036)
Process checks computer location settings
- couponprinter.exe (PID: 6976)
Reads the computer name
- irsetup.exe (PID: 7036)
- couponprinter.exe (PID: 6976)
Checks proxy server information
- irsetup.exe (PID: 7036)
Process checks Internet Explorer phishing filters
- irsetup.exe (PID: 7036)
UPX packer has been detected
- irsetup.exe (PID: 7036)
Creates files in the program directory
- irsetup.exe (PID: 7036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (31) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (27.4) |
| .exe | | | Win32 EXE Yoda's Crypter (26.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.5) |
| .exe | | | Win32 Executable (generic) (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:11:06 19:53:27+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 32768 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3079 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.0.0 |
| ProductVersionNumber: | 5.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | Coupon Printer Installer |
| CompanyName: | Coupons.com Incorporated |
| FileDescription: | Coupon Printer Installer |
| FileVersion: | 5.0.0.0 |
| InternalName: | sf_rt |
| LegalCopyright: | Copyright © 2009 by Coupons.com Incorporated |
| OriginalFileName: | suf80_launch.exe |
| ProductName: | Coupon Printer |
| ProductVersion: | 5.0.0.0 |
Total processes
135
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6820 | "C:\Users\admin\Desktop\couponprinter.exe" | C:\Users\admin\Desktop\couponprinter.exe | — | explorer.exe | |||||||||||
User: admin Company: Coupons.com Incorporated Integrity Level: MEDIUM Description: Coupon Printer Installer Exit code: 3221226540 Version: 5.0.0.0 Modules
| |||||||||||||||
| 6976 | "C:\Users\admin\Desktop\couponprinter.exe" | C:\Users\admin\Desktop\couponprinter.exe | explorer.exe | ||||||||||||
User: admin Company: Coupons.com Incorporated Integrity Level: HIGH Description: Coupon Printer Installer Exit code: 0 Version: 5.0.0.0 Modules
| |||||||||||||||
| 7036 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe" __IRAOFF:662050 "__IRAFN:C:\Users\admin\Desktop\couponprinter.exe" "__IRCT:1" "__IRTSS:0" "__IRSID:S-1-5-21-1693682860-607145093-2874071422-1001" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | couponprinter.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 8.2.1.0 Modules
| |||||||||||||||
Total events
5 854
Read events
5 810
Write events
41
Delete events
3
Modification events
| (PID) Process: | (6976) couponprinter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6976) couponprinter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6976) couponprinter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6976) couponprinter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7036) irsetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7036) irsetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7036) irsetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7036) irsetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7036) irsetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7036) irsetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
6
Suspicious files
4
Text files
20
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7036 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG8.JPG | image | |
MD5:6FB2B3B60780236D59F8E3DC480C425A | SHA256:1E18EB542AF573D73E7CB3778972D756CBD6C2306157BD06CDD3B4EE3DD72448 | |||
| 7036 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG3.JPG | image | |
MD5:6FB2B3B60780236D59F8E3DC480C425A | SHA256:1E18EB542AF573D73E7CB3778972D756CBD6C2306157BD06CDD3B4EE3DD72448 | |||
| 7036 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG5.JPG | image | |
MD5:238276D8C6D3692A08B8049C5870AAAD | SHA256:7D48F24E0C725BD539DC6533FFC62B1389FF6E6632B45066BDCFDFBF0E8080EC | |||
| 7036 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG2.JPG | image | |
MD5:549CC74A0E3DEF6B8D850B10678A20A8 | SHA256:CF1B2320C45D21B9A62F3D7D4E6B2557A0ADA17CB32C774B4C54385B67C410D4 | |||
| 7036 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG6.JPG | image | |
MD5:5DDF49CBB7F7021744ECEF1B51A7F6B5 | SHA256:5F1F30359146A9855620A3ADCF0AAE8AF70EFB5B12EC0E0D94ACE5DB5C6612F4 | |||
| 7036 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\Verdana_1.FON | executable | |
MD5:FE4C63FDFDB7C981F5F39CF9C9AB18FA | SHA256:F2188F19D1727FF2B688FCD475B925665182E909A95772DF5767DFBE40FBA0AF | |||
| 7036 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG7.JPG | image | |
MD5:E803AEC3D341834DF73154C15EF23CE0 | SHA256:7E797A08FA7785DC1527E5E8E0DEACE4F6978999FAE06C306D4116AC691C616A | |||
| 7036 | irsetup.exe | C:\Program Files (x86)\Coupons\Uninstall\uniA454.tmp | binary | |
MD5:A6163FE1C642FDDEEE6F16610236DE12 | SHA256:49286501C0A00570EDEFE9301F9FFAA0601A6BE4120115192FEB709EF1F9B71E | |||
| 7036 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\Verdana_1.TFT | odttf | |
MD5:1AE9B9868BD3121E932225B140A839A5 | SHA256:AEF25C78EAF9CB243F62508ED5A373BB98918FE880A63B3E17EA0B123270175C | |||
| 7036 | irsetup.exe | C:\Program Files (x86)\Coupons\Uninstall\uninstall.dat | binary | |
MD5:4A76752DD9675622AC23727350842515 | SHA256:3DAF277D7E9DDA3D6A78989F8AEFB7562D1E9031BA2AF33C56494D37DDA8FBDA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
39
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6284 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6292 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
5796 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 104.126.37.138:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6220 | backgroundTaskHost.exe | 104.126.37.138:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
connect.coupons.com |
| unknown |