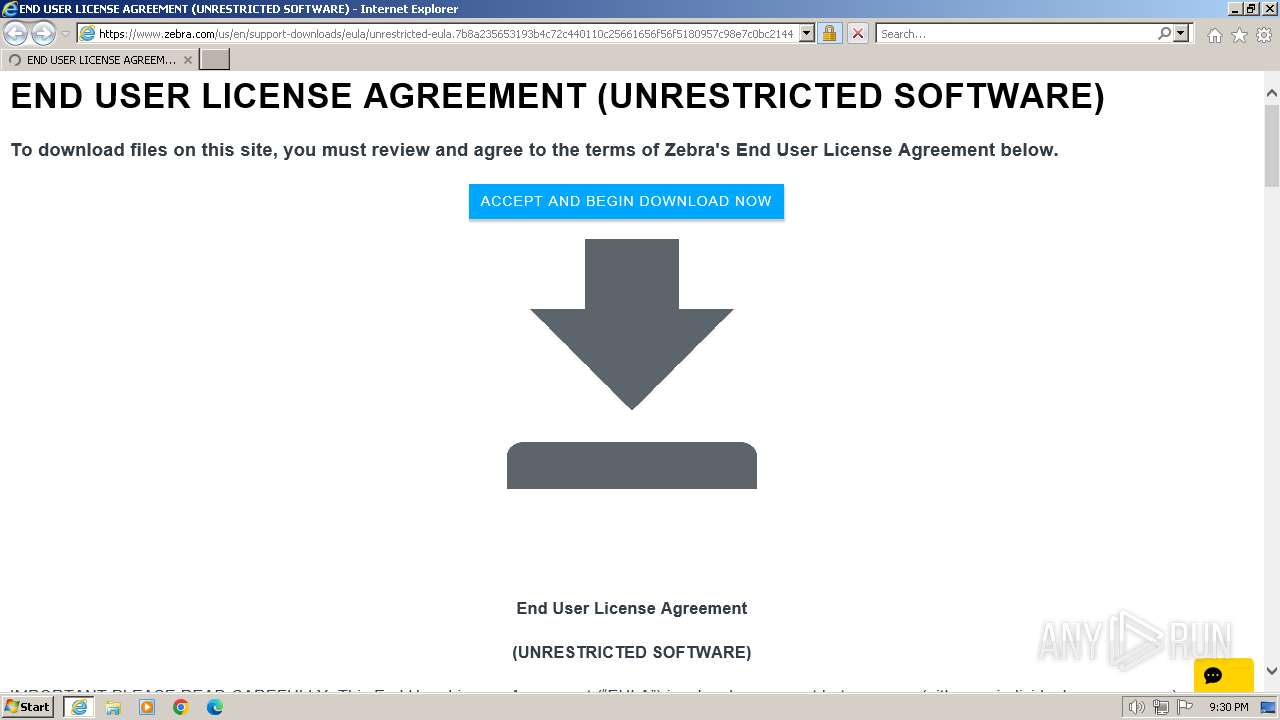
| URL: | https://www.zebra.com/us/en/support-downloads/eula/unrestricted-eula.7b8a235653193b4c72c440110c25661656f56f5180957c98e7c0bc2144149cd156a1bc6e684725abae8eaa3b64ee1090a63134434792cf7fe7ebd953120a60cd367633fe9f513f4af05bcf3ca8fdcf836c93e23b0860d2ecb3b9f68761e10d9e250a5e4c91d53813.html# |
| Full analysis: | https://app.any.run/tasks/2027e5f5-423e-4afc-9a47-f507f6dc5319 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2024, 21:30:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C989923868A1ACD317BCAE82FF0F59E9 |
| SHA1: | 416CE7939F83625013714B3E9C387D425FA42F06 |
| SHA256: | A89E5A5B9E76EFB3EAF27FAD8DFDF4363B97A7736D8C946C24C1485780ADC183 |
| SSDEEP: | 6:2OLoyoY2VKOXcDASW+WEGpyeMABWrKysvI+ZpE5M7i8q0t5owX:2R/XcDASD2tpysTHE5Si8qyX |
MALICIOUS
Creates a writable file in the system directory
- PrnInst.exe (PID: 552)
- drvinst.exe (PID: 876)
- spoolsv.exe (PID: 2728)
- is-6FR2U.tmp (PID: 2540)
- PrnInst.exe (PID: 3452)
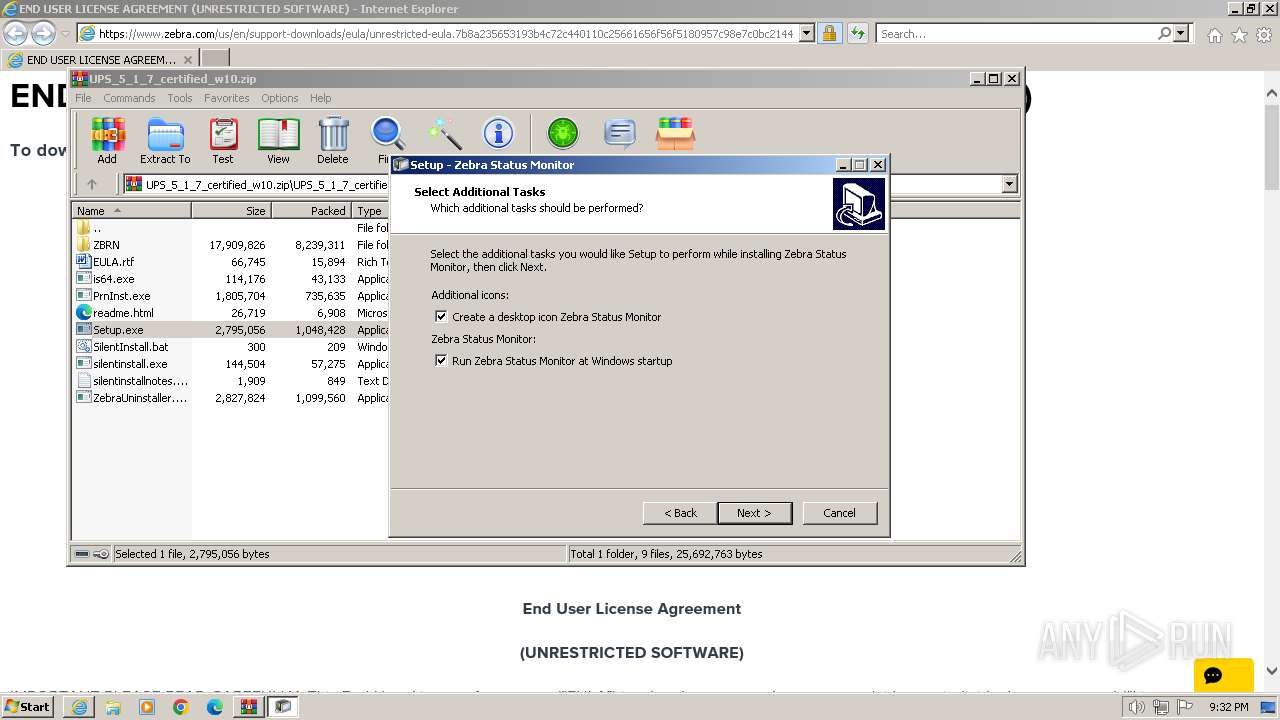
Create files in the Startup directory
- StatMonSetup.tmp (PID: 2360)
SUSPICIOUS
Reads the Internet Settings
- Setup.exe (PID: 2640)
- silentinstall.exe (PID: 3080)
Checks Windows Trust Settings
- drvinst.exe (PID: 876)
Reads the Windows owner or organization settings
- is-6FR2U.tmp (PID: 2540)
- StatMonSetup.tmp (PID: 2360)
- is-FP4F5.tmp (PID: 3672)
Creates files in the driver directory
- drvinst.exe (PID: 876)
Searches for installed software
- is-FP4F5.tmp (PID: 3672)
INFO
Application launched itself
- iexplore.exe (PID: 1072)
Checks supported languages
- Setup.exe (PID: 2640)
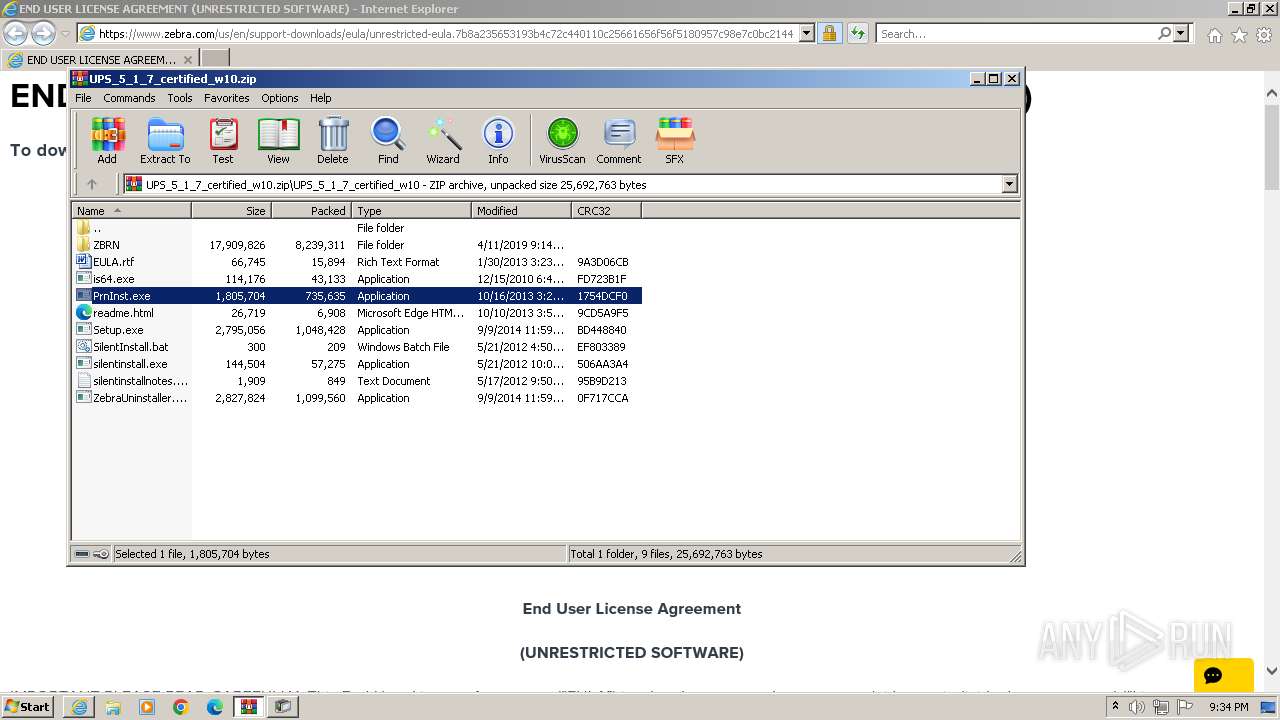
- PrnInst.exe (PID: 552)
- drvinst.exe (PID: 876)
- ZebraFD.exe (PID: 1196)
- is-6FR2U.tmp (PID: 2540)
- ZDDownloader2.exe (PID: 2528)
- StatMonSetup.exe (PID: 2860)
- StatMonSetup.tmp (PID: 2360)
- StatusMonitor.exe (PID: 968)
- silentinstall.exe (PID: 3080)
- is-FP4F5.tmp (PID: 3672)
- ZebraFD.exe (PID: 3680)
- DPInst.exe (PID: 3244)
- PrnInst.exe (PID: 3452)
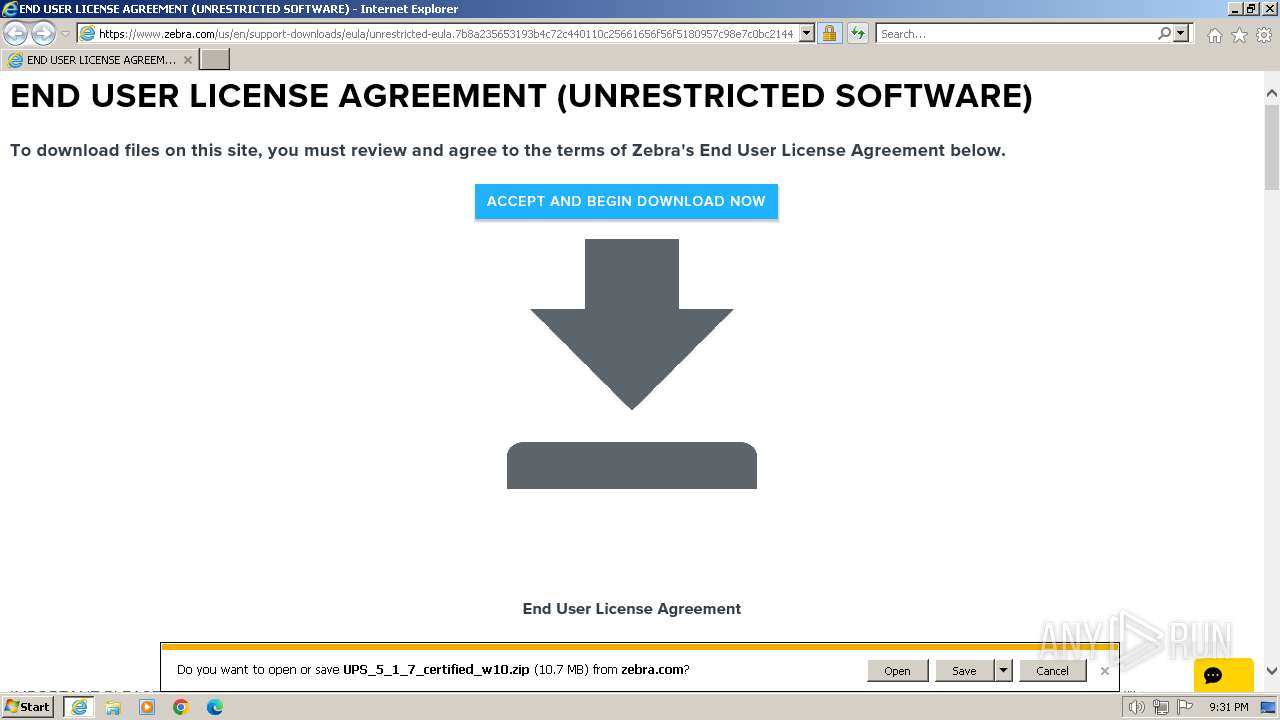
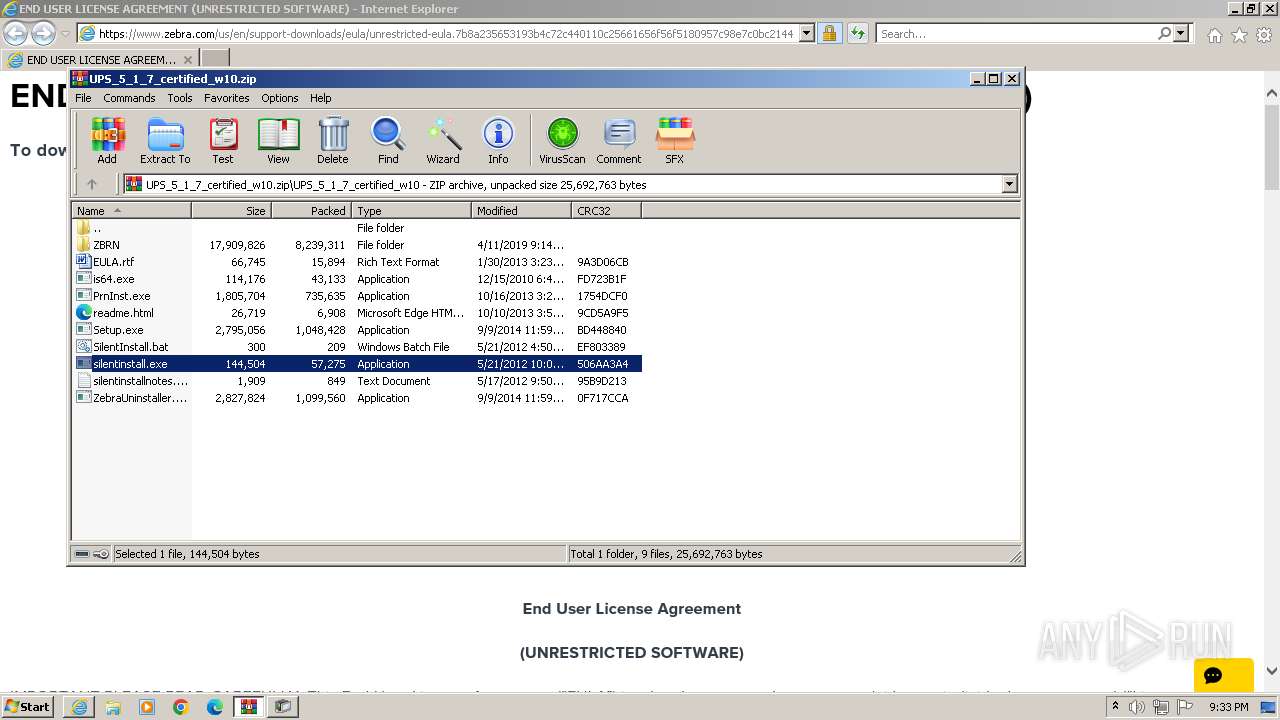
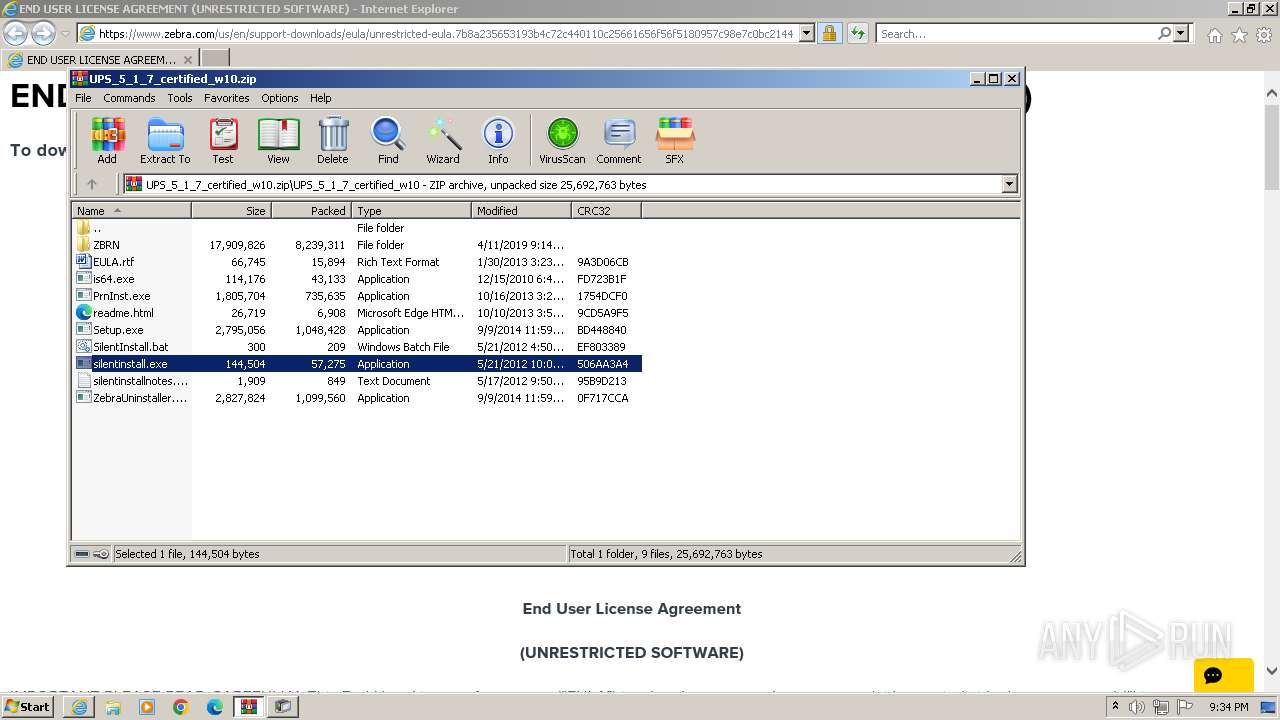
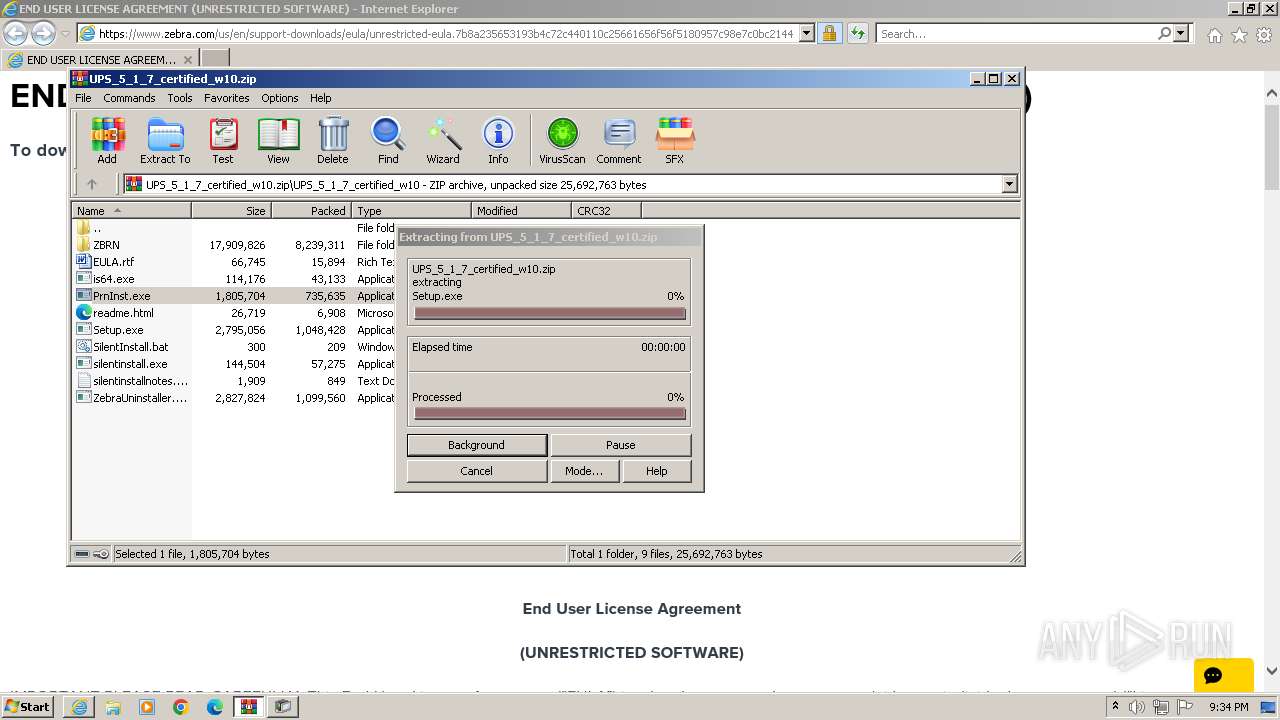
The process uses the downloaded file
- WinRAR.exe (PID: 632)
- iexplore.exe (PID: 1072)
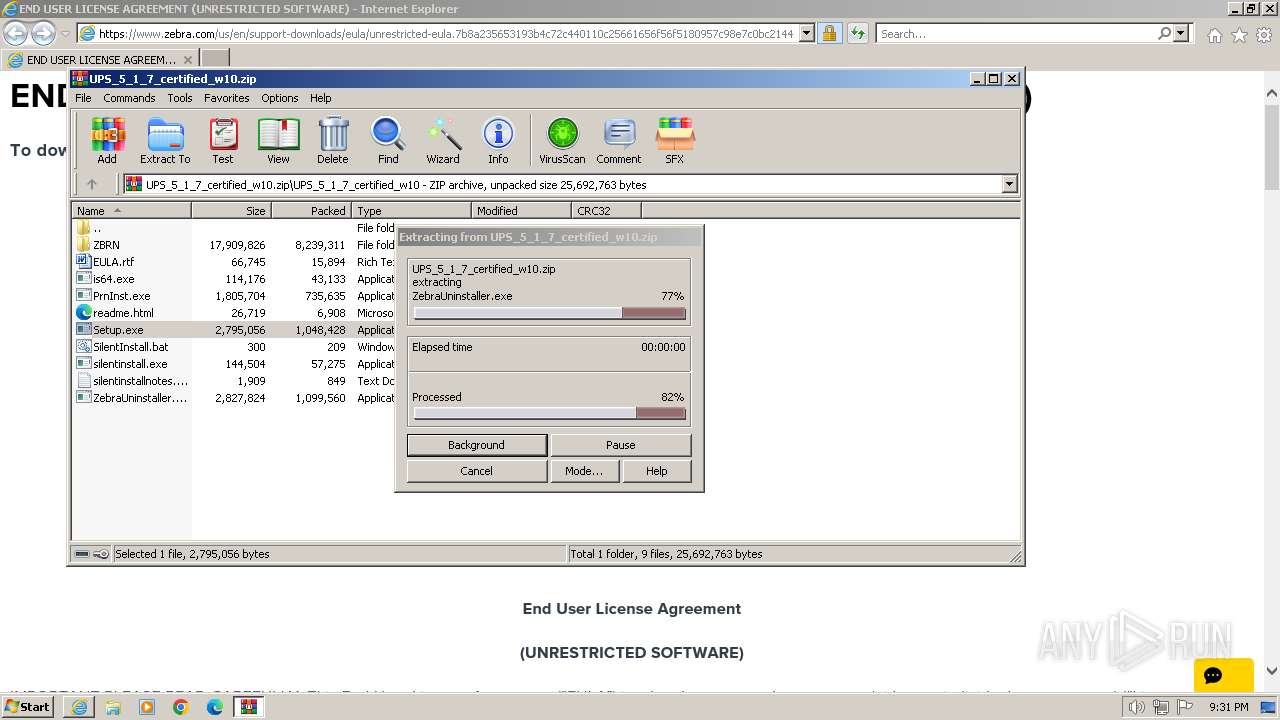
Process drops legitimate windows executable
- WinRAR.exe (PID: 632)
- is-6FR2U.tmp (PID: 2540)
- StatMonSetup.tmp (PID: 2360)
- is-FP4F5.tmp (PID: 3672)
Reads the computer name
- Setup.exe (PID: 2640)
- PrnInst.exe (PID: 552)
- drvinst.exe (PID: 876)
- is-6FR2U.tmp (PID: 2540)
- StatusMonitor.exe (PID: 968)
- StatMonSetup.tmp (PID: 2360)
- silentinstall.exe (PID: 3080)
- ZDDownloader2.exe (PID: 2528)
- PrnInst.exe (PID: 3452)
- is-FP4F5.tmp (PID: 3672)
Reads the machine GUID from the registry
- PrnInst.exe (PID: 552)
- drvinst.exe (PID: 876)
- PrnInst.exe (PID: 3452)
Create files in a temporary directory
- PrnInst.exe (PID: 552)
- ZebraFD.exe (PID: 1196)
- is-6FR2U.tmp (PID: 2540)
- StatMonSetup.tmp (PID: 2360)
- StatusMonitor.exe (PID: 968)
- StatMonSetup.exe (PID: 2860)
- ZebraFD.exe (PID: 3680)
- is-FP4F5.tmp (PID: 3672)
Drops the executable file immediately after the start
- drvinst.exe (PID: 876)
- ZebraFD.exe (PID: 1196)
- is-6FR2U.tmp (PID: 2540)
- WinRAR.exe (PID: 632)
- PrnInst.exe (PID: 552)
- StatMonSetup.exe (PID: 2860)
- spoolsv.exe (PID: 2728)
- StatMonSetup.tmp (PID: 2360)
- PrnInst.exe (PID: 3452)
- ZebraFD.exe (PID: 3680)
- is-FP4F5.tmp (PID: 3672)
Executes as Windows Service
- spoolsv.exe (PID: 2728)
Creates files in the program directory
- is-6FR2U.tmp (PID: 2540)
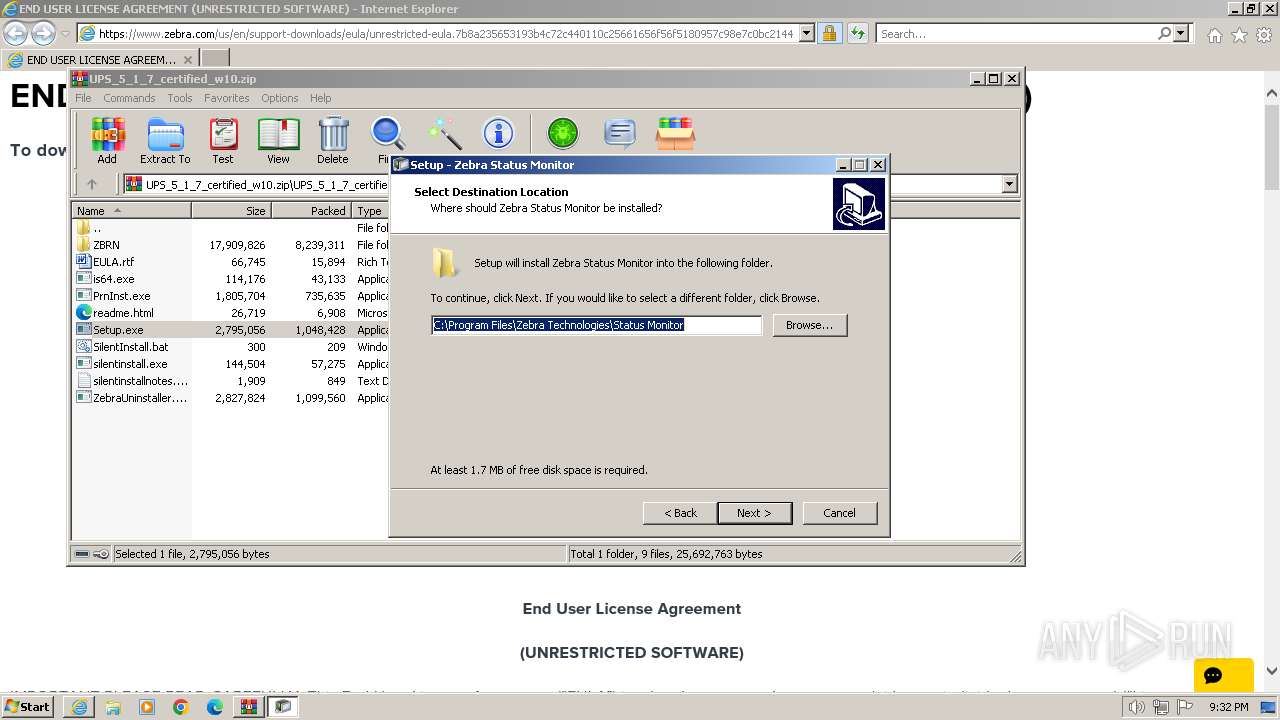
- StatMonSetup.tmp (PID: 2360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
22
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
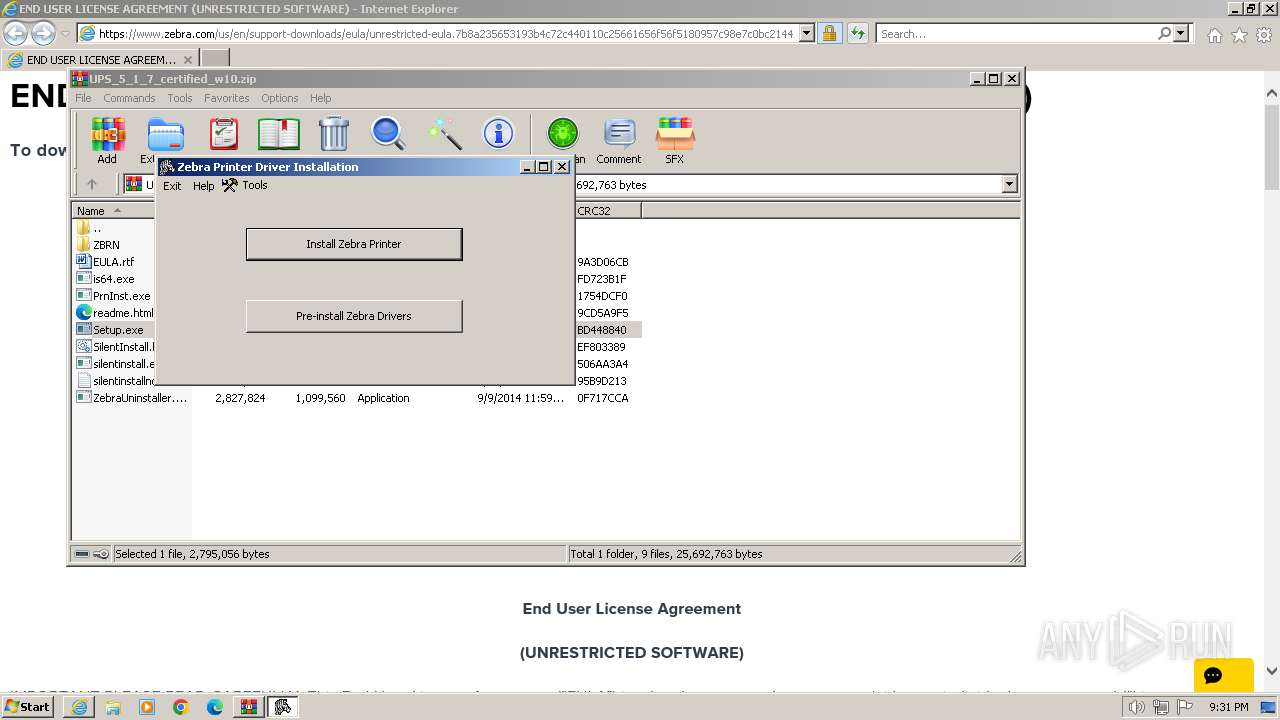
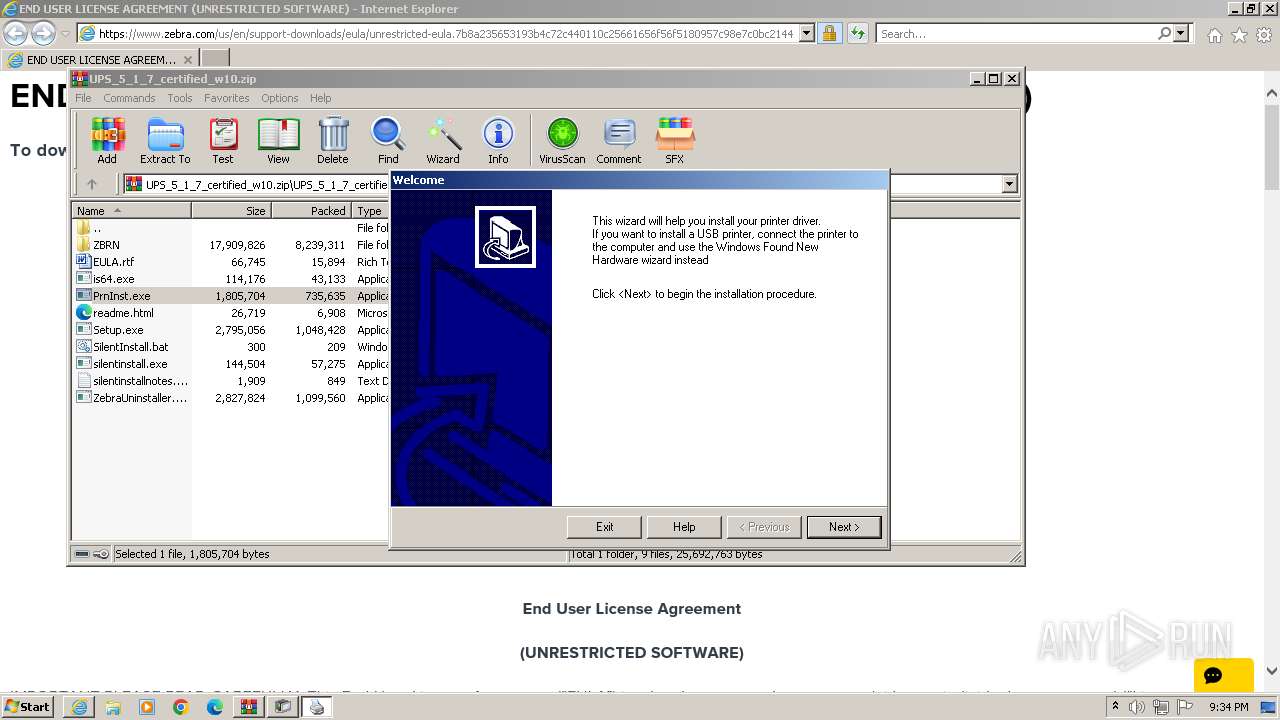
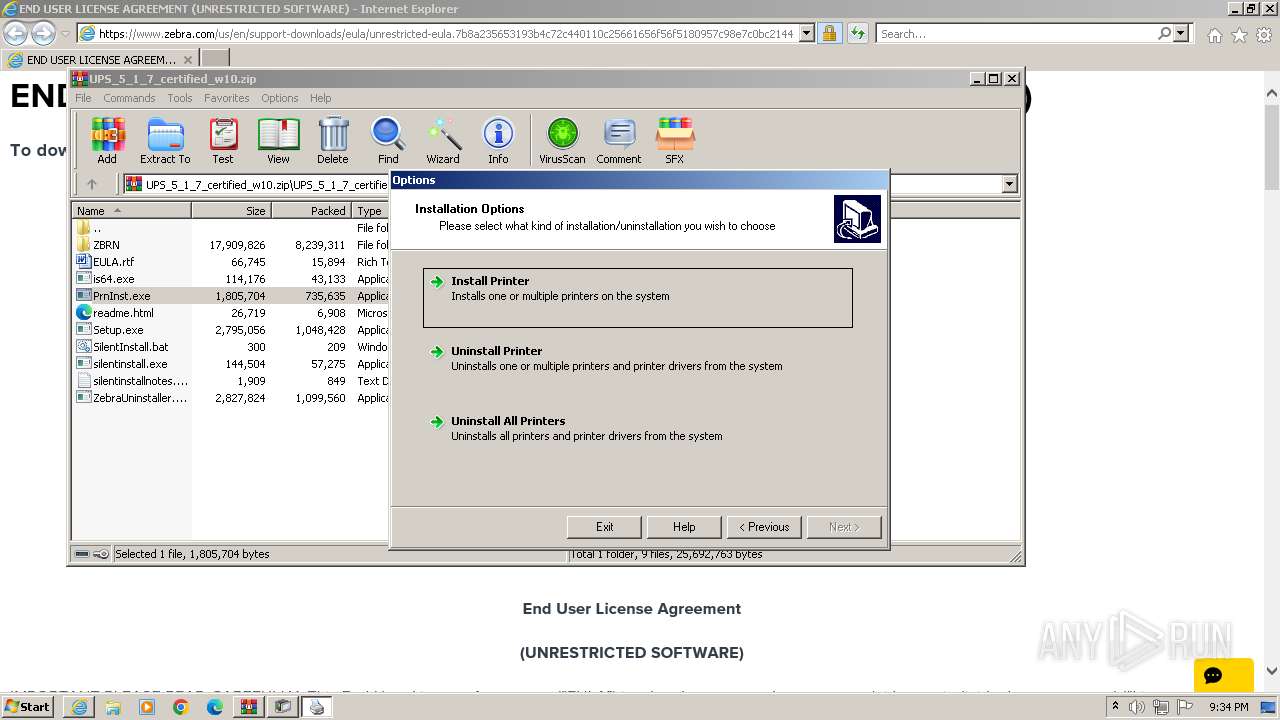
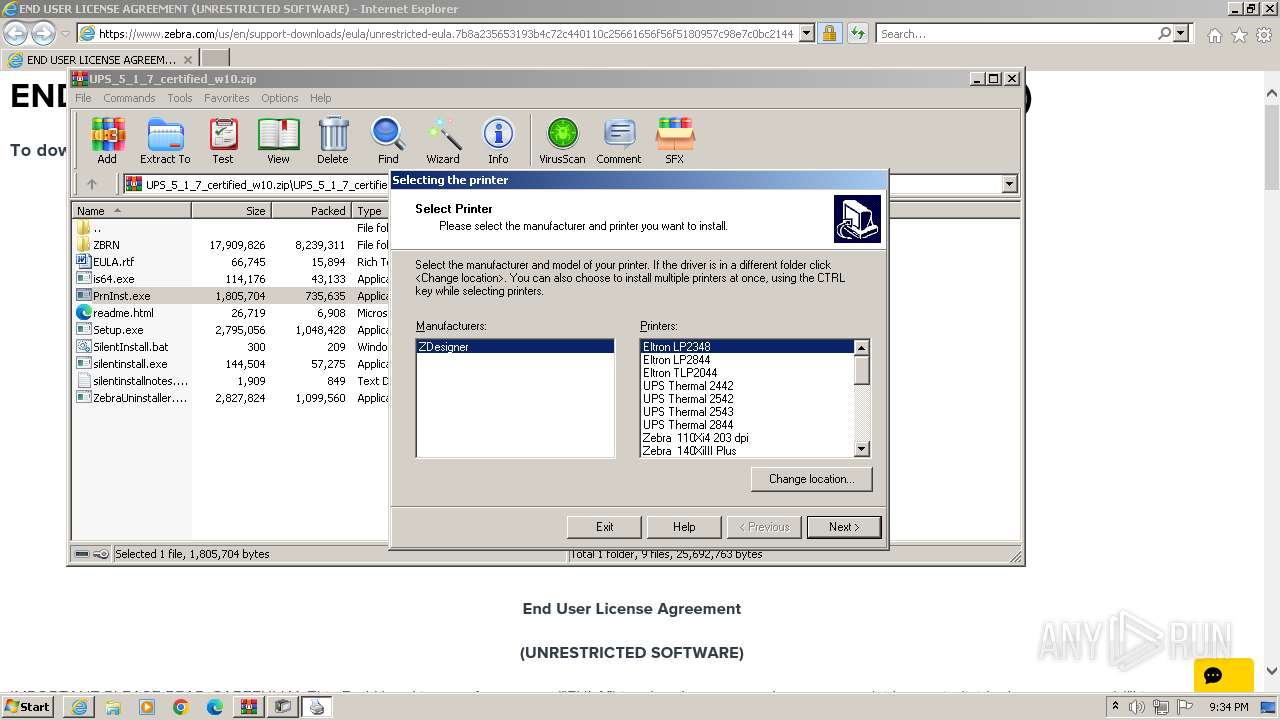
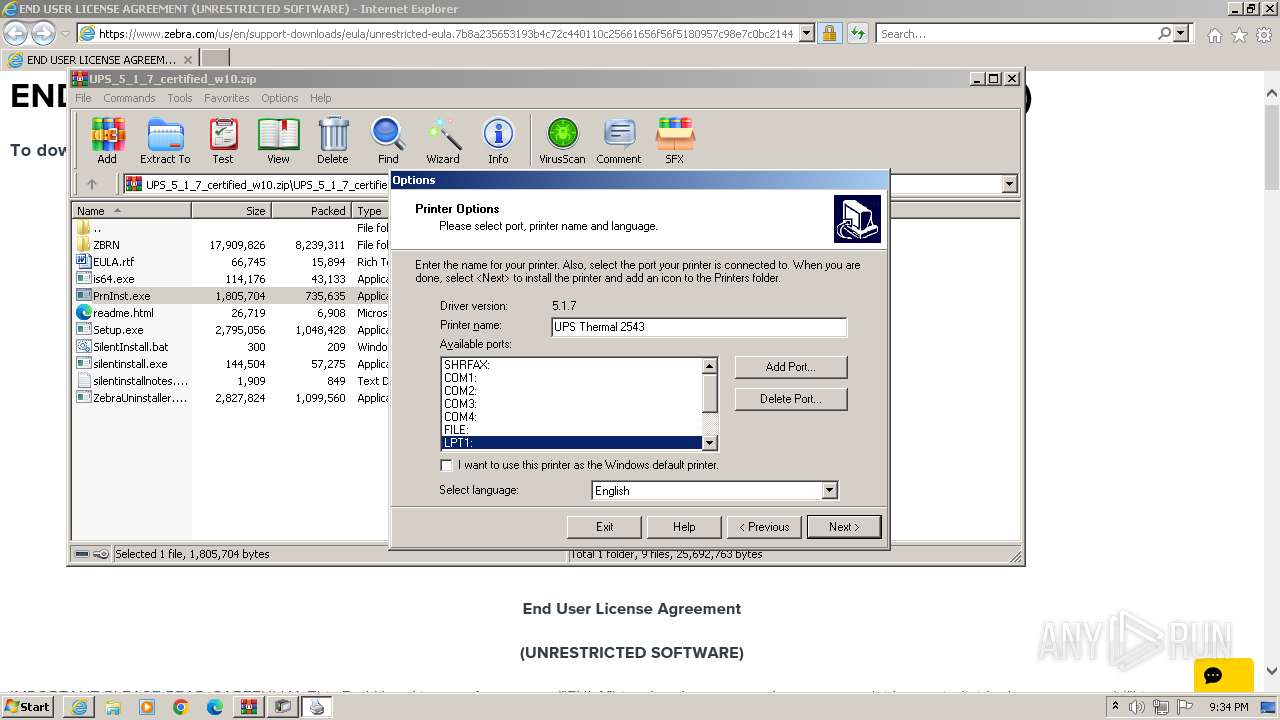
| 552 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa632.25905\UPS_5_1_7_certified_w10\PrnInst.exe" /NOWEL | C:\Users\admin\AppData\Local\Temp\Rar$EXa632.25905\UPS_5_1_7_certified_w10\PrnInst.exe | Setup.exe | ||||||||||||
User: admin Company: Zebra Technologies International, LLC Integrity Level: HIGH Description: Printer Installation Wizard Exit code: 0 Version: 5.0.3 Modules
| |||||||||||||||
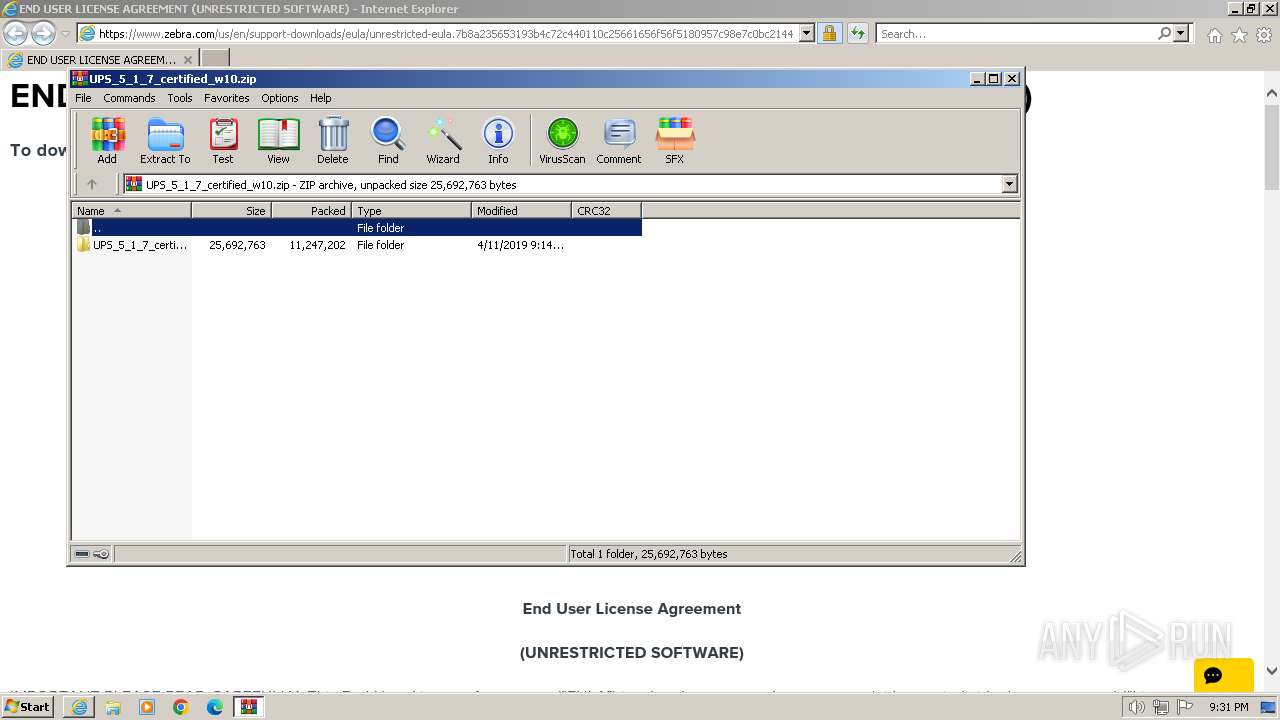
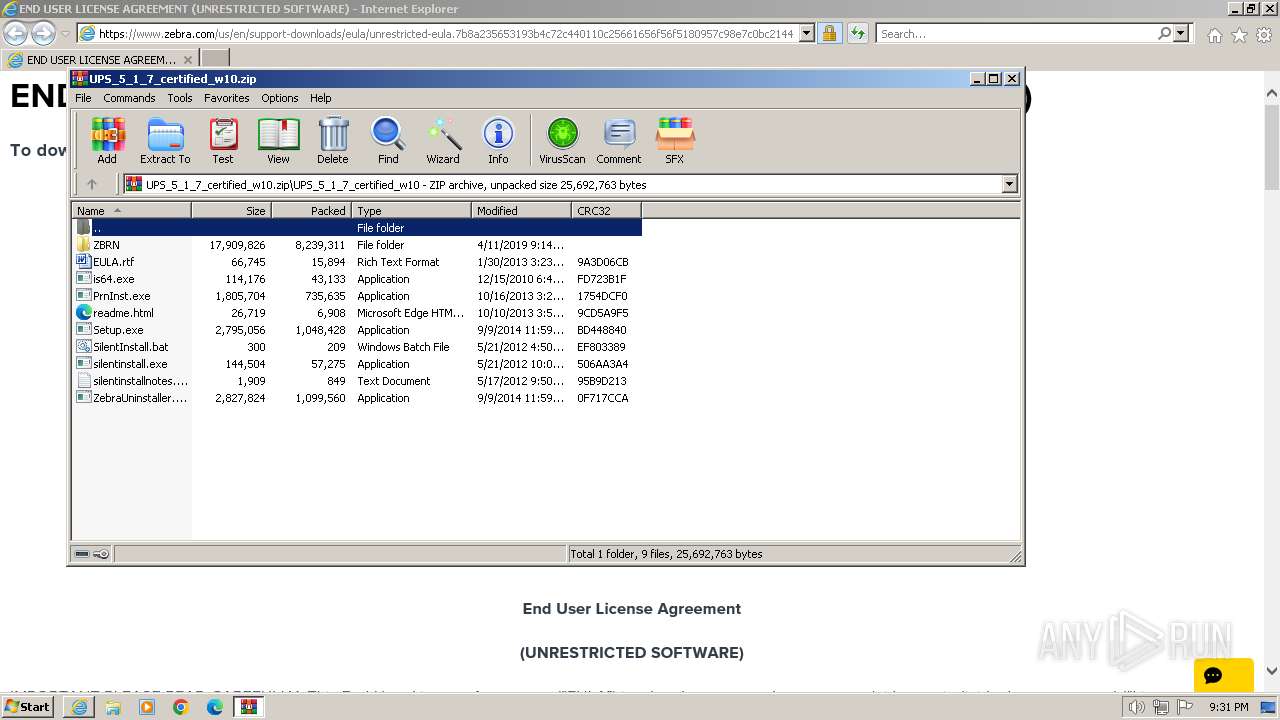
| 632 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\UPS_5_1_7_certified_w10.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 876 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{6ef979df-8342-2523-8110-fc5ea4d64652}\ZBRN.inf" "0" "626353a0b" "00000330" "WinSta0\Default" "000005D4" "208" "C:\Users\admin\AppData\Local\Temp\Rar$EXa632.25905\UPS_5_1_7_certified_w10\ZBRN" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
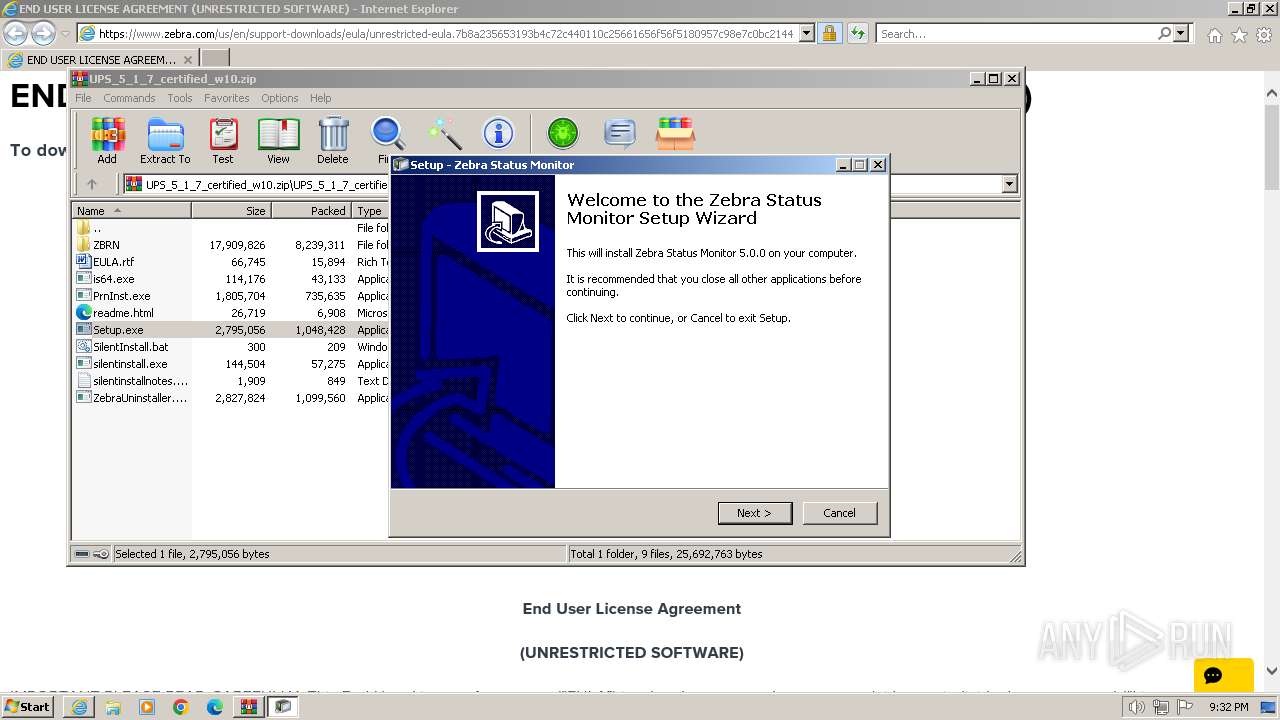
| 968 | "C:\Program Files\Zebra Technologies\Status Monitor\Status Monitor\StatusMonitor.exe" /STARTMINIMIZE | C:\Program Files\Zebra Technologies\Status Monitor\Status Monitor\StatusMonitor.exe | — | StatMonSetup.tmp | |||||||||||
User: admin Company: Zebra Technologies Corporation Integrity Level: HIGH Description: Zebra Status Monitor Exit code: 0 Version: 5.0.0 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.zebra.com/us/en/support-downloads/eula/unrestricted-eula.7b8a235653193b4c72c440110c25661656f56f5180957c98e7c0bc2144149cd156a1bc6e684725abae8eaa3b64ee1090a63134434792cf7fe7ebd953120a60cd367633fe9f513f4af05bcf3ca8fdcf836c93e23b0860d2ecb3b9f68761e10d9e250a5e4c91d53813.html#" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
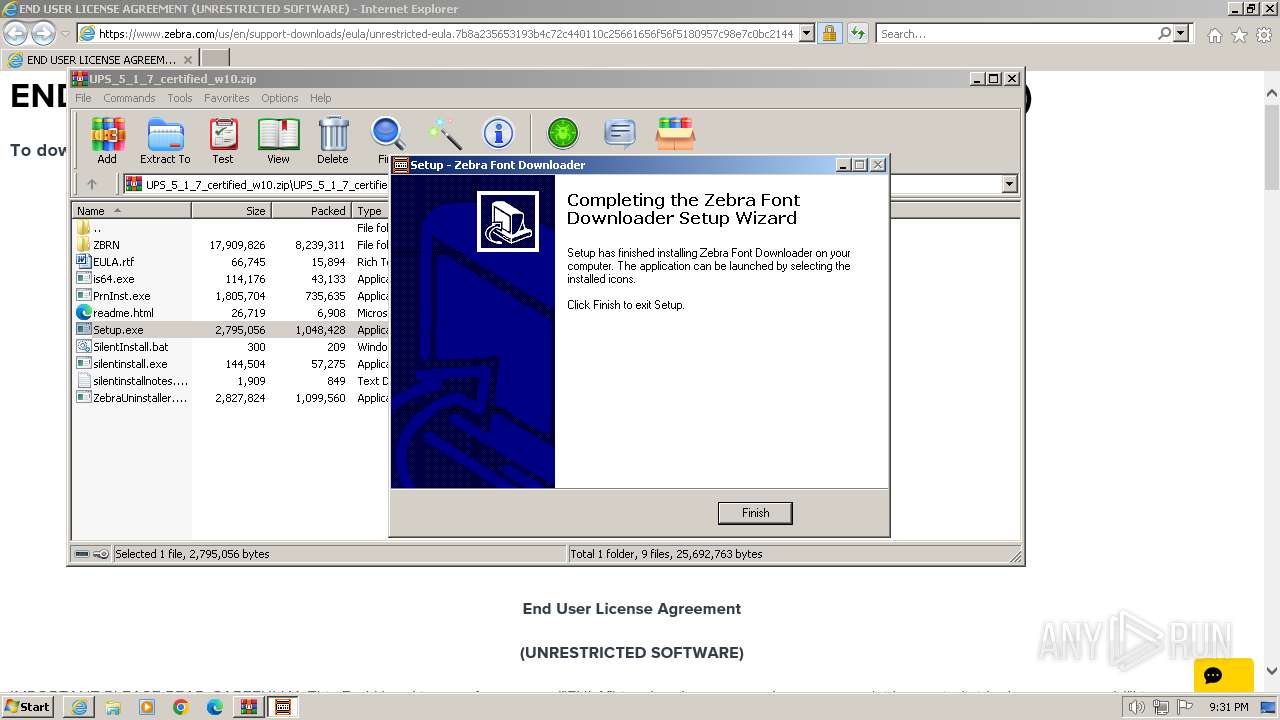
| 1196 | C:\Users\admin\AppData\Local\Temp\Rar$EXa632.25905\UPS_5_1_7_certified_w10\ZBRN\ZebraFD.exe /LANG=en | C:\Users\admin\AppData\Local\Temp\Rar$EXa632.25905\UPS_5_1_7_certified_w10\ZBRN\ZebraFD.exe | — | PrnInst.exe | |||||||||||
User: admin Company: Zebra Technologies Corporation Integrity Level: HIGH Description: Exit code: 0 Version: 2.2.3.4260 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1072 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2100 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2360 | "C:\Users\admin\AppData\Local\Temp\is-ED29C.tmp\StatMonSetup.tmp" /SL5="$60210,426073,74752,C:\Users\admin\AppData\Local\Temp\Rar$EXa632.25905\UPS_5_1_7_certified_w10\ZBRN\StatMonSetup.exe" /LANG=en | C:\Users\admin\AppData\Local\Temp\is-ED29C.tmp\StatMonSetup.tmp | StatMonSetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Zebra Technologies\Zebra Font Downloader\Font Download\ZDDownloader2.exe" /regserver | C:\Program Files\Zebra Technologies\Zebra Font Downloader\Font Download\ZDDownloader2.exe | — | is-6FR2U.tmp | |||||||||||
User: admin Company: Zebra Technologies Corporation Integrity Level: HIGH Description: ZebraDesigner Font Downloader Exit code: 0 Version: 2.2.3.4267 Modules
| |||||||||||||||
Total events
36 791
Read events
35 762
Write events
1 023
Delete events
6
Modification events
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
655
Suspicious files
123
Text files
367
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\zebra-nav.min[1].js | text | |
MD5:7963C4BD45F73EFA7727D8F7EDC882ED | SHA256:293C065A22A886F8ED6E16F46EEF8D49FE705554C1FD5D3822EE16001EF2D745 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:5715E1E4E62EE95E6C31685978092461 | SHA256:B73D92204F95668AF2B0D464CF51A0E084D30E829BFC72A7AB917B6A45B5E226 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\otSDKStub[1].js | text | |
MD5:72B4D7D753CB0A37F1E4B3320756A981 | SHA256:98BC0753B3F7392176A4AF252BFAE9BCD1F2804B73DEE374119899D8F52AE3D2 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\csrf.min[1].js | text | |
MD5:652A558C3774088B61B0530C184710D1 | SHA256:90A9ACAA2B73D4E87BC59BEB161A8E9771D517AE8577BA38F6724F40D3461073 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:BAD85A6F47015F6882849600E6ED8367 | SHA256:50151F7A69FC73BCA05EFB1008A5D6E113B885658042462B5F29DF87FF934CDD | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | binary | |
MD5:F8DF1055A0B35254F01B9D753415EEF1 | SHA256:8F855A4D66FC4158158D02538A95516C1B1FF2008CB5EB8F80C583890EB227EF | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | binary | |
MD5:088EE94D2ACDC4B5200B659377D0C6FD | SHA256:E6248B87D71FE454B559143035485BCF5BCBB7CD8CAE2C9C6F29045597A9CDA7 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_A30EA9B4E1BC5DBF09A8EF399E086D27 | binary | |
MD5:D7A1886A5AD7B773CD7C3A038226E490 | SHA256:B3DCF45050FCEE450E3252B6B58804963DBE9DE8C3BE5537074F13E6C90B6E47 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_A30EA9B4E1BC5DBF09A8EF399E086D27 | binary | |
MD5:511170ECD65A3C63D654ACFB2CA9CD47 | SHA256:C94088D867E4197C42DB891C8BD6A640B05EB3CA791B60BEF28EFED6D047769B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
101
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2072 | iexplore.exe | GET | 200 | 184.24.77.185:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7a9d8baceff24343 | unknown | compressed | 4.66 Kb | unknown |
2072 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
2072 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | binary | 471 b | unknown |
2072 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
2072 | iexplore.exe | GET | 200 | 184.24.77.185:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?16e53a13f7f2d96f | unknown | compressed | 4.66 Kb | unknown |
2072 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | unknown | binary | 471 b | unknown |
2072 | iexplore.exe | GET | 200 | 108.138.34.140:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | binary | 2.02 Kb | unknown |
2072 | iexplore.exe | GET | 200 | 18.66.190.71:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | binary | 1.49 Kb | unknown |
2072 | iexplore.exe | GET | 200 | 18.66.142.79:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | unknown | binary | 1.37 Kb | unknown |
2072 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2072 | iexplore.exe | 23.67.131.85:443 | www.zebra.com | AKAMAI-AS | DE | unknown |
2072 | iexplore.exe | 184.24.77.185:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2072 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2072 | iexplore.exe | 104.18.130.236:443 | cdn.cookielaw.org | CLOUDFLARENET | — | unknown |
2072 | iexplore.exe | 184.24.77.138:443 | use.typekit.net | Akamai International B.V. | DE | unknown |
2072 | iexplore.exe | 151.101.128.114:443 | cdn.evgnet.com | FASTLY | US | unknown |
2072 | iexplore.exe | 23.213.165.28:443 | assets.adobedtm.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.zebra.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cdn.cookielaw.org |
| whitelisted |
use.typekit.net |
| whitelisted |
cdn.evgnet.com |
| whitelisted |
assets.adobedtm.com |
| whitelisted |
static.cloud.coveo.com |
| shared |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |