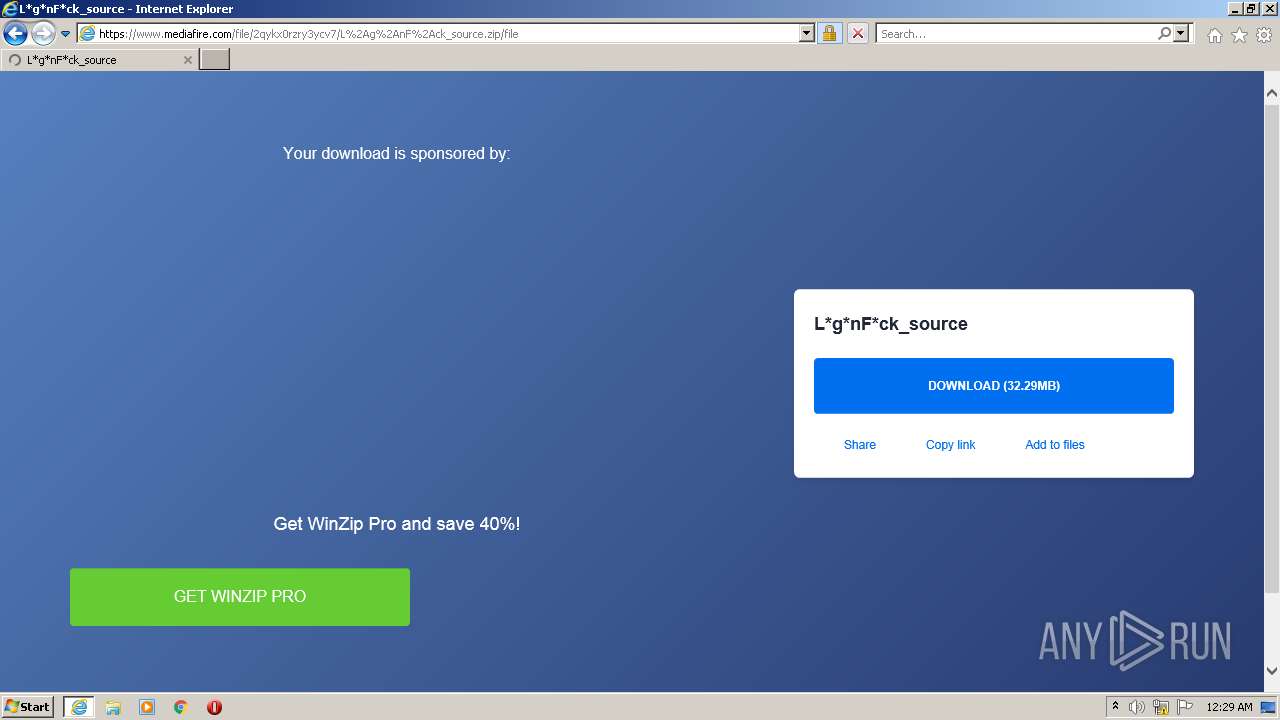
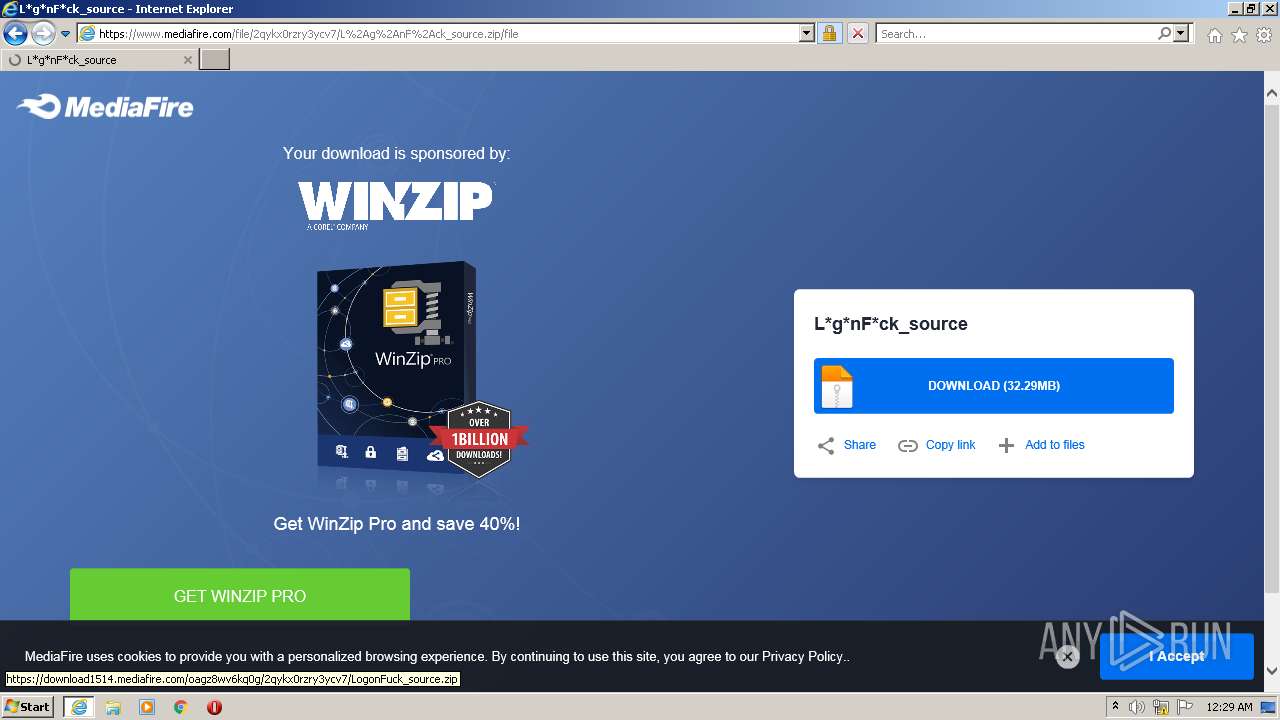
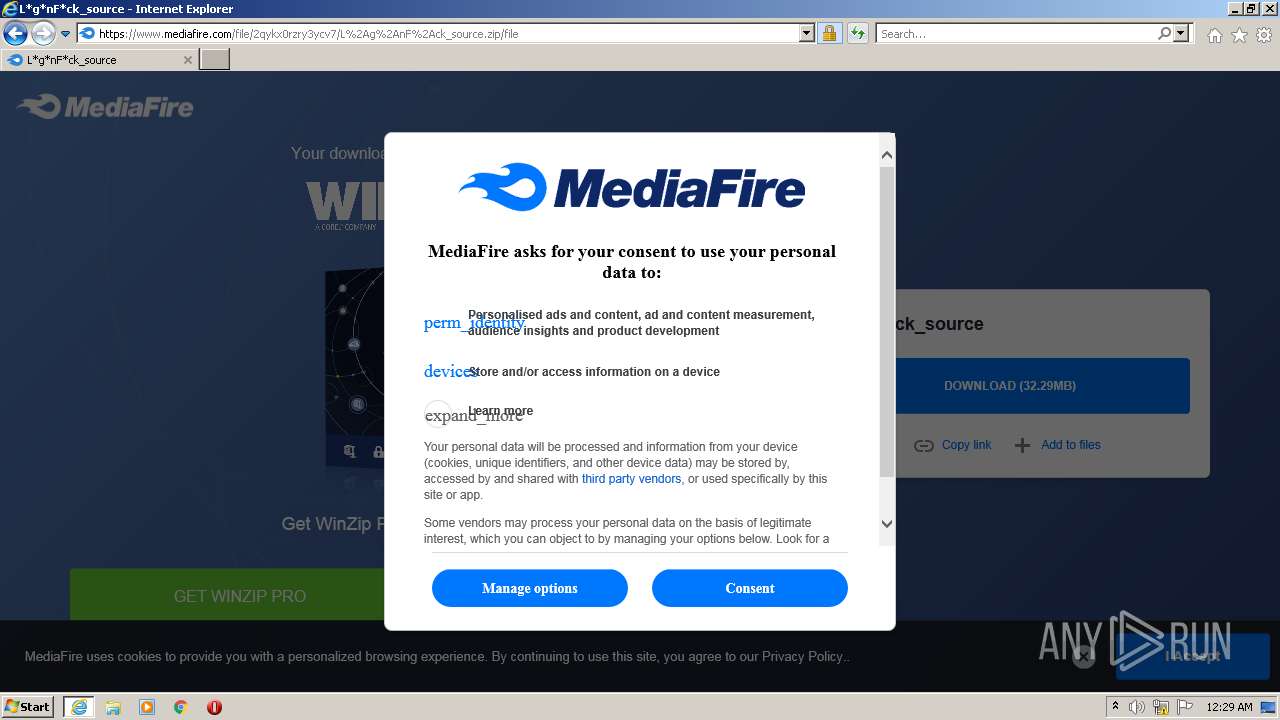
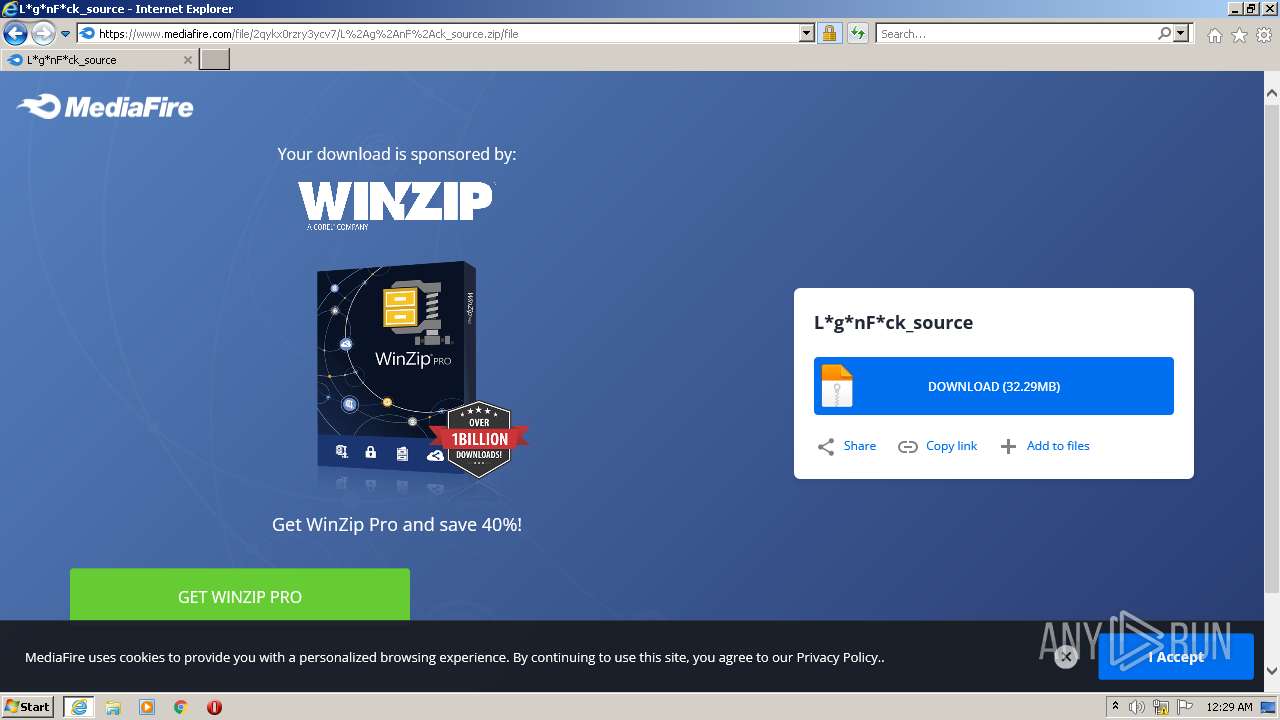
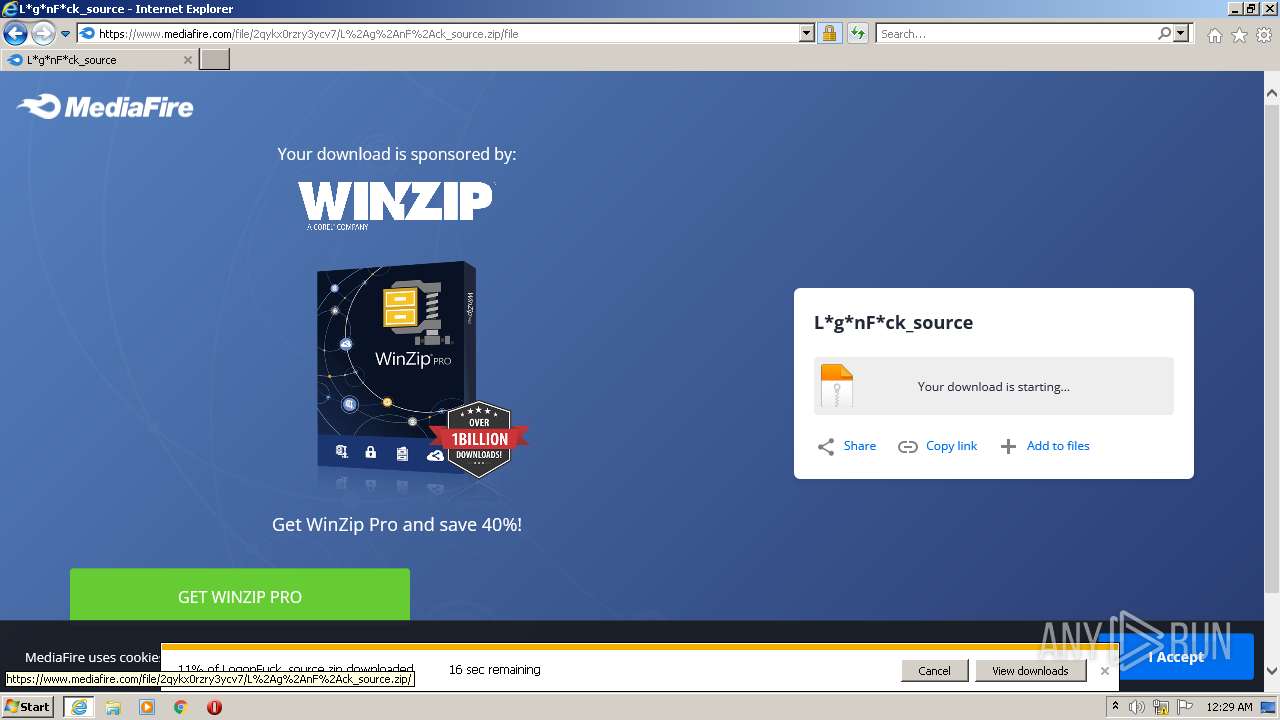
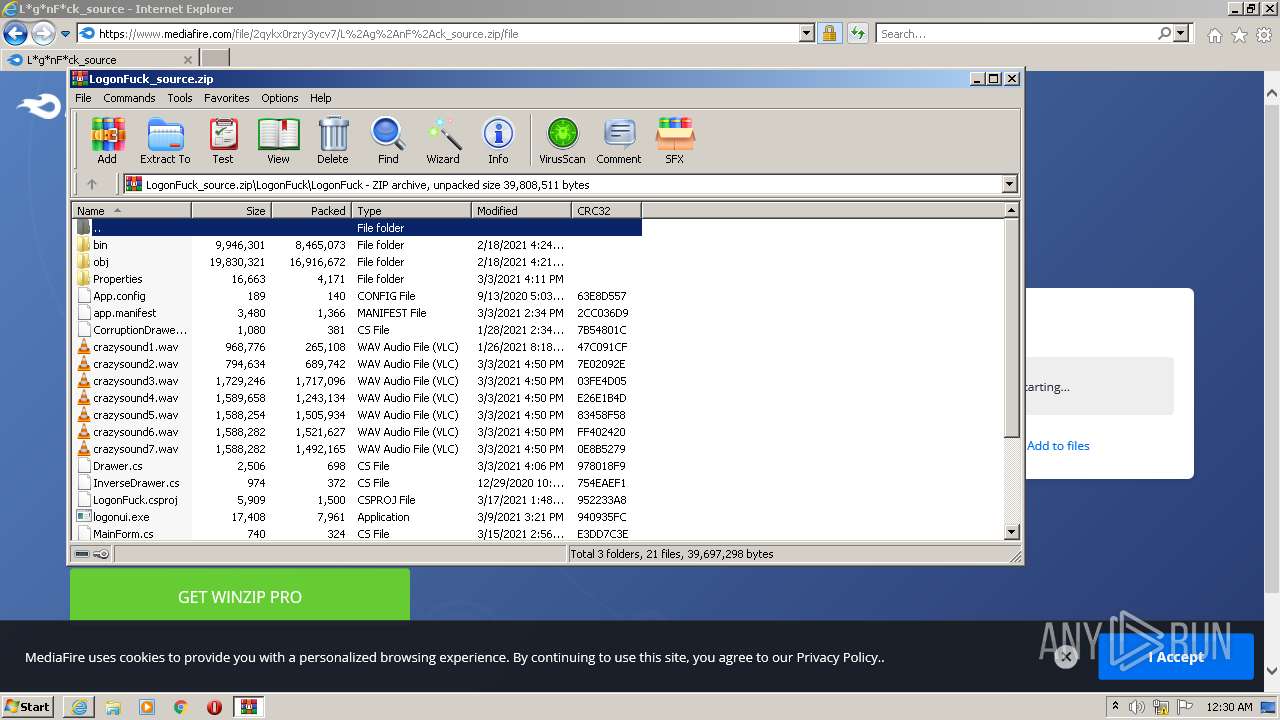
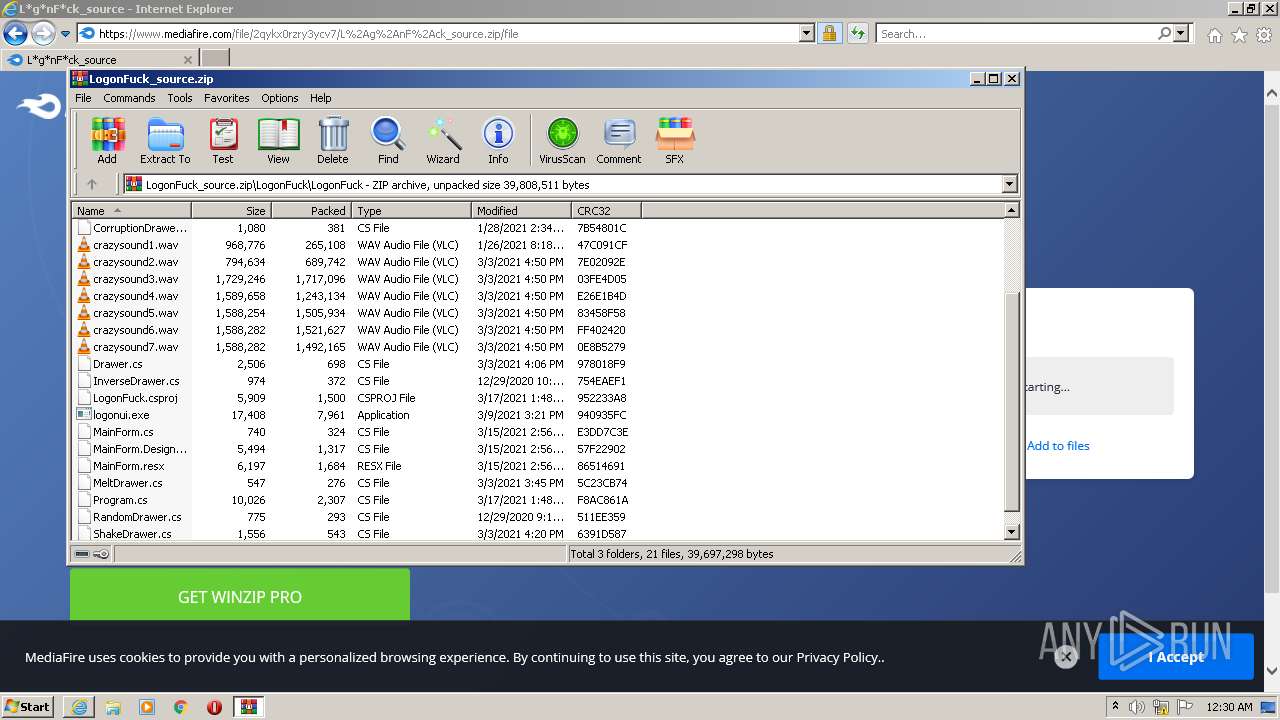
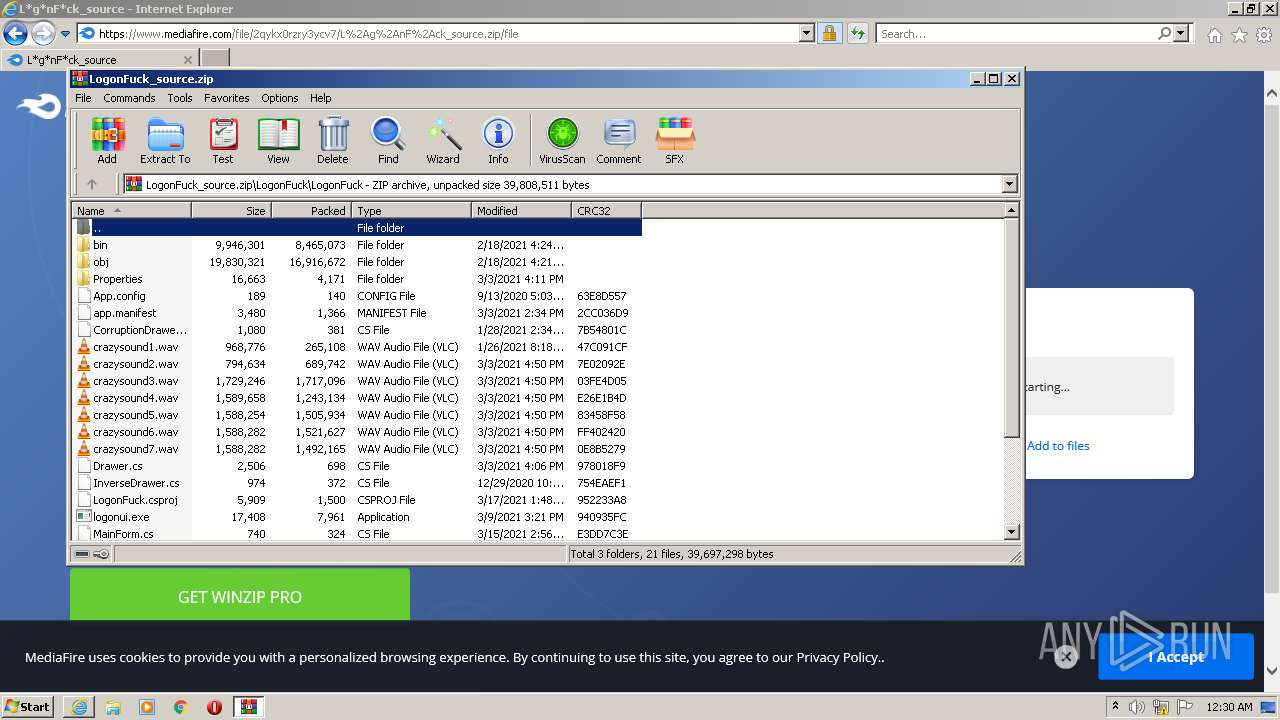
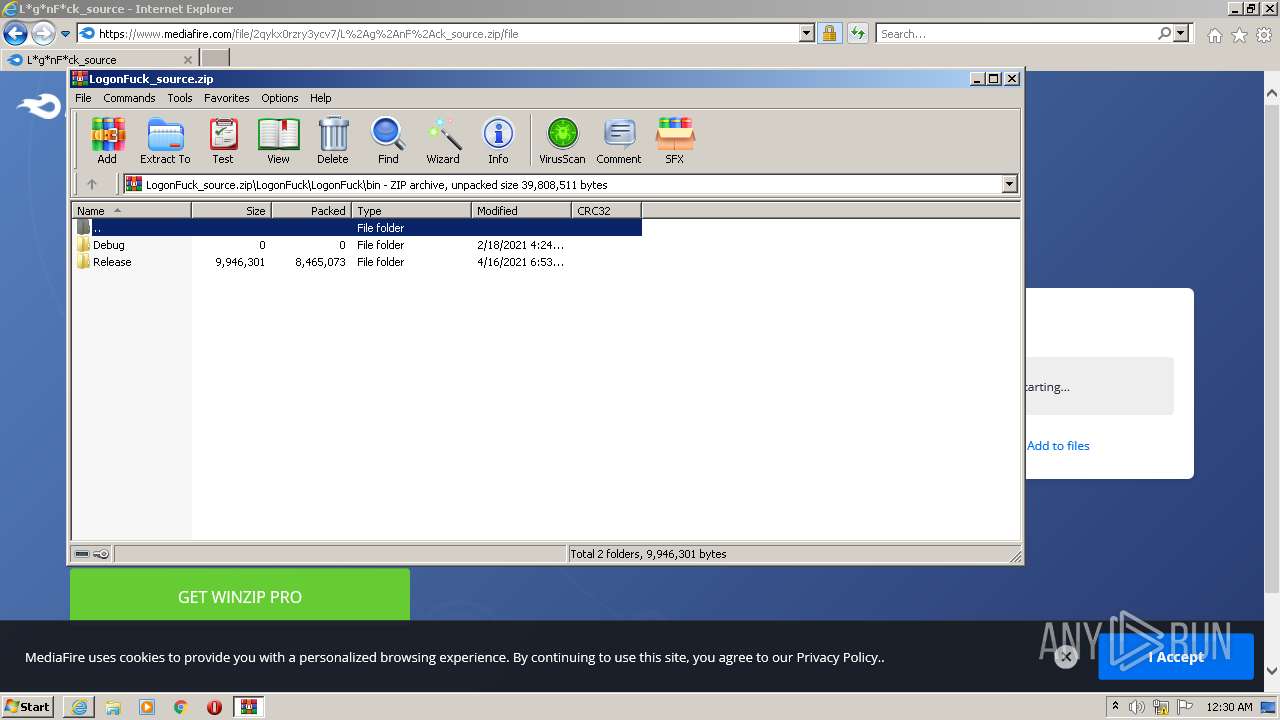
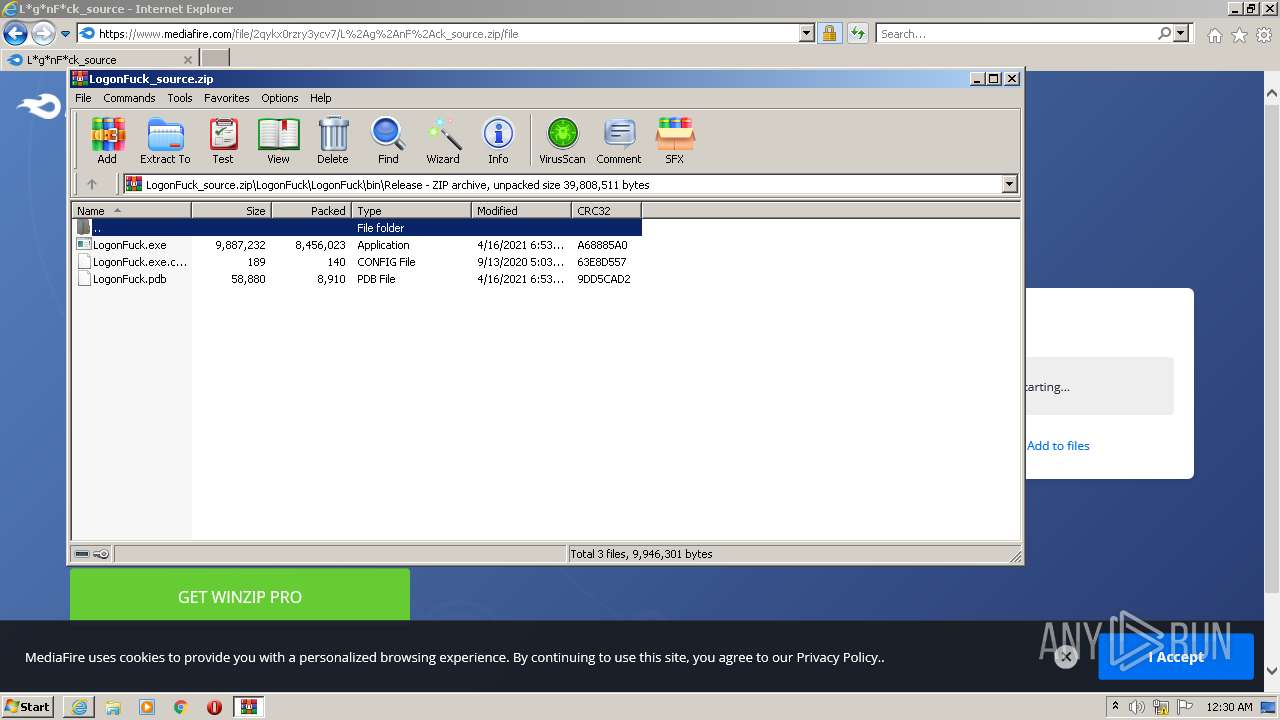
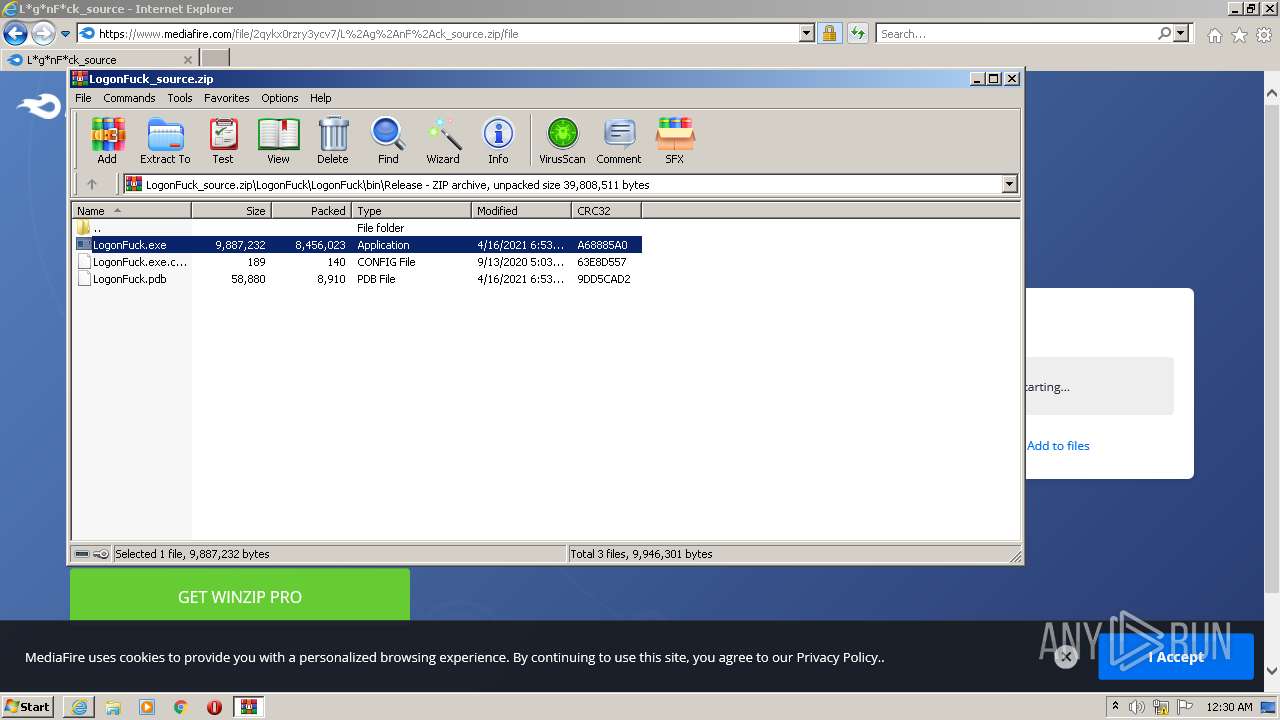
| URL: | https://www.youtube.com/redirect?event=video_description&redir_token=QUFFLUhqa05jSmxTT3FlTENtNnJXN0RiazZkT2EyVVUtQXxBQ3Jtc0trd2hvN3M1UV9CdTFnMG05cEFDVHI4RnhUcHFLbDhBb2VDQ1g1ekd1MDd4SFE3cktlQVB6MlpvazlWWDB5cW5tZTNBQkktYlgtVU5lYWFBMUdXc2ZUT05Xemhlc3hhaE02TjI3cVlSQU0tNDZvX1FZcw&q=https%3A%2F%2Fwww.mediafire.com%2Ffile%2F2qykx0rzry3ycv7%2FL%252Ag%252AnF%252Ack_source.zip%2Ffile |
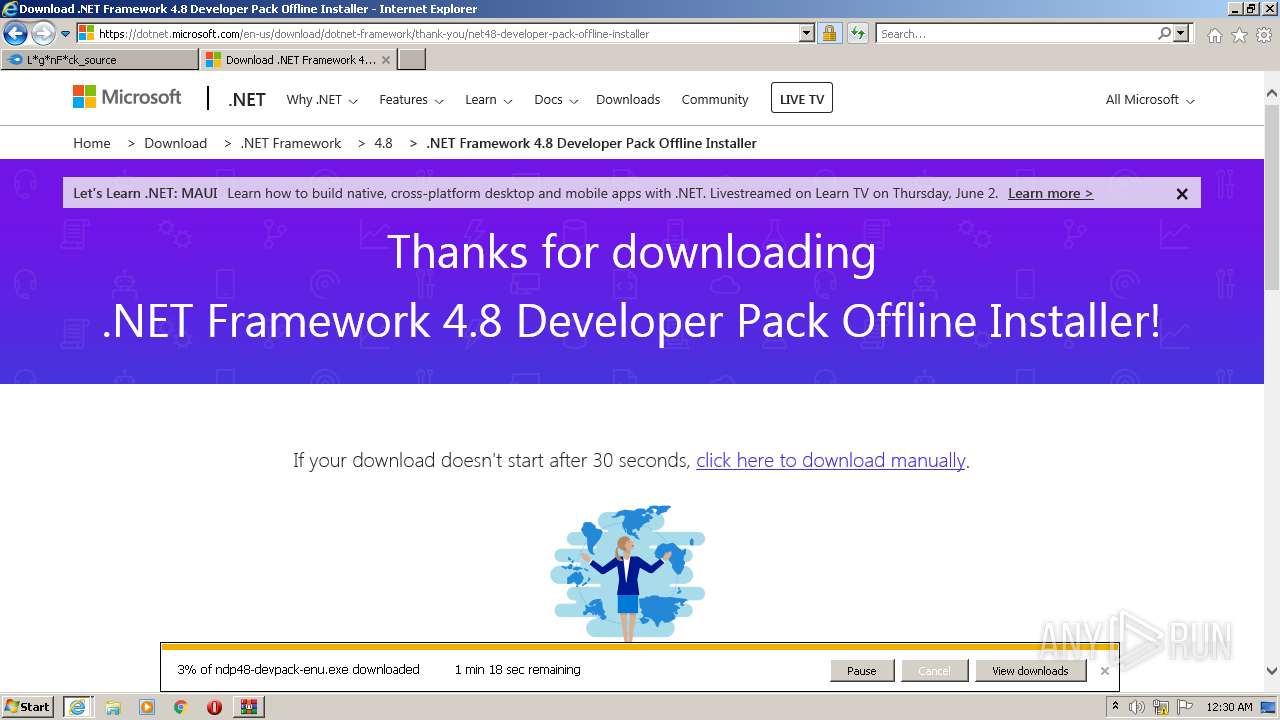
| Full analysis: | https://app.any.run/tasks/285245ca-33ae-4e66-827d-5e4faaa03504 |
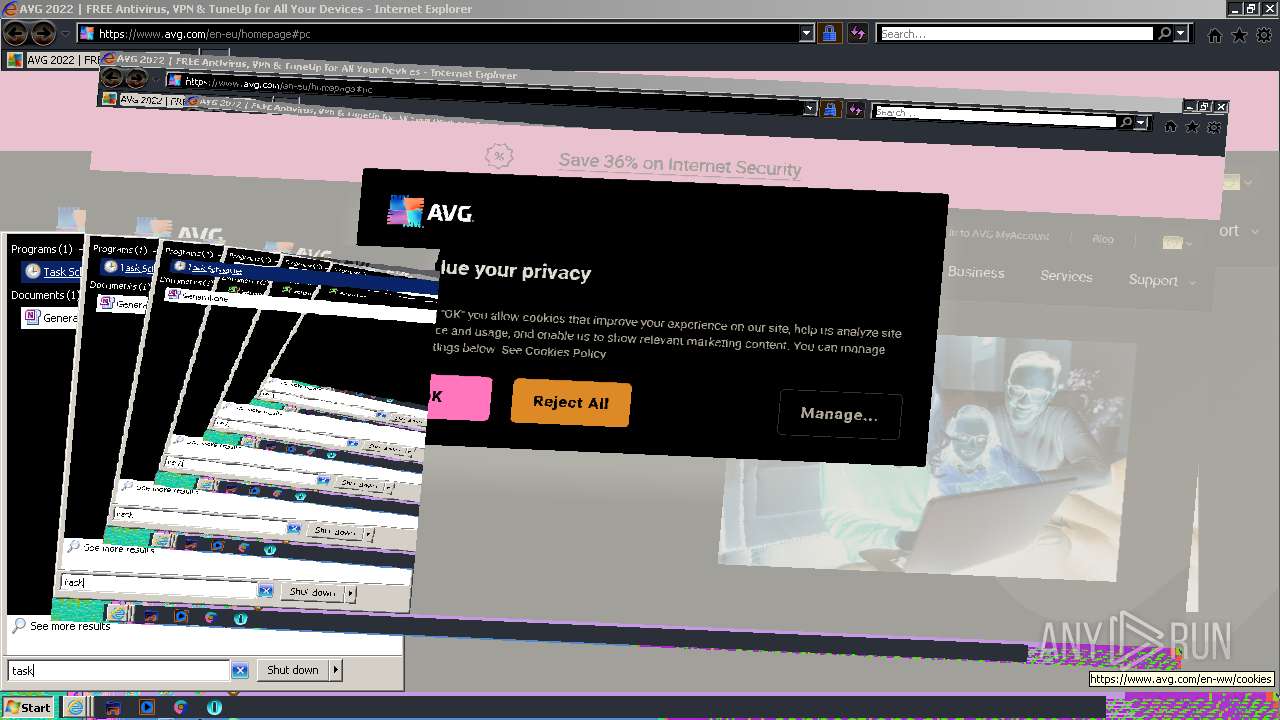
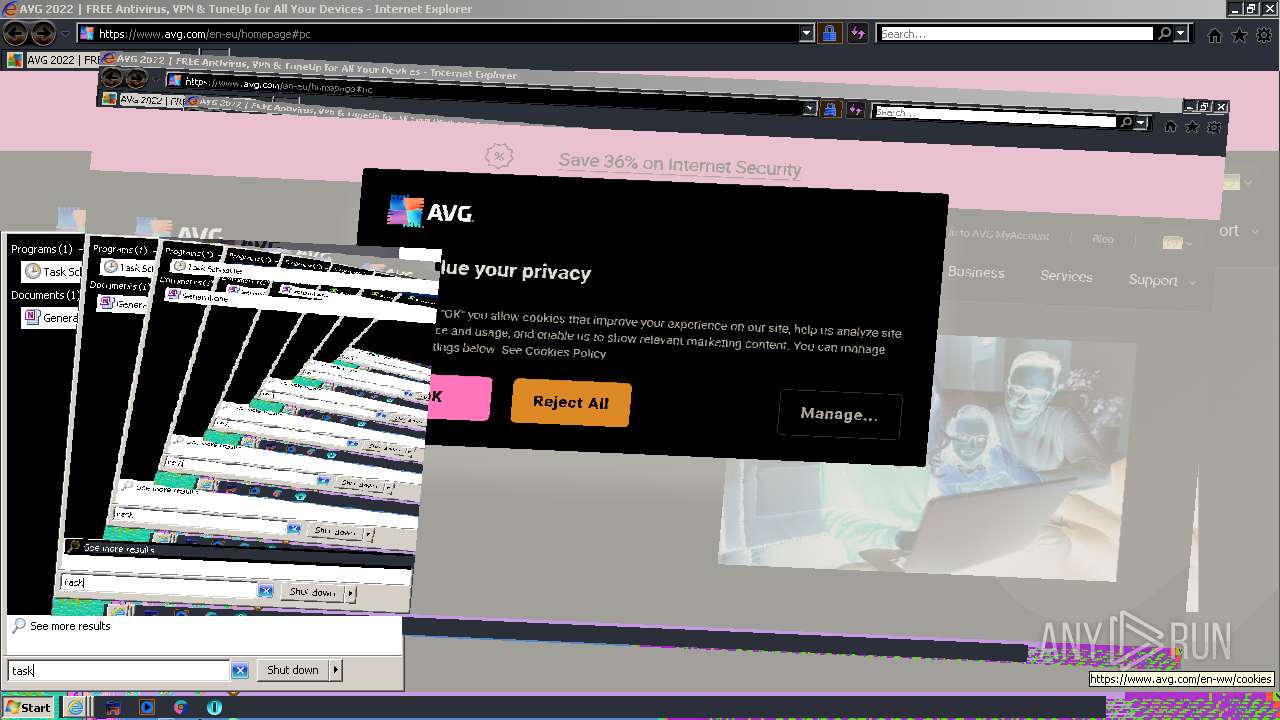
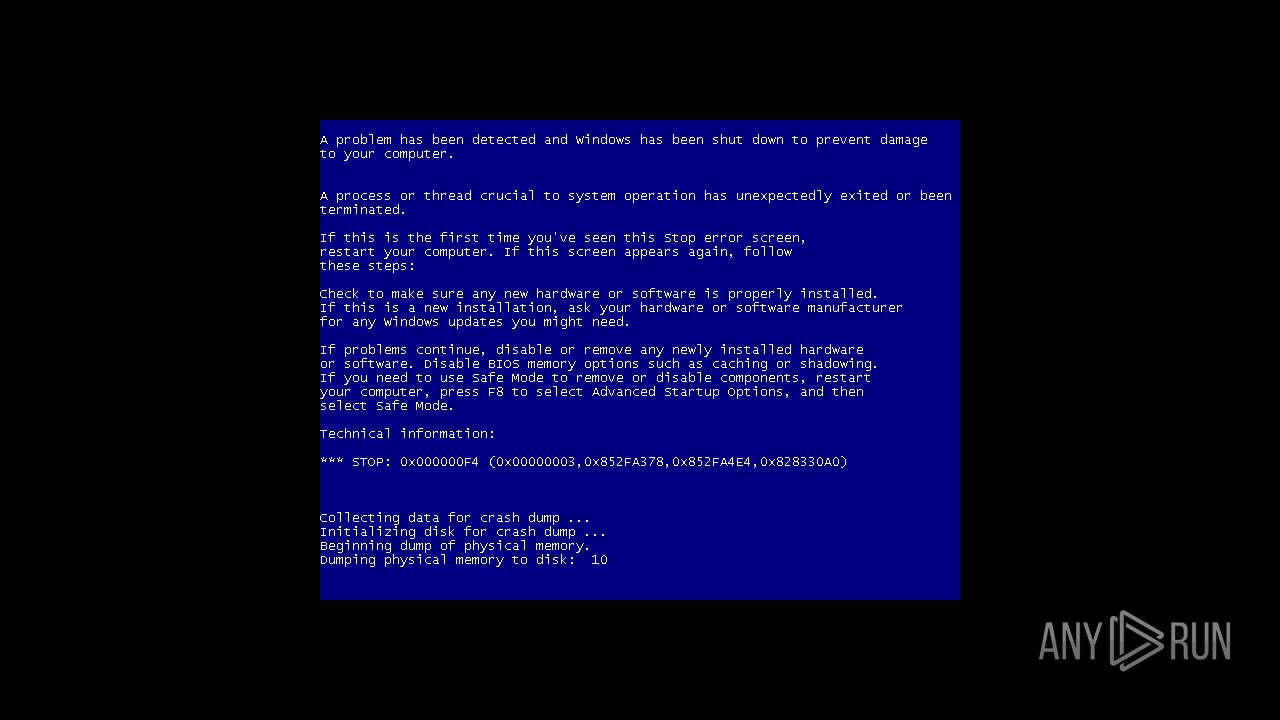
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 23:29:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 080BDCA01910CBC8B72DD30AC05B1E21 |
| SHA1: | 7A84E747273E8B222A09F24AF5342F17303C53E5 |
| SHA256: | A869F728B1956B6F55277CC3A984FF48A7552BA2F886EDDC7DDE327B55803F1A |
| SSDEEP: | 6:2OLUxGKmKLqZvNIb+EYTpvAbU23NQ3uaLtjN2N3zh3eG/7F8uRLQP6PO:2jGRfvNIaEYThAbUGQeaxWF3ee7F8uRc |
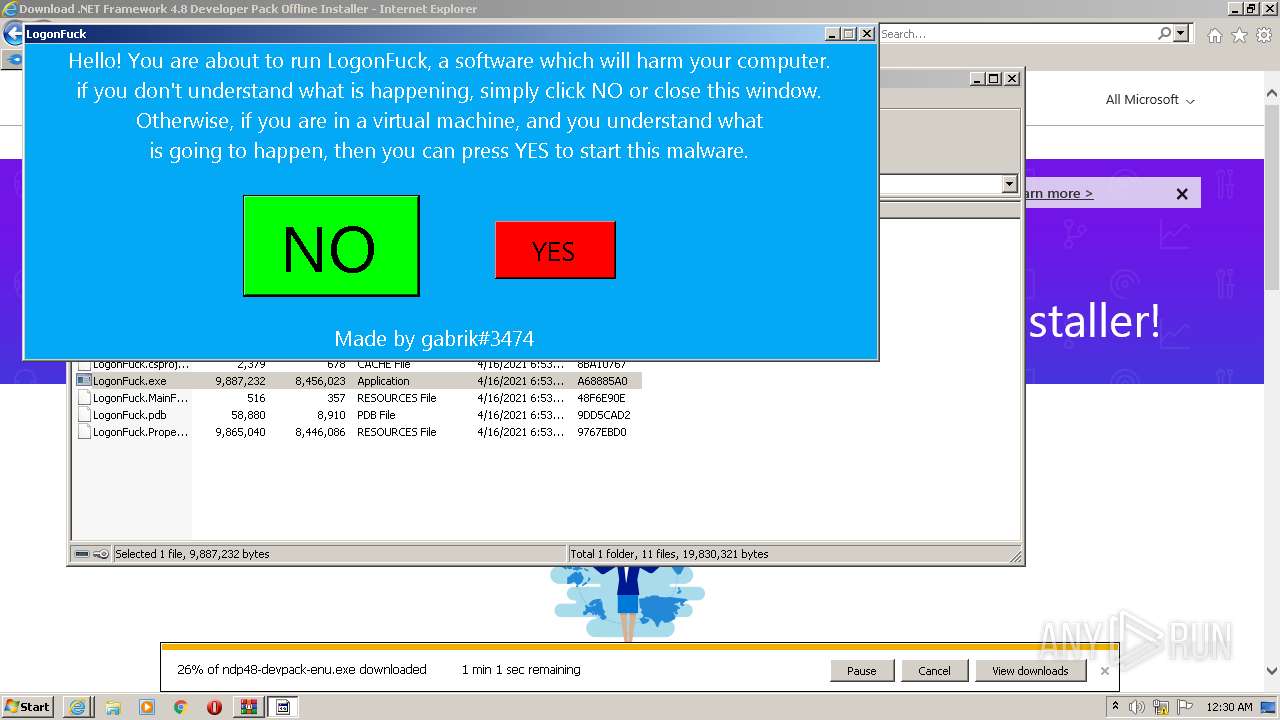
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 2724)
- iexplore.exe (PID: 824)
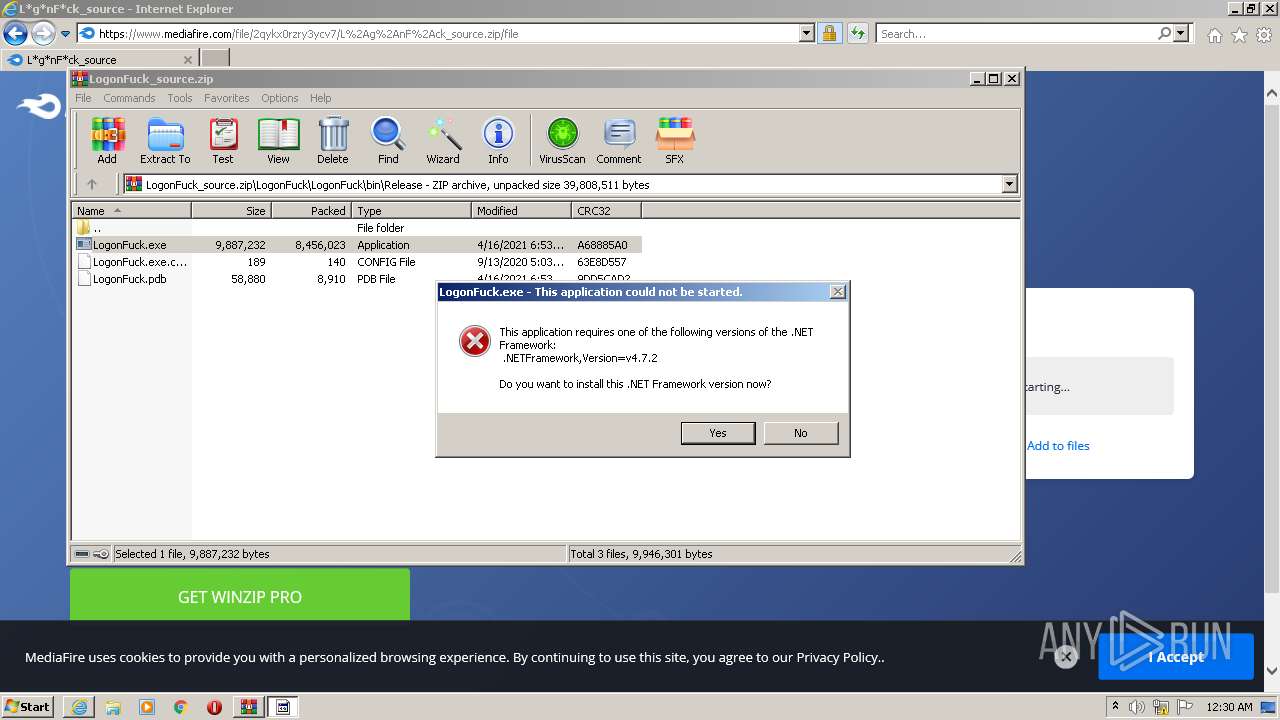
- LogonFuck.exe (PID: 4036)
Application was dropped or rewritten from another process
- LogonFuck.exe (PID: 3948)
- LogonFuck.exe (PID: 2912)
- LogonFuck.exe (PID: 2764)
- LogonFuck.exe (PID: 4036)
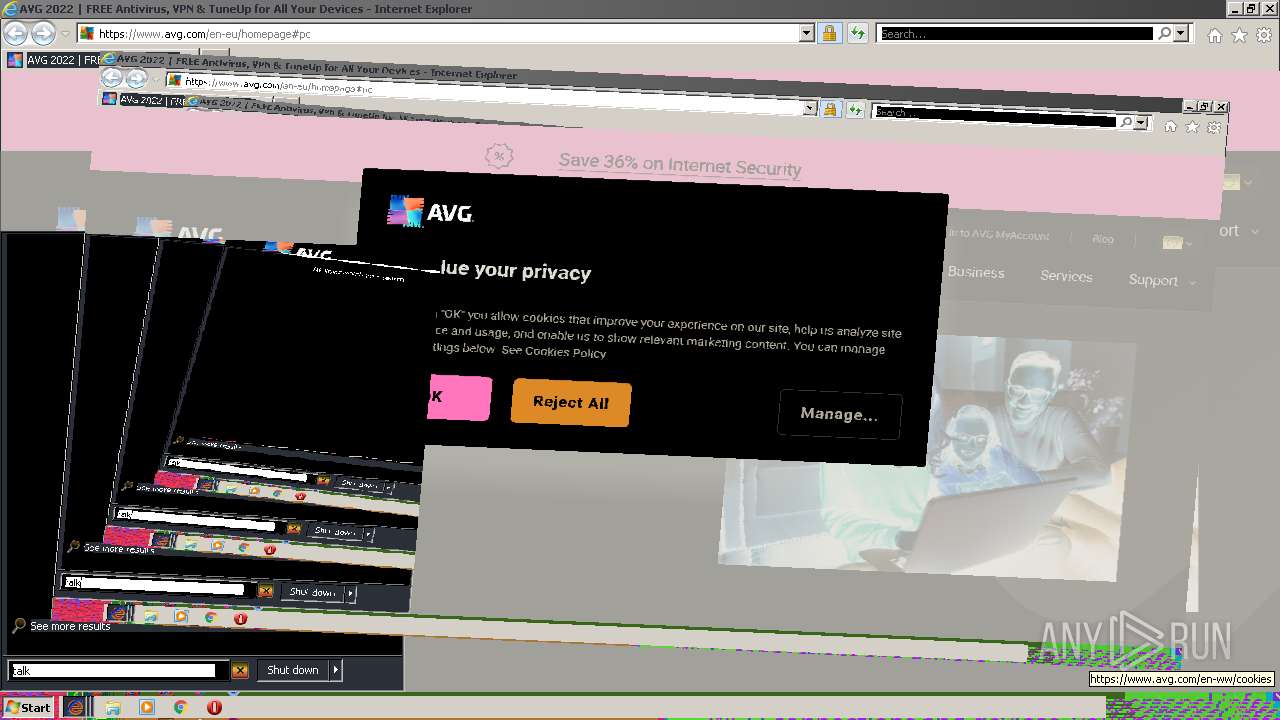
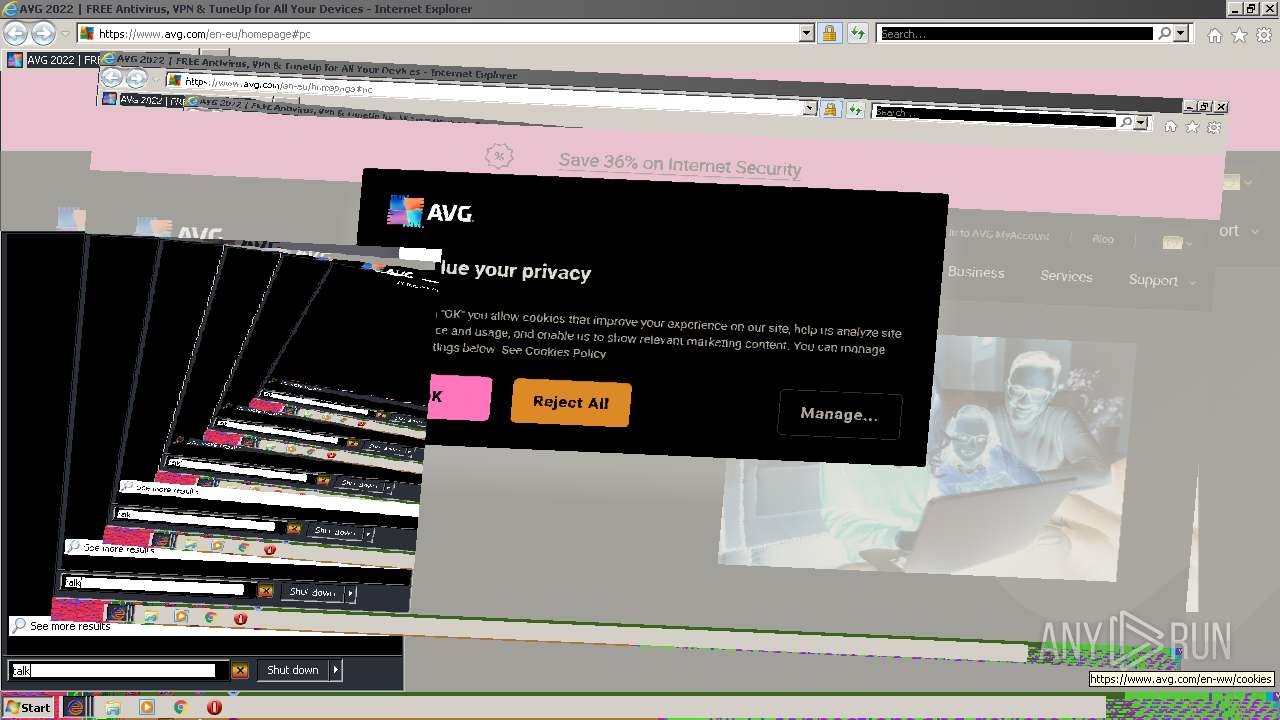
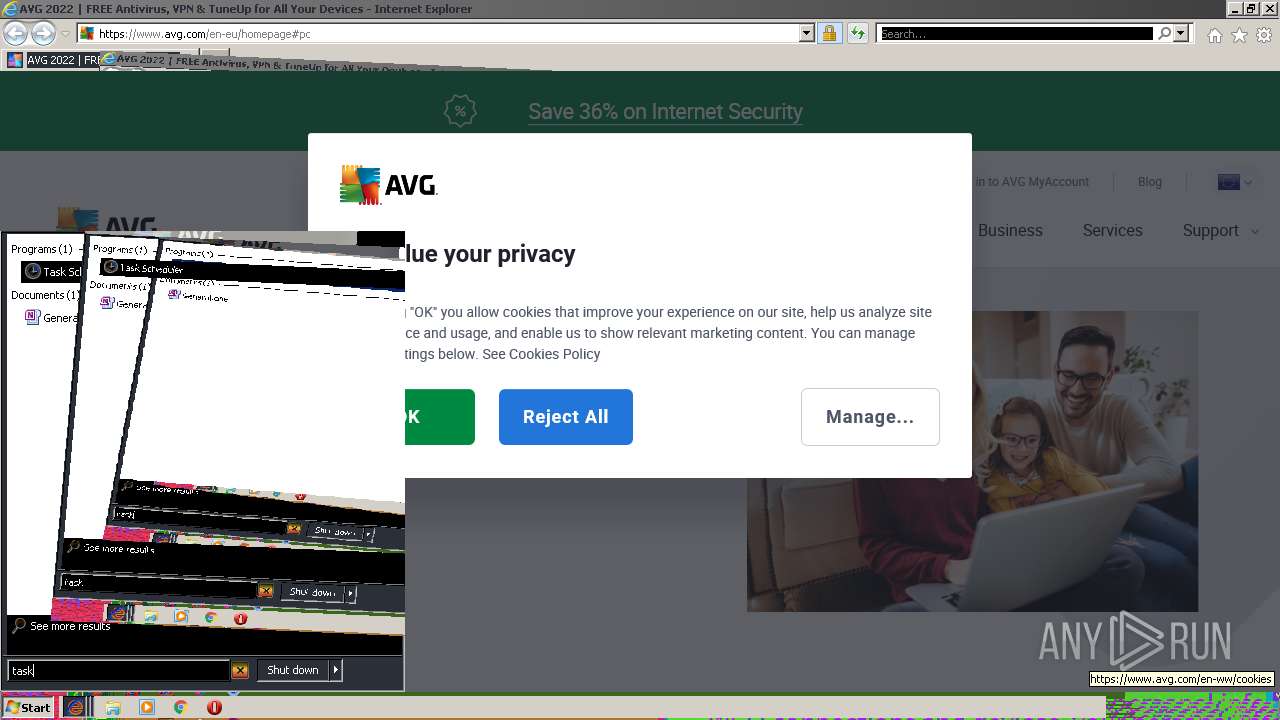
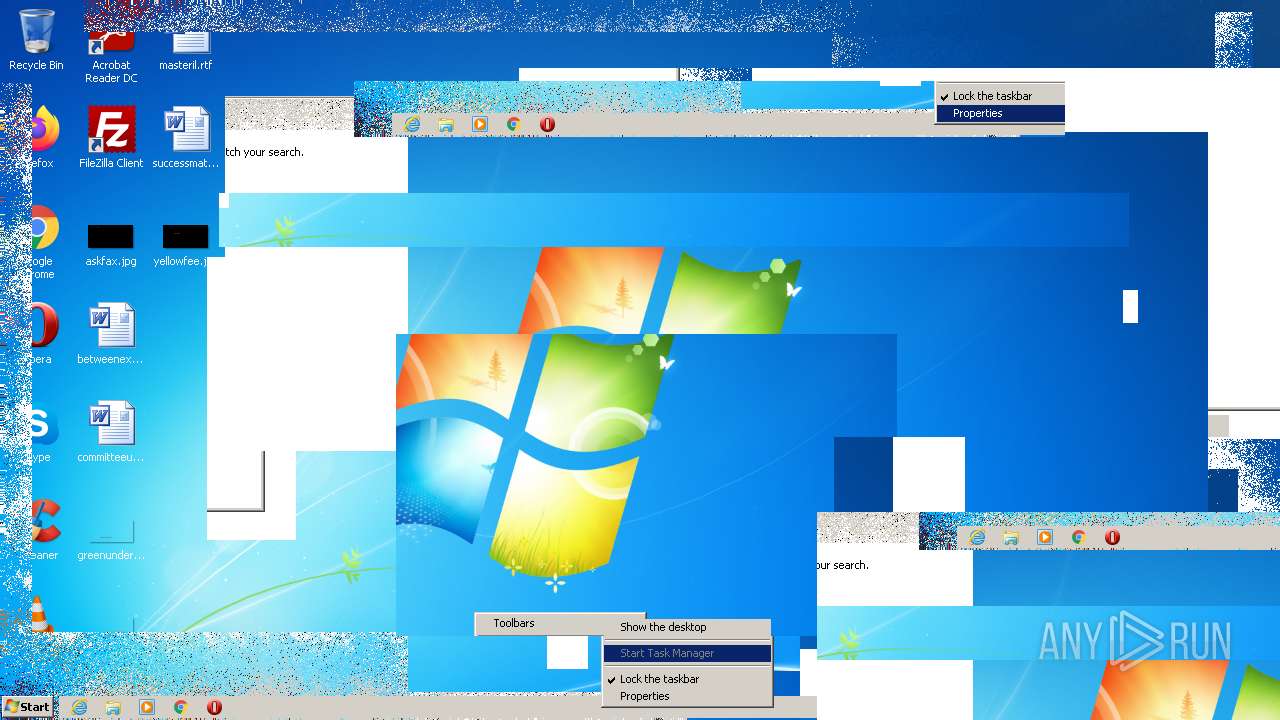
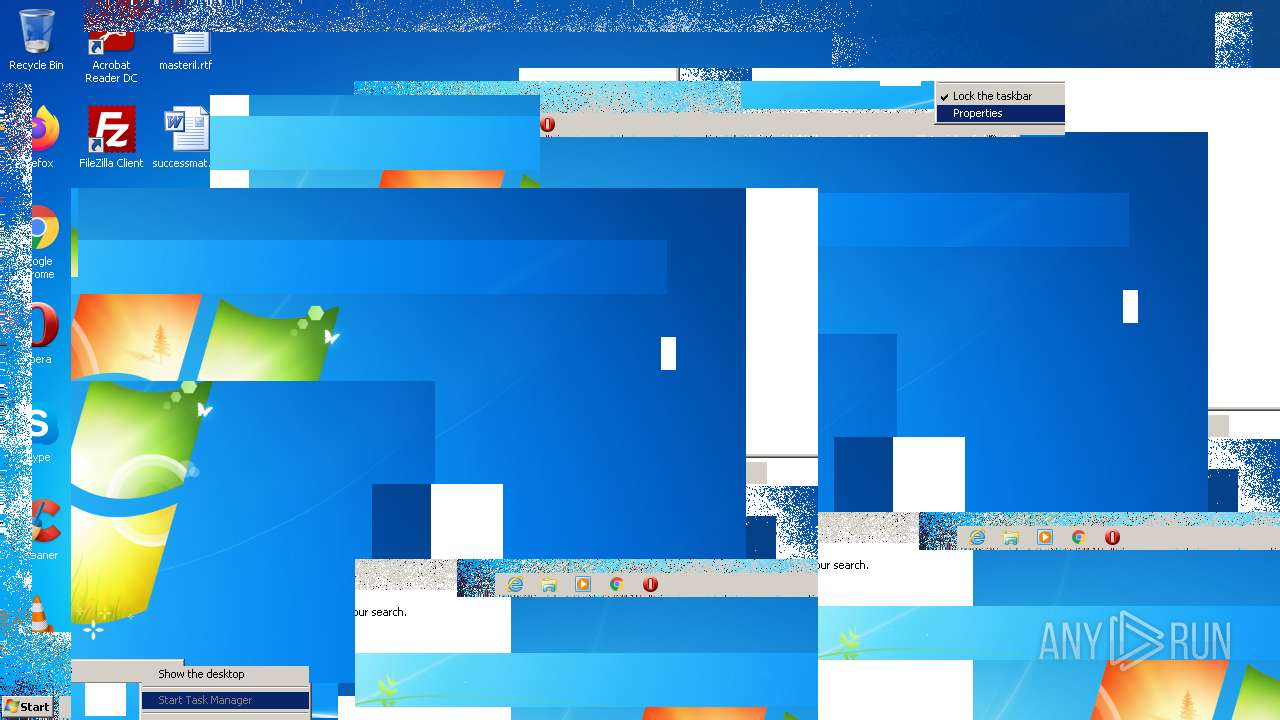
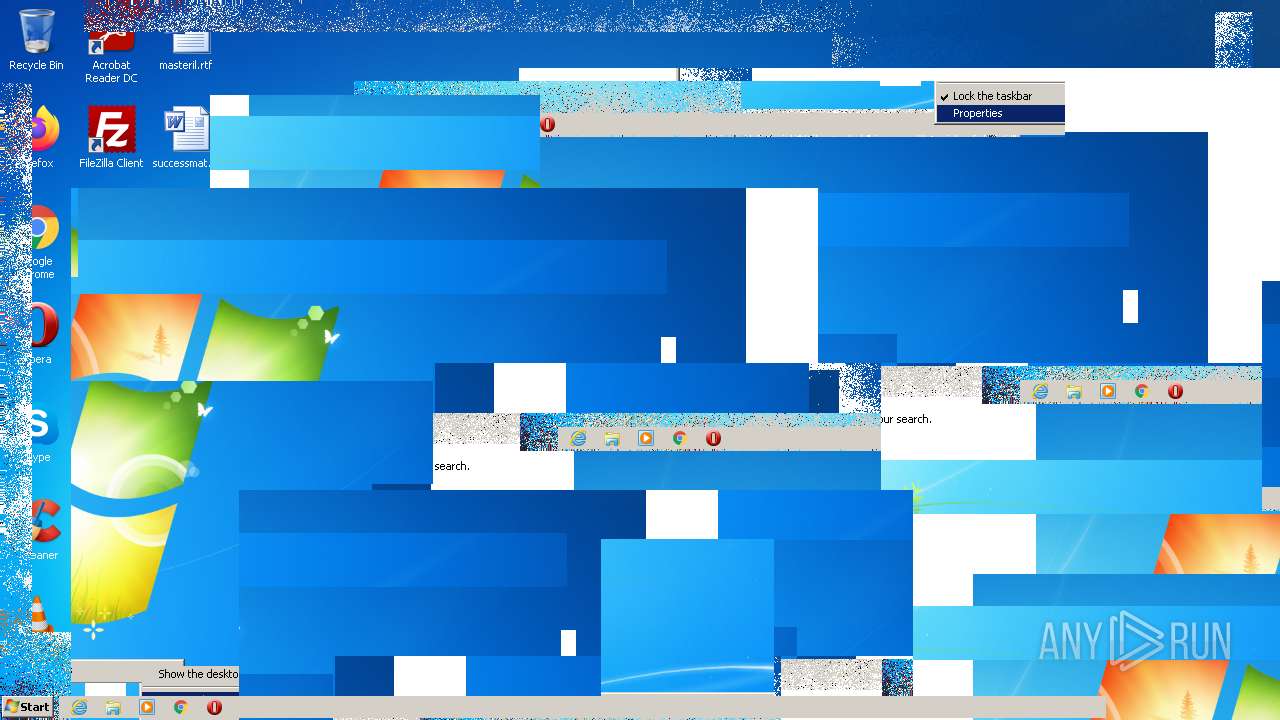
Disables the Run in Start menu
- LogonFuck.exe (PID: 4036)
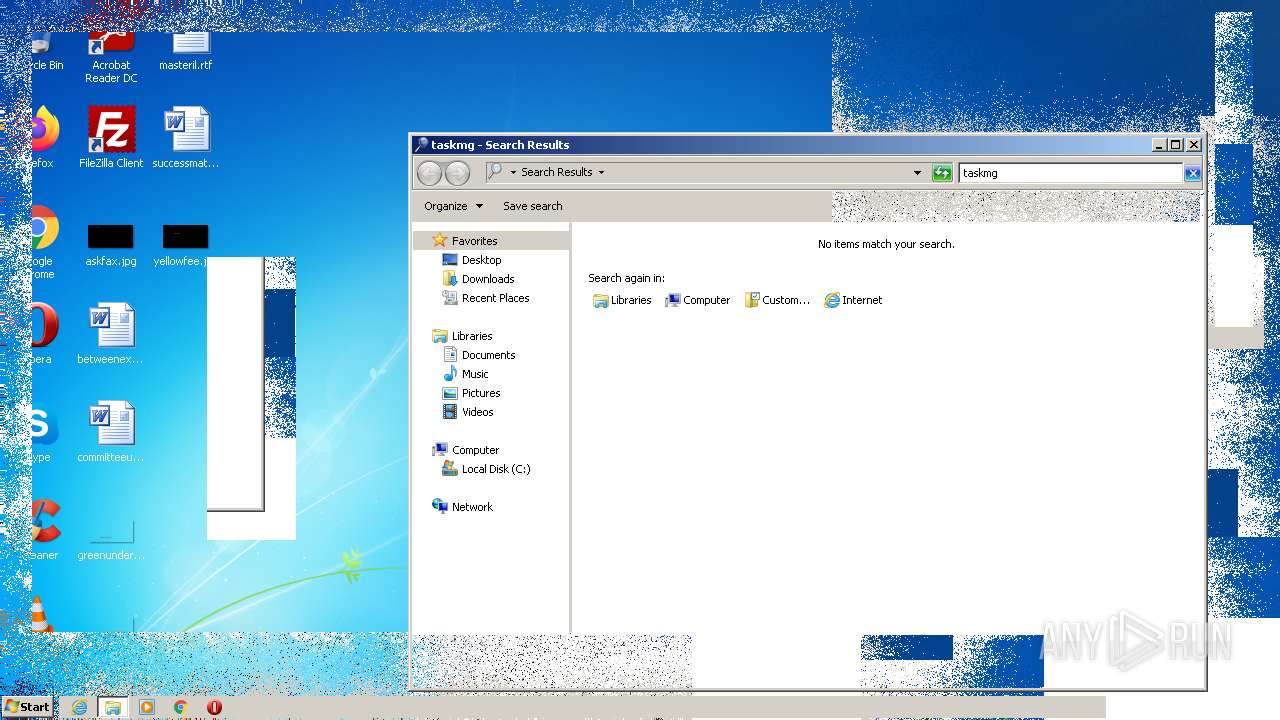
Task Manager has been disabled (taskmgr)
- LogonFuck.exe (PID: 4036)
Disables the Command Prompt (cmd)
- LogonFuck.exe (PID: 4036)
Disables registry editing tools (regedit)
- LogonFuck.exe (PID: 4036)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 824)
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 1148)
- iexplore.exe (PID: 3248)
- iexplore.exe (PID: 3404)
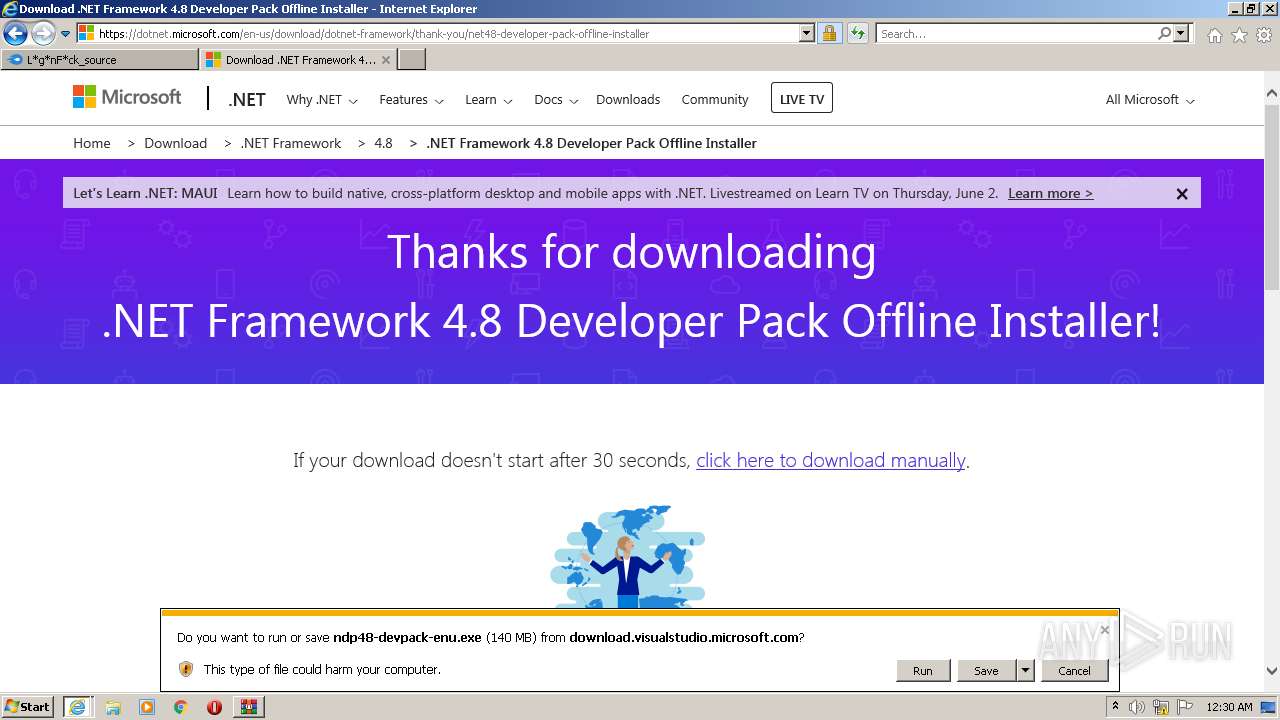
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2724)
- iexplore.exe (PID: 824)
- LogonFuck.exe (PID: 4036)
Checks supported languages
- WinRAR.exe (PID: 2724)
- LogonFuck.exe (PID: 2912)
- LogonFuck.exe (PID: 4036)
Reads the computer name
- WinRAR.exe (PID: 2724)
- LogonFuck.exe (PID: 4036)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2724)
- iexplore.exe (PID: 824)
- LogonFuck.exe (PID: 4036)
Reads Environment values
- LogonFuck.exe (PID: 4036)
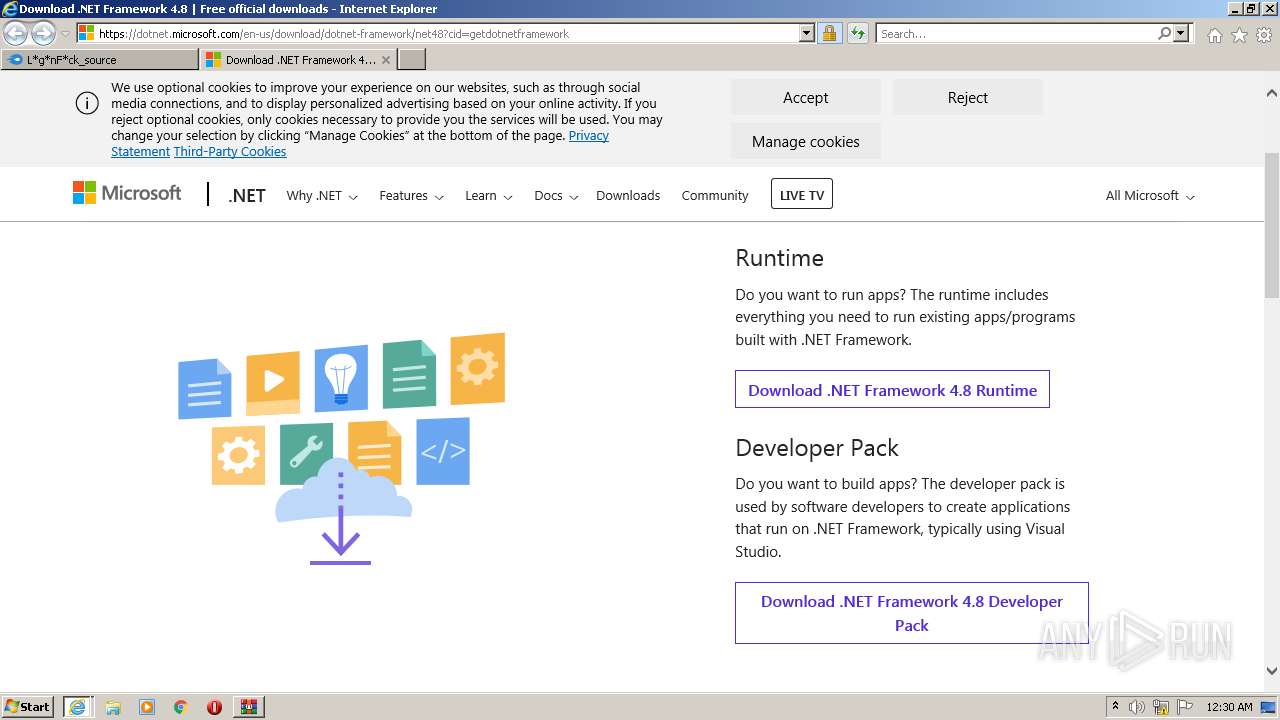
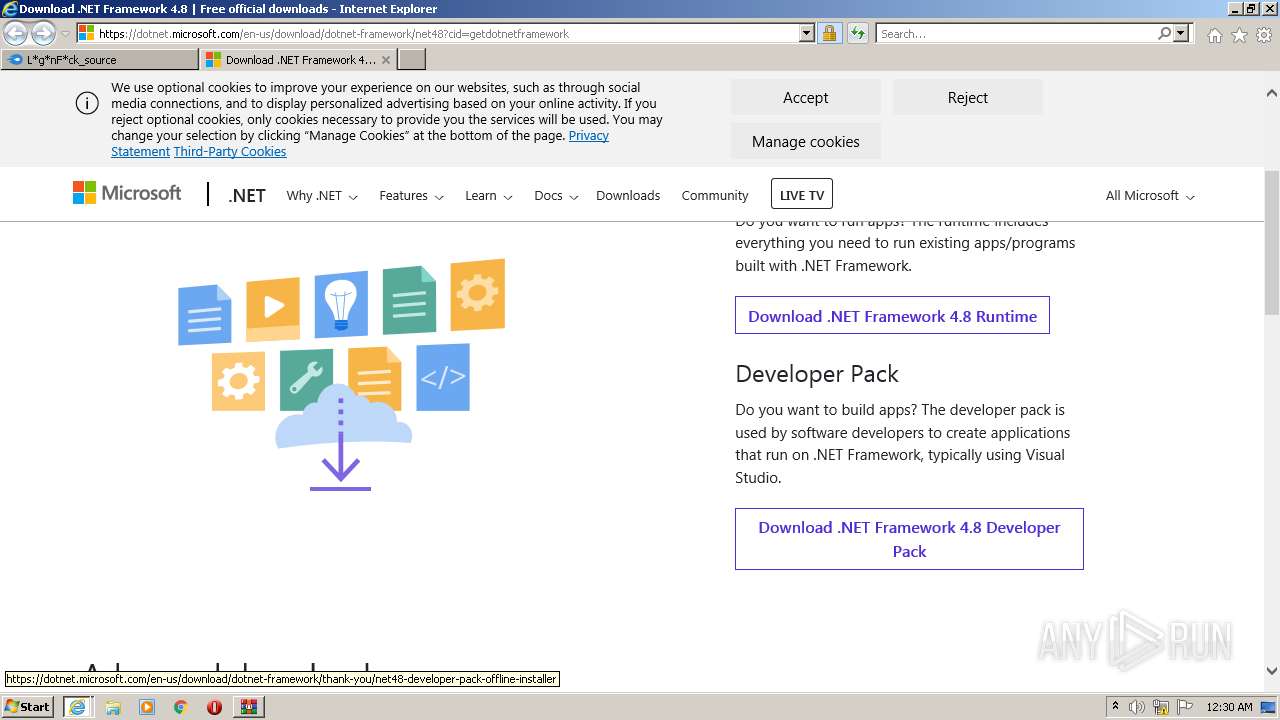
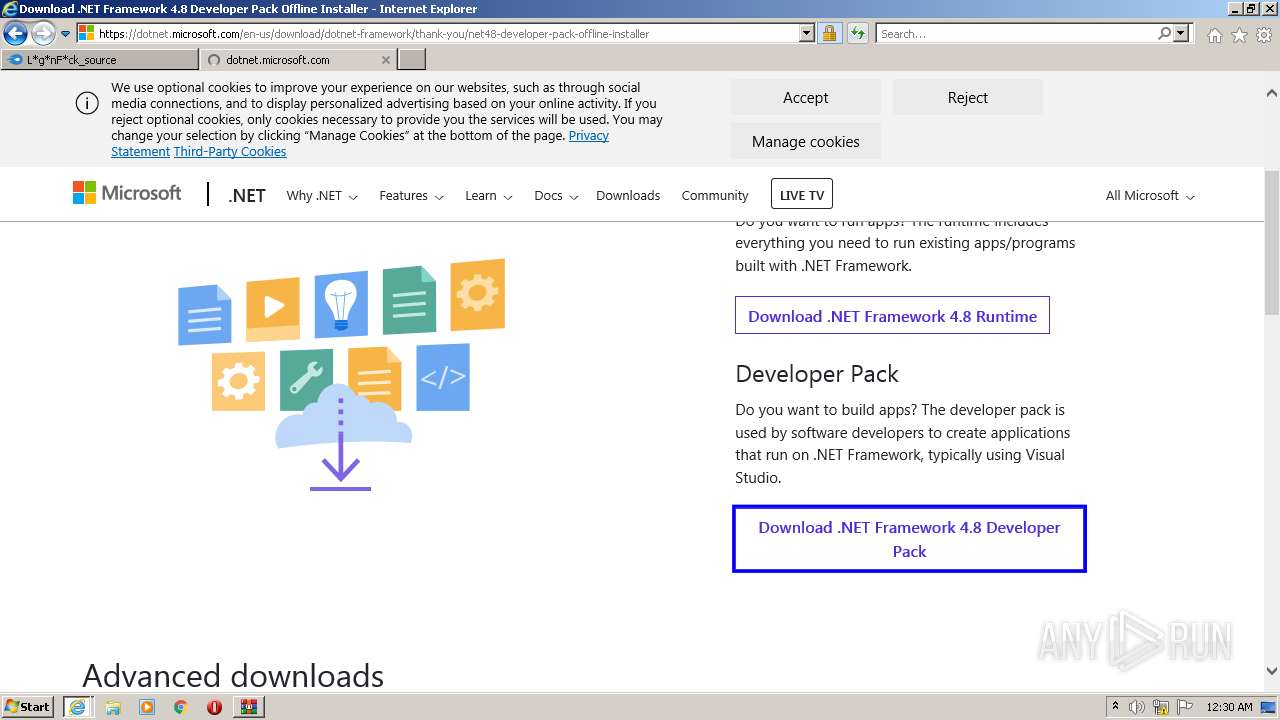
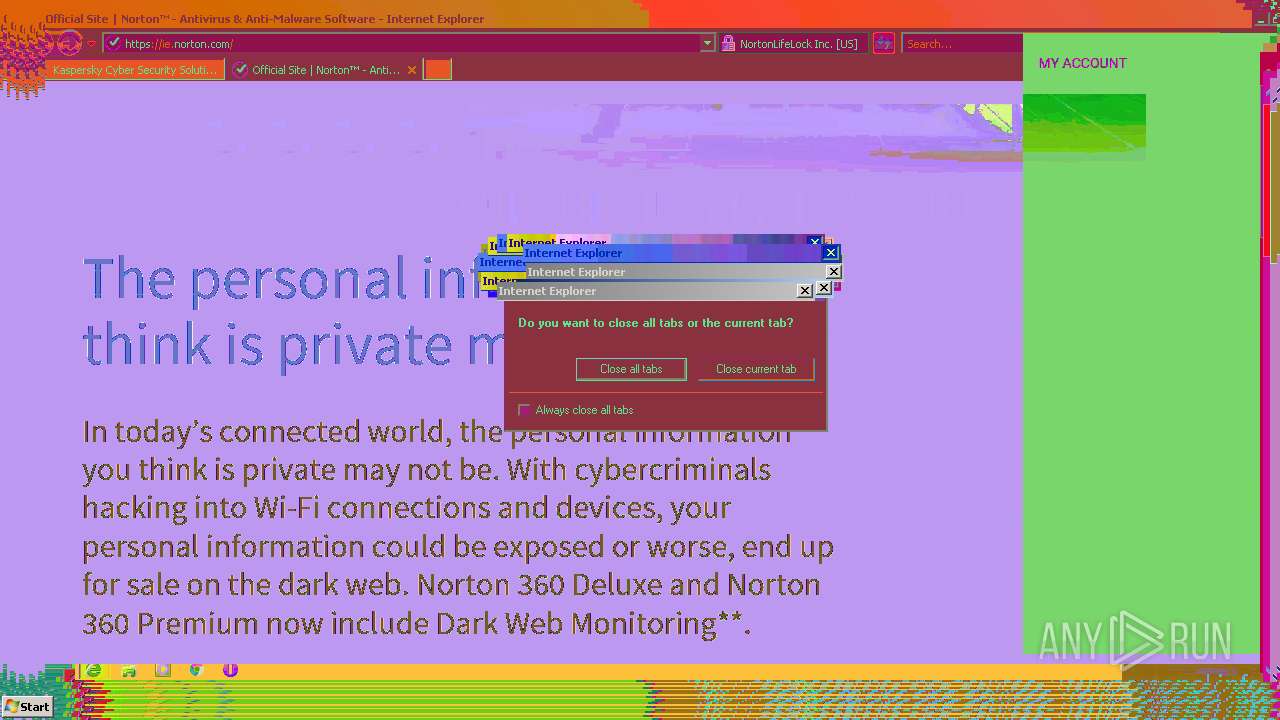
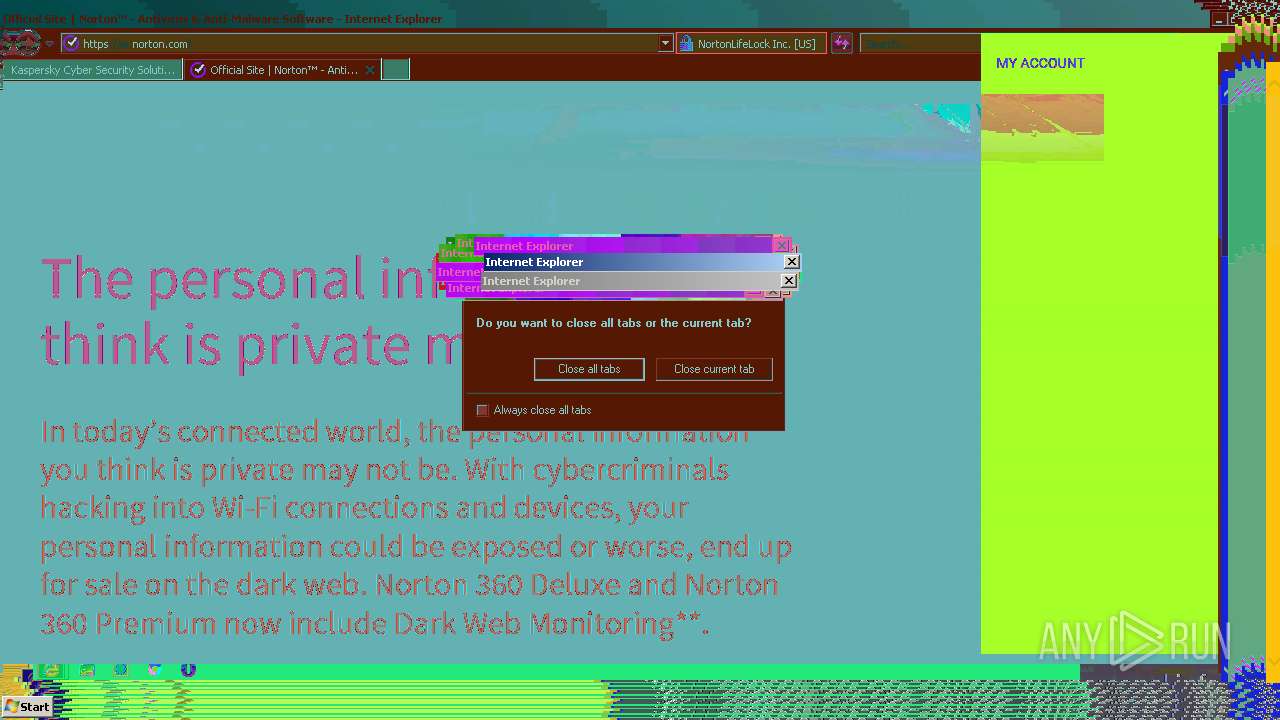
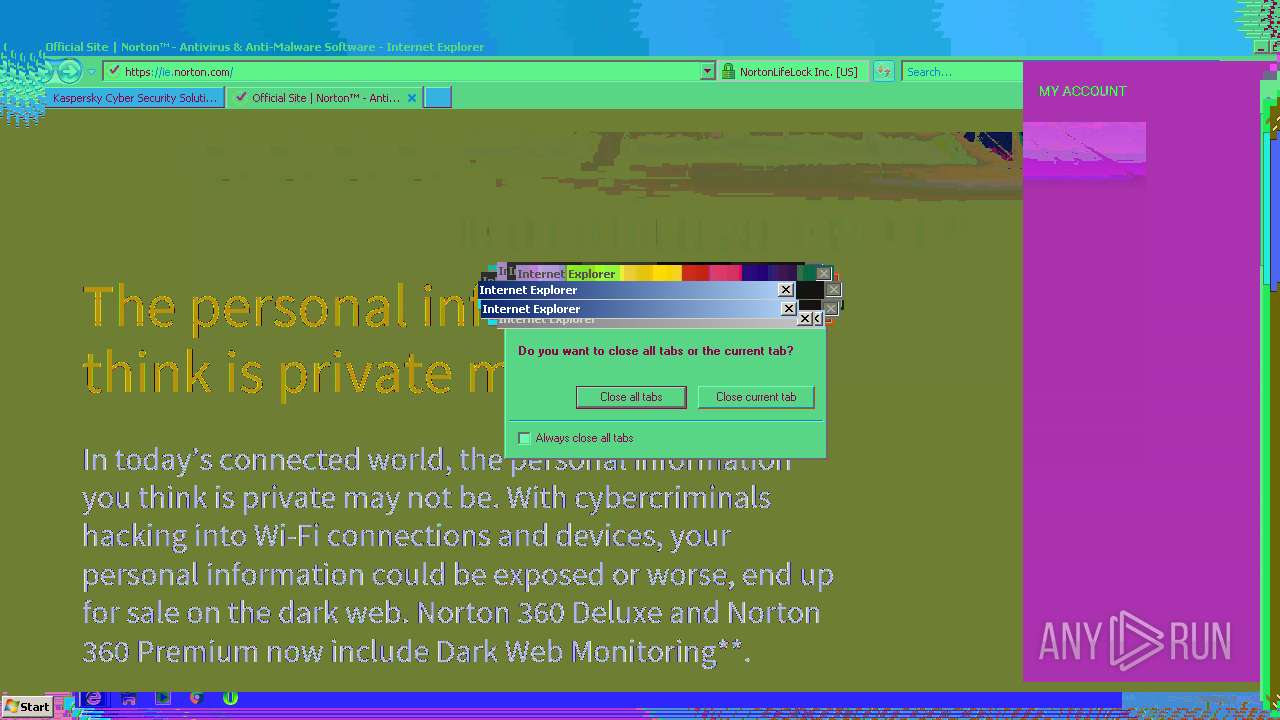
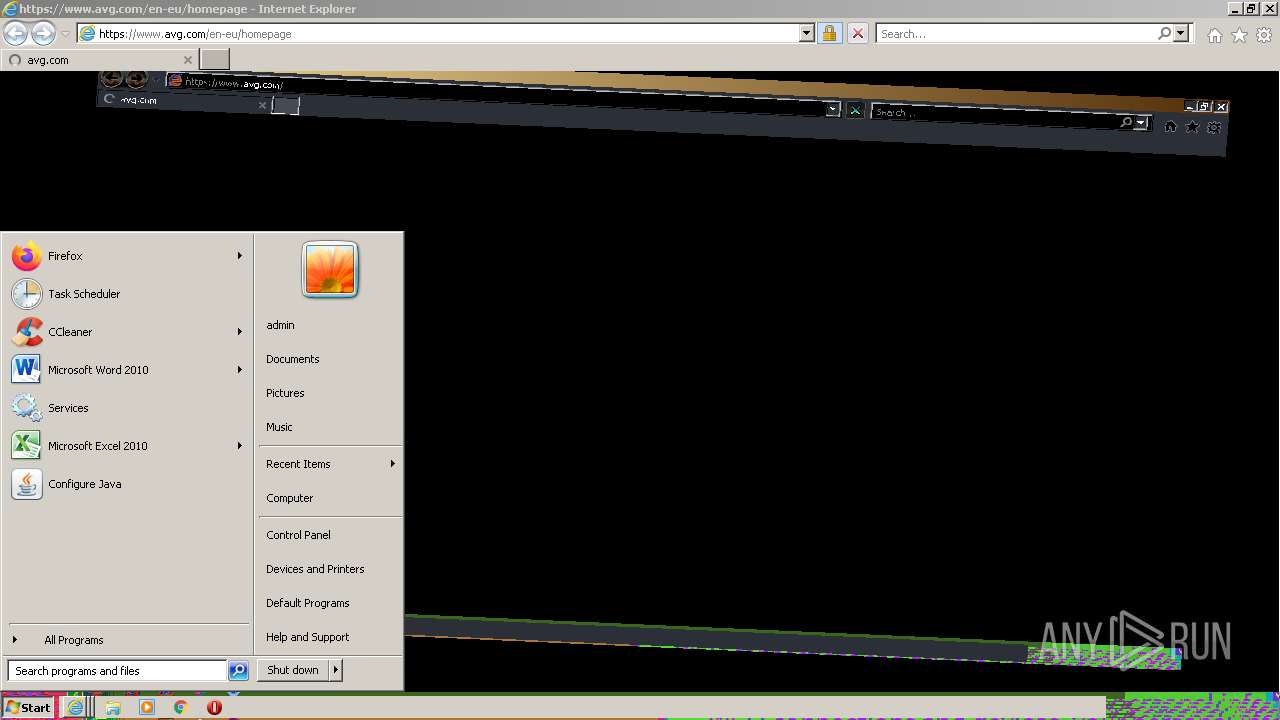
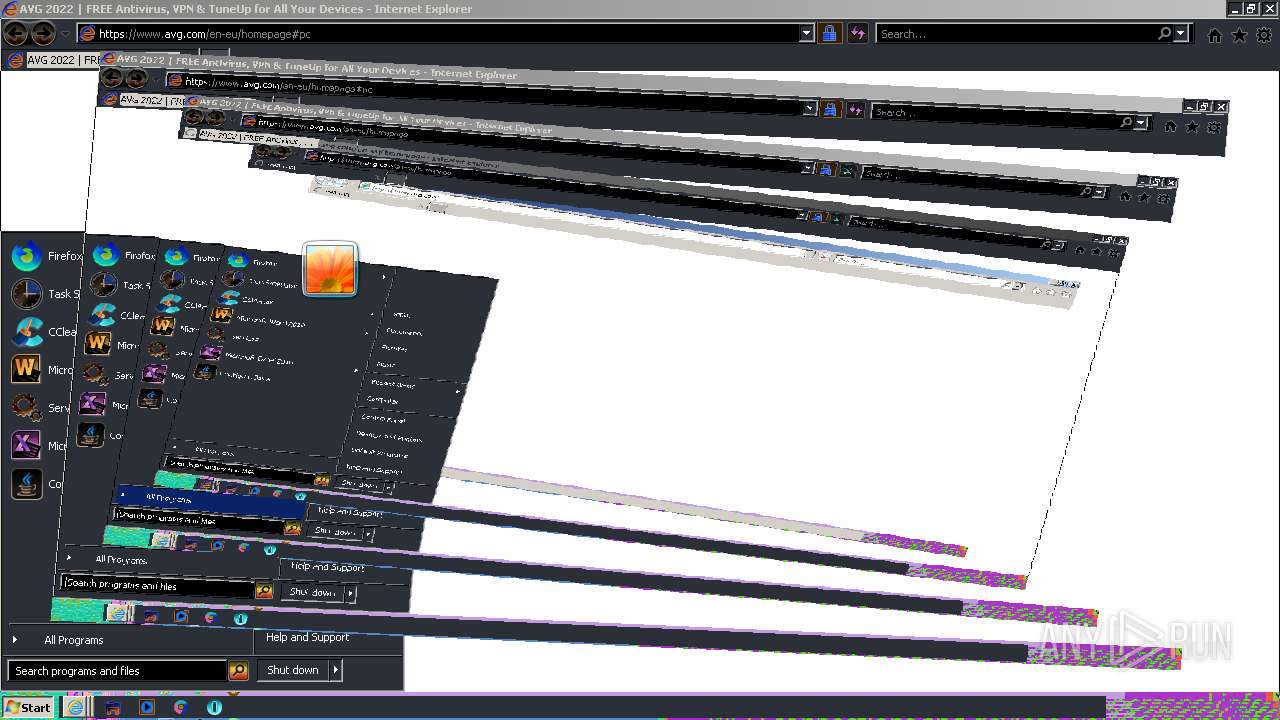
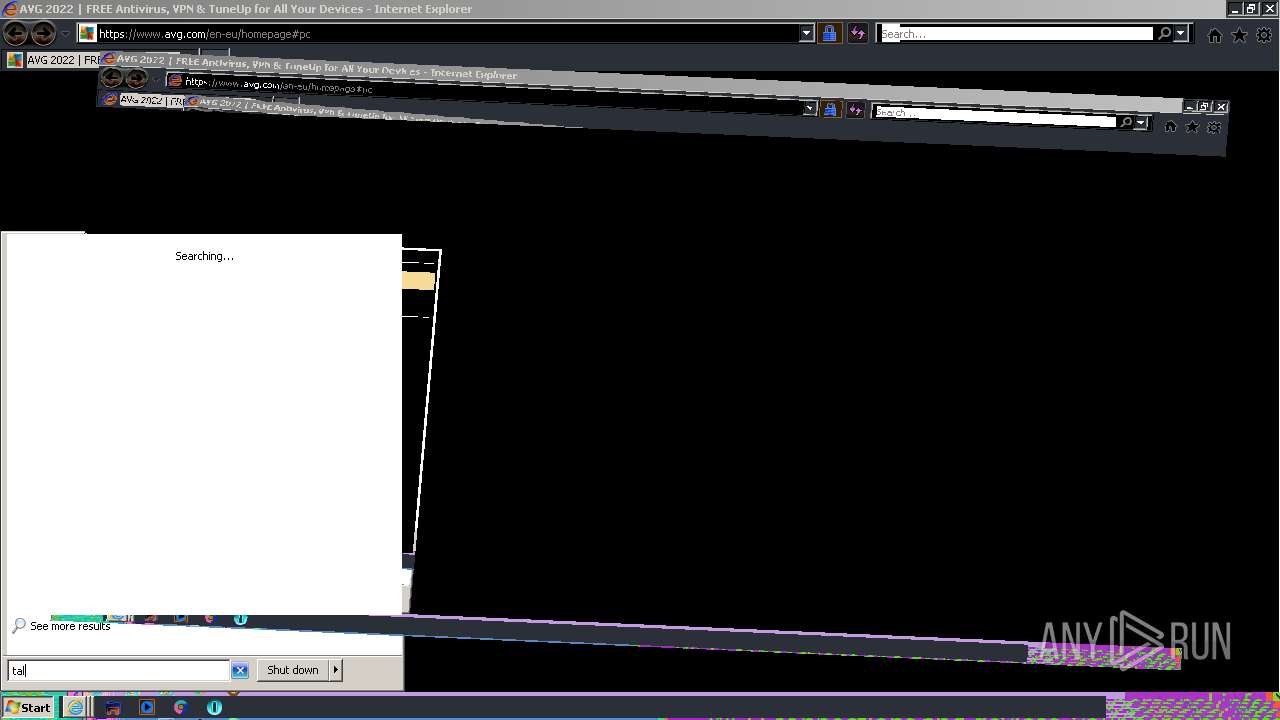
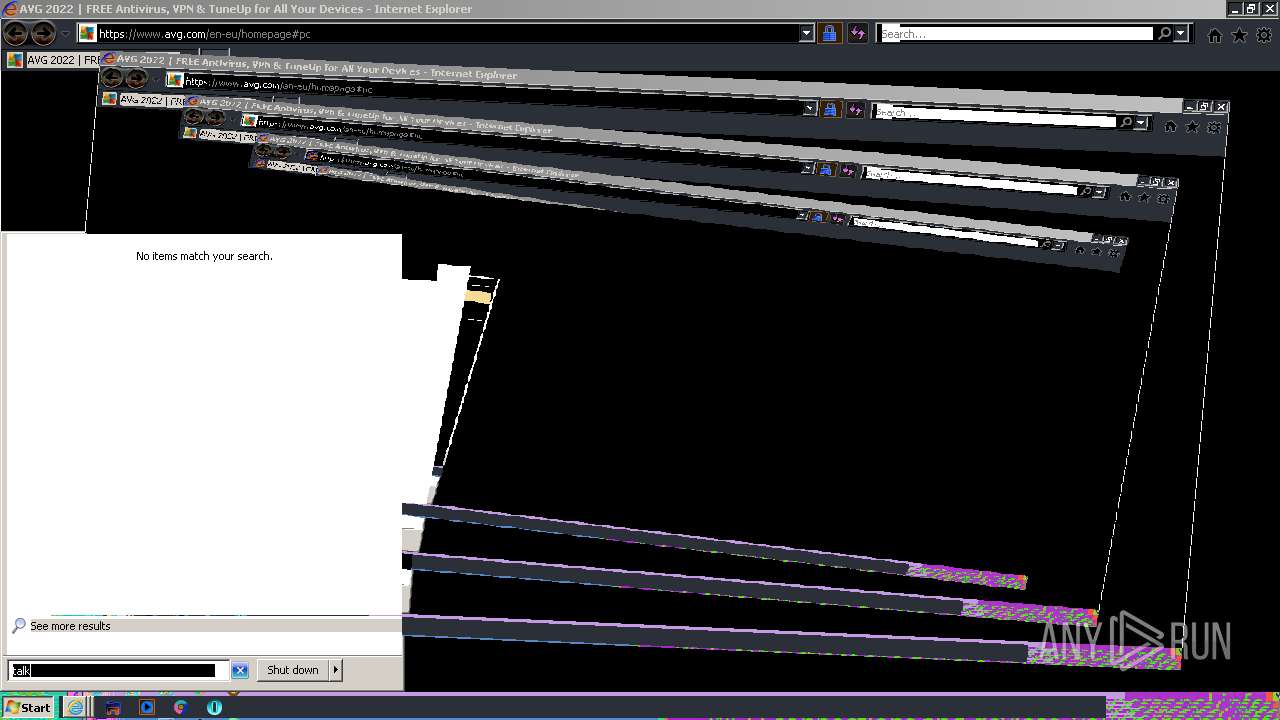
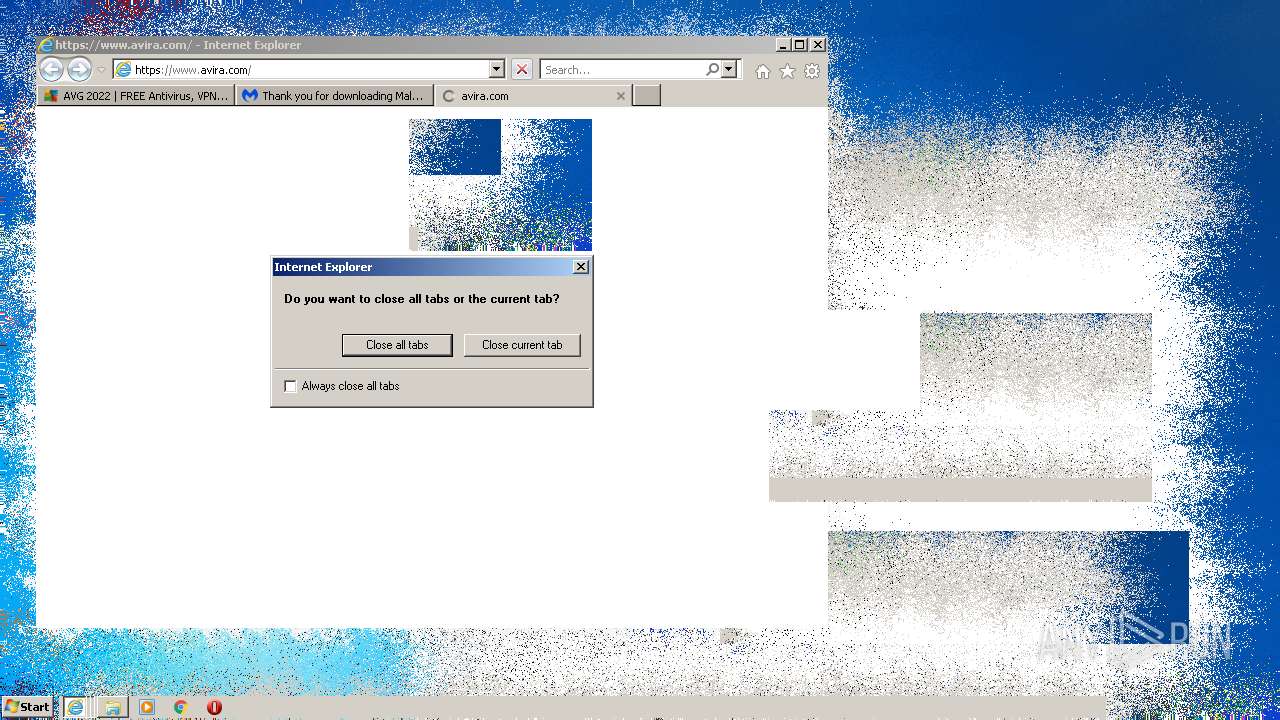
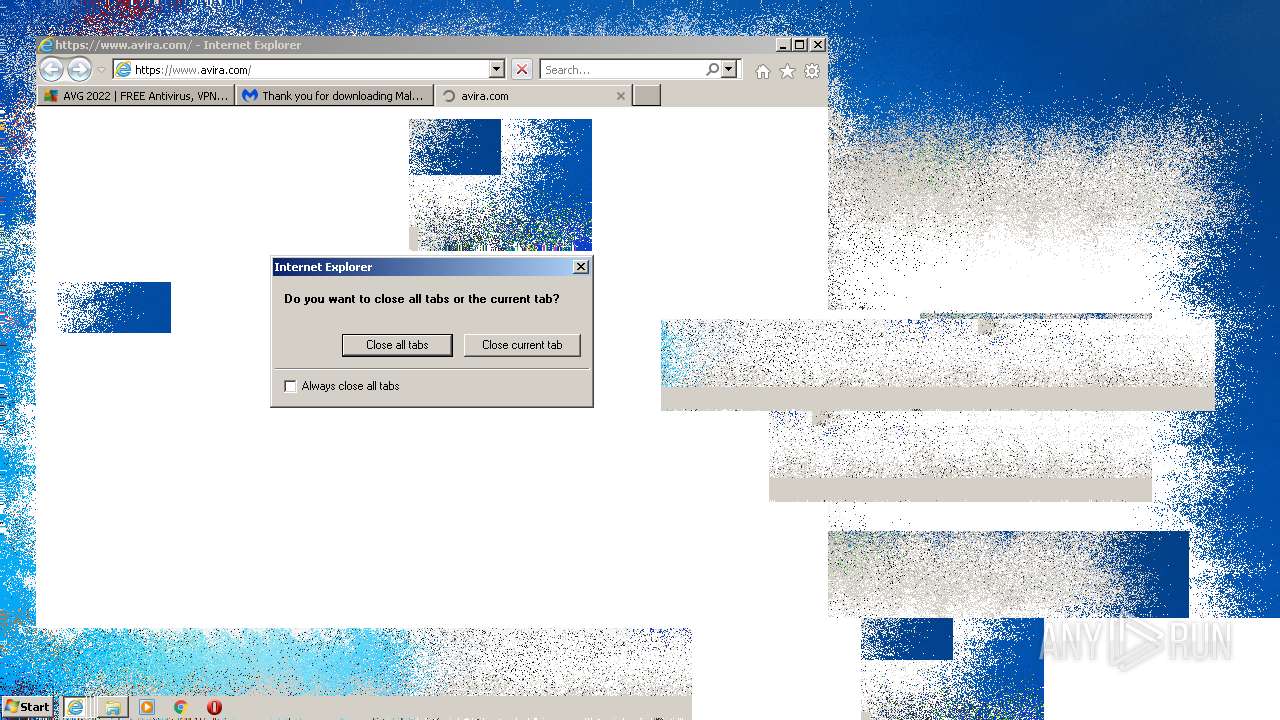
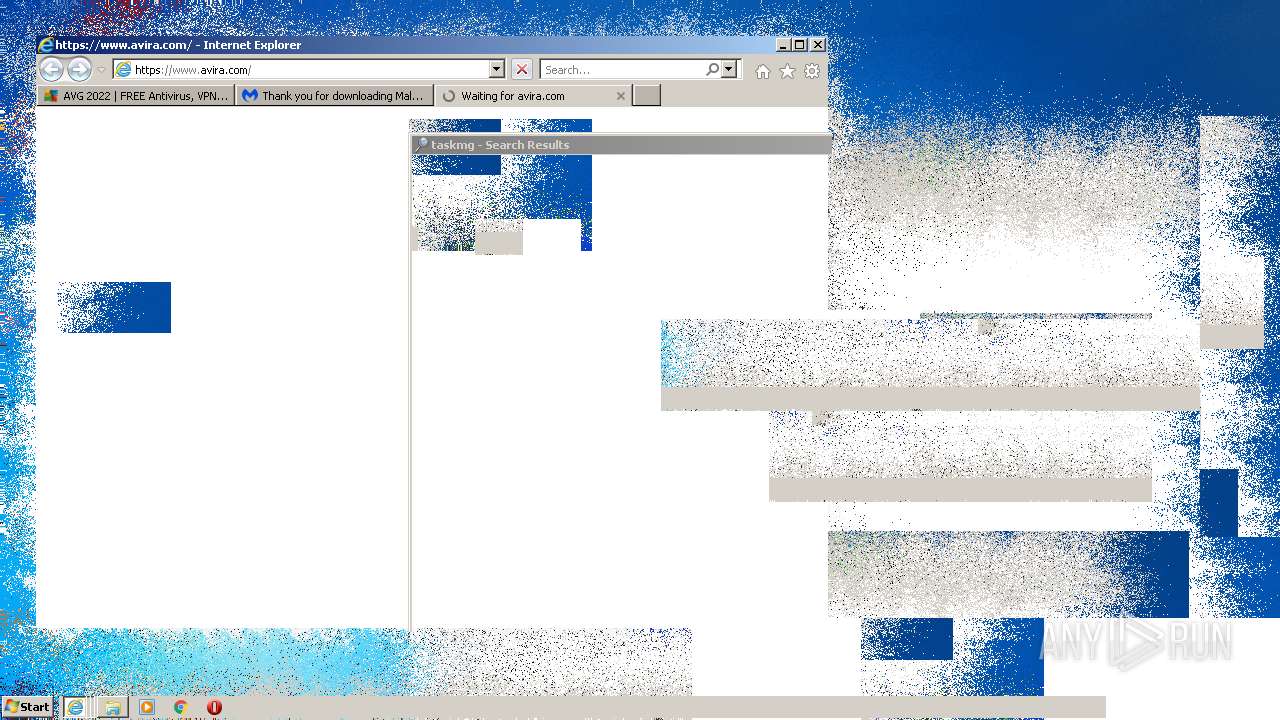
Starts Internet Explorer
- LogonFuck.exe (PID: 4036)
Reads the time zone
- iexplore.exe (PID: 3404)
INFO
Application launched itself
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 900)
- iexplore.exe (PID: 2260)
- iexplore.exe (PID: 3144)
Checks supported languages
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 824)
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 900)
- takeown.exe (PID: 2336)
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 1360)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 1148)
- iexplore.exe (PID: 2260)
- iexplore.exe (PID: 3248)
- iexplore.exe (PID: 3404)
- iexplore.exe (PID: 3144)
Checks Windows Trust Settings
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 824)
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 3248)
- iexplore.exe (PID: 1148)
- iexplore.exe (PID: 3404)
Changes internet zones settings
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 900)
- iexplore.exe (PID: 2260)
- iexplore.exe (PID: 3144)
Creates files in the user directory
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 824)
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 1148)
- iexplore.exe (PID: 900)
- iexplore.exe (PID: 3248)
- iexplore.exe (PID: 3404)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 1148)
Reads the computer name
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 824)
- iexplore.exe (PID: 900)
- iexplore.exe (PID: 2100)
- takeown.exe (PID: 2336)
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 1360)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 1148)
- iexplore.exe (PID: 2260)
- iexplore.exe (PID: 3248)
- iexplore.exe (PID: 3144)
- iexplore.exe (PID: 3404)
Reads settings of System Certificates
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 824)
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 1148)
- iexplore.exe (PID: 3248)
- iexplore.exe (PID: 3404)
Changes settings of System certificates
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 1148)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1976)
Reads internet explorer settings
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 824)
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 1148)
- iexplore.exe (PID: 3248)
- iexplore.exe (PID: 3404)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3404)
Reads the date of Windows installation
- iexplore.exe (PID: 900)
- iexplore.exe (PID: 2260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
19
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 824 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1976 CREDAT:1053988 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 4294967295 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 900 | "C:\Program Files\Internet Explorer\iexplore.exe" https://kaspersky.com/ | C:\Program Files\Internet Explorer\iexplore.exe | — | LogonFuck.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:900 CREDAT:734246 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.avg.com/ | C:\Program Files\Internet Explorer\iexplore.exe | — | LogonFuck.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.youtube.com/redirect?event=video_description&redir_token=QUFFLUhqa05jSmxTT3FlTENtNnJXN0RiazZkT2EyVVUtQXxBQ3Jtc0trd2hvN3M1UV9CdTFnMG05cEFDVHI4RnhUcHFLbDhBb2VDQ1g1ekd1MDd4SFE3cktlQVB6MlpvazlWWDB5cW5tZTNBQkktYlgtVU5lYWFBMUdXc2ZUT05Xemhlc3hhaE02TjI3cVlSQU0tNDZvX1FZcw&q=https%3A%2F%2Fwww.mediafire.com%2Ffile%2F2qykx0rzry3ycv7%2FL%252Ag%252AnF%252Ack_source.zip%2Ffile" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 4294967295 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:900 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1976 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 4294967295 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.mcafee.com/ | C:\Program Files\Internet Explorer\iexplore.exe | — | LogonFuck.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2336 | "C:\Windows\System32\takeown.exe" /f C:\Windows\System32\LogonUI.exe | C:\Windows\System32\takeown.exe | — | LogonFuck.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
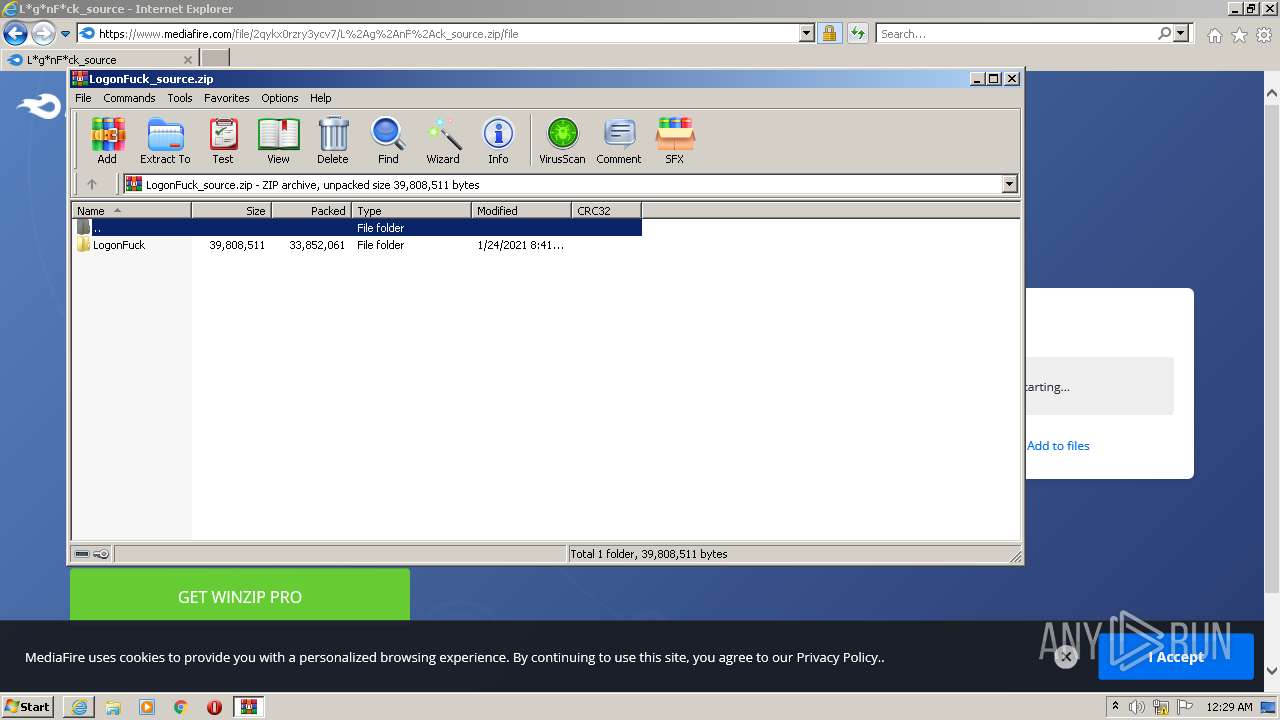
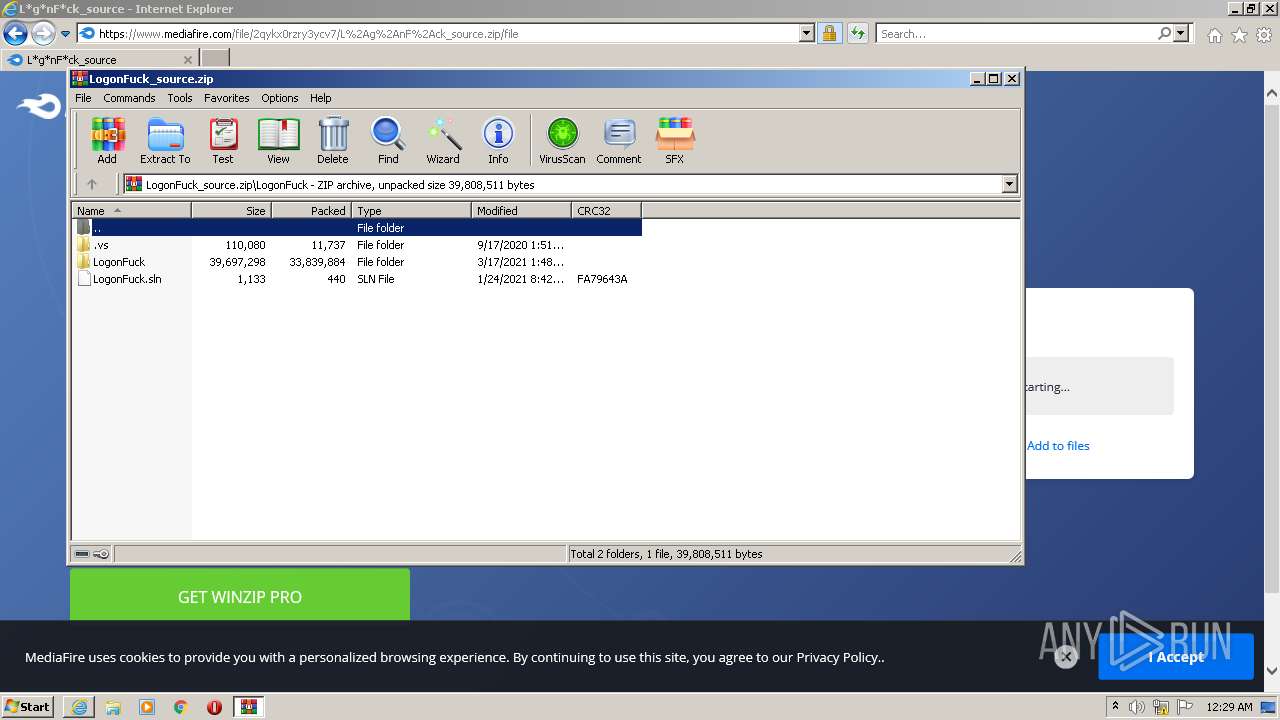
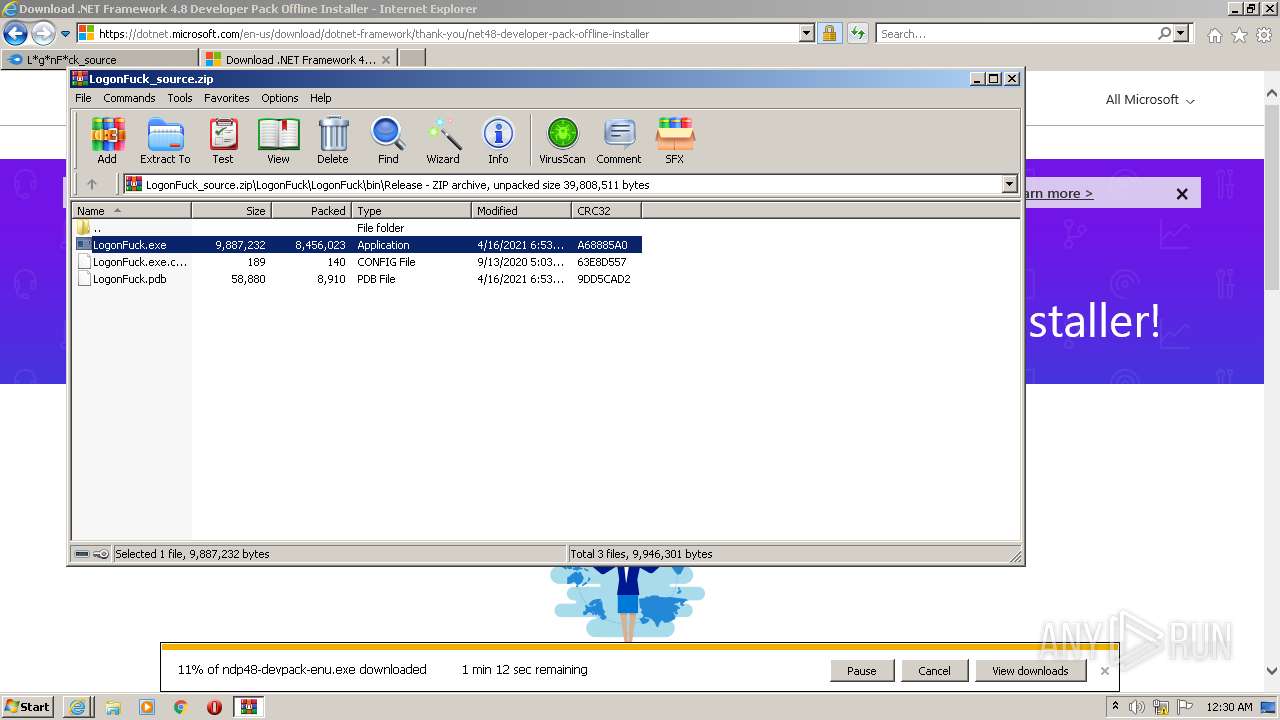
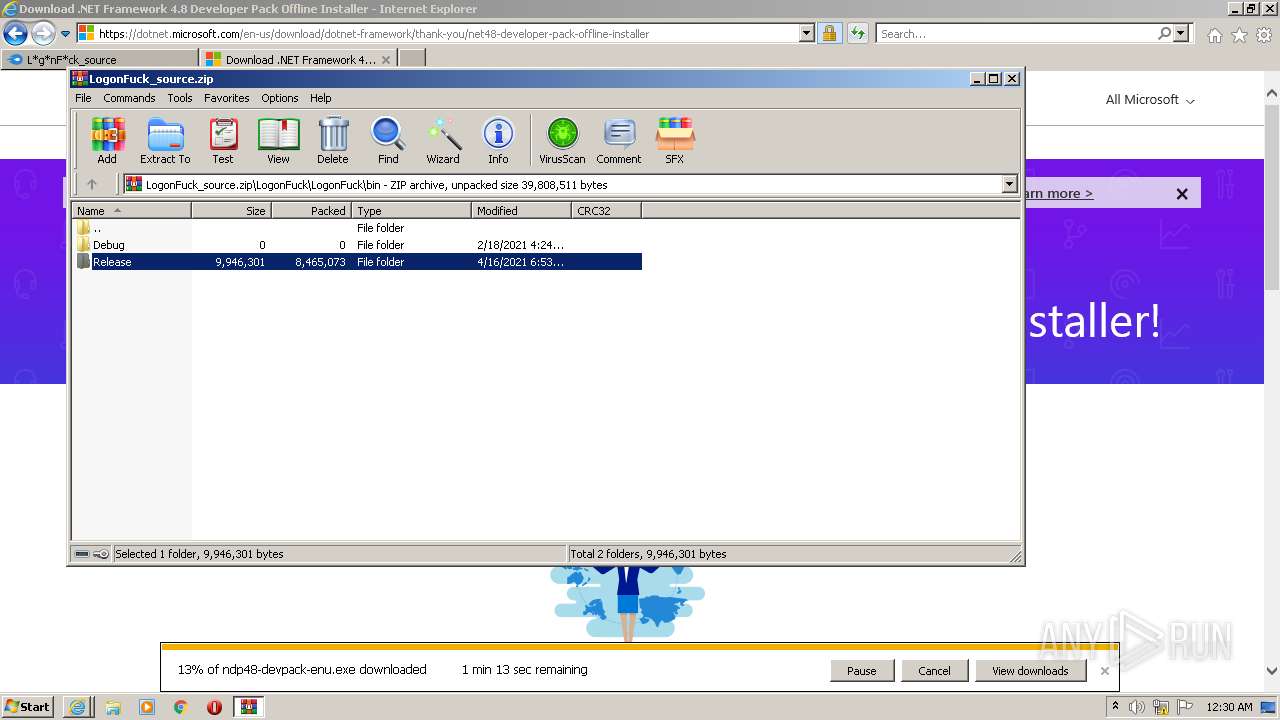
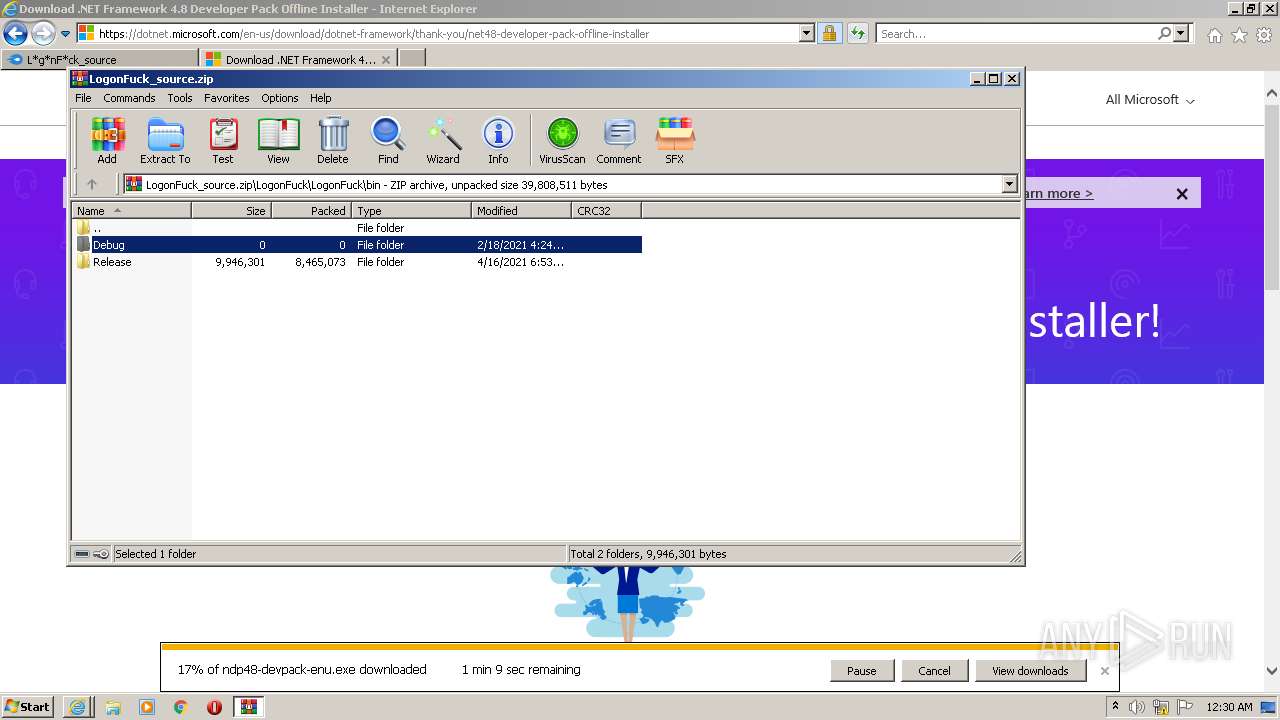
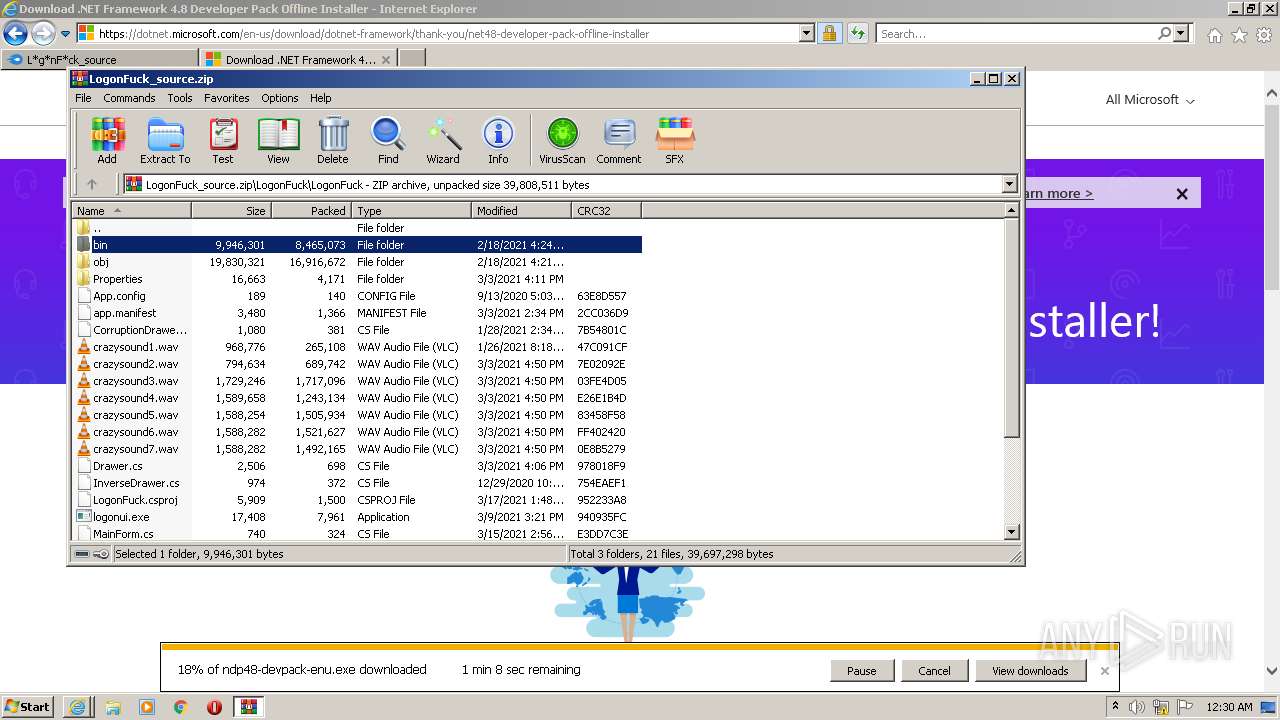
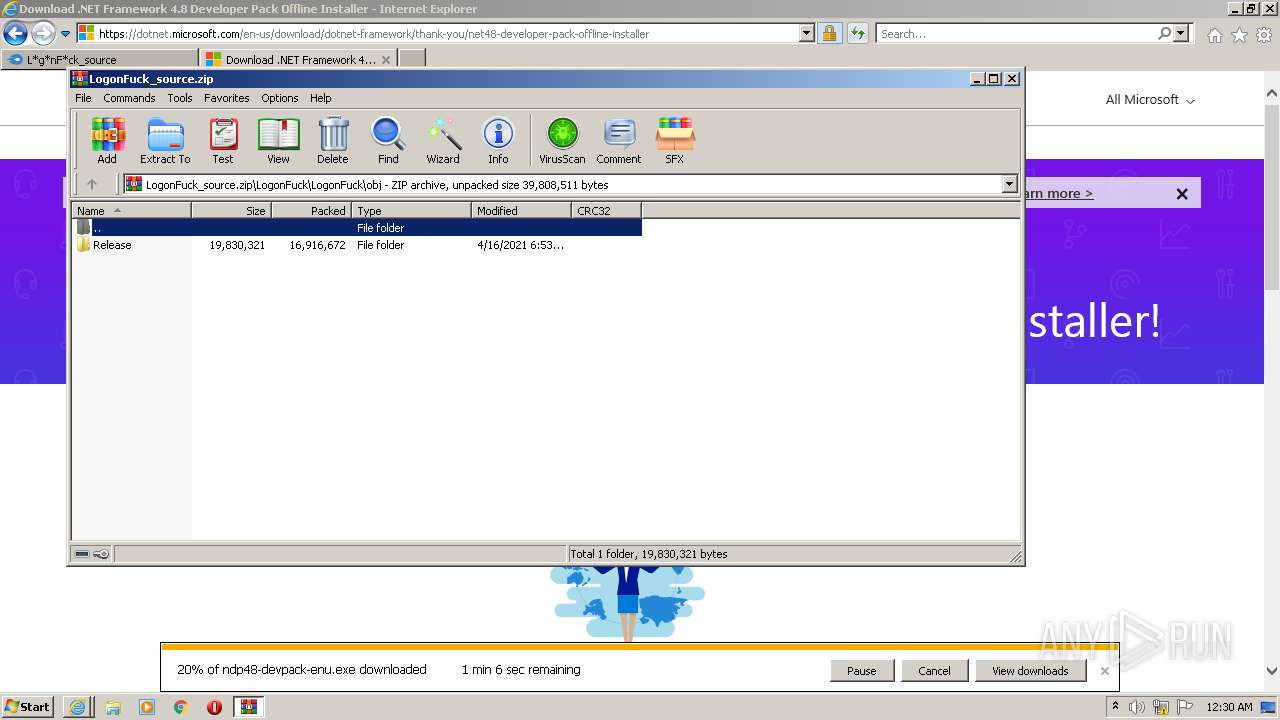
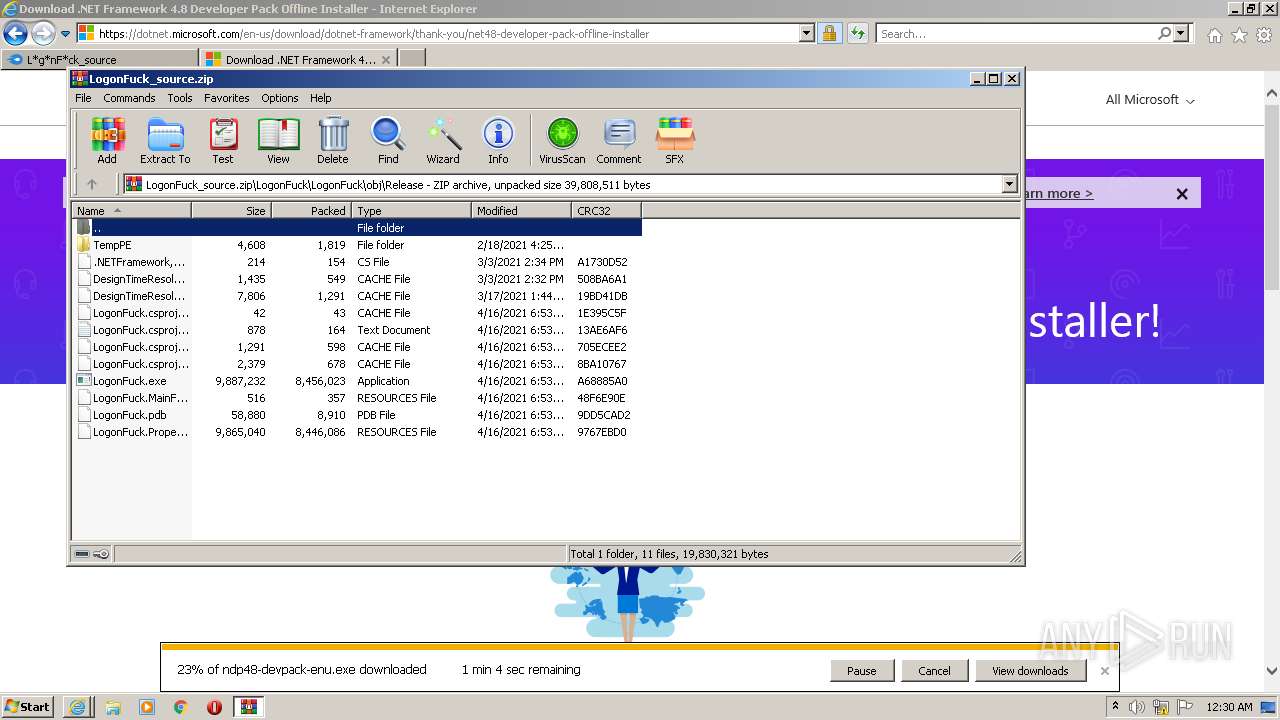
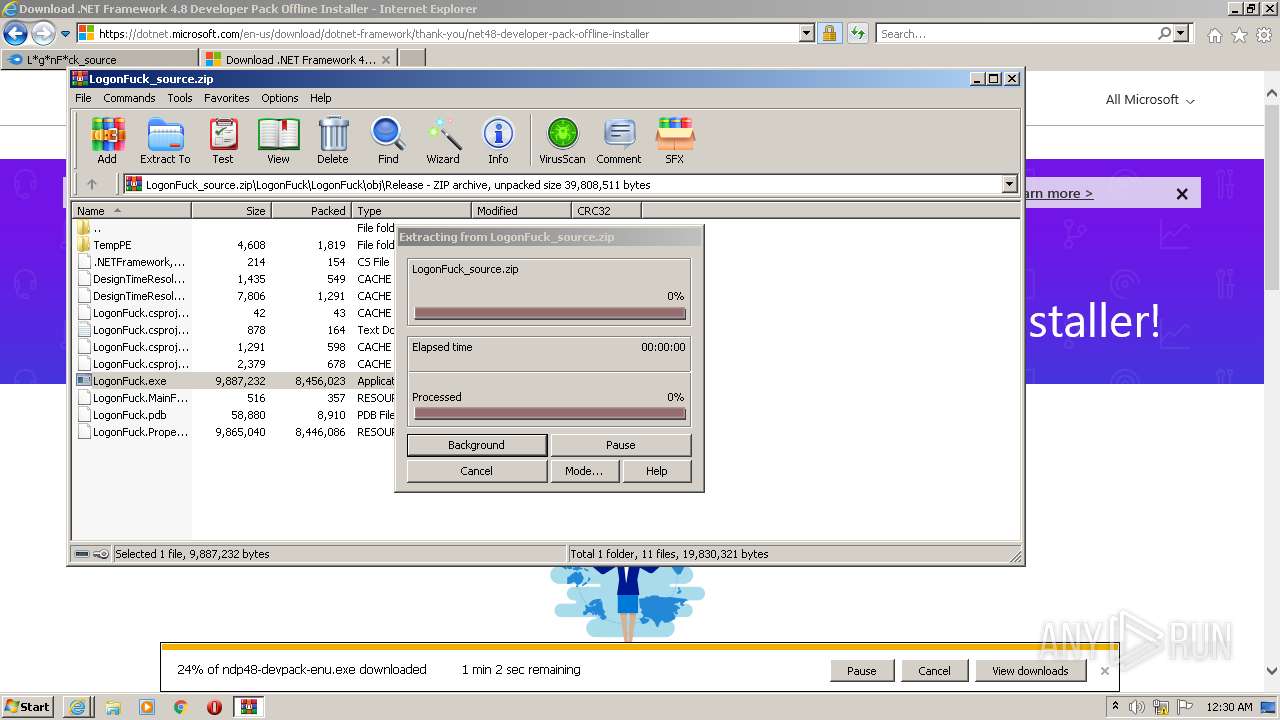
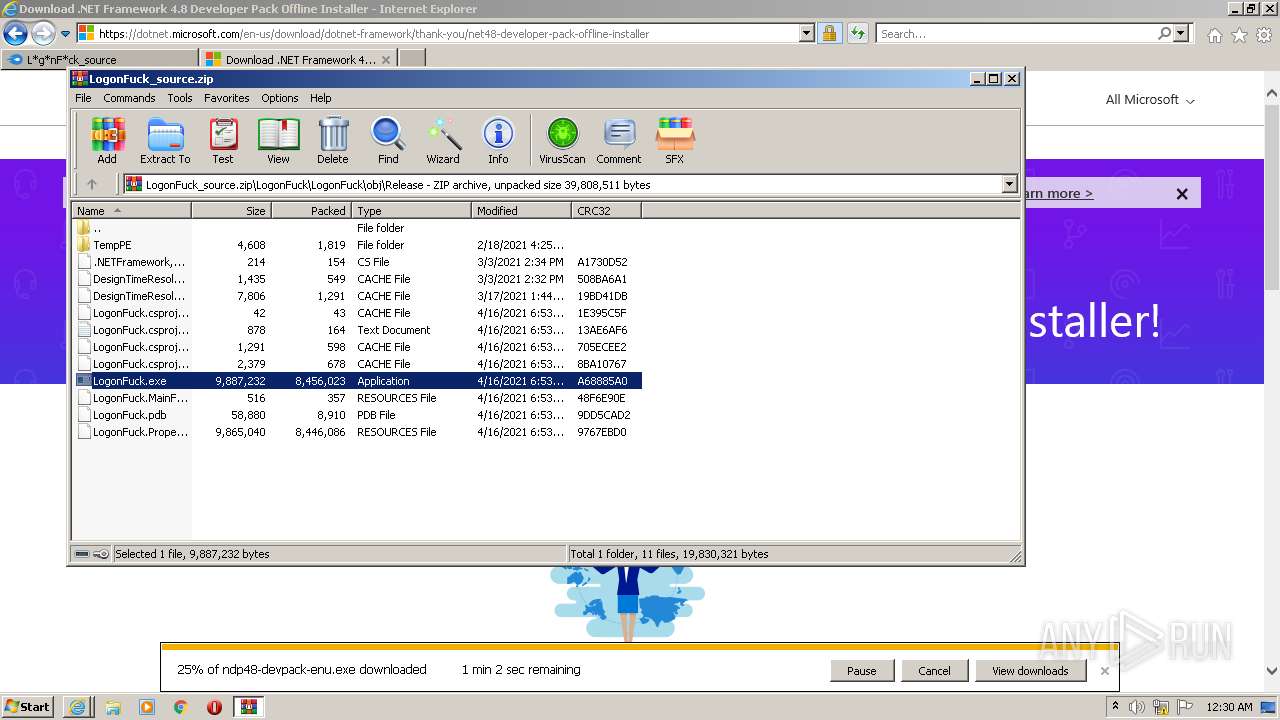
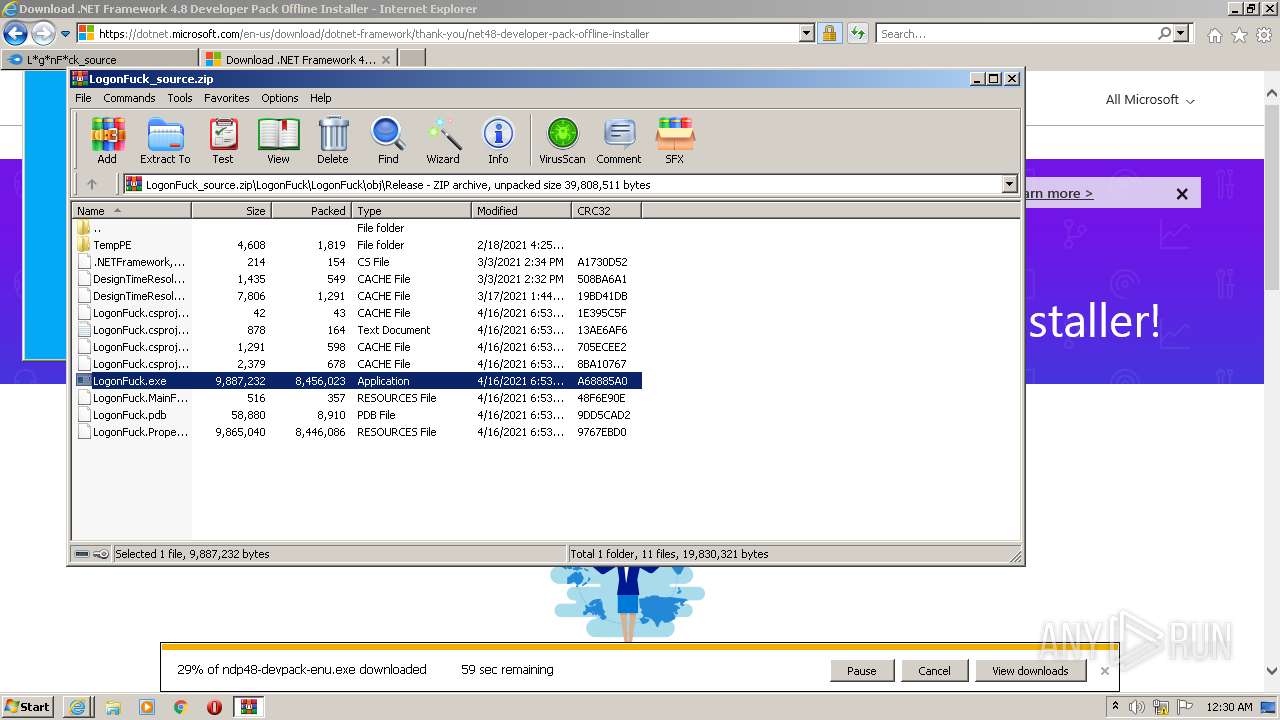
| 2724 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\LogonFuck_source.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 4294967295 Version: 5.91.0 Modules
| |||||||||||||||
Total events
99 329
Read events
98 237
Write events
1 079
Delete events
13
Modification events
| (PID) Process: | (1976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960801 | |||
| (PID) Process: | (1976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960801 | |||
| (PID) Process: | (1976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
10
Suspicious files
135
Text files
924
Unknown types
220
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F07644E38ED7C9F37D11EEC6D4335E02_7172467AE25B54F1B9D87A9343356E9B | binary | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\redirect[1].htm | html | |
MD5:— | SHA256:— | |||
| 1976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 1976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\265C0DEB29181DD1891051371C5F863A_7BD24FBCF7F89F33B2FA5E0C8CE277C8 | der | |
MD5:— | SHA256:— | |||
| 1976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
103
TCP/UDP connections
596
DNS requests
226
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2128 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDExSUZ712qmxLhqE9UUaDV | US | der | 472 b | whitelisted |
2128 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEG3aTvFLTYzNCmxS2fUJutw%3D | US | der | 471 b | whitelisted |
1976 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
2128 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2128 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
2128 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2128 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 727 b | whitelisted |
2128 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCHXS%2FWwGsOSRJbmAIB8NC3 | US | der | 472 b | whitelisted |
2128 | iexplore.exe | GET | 200 | 18.66.9.49:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2128 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2128 | iexplore.exe | 216.58.212.142:443 | www.youtube.com | Google Inc. | US | whitelisted |
1976 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1976 | iexplore.exe | 178.79.242.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | whitelisted |
1976 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2128 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2128 | iexplore.exe | 142.250.185.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1976 | iexplore.exe | 216.58.212.142:443 | www.youtube.com | Google Inc. | US | whitelisted |
2128 | iexplore.exe | 52.222.206.214:443 | cdn.amplitude.com | Amazon.com, Inc. | US | suspicious |
2128 | iexplore.exe | 104.16.202.237:443 | www.mediafire.com | Cloudflare Inc | US | unknown |
2128 | iexplore.exe | 104.19.215.37:443 | cdn.otnolatrnup.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
www.mediafire.com |
| shared |
ocsp.comodoca.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2100 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2100 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2100 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2100 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2100 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2100 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3496 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3496 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3496 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3496 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2 ETPRO signatures available at the full report