| File name: | a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin |
| Full analysis: | https://app.any.run/tasks/aa856783-68cd-41fe-9a12-d3c8627a1ecf |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 04:25:38 |
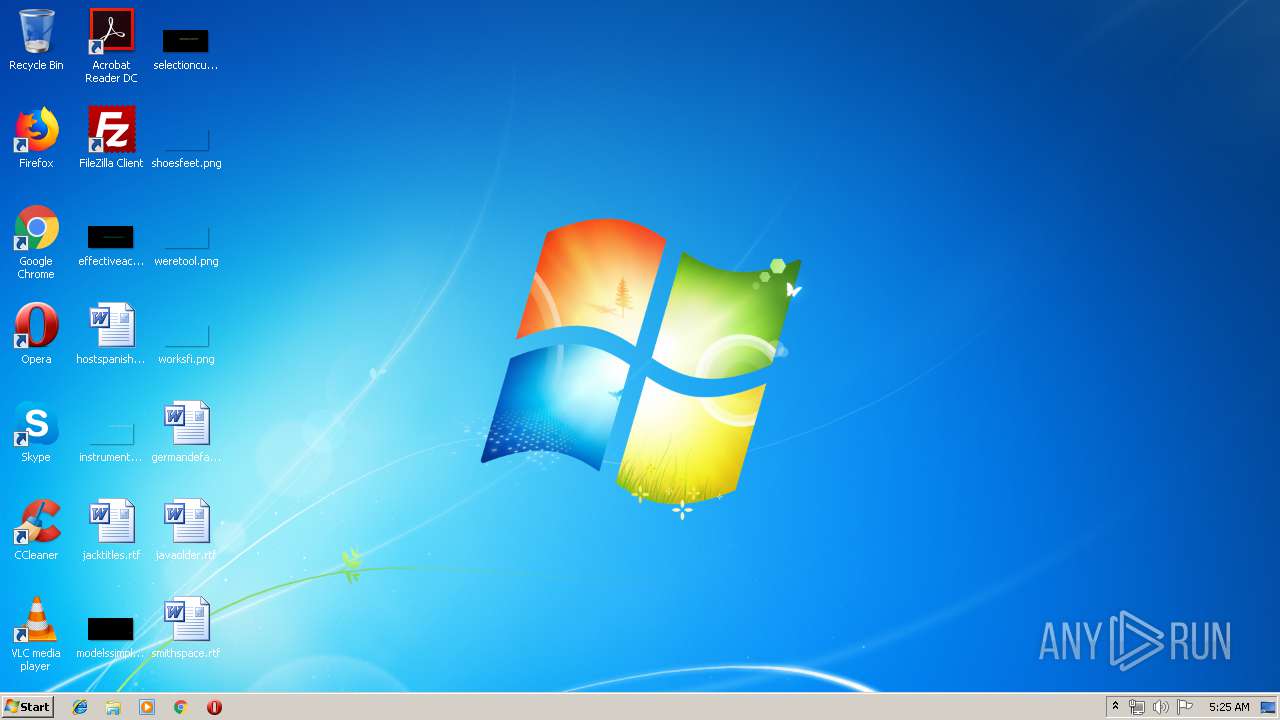
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | A04EB443870896FBE9A0B6468C4844F7 |
| SHA1: | E3001EF25B1386763CAEC9B5339EC6DDB0275A71 |
| SHA256: | A867DEB1578088D066941C40E598E4523AB5FD6C3327D3AFB951073BEE59FB02 |
| SSDEEP: | 6144:JrazEX0203RegvjxnpGhu3BJMIp2CuvY63:B+3JpGEBJMg2CuvY6 |
MALICIOUS
Deletes shadow copies
- cmd.exe (PID: 3264)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 3264)
SUSPICIOUS
Starts CMD.EXE for commands execution
- a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe (PID: 2956)
Creates files in the user directory
- a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe (PID: 2956)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:01 18:55:49+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 193536 |
| InitializedDataSize: | 23552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cc94 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Mar-2019 17:55:49 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Mar-2019 17:55:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002F298 | 0x0002F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65309 |
.data | 0x00031000 | 0x000059EA | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.35317 |
.rsrc | 0x00037000 | 0x000001F8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.84518 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89724 | 405 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
COMCTL32.dll |
KERNEL32.dll |
ole32.dll |
Total processes
50
Monitored processes
18
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 860 | vssadmin resize shadowstorage /for=f: /on=f: /maxsize=unbounded | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1352 | vssadmin resize shadowstorage /for=c: /on=c: /maxsize=unbounded | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1864 | vssadmin resize shadowstorage /for=h: /on=h: /maxsize=unbounded | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | vssadmin resize shadowstorage /for=d: /on=d: /maxsize=unbounded | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2276 | vssadmin resize shadowstorage /for=h: /on=h: /maxsize=401MB | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2484 | bcdedit /set {default} recoveryenabled No | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot Configuration Data Editor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2488 | vssadmin resize shadowstorage /for=d: /on=d: /maxsize=401MB | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2608 | vssadmin resize shadowstorage /for=e: /on=e: /maxsize=unbounded | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2936 | vssadmin resize shadowstorage /for=c: /on=c: /maxsize=401MB | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\Temp\a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe" | C:\Users\admin\AppData\Local\Temp\a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
356
Read events
352
Write events
4
Delete events
0
Modification events
| (PID) Process: | (2956) a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2956) a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
110
Text files
23
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp.CIop | binary | |
MD5:— | SHA256:— | |||
| 2956 | a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | C:\Users\admin\Contacts\admin.contact.CIop | binary | |
MD5:— | SHA256:— | |||
| 2956 | a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | binary | |
MD5:— | SHA256:— | |||
| 2956 | a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | C:\Users\admin\Documents\easilya.rtf.CIop | binary | |
MD5:— | SHA256:— | |||
| 2956 | a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | C:\Users\admin\Documents\clearfeedback.rtf.CIop | binary | |
MD5:— | SHA256:— | |||
| 2956 | a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | C:\Users\admin\Documents\friendsside.rtf.CIop | binary | |
MD5:— | SHA256:— | |||
| 2956 | a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | C:\Users\admin\Documents\pagesix.rtf.CIop | binary | |
MD5:— | SHA256:— | |||
| 2956 | a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | C:\Users\admin\.oracle_jre_usage\CIopReadMe.txt | text | |
MD5:E04A195C34B605286FBF1B6E3AE48EA8 | SHA256:D686127553BC8F72D8441AD441AFA795FDE914550FDB9FAD46889E8FE1019ED7 | |||
| 2956 | a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | C:\Users\admin\Documents\OneNote Notebooks\Personal\Unfiled Notes.one.CIop | binary | |
MD5:— | SHA256:— | |||
| 2956 | a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02.bin.exe | C:\Users\admin\Documents\CIopReadMe.txt | text | |
MD5:E04A195C34B605286FBF1B6E3AE48EA8 | SHA256:D686127553BC8F72D8441AD441AFA795FDE914550FDB9FAD46889E8FE1019ED7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report