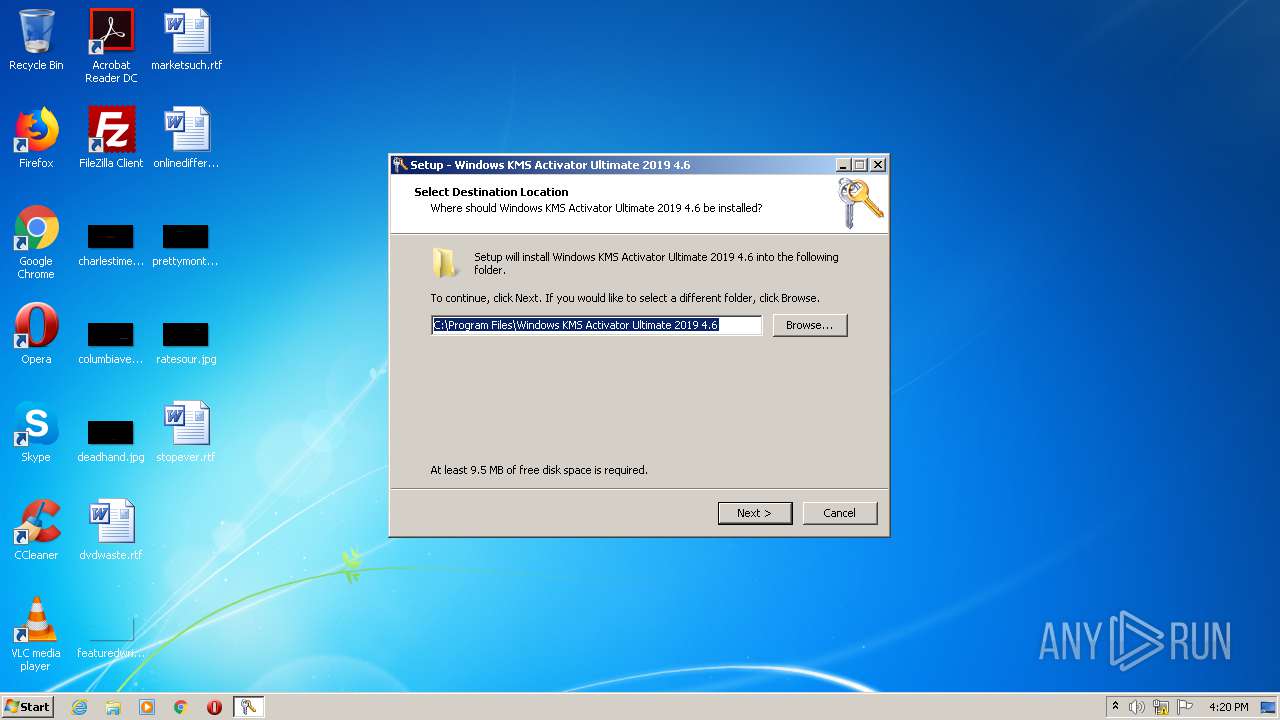
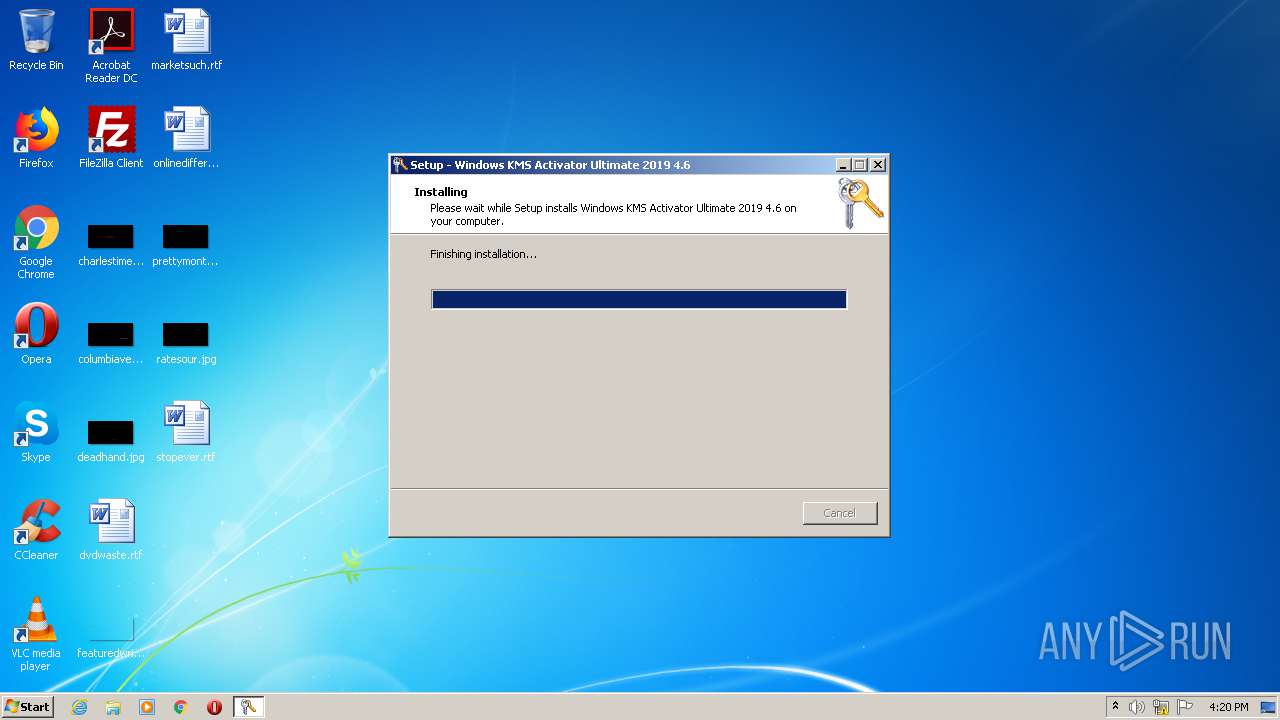
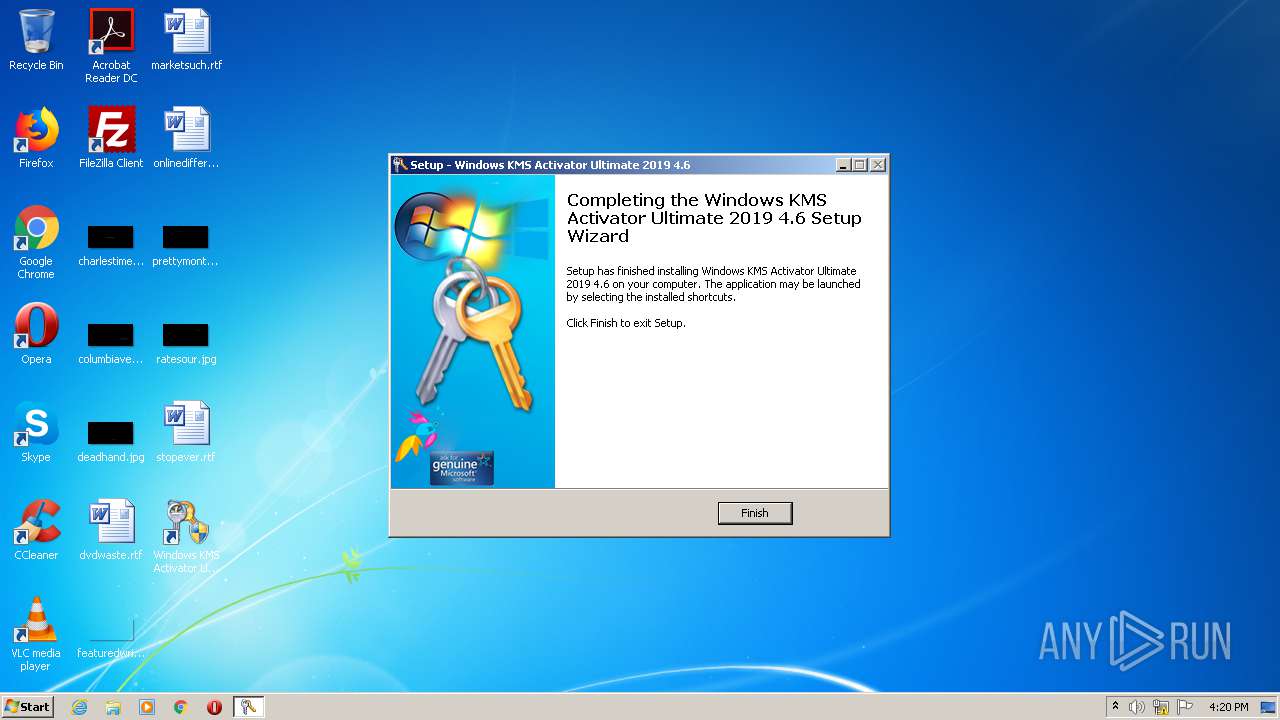
| File name: | Windows KMS Activator Ultimate 2019 4.6 Setup.exe |
| Full analysis: | https://app.any.run/tasks/2595ab17-c58b-4b93-aa2a-973a02793847 |
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2020, 15:19:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F230597DAABA5F4C4F1828600B56CFCA |
| SHA1: | 0420CD83D1593BE50DE9EE961E61A93E3BDB491C |
| SHA256: | A8588086E280BC6B8986B7EB98D198C7792404C675E016FC5F0A64CE192DA426 |
| SSDEEP: | 196608:E3LAsnEhX6tN4yPzgrRF2EQVD64jQ3n9MOlIave4keY:E7aXs1Pz6QVD6F9XldQR |
MALICIOUS
Application was dropped or rewritten from another process
- Windows KMS Activator Ultimate 2019 4.6.exe (PID: 4060)
- Upgrade-latest-072020201620-0afeaed7-0fc3-4113-b3de-e1fc81181c54.exe (PID: 3792)
- Windows KMS Activator Ultimate 2019 4.6.exe (PID: 3752)
Adds new firewall rule via NETSH.EXE
- Windows KMS Activator Ultimate 2019 4.6 Setup.tmp (PID: 3132)
Changes settings of System certificates
- Windows KMS Activator Ultimate 2019 4.6.exe (PID: 3752)
SUSPICIOUS
Executable content was dropped or overwritten
- Windows KMS Activator Ultimate 2019 4.6 Setup.exe (PID: 948)
- Windows KMS Activator Ultimate 2019 4.6.exe (PID: 3752)
- Windows KMS Activator Ultimate 2019 4.6 Setup.exe (PID: 2716)
- Windows KMS Activator Ultimate 2019 4.6 Setup.tmp (PID: 3132)
Modifies the phishing filter of IE
- Windows KMS Activator Ultimate 2019 4.6 Setup.tmp (PID: 3132)
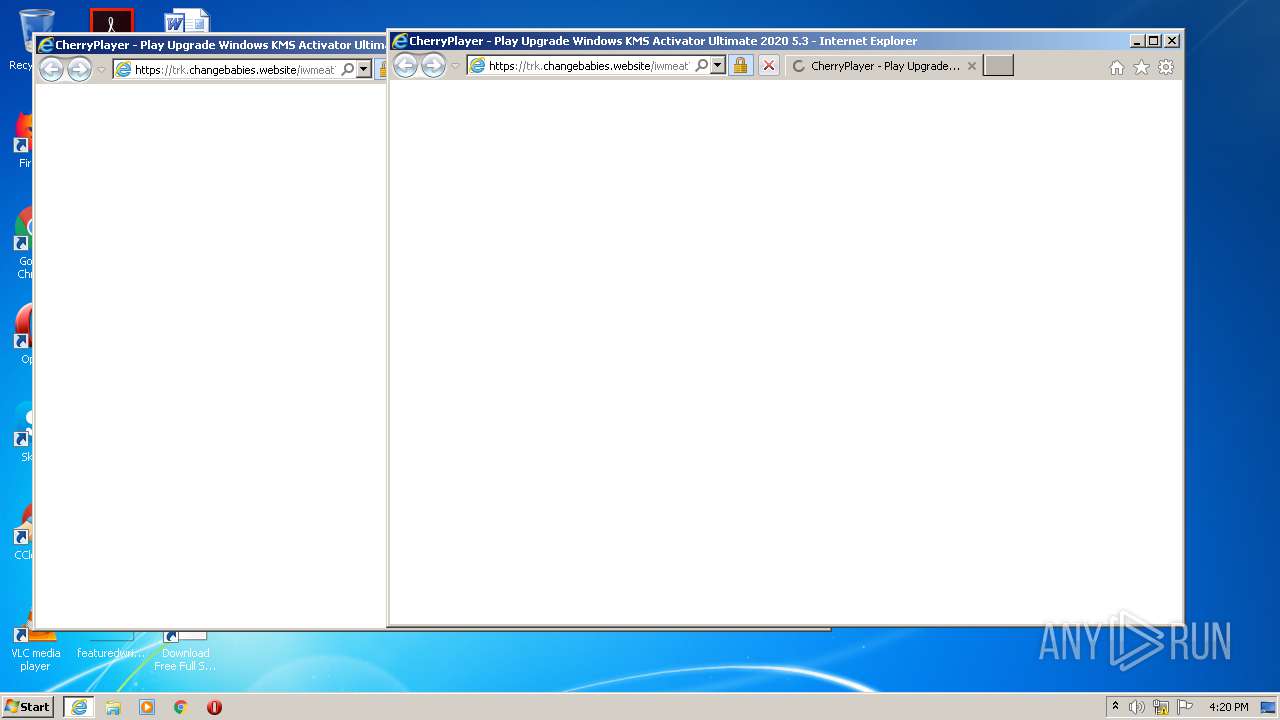
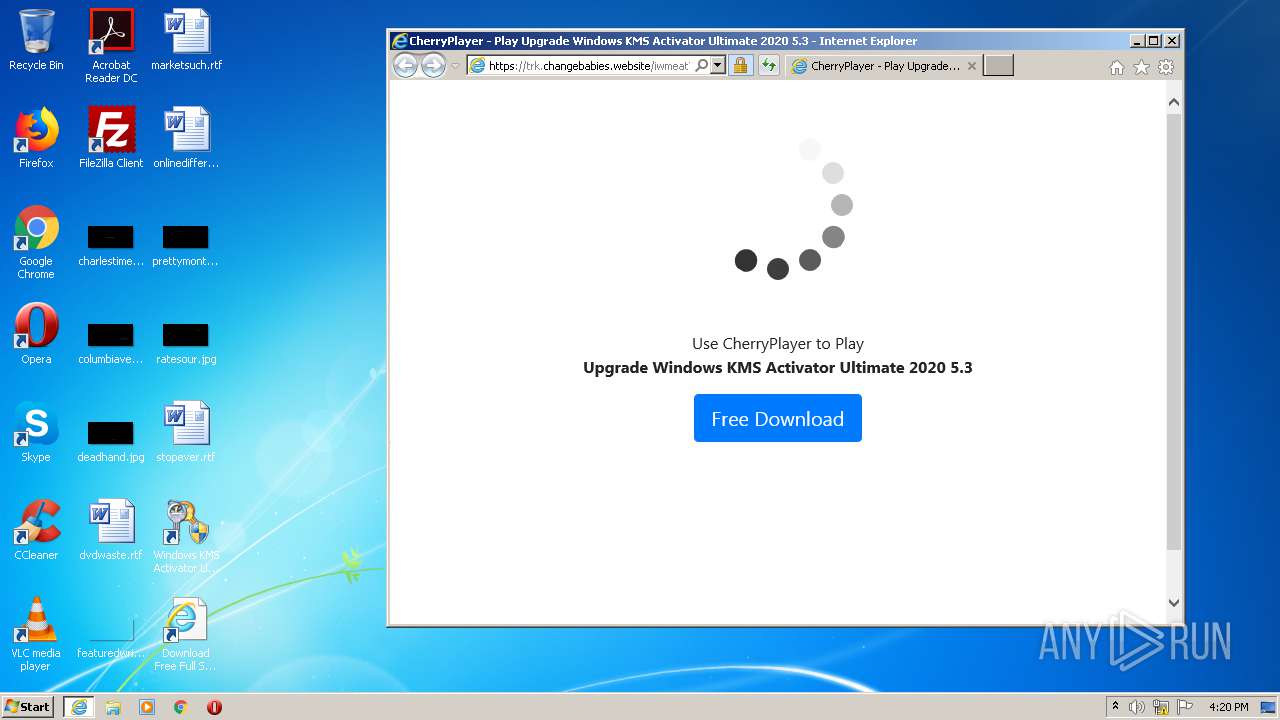
Starts Internet Explorer
- Upgrade-latest-072020201620-0afeaed7-0fc3-4113-b3de-e1fc81181c54.exe (PID: 3792)
Uses NETSH.EXE for network configuration
- Windows KMS Activator Ultimate 2019 4.6 Setup.tmp (PID: 3132)
Creates files in the program directory
- Windows KMS Activator Ultimate 2019 4.6.exe (PID: 3752)
Adds / modifies Windows certificates
- Windows KMS Activator Ultimate 2019 4.6.exe (PID: 3752)
INFO
Application was dropped or rewritten from another process
- Windows KMS Activator Ultimate 2019 4.6 Setup.tmp (PID: 3132)
- Windows KMS Activator Ultimate 2019 4.6 Setup.tmp (PID: 3496)
Creates a software uninstall entry
- Windows KMS Activator Ultimate 2019 4.6 Setup.tmp (PID: 3132)
Manual execution by user
- Windows KMS Activator Ultimate 2019 4.6.exe (PID: 4060)
- Windows KMS Activator Ultimate 2019 4.6.exe (PID: 3752)
Creates files in the program directory
- Windows KMS Activator Ultimate 2019 4.6 Setup.tmp (PID: 3132)
Changes internet zones settings
- iexplore.exe (PID: 3324)
Reads Internet Cache Settings
- iexplore.exe (PID: 2908)
- iexplore.exe (PID: 3324)
Creates files in the user directory
- iexplore.exe (PID: 2908)
Reads internet explorer settings
- iexplore.exe (PID: 2908)
Reads settings of System Certificates
- iexplore.exe (PID: 2908)
- iexplore.exe (PID: 3324)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2908)
Changes settings of System certificates
- iexplore.exe (PID: 2908)
Application launched itself
- iexplore.exe (PID: 3324)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (61.8) |
|---|---|---|
| .exe | | | InstallShield setup (24.2) |
| .exe | | | Win32 Executable Delphi generic (7.9) |
| .exe | | | Win32 Executable (generic) (2.5) |
| .exe | | | Win16/32 Executable Delphi generic (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41472 |
| InitializedDataSize: | 110592 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa98 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Windows KMS Activator Ultimate 2019 4.6 Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Windows KMS Activator Ultimate 2019 4.6 |
| ProductVersion: | 4.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Windows KMS Activator Ultimate 2019 4.6 Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | Windows KMS Activator Ultimate 2019 4.6 |
| ProductVersion: | 4.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A1D0 | 0x0000A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64375 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74012 |
BSS | 0x0000D000 | 0x00000E94 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000097C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x0000091C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x00019F2C | 0x0001A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.40005 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.38543 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.39888 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.11042 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.41603 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.27852 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.68971 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 2.84745 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.98029 | 52474 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 3.32209 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
54
Monitored processes
10
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | "C:\Users\admin\AppData\Local\Temp\Windows KMS Activator Ultimate 2019 4.6 Setup.exe" | C:\Users\admin\AppData\Local\Temp\Windows KMS Activator Ultimate 2019 4.6 Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Windows KMS Activator Ultimate 2019 4.6 Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1000 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name="Windows KMS Activator Ultimate 2019 4.6.exe" program="C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\Windows KMS Activator Ultimate 2019 4.6.exe" dir=in action=allow enable=yes | C:\Windows\system32\netsh.exe | — | Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2716 | "C:\Users\admin\AppData\Local\Temp\Windows KMS Activator Ultimate 2019 4.6 Setup.exe" /SPAWNWND=$401C4 /NOTIFYWND=$A0164 | C:\Users\admin\AppData\Local\Temp\Windows KMS Activator Ultimate 2019 4.6 Setup.exe | Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Windows KMS Activator Ultimate 2019 4.6 Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2908 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3324 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3132 | "C:\Users\admin\AppData\Local\Temp\is-DA97Q.tmp\Windows KMS Activator Ultimate 2019 4.6 Setup.tmp" /SL5="$B0178,9220174,153088,C:\Users\admin\AppData\Local\Temp\Windows KMS Activator Ultimate 2019 4.6 Setup.exe" /SPAWNWND=$401C4 /NOTIFYWND=$A0164 | C:\Users\admin\AppData\Local\Temp\is-DA97Q.tmp\Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | Windows KMS Activator Ultimate 2019 4.6 Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3324 | "C:\Program Files\Internet Explorer\iexplore.exe" https://bit.ly/2WvEBlC | C:\Program Files\Internet Explorer\iexplore.exe | Upgrade-latest-072020201620-0afeaed7-0fc3-4113-b3de-e1fc81181c54.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3496 | "C:\Users\admin\AppData\Local\Temp\is-VDFC6.tmp\Windows KMS Activator Ultimate 2019 4.6 Setup.tmp" /SL5="$A0164,9220174,153088,C:\Users\admin\AppData\Local\Temp\Windows KMS Activator Ultimate 2019 4.6 Setup.exe" | C:\Users\admin\AppData\Local\Temp\is-VDFC6.tmp\Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | — | Windows KMS Activator Ultimate 2019 4.6 Setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3752 | "C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\Windows KMS Activator Ultimate 2019 4.6.exe" | C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\Windows KMS Activator Ultimate 2019 4.6.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Windows KMS Activator Ultimate 2019 Exit code: 0 Version: 4.6.0.0 Modules
| |||||||||||||||
| 3792 | "C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\Upgrade-latest-072020201620-0afeaed7-0fc3-4113-b3de-e1fc81181c54.exe" | C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\Upgrade-latest-072020201620-0afeaed7-0fc3-4113-b3de-e1fc81181c54.exe | — | Windows KMS Activator Ultimate 2019 4.6.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4060 | "C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\Windows KMS Activator Ultimate 2019 4.6.exe" | C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\Windows KMS Activator Ultimate 2019 4.6.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Windows KMS Activator Ultimate 2019 Exit code: 3221226540 Version: 4.6.0.0 Modules
| |||||||||||||||
Total events
1 253
Read events
1 035
Write events
211
Delete events
7
Modification events
| (PID) Process: | (3132) Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 3C0C000024A0DF5BBD9CD601 | |||
| (PID) Process: | (3132) Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 997CEE5A7220B75344AE4B5CA34BCB69983AD8F2CB3DFD61F13855A09A8CF350 | |||
| (PID) Process: | (3132) Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3132) Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\Windows KMS Activator Ultimate 2019 4.6.exe | |||
| (PID) Process: | (3132) Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 7B8907C68FCA9DD78D933C76D08E87BEE7297462DAAF7B40860E4F4A137E9157 | |||
| (PID) Process: | (3132) Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\PhishingFilter |
| Operation: | write | Name: | EnabledV9 |
Value: 0 | |||
| (PID) Process: | (3132) Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SmartScreenEnabled |
Value: Off | |||
| (PID) Process: | (3132) Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | EnableSmartScreen |
Value: 0 | |||
| (PID) Process: | (3132) Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Windows KMS Activator Ultimate 2019 4.6_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.9 (a) | |||
| (PID) Process: | (3132) Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Windows KMS Activator Ultimate 2019 4.6_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Windows KMS Activator Ultimate 2019 4.6 | |||
Executable files
6
Suspicious files
41
Text files
22
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3132 | Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\is-R97DA.tmp | — | |
MD5:— | SHA256:— | |||
| 3132 | Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\is-C4LH2.tmp | — | |
MD5:— | SHA256:— | |||
| 3132 | Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\is-N6I61.tmp | — | |
MD5:— | SHA256:— | |||
| 3132 | Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\is-SLNQ5.tmp | — | |
MD5:— | SHA256:— | |||
| 3132 | Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\is-KHBMU.tmp | — | |
MD5:— | SHA256:— | |||
| 3752 | Windows KMS Activator Ultimate 2019 4.6.exe | C:\Users\admin\AppData\Local\Windows_8\Windows_KMS_Activator_Ult_Url_lzph5kh2ayu12wi2ksagswudnsyxvrgl\4.6.0.0\jhc54op4.newcfg | — | |
MD5:— | SHA256:— | |||
| 2908 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab983D.tmp | — | |
MD5:— | SHA256:— | |||
| 2908 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar983E.tmp | — | |
MD5:— | SHA256:— | |||
| 3132 | Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | C:\Users\Public\Desktop\Windows KMS Activator Ultimate 2019 4.6.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3132 | Windows KMS Activator Ultimate 2019 4.6 Setup.tmp | C:\Program Files\Windows KMS Activator Ultimate 2019 4.6\unins000.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
44
DNS requests
28
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2908 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAlY0UQ%2F%2FW4jtC14M2cPdNc%3D | US | der | 278 b | whitelisted |
3752 | Windows KMS Activator Ultimate 2019 4.6.exe | GET | 200 | 104.219.248.105:80 | http://renewsoftware.com/1-winkms/Version.txt | US | text | 7 b | malicious |
2908 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAqN7HPiQ2%2F4c3rdXE3uHG8%3D | US | der | 471 b | whitelisted |
2908 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3752 | Windows KMS Activator Ultimate 2019 4.6.exe | GET | 200 | 104.219.248.105:80 | http://renewsoftware.com/1-winkms/up.txt | US | text | 76 b | malicious |
2908 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2908 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2908 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2908 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2908 | iexplore.exe | GET | 200 | 13.226.156.224:80 | http://s.ss2.us/r.crl | US | der | 434 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3752 | Windows KMS Activator Ultimate 2019 4.6.exe | 162.125.66.15:443 | dl.dropboxusercontent.com | Dropbox, Inc. | DE | malicious |
2908 | iexplore.exe | 104.27.168.90:443 | trk.changebabies.website | Cloudflare Inc | US | shared |
2908 | iexplore.exe | 67.199.248.11:443 | bit.ly | Bitly Inc | US | shared |
2908 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3752 | Windows KMS Activator Ultimate 2019 4.6.exe | 104.219.248.105:80 | renewsoftware.com | Namecheap, Inc. | US | malicious |
2908 | iexplore.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
— | — | 172.67.177.33:443 | impress.polar-track.com | — | US | unknown |
2908 | iexplore.exe | 209.197.3.24:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
— | — | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
3324 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
renewsoftware.com |
| malicious |
dl.dropboxusercontent.com |
| shared |
bit.ly |
| shared |
ocsp.digicert.com |
| whitelisted |
trk.changebabies.website |
| suspicious |
code.jquery.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
impress.polar-track.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report