| File name: | file3.ps1 |
| Full analysis: | https://app.any.run/tasks/8af33984-62ab-48d9-8e7c-59cf1d8ad0c8 |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2025, 22:49:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (683), with CRLF line terminators |
| MD5: | 8829FE44A9948A1728DC4BC6E60B64A9 |
| SHA1: | 4C5F7885C54BEF2CF2531FF6911C705A6613237A |
| SHA256: | A848FFBA7A5E70CC4F1DC40CA6633EA42F803A61BD22C5313F7B439C9F1143B3 |
| SSDEEP: | 48:FYKvryKYOjCU8Ye+8TeRhOVoDhBgzZ+9AVsAmOEW0CKwmiJjQwQ+Hw1/d/gGHBnc:Vvu2O0UsOGDRwmqTy1aSoTgTS3G+ |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6700)
SUSPICIOUS
Reverses array data (POWERSHELL)
- powershell.exe (PID: 6700)
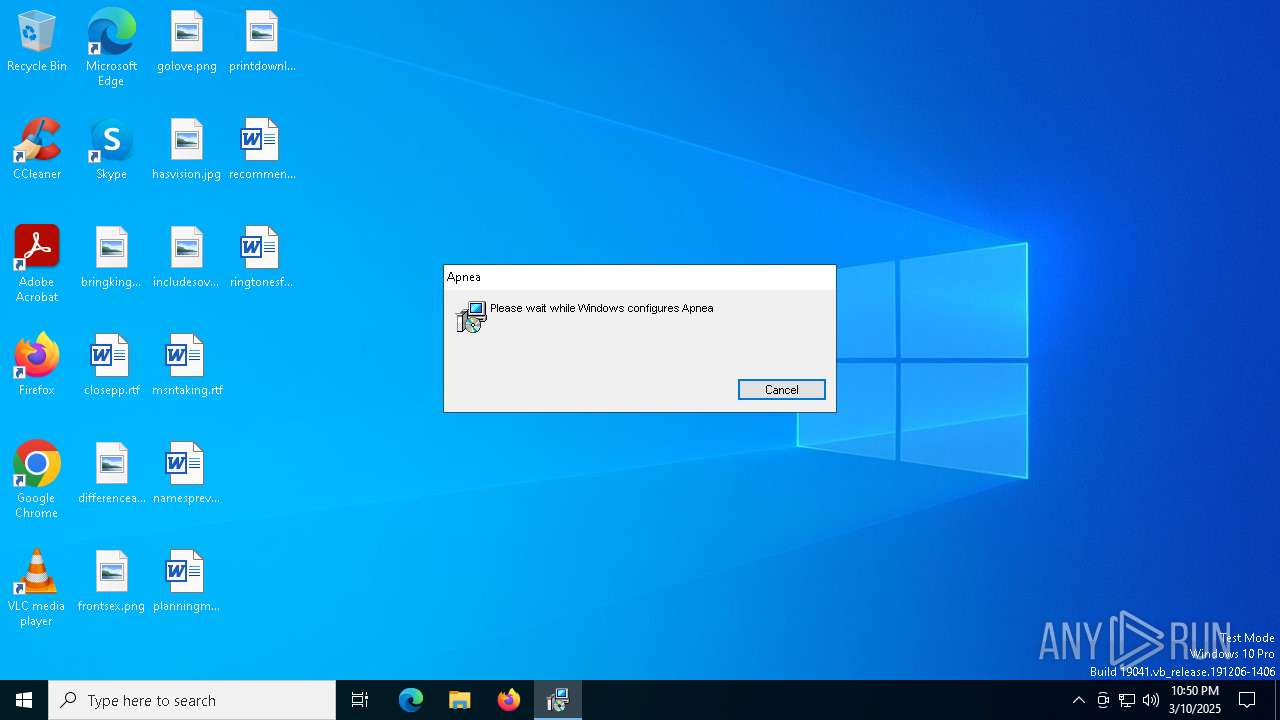
The process drops C-runtime libraries
- msiexec.exe (PID: 7616)
- ABEventBackup.exe (PID: 7276)
Process drops legitimate windows executable
- msiexec.exe (PID: 7616)
- ABEventBackup.exe (PID: 7276)
Executable content was dropped or overwritten
- ABEventBackup.exe (PID: 7276)
- cmd.exe (PID: 5352)
Starts CMD.EXE for commands execution
- ABEventBackup.exe (PID: 1184)
Starts itself from another location
- ABEventBackup.exe (PID: 7276)
Executes as Windows Service
- VSSVC.exe (PID: 7664)
The executable file from the user directory is run by the CMD process
- HK_validate_debug.exe (PID: 5576)
INFO
Disables trace logs
- powershell.exe (PID: 6700)
Reads the computer name
- msiexec.exe (PID: 7616)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6700)
Checks proxy server information
- powershell.exe (PID: 6700)
Checks supported languages
- msiexec.exe (PID: 7616)
Manages system restore points
- SrTasks.exe (PID: 6044)
The sample compiled with english language support
- msiexec.exe (PID: 7616)
- ABEventBackup.exe (PID: 7276)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
149
Monitored processes
14
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | C:\Users\admin\AppData\Roaming\LZ_Oracle_x86\ABEventBackup.exe | C:\Users\admin\AppData\Roaming\LZ_Oracle_x86\ABEventBackup.exe | — | ABEventBackup.exe | |||||||||||
User: admin Company: AOMEI International Network Limited Integrity Level: MEDIUM Description: It is used to notify backup service to perform AOMEI's logon, logoff scheduled tasks. Exit code: 1 Version: 6, 4, 0, 0 Modules
| |||||||||||||||
| 5352 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | ABEventBackup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5576 | C:\Users\admin\AppData\Local\Temp\HK_validate_debug.exe | C:\Users\admin\AppData\Local\Temp\HK_validate_debug.exe | — | cmd.exe | |||||||||||
User: admin Company: Nenad Hrg (SoftwareOK.com) Integrity Level: MEDIUM Description: Q-Dir Version: 11,4,4,0 Modules
| |||||||||||||||
| 5956 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6032 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6044 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6700 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\file3.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7276 | "C:\Users\admin\AppData\Local\Charabanc\ABEventBackup.exe" | C:\Users\admin\AppData\Local\Charabanc\ABEventBackup.exe | msiexec.exe | ||||||||||||
User: admin Company: AOMEI International Network Limited Integrity Level: MEDIUM Description: It is used to notify backup service to perform AOMEI's logon, logoff scheduled tasks. Exit code: 0 Version: 6, 4, 0, 0 Modules
| |||||||||||||||
Total events
8 833
Read events
8 565
Write events
250
Delete events
18
Modification events
| (PID) Process: | (6700) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.msi\OpenWithProgids |
| Operation: | write | Name: | Msi.Package |
Value: | |||
| (PID) Process: | (7616) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000052EFDFC30E92DB01C01D0000E01D0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7616) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000052EFDFC30E92DB01C01D0000E01D0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7616) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000D70F1EC40E92DB01C01D0000E01D0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7616) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000D70F1EC40E92DB01C01D0000E01D0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7616) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000264D20C40E92DB01C01D0000E01D0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7616) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000005E1525C40E92DB01C01D0000E01D0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7616) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (7616) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000455F90C40E92DB01C01D0000E01D0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7616) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000A7C292C40E92DB01C01D00006C1E0000E8030000010000000000000000000000853F10580038184396AD6566CA2B6BFE00000000000000000000000000000000 | |||
Executable files
13
Suspicious files
25
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6700 | powershell.exe | C:\Users\admin\AppData\Local\Temp\FRHXFNCT1.msi | — | |
MD5:— | SHA256:— | |||
| 7616 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7616 | msiexec.exe | C:\Windows\Installer\11293f.msi | — | |
MD5:— | SHA256:— | |||
| 7616 | msiexec.exe | C:\Users\admin\AppData\Local\Charabanc\impersonator.pdf | — | |
MD5:— | SHA256:— | |||
| 7616 | msiexec.exe | C:\Windows\Installer\112941.msi | — | |
MD5:— | SHA256:— | |||
| 6700 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HGWYIV5UDWMNP69LQU6P.temp | binary | |
MD5:0ADC4A650C7881174EF1144B073CD32A | SHA256:EABCA37E24E3B7FCD38931C8715A9675C1A74BFEB19A1C7C3831A874AF3A7CCD | |||
| 6700 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:12C4C836B981509CFB146396991C7387 | SHA256:A5A1E68833F407A14E52BF4D5284BE71B0DD13B7069940F655D32C67BD96379F | |||
| 6700 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10b23b.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7616 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{58103f85-3800-4318-96ad-6566ca2b6bfe}_OnDiskSnapshotProp | binary | |
MD5:F01241716C59EB1F512AC00C307CDE31 | SHA256:1FA8DF5E8EE639989FB08193A3583721A0D365AE5084502FC0C590992D9EAADC | |||
| 6700 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_c4geyi1d.m4z.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
35
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4408 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7964 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7964 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6700 | powershell.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
6700 | powershell.exe | 185.199.110.133:443 | objects.githubusercontent.com | FASTLY | US | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |