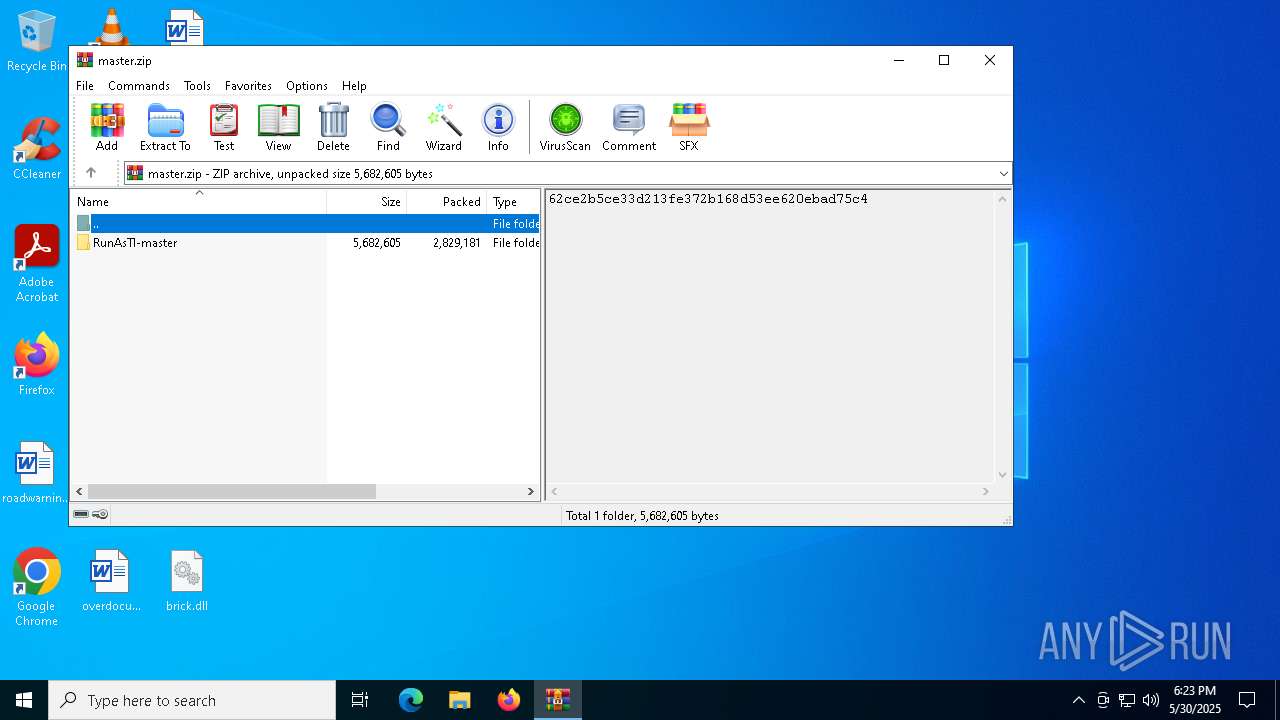
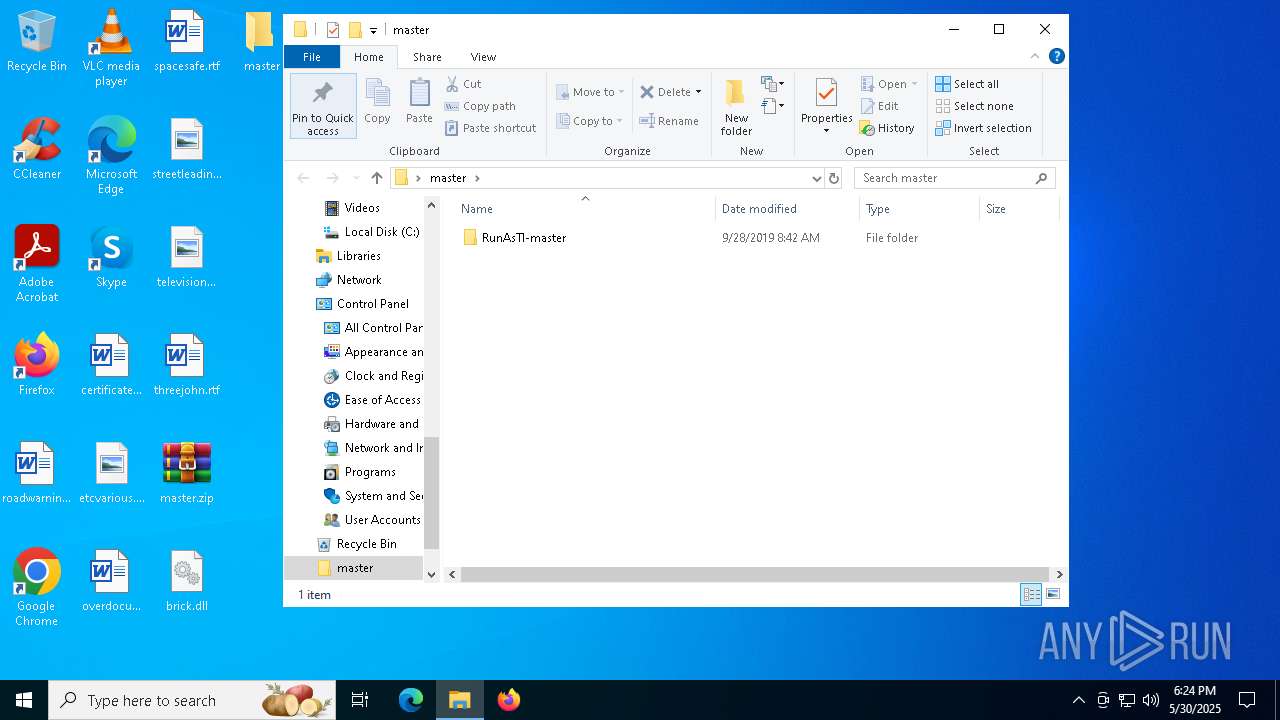
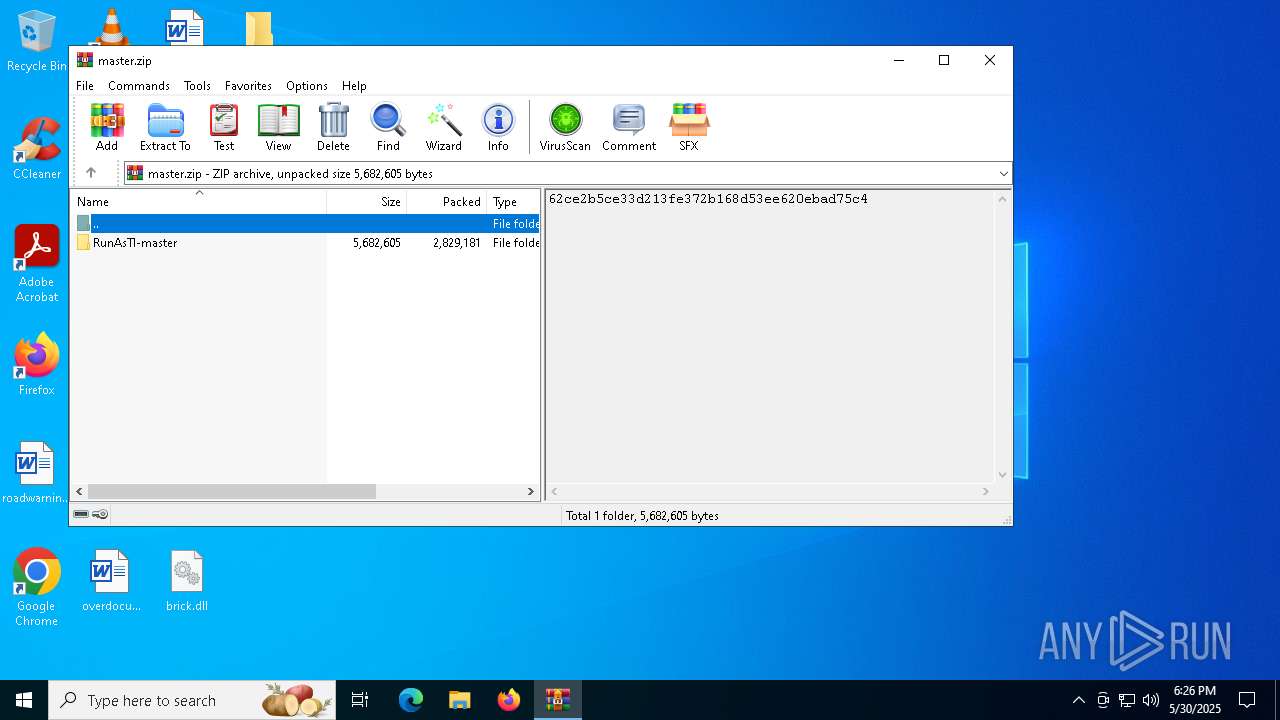
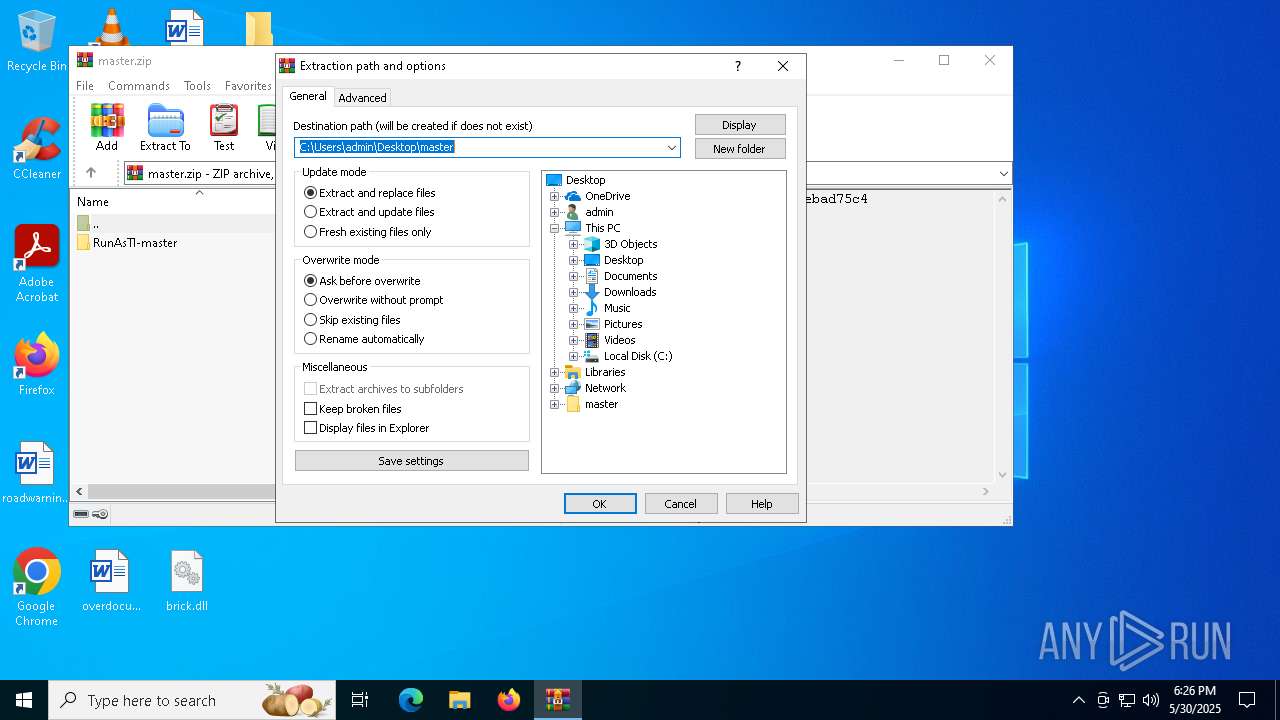
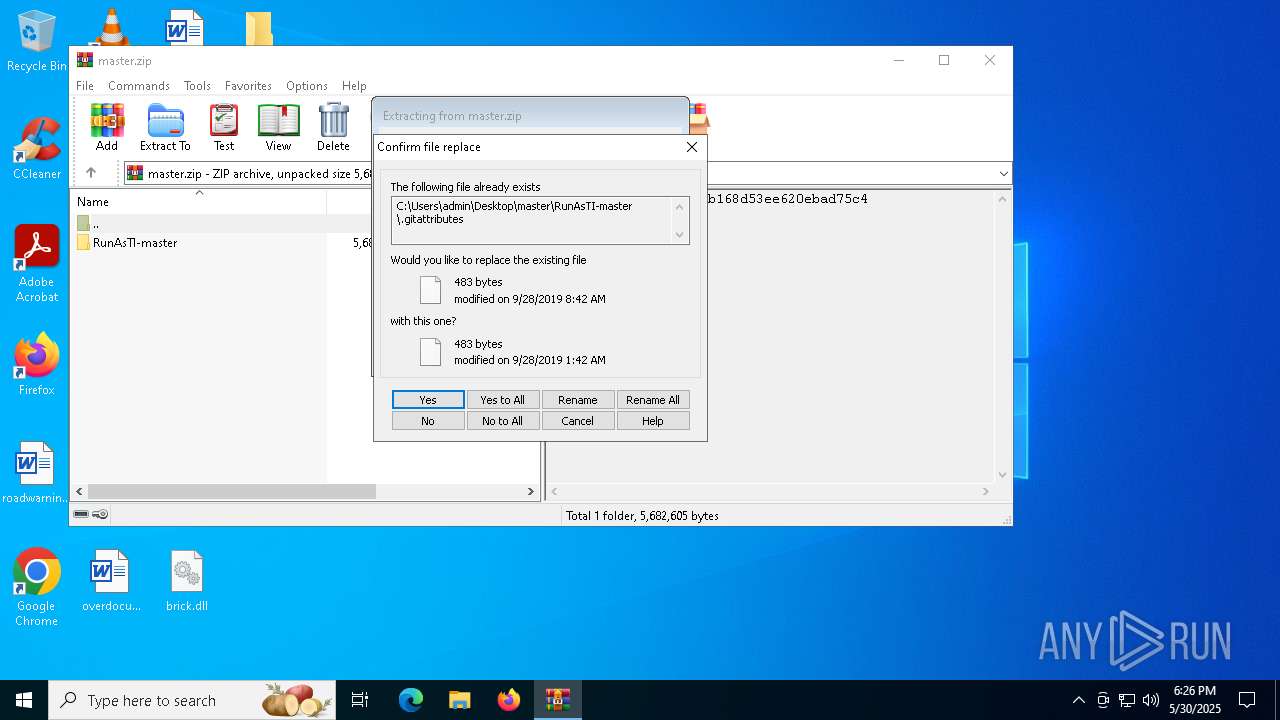
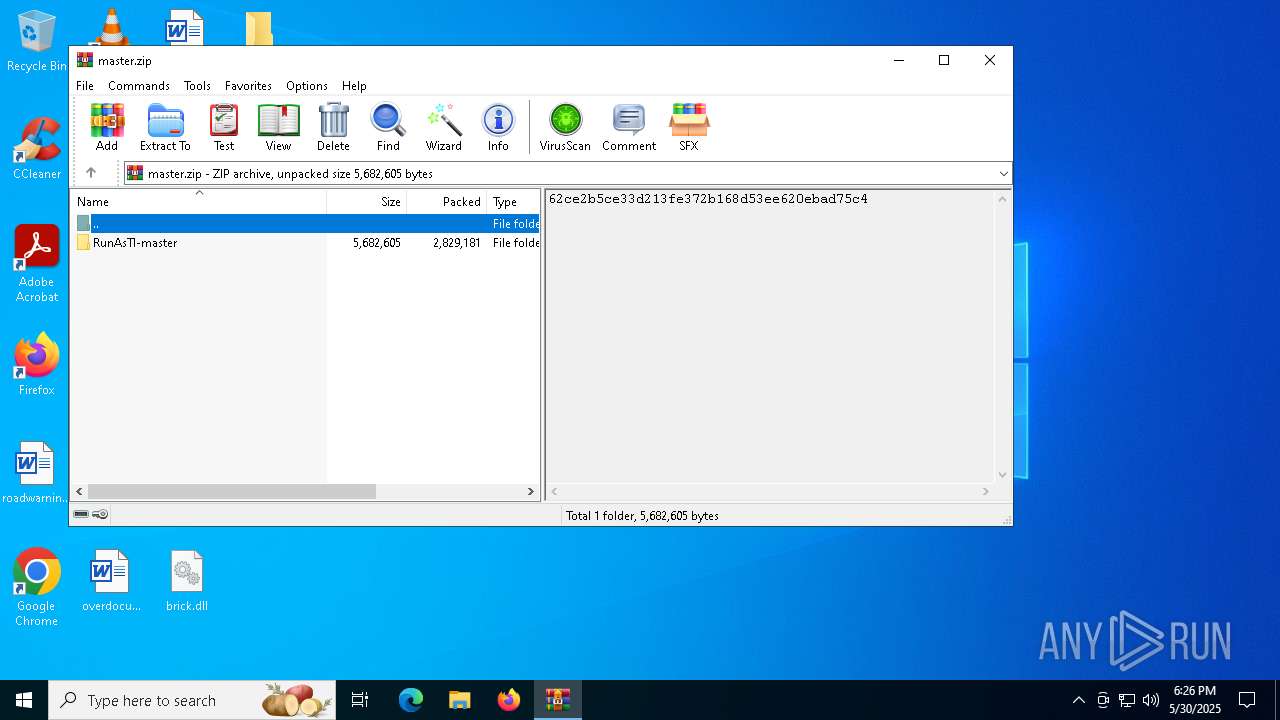
| File name: | master.zip |
| Full analysis: | https://app.any.run/tasks/bc0baf07-4a69-4fde-98b1-cd90db2ad555 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2025, 18:23:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | EE6E2702BF5889749740A8D310776E4D |
| SHA1: | FD3291F4E2473189CF69BE6D7CDA57A349FEB129 |
| SHA256: | A829BD71DC30486EC7CEB7E44B84684F0A745077FB922060F235A5CD5E2195D6 |
| SSDEEP: | 98304:3xH/crdz4VMhrhwwOsETppQM3JtD80H1fCi/Bvc8mFtsC9OJHG78xG7x+y9LcFtf:Weh5hx/L+q |
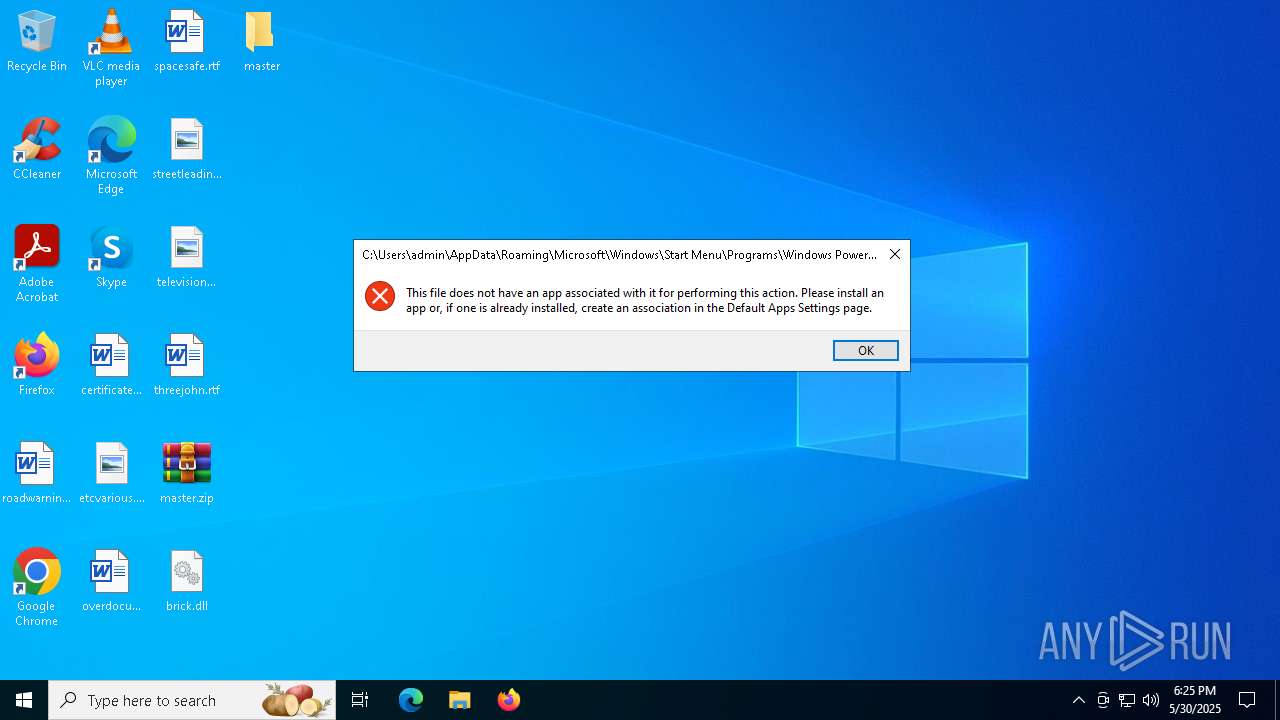
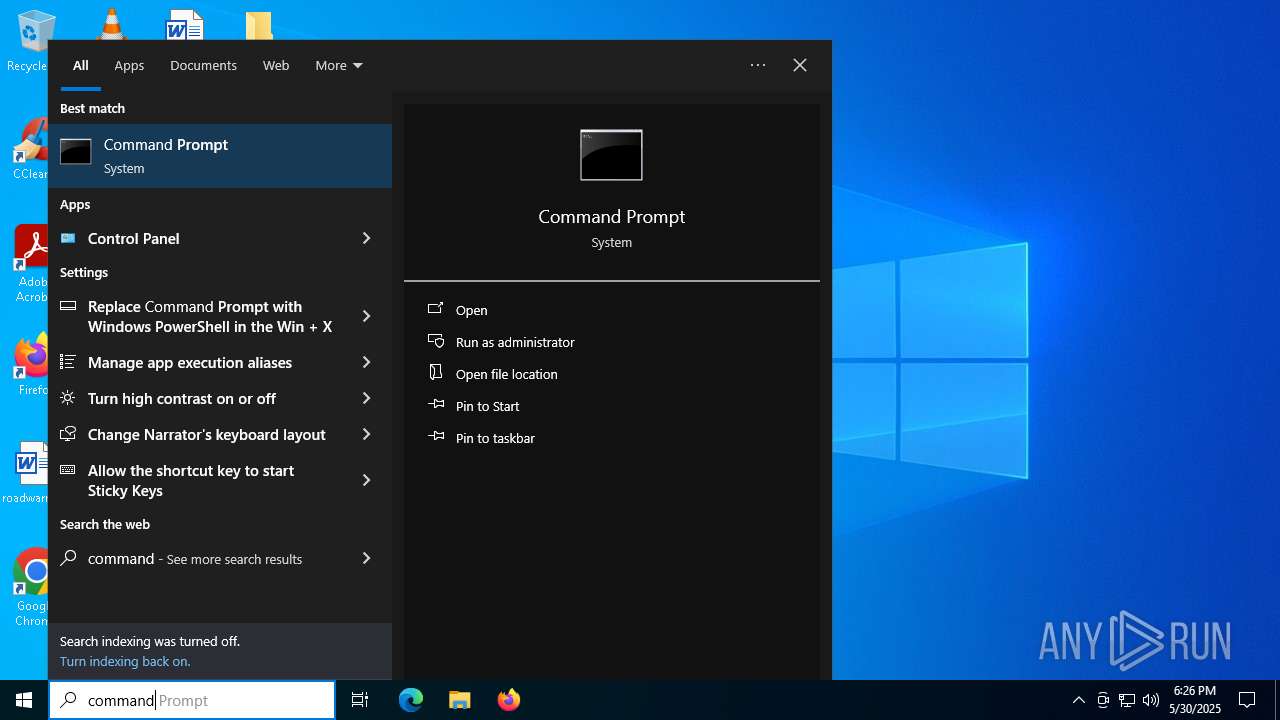
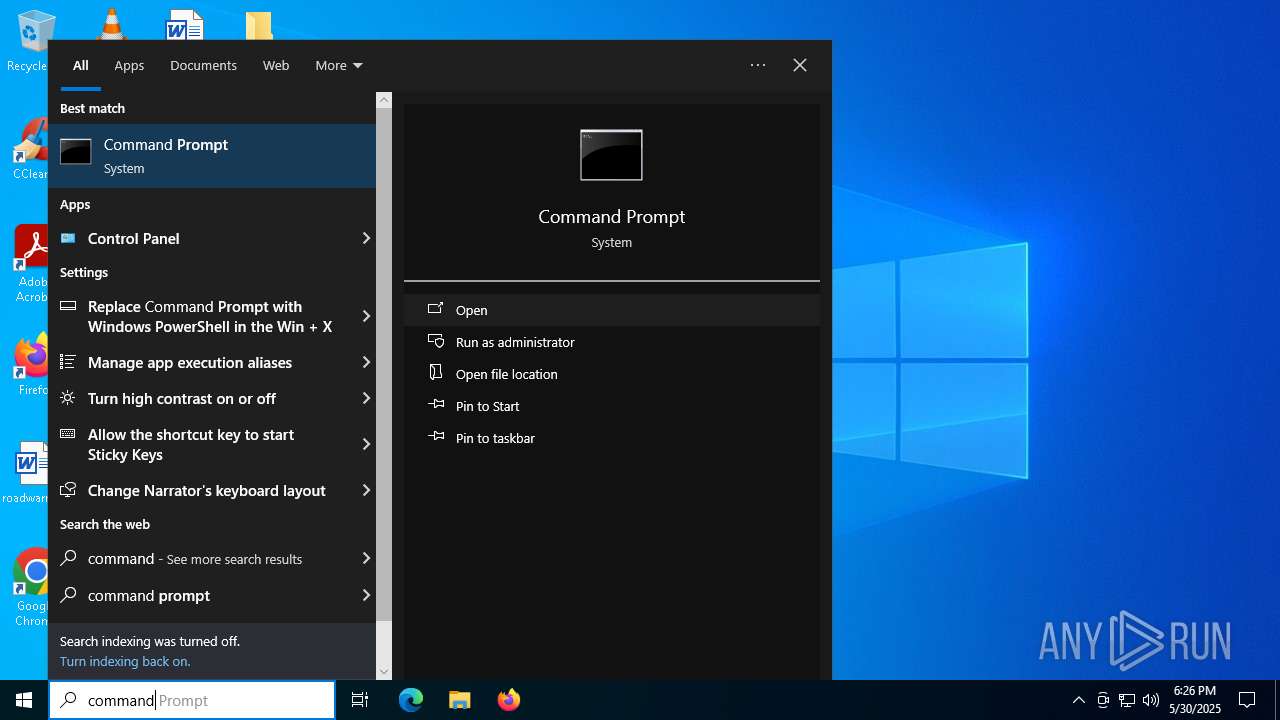
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 1176)
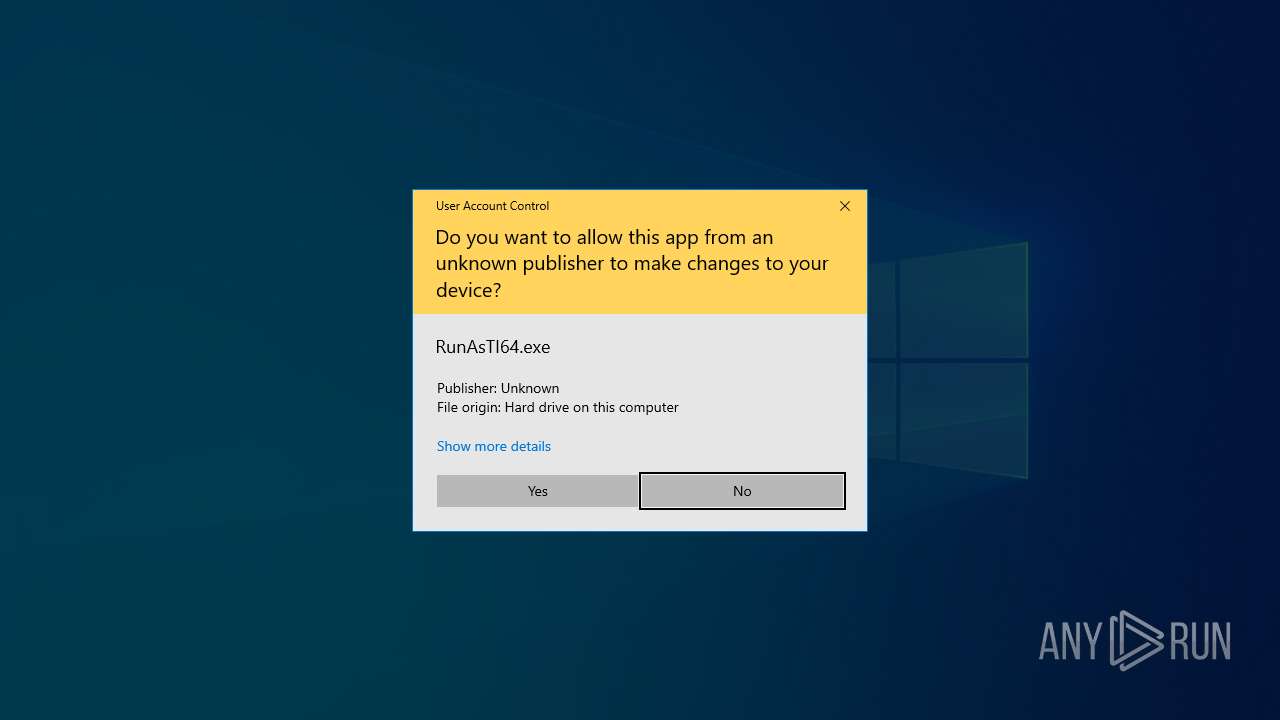
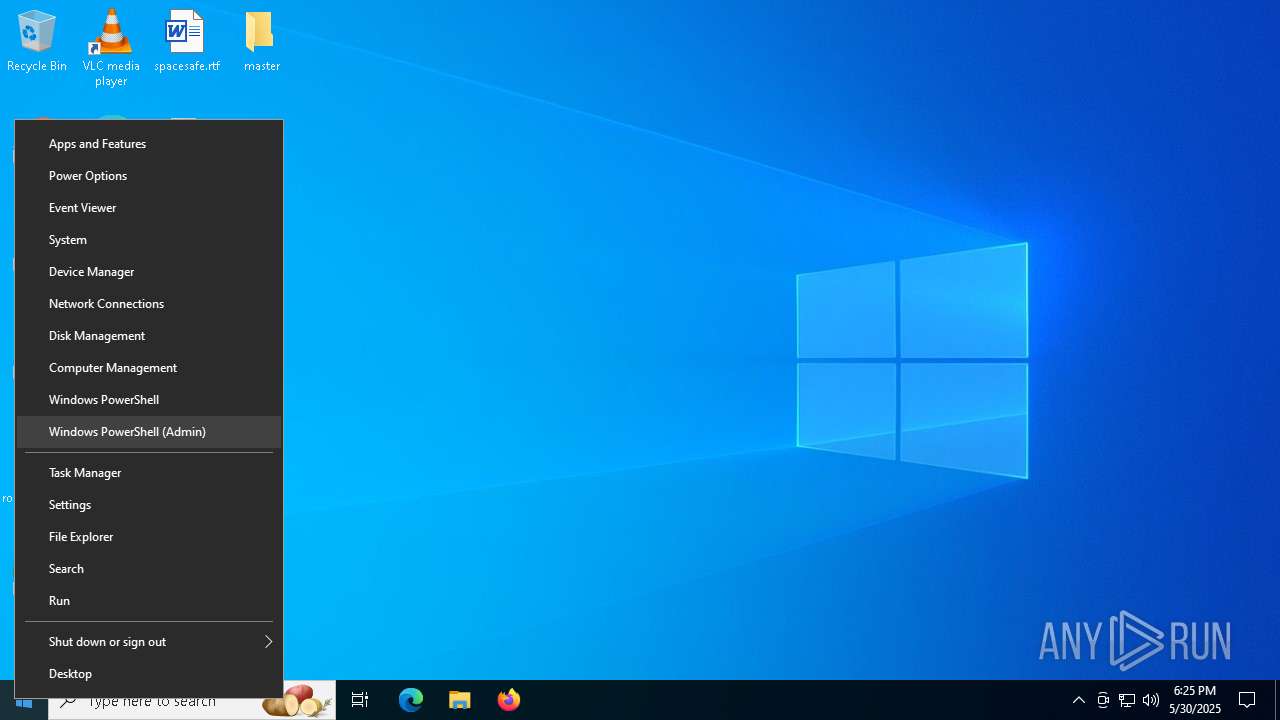
SUSPICIOUS
Reads security settings of Internet Explorer
- RunAsTI64.exe (PID: 5760)
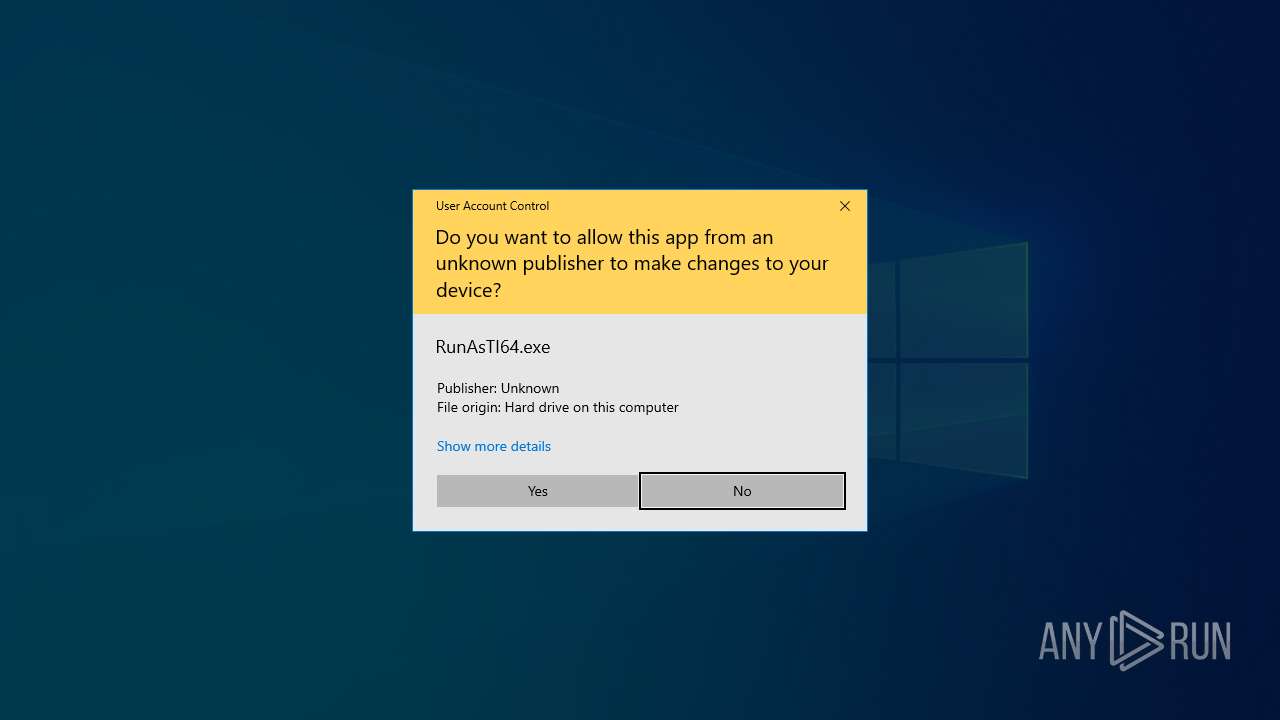
Application launched itself
- RunAsTI64.exe (PID: 5760)
- RunAsTI64.exe (PID: 5256)
Reads the date of Windows installation
- RunAsTI64.exe (PID: 5760)
Executable content was dropped or overwritten
- RunAsTI64.exe (PID: 7964)
- rundll32.exe (PID: 8140)
- RunAsTI64.exe (PID: 6092)
- rundll32.exe (PID: 5256)
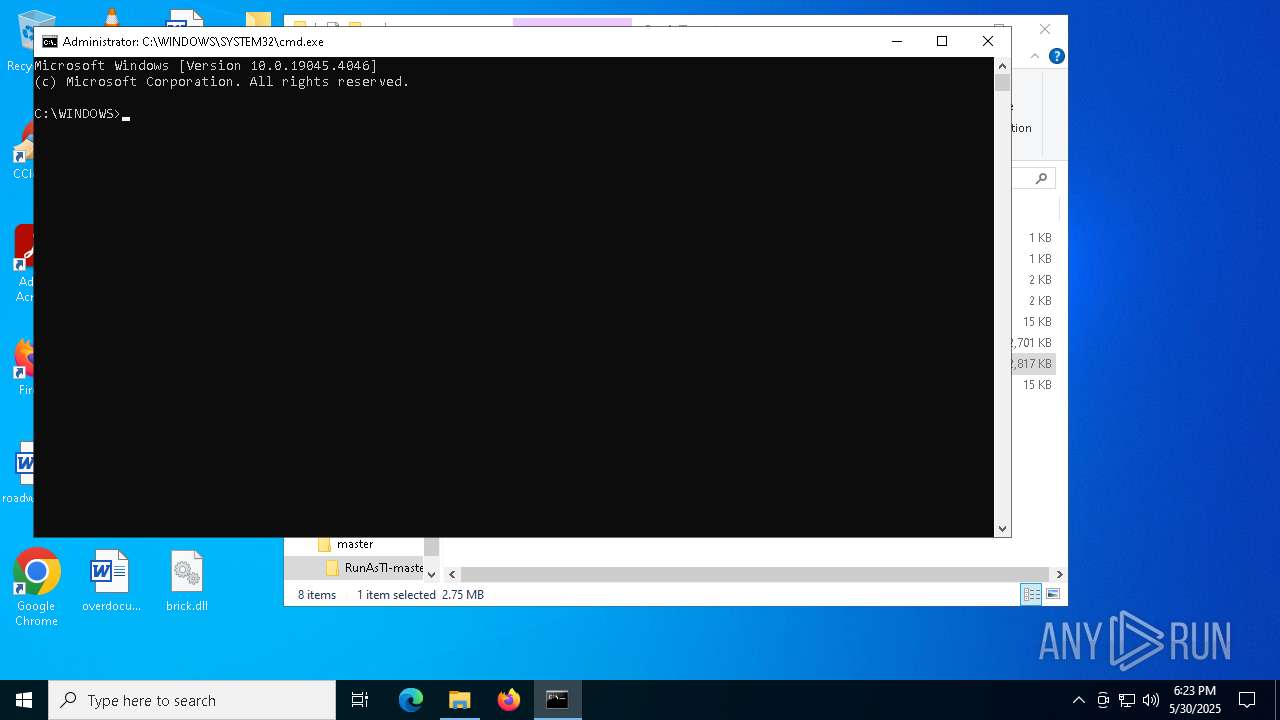
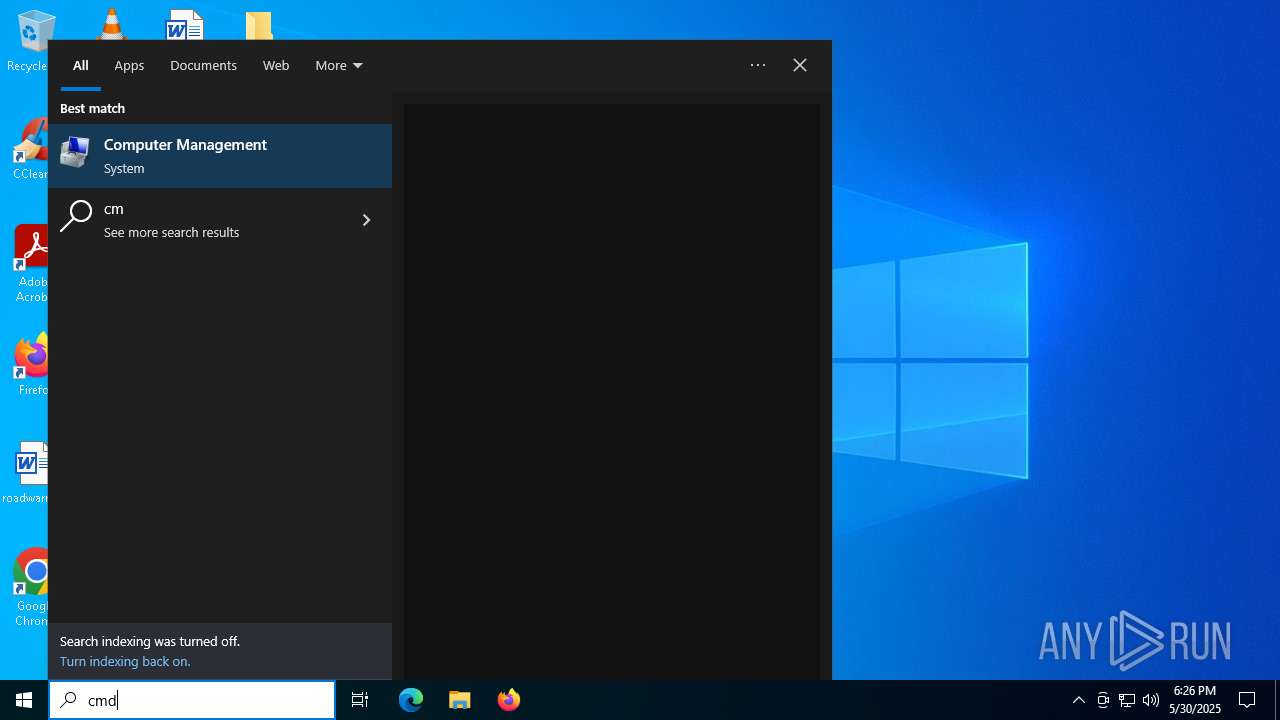
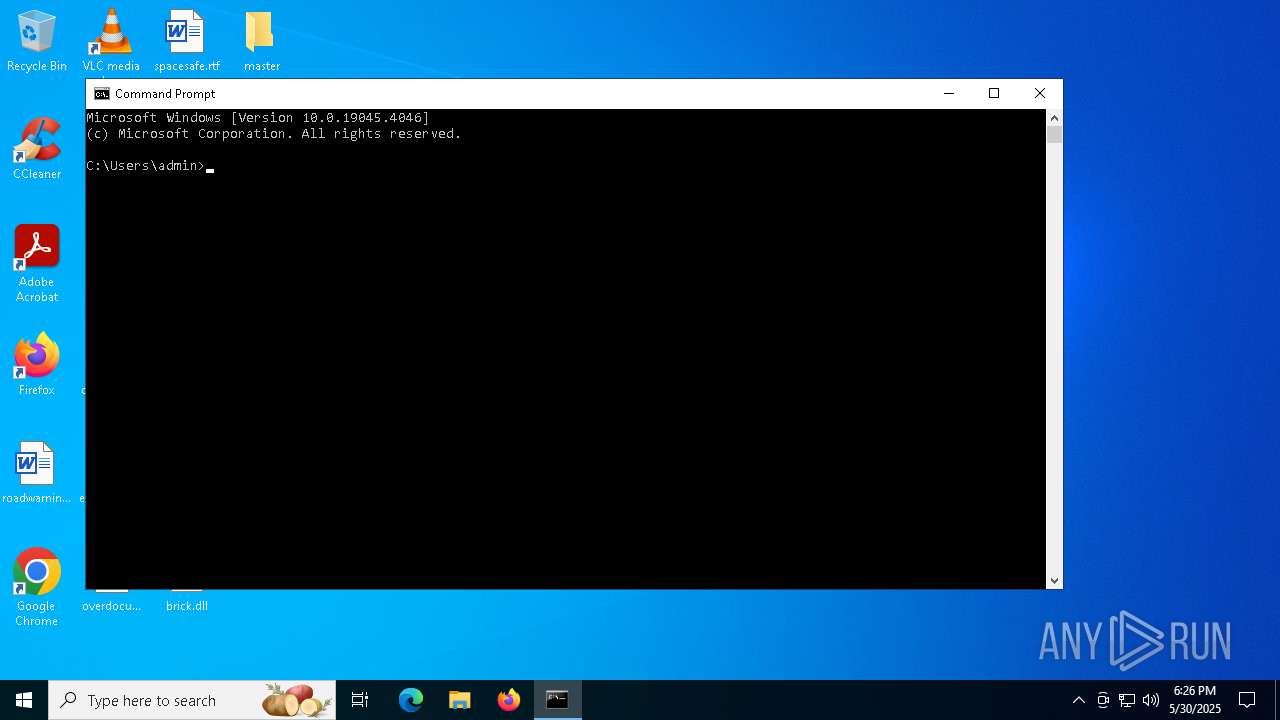
Starts CMD.EXE for commands execution
- RunAsTI64.exe (PID: 7964)
- RunFromToken64.exe (PID: 2064)
- RunAsTI64.exe (PID: 6092)
- RunFromToken64.exe (PID: 5176)
Windows service management via SC.EXE
- sc.exe (PID: 7184)
- sc.exe (PID: 5644)
Starts SC.EXE for service management
- cmd.exe (PID: 8000)
- cmd.exe (PID: 5964)
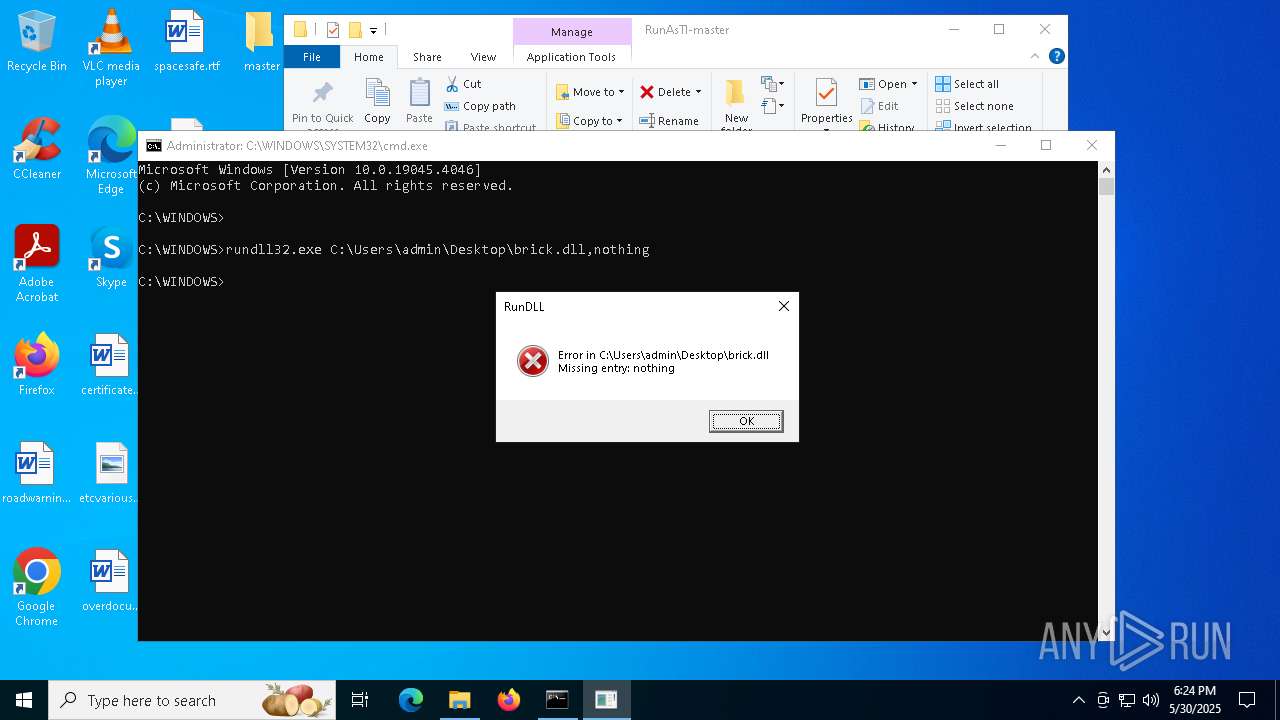
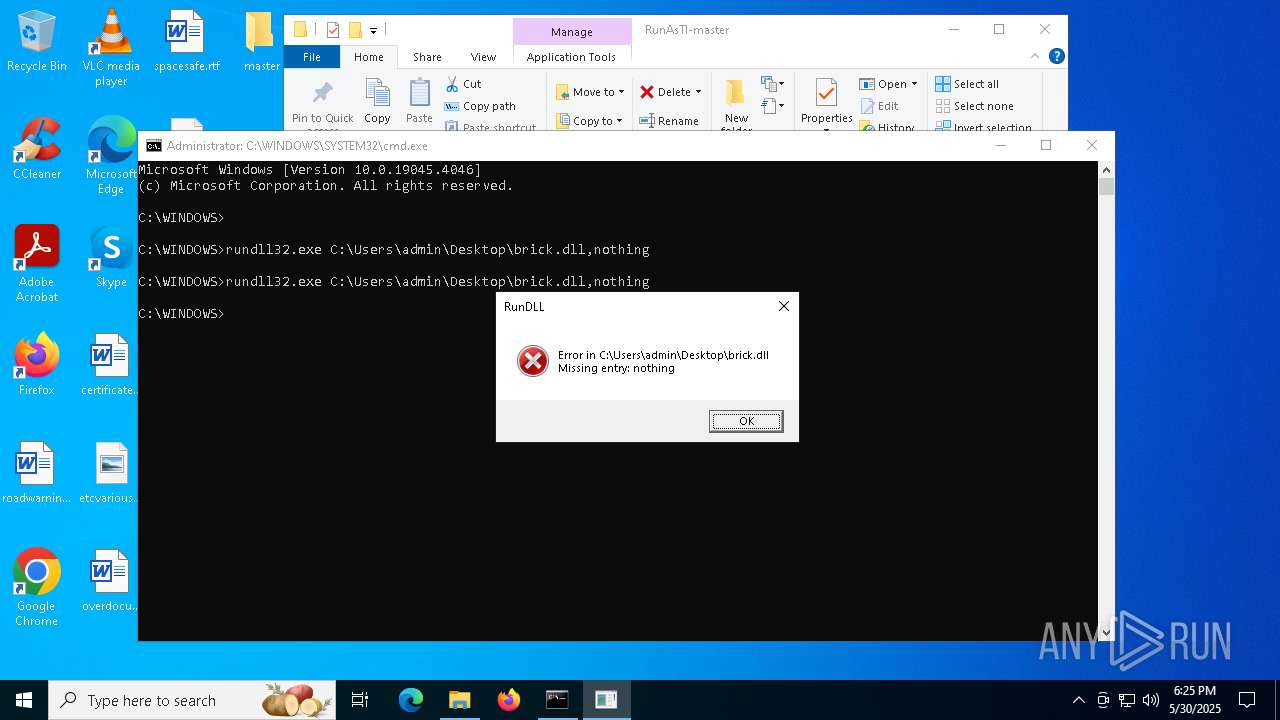
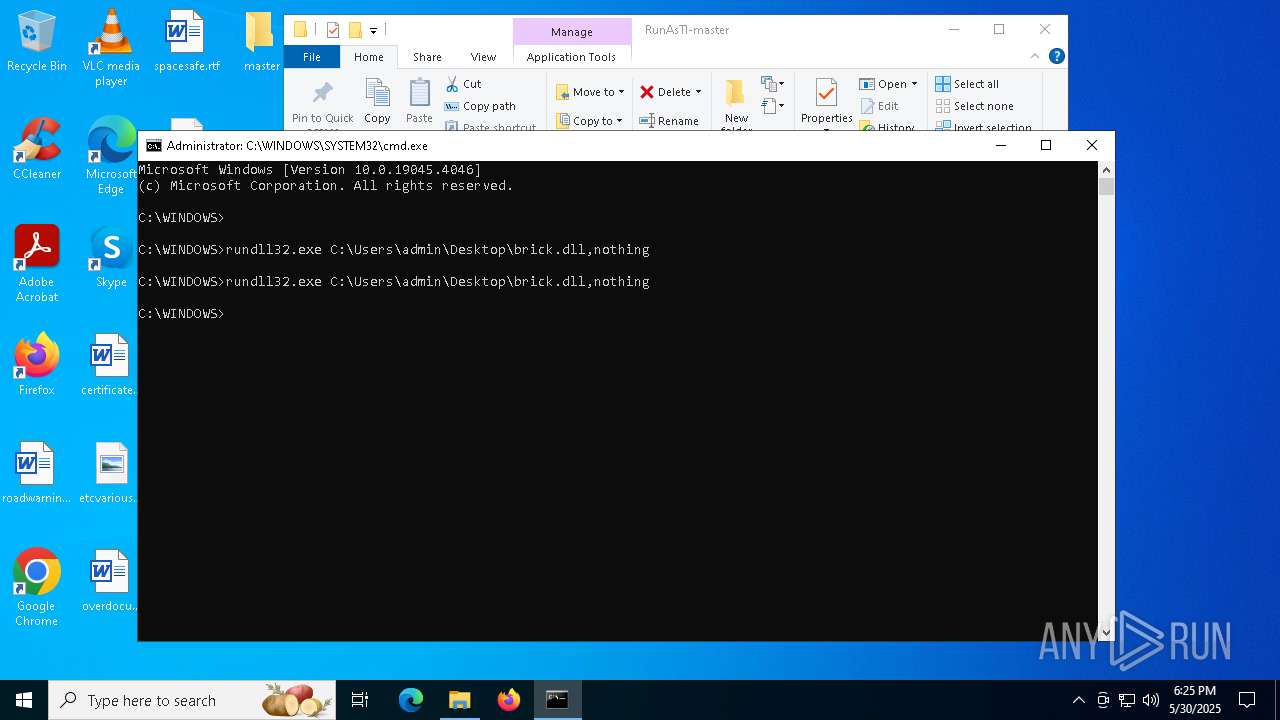
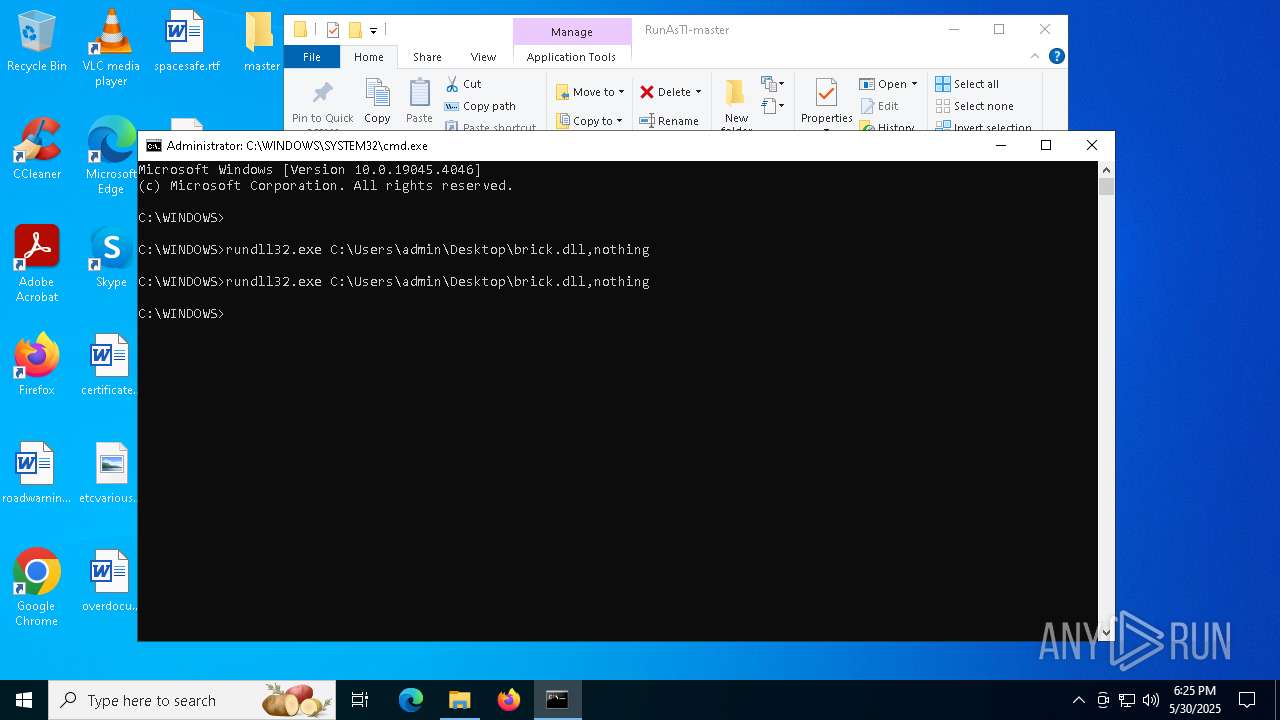
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 4748)
- cmd.exe (PID: 1112)
The process creates files with name similar to system file names
- rundll32.exe (PID: 8140)
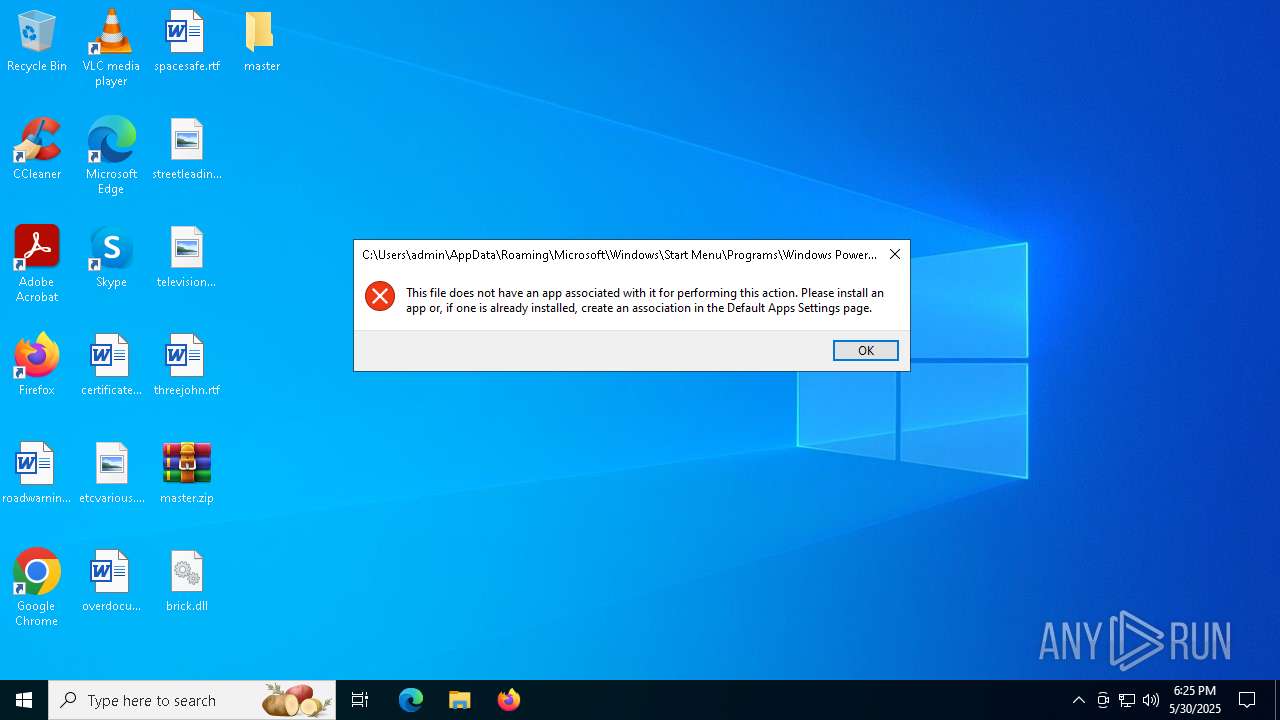
The system shut down or reboot
- rundll32.exe (PID: 8140)
- rundll32.exe (PID: 1260)
- cmd.exe (PID: 6196)
- firefox.exe (PID: 6800)
- rundll32.exe (PID: 5256)
- cmd.exe (PID: 1112)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4132)
- shutdown.exe (PID: 4620)
INFO
Create files in a temporary directory
- RunAsTI64.exe (PID: 7964)
Reads mouse settings
- RunAsTI64.exe (PID: 7964)
- RunAsTI64.exe (PID: 5760)
- RunFromToken64.exe (PID: 2064)
Checks supported languages
- RunAsTI64.exe (PID: 7964)
- RunAsTI64.exe (PID: 5760)
- RunFromToken64.exe (PID: 2064)
Reads the computer name
- RunAsTI64.exe (PID: 5760)
- RunAsTI64.exe (PID: 7964)
- RunFromToken64.exe (PID: 2064)
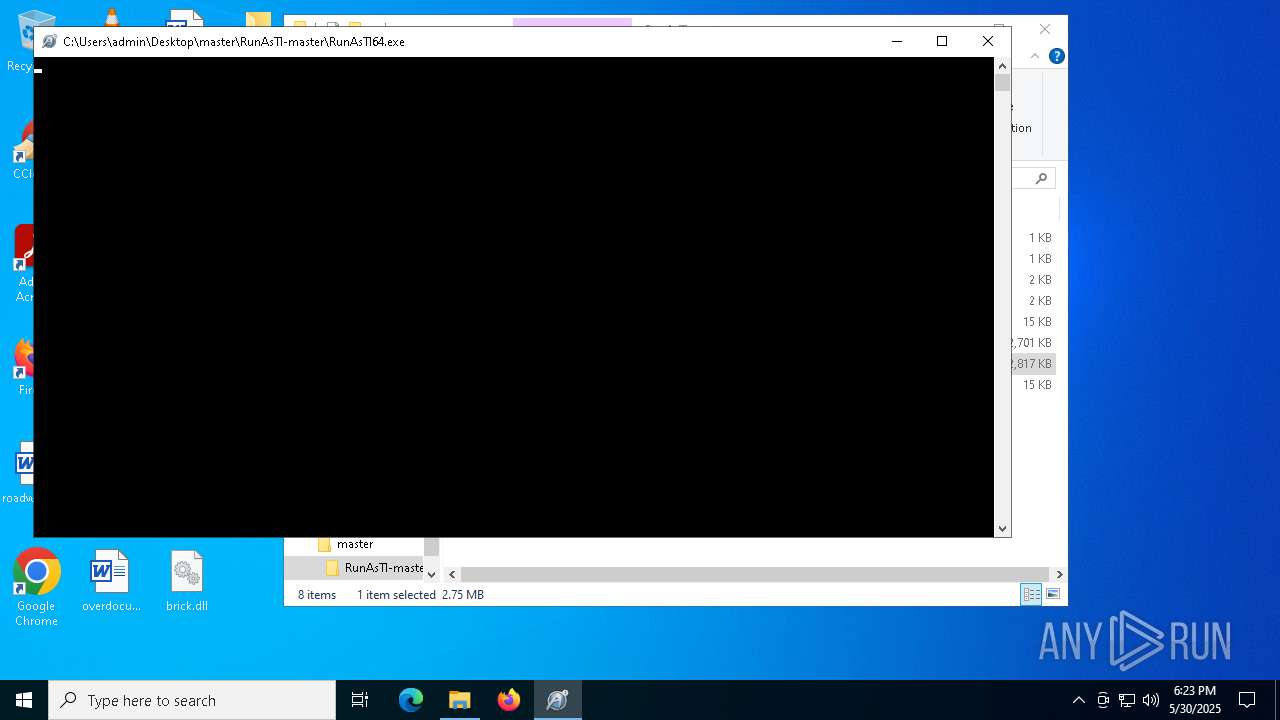
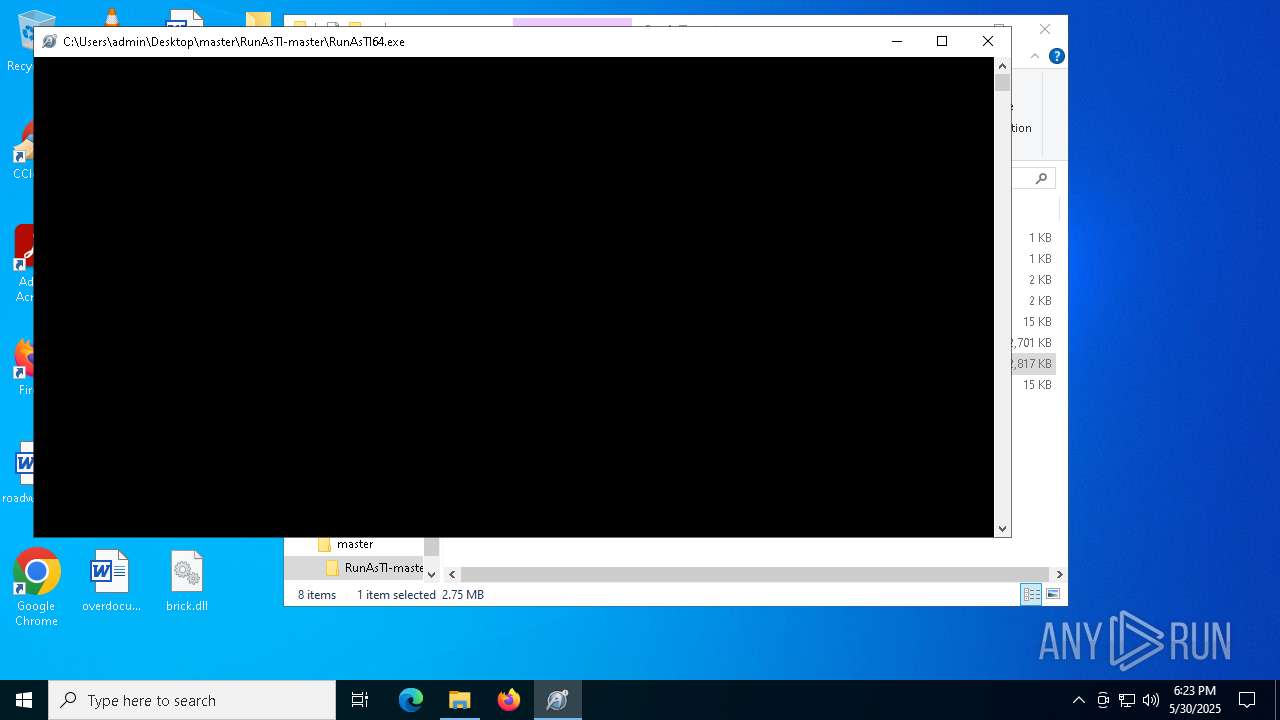
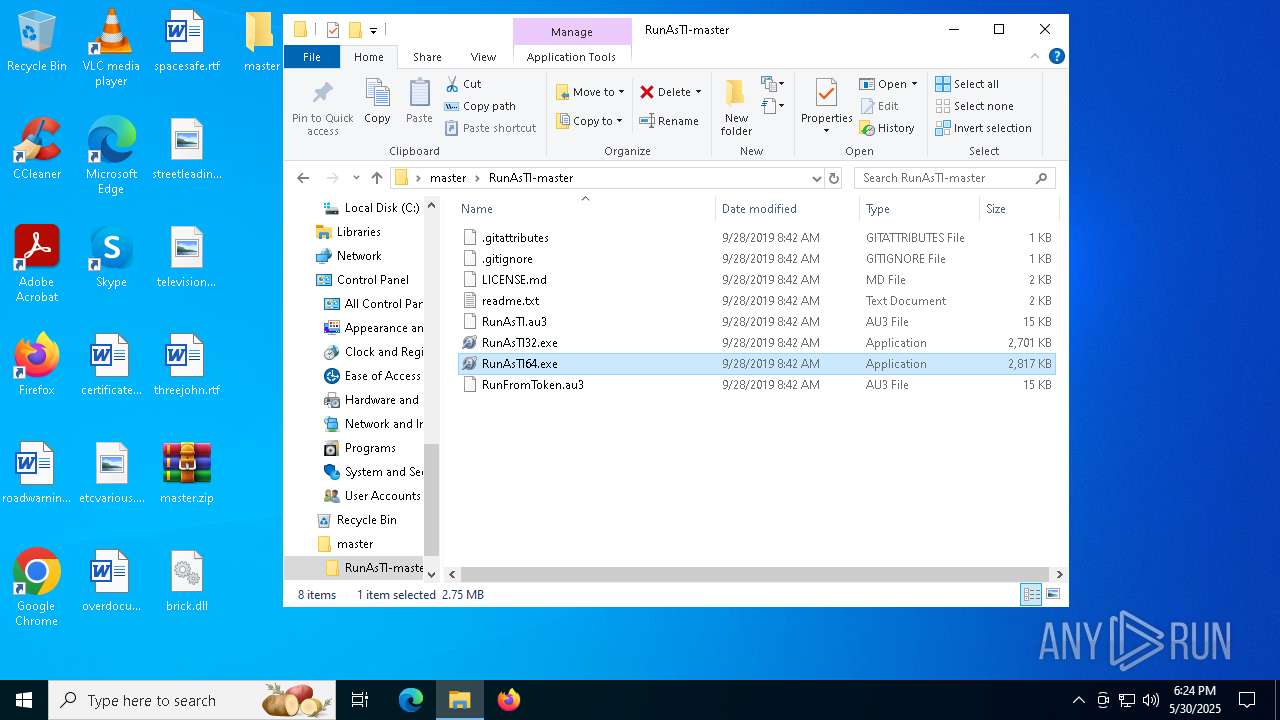
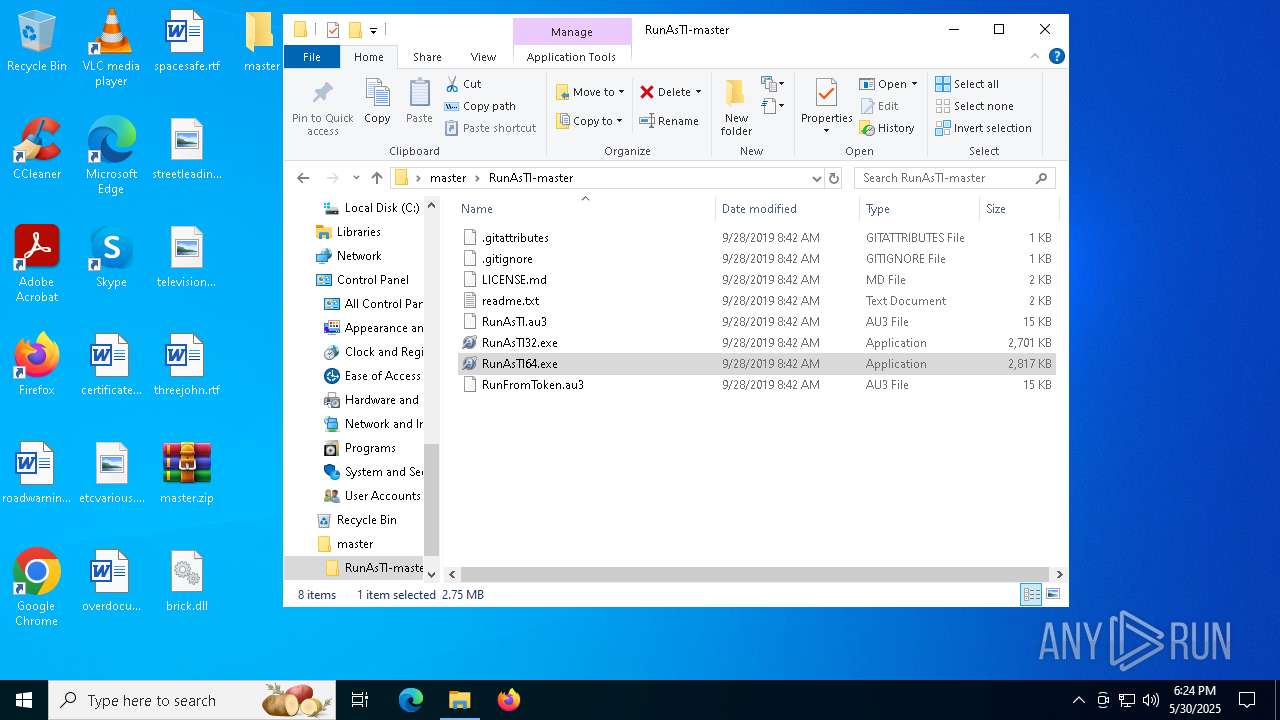
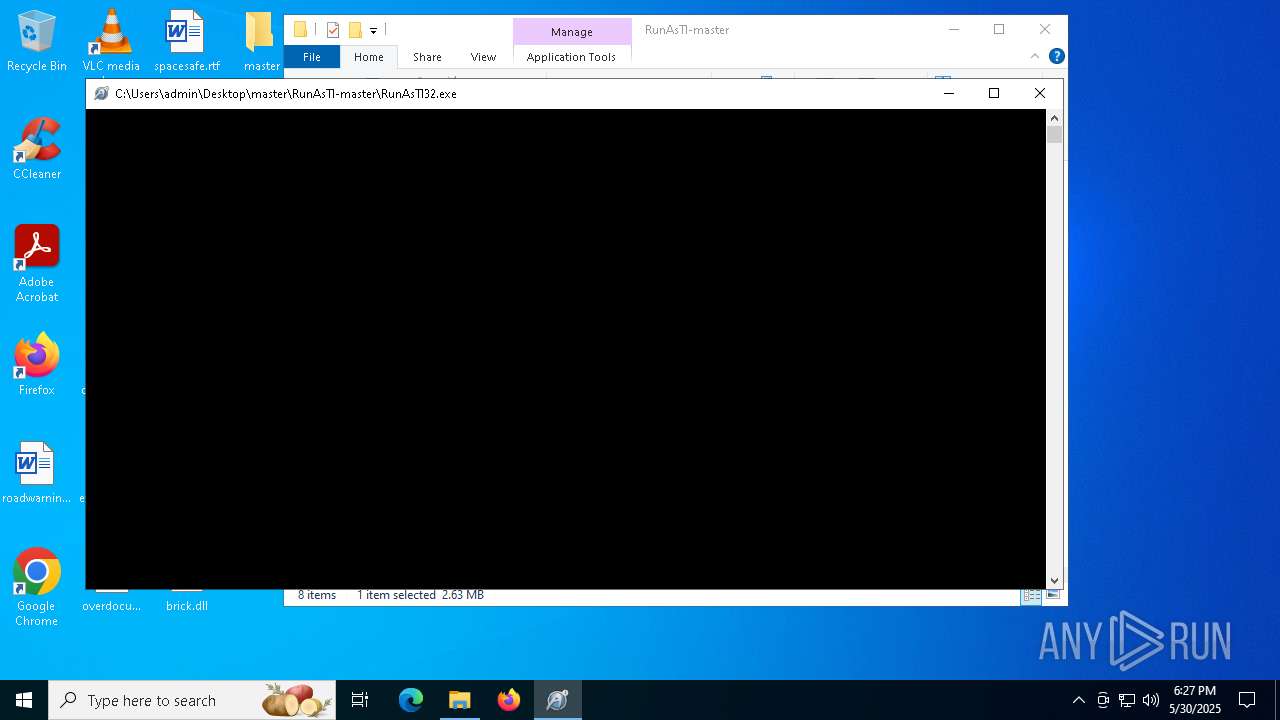
Manual execution by a user
- RunAsTI64.exe (PID: 5760)
- RunAsTI64.exe (PID: 5256)
- cmd.exe (PID: 6196)
- RunAsTI64.exe (PID: 6204)
- WinRAR.exe (PID: 2668)
- RunAsTI32.exe (PID: 6768)
- firefox.exe (PID: 928)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1176)
- WinRAR.exe (PID: 2668)
The sample compiled with english language support
- WinRAR.exe (PID: 1176)
- RunAsTI64.exe (PID: 7964)
- RunAsTI64.exe (PID: 6092)
- WinRAR.exe (PID: 2668)
Process checks computer location settings
- RunAsTI64.exe (PID: 5760)
Application launched itself
- firefox.exe (PID: 6800)
- firefox.exe (PID: 928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:09:28 01:42:02 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
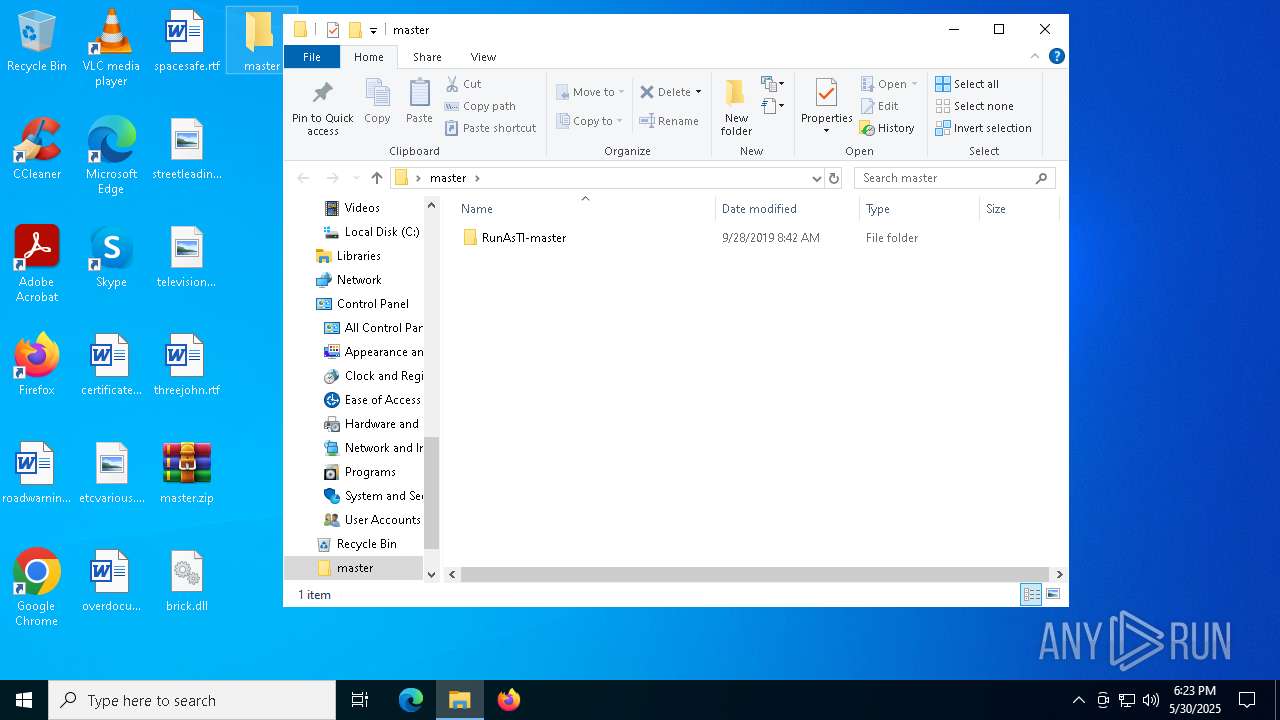
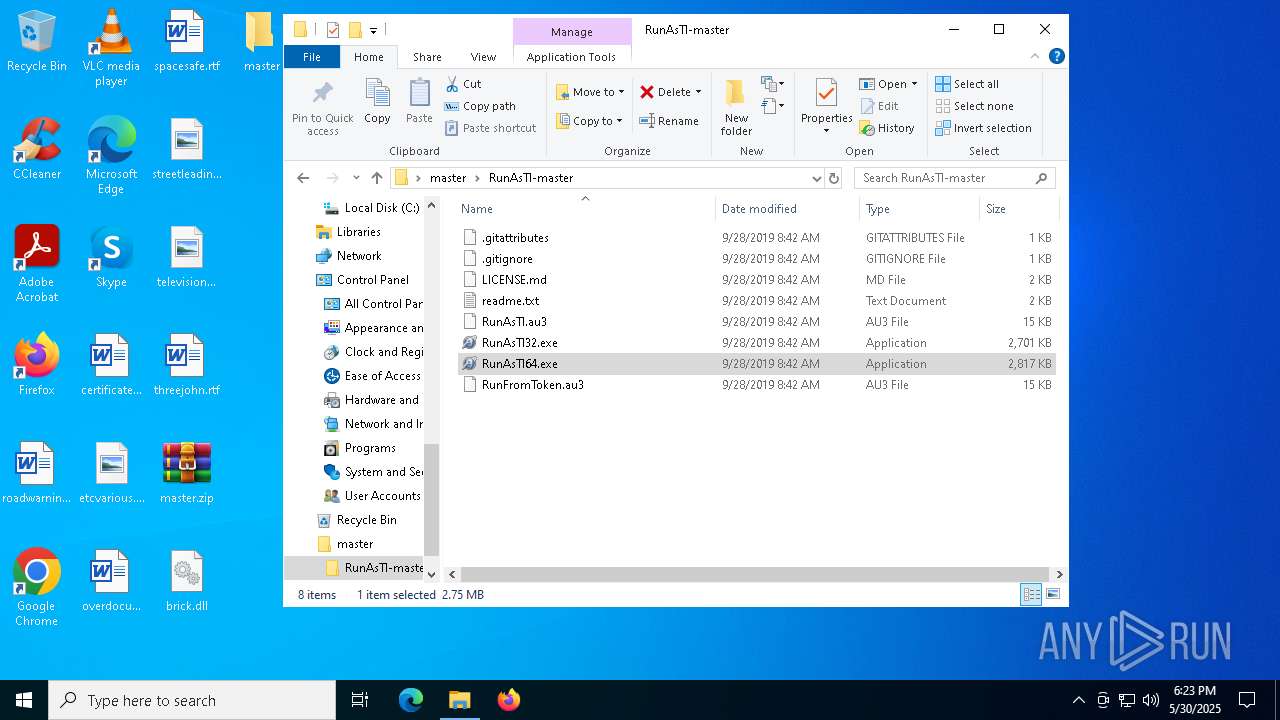
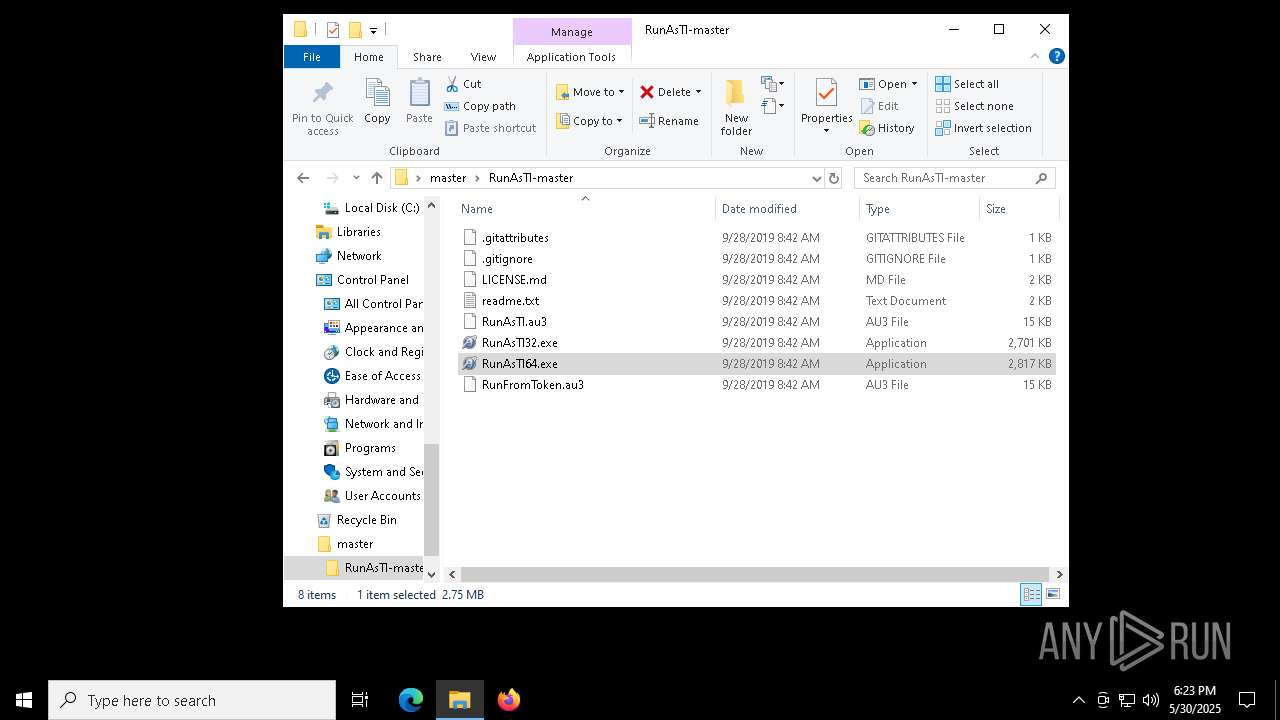
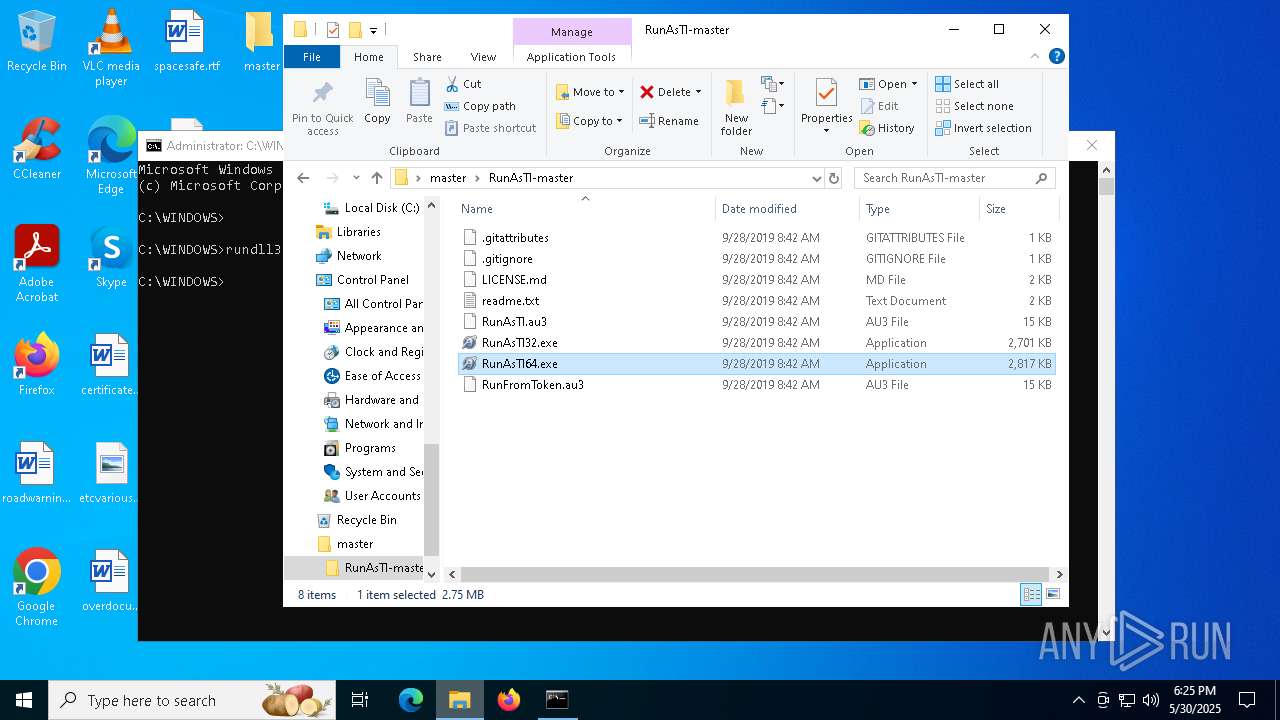
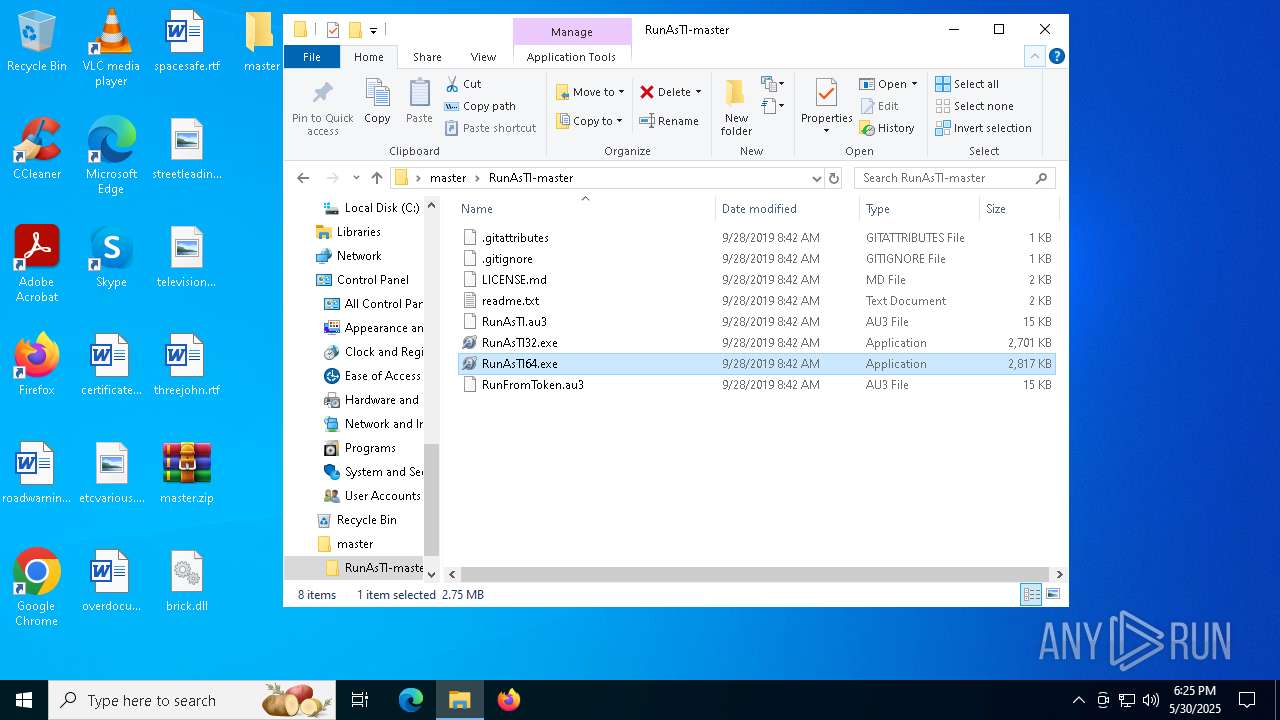
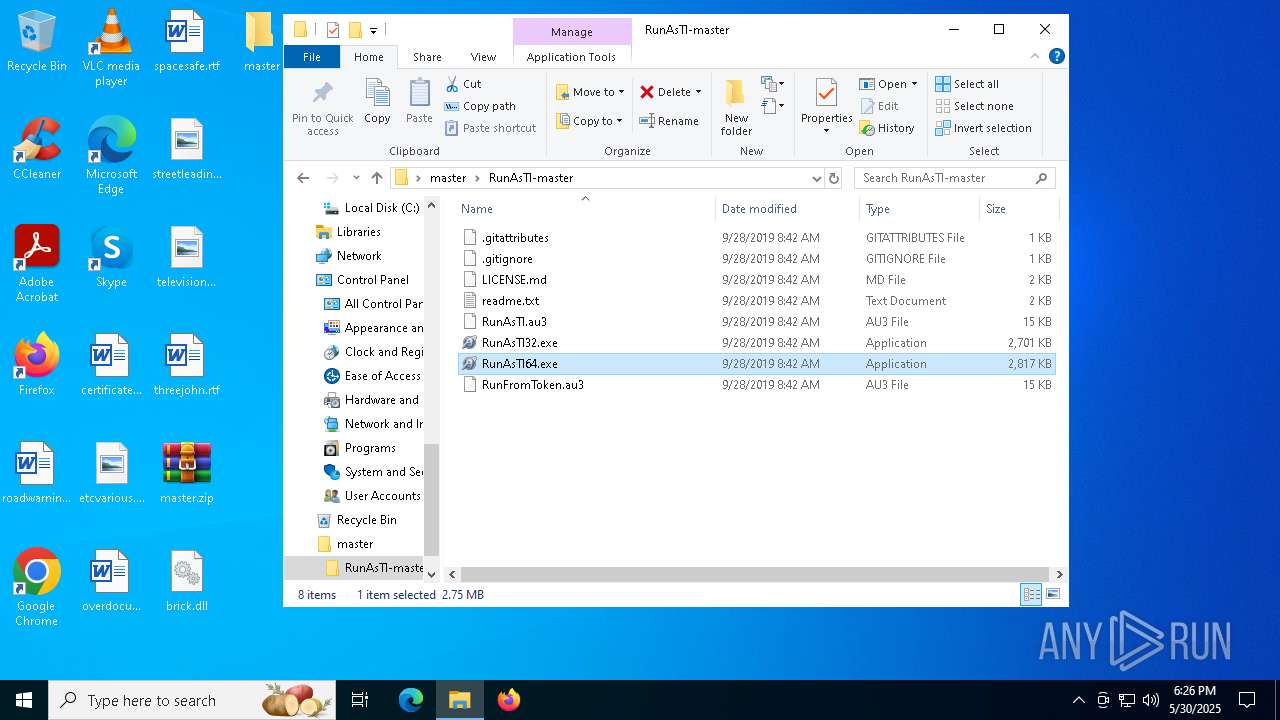
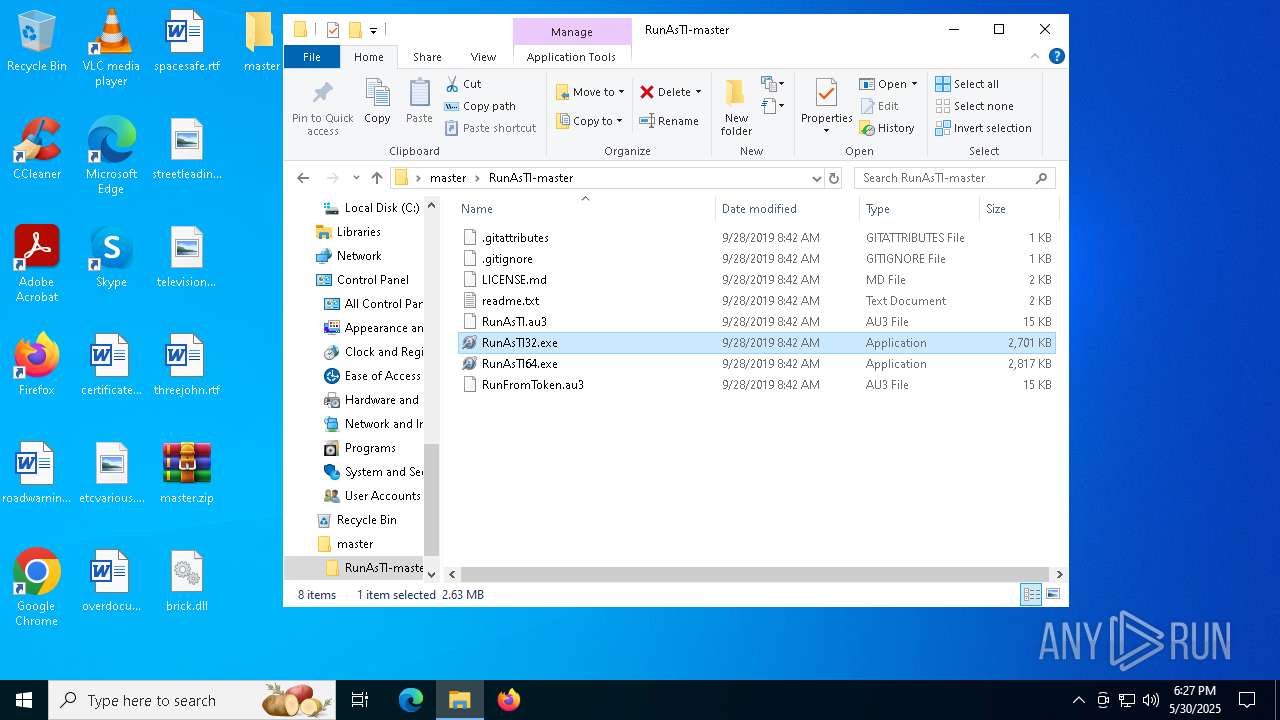
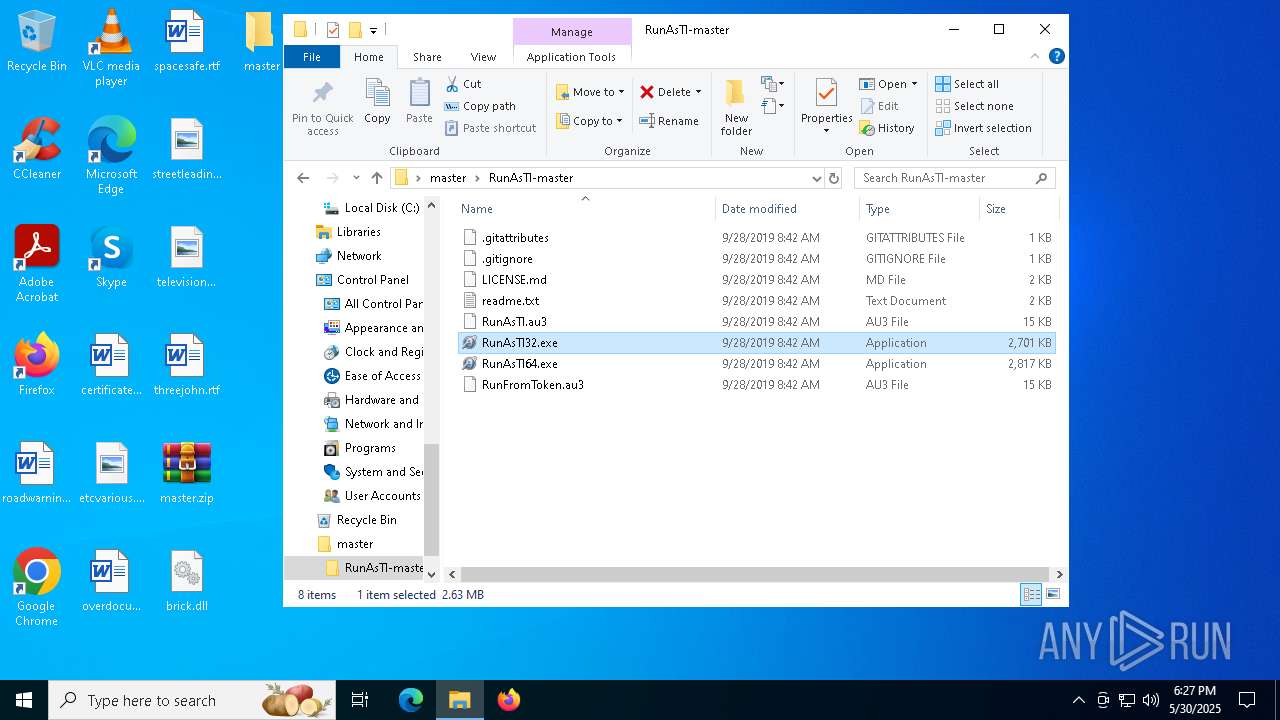
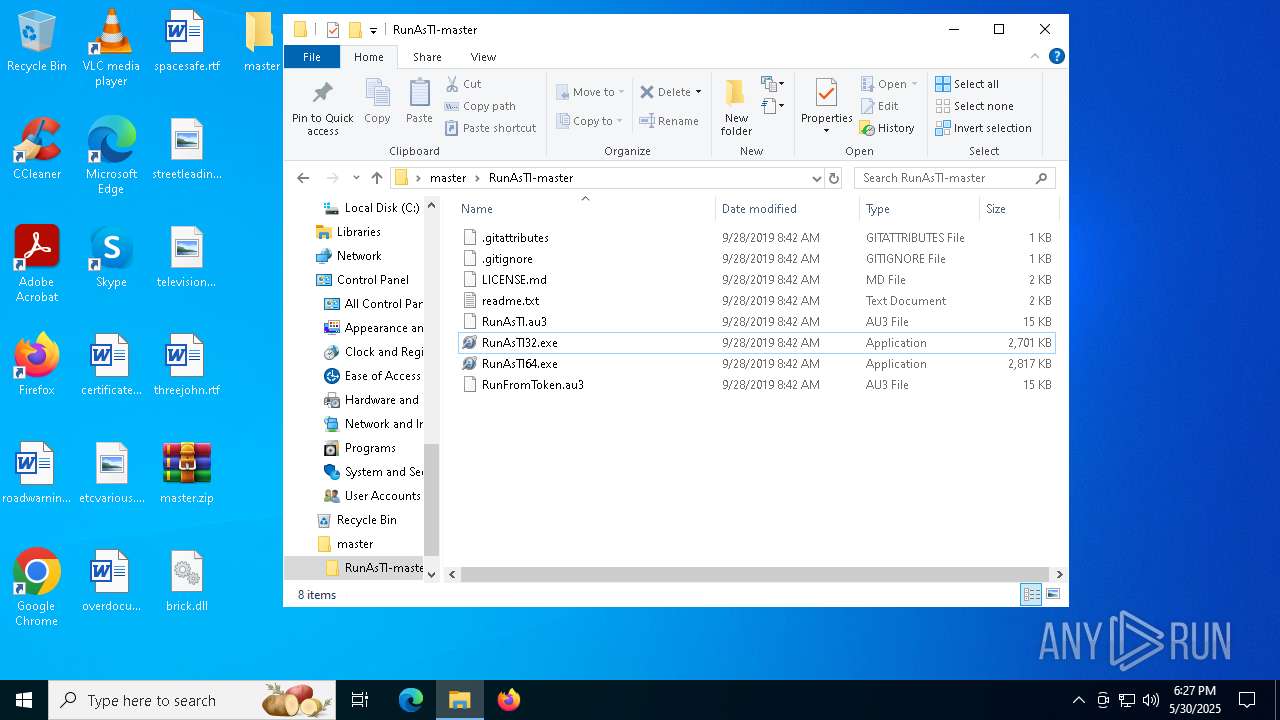
| ZipFileName: | RunAsTI-master/ |
Total processes
414
Monitored processes
63
Malicious processes
0
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 800 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | shutdown.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 928 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1112 | cmd.exe | C:\Windows\System32\cmd.exe | — | RunFromToken64.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | RunAsTI64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1176 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\master.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1260 | rundll32.exe C:\Users\admin\Desktop\brick.dll,nothing | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1888 -parentBuildID 20240213221259 -prefsHandle 1816 -prefMapHandle 1808 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {cf362783-c376-4cea-859f-59437e70edca} 6800 "\\.\pipe\gecko-crash-server-pipe.6800" 27cfbfbd110 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 1524 | "shutdown" /r /t 0 | C:\Windows\System32\shutdown.exe | — | rundll32.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Shutdown and Annotation Tool Exit code: 1115 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1592 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | shutdown.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | C:\Users\admin\AppData\Local\Temp\RunFromToken64.exe trustedinstaller.exe 5 cmd.exe | C:\Users\admin\AppData\Local\Temp\RunFromToken64.exe | RunAsTI64.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: Start a program based on the privileges from a given process' token Exit code: 0 Version: 1.0.0.3 Modules
| |||||||||||||||
Total events
30 050
Read events
29 786
Write events
239
Delete events
25
Modification events
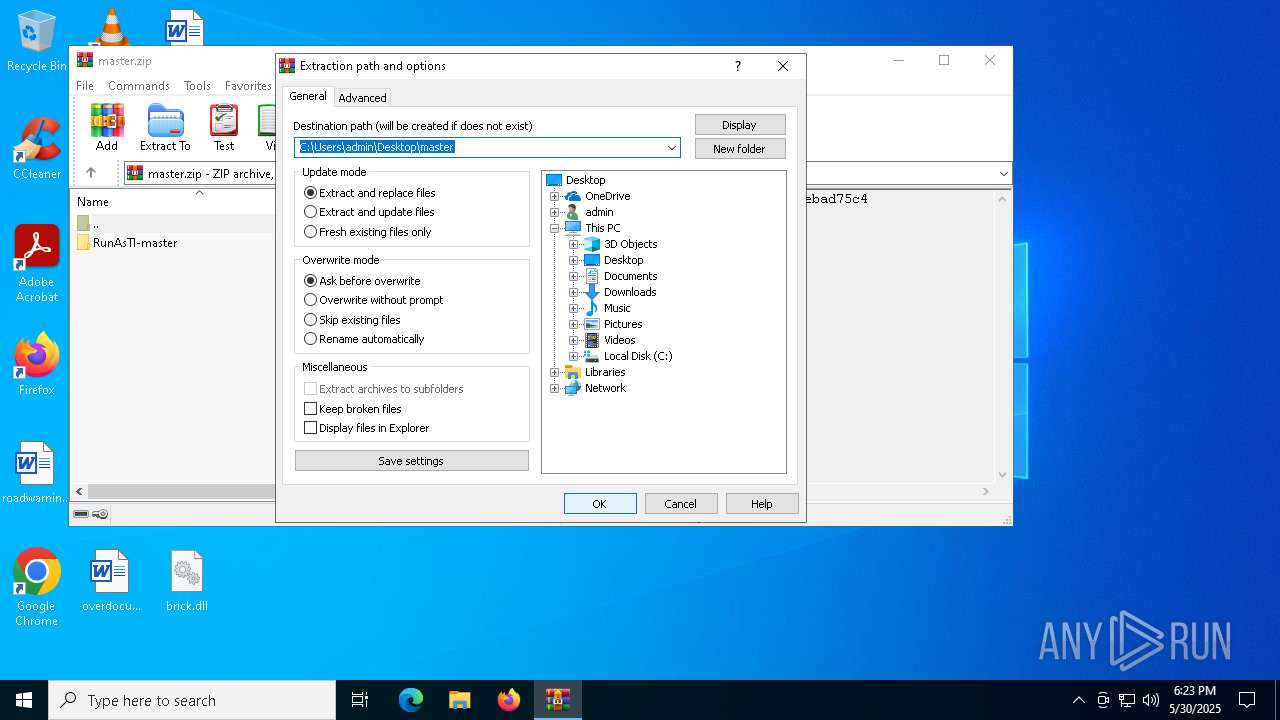
| (PID) Process: | (1176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\master.zip | |||
| (PID) Process: | (1176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (1176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
218
Suspicious files
160
Text files
233
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
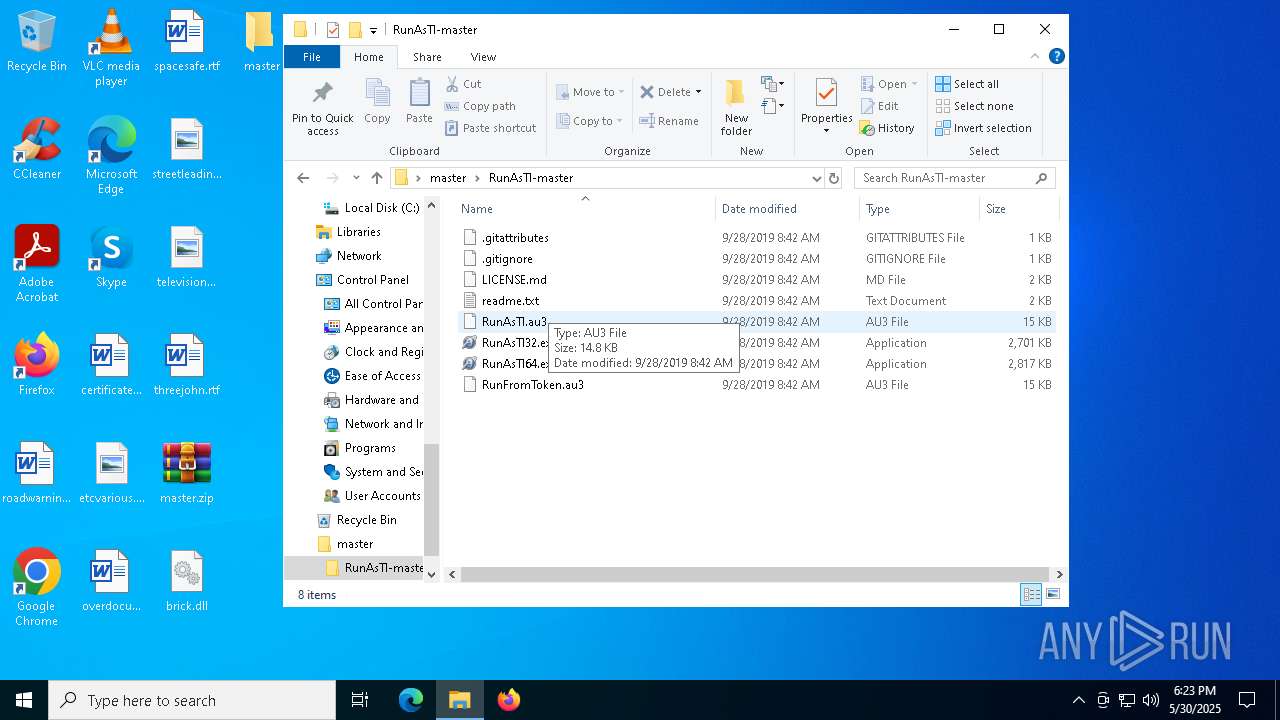
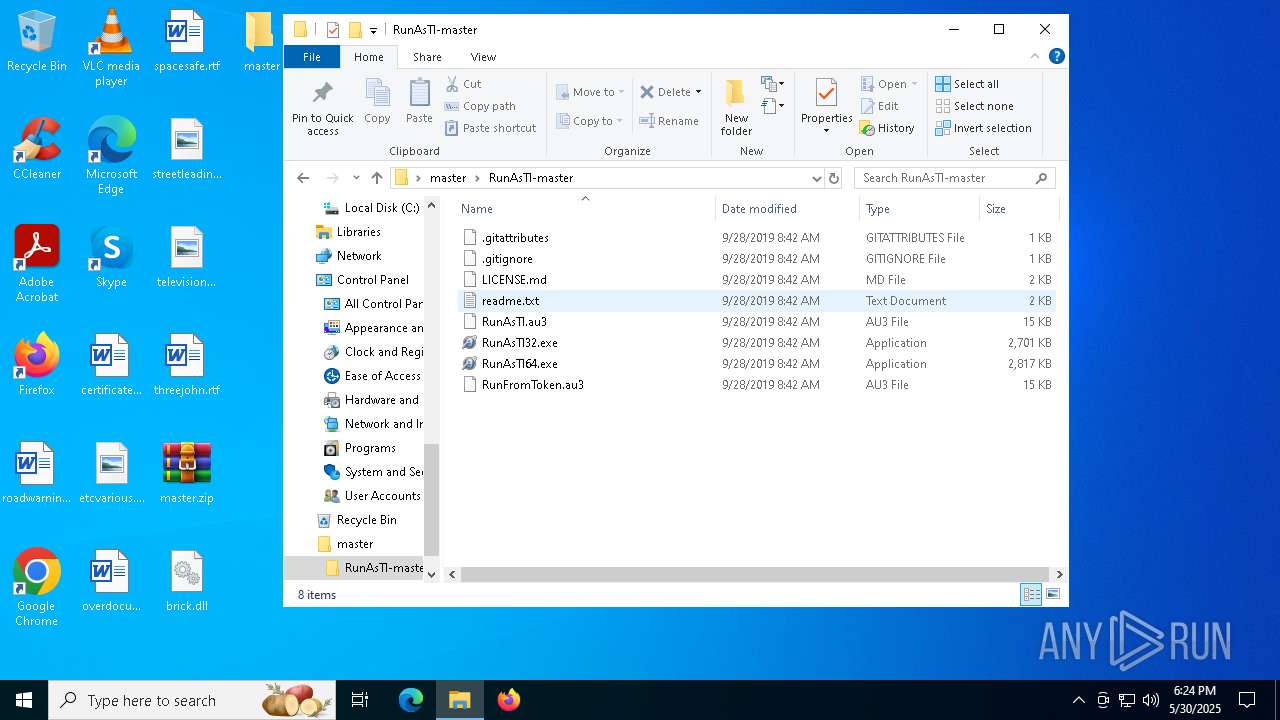
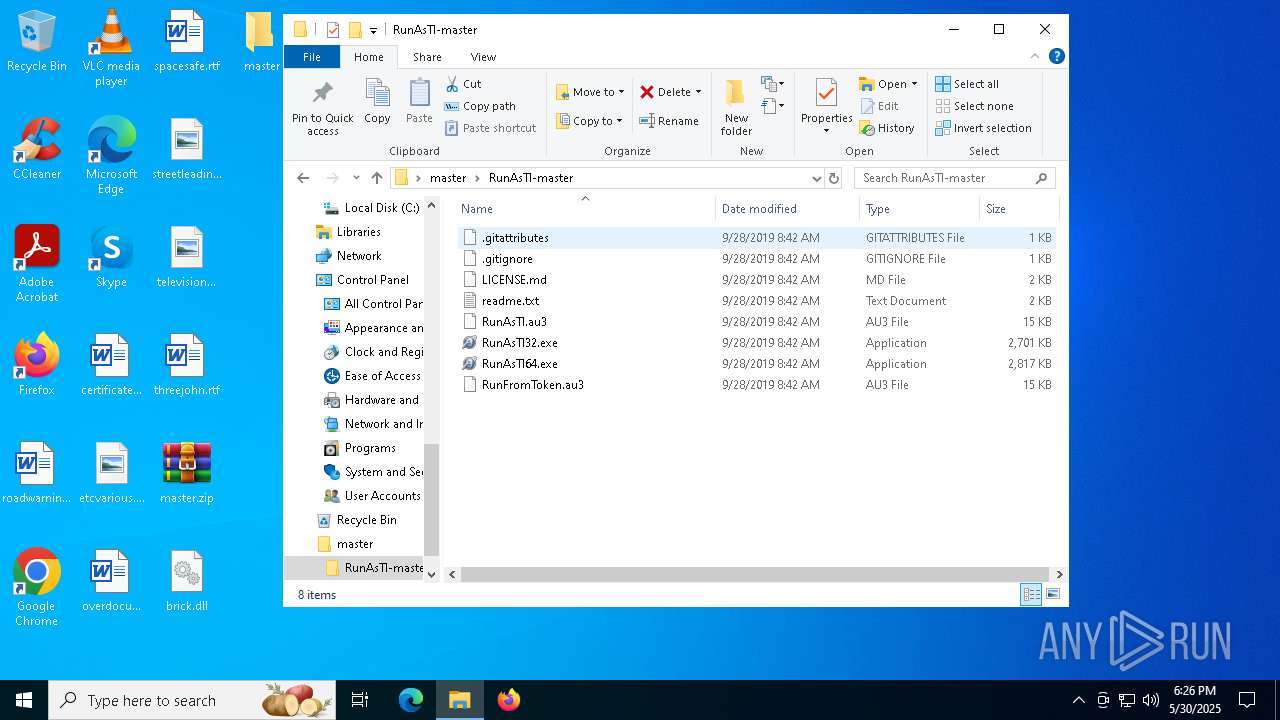
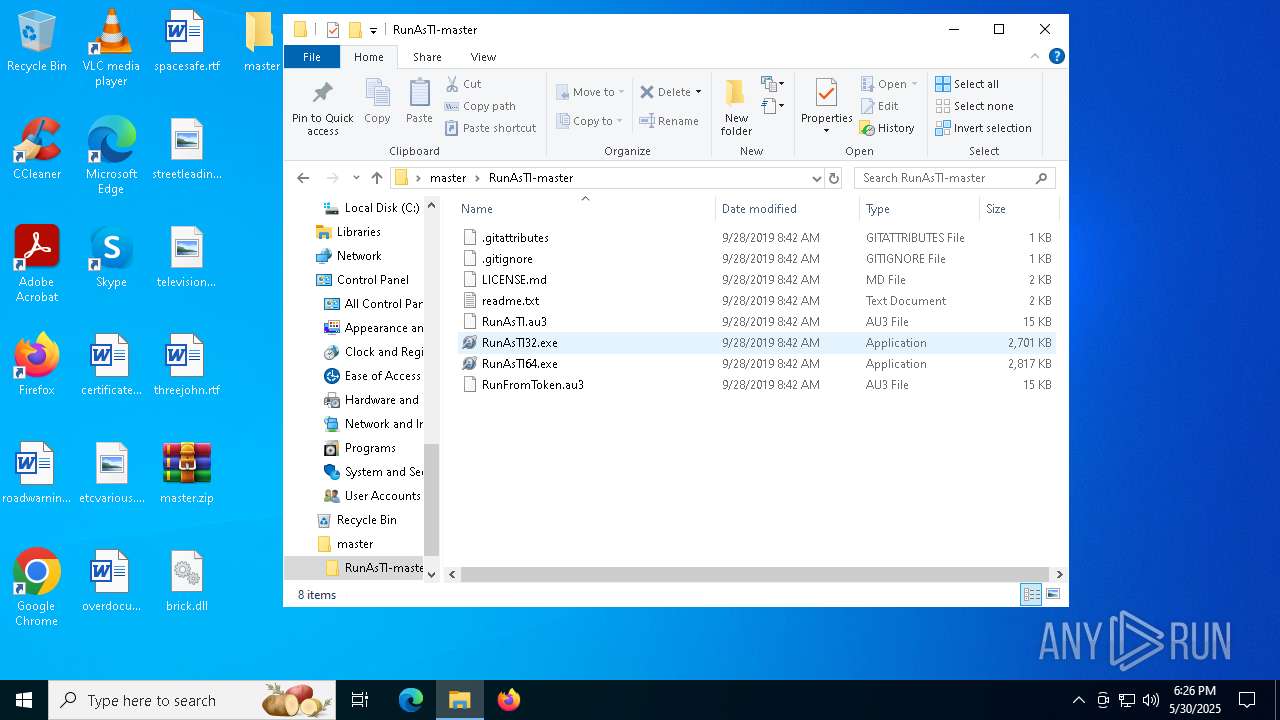
| 1176 | WinRAR.exe | C:\Users\admin\Desktop\master\RunAsTI-master\LICENSE.md | text | |
MD5:0CC0F65A3B9749B2070F2CBDFB426336 | SHA256:54E72028E80627A0687E9DF6947B1100EFB0B68E7824486A8D8E7F2632B5066B | |||
| 1176 | WinRAR.exe | C:\Users\admin\Desktop\master\RunAsTI-master\.gitattributes | text | |
MD5:C4F364B364A2AC980A1DBF9D9A73A0E1 | SHA256:DCC4E04A9952FF446B9D78C624D80379B0F20F5817A89B9B2B1AB8B55B82FD52 | |||
| 1176 | WinRAR.exe | C:\Users\admin\Desktop\master\RunAsTI-master\RunAsTI64.exe | executable | |
MD5:9B9F954F38F4987F1735F2A4AE15DDE0 | SHA256:BF365D7D5BC3076E5A7F41BB9F0B9E9BEB58AE900BFFCB3BBB10B575C08D66DB | |||
| 8140 | rundll32.exe | C:\Windows\System32\umpo-overrides.dll | executable | |
MD5:C5ABCA4CBEEC2C289BA71AE3994581B1 | SHA256:024CE8922E468C4F66E15BC4BED96F7BEB3541BD553B3815AFA45A1BA9900DD1 | |||
| 1176 | WinRAR.exe | C:\Users\admin\Desktop\master\RunAsTI-master\RunAsTI.au3 | text | |
MD5:3E16493C4DE00472602DE91E48986CB9 | SHA256:6B5ED8AB26C41D00B731BA13FD24681EEFBB0F0966D11CD94158BCFF38F07374 | |||
| 1176 | WinRAR.exe | C:\Users\admin\Desktop\master\RunAsTI-master\.gitignore | text | |
MD5:69E7DD8DBF58A60418B04DDB157AD1A5 | SHA256:A5E54048202DEF346FCD461496AAAF0B42D313153BEE1D54F46242E7B4ED9D20 | |||
| 8140 | rundll32.exe | C:\Windows\System32\directxdatabasehelper.dll | executable | |
MD5:C5ABCA4CBEEC2C289BA71AE3994581B1 | SHA256:024CE8922E468C4F66E15BC4BED96F7BEB3541BD553B3815AFA45A1BA9900DD1 | |||
| 8140 | rundll32.exe | C:\Windows\System32\hvhostsvc.dll | executable | |
MD5:C5ABCA4CBEEC2C289BA71AE3994581B1 | SHA256:024CE8922E468C4F66E15BC4BED96F7BEB3541BD553B3815AFA45A1BA9900DD1 | |||
| 7964 | RunAsTI64.exe | C:\Users\admin\AppData\Local\Temp\RunFromToken64.exe | executable | |
MD5:64746CBC92ABBB261097A7FA6EECD278 | SHA256:2E62931ADA755F4F09E4F7ED05C21C6681FF011992458F4344FEDDD9FCDFC960 | |||
| 8140 | rundll32.exe | C:\Windows\System32\pfclient.dll | executable | |
MD5:C5ABCA4CBEEC2C289BA71AE3994581B1 | SHA256:024CE8922E468C4F66E15BC4BED96F7BEB3541BD553B3815AFA45A1BA9900DD1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
111
DNS requests
97
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5140 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5140 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5116 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5140 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5140 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5140 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6008 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4608 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.31.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4608 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |