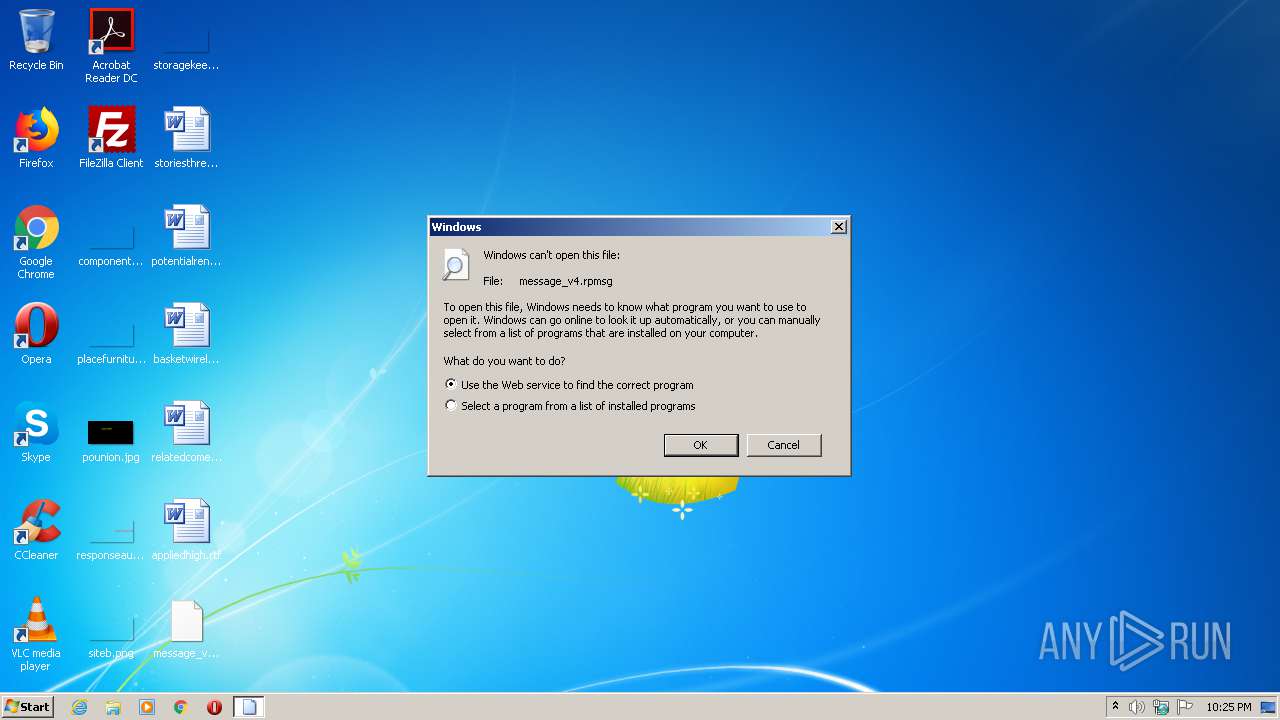
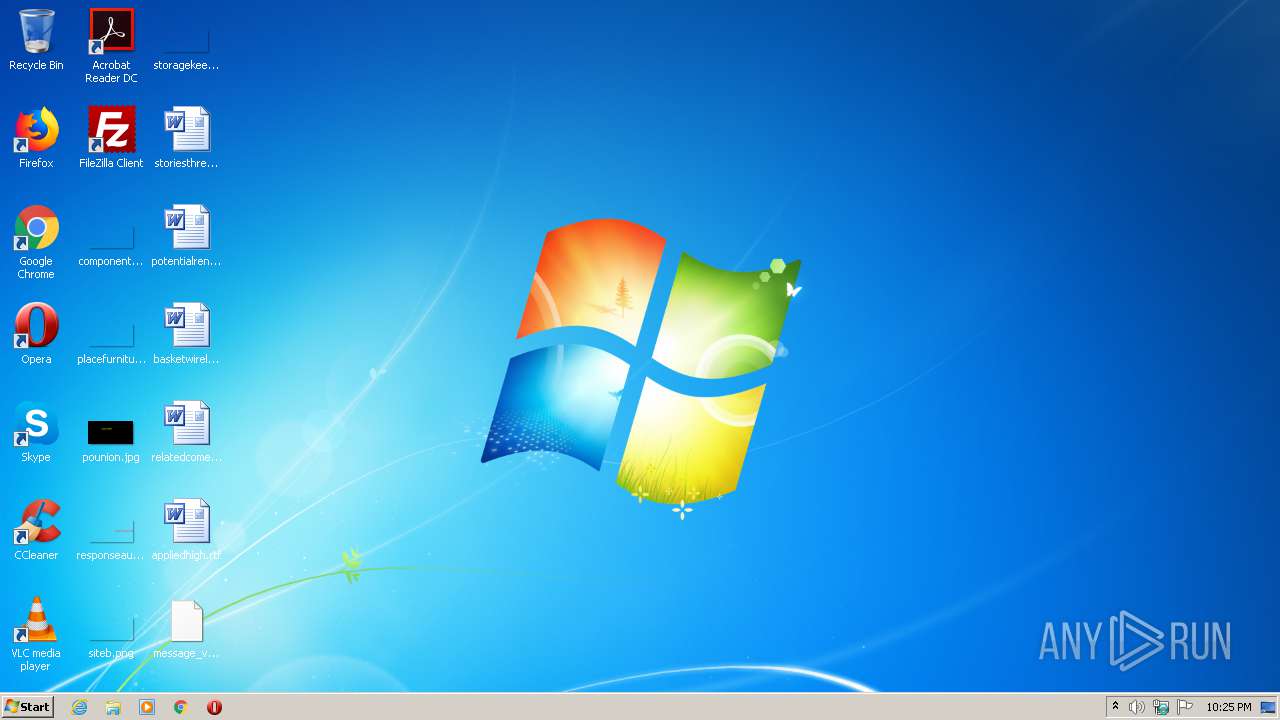
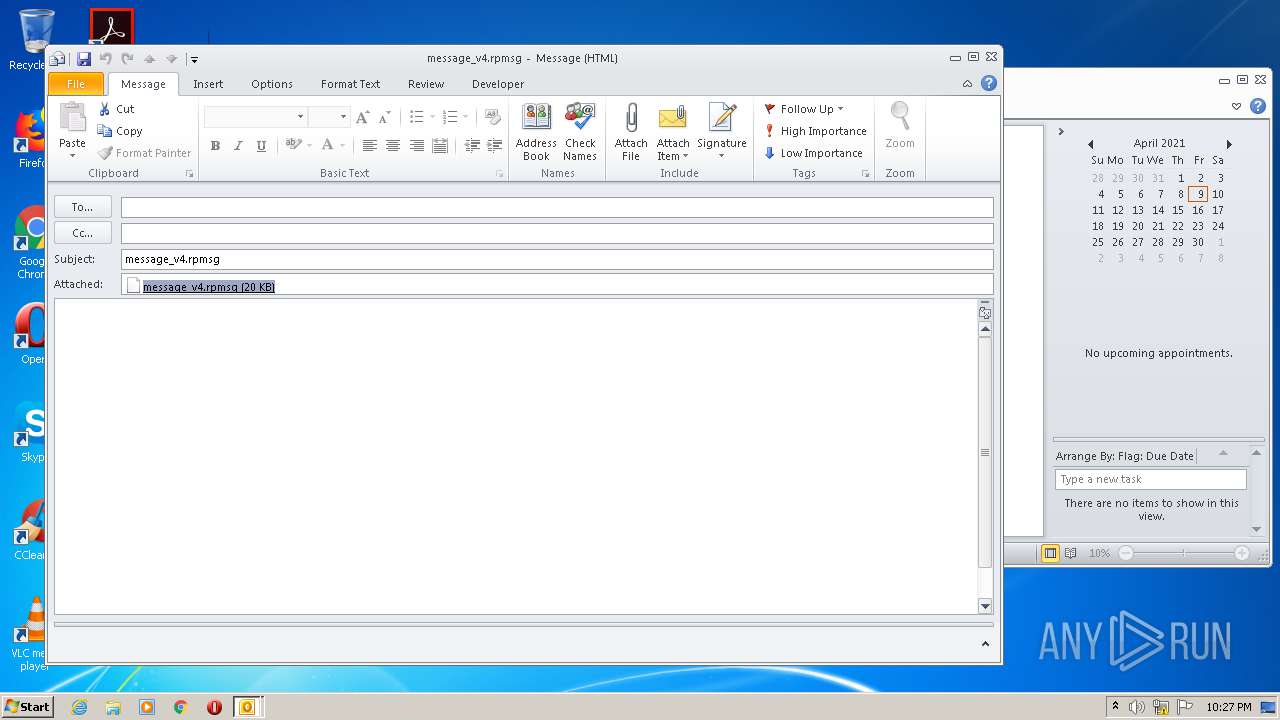
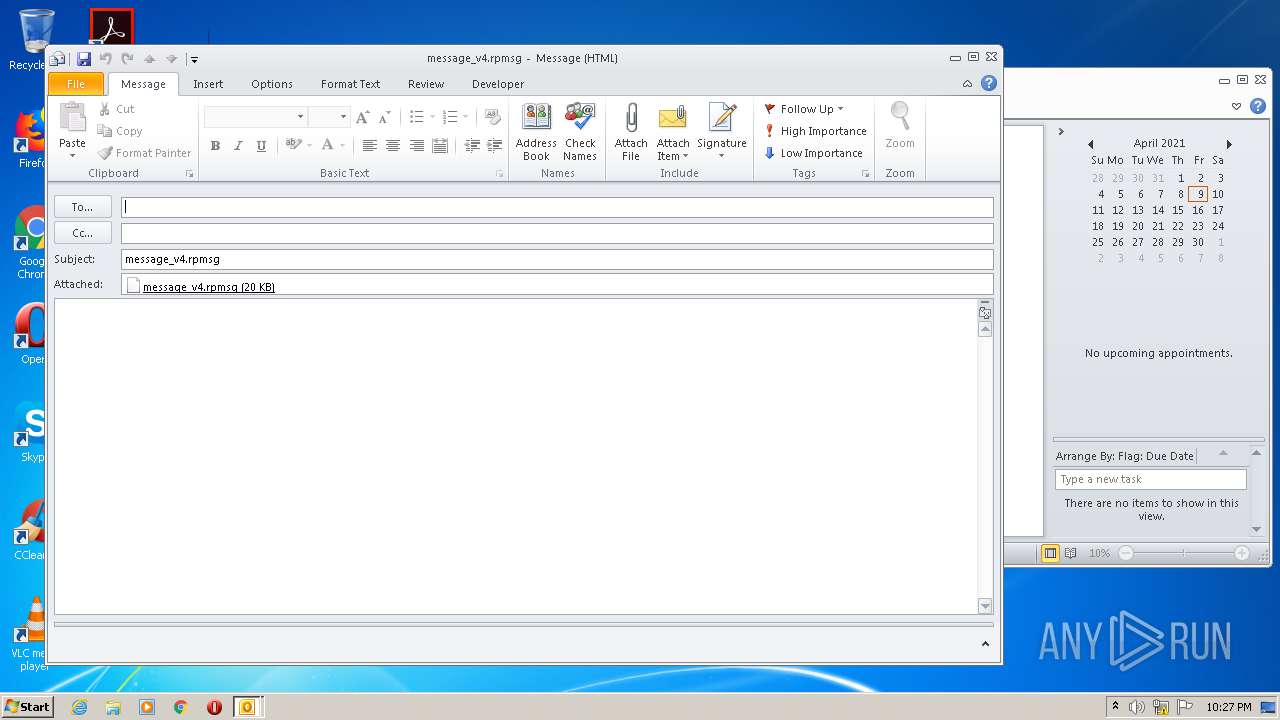
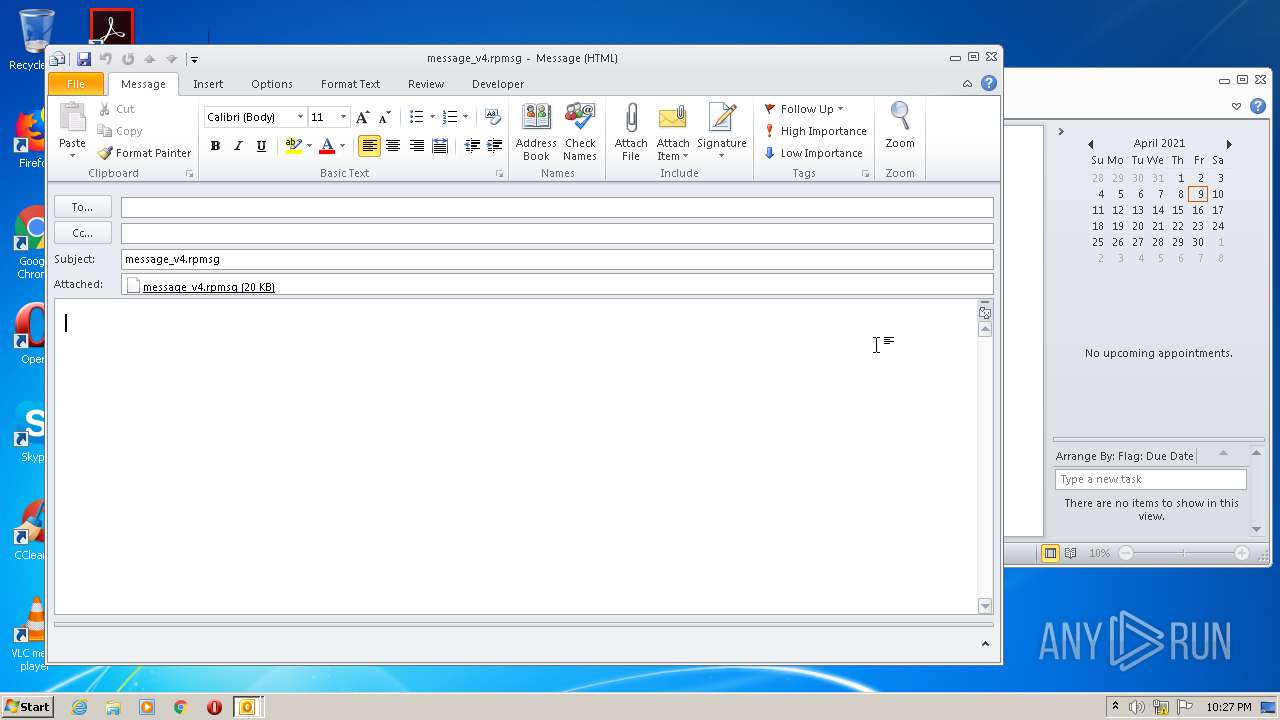
| File name: | message_v4.rpmsg |
| Full analysis: | https://app.any.run/tasks/7f3f0ef6-dca4-4b4d-9d37-633a2d25b229 |
| Verdict: | Malicious activity |
| Analysis date: | April 09, 2021, 21:25:19 |
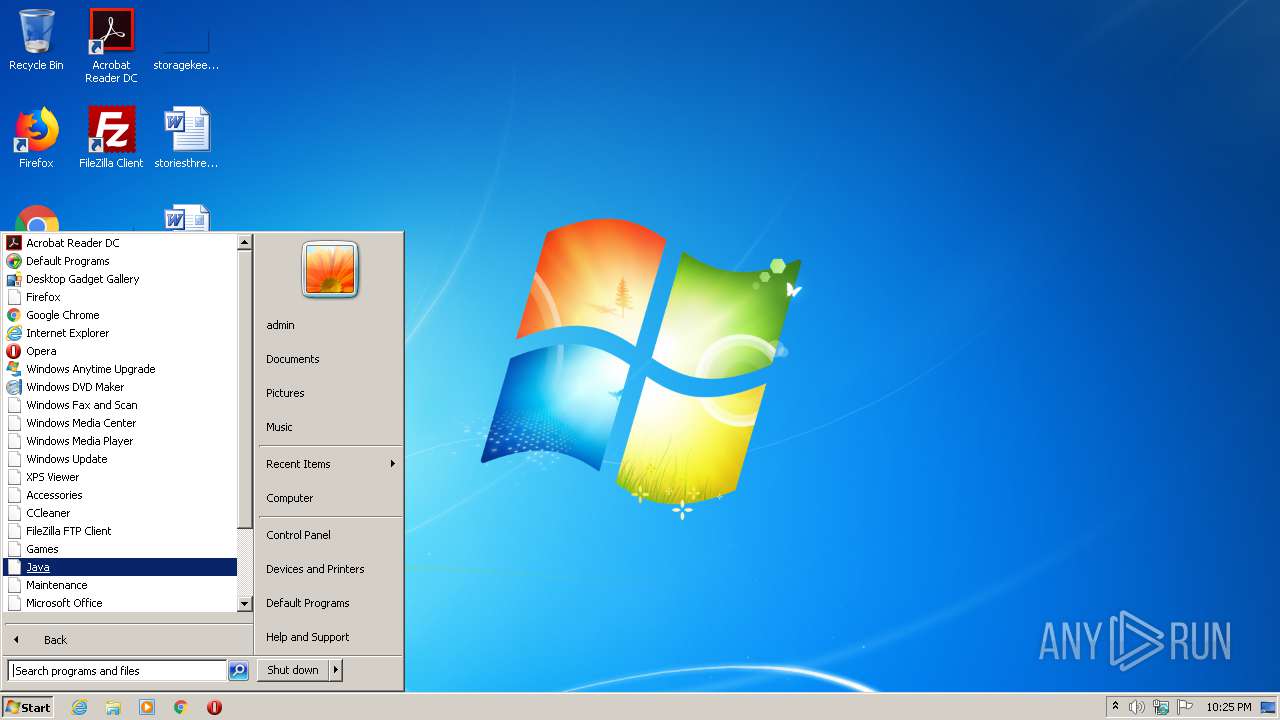
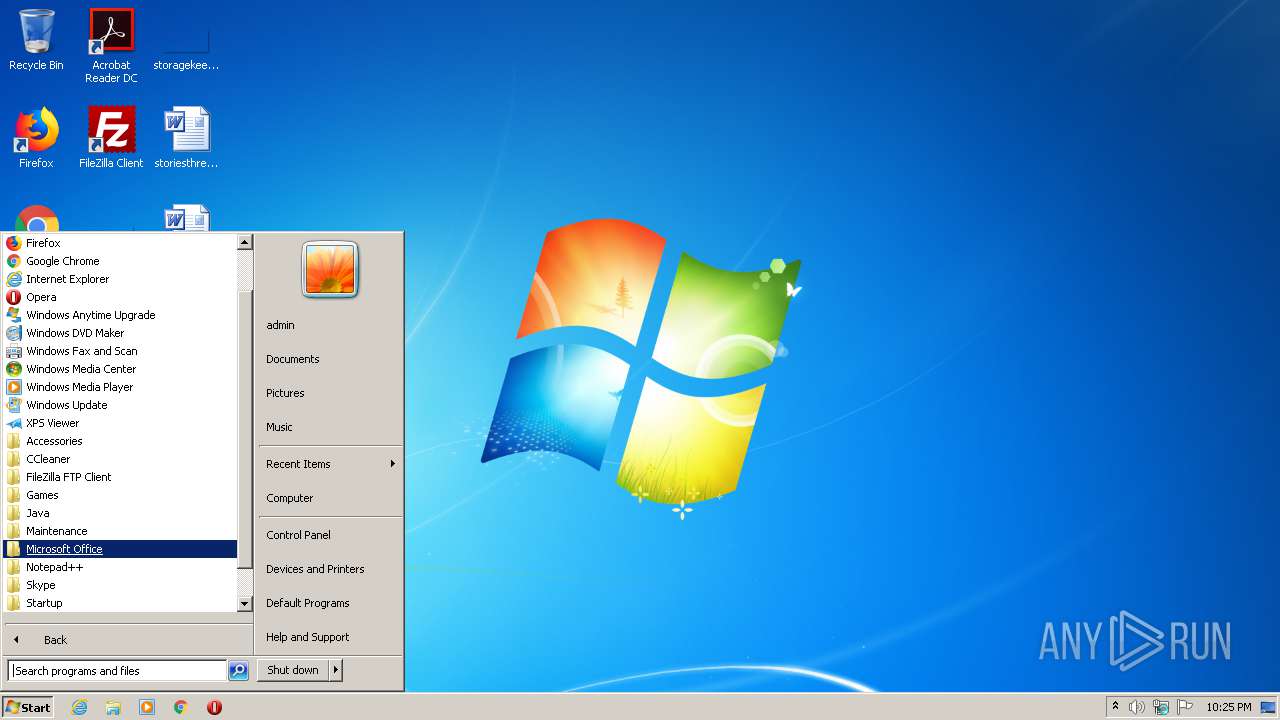
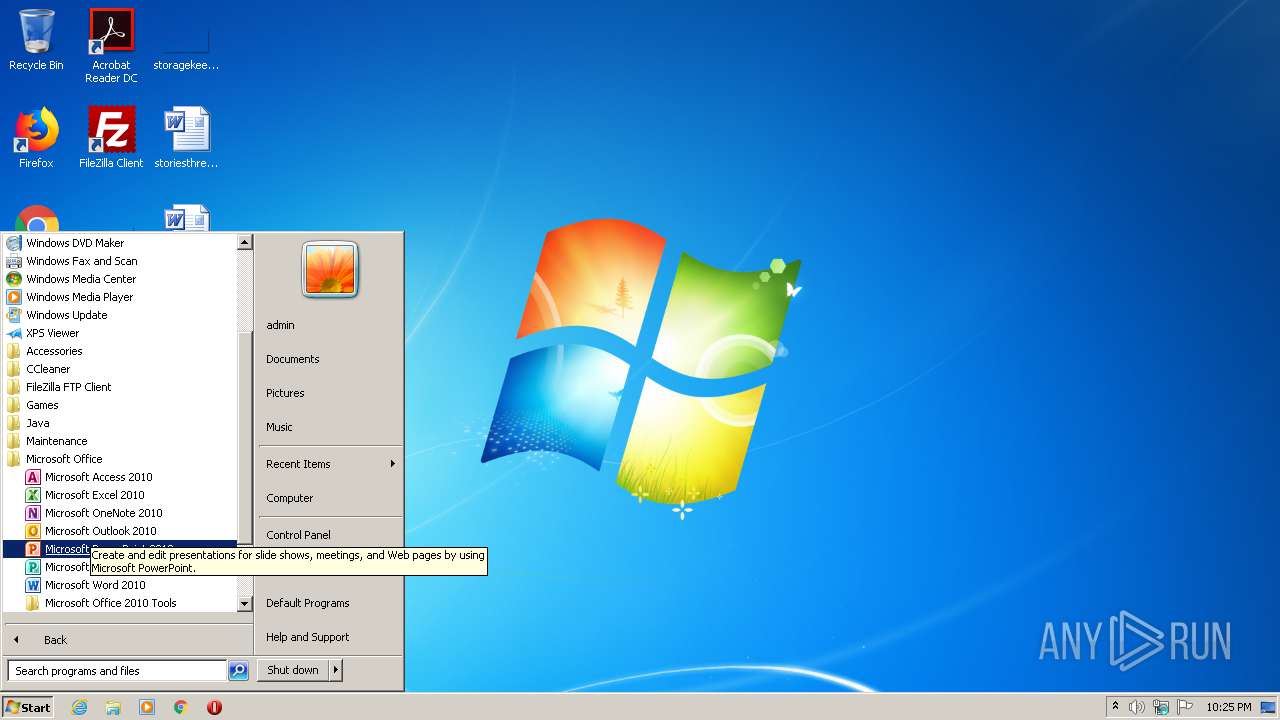
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | E2697F4337C4C913B401252BC11EE7DA |
| SHA1: | F30B802429CF7588E2328D4577489BD0F5A41899 |
| SHA256: | A8205378FAB07B036B33D1C88E8FB3DB5E9943B67D32CDE8A788545B513DB355 |
| SSDEEP: | 384:vGNSoqVZywcQR6JZSXszge8fWMVJX0OB6Nd+jWV2hj:PoqOeo8fWMVJXnB6NdRi |
MALICIOUS
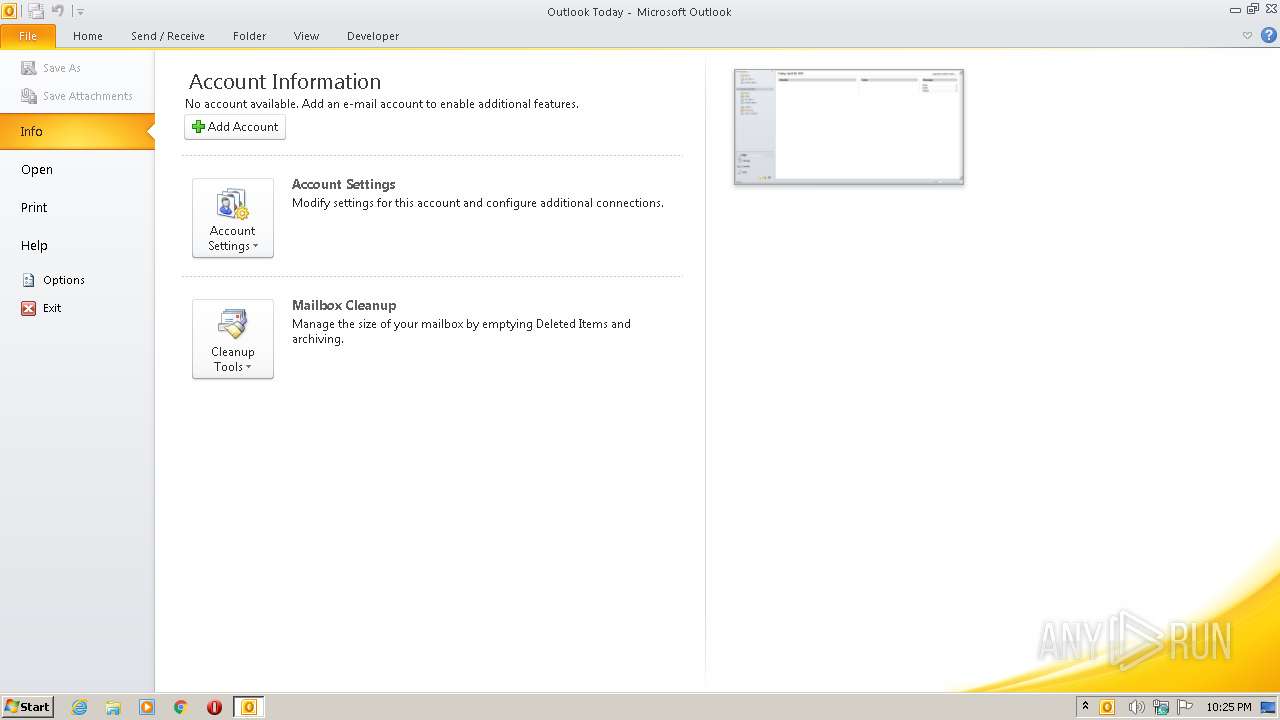
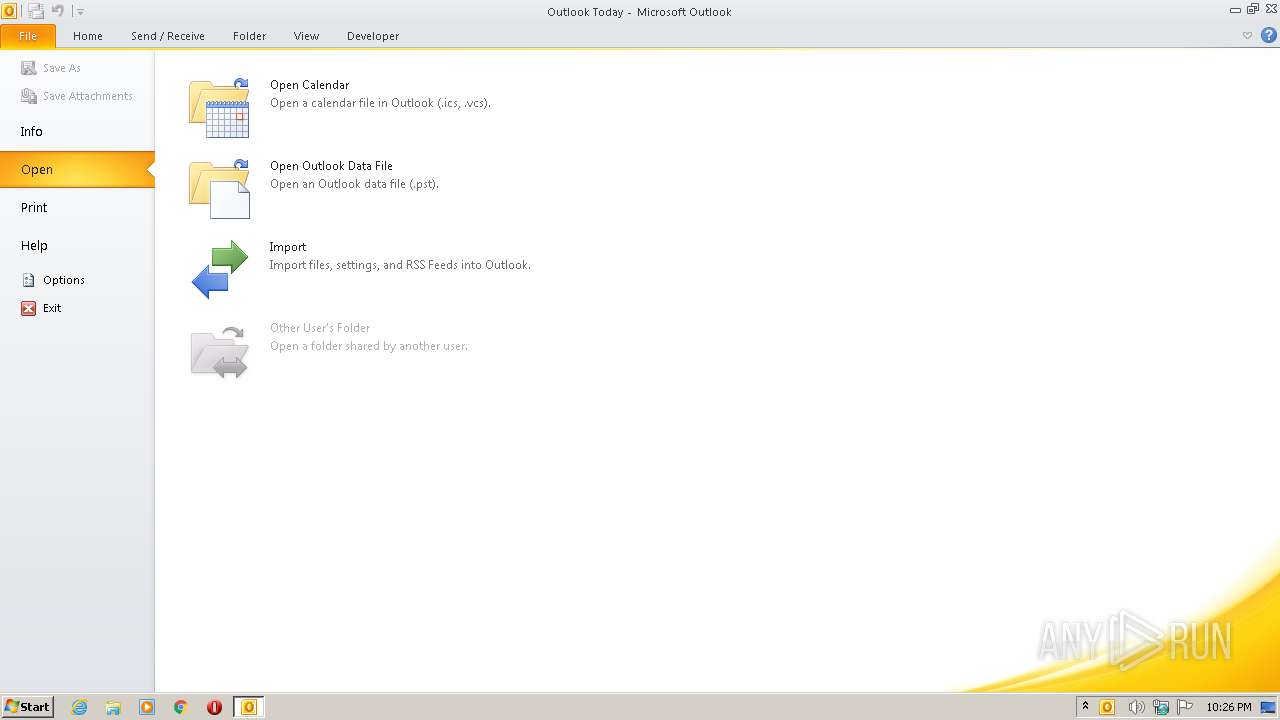
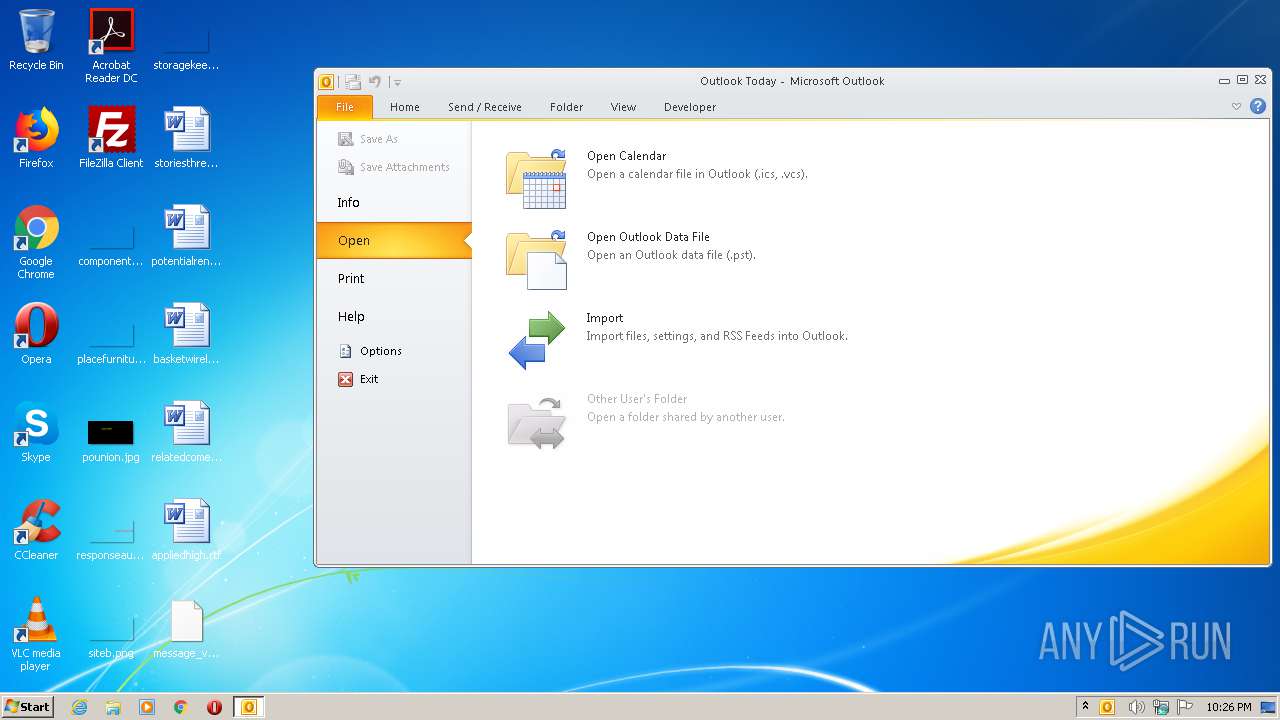
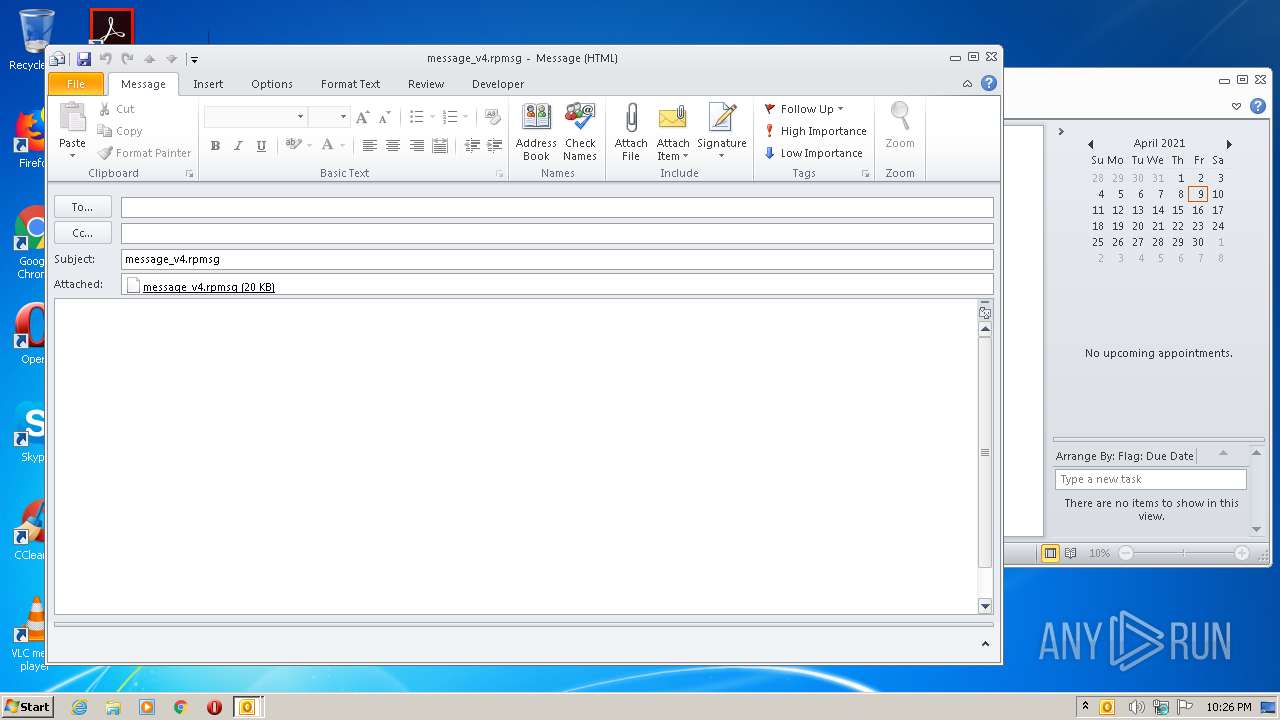
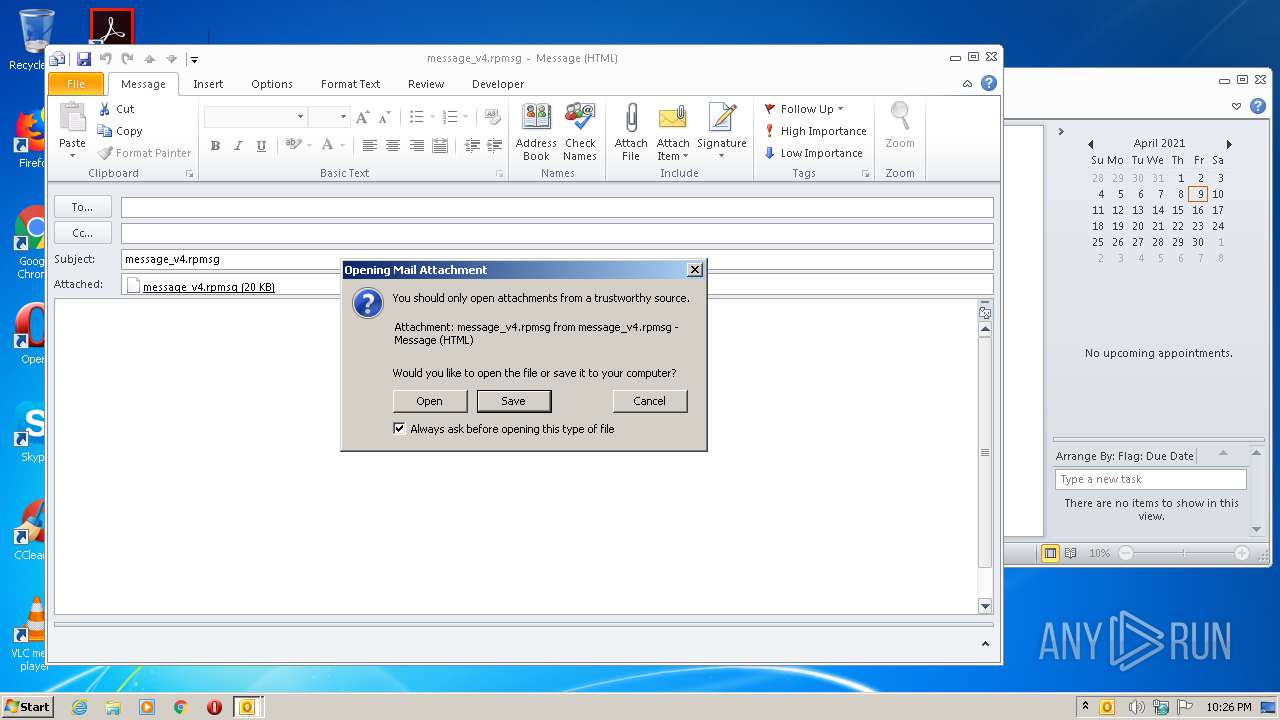
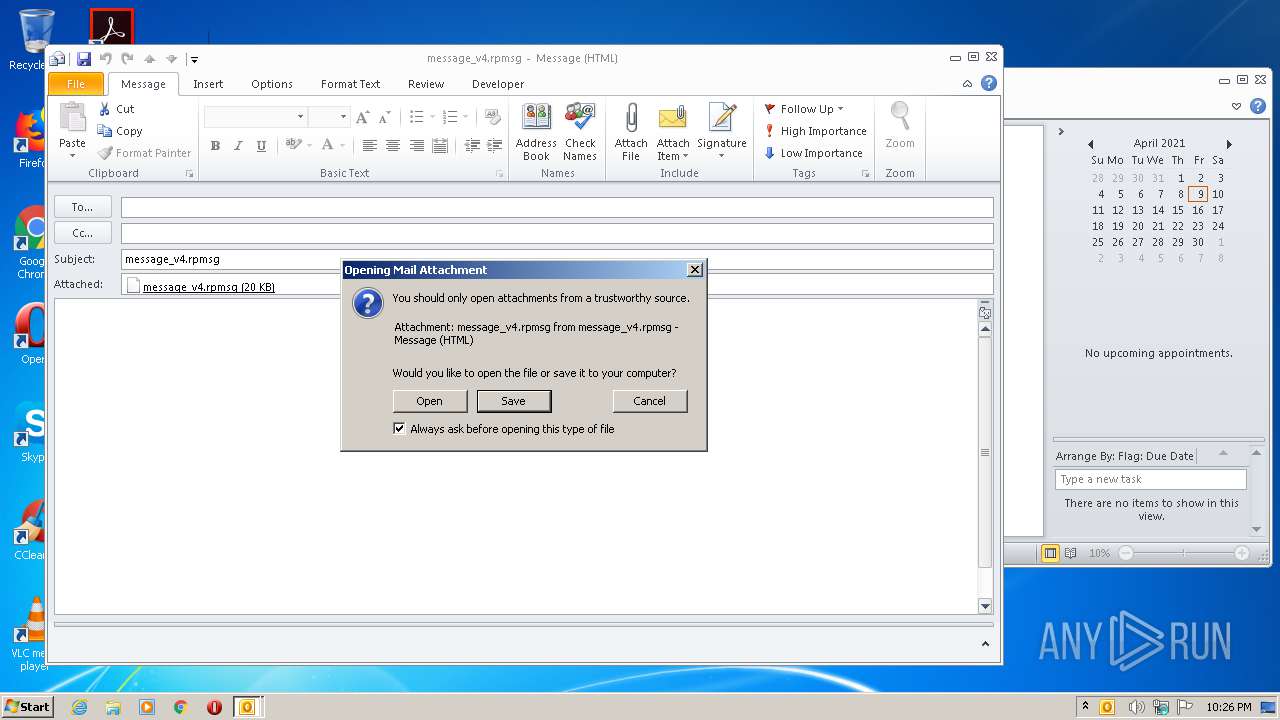
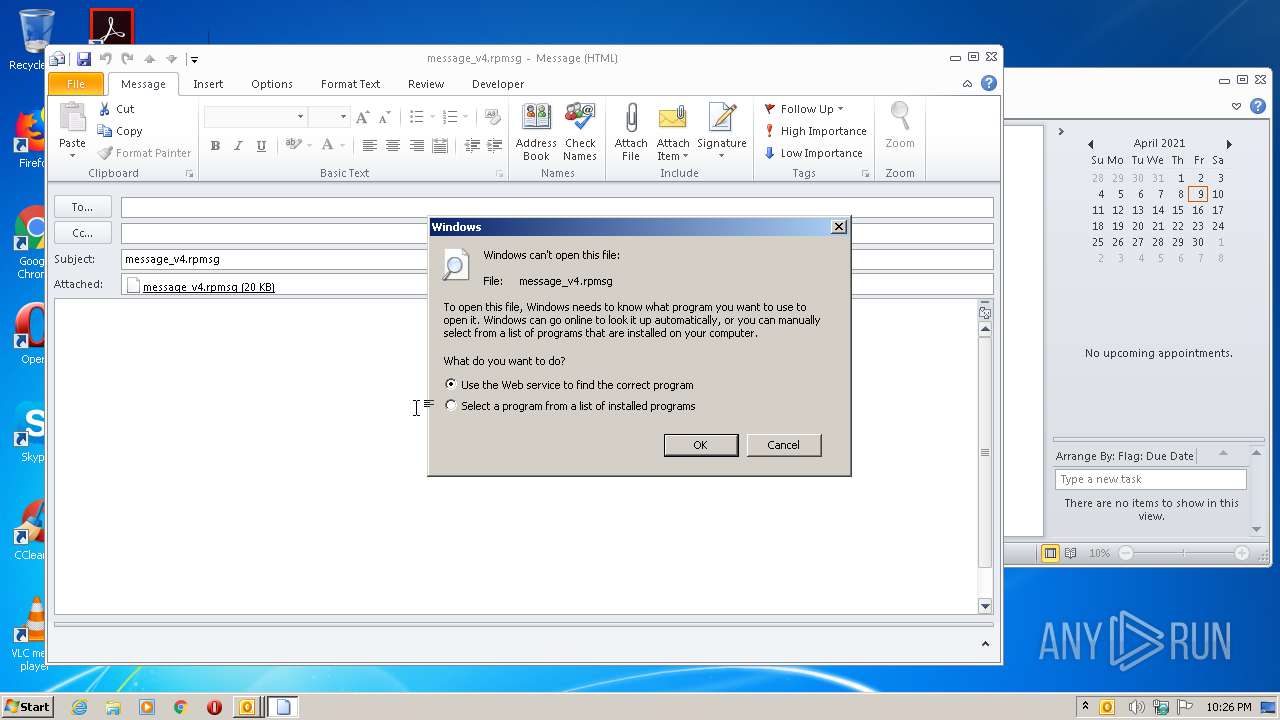
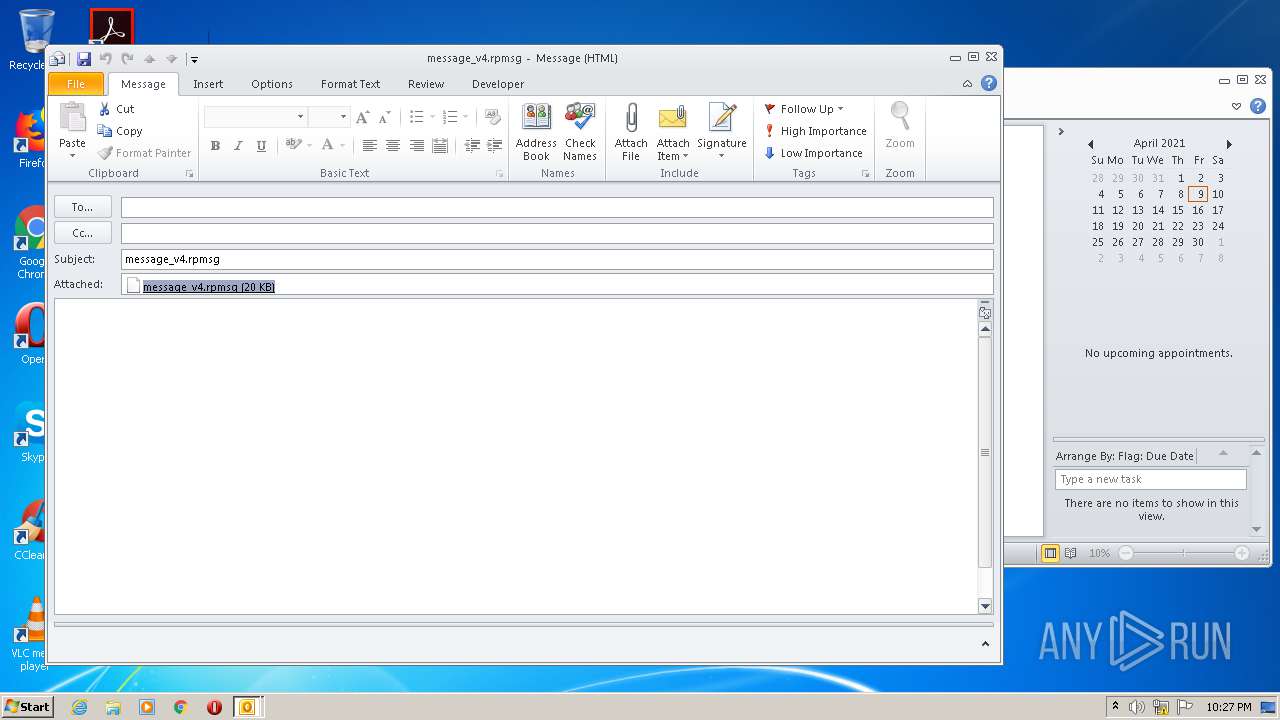
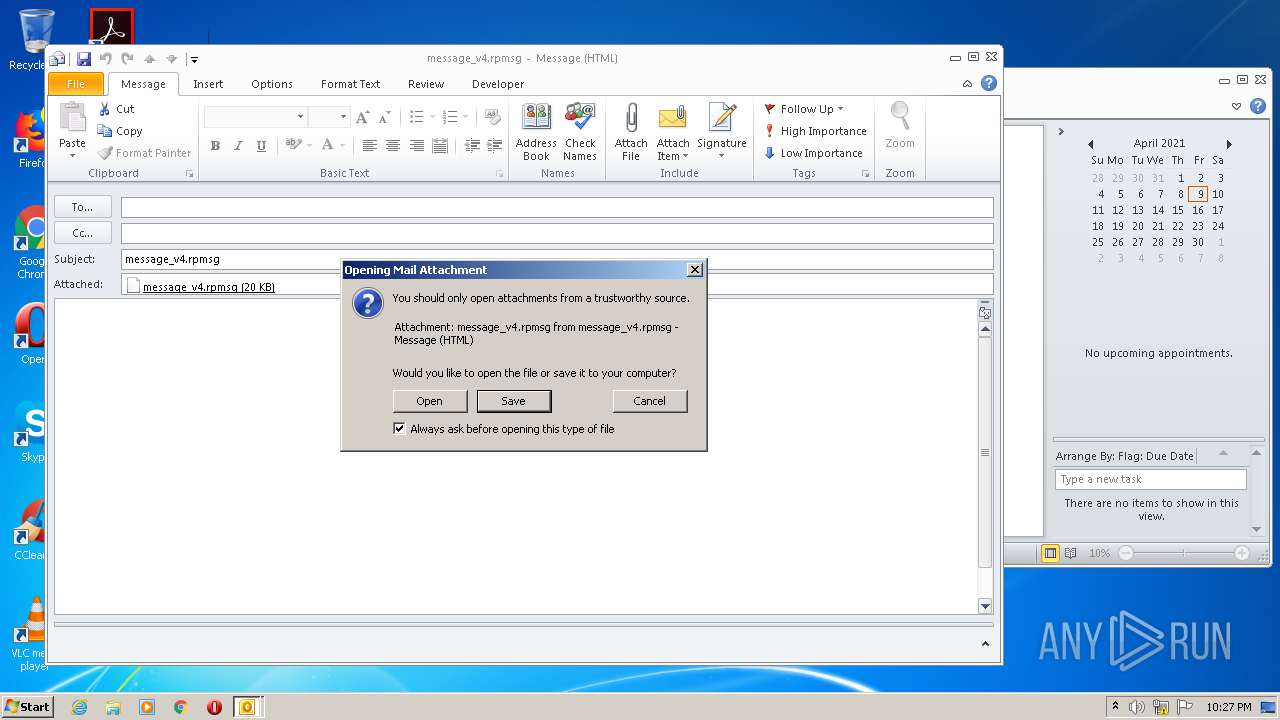
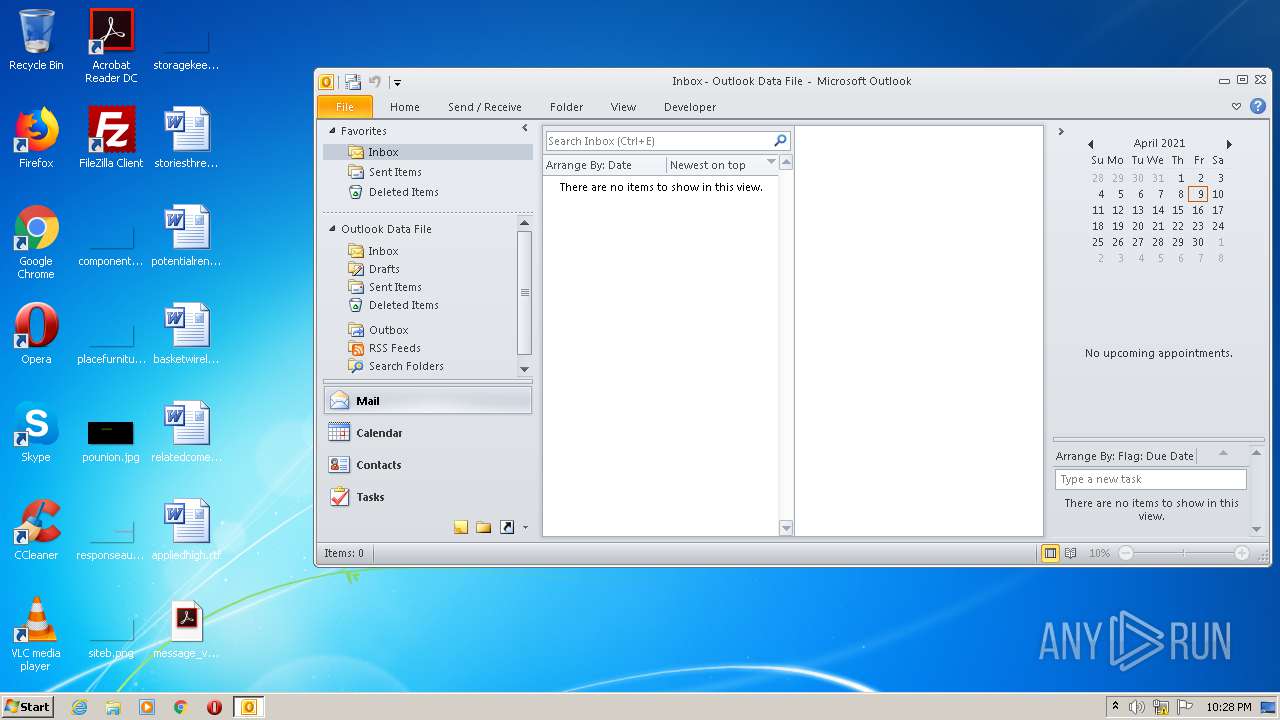
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 868)
SUSPICIOUS
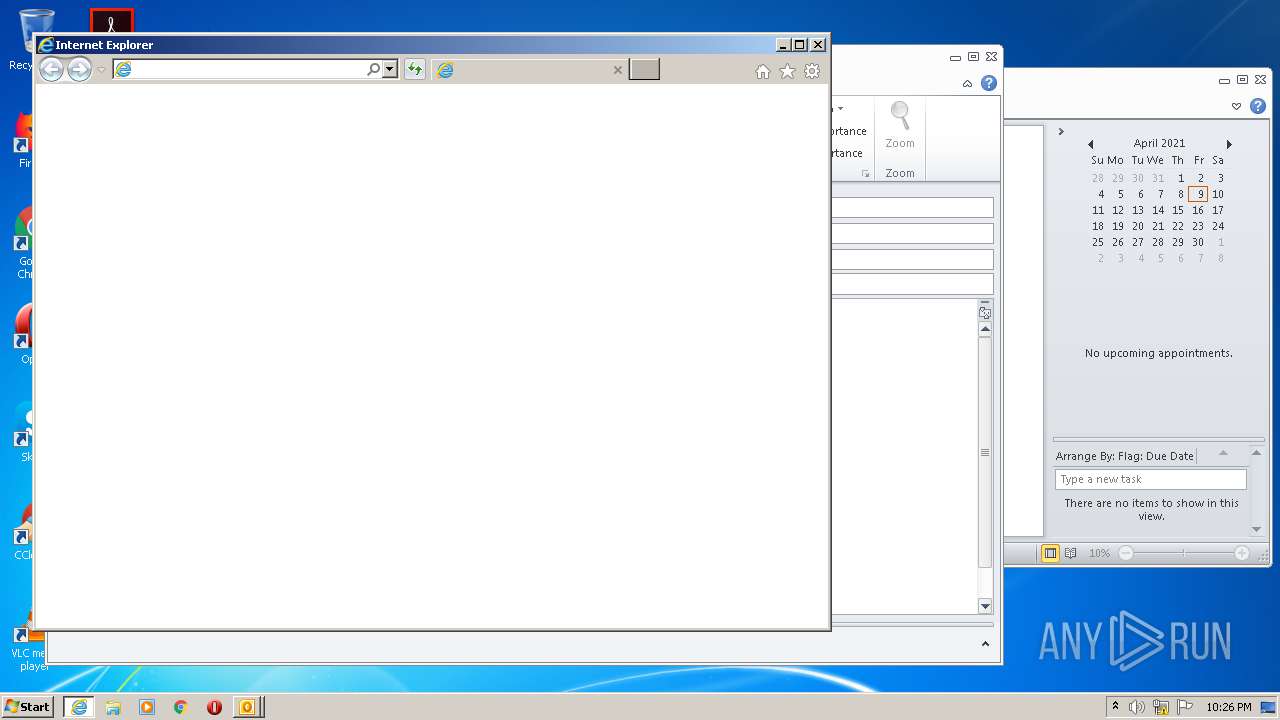
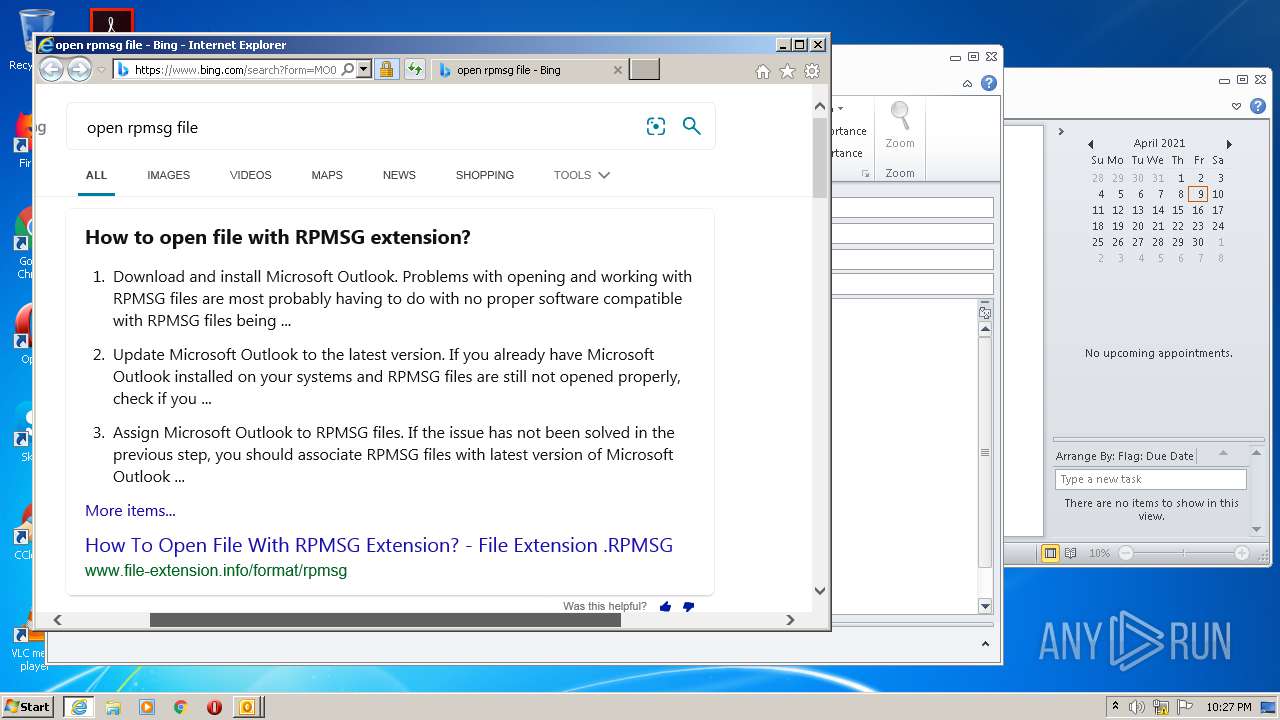
Starts Internet Explorer
- rundll32.exe (PID: 872)
Uses RUNDLL32.EXE to load library
- OUTLOOK.EXE (PID: 868)
INFO
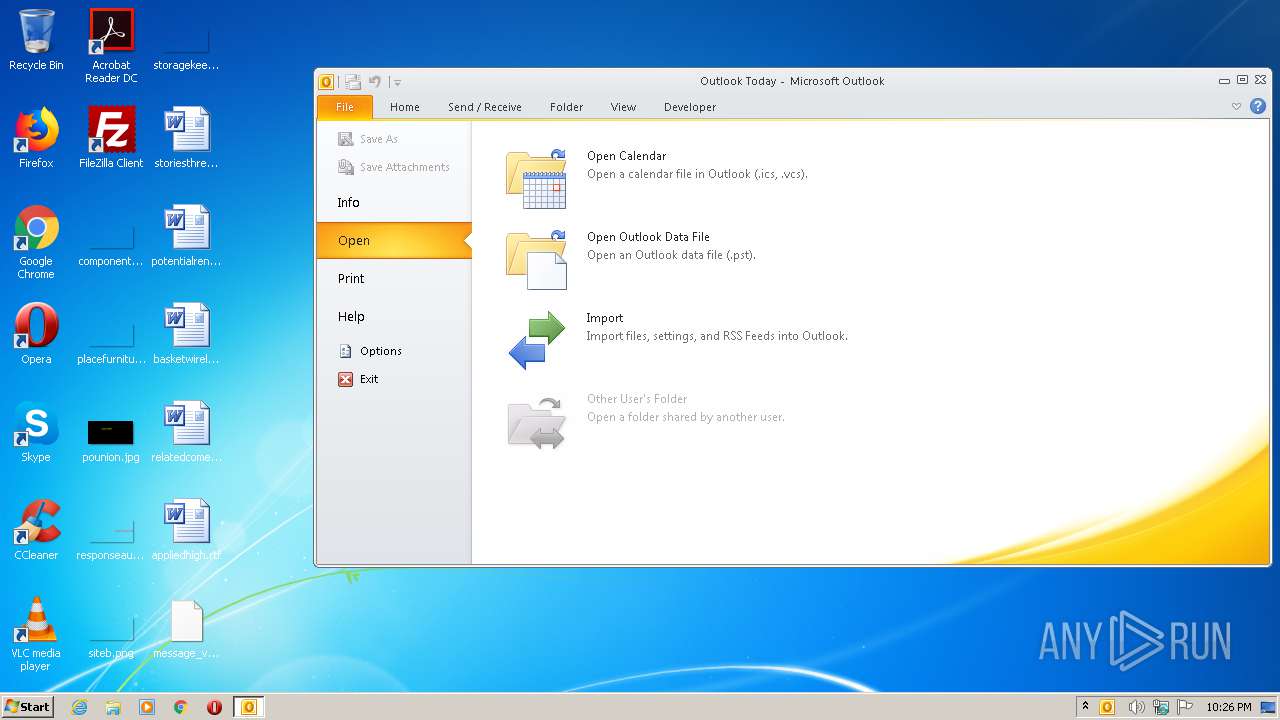
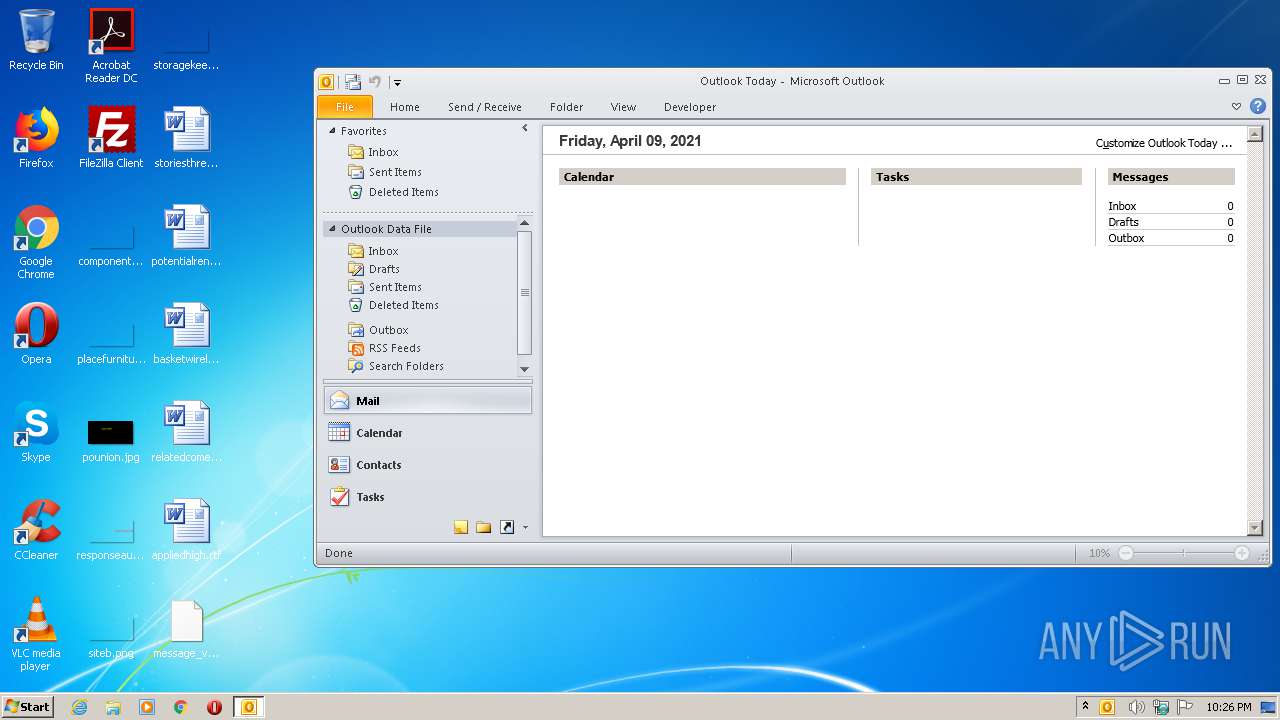
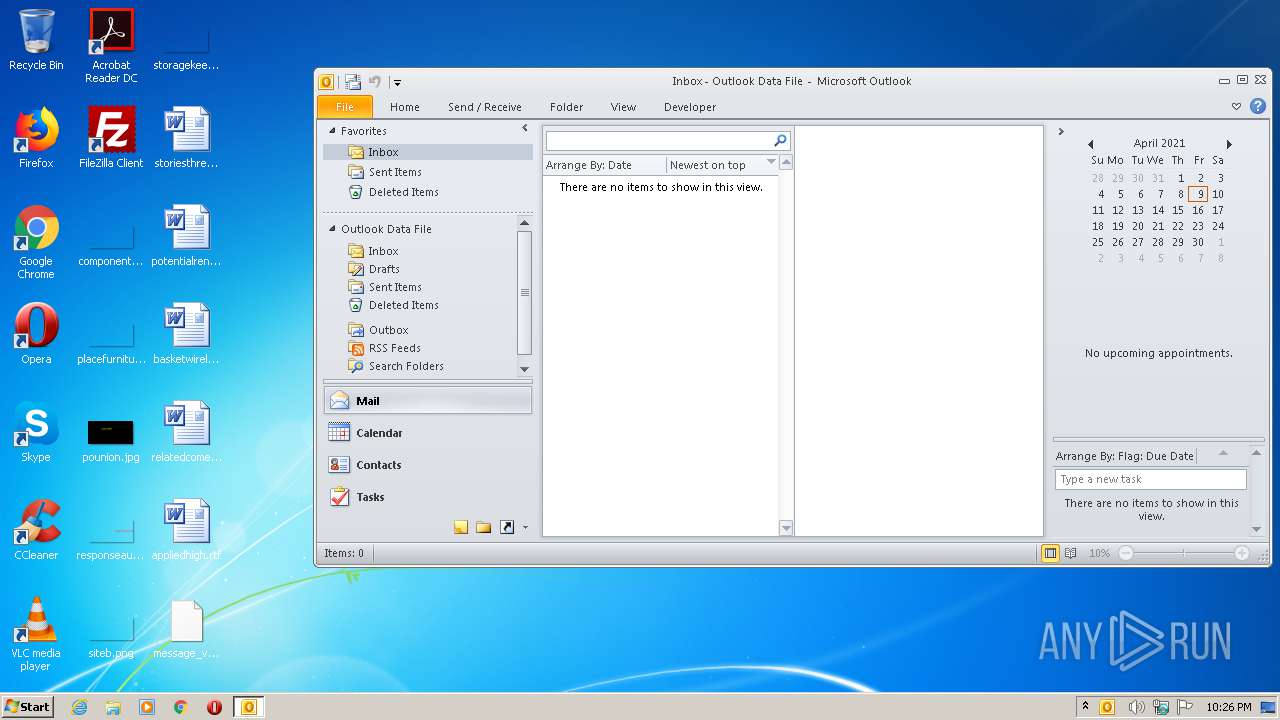
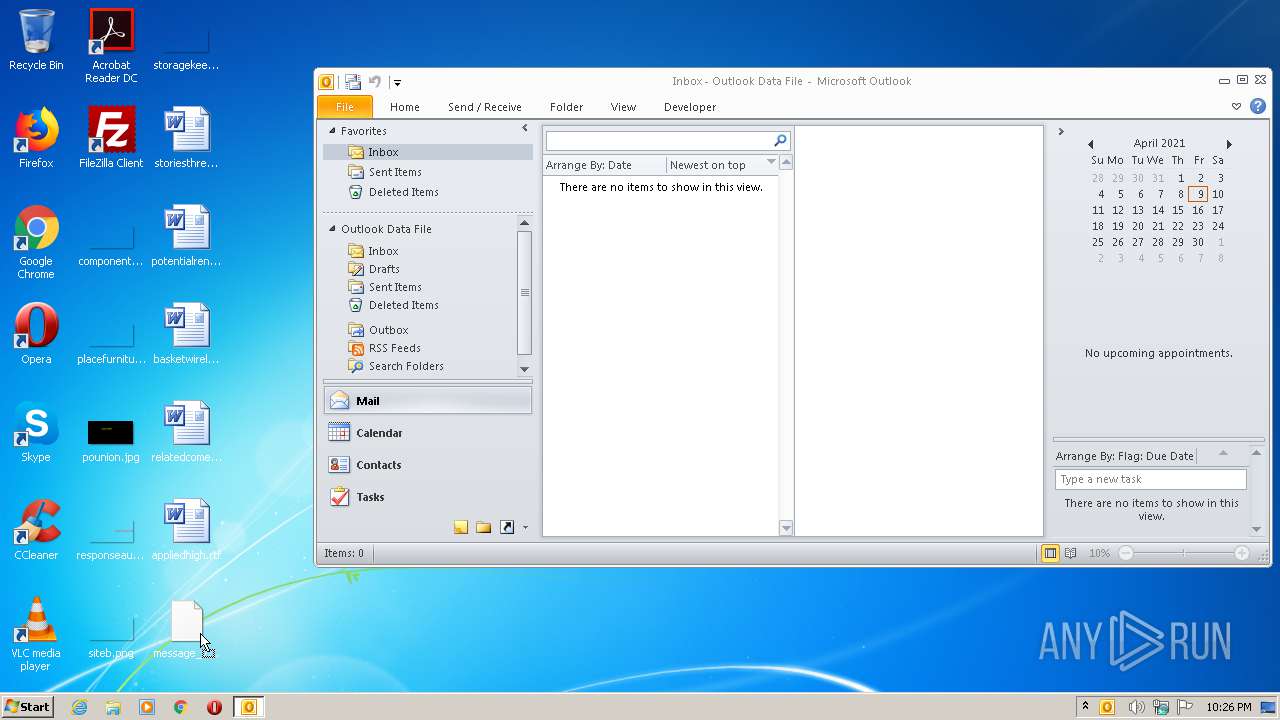
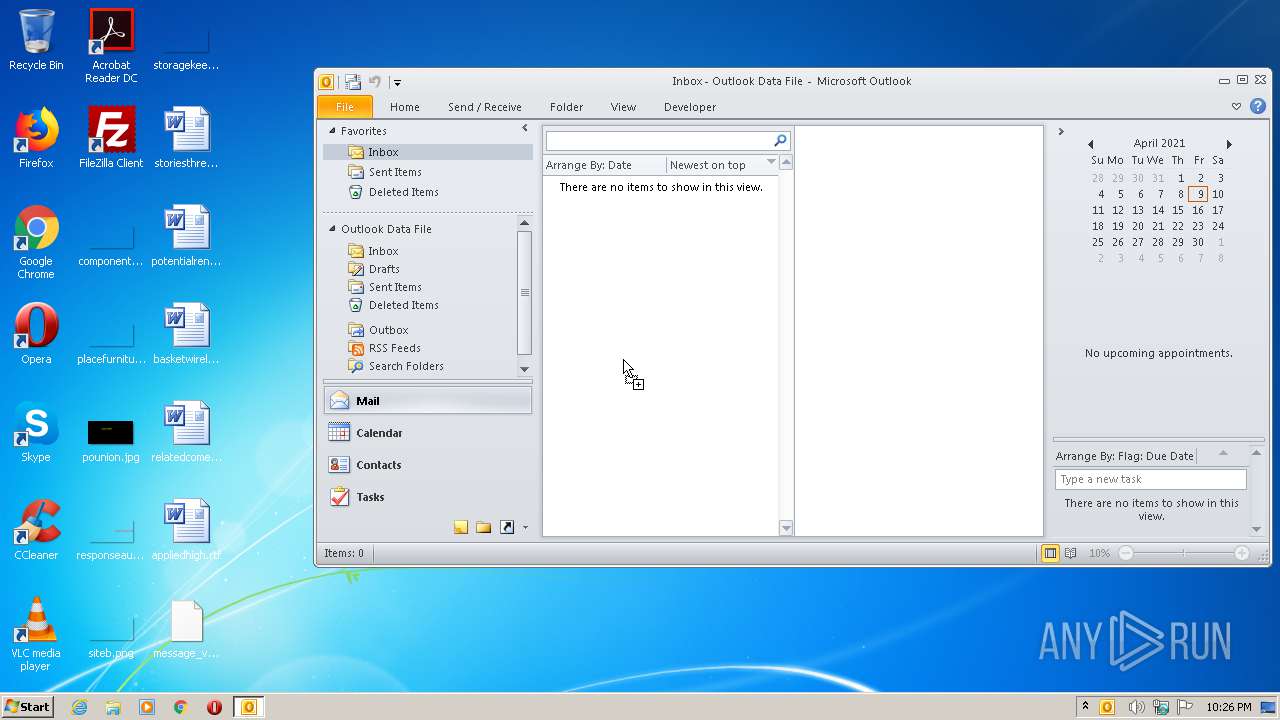
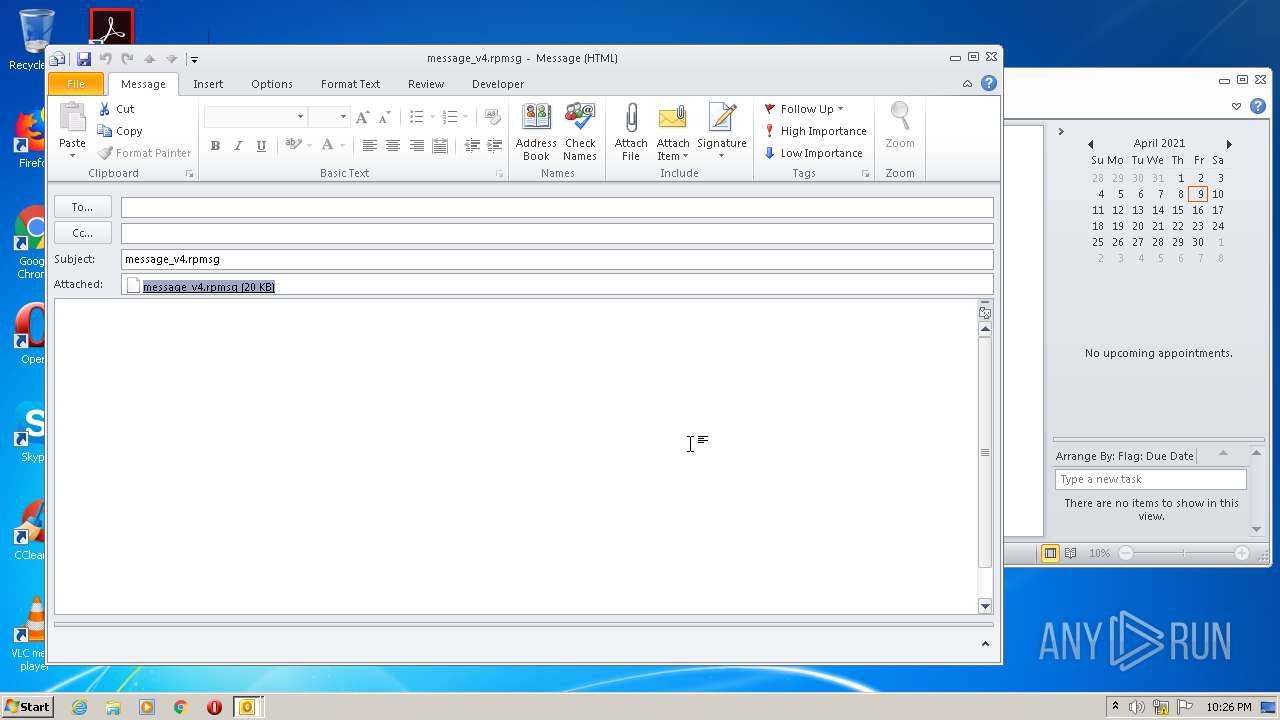
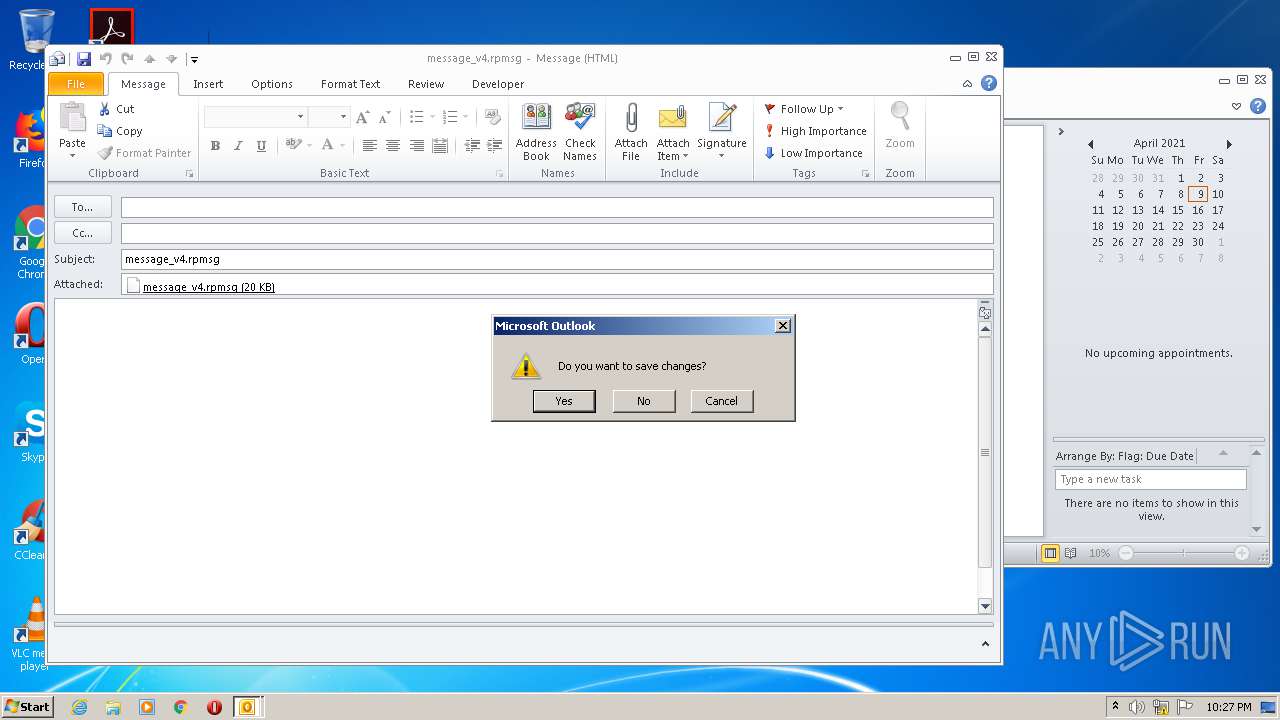
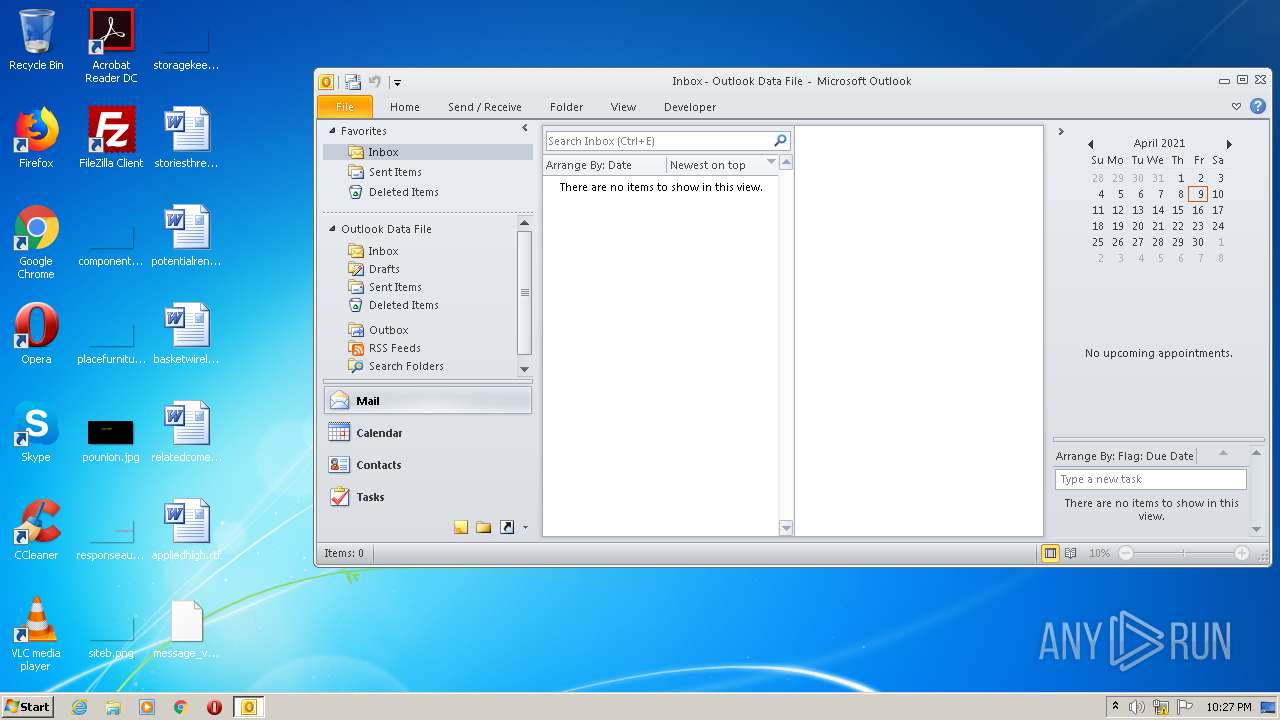
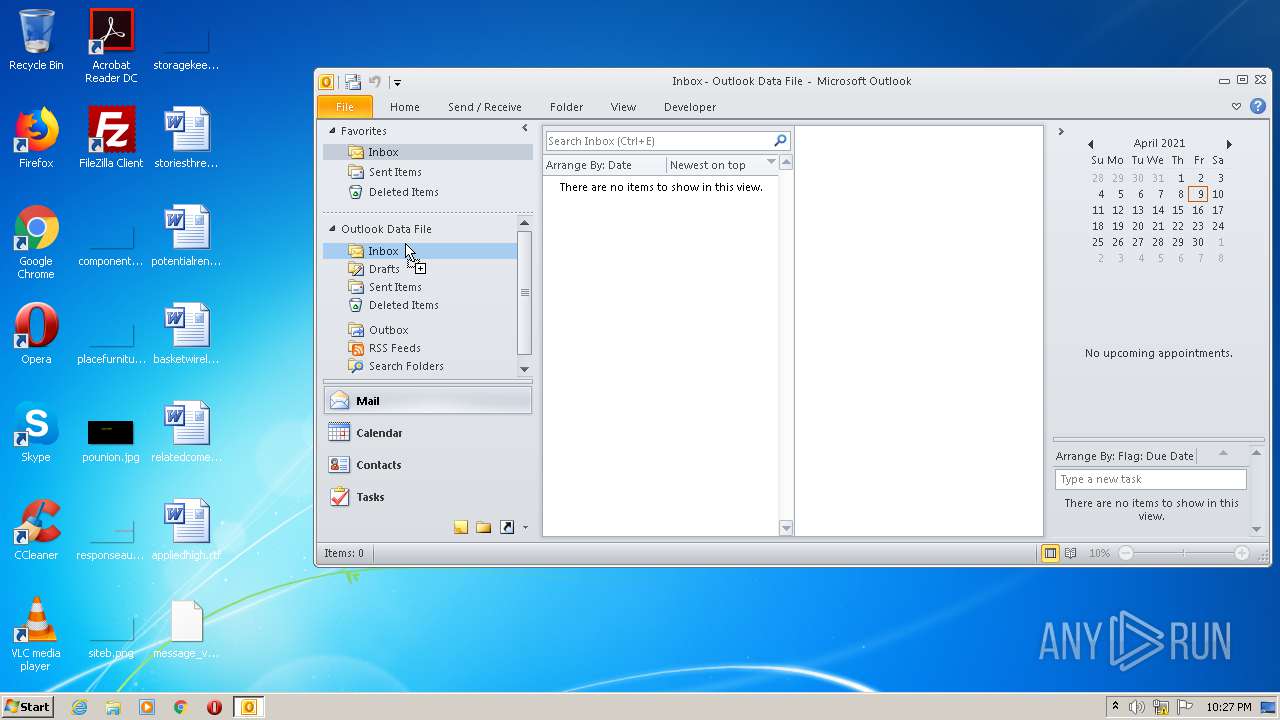
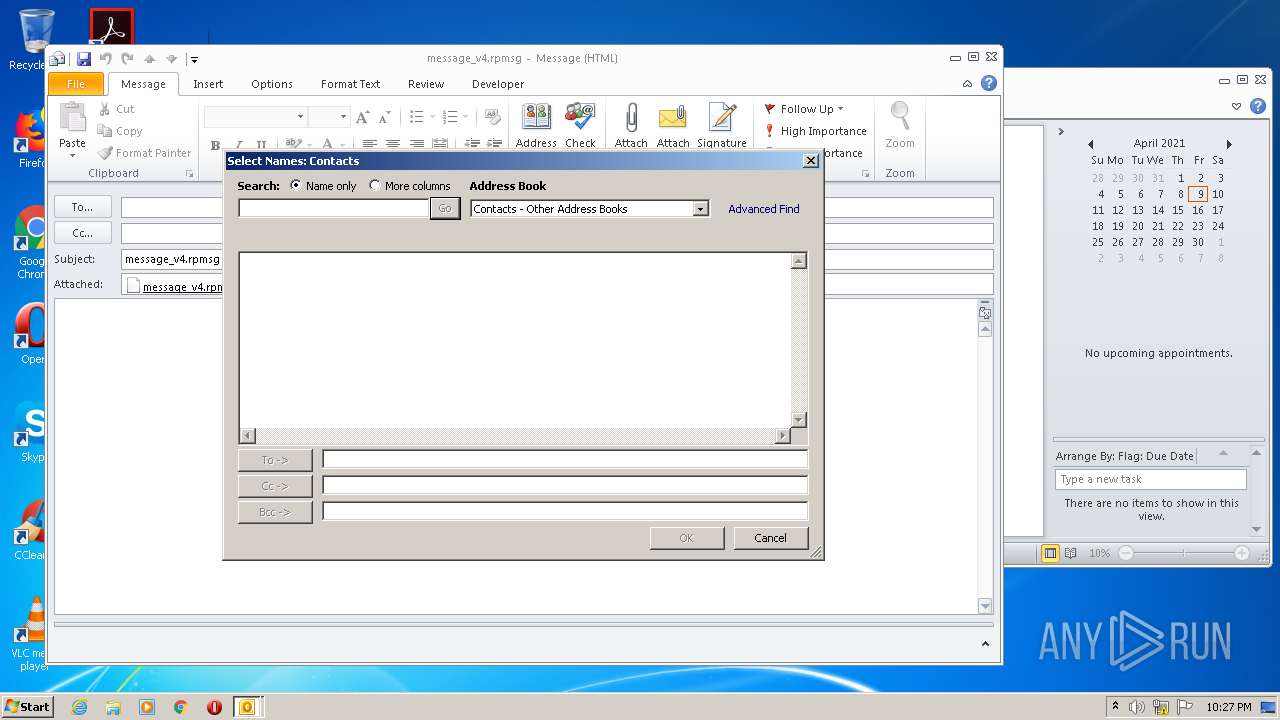
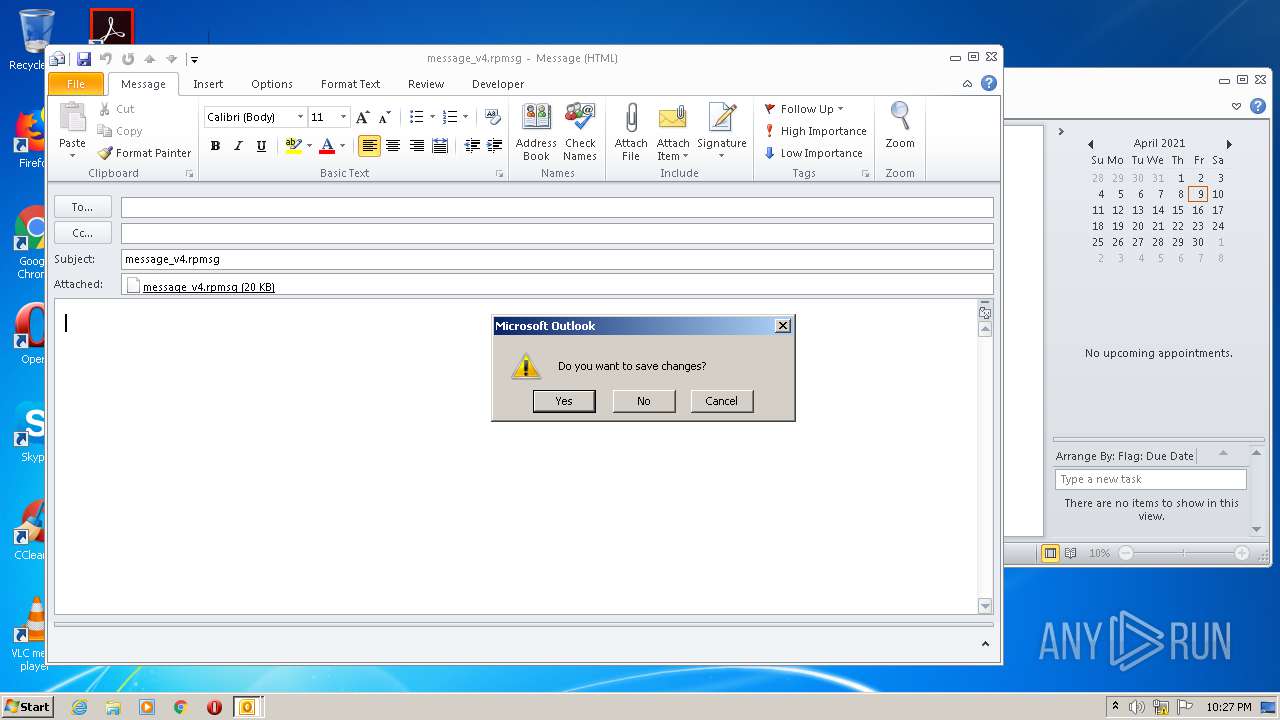
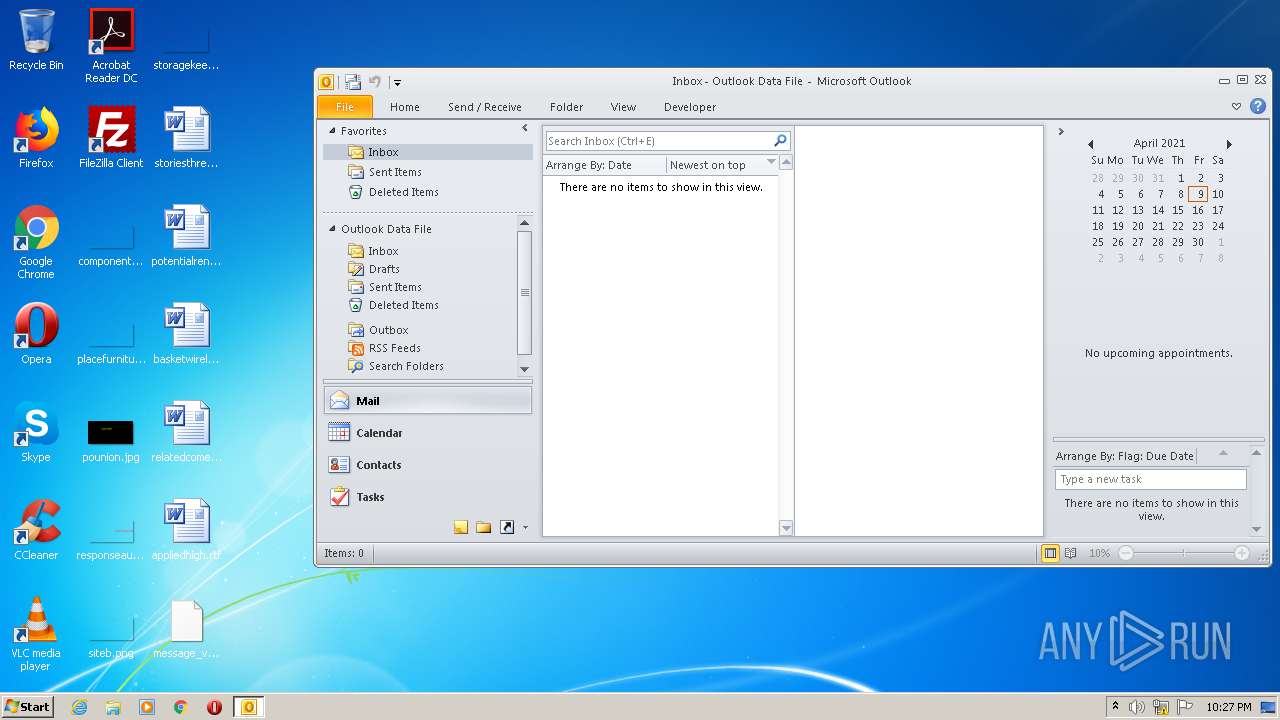
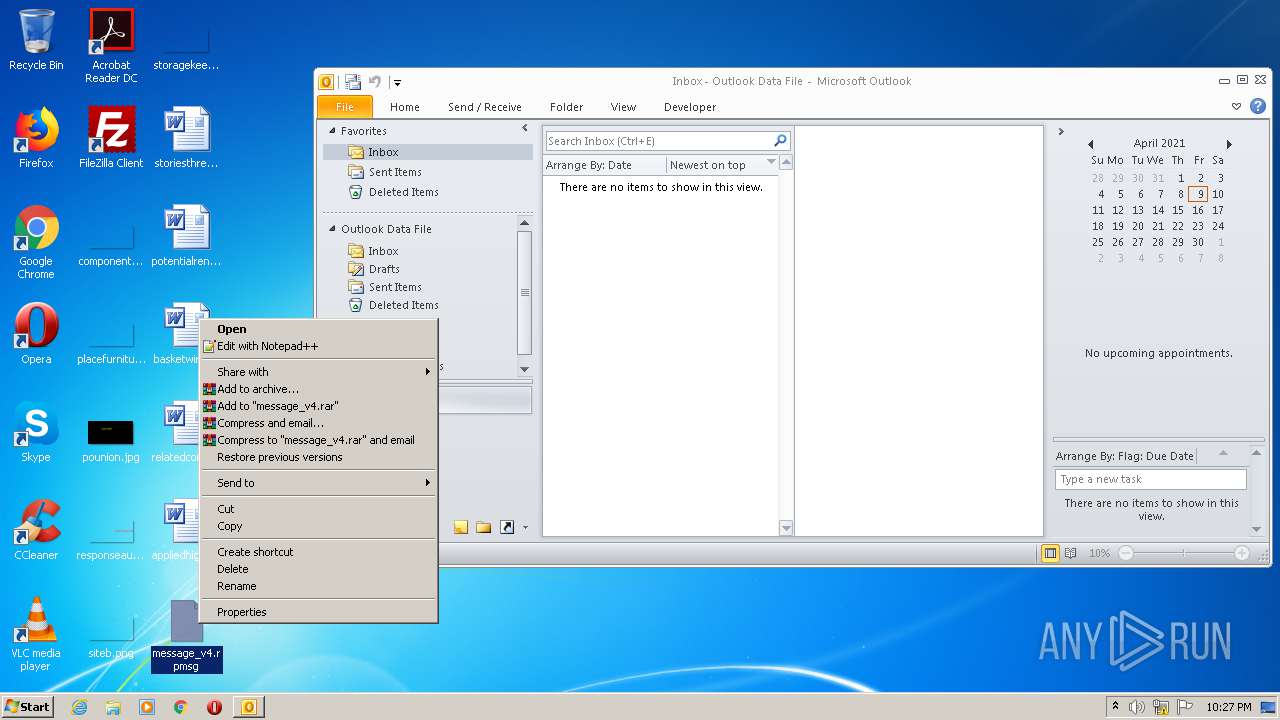
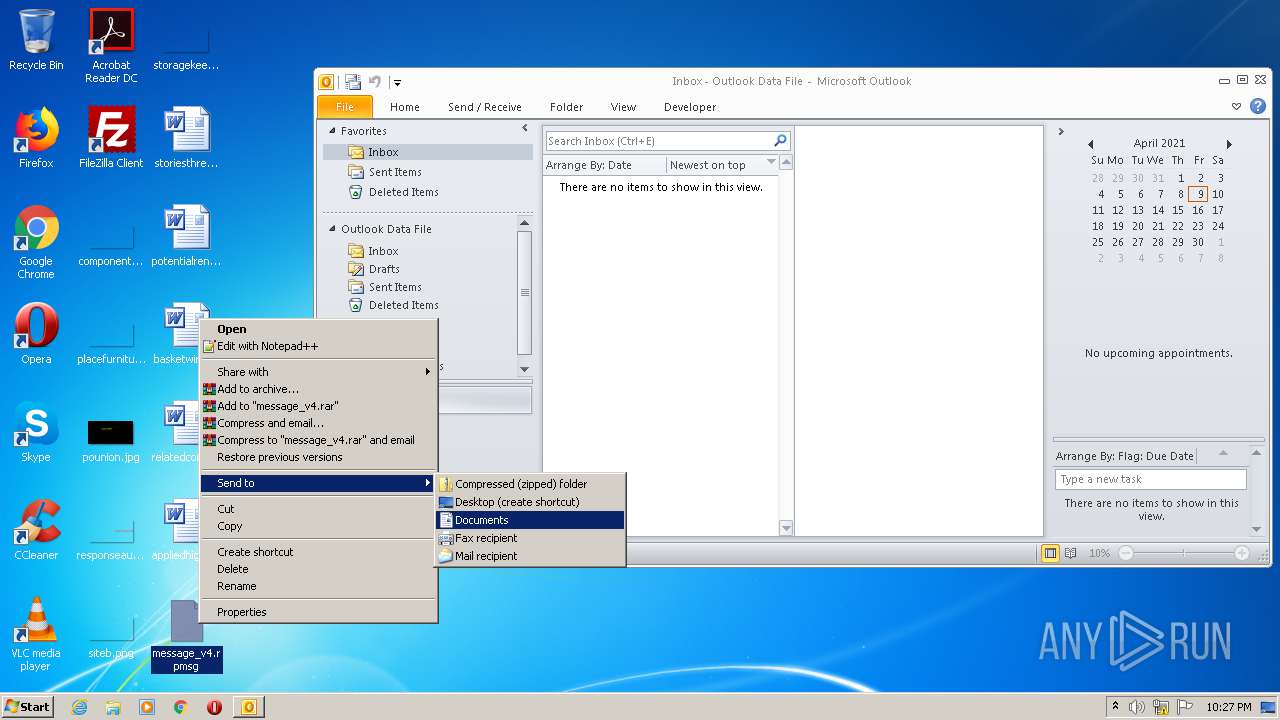
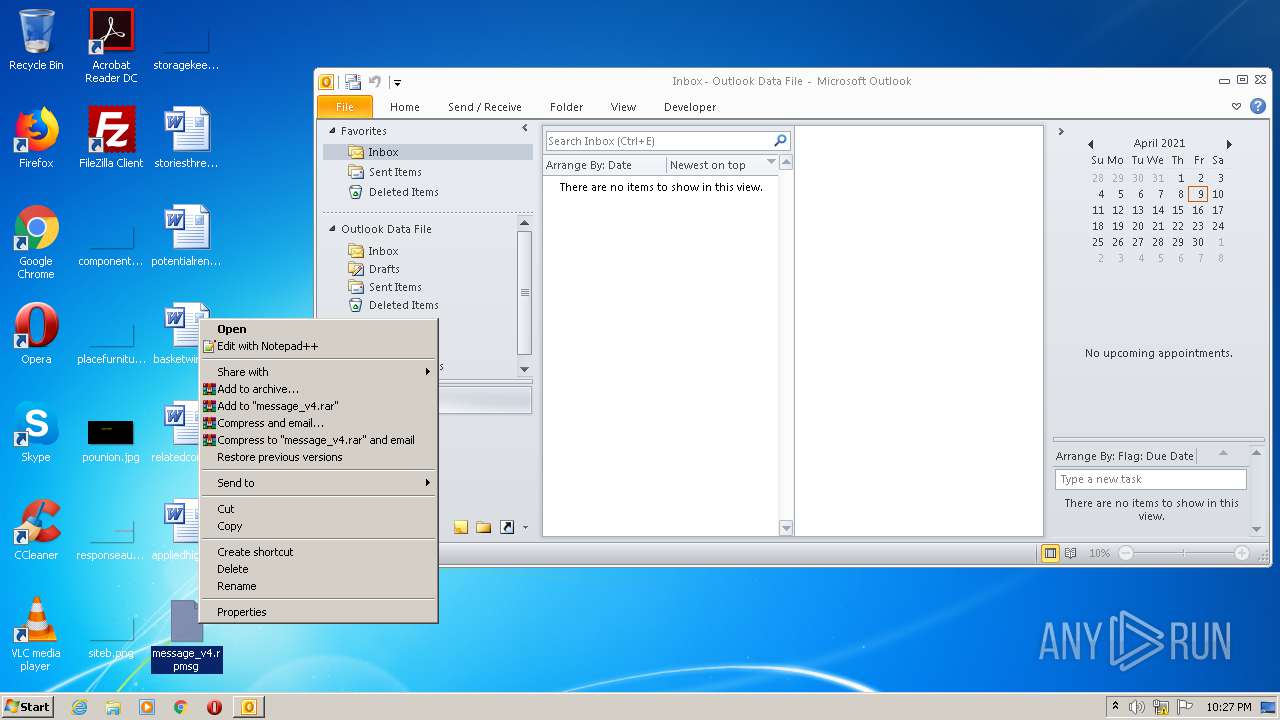
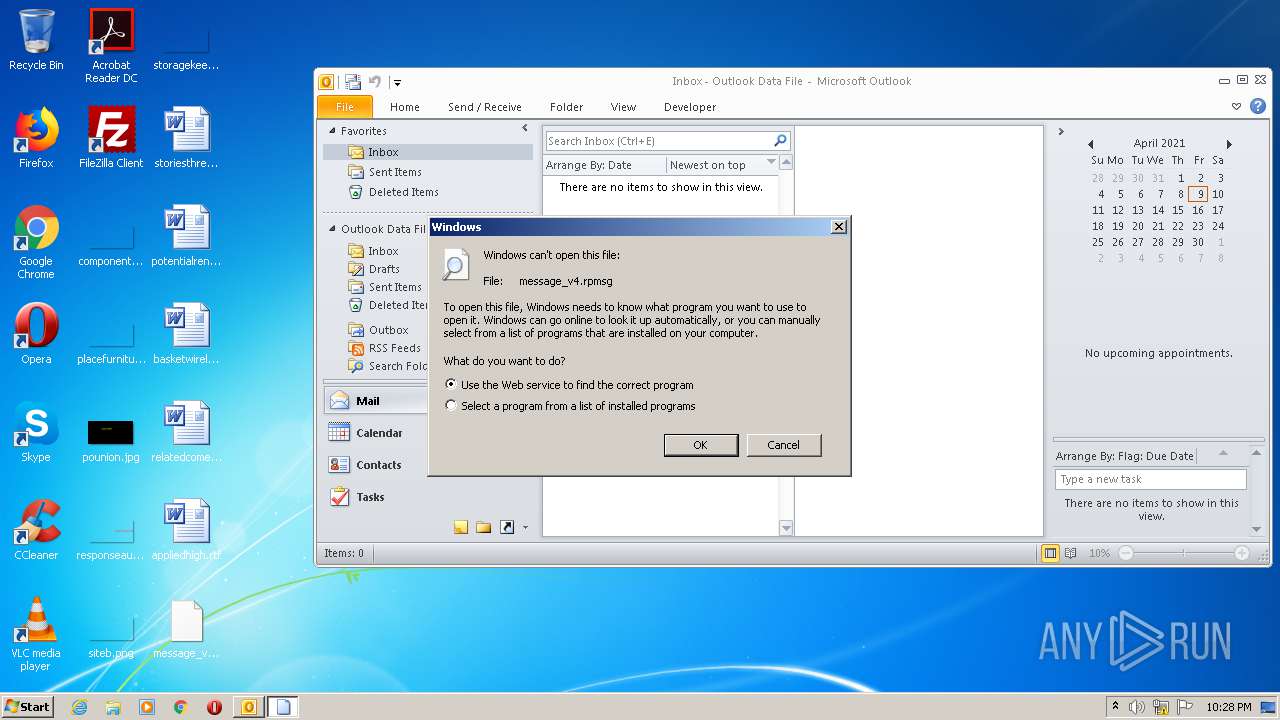
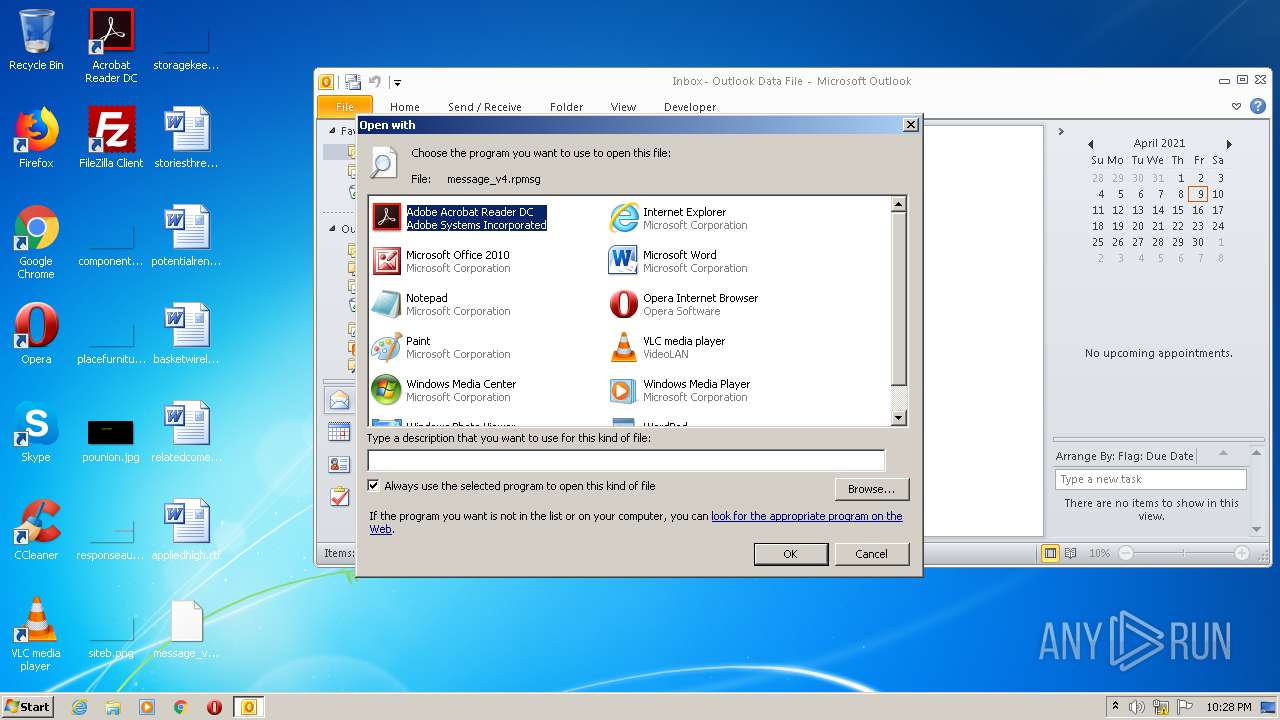
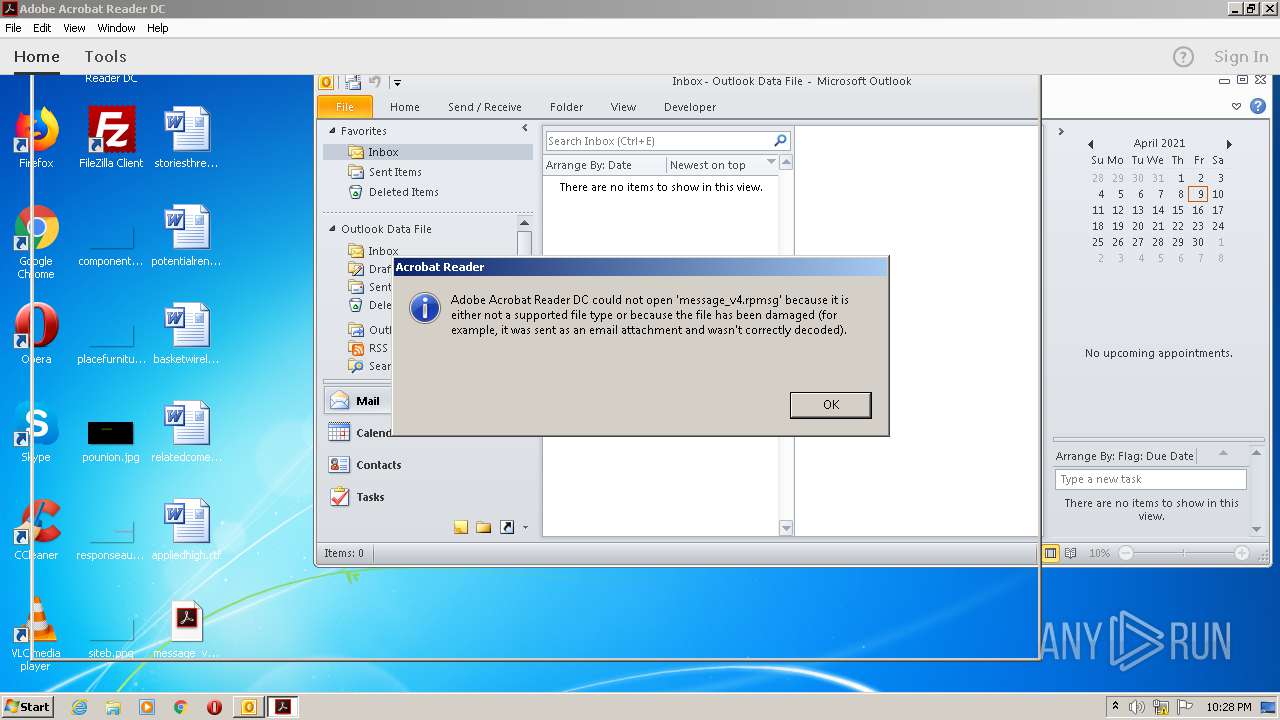
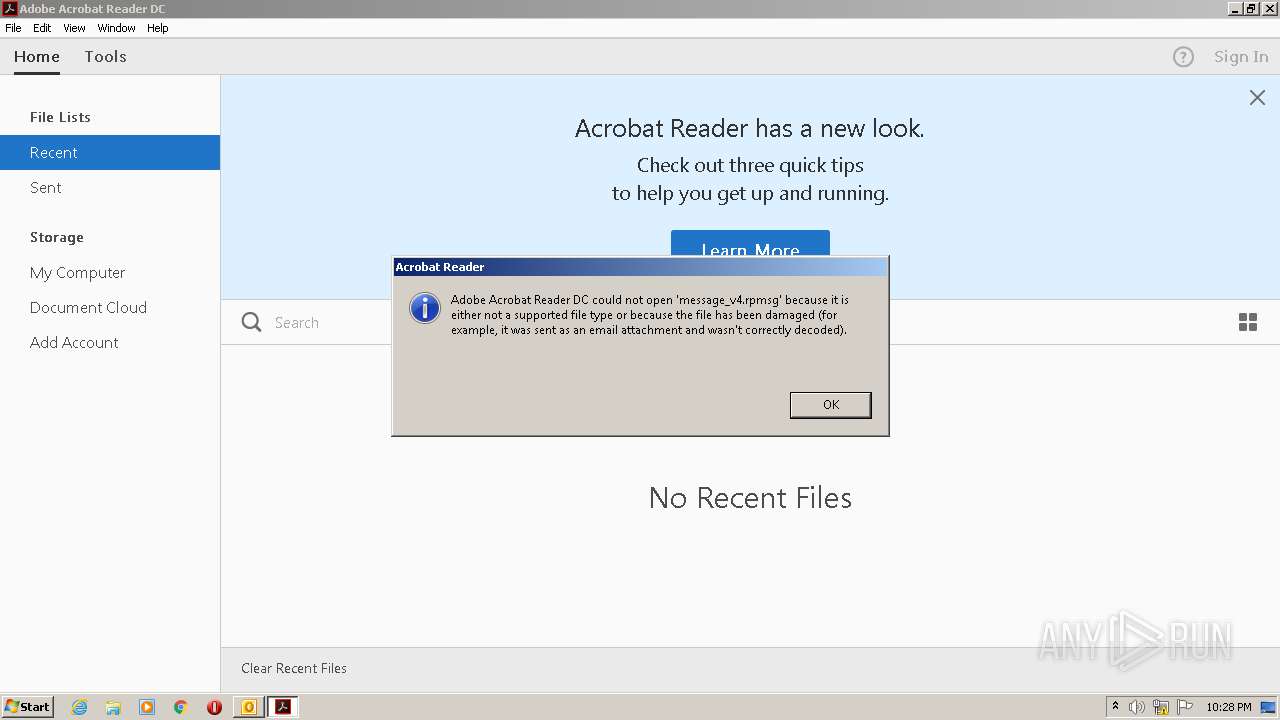
Manual execution by user
- OUTLOOK.EXE (PID: 868)
- rundll32.exe (PID: 2108)
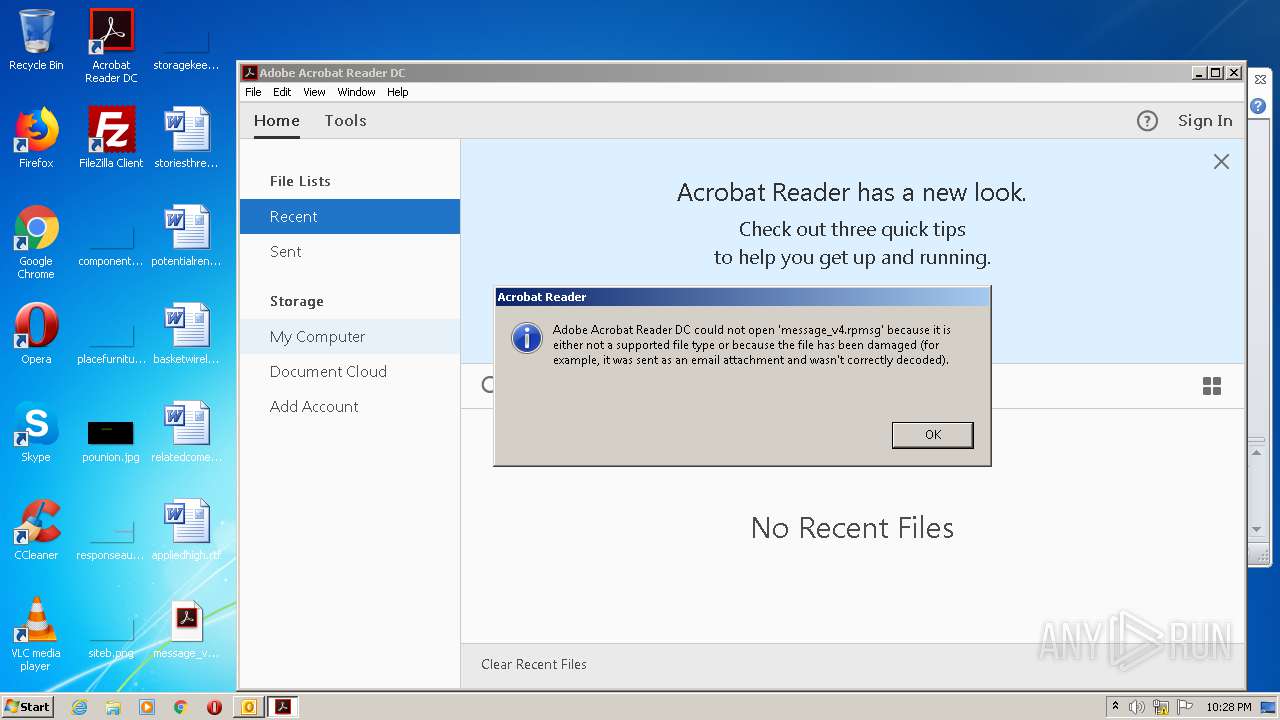
- AcroRd32.exe (PID: 3892)
Reads internet explorer settings
- OUTLOOK.EXE (PID: 868)
- iexplore.exe (PID: 3320)
Reads settings of System Certificates
- iexplore.exe (PID: 3320)
- iexplore.exe (PID: 3584)
- AcroRd32.exe (PID: 1144)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3320)
Application launched itself
- iexplore.exe (PID: 3584)
- AcroRd32.exe (PID: 1144)
- RdrCEF.exe (PID: 2208)
- AcroRd32.exe (PID: 3892)
Creates files in the user directory
- iexplore.exe (PID: 3320)
- OUTLOOK.EXE (PID: 868)
Changes internet zones settings
- iexplore.exe (PID: 3584)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3584)
Changes settings of System certificates
- iexplore.exe (PID: 3584)
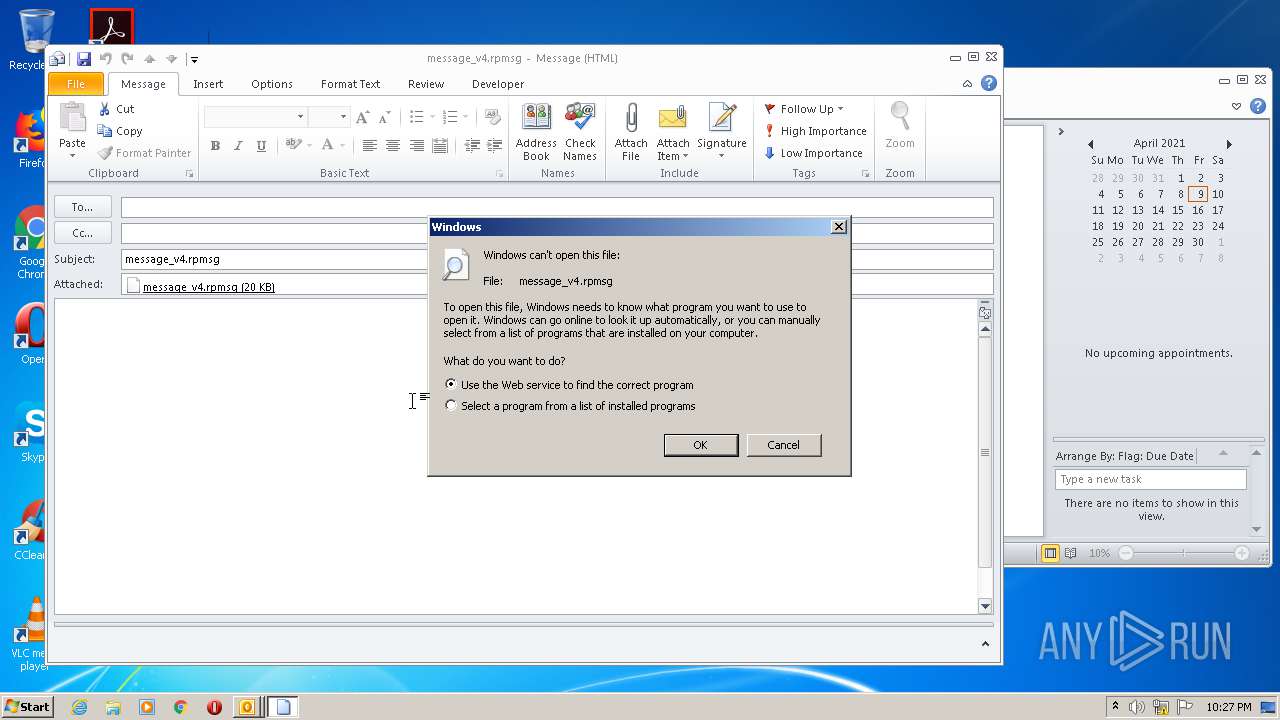
Changes default file association
- rundll32.exe (PID: 2108)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 1144)
Reads the hosts file
- RdrCEF.exe (PID: 2208)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rpmsg | | | Restricted-Permission Message (100) |
|---|
Total processes
53
Monitored processes
13
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 868 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 872 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\JBUMBJBA\message_v4.rpmsg | C:\Windows\system32\rundll32.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\Desktop\message_v4.rpmsg" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | rundll32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1700 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\message_v4.rpmsg | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2108 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\message_v4.rpmsg | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3584 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3360 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\Desktop\message_v4.rpmsg" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 3536 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2208.0.705613910\124084172" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 3584 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=rpmsg | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
3 370
Read events
2 495
Write events
822
Delete events
53
Modification events
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
23
Text files
114
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE3C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4SKDCO4SSSLTMDBI4A7P.temp | — | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\mso58C4.tmp | — | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\Microsoft Outlook.lnk | lnk | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\be71009ff8bb02a2.customDestinations-ms~RF131669.TMP | binary | |
MD5:— | SHA256:— | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFA22.tmp | — | |
MD5:— | SHA256:— | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFA23.tmp | — | |
MD5:— | SHA256:— | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\SOQN1WZE.txt | — | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\be71009ff8bb02a2.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
29
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
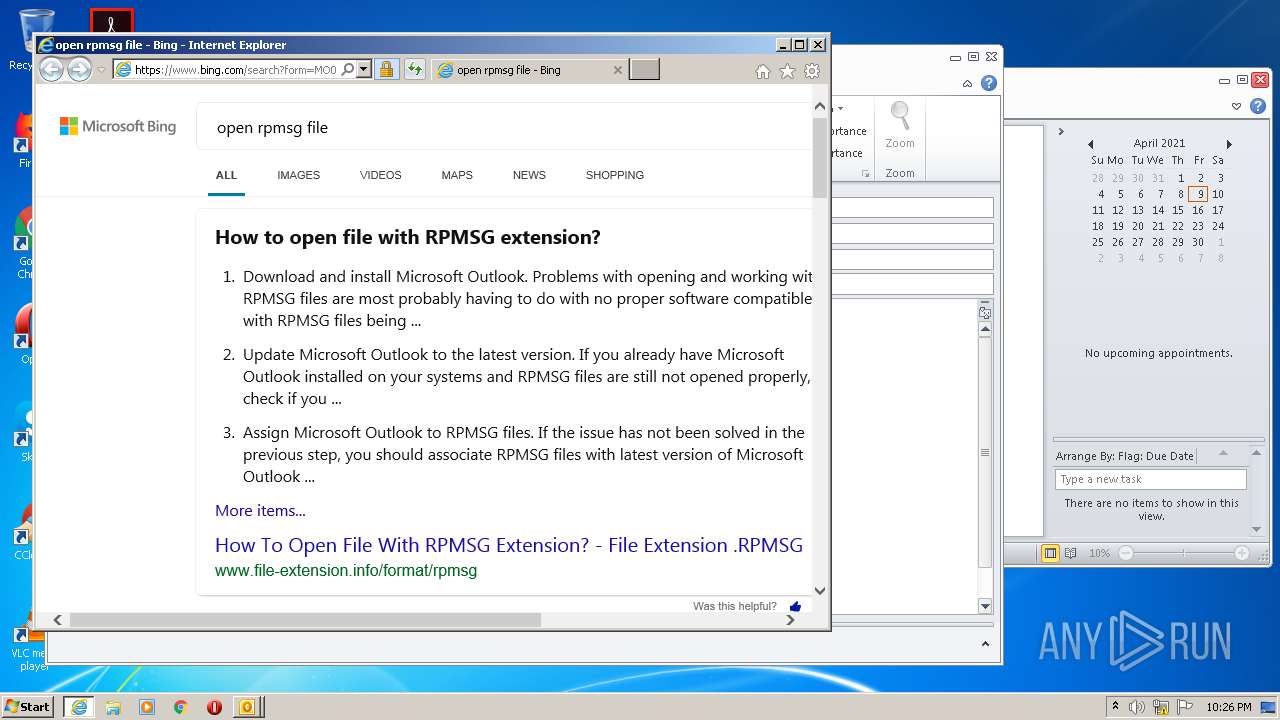
3320 | iexplore.exe | GET | 302 | 104.117.196.27:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=rpmsg | US | — | — | whitelisted |
3320 | iexplore.exe | GET | 301 | 23.55.161.159:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=rpmsg | US | — | — | whitelisted |
1144 | AcroRd32.exe | GET | 304 | 23.55.110.196:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | US | — | — | whitelisted |
1144 | AcroRd32.exe | GET | 304 | 23.55.110.196:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | US | — | — | whitelisted |
1144 | AcroRd32.exe | GET | 304 | 23.55.110.196:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/279_15_23_20070.zip | US | — | — | whitelisted |
1144 | AcroRd32.exe | GET | 304 | 23.55.110.196:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | US | — | — | whitelisted |
3320 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1144 | AcroRd32.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3584 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 4.19 Kb | whitelisted |
1144 | AcroRd32.exe | GET | 200 | 23.55.110.196:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | US | compressed | 9.54 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
868 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3320 | iexplore.exe | 104.117.196.27:80 | go.microsoft.com | TPG Telecom Limited | US | unknown |
3320 | iexplore.exe | 23.55.161.159:80 | shell.windows.com | Akamai International B.V. | US | unknown |
3320 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3320 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3320 | iexplore.exe | 20.190.160.136:443 | login.microsoftonline.com | Microsoft Corporation | US | suspicious |
3584 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3320 | iexplore.exe | 20.190.160.129:443 | login.microsoftonline.com | Microsoft Corporation | US | suspicious |
3584 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3584 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
api.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
www2.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |