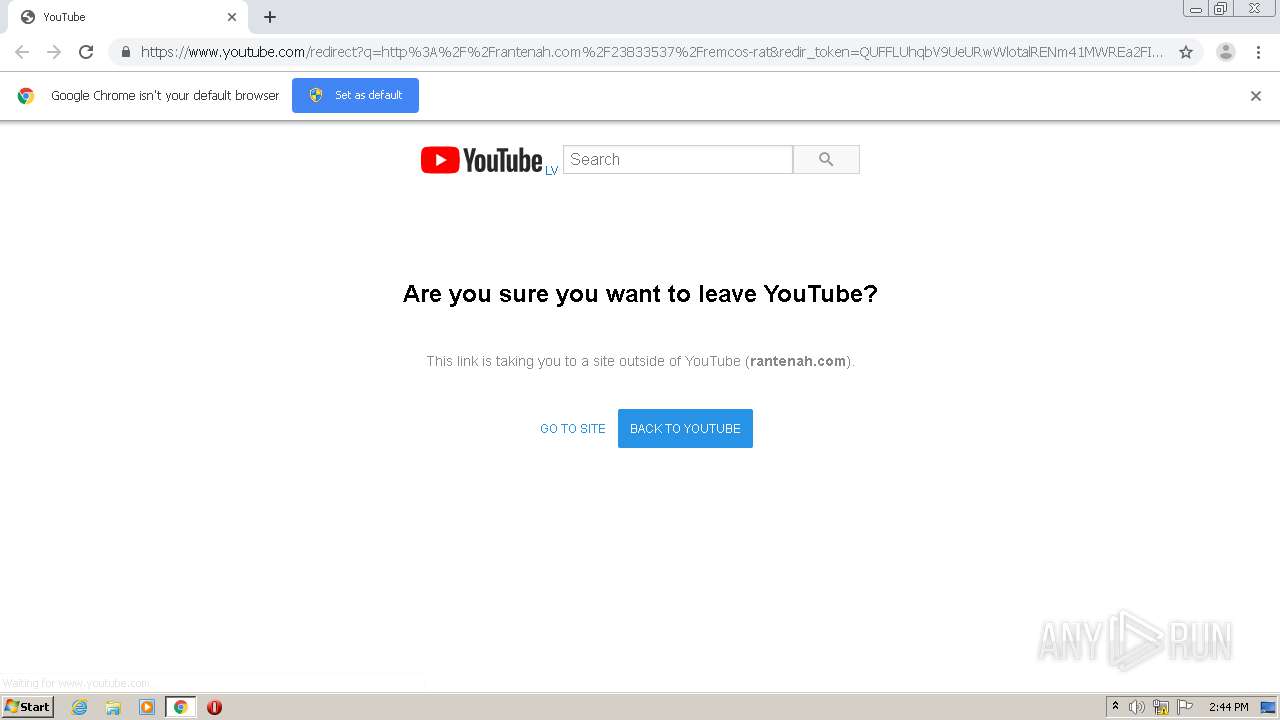
| URL: | https://www.youtube.com/redirect?q=http%3A%2F%2Frantenah.com%2F23833537%2Fremcos-rat&redir_token=QUFFLUhqbV9UeURwWlotalRENm41MWREa2FIM3U4Y1ZNZ3xBQ3Jtc0ttQWpFM1dBVlZvYUUxejhFTmh0ejF1MFdybjJNVGRjaUh2ZzhTa0hXZnRqZXpaQTB5N3pSS2dQQnoxeUxOeU4zTUUyWEI0QXpSd2FYdzhpMEhCSmIzMFpreFNwdkJJYk5NVmg4ckhCcjFMZXh4U1BuZw%3D%3D&v=_qnBOe4Bxxc&event=video_description |
| Full analysis: | https://app.any.run/tasks/da366334-a88f-4778-ba00-7c33c599ff13 |
| Verdict: | Malicious activity |
| Analysis date: | January 19, 2021, 14:43:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4F7DA6CAC9B644571E3A7C12FFA17369 |
| SHA1: | BE06ED649FEA251233E5CAAD635605F901F4E894 |
| SHA256: | A81C80D7BC0A03DC48CEE1A1744AC23ACA9C25FF106EEB80BE06589486F44BFE |
| SSDEEP: | 6:2OLUxGKWdszUAiZWP3OYZawSh1fW4NfNGITl223E080RfMgAjQiC3eNCBddZML+v:2jGZsAjZ6nawlUTg23d3MgAerBBMLk |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2596)
- chrome.exe (PID: 788)
Application launched itself
- chrome.exe (PID: 2596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,6005388481821838531,15568595882822306414,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13592092103057058483 --mojo-platform-channel-handle=3120 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2600 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6005388481821838531,15568595882822306414,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11441035181177667787 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,6005388481821838531,15568595882822306414,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5272626537931112888 --mojo-platform-channel-handle=1464 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,6005388481821838531,15568595882822306414,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5345003639047564927 --mojo-platform-channel-handle=984 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6005388481821838531,15568595882822306414,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7095812156305545513 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2368 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6005388481821838531,15568595882822306414,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4703773294554182305 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,6005388481821838531,15568595882822306414,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=336698761773177958 --mojo-platform-channel-handle=3664 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6005388481821838531,15568595882822306414,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4439119833493034311 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3720 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6005388481821838531,15568595882822306414,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3856245564801022737 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
614
Read events
548
Write events
63
Delete events
3
Modification events
| (PID) Process: | (2596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2596-13255541047520875 |
Value: 259 | |||
| (PID) Process: | (2596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2596) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
81
Text files
84
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6006F038-A24.pma | — | |
MD5:— | SHA256:— | |||
| 2596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\02070e97-ba48-4cd4-b9af-72fac1922644.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF127bc0.TMP | text | |
MD5:— | SHA256:— | |||
| 2596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF127fa8.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
101
DNS requests
65
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
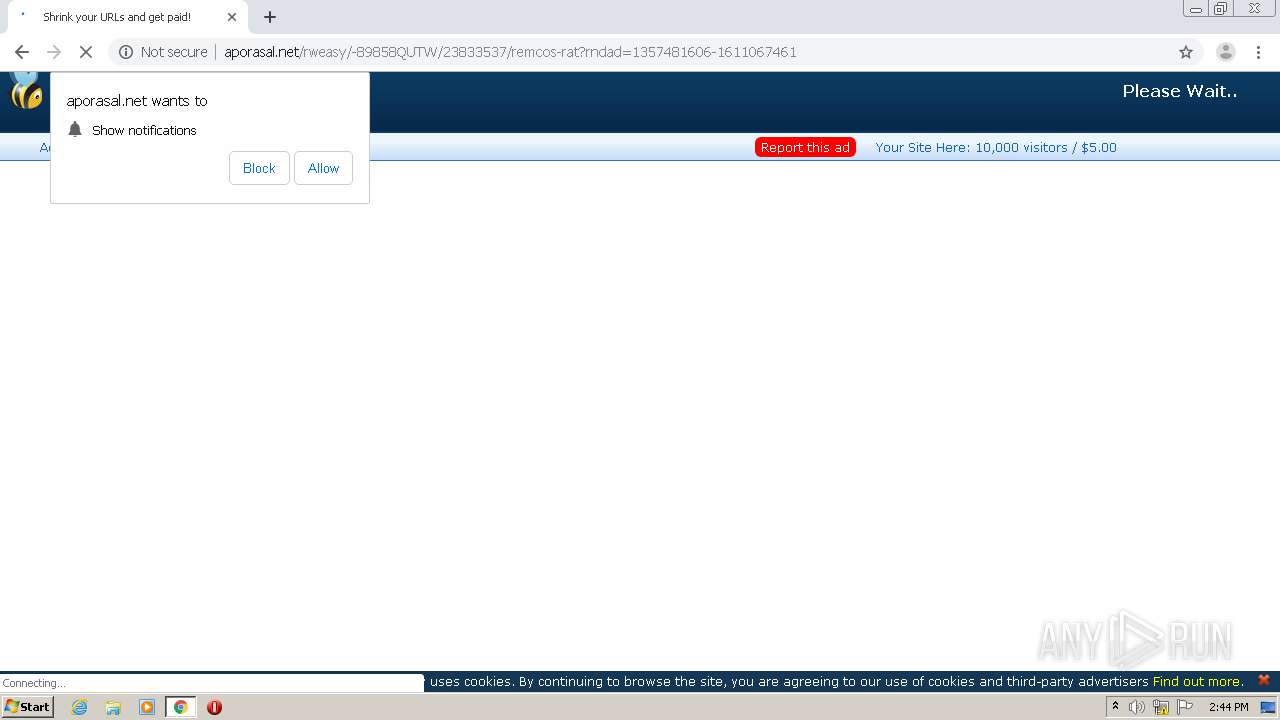
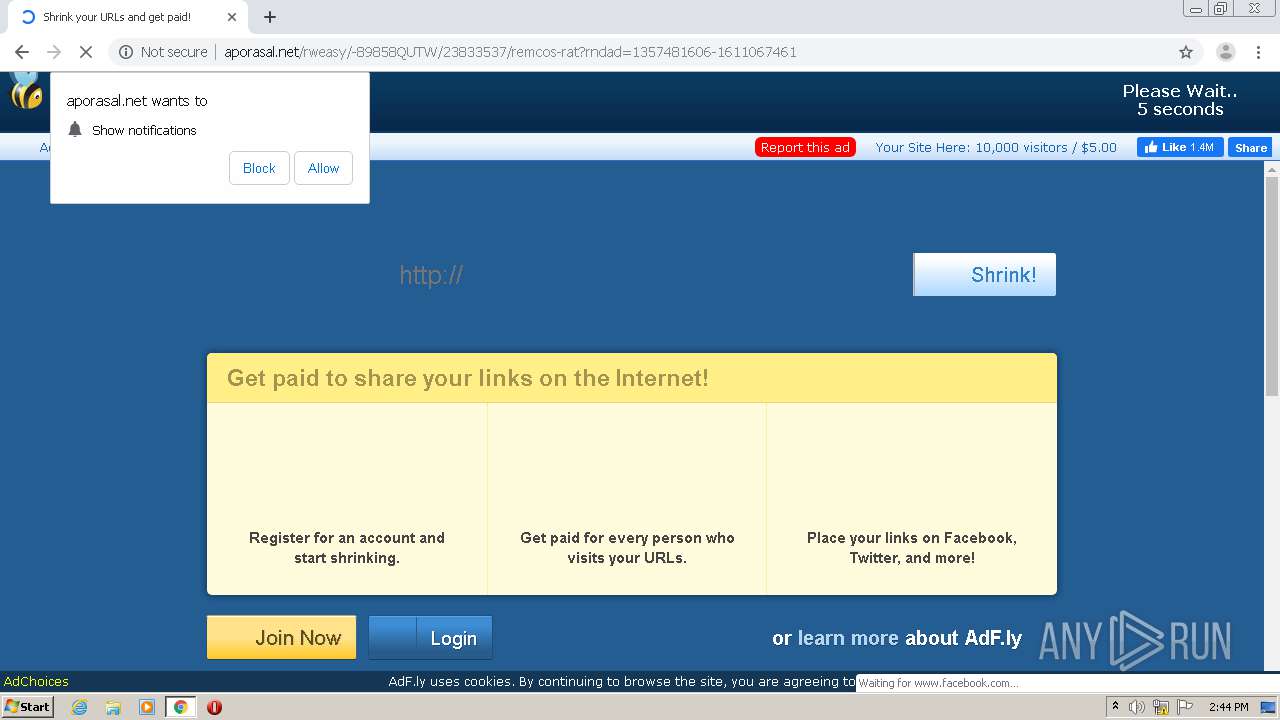
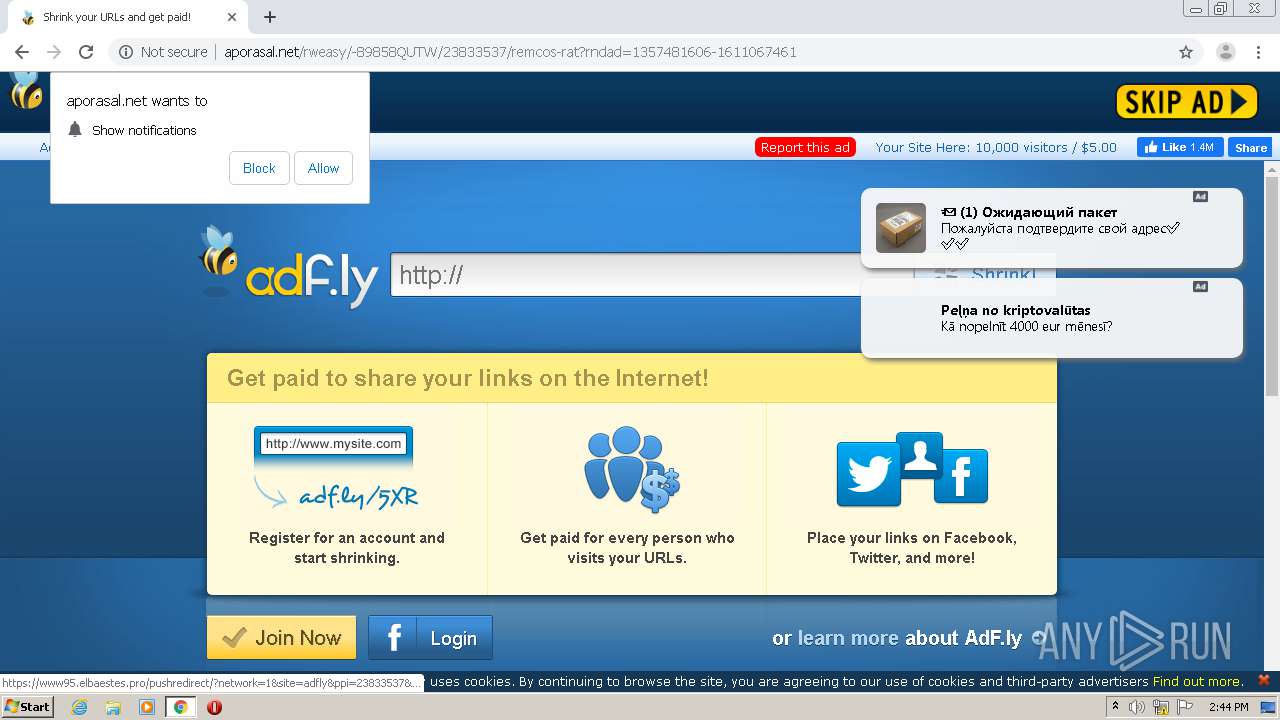
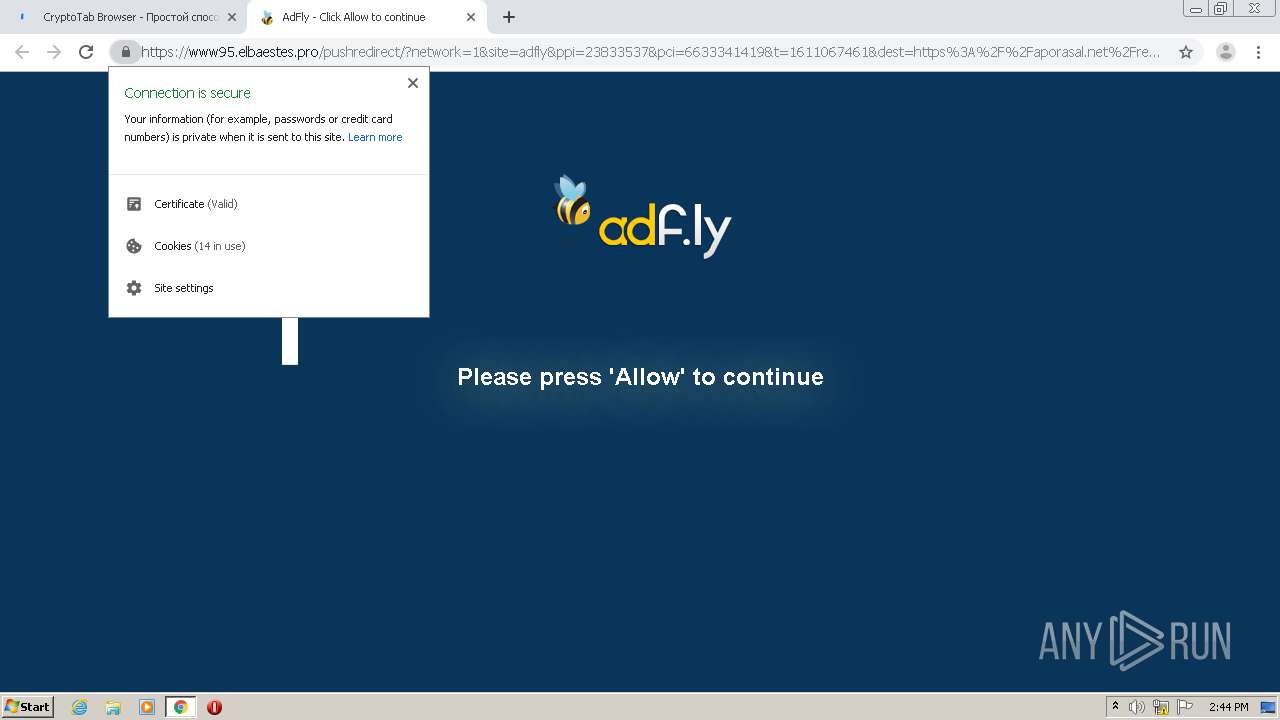
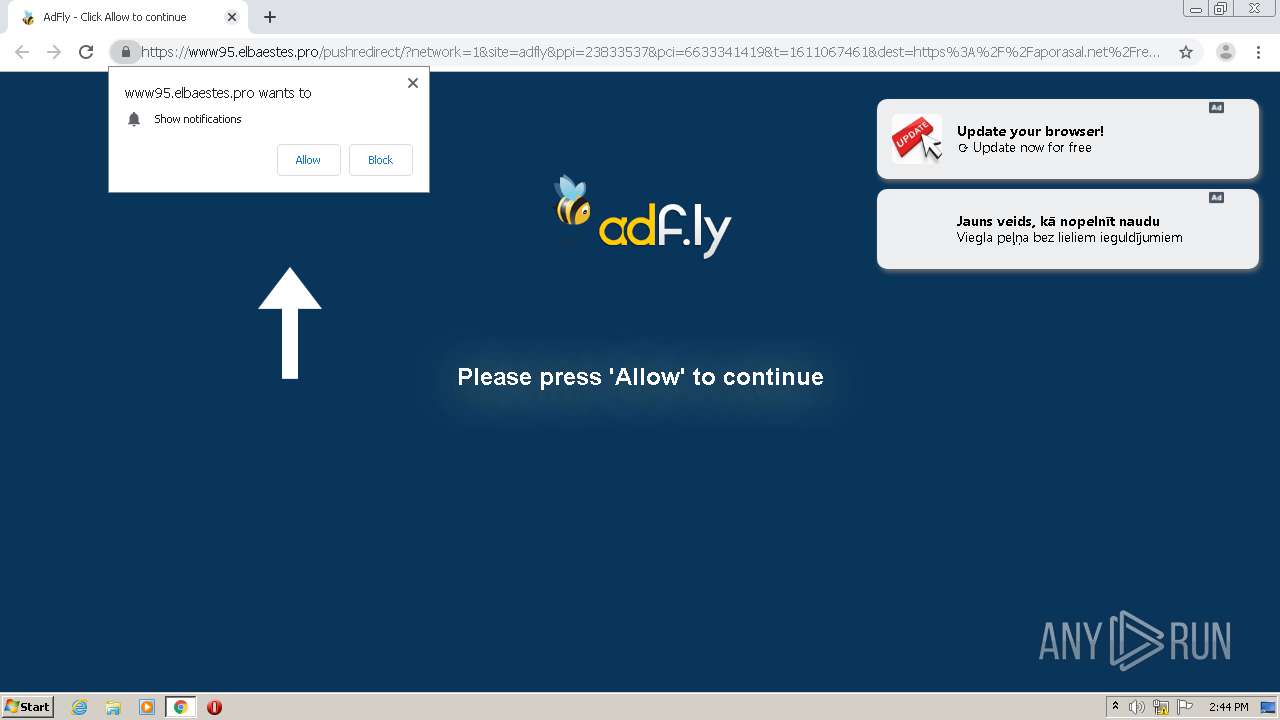
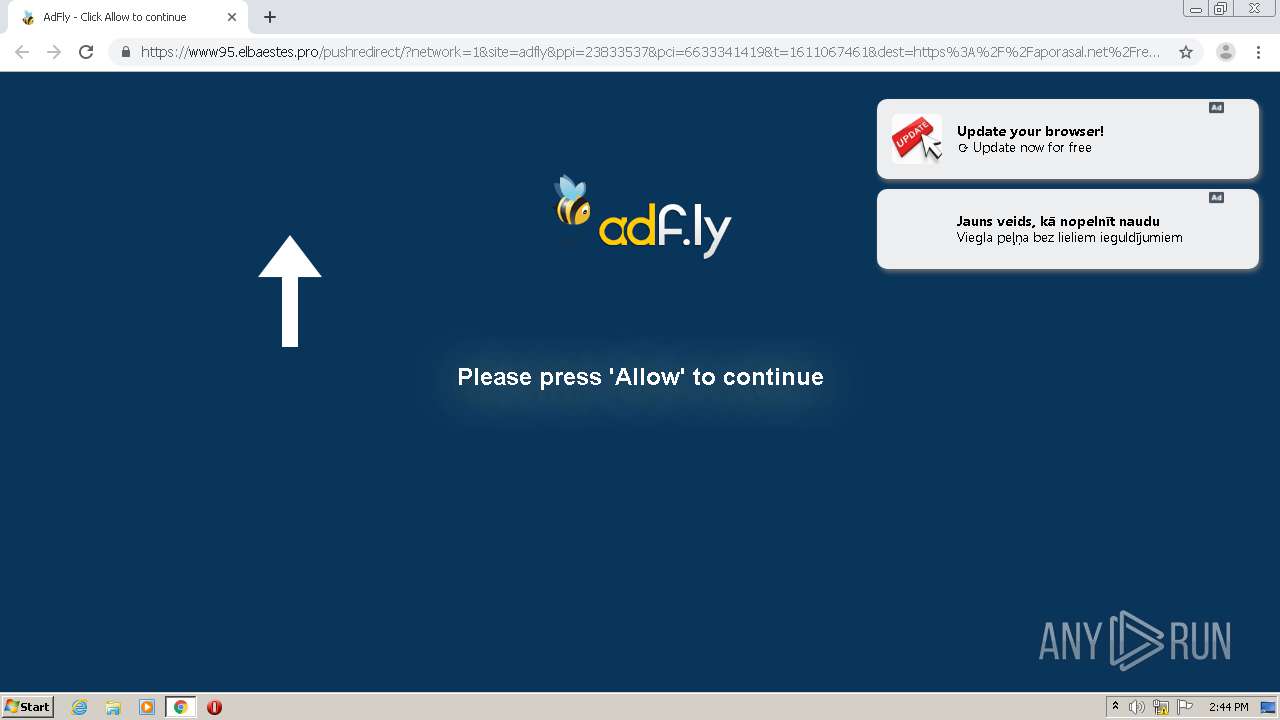
788 | chrome.exe | GET | 301 | 104.21.72.27:80 | http://rantenah.com/23833537/remcos-rat | US | — | — | suspicious |
788 | chrome.exe | GET | 301 | 31.13.92.36:80 | http://www.facebook.com/plugins/like.php?href=https%3A%2F%2Fwww.facebook.com%2Fx19ltd.adfly&width=150&fb_source=unshorten&layout=button_count&action=like&show_faces=false&share=true&height=21&appId=399141353502152 | IE | — | — | whitelisted |
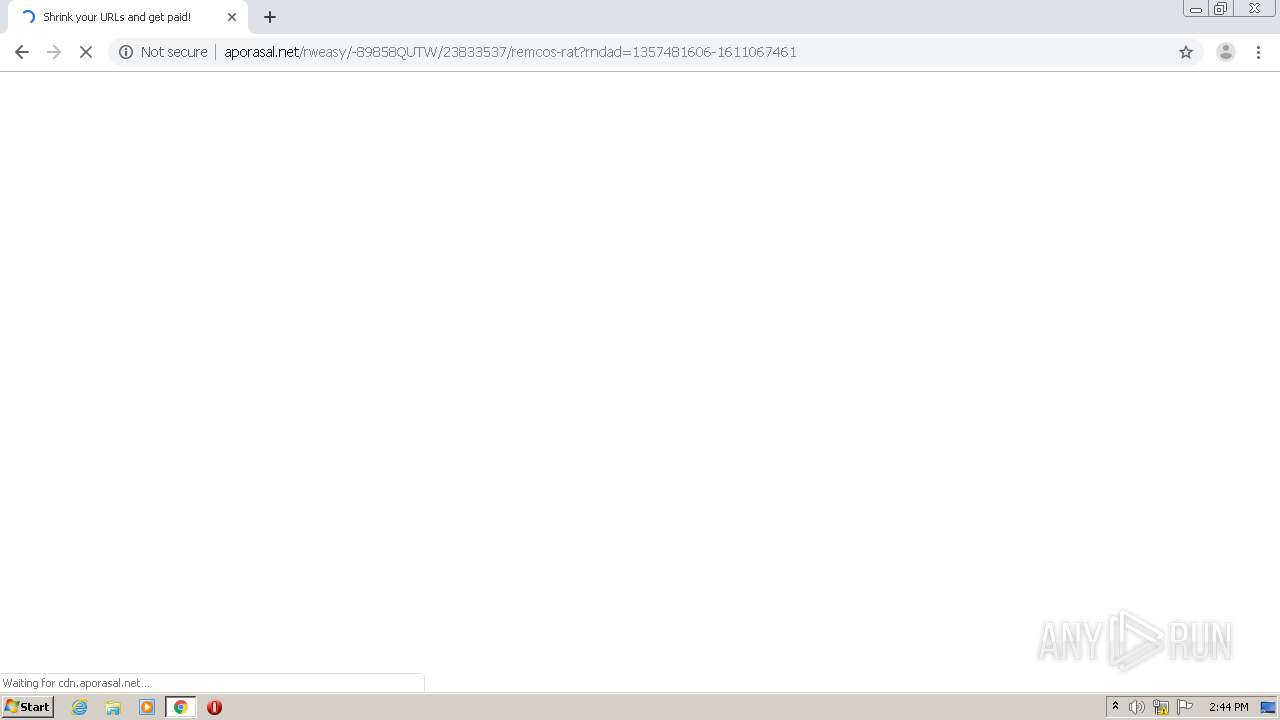
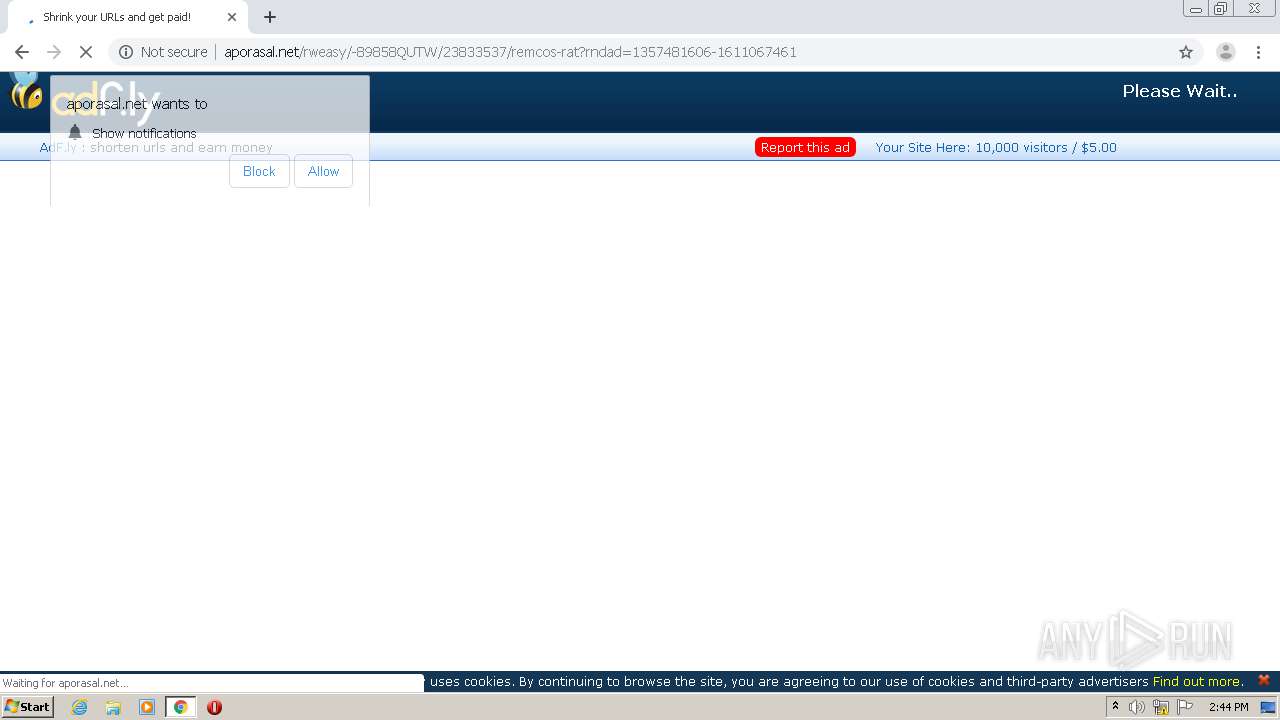
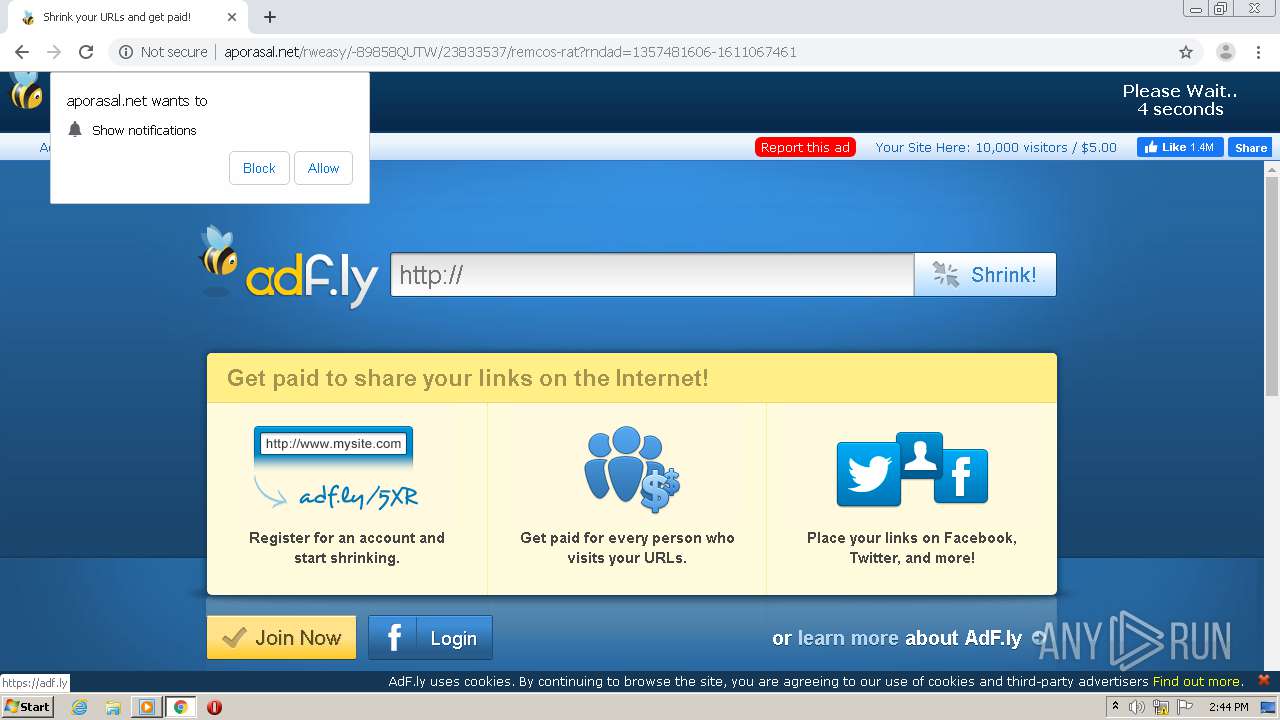
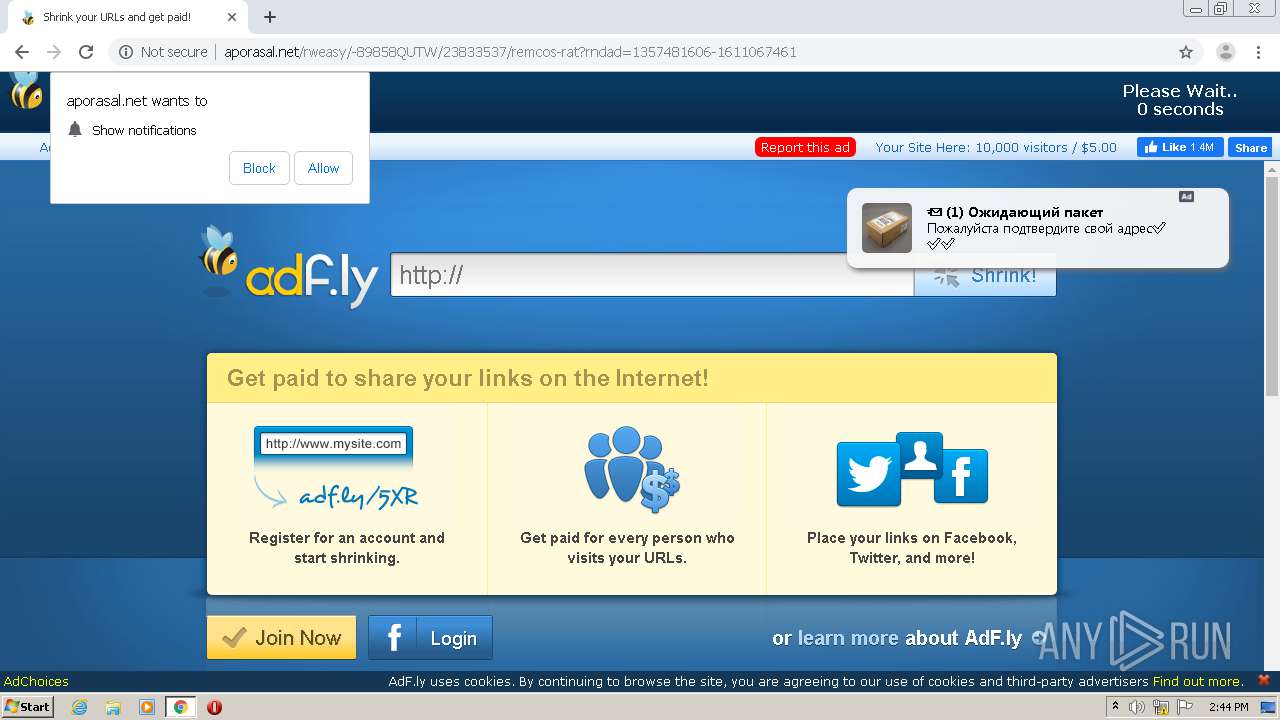
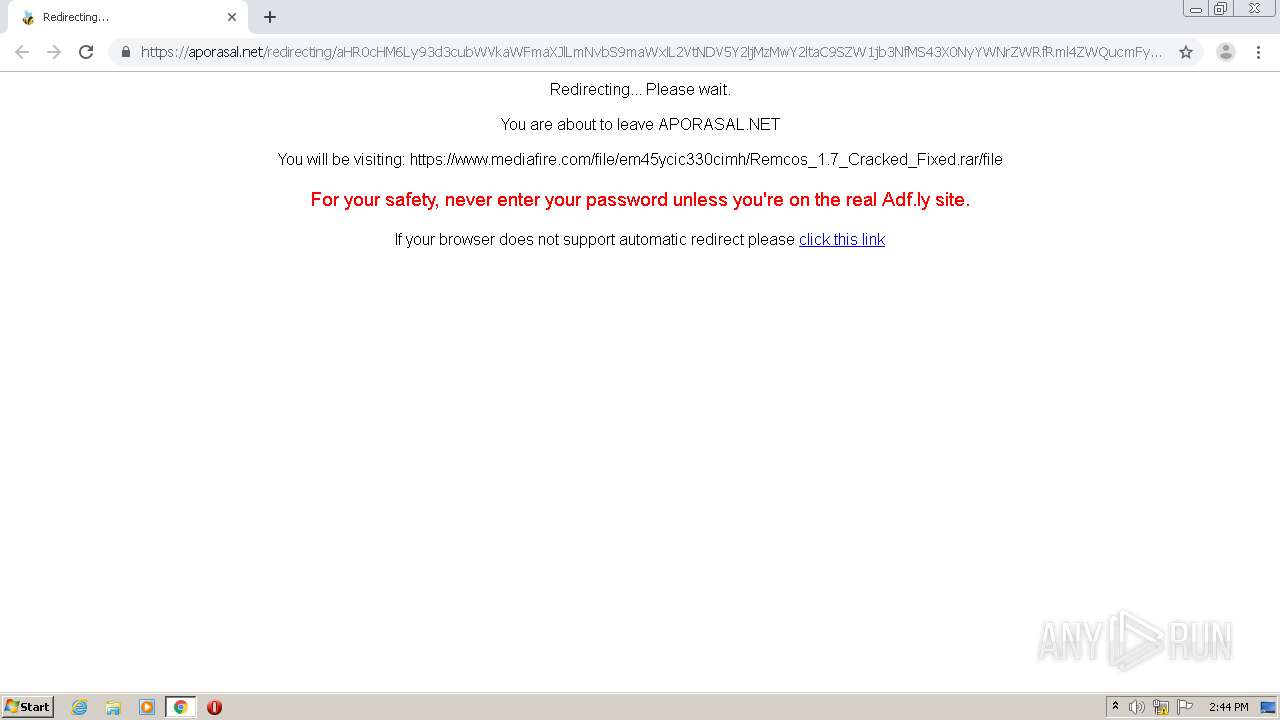
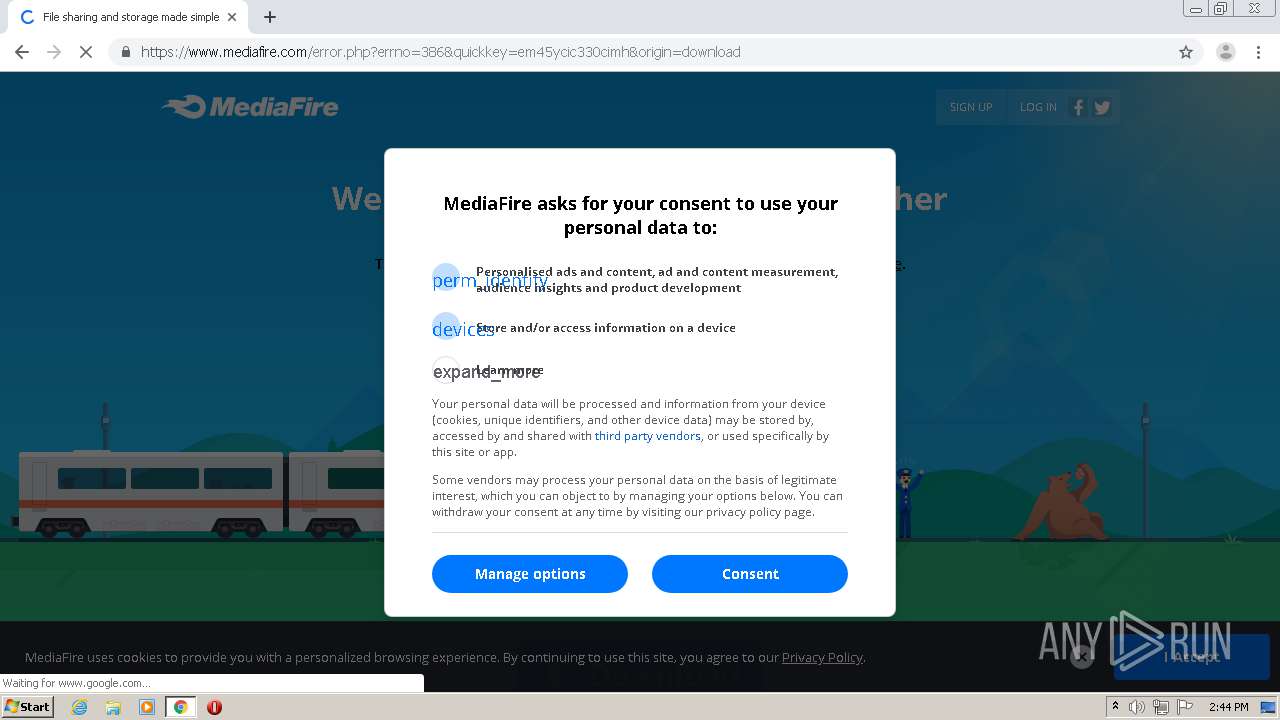
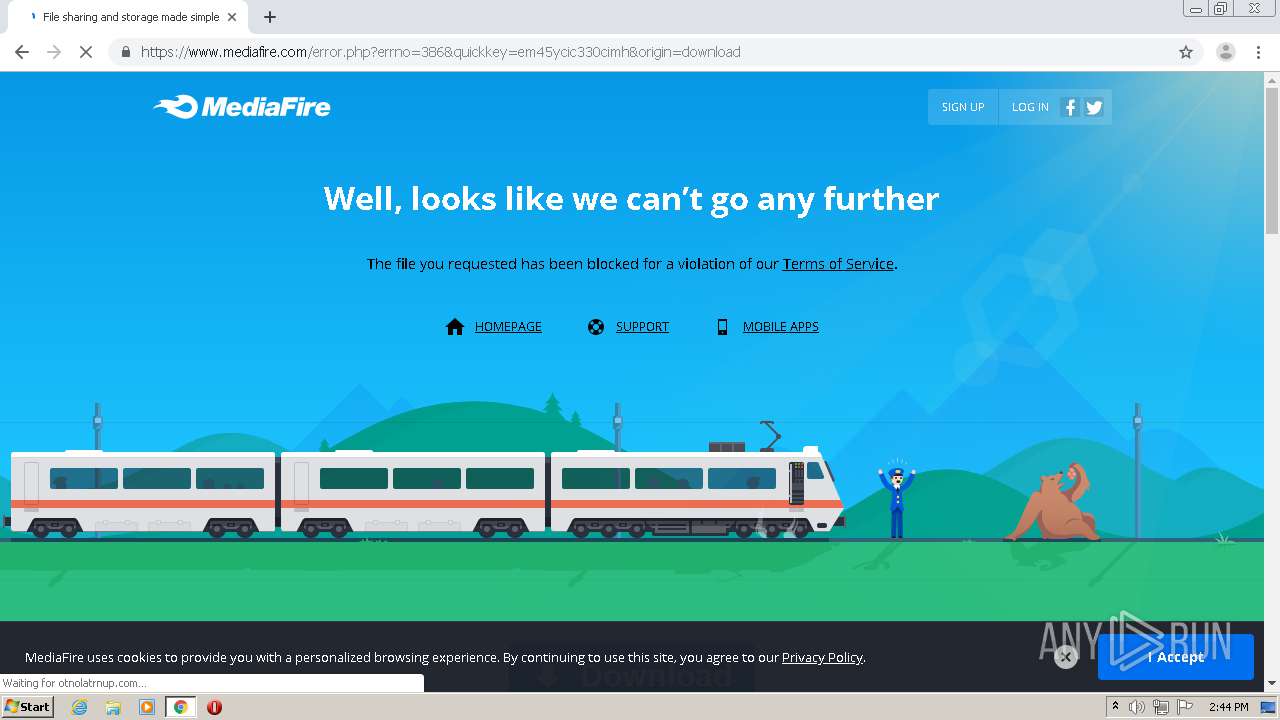
788 | chrome.exe | GET | 200 | 172.64.200.21:80 | http://aporasal.net/rweasy/-89858QUTW/23833537/remcos-rat?rndad=1357481606-1611067461 | US | html | 5.94 Kb | malicious |
788 | chrome.exe | GET | 200 | 172.64.200.21:80 | http://cdn.aporasal.net/static/css/adfly_7.css | US | text | 869 b | shared |
788 | chrome.exe | GET | 200 | 172.64.200.21:80 | http://cdn.aporasal.net/static/js/main.js | US | text | 667 b | shared |
788 | chrome.exe | GET | 200 | 172.64.200.21:80 | http://cdn.aporasal.net/static/js/view111.js | US | text | 28.1 Kb | shared |
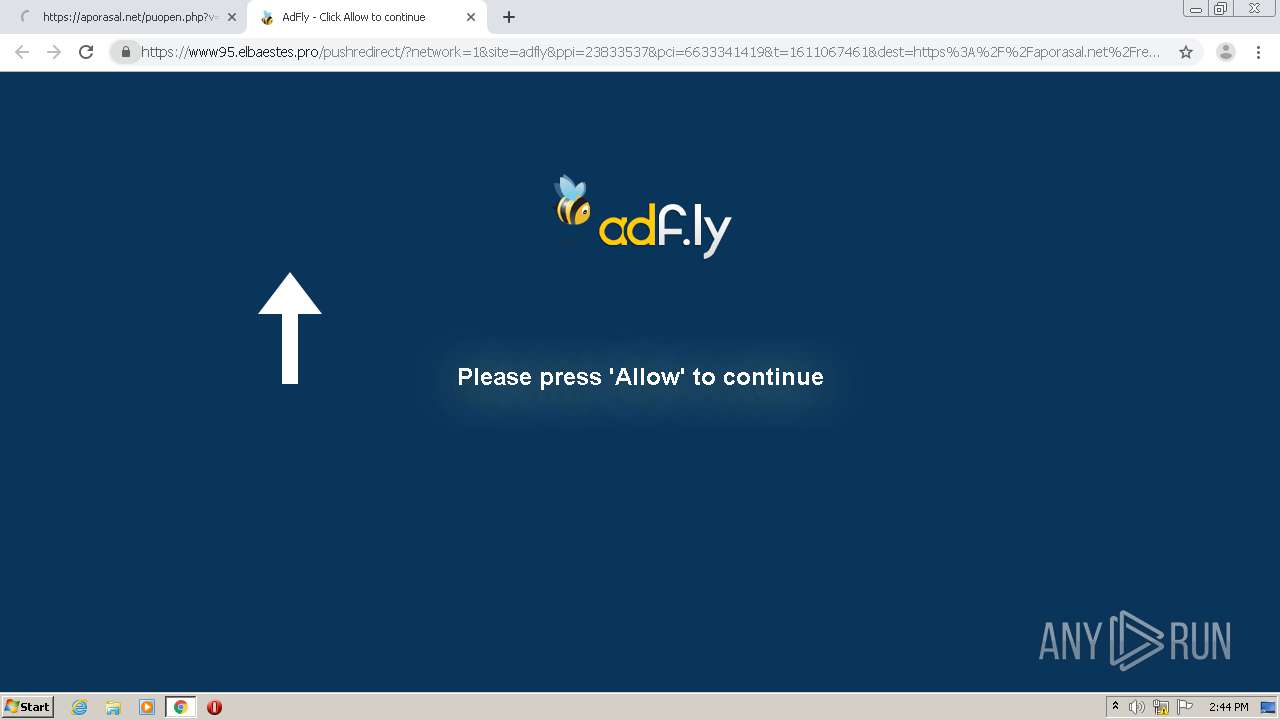
788 | chrome.exe | GET | 200 | 172.64.200.21:80 | http://aporasal.net/fp.rev11.php?ver=23833537&nocache=5551 | US | text | 12.7 Kb | malicious |
788 | chrome.exe | GET | 200 | 143.204.101.163:80 | http://d1nmxiiewlx627.cloudfront.net/?ixmnd=709056 | US | compressed | 35.6 Kb | whitelisted |
788 | chrome.exe | GET | 200 | 172.64.200.21:80 | http://aporasal.net/js/display.js | US | text | 13.1 Kb | malicious |
788 | chrome.exe | GET | 200 | 172.64.200.21:80 | http://cdn.aporasal.net/static/js/b64.js | US | text | 1.07 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
788 | chrome.exe | 74.125.133.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
788 | chrome.exe | 142.250.74.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
788 | chrome.exe | 172.217.212.102:443 | clients1.google.com | Google Inc. | US | whitelisted |
788 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 104.21.72.27:80 | rantenah.com | Cloudflare Inc | US | unknown |
788 | chrome.exe | 172.64.200.21:80 | aporasal.net | Cloudflare Inc | US | shared |
788 | chrome.exe | 104.21.72.27:80 | rantenah.com | Cloudflare Inc | US | unknown |
788 | chrome.exe | 216.58.206.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
788 | chrome.exe | 143.204.101.163:80 | d1nmxiiewlx627.cloudfront.net | — | US | unknown |
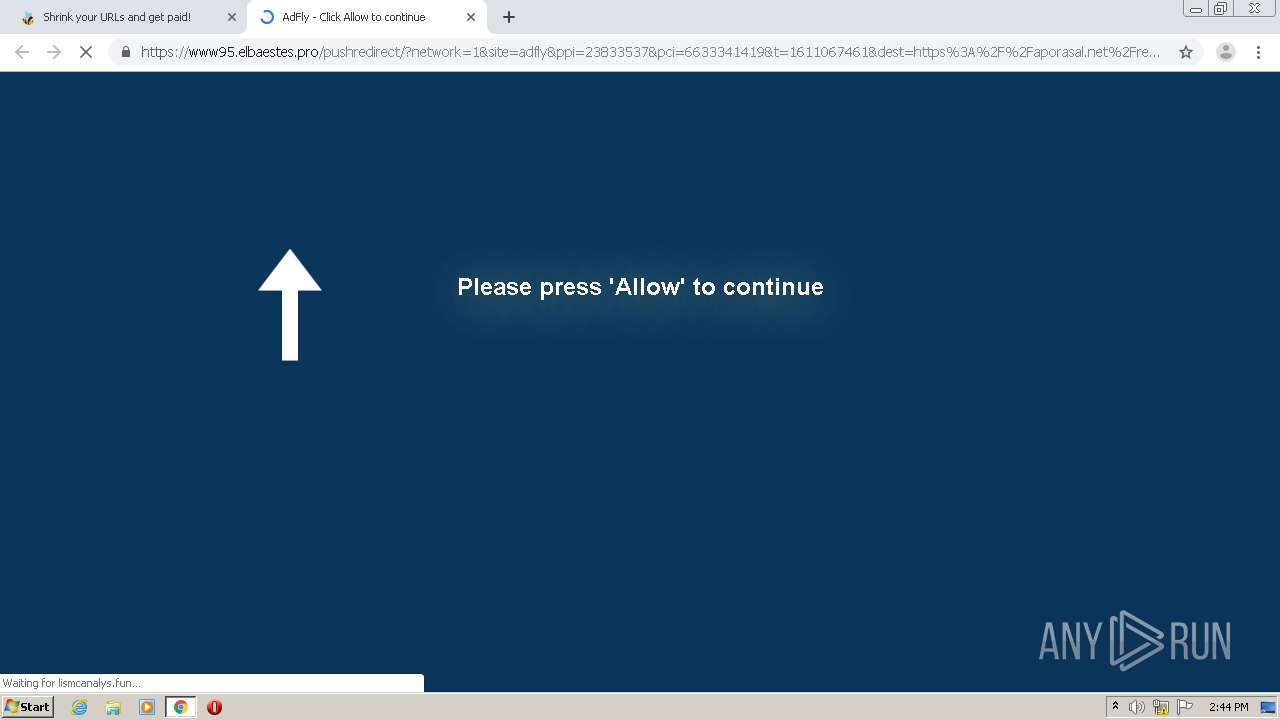
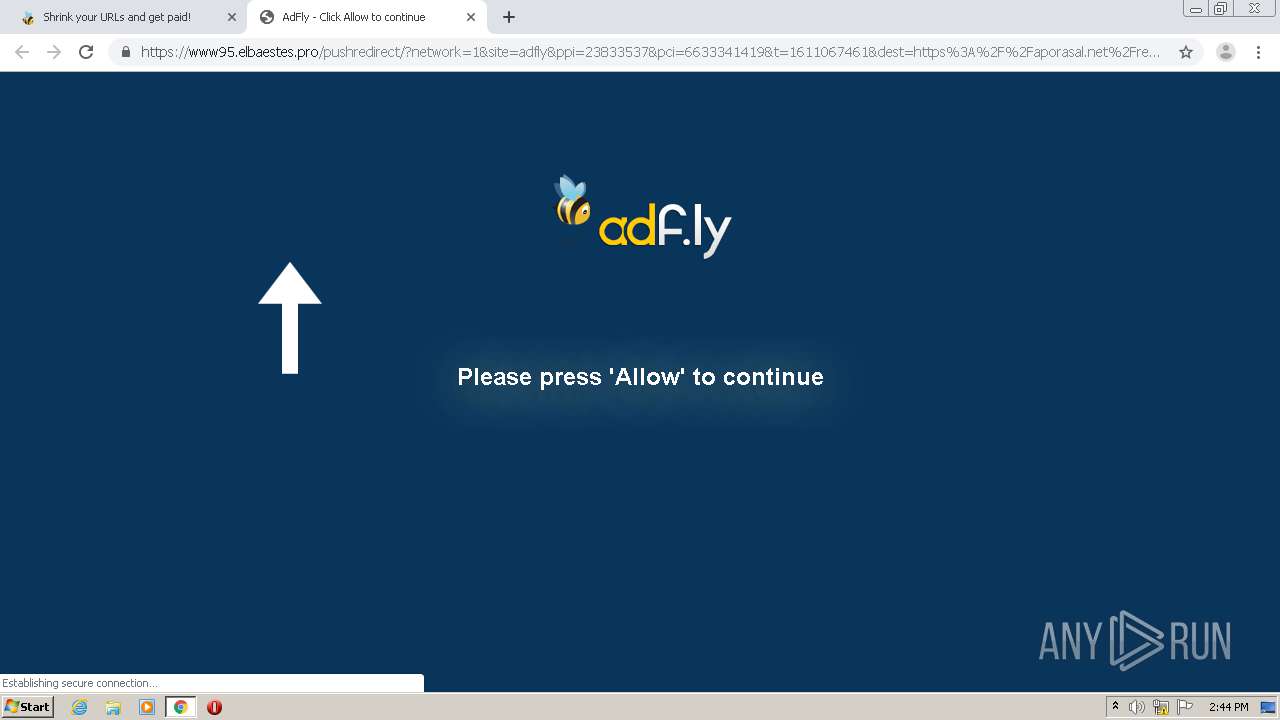
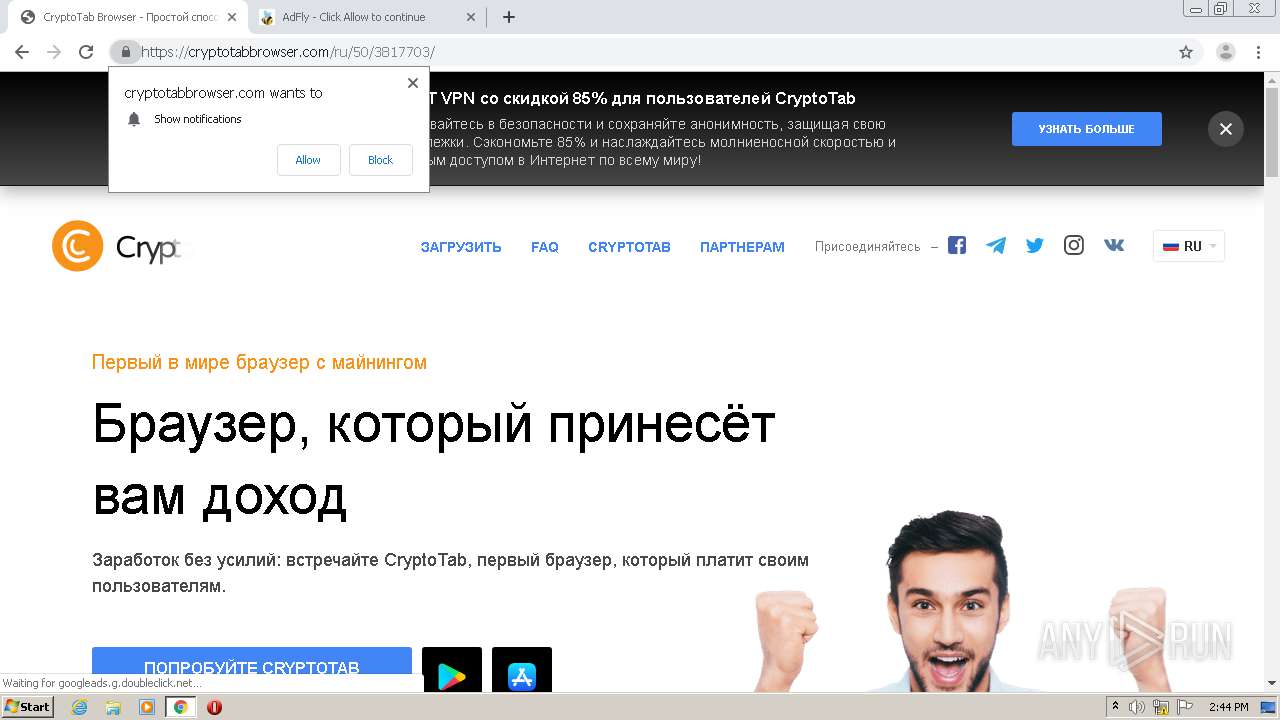
788 | chrome.exe | 99.86.7.14:443 | lismcanalys.fun | AT&T Services, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
accounts.google.com |
| shared |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
rantenah.com |
| suspicious |
aporasal.net |
| malicious |
ajax.googleapis.com |
| whitelisted |
cdn.aporasal.net |
| unknown |
d1nmxiiewlx627.cloudfront.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
788 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
788 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
788 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
788 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
788 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |