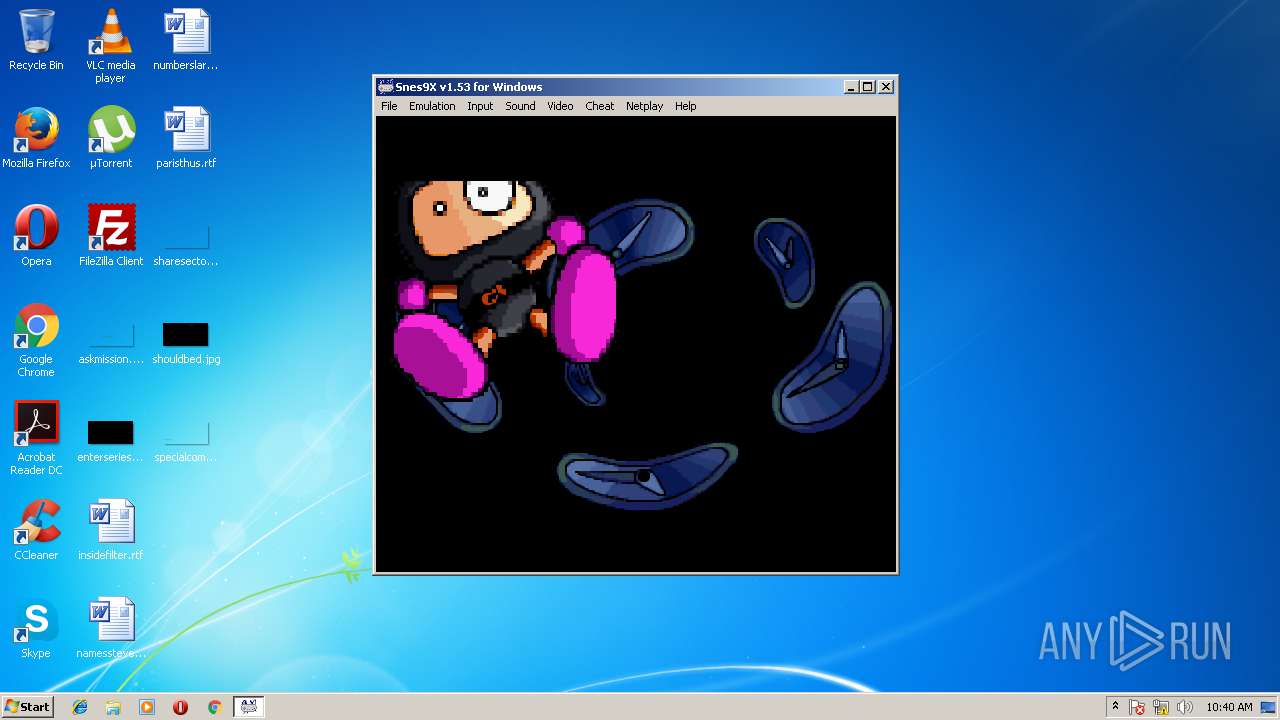
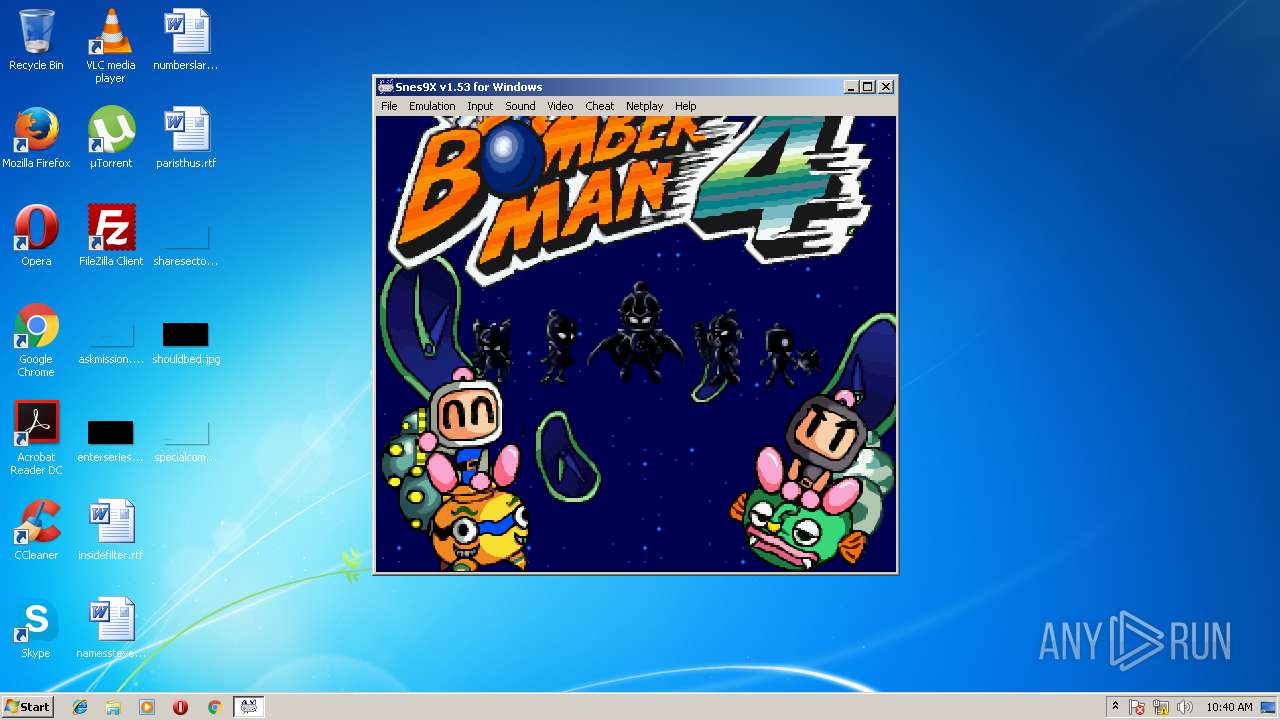
| File name: | [SNES] Super Bomberman 4 (U).exe |
| Full analysis: | https://app.any.run/tasks/f8b37893-22c2-4b60-a738-290ad4e7b565 |
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2018, 09:39:08 |
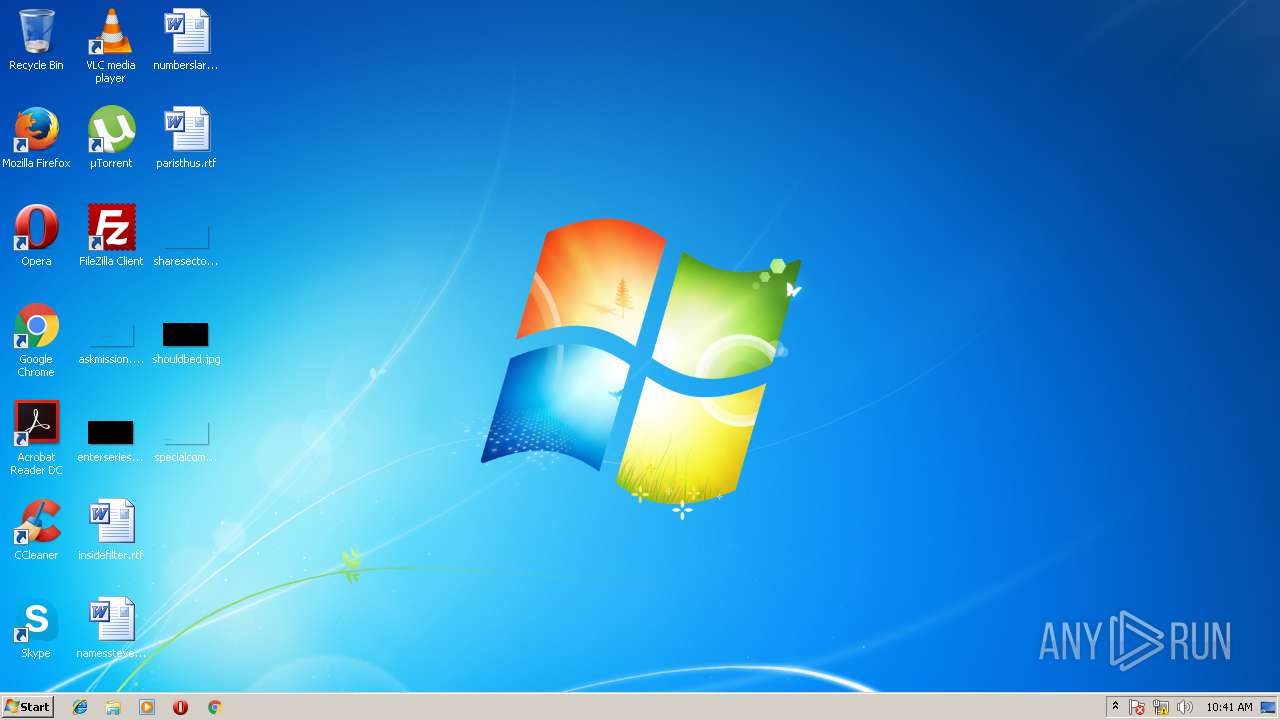
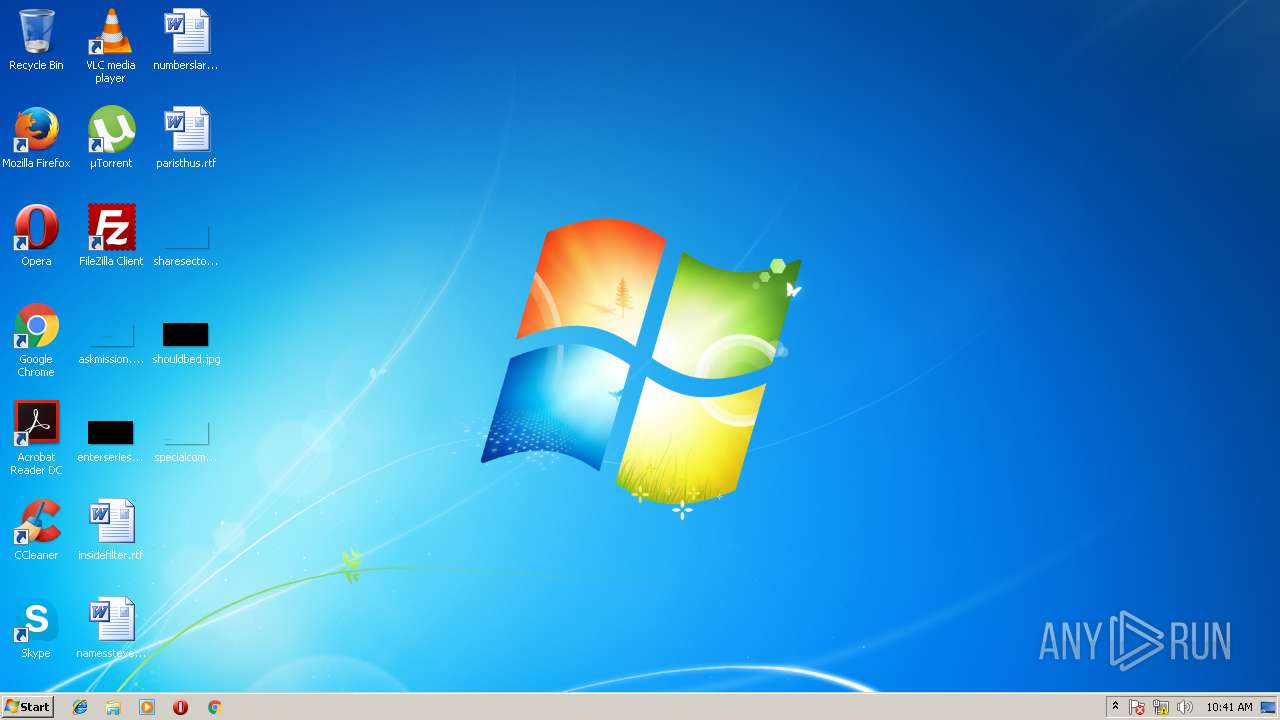
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 169BE8010166EAABA90A59F38BC9CFF8 |
| SHA1: | 30635CA6A562047042C369EC9F8618FF7F69CAAE |
| SHA256: | A81BBCBB6C3C6593E24FAE4ADC82ABA4D696FF90844B66EF20B32307BDFB0F69 |
| SSDEEP: | 98304:G0ubxCP4jzFB/mP+1jB0rVcLTlQAKGsrNDUjE5:vgGPiBZxQesrNUo5 |
MALICIOUS
Application was dropped or rewritten from another process
- snes9x.exe (PID: 3800)
Loads dropped or rewritten executable
- snes9x.exe (PID: 3800)
- SearchProtocolHost.exe (PID: 2540)
SUSPICIOUS
Executable content was dropped or overwritten
- [SNES] Super Bomberman 4 (U).exe (PID: 3852)
Modifies the open verb of a shell class
- snes9x.exe (PID: 3800)
INFO
Dropped object may contain URL's
- [SNES] Super Bomberman 4 (U).exe (PID: 3852)
Dropped object may contain Bitcoin addresses
- [SNES] Super Bomberman 4 (U).exe (PID: 3852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:12:17 17:14:19+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 51712 |
| InitializedDataSize: | 60928 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x98e9 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Dec-2010 16:14:19 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 17-Dec-2010 16:14:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000C961 | 0x0000CA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53423 |
.rdata | 0x0000E000 | 0x00001B75 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.97391 |
.data | 0x00010000 | 0x0001D9D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.29695 |
.CRT | 0x0002E000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.213101 |
.rsrc | 0x0002F000 | 0x0000CCA0 | 0x0000CE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.84724 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.20816 | 1464 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.30274 | 296 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 5.53785 | 3752 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 6.01308 | 2216 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 5.54694 | 1384 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 2.83885 | 16936 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.24143 | 556 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.26996 | 974 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.04375 | 530 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.16254 | 776 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2540 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3800 | "C:\Users\admin\Documents\TopGameRetro\E-SNES9X\snes9x.exe" "[SNES] Super Bomberman 4 (U).smc" | C:\Users\admin\Documents\TopGameRetro\E-SNES9X\snes9x.exe | — | [SNES] Super Bomberman 4 (U).exe | |||||||||||
User: admin Company: http://www.snes9x.com Integrity Level: MEDIUM Description: Snes9X Exit code: 0 Version: 1.53 Modules
| |||||||||||||||
| 3852 | "C:\Users\admin\AppData\Local\Temp\[SNES] Super Bomberman 4 (U).exe" | C:\Users\admin\AppData\Local\Temp\[SNES] Super Bomberman 4 (U).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
946
Read events
852
Write events
94
Delete events
0
Modification events
| (PID) Process: | (3852) [SNES] Super Bomberman 4 (U).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3852) [SNES] Super Bomberman 4 (U).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3800) snes9x.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: snes9x.exe | |||
| (PID) Process: | (3800) snes9x.exe | Key: | HKEY_CLASSES_ROOT\Snes9x.Win32 |
| Operation: | write | Name: | |
Value: Snes9x ROM | |||
| (PID) Process: | (3800) snes9x.exe | Key: | HKEY_CLASSES_ROOT\Snes9x.Win32\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Users\admin\Documents\TopGameRetro\E-SNES9X\snes9x.exe,0 | |||
| (PID) Process: | (3800) snes9x.exe | Key: | HKEY_CLASSES_ROOT\Snes9x.Win32\shell |
| Operation: | write | Name: | |
Value: open | |||
| (PID) Process: | (3800) snes9x.exe | Key: | HKEY_CLASSES_ROOT\Snes9x.Win32\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Users\admin\Documents\TopGameRetro\E-SNES9X\snes9x.exe" "%L" | |||
| (PID) Process: | (3800) snes9x.exe | Key: | HKEY_CLASSES_ROOT\.(null)\OpenWithProgids |
| Operation: | write | Name: | Snes9x.Win32 |
Value: | |||
| (PID) Process: | (3800) snes9x.exe | Key: | HKEY_CLASSES_ROOT\.smc\OpenWithProgids |
| Operation: | write | Name: | Snes9x.Win32 |
Value: | |||
| (PID) Process: | (3800) snes9x.exe | Key: | HKEY_CLASSES_ROOT\.zip\OpenWithProgids |
| Operation: | write | Name: | Snes9x.Win32 |
Value: | |||
Executable files
3
Suspicious files
0
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3800 | snes9x.exe | C:\Users\admin\Documents\TopGameRetro\E-SNES9X\snes9x.conf.autobak | — | |
MD5:— | SHA256:— | |||
| 3852 | [SNES] Super Bomberman 4 (U).exe | C:\Users\admin\Documents\TopGameRetro\E-SNES9X\[SNES] Super Bomberman 4 (U).smc | pi2 | |
MD5:AD79DDFEF6A85835349723588DF65ED6 | SHA256:87CA09DE3242AD3DEF0F59C1F6D47AC74530C254BB574EC95F7C4D5CD87750D8 | |||
| 3852 | [SNES] Super Bomberman 4 (U).exe | C:\Users\admin\Documents\TopGameRetro\E-SNES9X\Access - TopGameRetro!!!.url | text | |
MD5:A5D858CC2BB5526BFE505BA856889F63 | SHA256:1F9593DC86B1F3BF6A569825D05F8D5DBC389FE8C3D454DD0DC139578C35A2EE | |||
| 3800 | snes9x.exe | C:\Users\admin\Documents\TopGameRetro\E-SNES9X\snes9x.conf | text | |
MD5:4FE1C85BF804C1E41350C66CE29094C2 | SHA256:916EEB2CD6EBCDEEF4C310571424780908DD255DFC1F489F9B1BF39BF2CBFC4B | |||
| 3852 | [SNES] Super Bomberman 4 (U).exe | C:\Users\admin\Documents\TopGameRetro\E-SNES9X\snes9x.conf | text | |
MD5:B3DA391F42EFA851CBD9AB9C5F9E9F6D | SHA256:0BF682AB9F4C99EDC051BA4D0E700BB662028DD69B79269E438A3CAAEE0C06BA | |||
| 3800 | snes9x.exe | C:\Users\admin\Documents\TopGameRetro\E-SNES9X\stdout.txt | text | |
MD5:16F0204E7FEDB6F5E83B2A6BF786B864 | SHA256:2F0A50767C3DE467A9ADDB458AC5EB85834397D29364C34ECD1A56BB25783097 | |||
| 3852 | [SNES] Super Bomberman 4 (U).exe | C:\Users\admin\Documents\TopGameRetro\E-SNES9X\Valid.Ext | text | |
MD5:99E7C9707AAE19CF5A07817A570917C5 | SHA256:327BE58F8F2AD1DBA48C4C8B93DD1319076795F98EEED8B346BDCF24A5A9FAB3 | |||
| 3852 | [SNES] Super Bomberman 4 (U).exe | C:\Users\admin\Documents\TopGameRetro\E-SNES9X\snes9x.exe | executable | |
MD5:F7A21F9840C86E3F877BCE77B5463E4C | SHA256:27337DF942836ABC7AFB29AE26CA3AC7E7E83C04A176F114B0162A55841B9DFA | |||
| 3852 | [SNES] Super Bomberman 4 (U).exe | C:\Users\admin\Documents\TopGameRetro\E-SNES9X\fmodex.dll | executable | |
MD5:128A9D2C5EB4923E952EB658EC2310BF | SHA256:0CCF06B14EF7EAEAAEDF0DAB2CF9B5638AF28445BAADDE8899D662BB7756EBA4 | |||
| 3852 | [SNES] Super Bomberman 4 (U).exe | C:\Users\admin\Documents\TopGameRetro\E-SNES9X\d3dx9_38.dll | executable | |
MD5:8F3EB548AC4ED90252394F60C77E3196 | SHA256:743E77A228E7D75442263AD70051E44534F7972C6326FD34B505A9C2C245894B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report