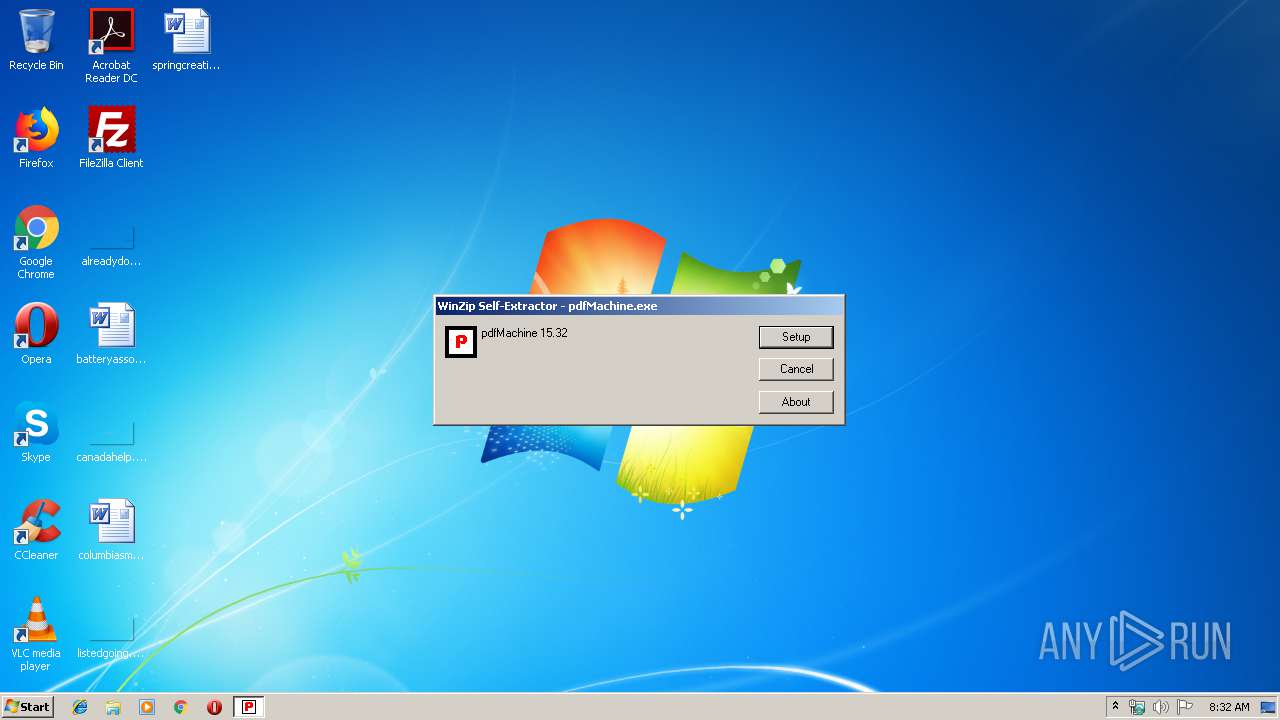
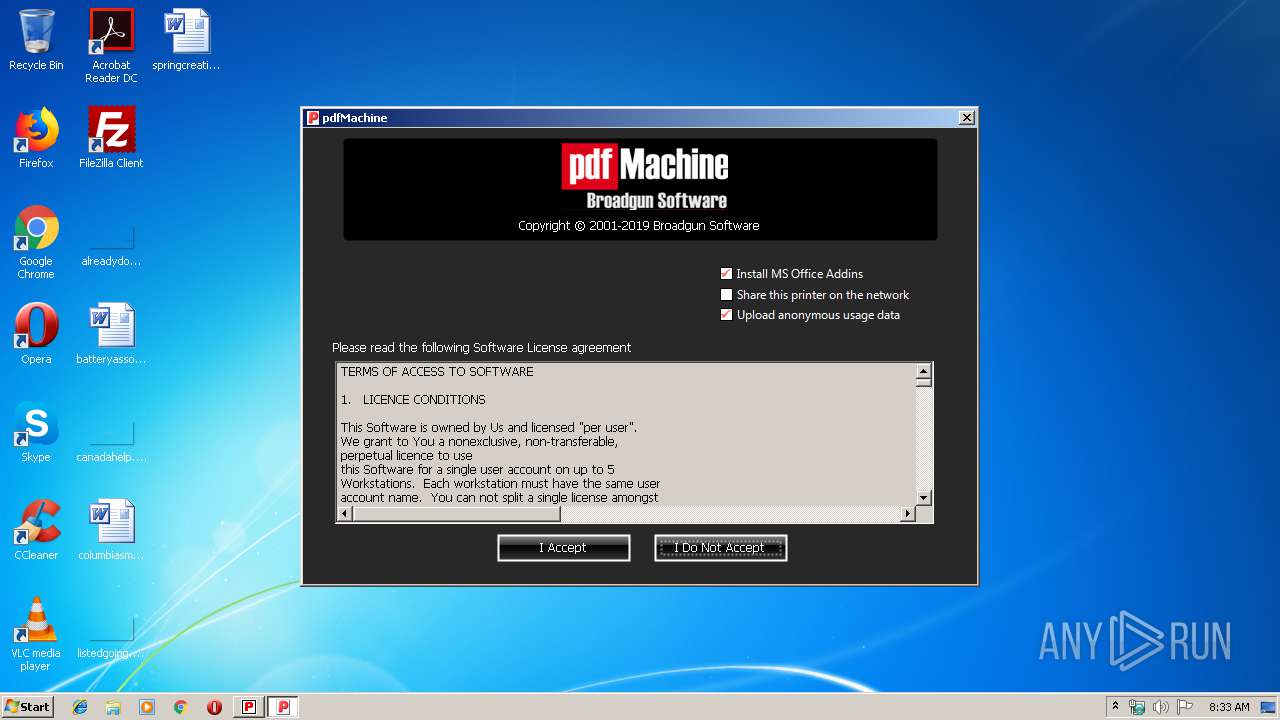
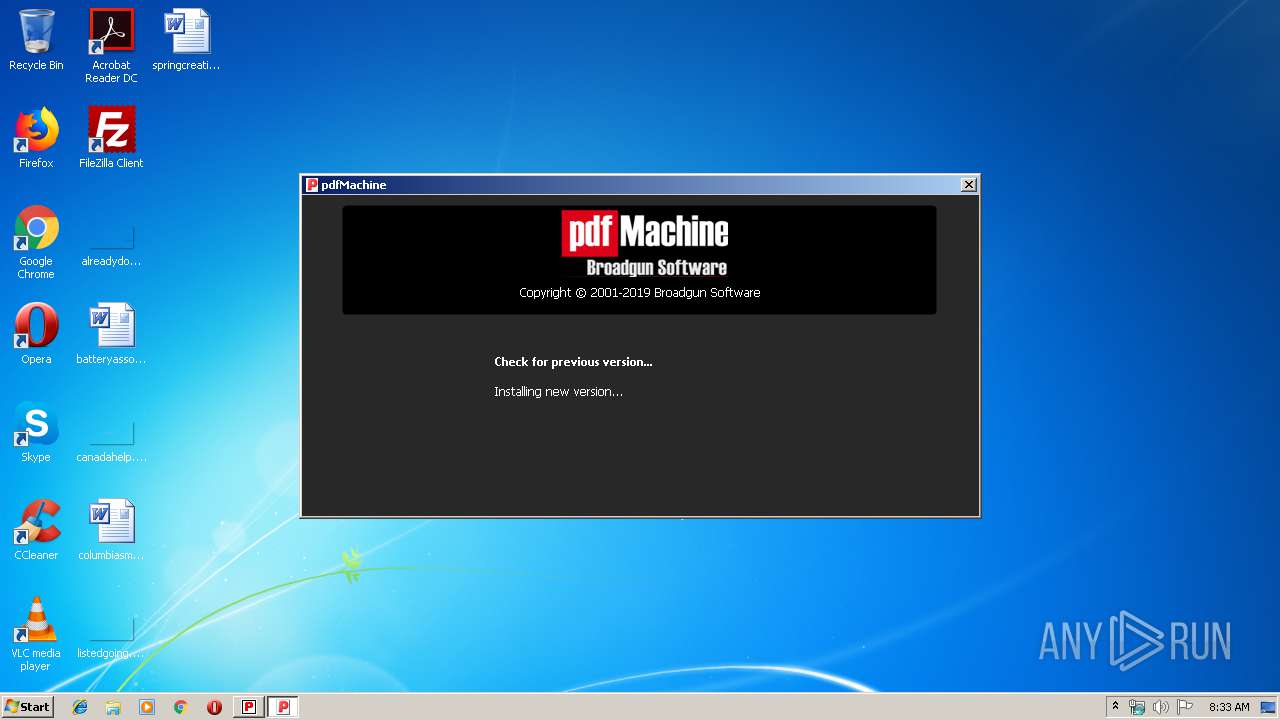
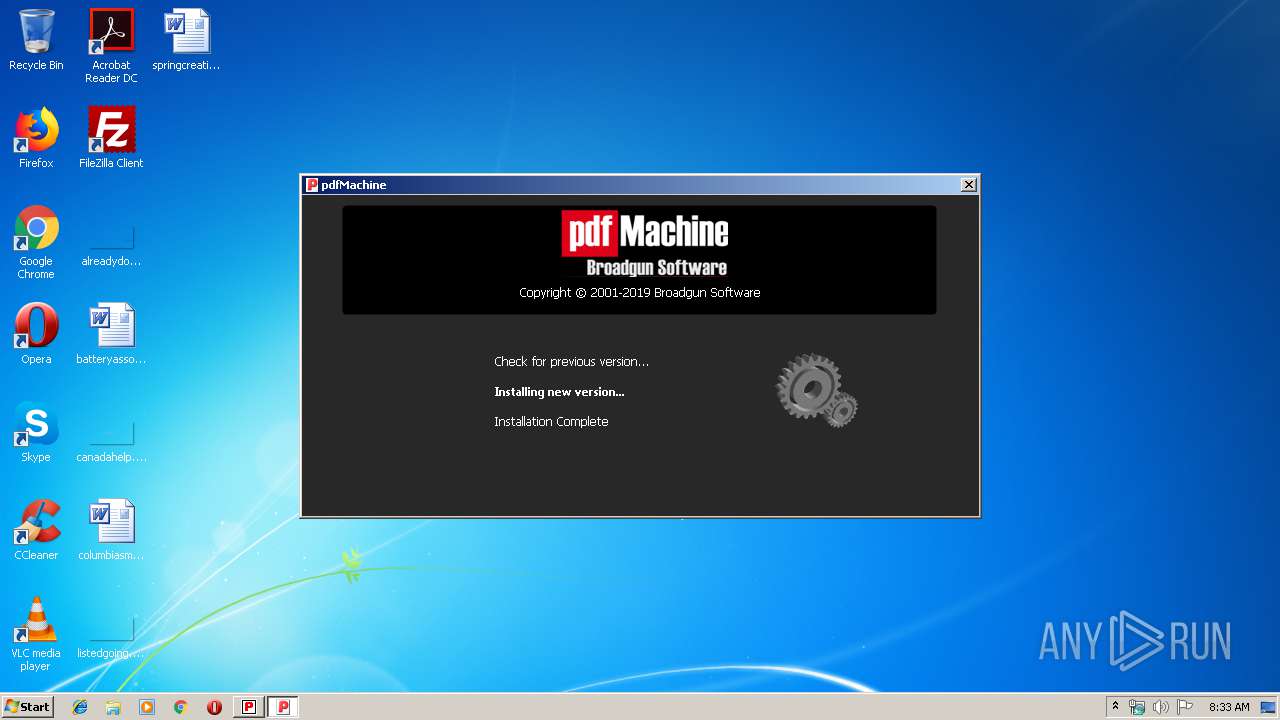
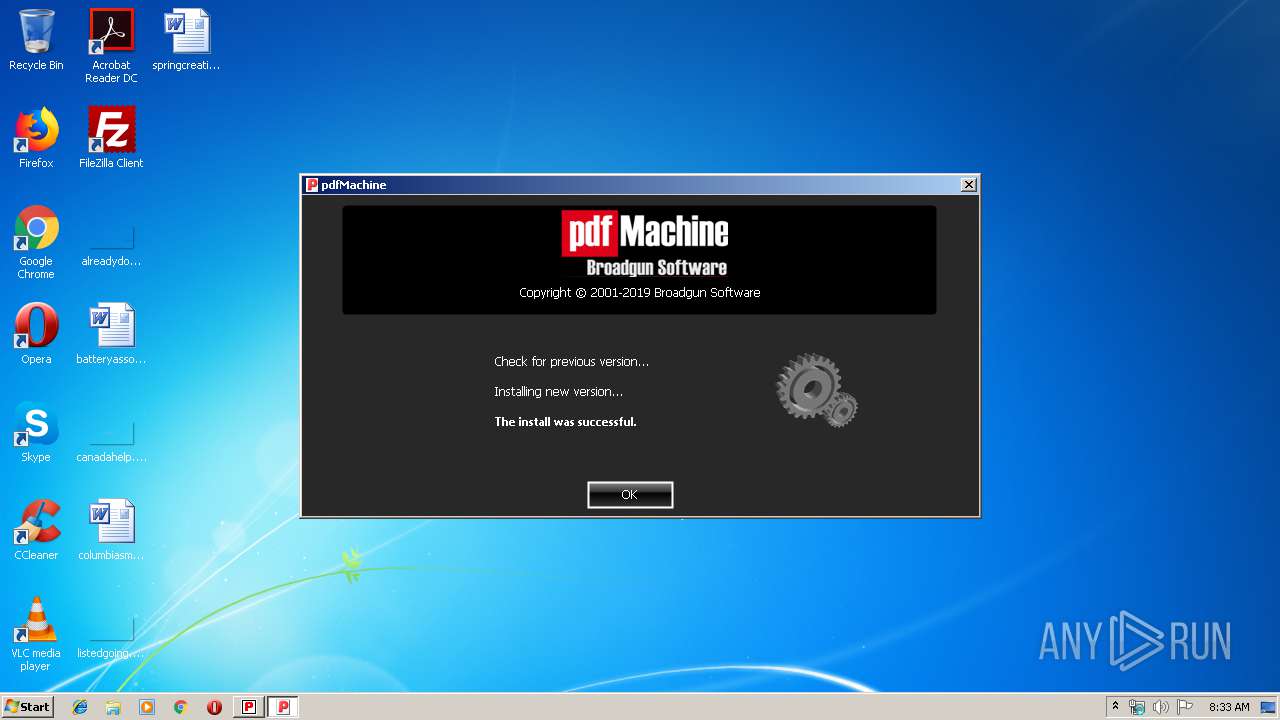
| File name: | pdfMachine.exe |
| Full analysis: | https://app.any.run/tasks/a3c16508-8c07-444f-834d-2fbd8fefd923 |
| Verdict: | Malicious activity |
| Analysis date: | September 23, 2019, 07:32:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 694A4D543D79EEC3302B49D3D822A9D6 |
| SHA1: | CE946F1CFFFA38DB1382B26BF737058A6A037BDC |
| SHA256: | A8177190E6F3665A3C9FA32DFD8BF43652ED5CE1837A57D2883816147F531D97 |
| SSDEEP: | 393216:6p0eekfHWz/Mb8/xBYuqJapG7I9gl2LpJ:MLW7/xB7BG7QwMpJ |
MALICIOUS
Loads dropped or rewritten executable
- spoolsv.exe (PID: 1196)
- regsvr32.exe (PID: 1004)
- bgsview.exe (PID: 1632)
- iexplore.exe (PID: 1344)
- svchost.exe (PID: 852)
- iexplore.exe (PID: 2608)
- regsvr32.exe (PID: 2692)
- bgsview.exe (PID: 1932)
- WerFault.exe (PID: 3984)
- regsvr32.exe (PID: 3424)
- regsvr32.exe (PID: 2860)
- regsvr32.exe (PID: 1076)
- iexplore.exe (PID: 1756)
- iexplore.exe (PID: 2300)
- WerFault.exe (PID: 2688)
Application was dropped or rewritten from another process
- bgsview.exe (PID: 1632)
- bgsview.exe (PID: 1932)
- bgssetup.exe (PID: 2212)
- bgsmsnd.exe (PID: 1088)
Registers / Runs the DLL via REGSVR32.EXE
- spoolsv.exe (PID: 1196)
- bgssetup.exe (PID: 2212)
Changes the autorun value in the registry
- bgssetup.exe (PID: 2212)
SUSPICIOUS
Creates files in the Windows directory
- bgssetup.exe (PID: 2212)
- spoolsv.exe (PID: 1196)
- ie4uinit.exe (PID: 3696)
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 1344)
- WerFault.exe (PID: 3984)
Executable content was dropped or overwritten
- pdfMachine.exe (PID: 876)
- spoolsv.exe (PID: 1196)
- bgssetup.exe (PID: 2212)
Removes files from Windows directory
- spoolsv.exe (PID: 1196)
- WerFault.exe (PID: 3984)
- iexplore.exe (PID: 2608)
Creates COM task schedule object
- regsvr32.exe (PID: 1004)
- regsvr32.exe (PID: 2692)
- ssvagent.exe (PID: 3448)
- regsvr32.exe (PID: 3424)
- regsvr32.exe (PID: 2860)
- regsvr32.exe (PID: 1076)
Executed via COM
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 1756)
Writes to a desktop.ini file (may be used to cloak folders)
- ie4uinit.exe (PID: 3696)
Creates a software uninstall entry
- bgssetup.exe (PID: 2212)
Creates files in the program directory
- WerFault.exe (PID: 3984)
- bgssetup.exe (PID: 2212)
- WerFault.exe (PID: 2688)
Modifies the open verb of a shell class
- bgssetup.exe (PID: 2212)
INFO
Writes to a desktop.ini file (may be used to cloak folders)
- iexplore.exe (PID: 2608)
Application launched itself
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 1756)
Changes internet zones settings
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 1756)
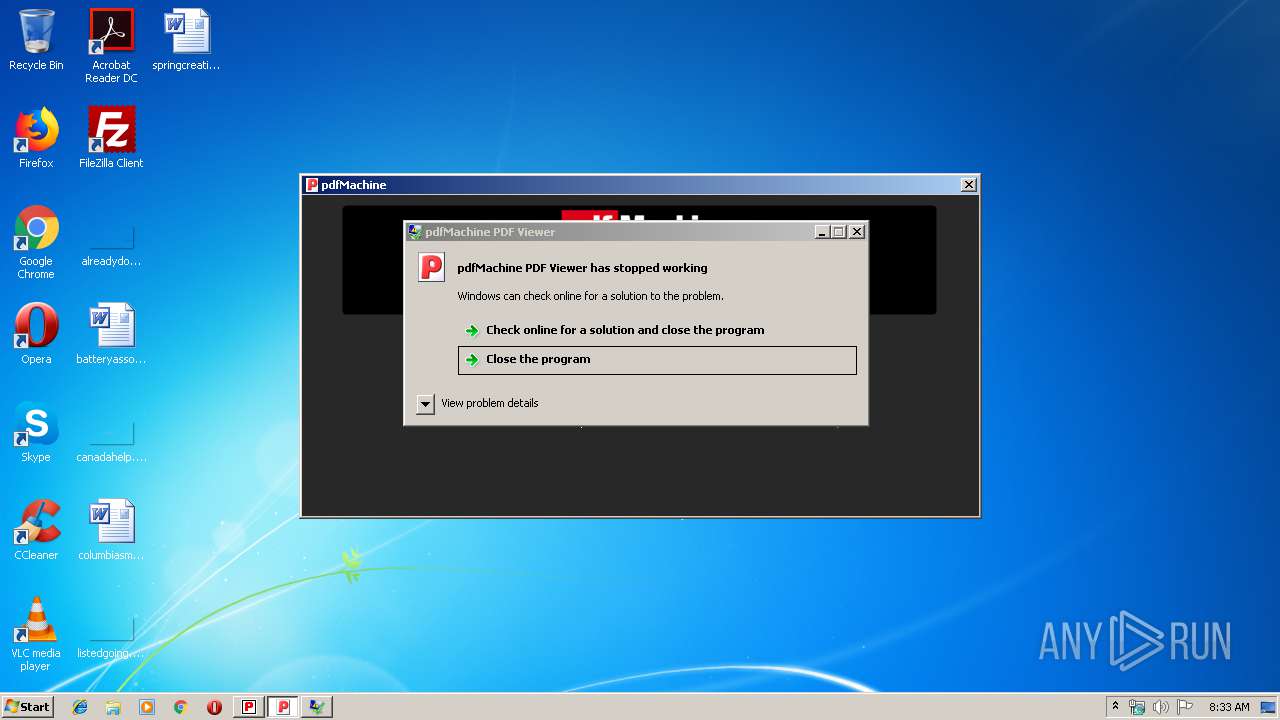
Application was crashed
- bgsview.exe (PID: 1632)
- bgsview.exe (PID: 1932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (28.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (25.1) |
| .exe | | | Winzip Win32 self-extracting archive (generic) (20.9) |
| .scr | | | Windows screen saver (11.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:07:23 19:30:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 61440 |
| InitializedDataSize: | 36864 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7eb8 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Jul-2007 17:30:02 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 23-Jul-2007 17:30:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000E6D8 | 0x0000F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43285 |
.rdata | 0x00010000 | 0x000029F2 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18273 |
.data | 0x00013000 | 0x000062E4 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.58546 |
.rsrc | 0x0001A000 | 0x000037F0 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.31782 |
_winzip_ | 0x0001E000 | 0x00DC8000 | 0x00DC8000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.99806 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.83356 | 989 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.27745 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
63 | 3.18826 | 764 | Latin 1 / Western European | English - United States | RT_STRING |
64 | 3.37002 | 1496 | Latin 1 / Western European | English - United States | RT_STRING |
65 | 3.39511 | 2382 | Latin 1 / Western European | English - United States | RT_STRING |
66 | 3.44783 | 2322 | Latin 1 / Western European | English - United States | RT_STRING |
67 | 3.39647 | 1278 | Latin 1 / Western European | English - United States | RT_STRING |
100 | 3.08197 | 290 | Latin 1 / Western European | English - United States | RT_DIALOG |
126 | 3.58134 | 1304 | Latin 1 / Western European | English - United States | RT_STRING |
127 | 2.47759 | 110 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
58
Monitored processes
21
Malicious processes
6
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 852 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | "C:\Users\admin\AppData\Local\Temp\pdfMachine.exe" | C:\Users\admin\AppData\Local\Temp\pdfMachine.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1004 | C:\Windows\system32\regsvr32.exe /s C:\Windows\system32\spool\DRIVERS\W32X86\3\\bgsofice.dll | C:\Windows\system32\regsvr32.exe | — | spoolsv.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1076 | regsvr32 /s C:\Windows\system32\spool\DRIVERS\W32X86\3\bgsSE.dll | C:\Windows\system32\regsvr32.exe | — | bgssetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | C:\Windows\system32\spool\DRIVERS\W32X86\3\bgsmsnd.exe | C:\Windows\system32\spool\DRIVERS\W32X86\3\bgsmsnd.exe | — | bgssetup.exe | |||||||||||
User: admin Company: Broadgun Software Integrity Level: HIGH Description: pdfMachine background process Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1196 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2608 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1632 | "C:\Windows\system32\spool\DRIVERS\W32X86\3\bgsview.exe" -RegServer | C:\Windows\system32\spool\DRIVERS\W32X86\3\bgsview.exe | spoolsv.exe | ||||||||||||
User: SYSTEM Company: Broadgun Software Pty Ltd Integrity Level: SYSTEM Description: pdfMachine PDF Viewer Exit code: 255 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1932 | C:\Windows\system32\spool\DRIVERS\W32X86\3\bgsview.exe -RegServer | C:\Windows\system32\spool\DRIVERS\W32X86\3\bgsview.exe | bgssetup.exe | ||||||||||||
User: admin Company: Broadgun Software Pty Ltd Integrity Level: HIGH Description: pdfMachine PDF Viewer Exit code: 3221225477 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
1 559
Read events
825
Write events
695
Delete events
39
Modification events
| (PID) Process: | (2212) bgssetup.exe | Key: | HKEY_CURRENT_USER\Software\pdfMachine |
| Operation: | write | Name: | printerName |
Value: Broadgun pdfMachine | |||
| (PID) Process: | (2212) bgssetup.exe | Key: | HKEY_CURRENT_USER\Software\pdfMachine\Broadgun pdfMachine |
| Operation: | write | Name: | NextAction |
Value: 3 | |||
| (PID) Process: | (2212) bgssetup.exe | Key: | HKEY_CURRENT_USER\Software\pdfMachine\Broadgun pdfMachine |
| Operation: | write | Name: | SaveFilenameAction |
Value: 3 | |||
| (PID) Process: | (2212) bgssetup.exe | Key: | HKEY_CURRENT_USER\Software\pdfMachine\Broadgun pdfMachine |
| Operation: | write | Name: | DefaultSaveDir |
Value: C:\Users\admin\AppData\Local\pdfMachine | |||
| (PID) Process: | (2212) bgssetup.exe | Key: | HKEY_CURRENT_USER\Software\pdfMachine\Broadgun pdfMachine |
| Operation: | write | Name: | LastDir |
Value: C:\Users\admin\Documents | |||
| (PID) Process: | (2212) bgssetup.exe | Key: | HKEY_CURRENT_USER\Software\pdfMachine\Broadgun pdfMachine |
| Operation: | write | Name: | ExecCmdLine |
Value: C:\Windows\system32\spool\DRIVERS\W32X86\3\bgsview.exe -nav="%s" -docname="%s" | |||
| (PID) Process: | (2212) bgssetup.exe | Key: | HKEY_CURRENT_USER\Software\pdfMachine\Broadgun pdfMachine |
| Operation: | write | Name: | DefaultSaveFilename |
Value: {DOC}.pdf | |||
| (PID) Process: | (2212) bgssetup.exe | Key: | HKEY_CURRENT_USER\Software\pdfMachine\Broadgun pdfMachine |
| Operation: | write | Name: | resIndex |
Value: 3 | |||
| (PID) Process: | (2212) bgssetup.exe | Key: | HKEY_CURRENT_USER\Software\pdfMachine\Broadgun pdfMachine |
| Operation: | write | Name: | jpegImageQuality |
Value: 75 | |||
| (PID) Process: | (2212) bgssetup.exe | Key: | HKEY_CURRENT_USER\Software\pdfMachine\Broadgun pdfMachine |
| Operation: | write | Name: | imageDPI |
Value: 300 | |||
Executable files
108
Suspicious files
4
Text files
19
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 852 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 876 | pdfMachine.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\BgsOfice.dll | executable | |
MD5:— | SHA256:— | |||
| 876 | pdfMachine.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\bgshelp.chm | chm | |
MD5:— | SHA256:— | |||
| 876 | pdfMachine.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\bgsconf.ini | text | |
MD5:— | SHA256:— | |||
| 876 | pdfMachine.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\bgshtma.exe | executable | |
MD5:— | SHA256:— | |||
| 876 | pdfMachine.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\BgsOfice64.dll | executable | |
MD5:— | SHA256:— | |||
| 876 | pdfMachine.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\bgspd64.dll | executable | |
MD5:— | SHA256:— | |||
| 876 | pdfMachine.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\bgspd2k.dll | executable | |
MD5:— | SHA256:— | |||
| 876 | pdfMachine.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\bgspdui64.dll | executable | |
MD5:— | SHA256:— | |||
| 876 | pdfMachine.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\bgspdui.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1632 | bgsview.exe | GET | 200 | 158.69.82.26:80 | http://broadgun.com/pdfmachine-logging.txt | CA | text | 4 b | suspicious |
1756 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1632 | bgsview.exe | 158.69.82.26:80 | broadgun.com | OVH SAS | CA | unknown |
1756 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1932 | bgsview.exe | 158.69.82.26:80 | broadgun.com | OVH SAS | CA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
broadgun.com |
| suspicious |
www.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
bgssetup.exe | BgsSetup called with parameters :
|
spoolsv.exe | ppd.c (181): Cannot open BPD file
|
spoolsv.exe | ppd.c (368): No binary PPD data exists
|
spoolsv.exe | ppdkwd.c (501): |
spoolsv.exe | *TTRasterizer expects QuotedValue instead of StringValue
|
spoolsv.exe | ppdproc.c (227): Invalid integer number.
|
spoolsv.exe | ppdobj.c (426): |
spoolsv.exe | Syntax error in keyword entry *TTRasterizer
|
spoolsv.exe | ShellExecuteEx returned 1
|
spoolsv.exe | PRNEVENT executeCmd exitCode = 3
|