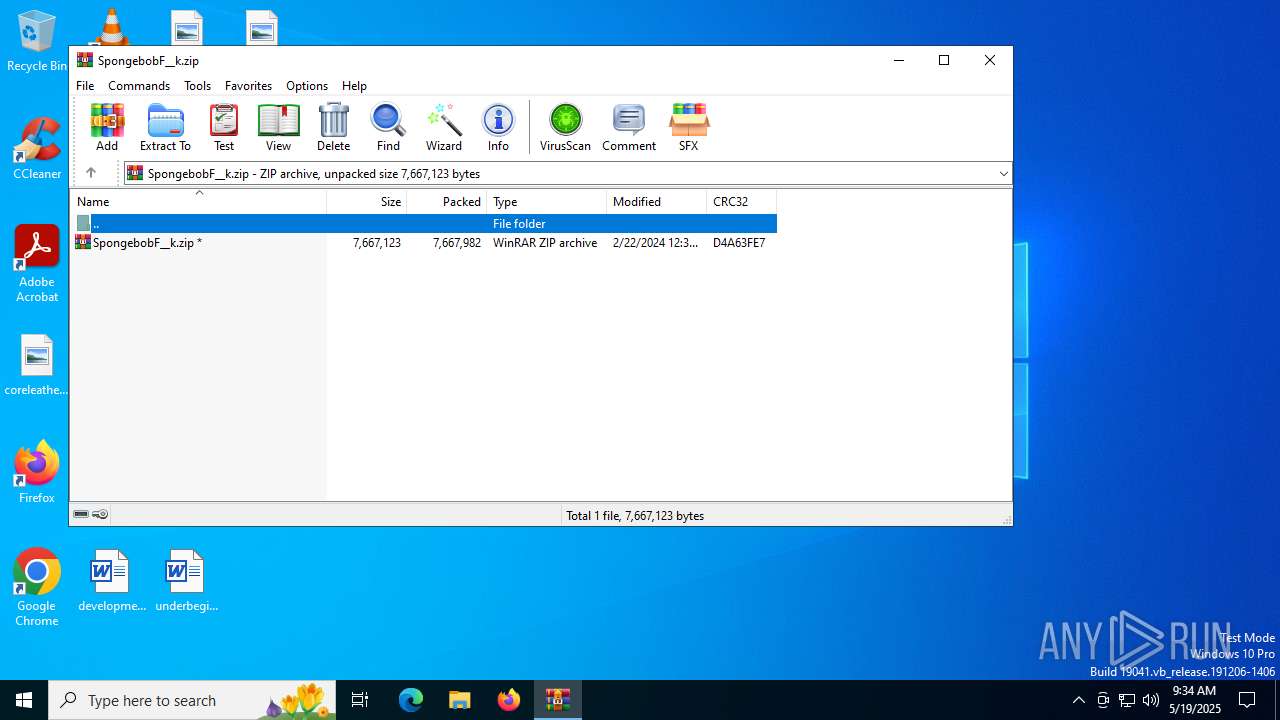
| File name: | SpongebobF__k.zip |
| Full analysis: | https://app.any.run/tasks/2f1e610b-4f69-4ea2-a654-80c9c6488738 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 09:34:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | F8291DA1E099DF0FFD0C29B1D524486A |
| SHA1: | D585BC7505C143175AF3DD211528312CCA3B518E |
| SHA256: | A80CCB67B62BE1F2E7A76DC2901EF45B187FD1E50DA23380F3155DDC180A242C |
| SSDEEP: | 98304:oGtXrezJqoEEkXYoowXcMaoH3SndfMcaSup0P6kG/2UdcmNgLKQTZ30S2BIczyOc:jxZmnMocaRakB |
MALICIOUS
Generic archive extractor
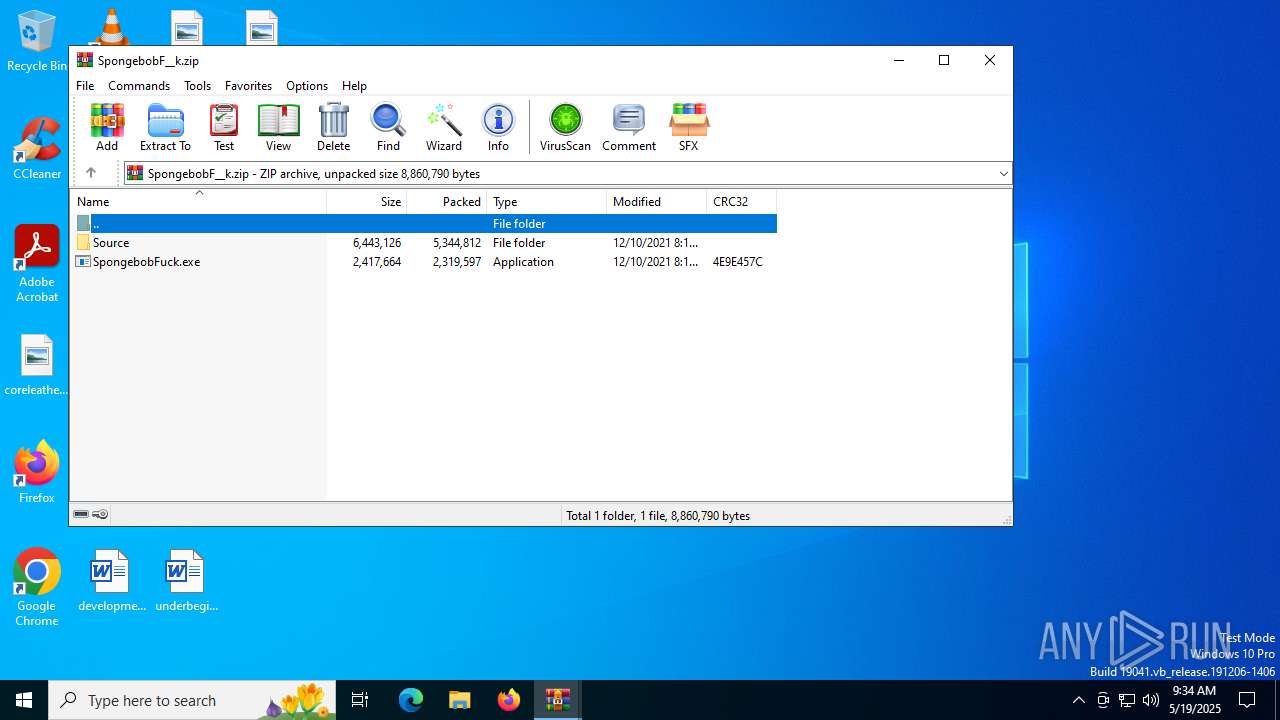
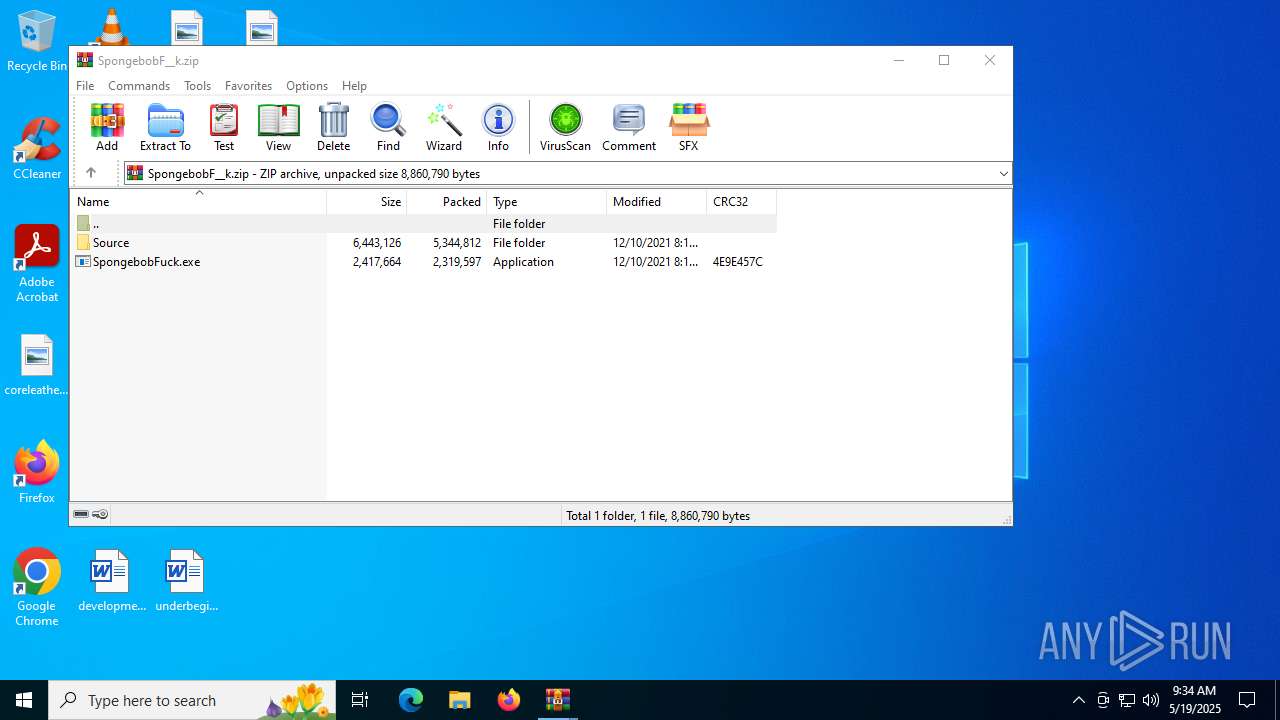
- WinRAR.exe (PID: 6140)
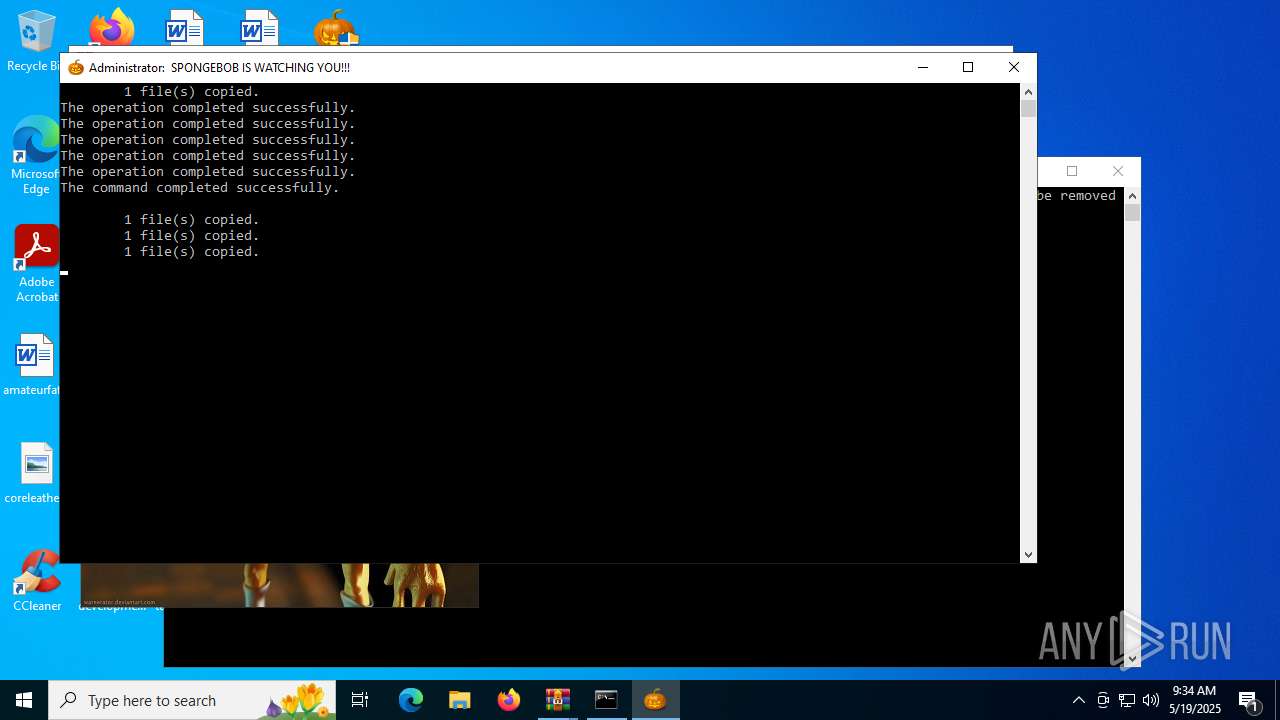
UAC/LUA settings modification
- reg.exe (PID: 6172)
Disables task manager
- reg.exe (PID: 1652)
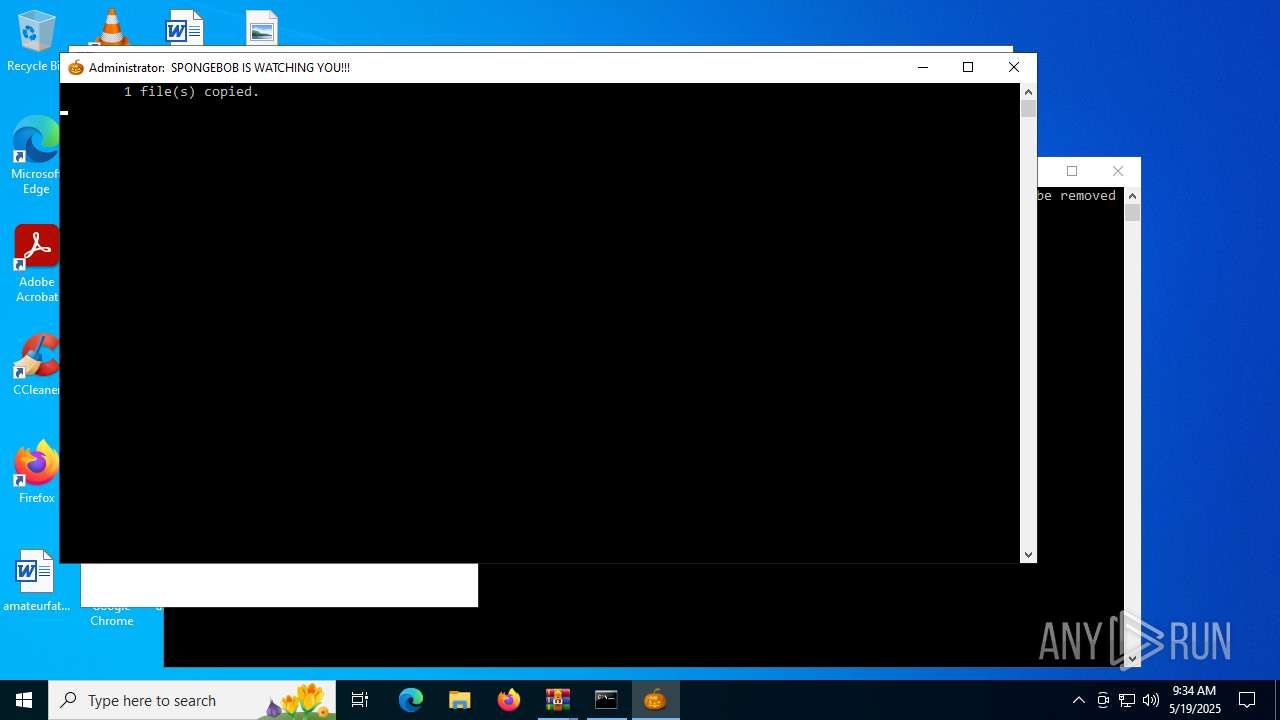
Create files in the Startup directory
- cmd.exe (PID: 6856)
Disables Windows Defender
- reg.exe (PID: 5528)
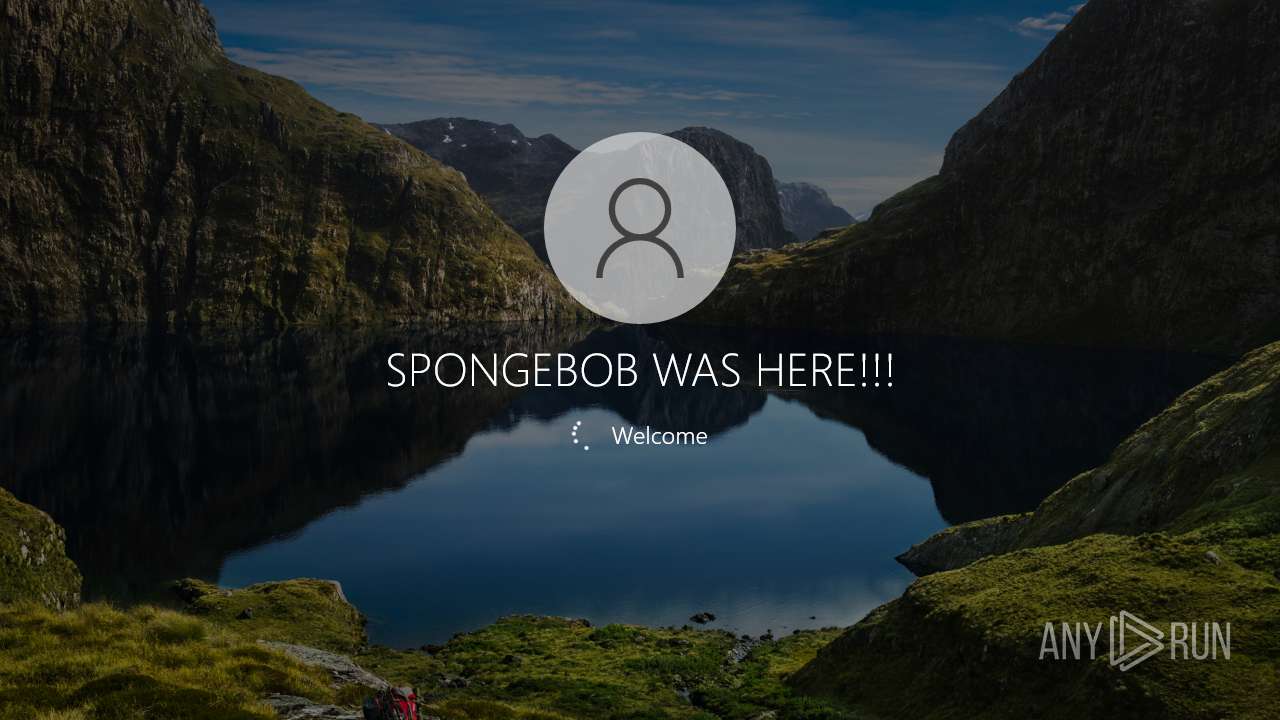
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 6856)
- net.exe (PID: 4948)
SUSPICIOUS
Executable content was dropped or overwritten
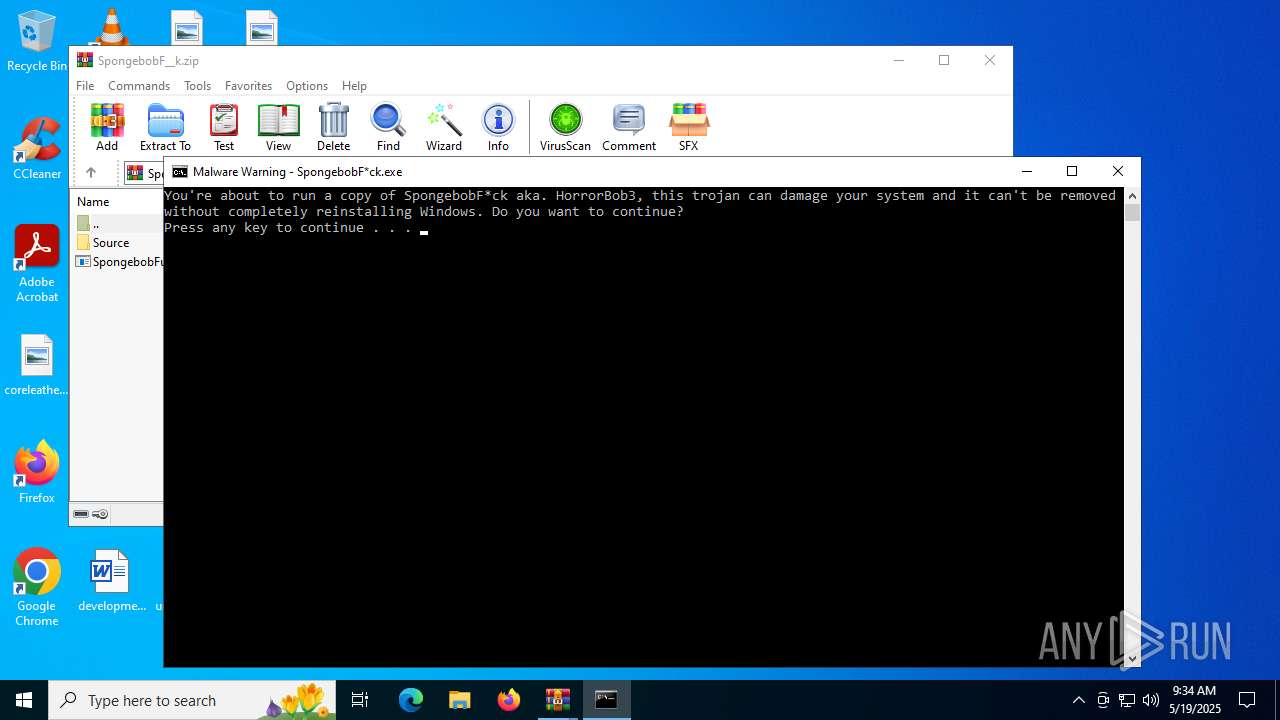
- SpongebobFuck.exe (PID: 856)
- cmd.exe (PID: 6856)
Starts CMD.EXE for commands execution
- SpongebobFuck.exe (PID: 856)
Executing commands from ".cmd" file
- SpongebobFuck.exe (PID: 856)
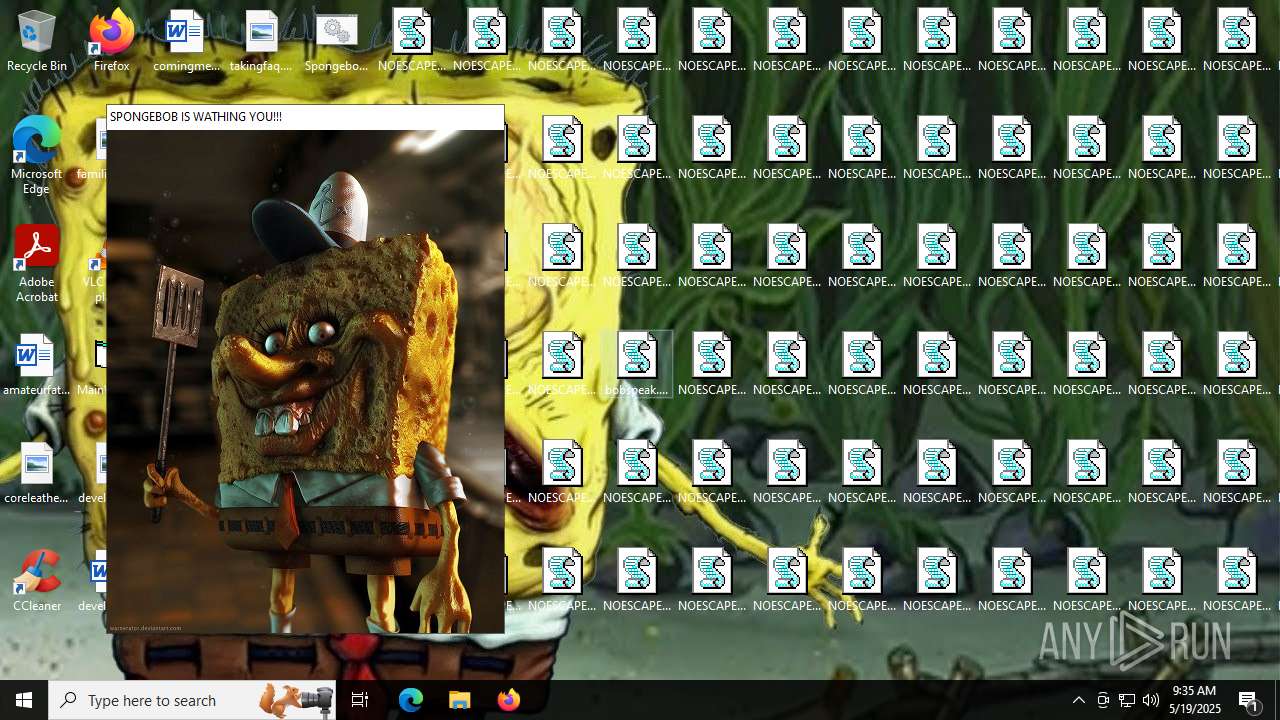
Changes the desktop background image
- reg.exe (PID: 6128)
- reg.exe (PID: 1232)
Creates file in the systems drive root
- cmd.exe (PID: 6856)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6856)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 2756)
- updater.exe (PID: 4104)
Application launched itself
- updater.exe (PID: 4104)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 4916)
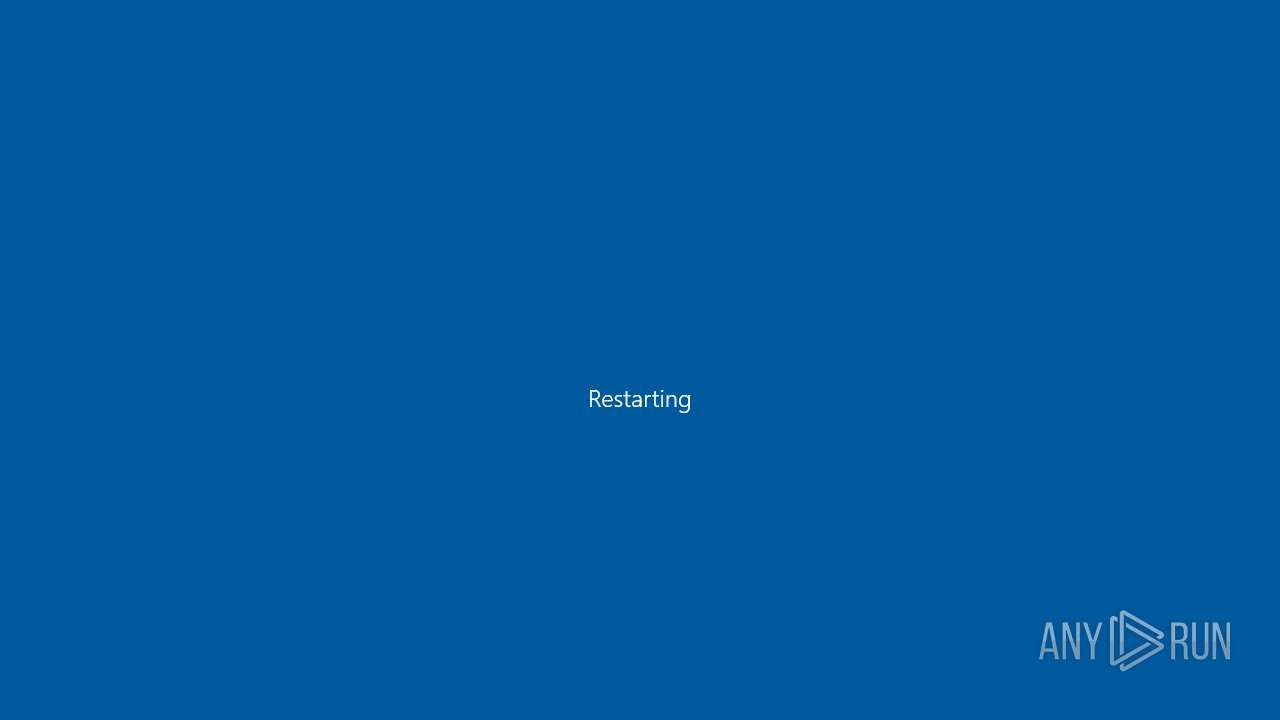
The system shut down or reboot
- cmd.exe (PID: 6856)
INFO
Create files in a temporary directory
- SpongebobFuck.exe (PID: 856)
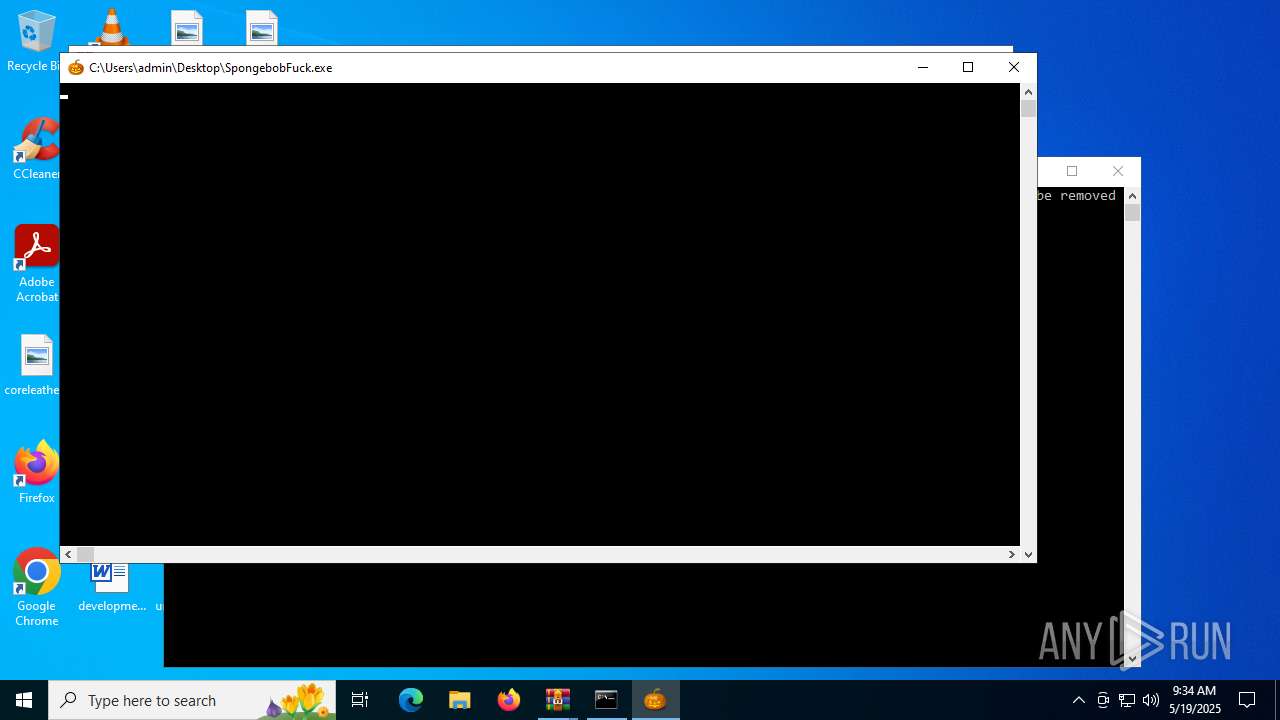
Manual execution by a user
- cmd.exe (PID: 6364)
- SpongebobFuck.exe (PID: 856)
- WinRAR.exe (PID: 1288)
- SpongebobFuck.exe (PID: 6672)
- mover.exe (PID: 5468)
- MainWindow.exe (PID: 1604)
- wscript.exe (PID: 6104)
- wscript.exe (PID: 6400)
- mover.exe (PID: 6552)
- MainWindow.exe (PID: 6532)
The sample compiled with english language support
- SpongebobFuck.exe (PID: 856)
- cmd.exe (PID: 6856)
Checks supported languages
- SpongebobFuck.exe (PID: 856)
- mover.exe (PID: 5468)
- MainWindow.exe (PID: 1604)
- ShellExperienceHost.exe (PID: 4916)
Reads mouse settings
- mover.exe (PID: 5468)
Reads the time zone
- net1.exe (PID: 1760)
Creates files in the program directory
- cmd.exe (PID: 6856)
Reads the computer name
- MainWindow.exe (PID: 1604)
- ShellExperienceHost.exe (PID: 4916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2024:02:22 12:39:14 |
| ZipCRC: | 0xd4a63fe7 |
| ZipCompressedSize: | 7667982 |
| ZipUncompressedSize: | 7667123 |
| ZipFileName: | SpongebobF__k.zip |
Total processes
270
Monitored processes
27
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Users\admin\Desktop\SpongebobFuck.exe" | C:\Users\admin\Desktop\SpongebobFuck.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1232 | reg add "HKEY_CURRENT_USER\Control Panel\Desktop" /v Wallpaper /t REG_SZ /d c:\bg.bmp /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1288 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\SpongebobF__k.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1073807364 Version: 5.91.0 Modules
| |||||||||||||||
| 1604 | "C:\Users\admin\Desktop\MainWindow.exe" | C:\Users\admin\Desktop\MainWindow.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1073807364 Version: 1.00 Modules
| |||||||||||||||
| 1652 | REG add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1760 | C:\WINDOWS\system32\net1 user admin /fullname:"SPONGEBOB WAS HERE!!!" | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2696 | shutdown /r /t 00 | C:\Windows\SysWOW64\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2756 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3768 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SpongebobFuck.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 401
Read events
5 201
Write events
200
Delete events
0
Modification events
| (PID) Process: | (6140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SpongebobF__k.zip | |||
| (PID) Process: | (6140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
4
Suspicious files
38
Text files
106
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 856 | SpongebobFuck.exe | C:\Users\admin\AppData\Local\Temp\AE41.tmp\bobspeak.vbs | text | |
MD5:8884A25E47D799F6BD3D4EC20F05A3B7 | SHA256:5A68437EDD63BD826A1F1557121D4C05114C608FD8A18A0C9C156A60D90BD0C1 | |||
| 856 | SpongebobFuck.exe | C:\Users\admin\AppData\Local\Temp\AE41.tmp\SpongebobFuck.cmd | text | |
MD5:7A918ED93F7FB297E05464EDCCC46756 | SHA256:82FCB47B437DC1BEDB77648755770B7CD9A29342FD2AB972C8BD063968D04604 | |||
| 856 | SpongebobFuck.exe | C:\Users\admin\AppData\Local\Temp\AE41.tmp\MainWindow.exe | executable | |
MD5:03D8B31DB1ED1294334B872F756AD1A1 | SHA256:7E17DCAAFC07877E720B3FC0E666AC69E2DCE8E7458AE9B23902BCF5F8F2A40A | |||
| 856 | SpongebobFuck.exe | C:\Users\admin\AppData\Local\Temp\AE41.tmp\mover.exe | executable | |
MD5:C1978E4080D1EC7E2EDF49D6C9710045 | SHA256:C9E2A7905501745C304FFC5A70B290DB40088D9DC10C47A98A953267468284A8 | |||
| 6856 | cmd.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\bobspeak.vbs | text | |
MD5:8884A25E47D799F6BD3D4EC20F05A3B7 | SHA256:5A68437EDD63BD826A1F1557121D4C05114C608FD8A18A0C9C156A60D90BD0C1 | |||
| 856 | SpongebobFuck.exe | C:\Users\admin\AppData\Local\Temp\AE41.tmp\bg.bmp | image | |
MD5:CE45A70D3CC2941A147C09264FC1CDA5 | SHA256:ECEEDADFDE8506A73650CFA9A936E6A8FFF7FFB664C9602BB14432AA2F8109AC | |||
| 6856 | cmd.exe | C:\Users\Public\Desktop\NOESCAPE9397.vbs | text | |
MD5:7C0B3EF9968D114404D5CB1EF66EAE49 | SHA256:B765F9B09B6C3D040C96E9B09ECA1ED1A8BC3F980BA09BEABC0A8DF726181BBF | |||
| 6856 | cmd.exe | C:\Users\Public\Desktop\NOESCAPE30114.vbs | text | |
MD5:7C0B3EF9968D114404D5CB1EF66EAE49 | SHA256:B765F9B09B6C3D040C96E9B09ECA1ED1A8BC3F980BA09BEABC0A8DF726181BBF | |||
| 6856 | cmd.exe | C:\Users\Public\Desktop\NOESCAPE20269.vbs | text | |
MD5:7C0B3EF9968D114404D5CB1EF66EAE49 | SHA256:B765F9B09B6C3D040C96E9B09ECA1ED1A8BC3F980BA09BEABC0A8DF726181BBF | |||
| 6856 | cmd.exe | C:\Users\Public\Desktop\NOESCAPE19928.vbs | text | |
MD5:7C0B3EF9968D114404D5CB1EF66EAE49 | SHA256:B765F9B09B6C3D040C96E9B09ECA1ED1A8BC3F980BA09BEABC0A8DF726181BBF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
37
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2288 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.164.81:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5080 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5376 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
7152 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1268 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2288 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2288 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.16.164.81:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |