| File name: | solara.exe |
| Full analysis: | https://app.any.run/tasks/8005fcf8-14b0-4747-be7c-74337b87191e |
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2024, 15:42:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 6557BD5240397F026E675AFB78544A26 |
| SHA1: | 839E683BF68703D373B6EAC246F19386BB181713 |
| SHA256: | A7FECFC225DFDD4E14DCD4D1B4BA1B9F8E4D1984F1CDD8CDA3A9987E5D53C239 |
| SSDEEP: | 192:LSepQwnHxaR7cAcRIaqaLHmr/XKT0i0nTJ1tXVX+7pnBR:GqHAR7cnRIaqayzKAi0d1tVcpnB |
MALICIOUS
Drops the executable file immediately after the start
- solara.exe (PID: 6416)
SUSPICIOUS
Process drops legitimate windows executable
- solara.exe (PID: 6416)
Reads the date of Windows installation
- solara.exe (PID: 6416)
Executable content was dropped or overwritten
- solara.exe (PID: 6416)
Reads security settings of Internet Explorer
- solara.exe (PID: 6416)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 6872)
The process drops C-runtime libraries
- solara.exe (PID: 6416)
INFO
Reads the computer name
- solara.exe (PID: 6416)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 6872)
Checks supported languages
- solara.exe (PID: 6416)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 6872)
Disables trace logs
- solara.exe (PID: 6416)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 6872)
Checks proxy server information
- solara.exe (PID: 6416)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 6872)
Reads Environment values
- solara.exe (PID: 6416)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 6872)
Reads the machine GUID from the registry
- solara.exe (PID: 6416)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 6872)
Reads the software policy settings
- solara.exe (PID: 6416)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 6872)
Process checks computer location settings
- solara.exe (PID: 6416)
Create files in a temporary directory
- solara.exe (PID: 6416)
Dropped object may contain TOR URL's
- solara.exe (PID: 6416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2054:05:05 20:04:52+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 10752 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4992 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | SolaraBootstrapper |
| FileVersion: | 1.0.0.0 |
| InternalName: | SolaraBootstrapper.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | SolaraBootstrapper.exe |
| ProductName: | SolaraBootstrapper |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
117
Monitored processes
3
Malicious processes
1
Suspicious processes
1
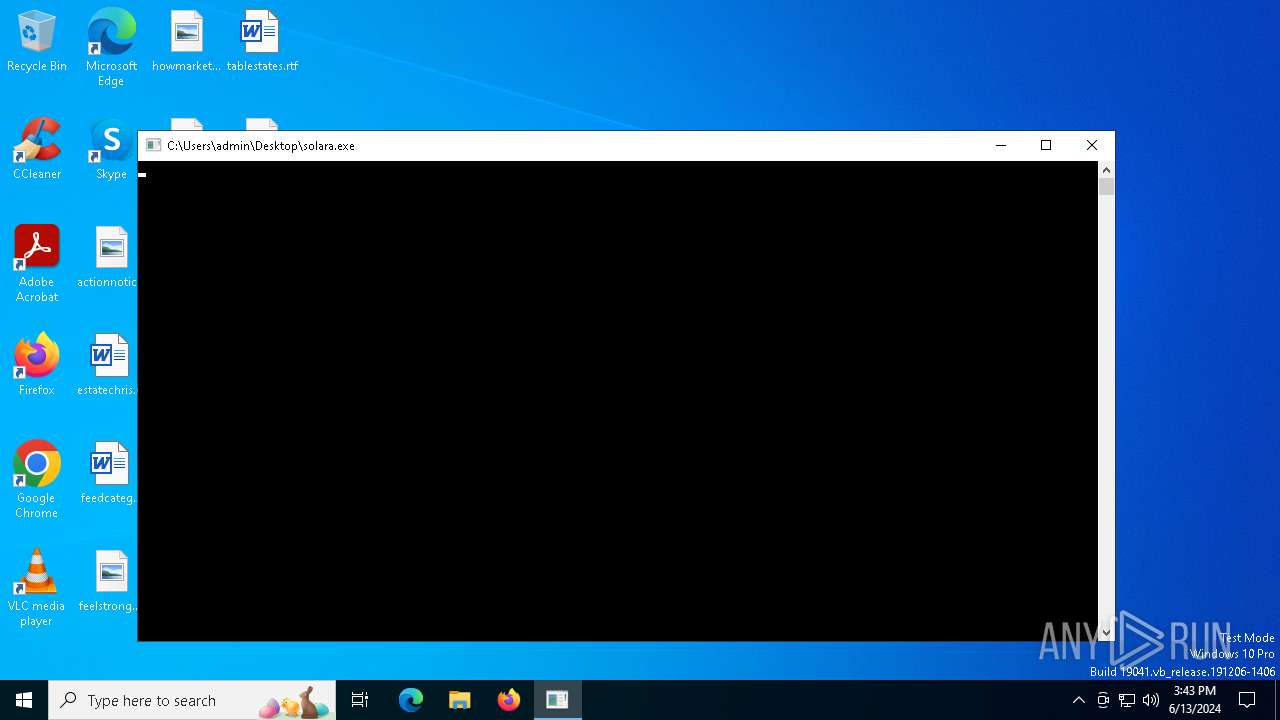
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6416 | "C:\Users\admin\Desktop\solara.exe" | C:\Users\admin\Desktop\solara.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: SolaraBootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6424 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | solara.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
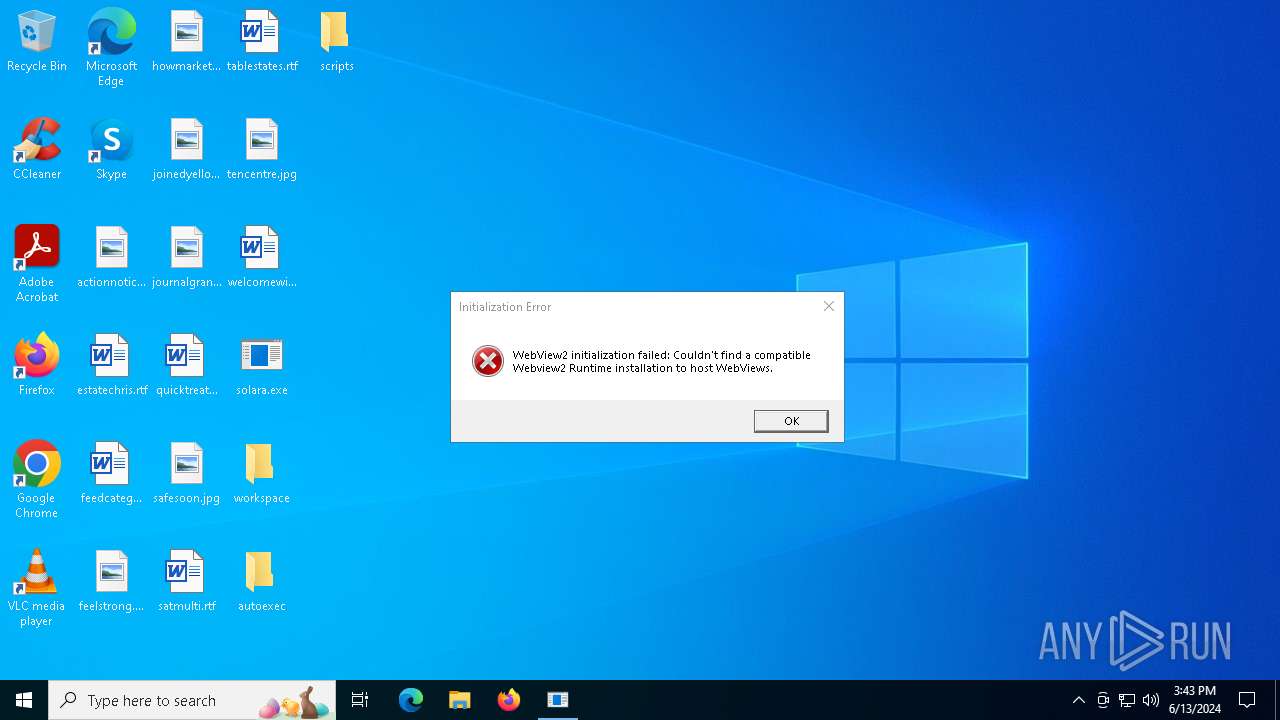
| 6872 | "C:\Users\admin\AppData\Local\Temp\Solara.Dir\cd57e4c171d6e8f5ea8b8f824a6a7316.exe" | C:\Users\admin\AppData\Local\Temp\Solara.Dir\cd57e4c171d6e8f5ea8b8f824a6a7316.exe | solara.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: WpfApp1 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
11 979
Read events
11 942
Write events
37
Delete events
0
Modification events
| (PID) Process: | (6416) solara.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6416) solara.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\solara_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6416) solara.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\solara_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6416) solara.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\solara_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6416) solara.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\solara_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6416) solara.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\solara_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6416) solara.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\solara_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6416) solara.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\solara_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6416) solara.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\solara_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6416) solara.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\solara_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
28
Suspicious files
290
Text files
401
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6416 | solara.exe | C:\Users\admin\AppData\Local\Temp\Solara.Dir\api-ms-win-crt-heap-l1-1-0.dll | executable | |
MD5:A22F9A4CBD701209842B204895FEDF37 | SHA256:2EE3D52640D84AC4F7F7DDFE748F51BAA6FD0D492286C781251222420E85CA97 | |||
| 6416 | solara.exe | C:\Users\admin\AppData\Local\Temp\Solara.zip | compressed | |
MD5:0667F585B9368DCA0BB4936684185DB2 | SHA256:EA5D489AE7CA40693E0152537DAADD1B02561ECD577282AD28D2D84ED3DBCFFB | |||
| 6416 | solara.exe | C:\Users\admin\AppData\Local\Temp\Solara.Dir\api-ms-win-crt-locale-l1-1-0.dll | executable | |
MD5:BA17B278FFF2C18E34E47562DDDE8166 | SHA256:C36F5C0AC5D91A8417866DD4D8C670C2192BA83364693E7438282FB8678C3D1E | |||
| 6416 | solara.exe | C:\Users\admin\AppData\Local\Temp\Solara.Dir\api-ms-win-crt-math-l1-1-0.dll | executable | |
MD5:C4CAC2D609BB5E0DA9017EBB535634CE | SHA256:7C3336C3A50BF3B4C5492C0D085519C040878243E9F7D3EA9F6A2E35C8F1F374 | |||
| 6416 | solara.exe | C:\Users\admin\AppData\Local\Temp\Solara.Dir\api-ms-win-crt-convert-l1-1-0.dll | executable | |
MD5:0485C463CD8D2AE1CBD42DF6F0591246 | SHA256:983F4D4C7B7330E7F5F091080C1E81905575EBCCD97E11DFF8A064979EC8D9B8 | |||
| 6416 | solara.exe | C:\Users\admin\AppData\Local\Temp\Solara.Dir\Microsoft.Web.WebView2.WinForms.dll | executable | |
MD5:4CF94FFA50FD9BDC0BB93CCEAEDE0629 | SHA256:50B2E46C99076F6FA9C33E0A98F0FE3A2809A7C647BB509066E58F4C7685D7E6 | |||
| 6416 | solara.exe | C:\Users\admin\AppData\Local\Temp\Solara.Dir\Microsoft.Web.WebView2.Core.dll | executable | |
MD5:851FEE9A41856B588847CF8272645F58 | SHA256:5E7FAEE6B8230CA3B97CE9542B914DB3ABBBD1CB14FD95A39497AAAD4C1094CA | |||
| 6416 | solara.exe | C:\Users\admin\AppData\Local\Temp\Solara.Dir\Monaco\fgd.html | html | |
MD5:A1416C1FE209F7687FF79AB44301B3D3 | SHA256:A6897302DBA619DD3C156D57FC4B706662BFF4DF582975C33478B7878B060D2C | |||
| 6416 | solara.exe | C:\Users\admin\AppData\Local\Temp\Solara.Dir\libcurl.dll | executable | |
MD5:E31F5136D91BAD0FCBCE053AAC798A30 | SHA256:EE94E2201870536522047E6D7FE7B903A63CD2E13E20C8FFFC86D0E95361E671 | |||
| 6416 | solara.exe | C:\Users\admin\AppData\Local\Temp\Solara.Dir\Monaco\fileaccess\node_modules\.bin\mime | text | |
MD5:7AB5BFFF58B0A878A4614CDDBE424702 | SHA256:394B93EAAAC25F18A20D7CDD80920ECCA1FE43C8E5B37501389E644944C6E01F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
24
DNS requests
7
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1744 | RUXIMICS.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5228 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
5228 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
— | — | GET | 302 | 140.82.121.3:443 | https://github.com/quivings/Solara/raw/main/Files/Solara.Dir.zip | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/quivings/Solara/main/Storage/version.txt | unknown | text | 5 b | unknown |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/quivings/Solara/main/Files/Solara.Dir.zip | unknown | compressed | 12.8 Mb | unknown |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/quivings/Solara/main/Storage/patched.txt | unknown | text | 2 b | unknown |
— | — | POST | 200 | 51.132.193.104:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5228 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1744 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5140 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5140 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5228 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4364 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
1744 | RUXIMICS.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5140 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
5228 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
github.com |
| shared |
settings-win.data.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET HUNTING Terse Request for Zip File (GET) |
— | — | Potentially Bad Traffic | ET HUNTING Terse Request for Zip File (GET) |
1 ETPRO signatures available at the full report