| File name: | tj.exe |
| Full analysis: | https://app.any.run/tasks/e3653e90-31c2-46d6-8e64-5a61fa3fa05b |
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2020, 08:22:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable, MZ for MS-DOS |
| MD5: | 65B03F22012B70F780BFB3AA64DBC13E |
| SHA1: | EE69F1E6181268A61AE16A45A93C4A5E263585FC |
| SHA256: | A7FEC41AF41B36B95A33A396464D795FEF6ED5846B3419B1DF51C9EC896A878A |
| SSDEEP: | 98304:hB1tNorZ/VtC415qvz82DrEfAaFOQBSF1kiVYA/0jIWHUCgfFjOAp5P:/aZrC4yMAa5BSFHY4sUX9p |
MALICIOUS
Changes the autorun value in the registry
- explorer.exe (PID: 3036)
- svchost.exe (PID: 956)
Uses Task Scheduler to run other applications
- svchost.exe (PID: 956)
Application was dropped or rewritten from another process
- shuame_helper.exe (PID: 552)
- tj.exe (PID: 2412)
- shuame_helper.exe (PID: 3236)
- shuame_helper.exe (PID: 3224)
- shuame_helper.exe (PID: 2612)
- shuame_helper.exe (PID: 1688)
- shuame_helper.exe (PID: 1460)
- shuame_helper.exe (PID: 3060)
- shuame_helper.exe (PID: 3484)
Loads dropped or rewritten executable
- shuame_helper.exe (PID: 552)
- shuame_helper.exe (PID: 3236)
- tj.exe (PID: 2412)
- shuame_helper.exe (PID: 3224)
- shuame_helper.exe (PID: 2612)
- shuame_helper.exe (PID: 1688)
- shuame_helper.exe (PID: 3484)
- shuame_helper.exe (PID: 3060)
- shuame_helper.exe (PID: 1460)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3840)
SUSPICIOUS
Starts application with an unusual extension
- tj.exe (PID: 3136)
Executable content was dropped or overwritten
- tj.exe (PID: 3136)
- icsys.icn.exe (PID: 1680)
- explorer.exe (PID: 3036)
- spoolsv.exe (PID: 2152)
- tj.exe (PID: 2412)
Creates files in the Windows directory
- tj.exe (PID: 3136)
- icsys.icn.exe (PID: 1680)
- spoolsv.exe (PID: 2152)
- explorer.exe (PID: 3036)
Removes files from Windows directory
- icsys.icn.exe (PID: 1680)
- explorer.exe (PID: 3036)
- spoolsv.exe (PID: 2152)
Creates executable files which already exist in Windows
- icsys.icn.exe (PID: 1680)
- spoolsv.exe (PID: 2152)
Starts itself from another location
- explorer.exe (PID: 3036)
- icsys.icn.exe (PID: 1680)
- spoolsv.exe (PID: 2152)
- svchost.exe (PID: 956)
- tj.exe (PID: 3136)
Reads Internet Cache Settings
- tj.exe (PID: 2412)
Low-level read access rights to disk partition
- tj.exe (PID: 2412)
Creates files in the user directory
- tj.exe (PID: 2412)
Application launched itself
- shuame_helper.exe (PID: 552)
- shuame_helper.exe (PID: 1688)
INFO
Dropped object may contain Bitcoin addresses
- shuame_helper.exe (PID: 3236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:01 09:08:22+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 106496 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x290c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Project1 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | TJprojMain |
| OriginalFileName: | TJprojMain.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Apr-2013 07:08:22 |
| Detected languages: |
|
| ProductName: | Project1 |
| FileVersion: | 1.00 |
| ProductVersion: | 1.00 |
| InternalName: | TJprojMain |
| OriginalFilename: | TJprojMain.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Apr-2013 07:08:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000191D4 | 0x0001A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.7348 |
.data | 0x0001B000 | 0x0000180C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0001D000 | 0x000013F0 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.20866 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.71018 | 999 | UNKNOWN | English - United States | RT_MANIFEST |
30001 | 5.88875 | 3280 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
60
Monitored processes
17
Malicious processes
7
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
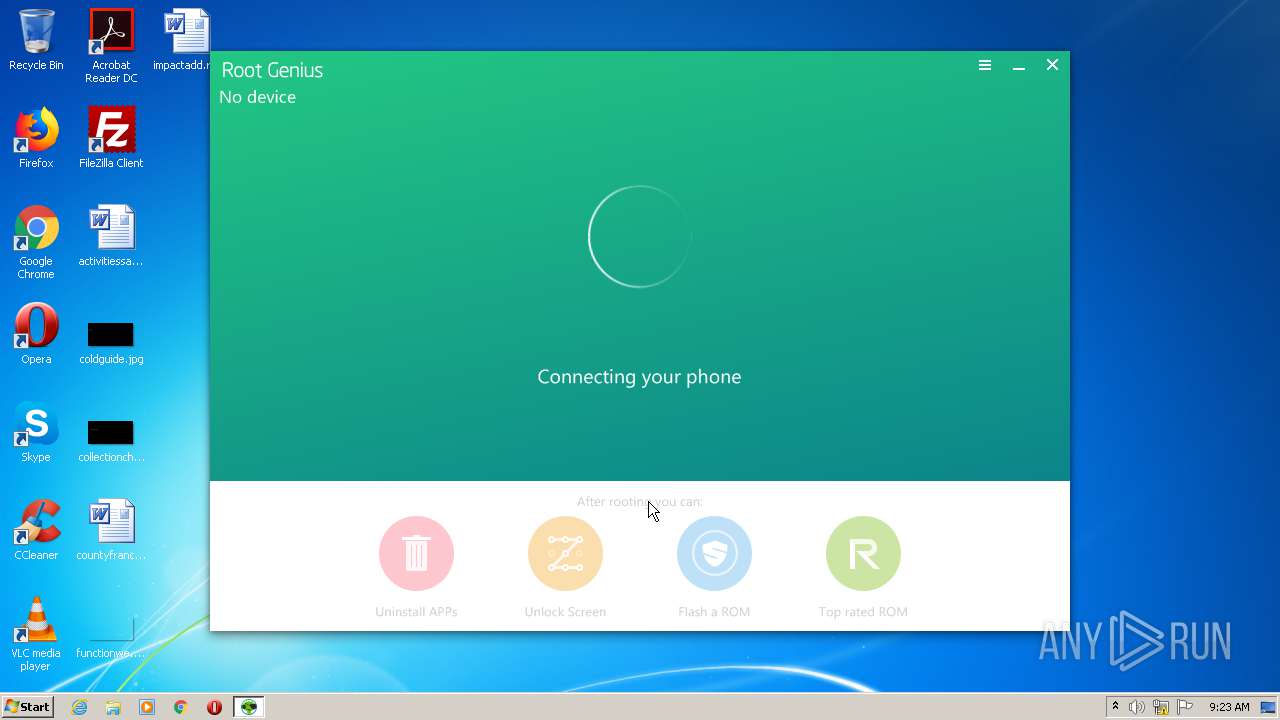
| 552 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | tj.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 956 | c:\windows\resources\svchost.exe | c:\windows\resources\svchost.exe | spoolsv.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 960 | "C:\Users\admin\AppData\Local\Temp\tj.exe" | C:\Users\admin\AppData\Local\Temp\tj.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 | |||||||||||||||
| 1460 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | tj.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1680 | C:\Windows\Resources\Themes\icsys.icn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | tj.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1688 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | tj.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2152 | c:\windows\resources\spoolsv.exe SE | c:\windows\resources\spoolsv.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
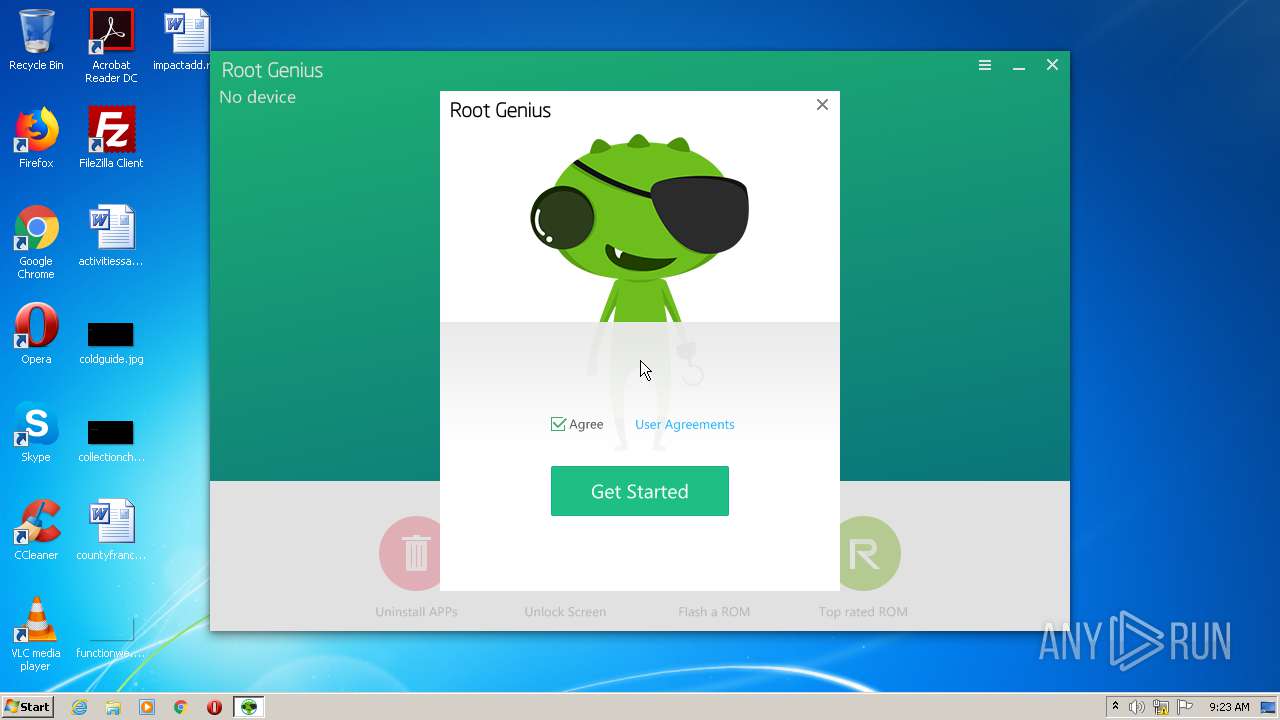
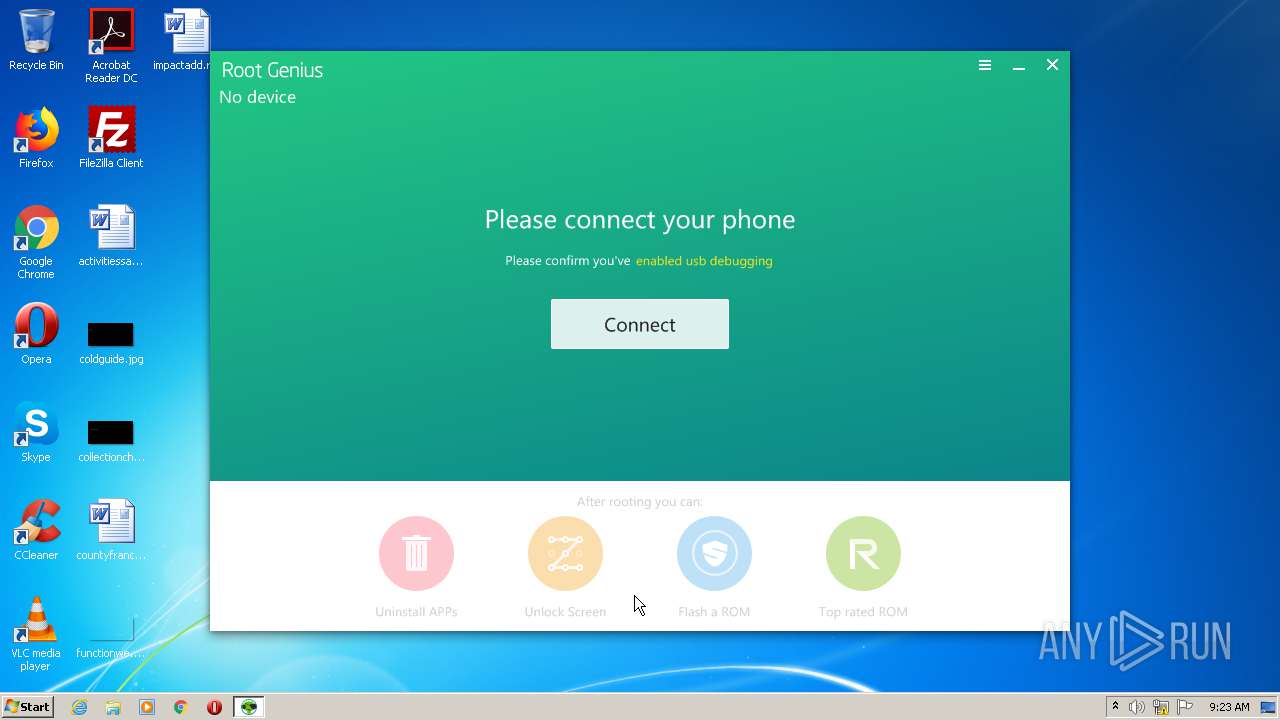
| 2412 | c:\users\admin\appdata\local\temp\tj.exe | c:\users\admin\appdata\local\temp\tj.exe | tj.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: RootGenius Exit code: 0 Version: 2. 2. 6 Modules
| |||||||||||||||
| 2612 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | tj.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3036 | c:\windows\resources\themes\explorer.exe | c:\windows\resources\themes\explorer.exe | icsys.icn.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
126
Read events
84
Write events
42
Delete events
0
Modification events
| (PID) Process: | (3136) tj.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (2412) tj.exe | Key: | HKEY_CURRENT_USER\Software\RootGenius |
| Operation: | write | Name: | (default) |
Value: c:\users\admin\appdata\local\temp\tj.exe | |||
| (PID) Process: | (2412) tj.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2412) tj.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2412) tj.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2412) tj.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2412) tj.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2412) tj.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2412) tj.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1680) icsys.icn.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
Executable files
16
Suspicious files
2
Text files
12
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3136 | tj.exe | C:\users\admin\appdata\local\temp\tj.exe | executable | |
MD5:— | SHA256:— | |||
| 3136 | tj.exe | C:\Windows\Resources\Themes\icsys.icn.exe | executable | |
MD5:— | SHA256:— | |||
| 2412 | tj.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\android_driver\devcon_x64.exe | executable | |
MD5:— | SHA256:— | |||
| 2412 | tj.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\android_driver\devcon_x86.exe | executable | |
MD5:— | SHA256:— | |||
| 2412 | tj.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\v | — | |
MD5:— | SHA256:— | |||
| 2412 | tj.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\RootGeniusEx.zip | — | |
MD5:— | SHA256:— | |||
| 2412 | tj.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\Data\Apk\StayAwake.apk | java | |
MD5:— | SHA256:— | |||
| 2412 | tj.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\AdbWinUsbApi.dll | executable | |
MD5:— | SHA256:— | |||
| 2412 | tj.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\Data\Bin\aapt | o | |
MD5:— | SHA256:— | |||
| 2412 | tj.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\Data\Bin\aapt-bak | o | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
12
DNS requests
5
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2412 | tj.exe | POST | — | 203.195.128.118:80 | http://api1.rootjl.com/v2/root/cfg?versionName=RootGenius_en&versionCode=105 | CN | — | — | suspicious |
2412 | tj.exe | POST | — | 203.195.128.118:80 | http://api1.rootjl.com/v2/root/cfg?versionName=RootGenius_en&versionCode=105 | CN | — | — | suspicious |
2412 | tj.exe | GET | — | 203.205.137.182:80 | http://download.sj.qq.com/update/connectservice/default_fix_cv/1.0.0.514.zip | CN | — | — | malicious |
2412 | tj.exe | POST | 200 | 203.205.235.63:80 | http://agent.sj.qq.com/query.do | CN | binary | 1 b | suspicious |
2412 | tj.exe | POST | — | 203.195.128.118:80 | http://api1.rootjl.com/v2/root/update?versionName=RootGenius_en&versionCode=105 | CN | — | — | suspicious |
2412 | tj.exe | POST | 200 | 120.241.190.60:8080 | http://120.241.190.60:8080/ | CN | binary | 155 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2412 | tj.exe | 14.17.41.155:8080 | — | China Telecom (Group) | CN | suspicious |
2412 | tj.exe | 203.195.142.168:443 | api1.shuame.com | Shenzhen Tencent Computer Systems Company Limited | CN | unknown |
2412 | tj.exe | 203.195.128.118:80 | api1.rootjl.com | Shenzhen Tencent Computer Systems Company Limited | CN | suspicious |
2412 | tj.exe | 203.205.235.63:80 | agent.sj.qq.com | — | CN | suspicious |
2412 | tj.exe | 120.241.190.60:8080 | — | China Mobile communications corporation | CN | unknown |
2412 | tj.exe | 203.205.137.182:80 | download.sj.qq.com | Tencent Building, Kejizhongyi Avenue | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api1.shuame.com |
| unknown |
agent.sj.qq.com |
| suspicious |
api1.rootjl.com |
| suspicious |
download.sj.qq.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2412 | tj.exe | A Network Trojan was detected | SUSPICIOUS [PTsecurity] Win32/RootGenius.B potentially unsafe |
2412 | tj.exe | A Network Trojan was detected | SUSPICIOUS [PTsecurity] Win32/RootGenius.B potentially unsafe |