| URL: | https://docs.google.com/uc?export=download&id=1dy7kl6EYPcb0i2efZtBUQDSVDUIe378T |
| Full analysis: | https://app.any.run/tasks/aab2a5ce-a55a-4bb5-a832-b4e00713e8bc |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 22:41:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F91CB1F37872596E61CF24D4C2FBFA9F |
| SHA1: | 4D9BAB9DFA7400D68206562D5FFCA16B3A01B5C1 |
| SHA256: | A7FAE7B151A2FE5F2A2ABEE47F3DCD15704CEF5BC301603C5351F41A6669C00C |
| SSDEEP: | 3:N8SP3u2NAaBrC2qrsPHm4GY2ihW+:2Sm2BB+2qrsOI9hW+ |
MALICIOUS
Application was dropped or rewritten from another process
- DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002 DOIMAGCAPTPDFARC7648726397826722657284576003.exe (PID: 272)
- DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002 DOIMAGCAPTPDFARC7648726397826722657284576003.exe (PID: 2156)
Writes to a start menu file
- DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002 DOIMAGCAPTPDFARC7648726397826722657284576003.exe (PID: 272)
- DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002 DOIMAGCAPTPDFARC7648726397826722657284576003.exe (PID: 2156)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3860)
- schtasks.exe (PID: 3912)
- schtasks.exe (PID: 2344)
- schtasks.exe (PID: 1816)
Uses Task Scheduler to run other applications
- RegSvcs.exe (PID: 3716)
- RegSvcs.exe (PID: 324)
Changes the autorun value in the registry
- RegSvcs.exe (PID: 324)
SUSPICIOUS
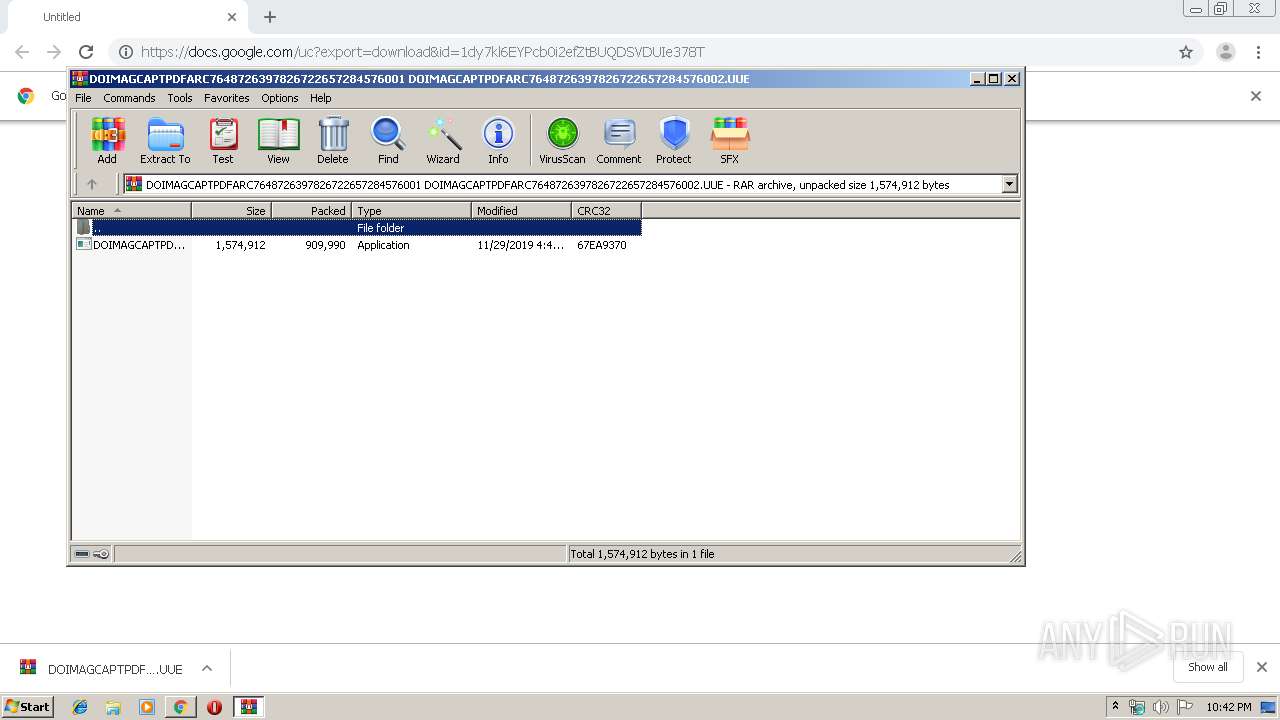
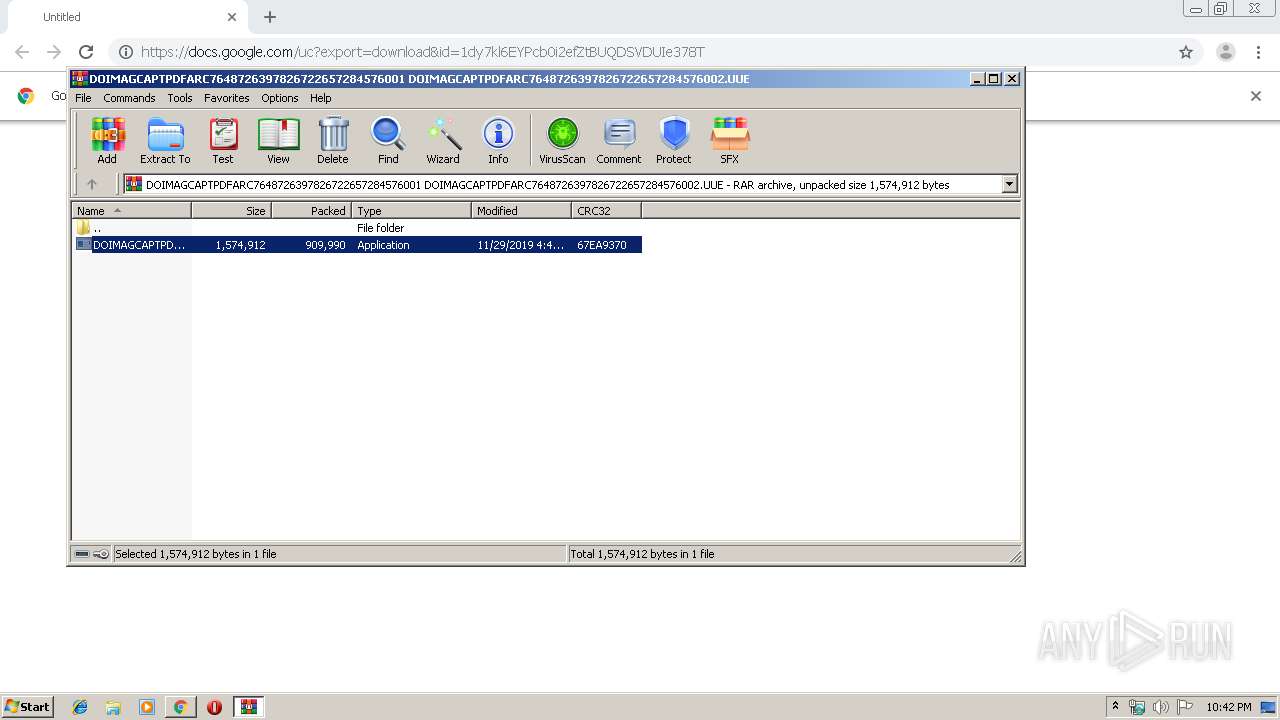
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2728)
- DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002 DOIMAGCAPTPDFARC7648726397826722657284576003.exe (PID: 272)
- DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002 DOIMAGCAPTPDFARC7648726397826722657284576003.exe (PID: 2156)
Creates files in the user directory
- DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002 DOIMAGCAPTPDFARC7648726397826722657284576003.exe (PID: 272)
INFO
Application launched itself
- chrome.exe (PID: 2132)
Reads the hosts file
- chrome.exe (PID: 2132)
- chrome.exe (PID: 2784)
Reads Internet Cache Settings
- chrome.exe (PID: 2132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
19
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2728.4557\DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002 DOIMAGCAPTPDFARC7648726397826722657284576003.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2728.4557\DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002 DOIMAGCAPTPDFARC7648726397826722657284576003.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 324 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v4.0.30319\\\\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002 DOIMAGCAPTPDFARC7648726397826722657284576003.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 1816 | schtasks /Delete /tn NYAN /F | C:\Windows\system32\schtasks.exe | — | RegSvcs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://docs.google.com/uc?export=download&id=1dy7kl6EYPcb0i2efZtBUQDSVDUIe378T" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2524 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2156 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2728.5579\DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002 DOIMAGCAPTPDFARC7648726397826722657284576003.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2728.5579\DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002 DOIMAGCAPTPDFARC7648726397826722657284576003.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,2822993343566949409,16240473352529002159,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15954223181019701302 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2344 | schtasks /create /tn NYAN /tr "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" /sc minute /mo 1 | C:\Windows\system32\schtasks.exe | — | RegSvcs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2728 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\DOIMAGCAPTPDFARC7648726397826722657284576001 DOIMAGCAPTPDFARC7648726397826722657284576002.UUE" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,2822993343566949409,16240473352529002159,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12914553250269518239 --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 376
Read events
1 302
Write events
71
Delete events
3
Modification events
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2132-13219800111777875 |
Value: 259 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
4
Suspicious files
14
Text files
58
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2d74c298-e4a0-4812-ad63-ed0f1b2c4fde.tmp | — | |
MD5:— | SHA256:— | |||
| 2132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a8ec.TMP | text | |
MD5:— | SHA256:— | |||
| 2132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a87f.TMP | text | |
MD5:— | SHA256:— | |||
| 2132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a87f.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
13
DNS requests
7
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2784 | chrome.exe | 172.217.18.161:443 | doc-00-0g-docs.googleusercontent.com | Google Inc. | US | whitelisted |
2784 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2784 | chrome.exe | 172.217.22.14:443 | docs.google.com | Google Inc. | US | whitelisted |
2784 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2784 | chrome.exe | 172.217.16.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2784 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2784 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
docs.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
doc-00-0g-docs.googleusercontent.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |