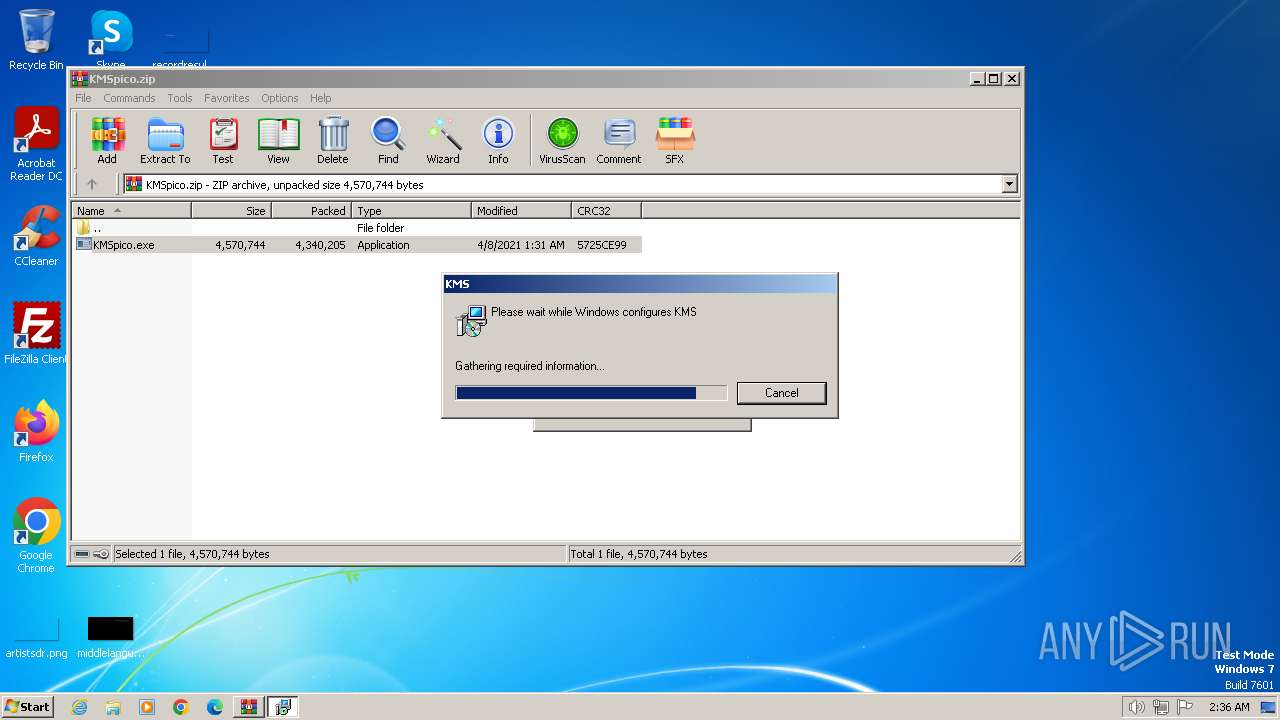
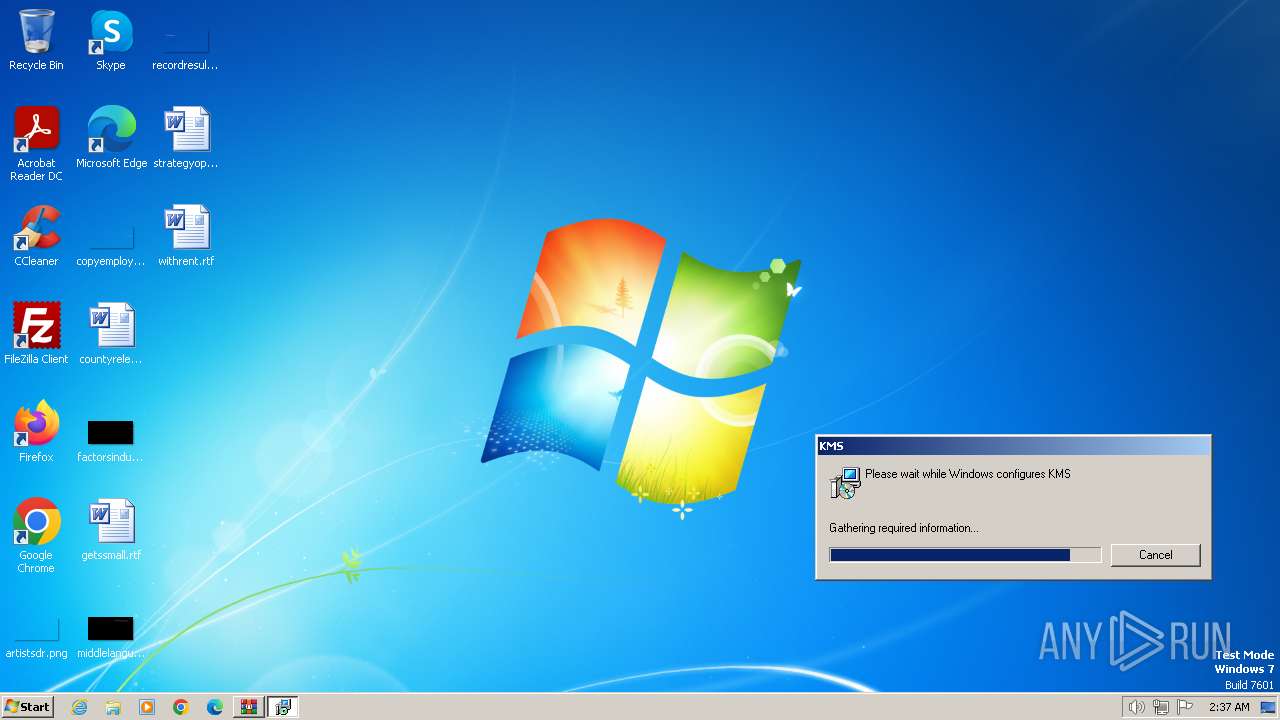
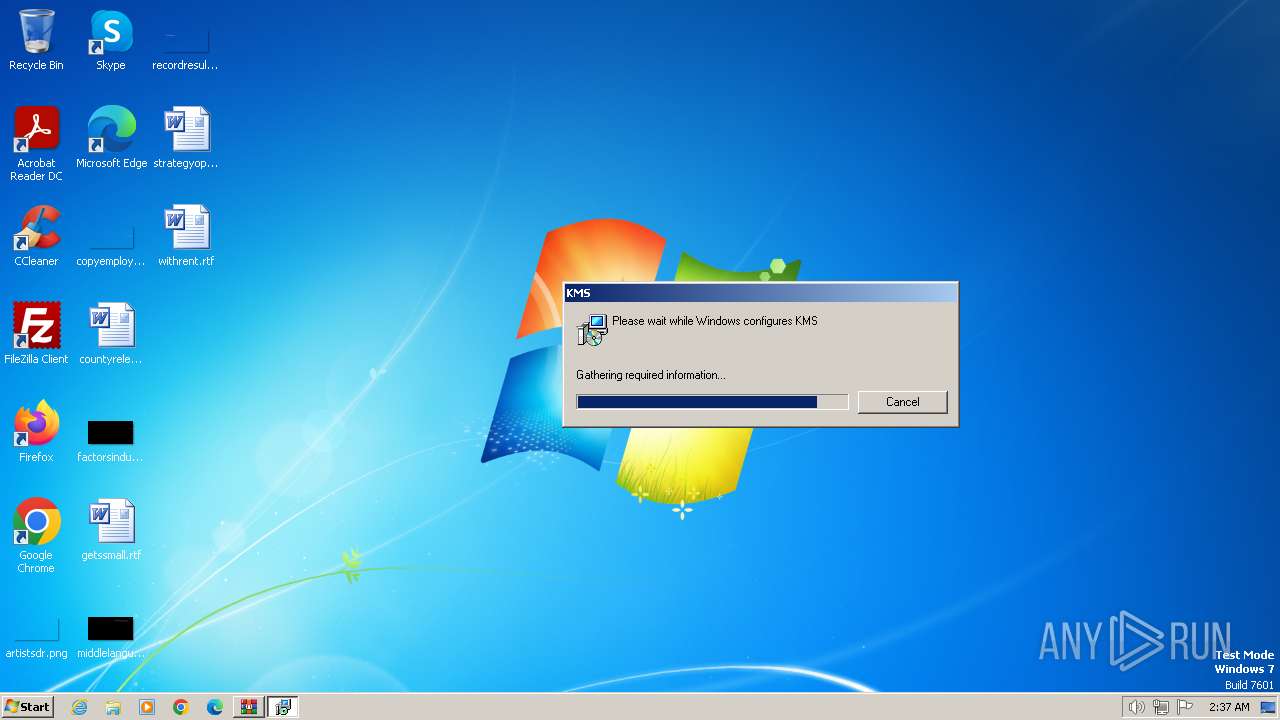
| File name: | KMSpico.zip |
| Full analysis: | https://app.any.run/tasks/7352592e-1871-4c75-8a9b-fdf8750831cd |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2024, 01:34:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 59DA58287FC25AB7529FC443C43C8386 |
| SHA1: | 9ACE5CA8CB01689CC37277F22646472B756EC4E4 |
| SHA256: | A7E784AB018250113850A28C179ACCFB86FF03B7B34B3490DB55C80E7C32E9EC |
| SSDEEP: | 98304:NuXF17wpJHFeGSETVV4ZYvIRBW3MBSwTPRIf4VGKAXxEcx:EVVwpJHEGSETVV4ZYvig32SOPbVGKAn |
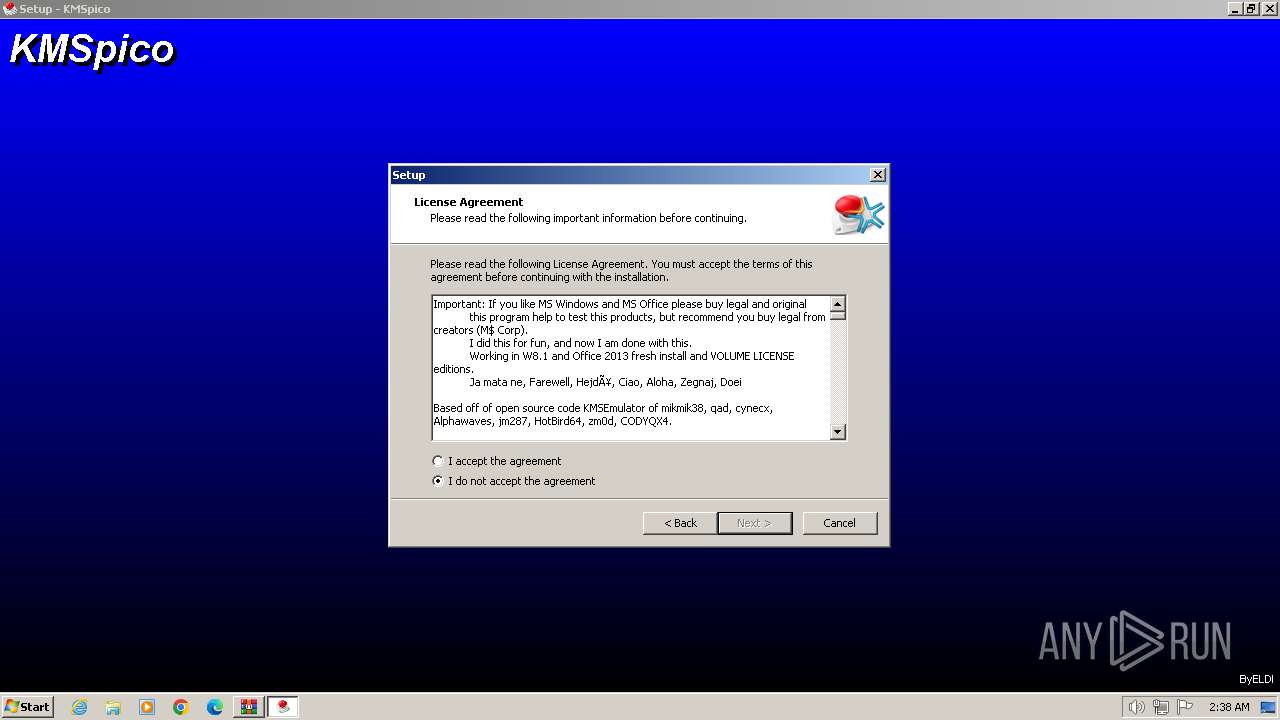
MALICIOUS
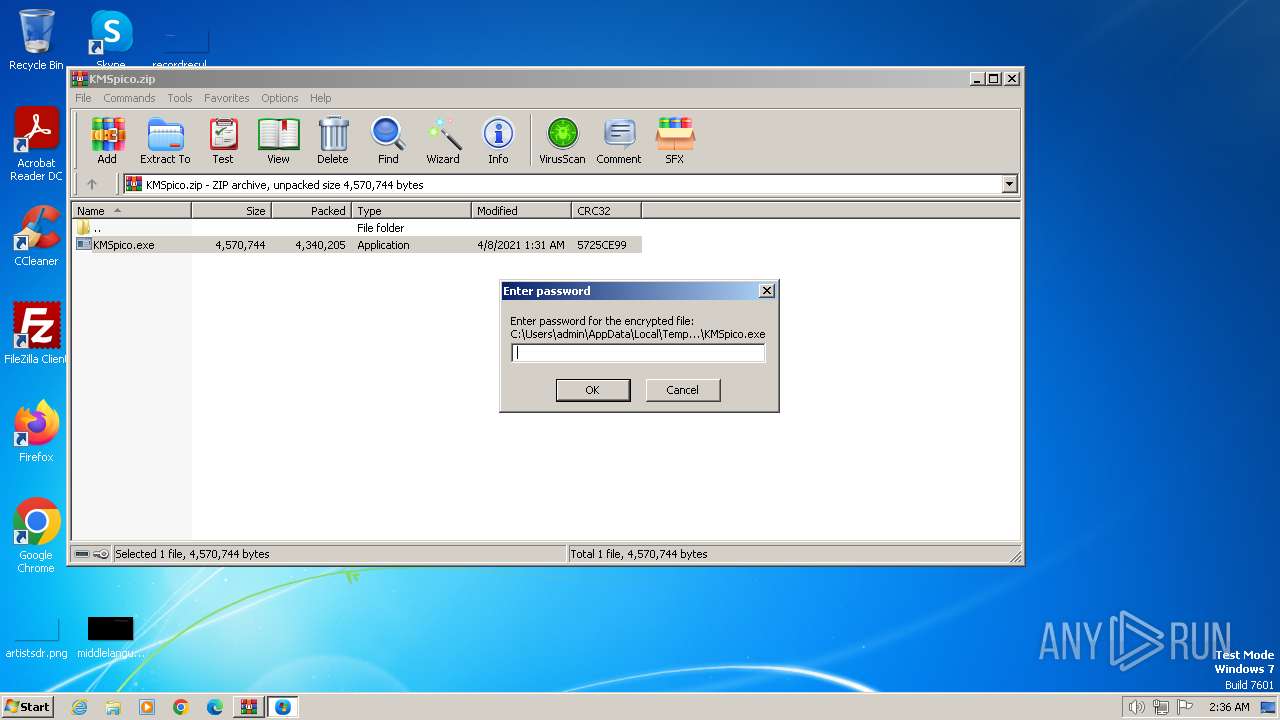
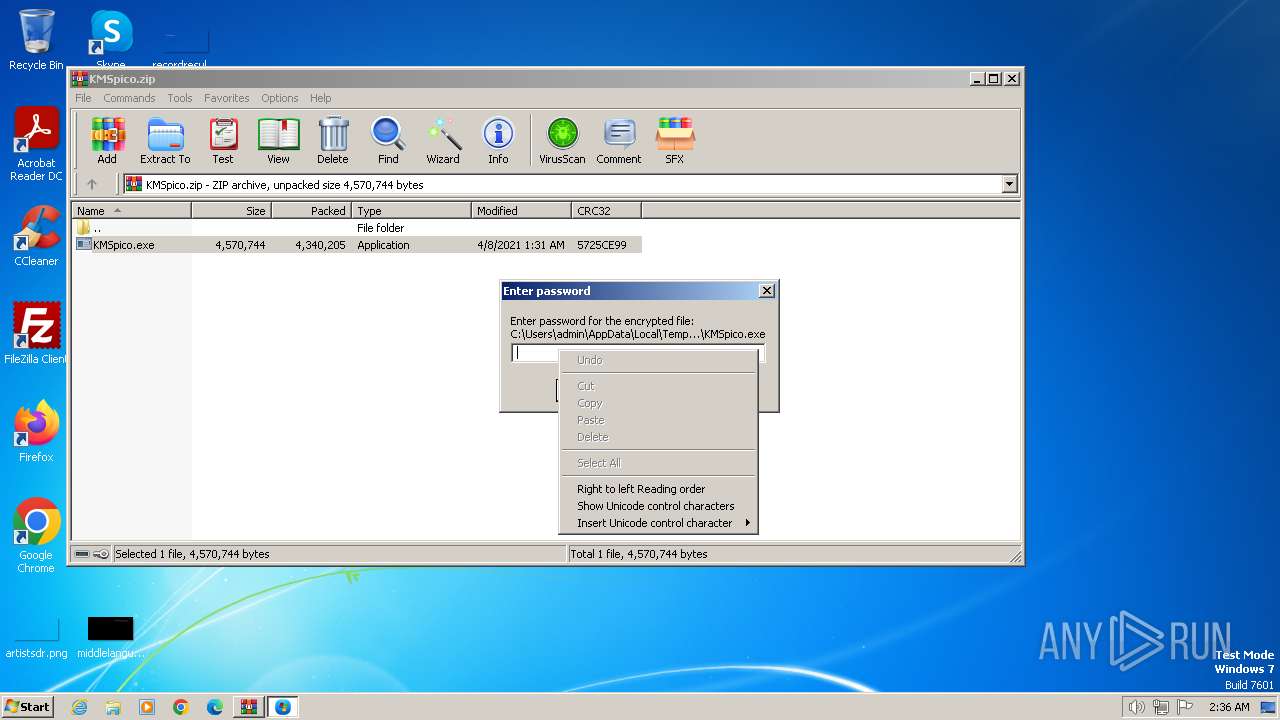
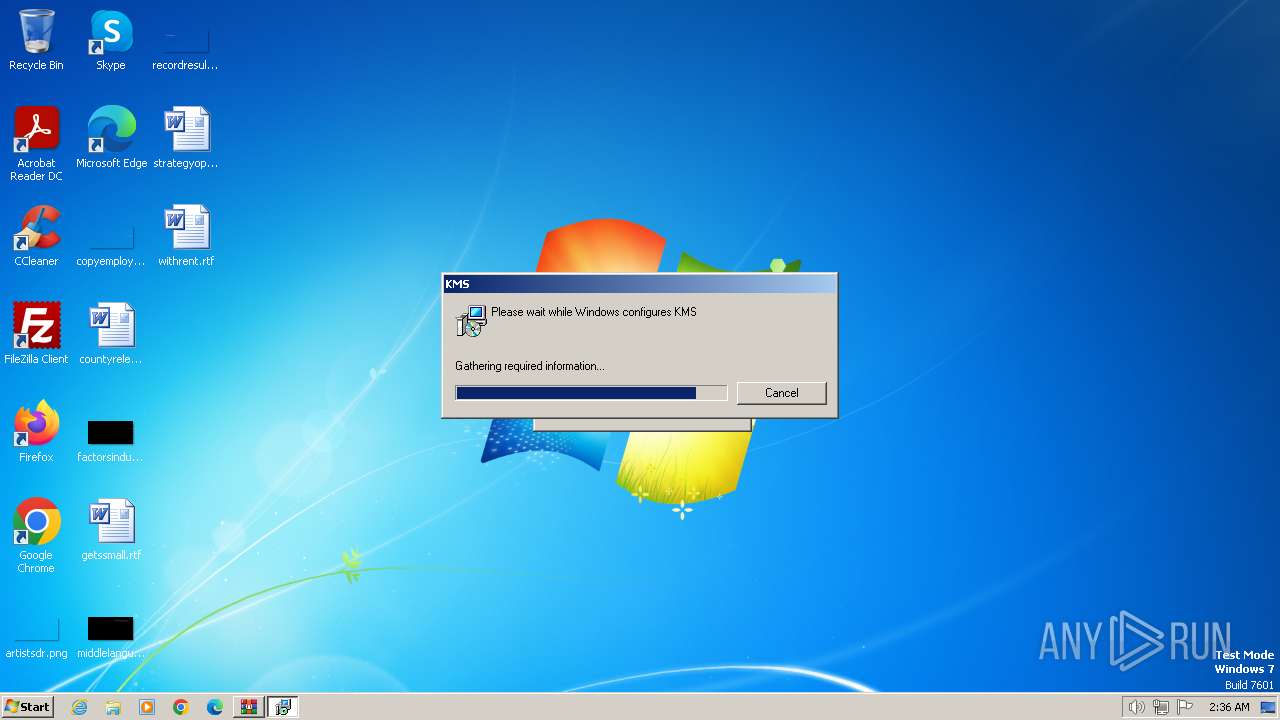
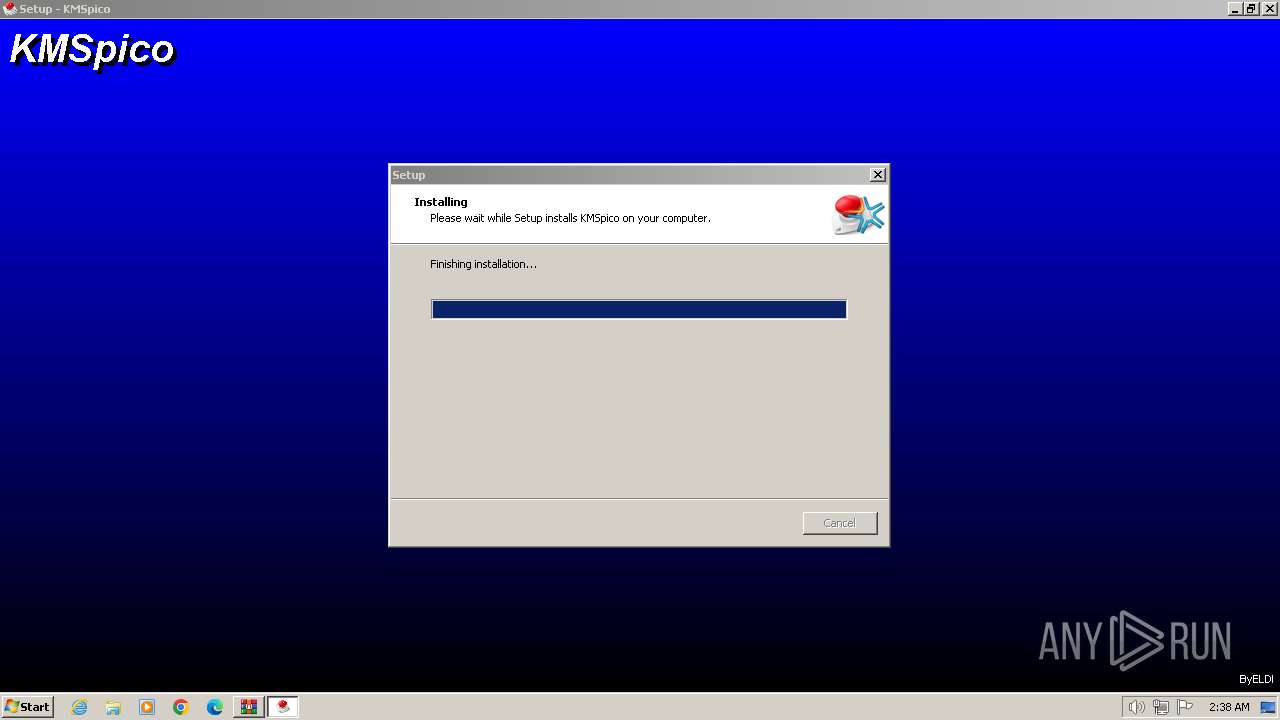
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1072)
- KMSpico.exe (PID: 3004)
- setup.exe (PID: 3708)
- setup.exe (PID: 3572)
- setup.tmp (PID: 1728)
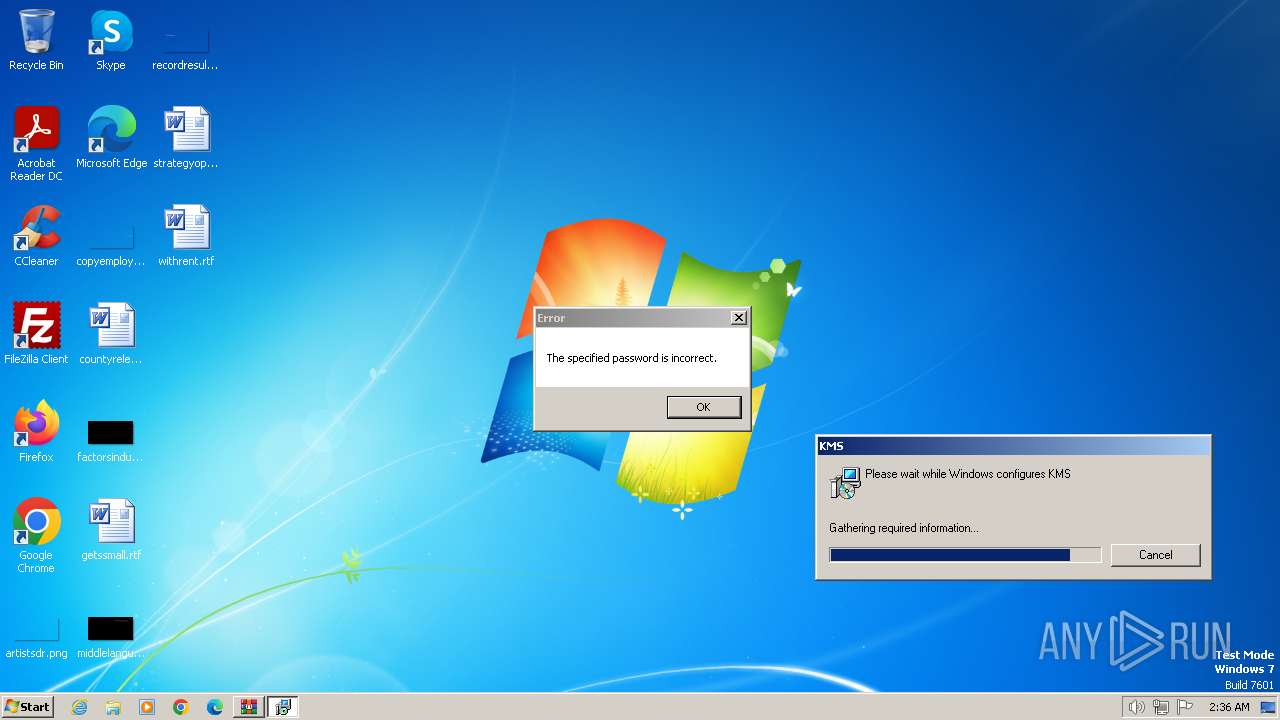
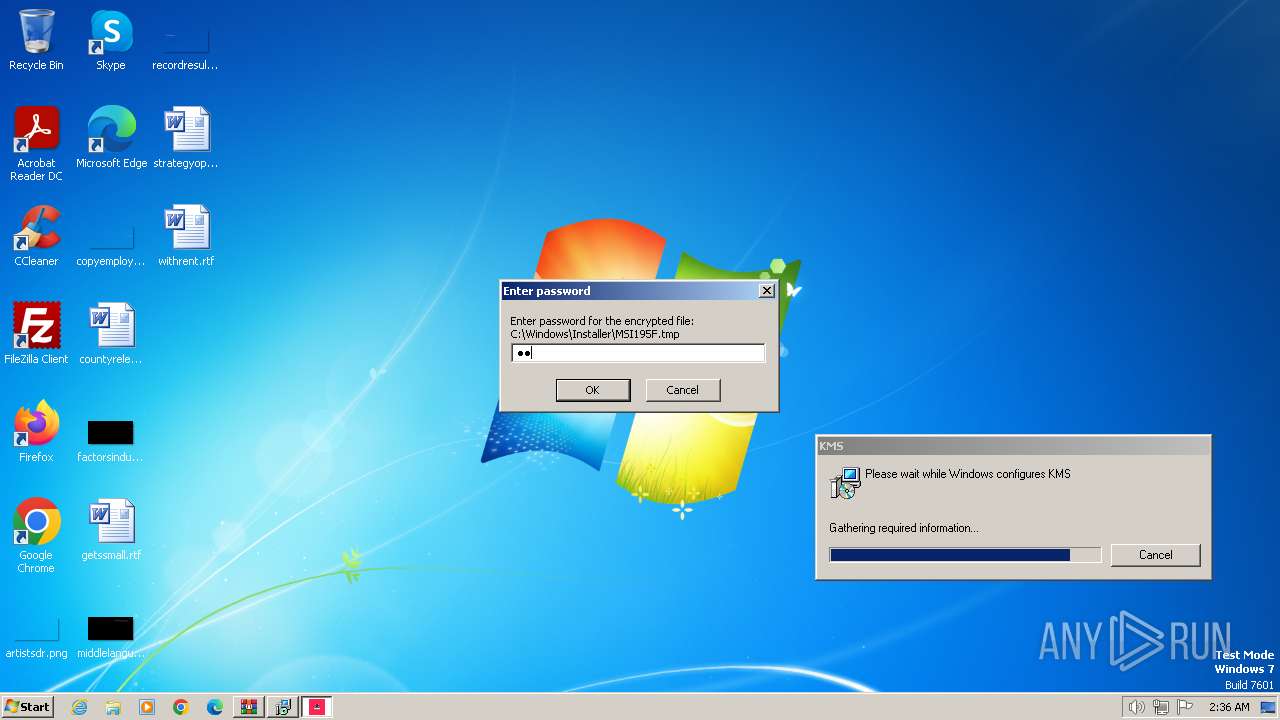
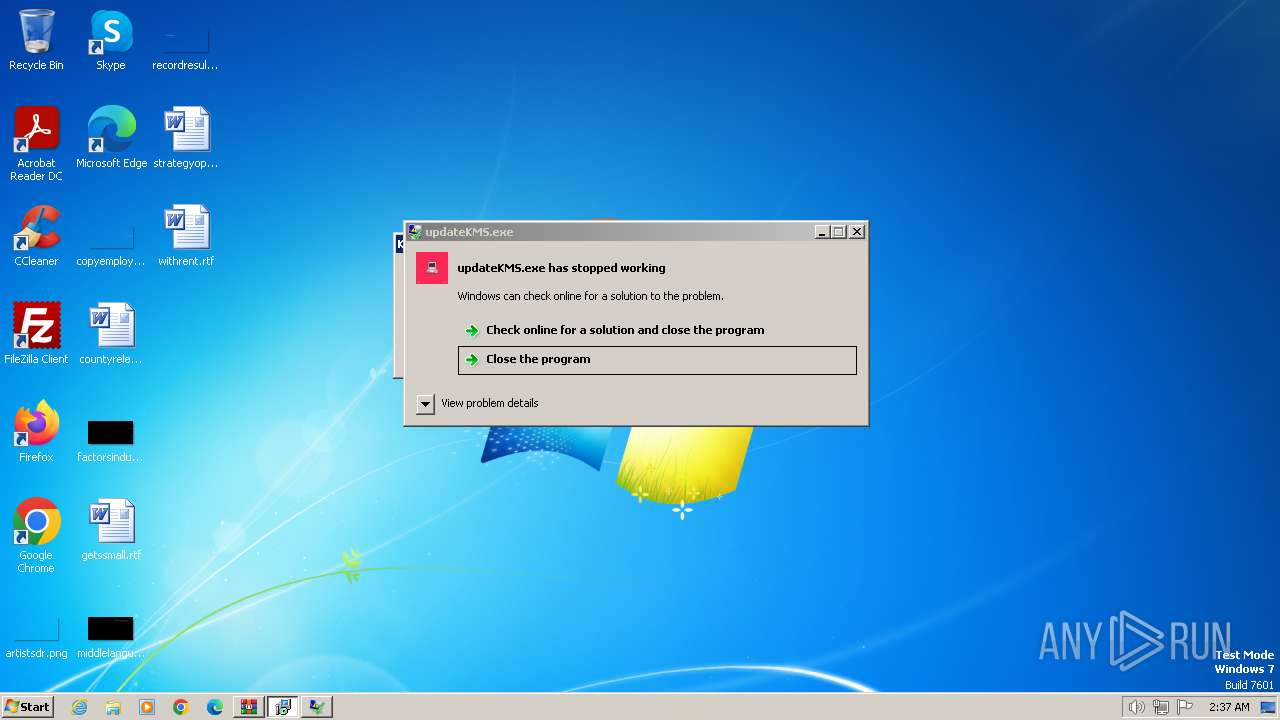
Steals credentials from Web Browsers
- updateKMS.exe (PID: 2444)
Actions looks like stealing of personal data
- updateKMS.exe (PID: 2444)
Creates a writable file in the system directory
- setup.tmp (PID: 1728)
SUSPICIOUS
Process drops legitimate windows executable
- KMSpico.exe (PID: 3004)
- setup.tmp (PID: 1728)
Reads security settings of Internet Explorer
- KMSpico.exe (PID: 3004)
- WinRAR.exe (PID: 1072)
- updateKMS.exe (PID: 2444)
Executable content was dropped or overwritten
- KMSpico.exe (PID: 3004)
- setup.exe (PID: 3708)
- setup.exe (PID: 3572)
- setup.tmp (PID: 1728)
Reads the Internet Settings
- KMSpico.exe (PID: 3004)
- updateKMS.exe (PID: 2444)
Accesses Microsoft Outlook profiles
- updateKMS.exe (PID: 2444)
Reads the Windows owner or organization settings
- setup.tmp (PID: 1728)
Reads browser cookies
- updateKMS.exe (PID: 2444)
Modifies the phishing filter of IE
- setup.tmp (PID: 1728)
Starts CMD.EXE for commands execution
- setup.tmp (PID: 1728)
Executing commands from ".cmd" file
- setup.tmp (PID: 1728)
Starts SC.EXE for service management
- cmd.exe (PID: 1368)
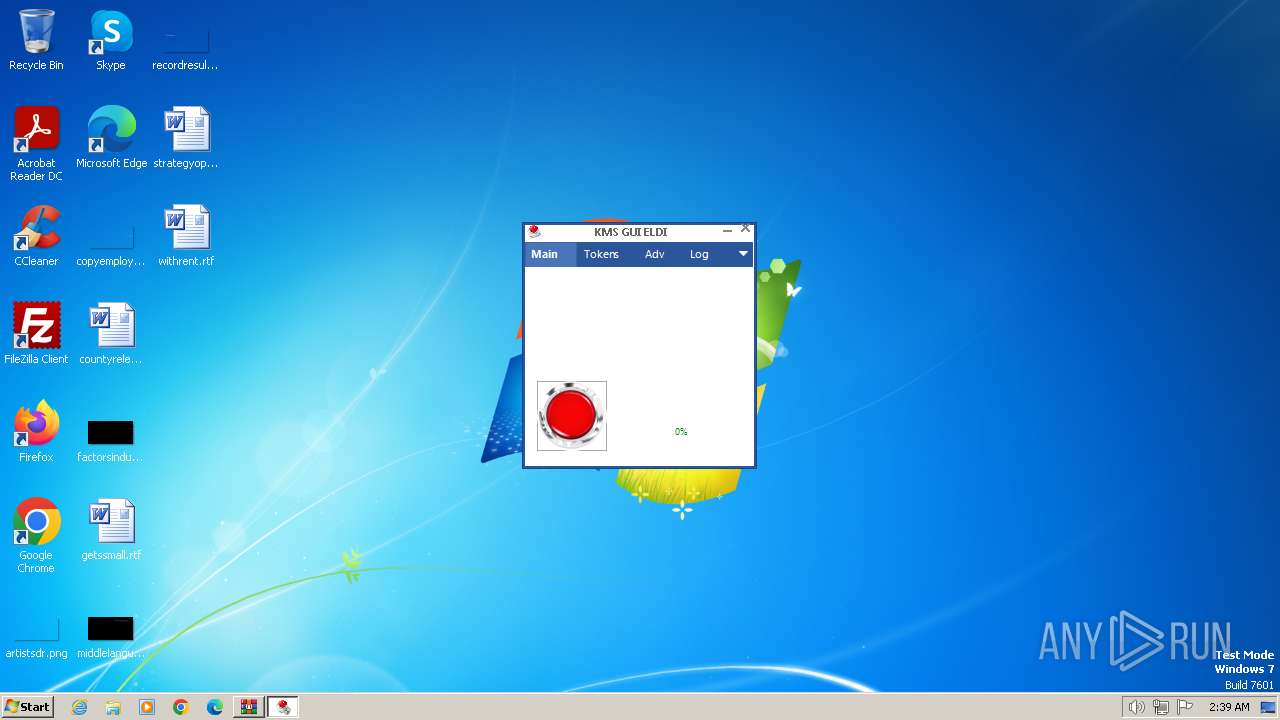
Creates or modifies Windows services
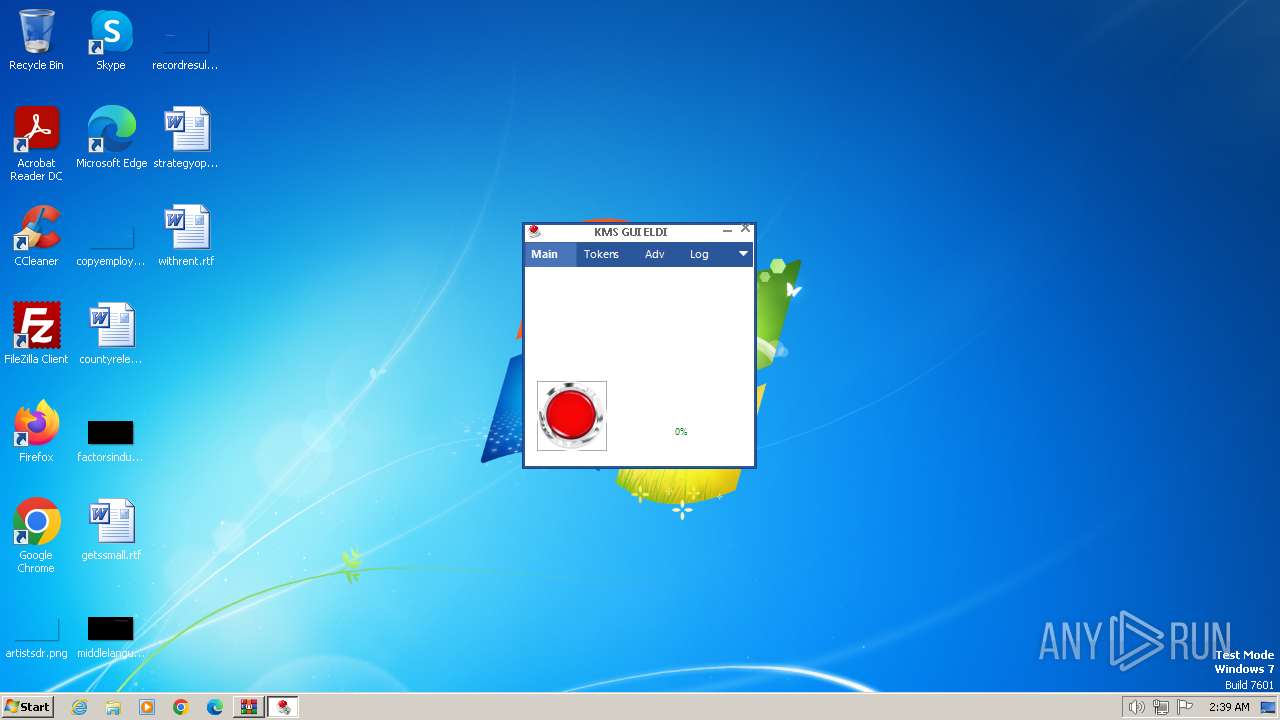
- KMSELDI.exe (PID: 748)
Non-standard symbols in registry
- setup.tmp (PID: 1728)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1072)
Checks supported languages
- KMSpico.exe (PID: 3004)
- updateKMS.exe (PID: 2444)
- setup.exe (PID: 3708)
- setup.tmp (PID: 3216)
- setup.tmp (PID: 1728)
- setup.exe (PID: 3572)
- UninsHs.exe (PID: 2176)
- KMSELDI.exe (PID: 748)
- AutoPico.exe (PID: 552)
- KMSELDI.exe (PID: 268)
- KMSELDI.exe (PID: 2444)
- KMSELDI.exe (PID: 2560)
- KMSELDI.exe (PID: 3900)
Reads the computer name
- KMSpico.exe (PID: 3004)
- updateKMS.exe (PID: 2444)
- setup.tmp (PID: 3216)
- setup.tmp (PID: 1728)
- KMSELDI.exe (PID: 748)
- AutoPico.exe (PID: 552)
- KMSELDI.exe (PID: 268)
- KMSELDI.exe (PID: 2444)
- KMSELDI.exe (PID: 2560)
- KMSELDI.exe (PID: 3900)
Create files in a temporary directory
- KMSpico.exe (PID: 3004)
- setup.exe (PID: 3708)
- setup.exe (PID: 3572)
- setup.tmp (PID: 1728)
Checks proxy server information
- updateKMS.exe (PID: 2444)
Reads the machine GUID from the registry
- updateKMS.exe (PID: 2444)
- KMSELDI.exe (PID: 748)
- KMSELDI.exe (PID: 268)
- AutoPico.exe (PID: 552)
- KMSELDI.exe (PID: 2444)
- KMSELDI.exe (PID: 2560)
- KMSELDI.exe (PID: 3900)
Creates files in the program directory
- updateKMS.exe (PID: 2444)
- setup.tmp (PID: 1728)
- KMSELDI.exe (PID: 748)
- KMSELDI.exe (PID: 268)
- AutoPico.exe (PID: 552)
- KMSELDI.exe (PID: 2444)
- KMSELDI.exe (PID: 2560)
- KMSELDI.exe (PID: 3900)
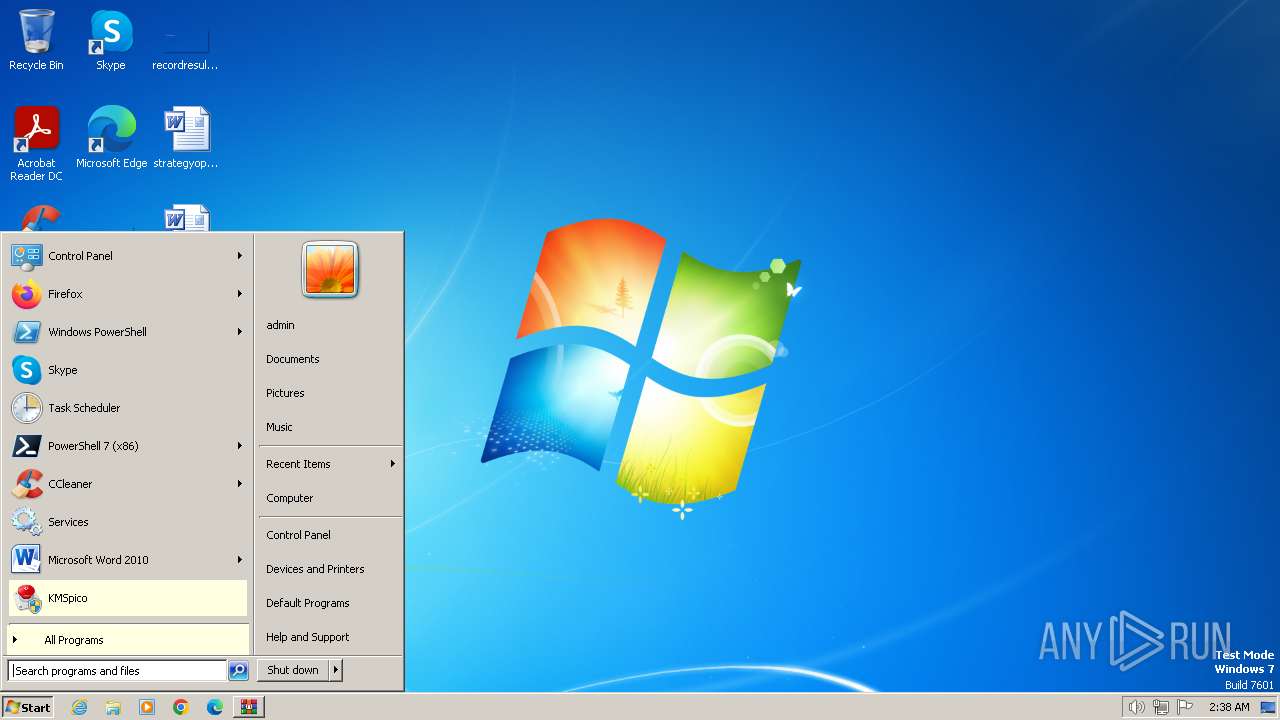
Creates a software uninstall entry
- setup.tmp (PID: 1728)
Reads Environment values
- KMSELDI.exe (PID: 748)
- AutoPico.exe (PID: 552)
- KMSELDI.exe (PID: 268)
- KMSELDI.exe (PID: 2444)
- KMSELDI.exe (PID: 2560)
- KMSELDI.exe (PID: 3900)
Reads product name
- KMSELDI.exe (PID: 748)
- AutoPico.exe (PID: 552)
- KMSELDI.exe (PID: 268)
- KMSELDI.exe (PID: 2444)
- KMSELDI.exe (PID: 2560)
- KMSELDI.exe (PID: 3900)
Reads Microsoft Office registry keys
- KMSELDI.exe (PID: 748)
- AutoPico.exe (PID: 552)
- KMSELDI.exe (PID: 268)
- KMSELDI.exe (PID: 2444)
- KMSELDI.exe (PID: 2560)
- KMSELDI.exe (PID: 3900)
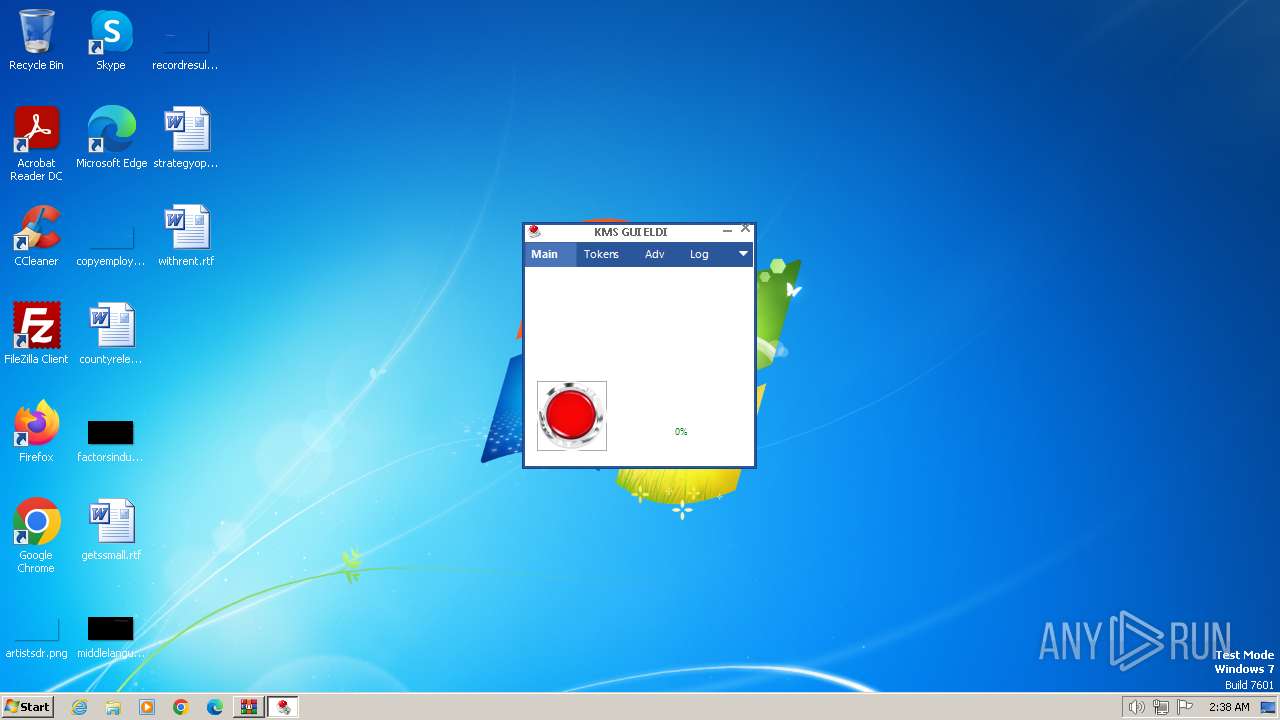
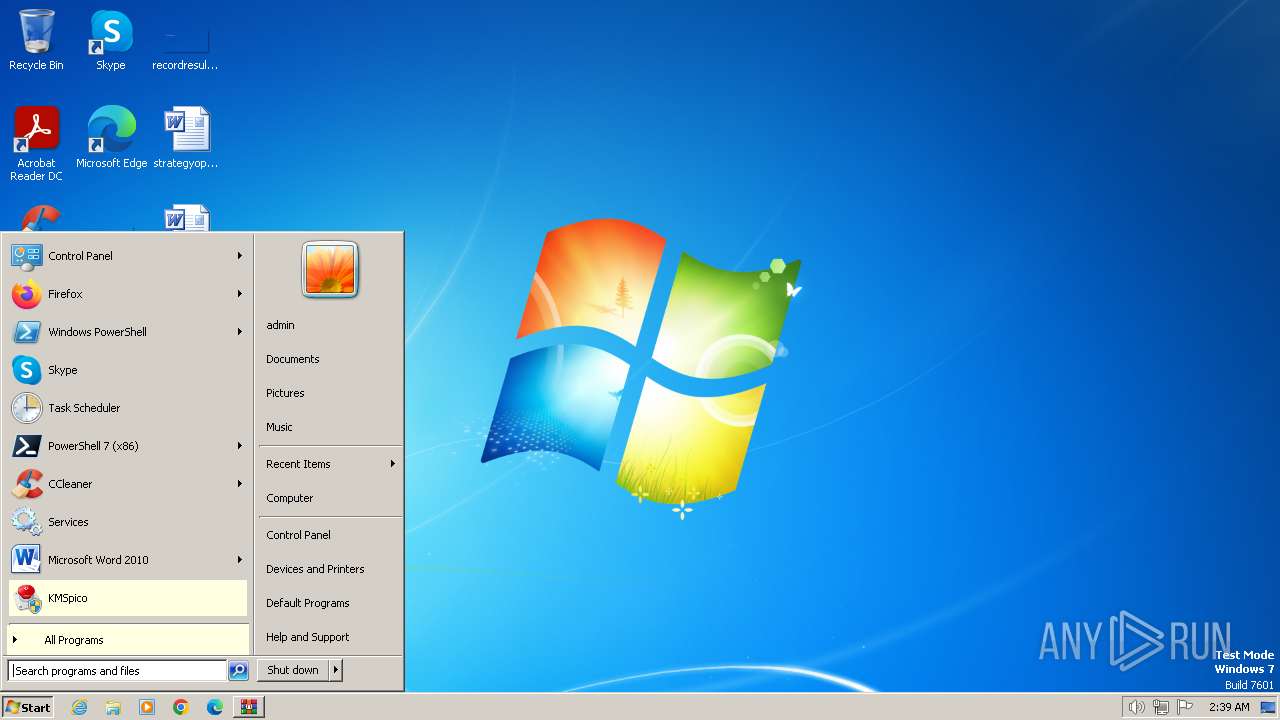
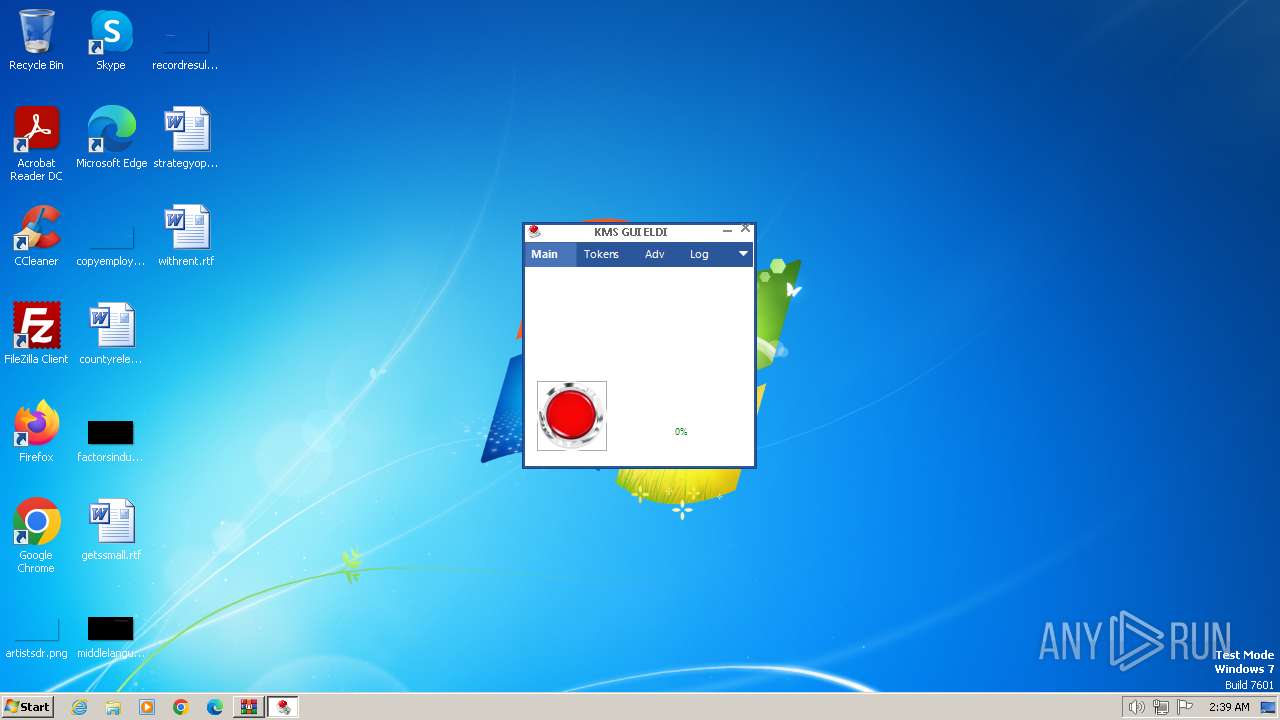
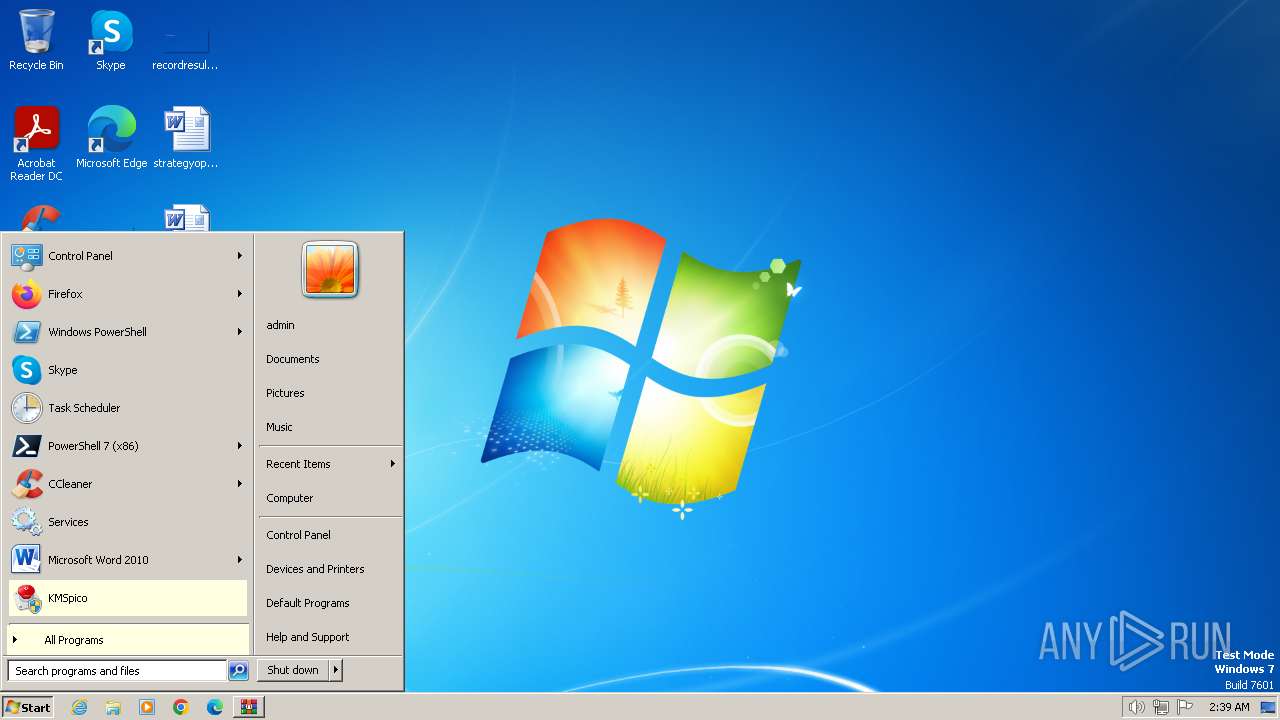
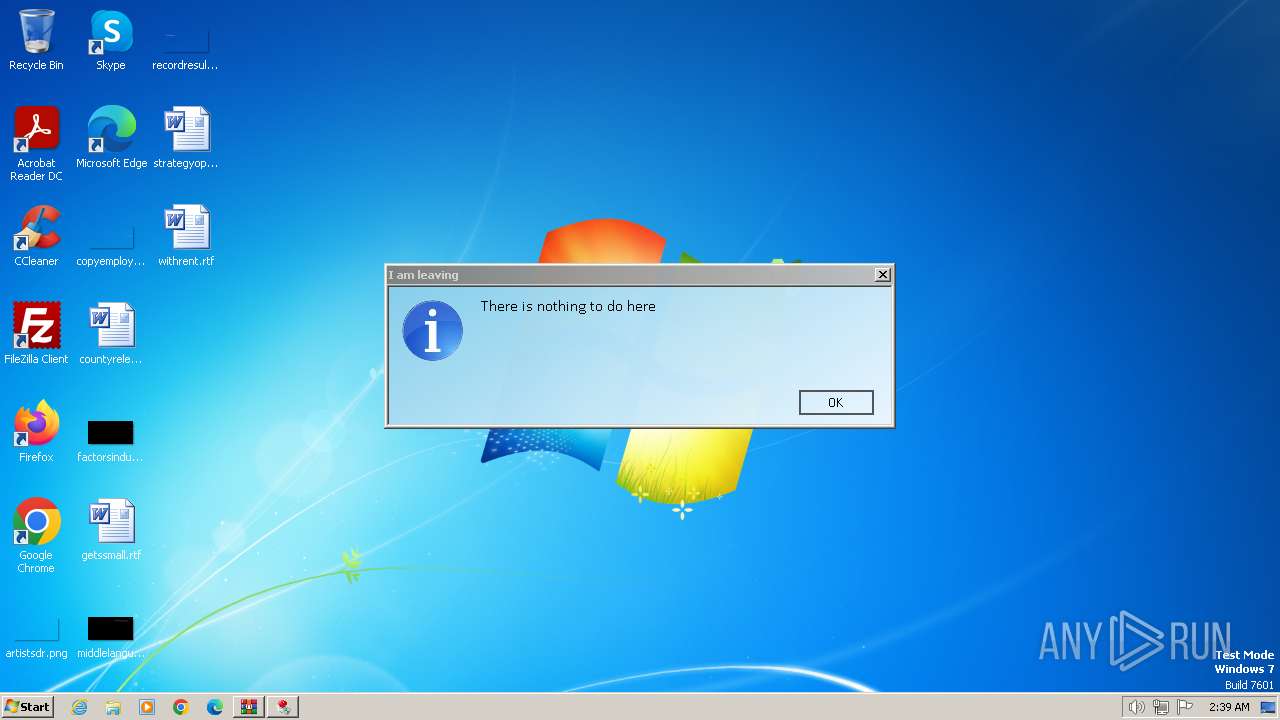
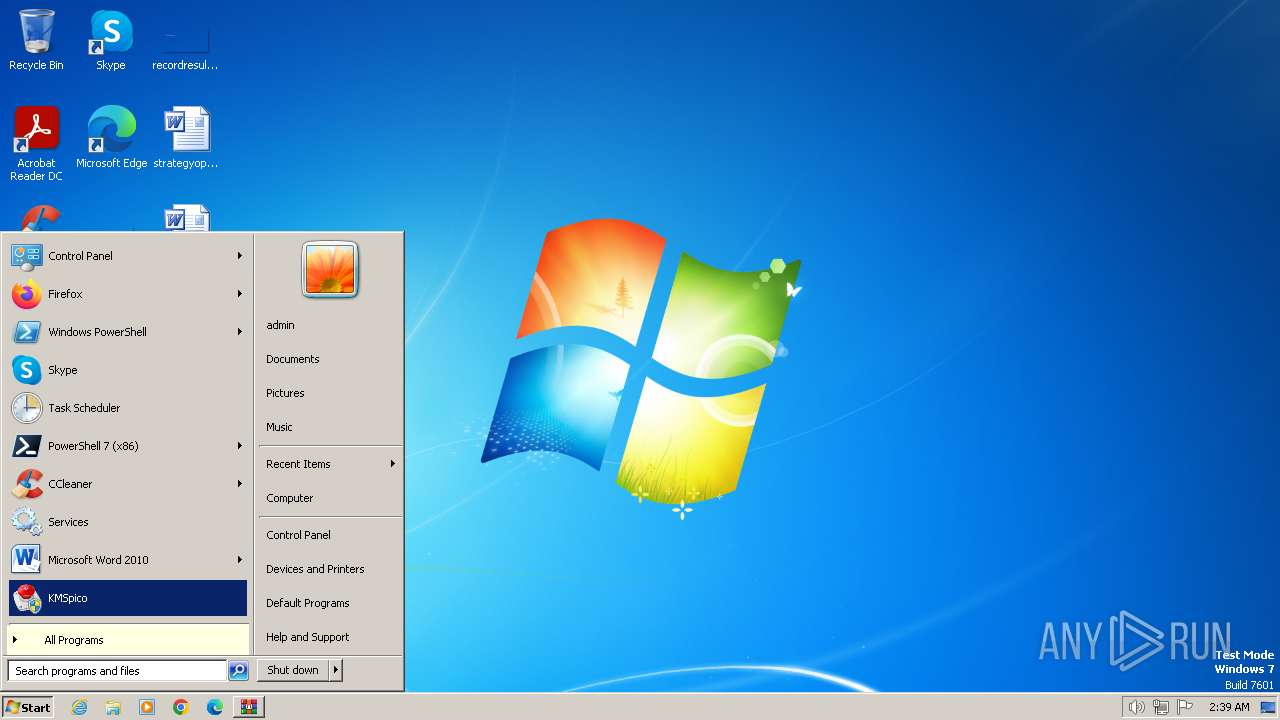
Manual execution by a user
- KMSELDI.exe (PID: 3036)
- KMSELDI.exe (PID: 268)
- KMSELDI.exe (PID: 3352)
- KMSELDI.exe (PID: 2444)
- KMSELDI.exe (PID: 2192)
- KMSELDI.exe (PID: 2560)
- KMSELDI.exe (PID: 3900)
- KMSELDI.exe (PID: 3492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
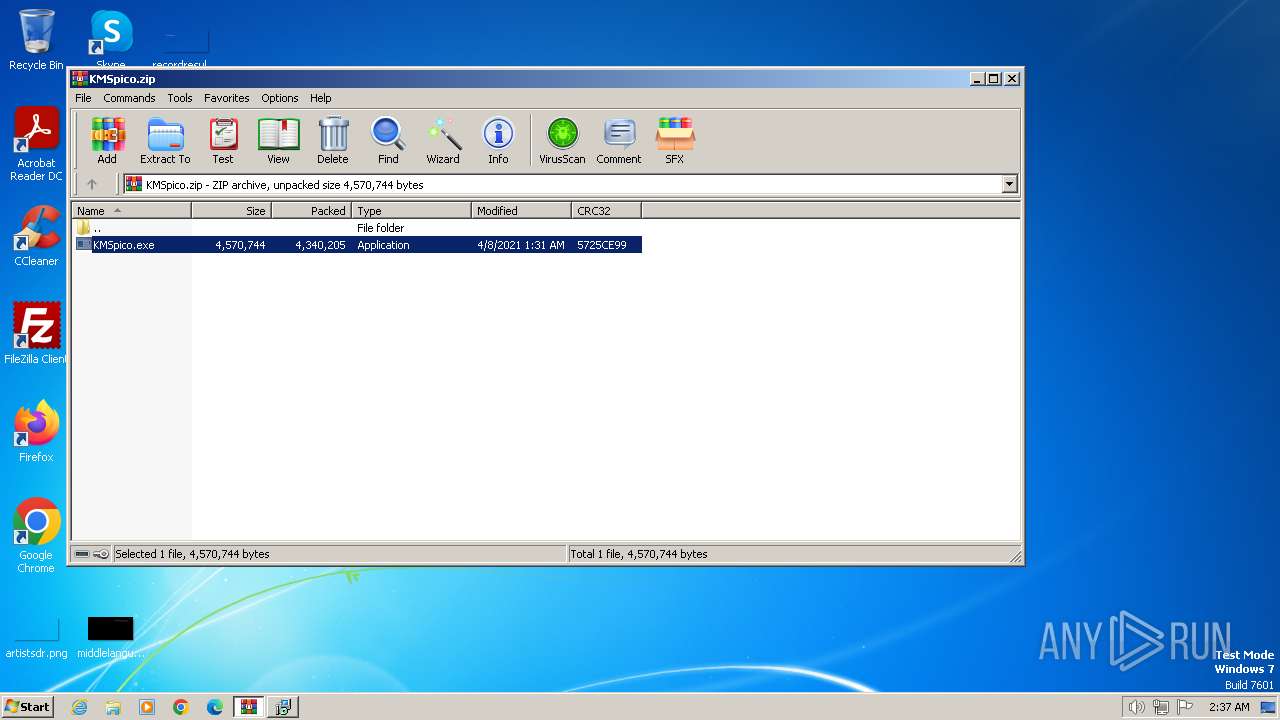
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2021:04:07 19:31:42 |
| ZipCRC: | 0x5725ce99 |
| ZipCompressedSize: | 4340205 |
| ZipUncompressedSize: | 4570744 |
| ZipFileName: | KMSpico.exe |
Total processes
88
Monitored processes
24
Malicious processes
7
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Program Files\KMSpico\KMSELDI.exe" | C:\Program Files\KMSpico\KMSELDI.exe | explorer.exe | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: KMS GUI ELDI Exit code: 3221225547 Version: 37.1.0.0 Modules
| |||||||||||||||
| 552 | "C:\Program Files\KMSpico\AutoPico.exe" /silent | C:\Program Files\KMSpico\AutoPico.exe | setup.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: AutoPico Exit code: 0 Version: 16.1.0.0 Modules
| |||||||||||||||
| 748 | "C:\Program Files\KMSpico\KMSELDI.exe" /silent /backup | C:\Program Files\KMSpico\KMSELDI.exe | setup.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: KMS GUI ELDI Exit code: 4294967295 Version: 37.1.0.0 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\KMSpico.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1368 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Service.cmd"" | C:\Windows\System32\cmd.exe | — | setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1728 | "C:\Users\admin\AppData\Local\Temp\is-F26TR.tmp\setup.tmp" /SL5="$16016E,2952592,69120,C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe" /SPAWNWND=$180128 /NOTIFYWND=$1B0102 | C:\Users\admin\AppData\Local\Temp\is-F26TR.tmp\setup.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1816 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Task.cmd"" | C:\Windows\System32\cmd.exe | — | setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1880 | SCHTASKS /Create /TN "AutoPico Daily Restart" /TR "'C:\Program Files\KMSpico\AutoPico.exe' /silent" /SC DAILY /ST 23:59:59 /RU "NT AUTHORITY\SYSTEM" /RL Highest /F | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | "C:\Users\admin\AppData\Local\Temp\RarSFX1\updateKMS.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX1\updateKMS.exe | — | MSI195F.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\KMSpico\UninsHs.exe" /r0=KMSpico,default,C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe | C:\Program Files\KMSpico\UninsHs.exe | — | setup.tmp | |||||||||||
User: admin Company: Han-soft Integrity Level: HIGH Description: Uninstall for InnoSetup by Han-soft Exit code: 0 Version: 2.1.0.283 Modules
| |||||||||||||||
Total events
29 251
Read events
29 006
Write events
229
Delete events
16
Modification events
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KMSpico.zip | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
24
Suspicious files
29
Text files
719
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3572 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-F26TR.tmp\setup.tmp | executable | |
MD5:1778C1F66FF205875A6435A33229AB3C | SHA256:95C06ACAC4FE4598840E5556F9613D43AA1039C52DAC64536F59E45A70F79DA6 | |||
| 1728 | setup.tmp | C:\Program Files\KMSpico\DevComponents.DotNetBar2.dll | executable | |
MD5:1397B23F30681F97049DF61F94F54D05 | SHA256:FA76151A783250014AC8FA55D4C833100A623FCAD1D6E2DDADCDE259F5709609 | |||
| 1728 | setup.tmp | C:\Program Files\KMSpico\unins000.exe | executable | |
MD5:30C7E8E918403B9247315249A8842CE5 | SHA256:6D4FA6727CA952B7B44FA9F3538D84B64E06C76908C76FADE7846532A7115A49 | |||
| 1728 | setup.tmp | C:\Program Files\KMSpico\Vestris.ResourceLib.dll | executable | |
MD5:3D733144477CADCF77009EF614413630 | SHA256:392D73617FD0A55218261572ECE2F50301E0CFA29B5ED24C3F692130AA406AF3 | |||
| 1728 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-TCJ1E.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 1728 | setup.tmp | C:\Windows\system32\is-O0JCR.tmp | executable | |
MD5:3D733144477CADCF77009EF614413630 | SHA256:392D73617FD0A55218261572ECE2F50301E0CFA29B5ED24C3F692130AA406AF3 | |||
| 1728 | setup.tmp | C:\Program Files\KMSpico\AutoPico.exe | executable | |
MD5:CFE1C391464C446099A5EB33276F6D57 | SHA256:4A714D98CE40F5F3577C306A66CB4A6B1FF3FD01047C7F4581F8558F0BCDF5FA | |||
| 3708 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-OVM08.tmp\setup.tmp | executable | |
MD5:1778C1F66FF205875A6435A33229AB3C | SHA256:95C06ACAC4FE4598840E5556F9613D43AA1039C52DAC64536F59E45A70F79DA6 | |||
| 1728 | setup.tmp | C:\Program Files\KMSpico\is-44NE4.tmp | executable | |
MD5:1397B23F30681F97049DF61F94F54D05 | SHA256:FA76151A783250014AC8FA55D4C833100A623FCAD1D6E2DDADCDE259F5709609 | |||
| 1728 | setup.tmp | C:\Windows\System32\Vestris.ResourceLib.dll | executable | |
MD5:3D733144477CADCF77009EF614413630 | SHA256:392D73617FD0A55218261572ECE2F50301E0CFA29B5ED24C3F692130AA406AF3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
12
DNS requests
6
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2444 | updateKMS.exe | 49.13.77.253:443 | polyminers.com | Hetzner Online GmbH | DE | unknown |
748 | KMSELDI.exe | 148.251.54.81:123 | 1.pool.ntp.org | — | — | unknown |
552 | AutoPico.exe | 173.249.33.207:123 | 2.pool.ntp.org | — | — | unknown |
268 | KMSELDI.exe | 62.75.236.38:123 | 1.pool.ntp.org | — | — | unknown |
2444 | KMSELDI.exe | 116.203.244.102:123 | 3.pool.ntp.org | — | — | unknown |
2560 | KMSELDI.exe | 62.75.236.38:123 | 1.pool.ntp.org | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
polyminers.com |
| unknown |
dns.msftncsi.com |
| shared |
1.pool.ntp.org |
| whitelisted |
www.google.com |
| whitelisted |
2.pool.ntp.org |
| whitelisted |
3.pool.ntp.org |
| whitelisted |