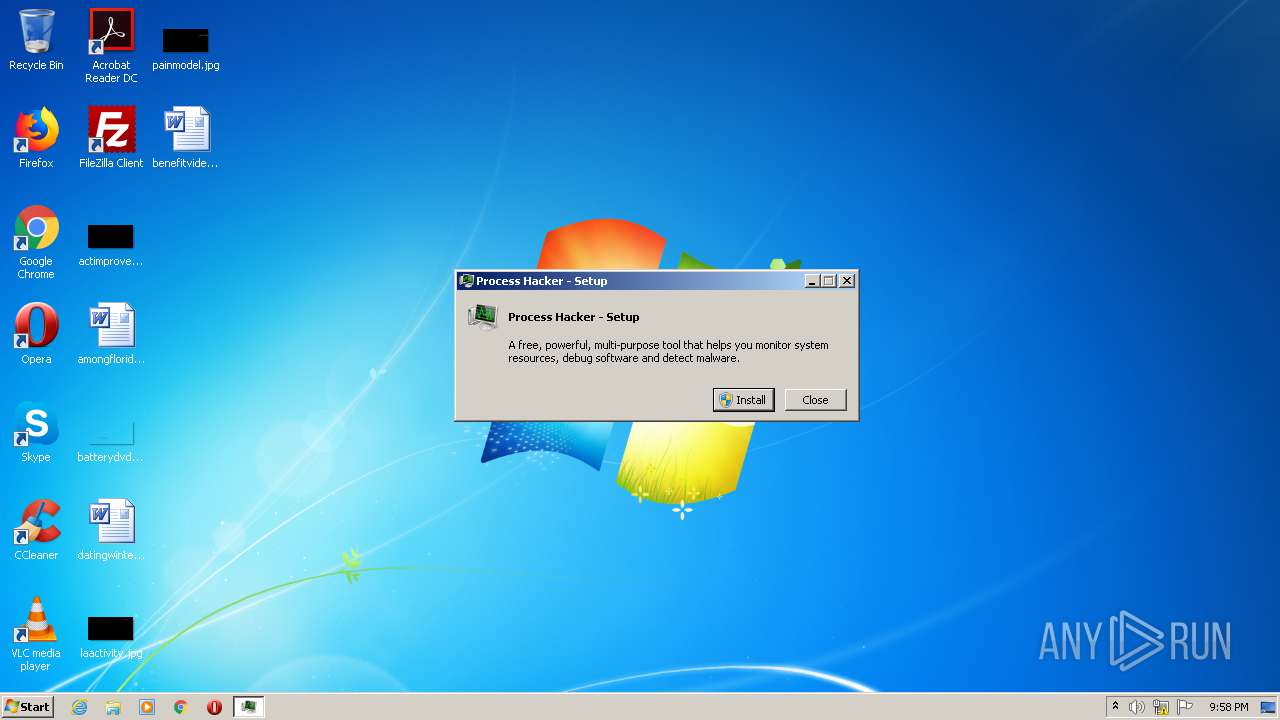
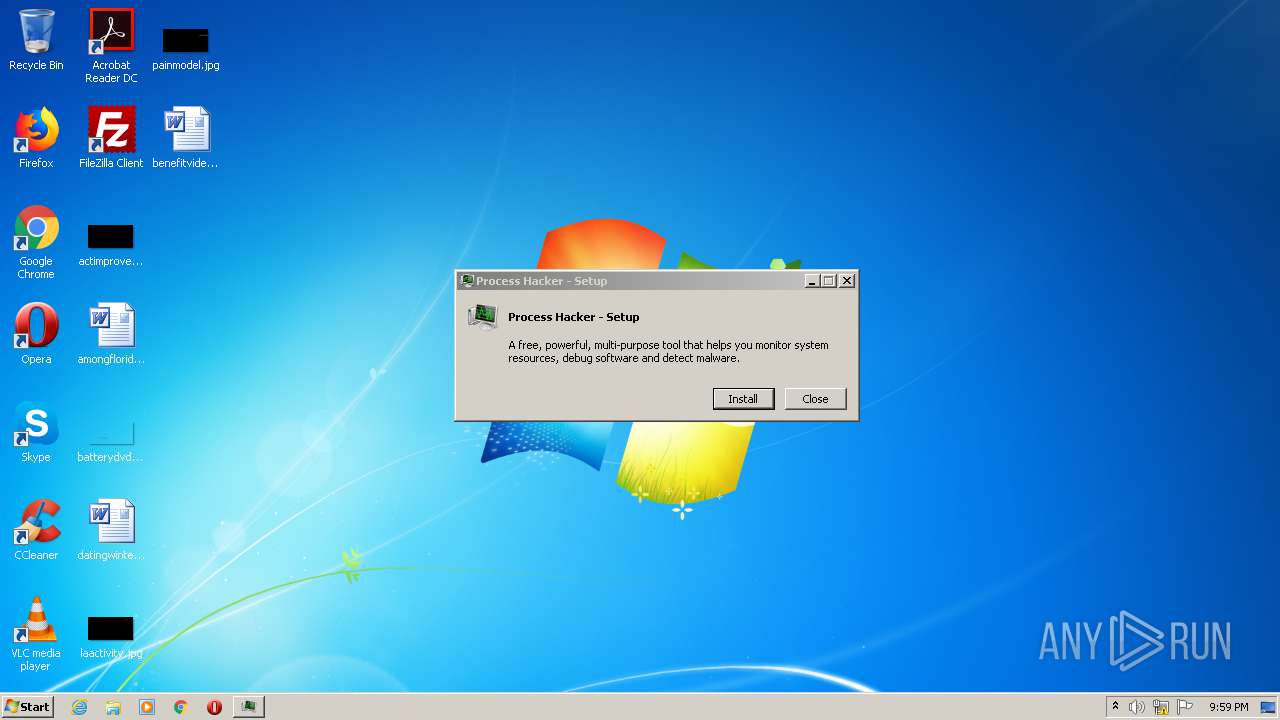
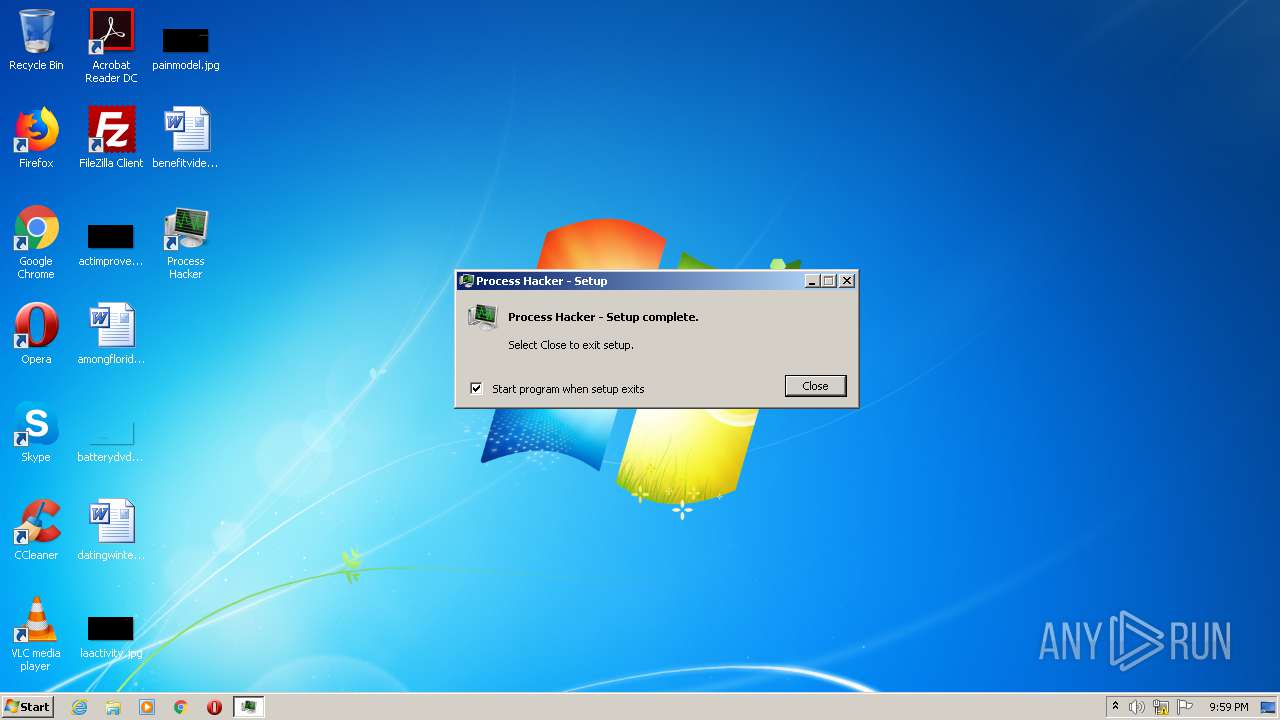
| File name: | processhacker-3.0.3477-setup.exe |
| Full analysis: | https://app.any.run/tasks/7066ebe6-d364-4ca4-b501-5443a87f87df |
| Verdict: | Malicious activity |
| Analysis date: | October 23, 2020, 20:58:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 76FE9E01C6A3FF99A933761C98608AD9 |
| SHA1: | D84322B560938E3C8D6E00E06921D12739B78D55 |
| SHA256: | A7E190E9638E8402B3CB7E65F5B2156AACCC63A509DD1F328D5083940919B0A1 |
| SSDEEP: | 49152:nUX80JS/bqKBlysEzG1eK+A/ZfAjZPZ0Zd4hWy2qctMjxBQUcldTc7D6RGdXIf9+:nUXt |
MALICIOUS
Application was dropped or rewritten from another process
- ProcessHacker.exe (PID: 4004)
Loads dropped or rewritten executable
- ProcessHacker.exe (PID: 4004)
Changes settings of System certificates
- ProcessHacker.exe (PID: 4004)
SUSPICIOUS
Adds / modifies Windows certificates
- ProcessHacker.exe (PID: 4004)
Creates files in the program directory
- processhacker-3.0.3477-setup.exe (PID: 2924)
Application launched itself
- processhacker-3.0.3477-setup.exe (PID: 2656)
Creates a software uninstall entry
- processhacker-3.0.3477-setup.exe (PID: 2924)
Executable content was dropped or overwritten
- processhacker-3.0.3477-setup.exe (PID: 2924)
INFO
Reads settings of System Certificates
- ProcessHacker.exe (PID: 4004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2037:12:16 01:24:23+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.27 |
| CodeSize: | 171520 |
| InitializedDataSize: | 8640512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x13f10 |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.8004.3477 |
| ProductVersionNumber: | 3.0.8004.3477 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (Australian) |
| CharacterSet: | Unicode |
| CompanyName: | Process Hacker |
| FileDescription: | Process Hacker - Setup |
| FileVersion: | 3.0.8004.3477 |
| InternalName: | processhacker-setup.exe |
| LegalCopyright: | Licensed under the GNU GPL, v3. Copyright (C) 2017 |
| OriginalFileName: | processhacker-setup.exe |
| ProductName: | Process Hacker |
| ProductVersion: | 3.0.8004.3477 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Dec-2037 00:24:23 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Process Hacker |
| FileDescription: | Process Hacker - Setup |
| FileVersion: | 3.0.8004.3477 |
| InternalName: | processhacker-setup.exe |
| LegalCopyright: | Licensed under the GNU GPL, v3. Copyright (C) 2017 |
| OriginalFilename: | processhacker-setup.exe |
| ProductName: | Process Hacker |
| ProductVersion: | 3.0.8004.3477 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 16-Dec-2037 00:24:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00029C7D | 0x00029E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65036 |
.rdata | 0x0002B000 | 0x00026DA4 | 0x00026E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.4343 |
.data | 0x00052000 | 0x00002268 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.15213 |
.didat | 0x00055000 | 0x000000A8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.49479 |
.rsrc | 0x00056000 | 0x00812038 | 0x00812200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.08258 |
.reloc | 0x00869000 | 0x000021C8 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64501 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19222 | 2841 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.80858 | 744 | UNKNOWN | English - Australia | RT_ICON |
3 | 3.29425 | 488 | UNKNOWN | English - Australia | RT_ICON |
4 | 3.1653 | 296 | UNKNOWN | English - Australia | RT_ICON |
5 | 5.5254 | 3752 | UNKNOWN | English - Australia | RT_ICON |
6 | 6.002 | 2216 | UNKNOWN | English - Australia | RT_ICON |
7 | 5.2012 | 1736 | UNKNOWN | English - Australia | RT_ICON |
8 | 2.89511 | 1384 | UNKNOWN | English - Australia | RT_ICON |
9 | 7.94638 | 67507 | UNKNOWN | English - Australia | RT_ICON |
10 | 5.27113 | 9640 | UNKNOWN | English - Australia | RT_ICON |
Imports
COMCTL32.dll (delay-loaded) |
COMDLG32.dll |
KERNEL32.dll |
ntdll.dll |
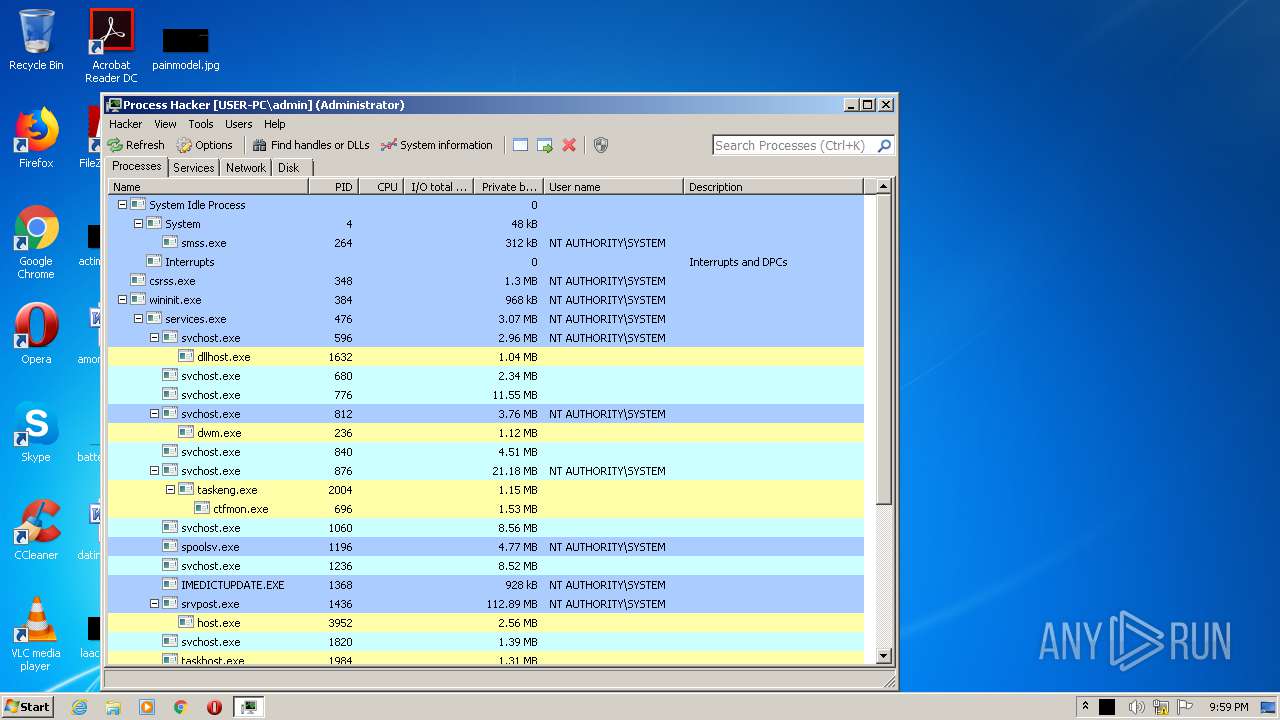
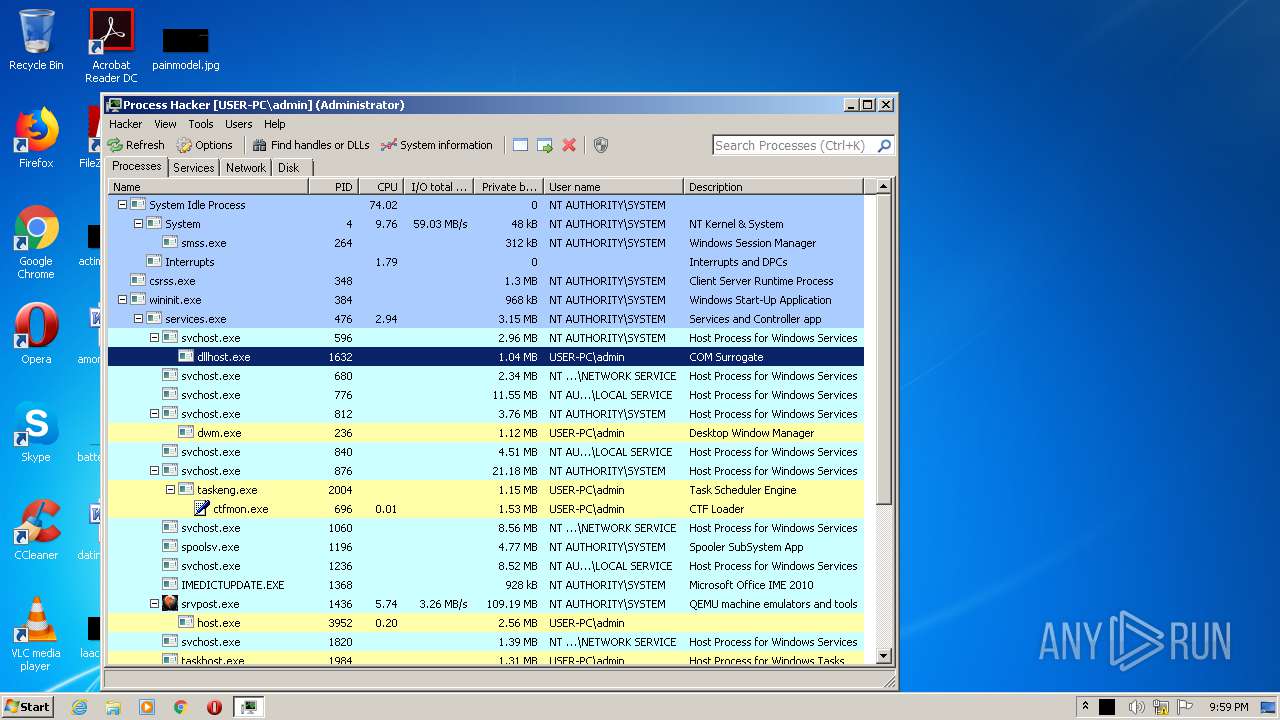
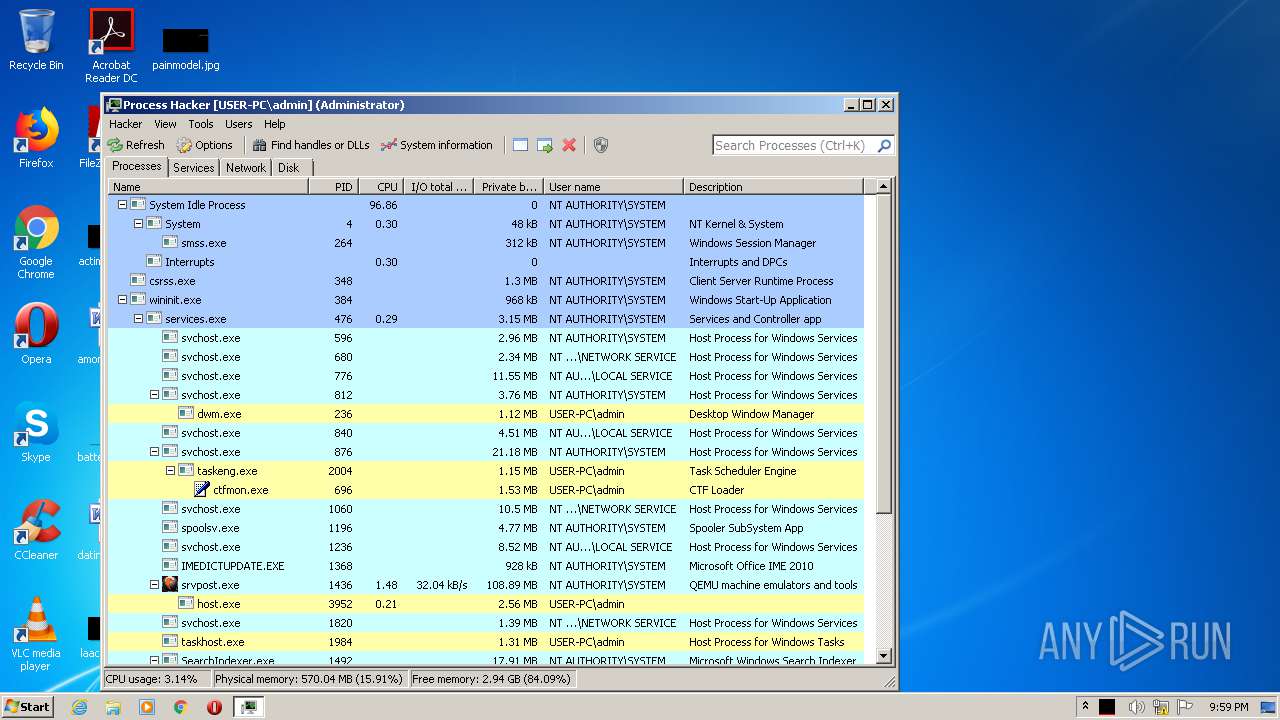
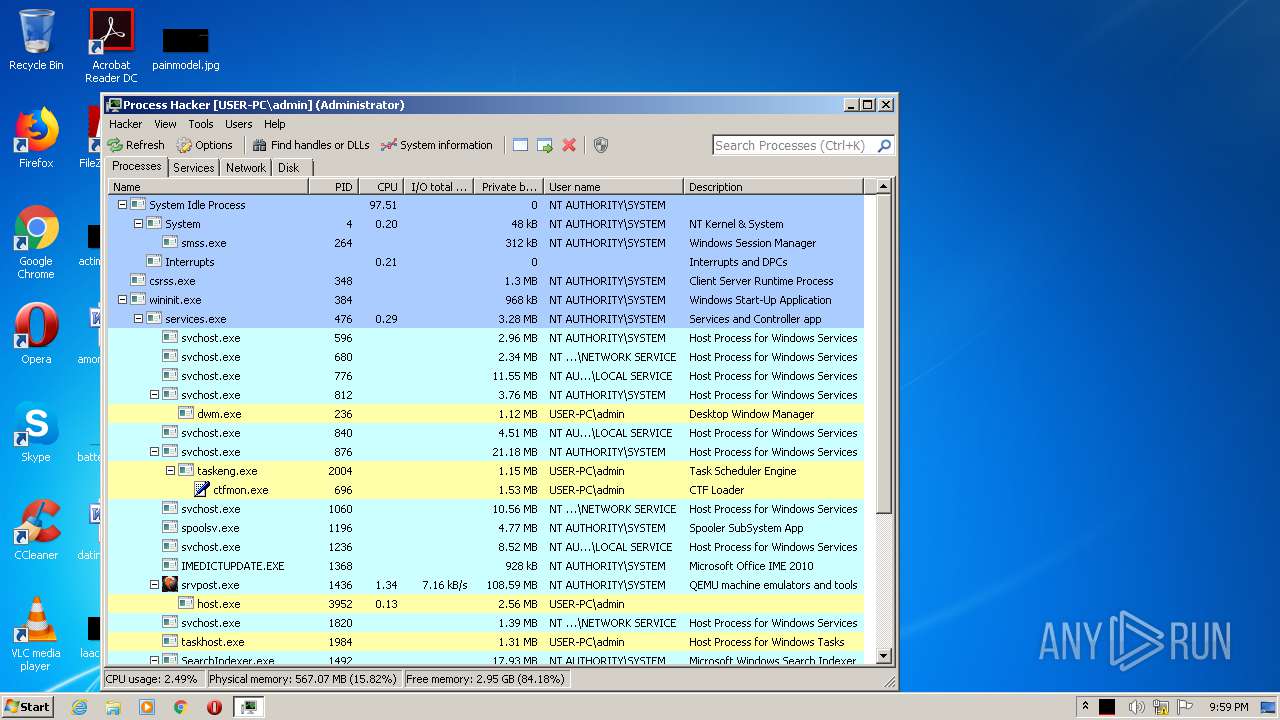
Total processes
40
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2656 | "C:\Users\admin\AppData\Local\Temp\processhacker-3.0.3477-setup.exe" | C:\Users\admin\AppData\Local\Temp\processhacker-3.0.3477-setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Process Hacker Integrity Level: MEDIUM Description: Process Hacker - Setup Exit code: 0 Version: 3.0.8004.3477 Modules
| |||||||||||||||
| 2924 | "C:\Users\admin\AppData\Local\Temp\processhacker-3.0.3477-setup.exe" "C:\Users\admin\AppData\Local\Temp\processhacker-3.0.3477-setup.exe" | C:\Users\admin\AppData\Local\Temp\processhacker-3.0.3477-setup.exe | processhacker-3.0.3477-setup.exe | ||||||||||||
User: admin Company: Process Hacker Integrity Level: HIGH Description: Process Hacker - Setup Exit code: 0 Version: 3.0.8004.3477 Modules
| |||||||||||||||
| 4004 | "C:\Program Files\Process Hacker\ProcessHacker.exe" | C:\Program Files\Process Hacker\ProcessHacker.exe | processhacker-3.0.3477-setup.exe | ||||||||||||
User: admin Company: Process Hacker Integrity Level: HIGH Description: Process Hacker Exit code: 0 Version: 3.0.8004.3477 Modules
| |||||||||||||||
Total events
852
Read events
822
Write events
30
Delete events
0
Modification events
| (PID) Process: | (2656) processhacker-3.0.3477-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2656) processhacker-3.0.3477-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2924) processhacker-3.0.3477-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ProcessHacker |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Process Hacker\processhacker.exe,0 | |||
| (PID) Process: | (2924) processhacker-3.0.3477-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ProcessHacker |
| Operation: | write | Name: | DisplayName |
Value: Process Hacker | |||
| (PID) Process: | (2924) processhacker-3.0.3477-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ProcessHacker |
| Operation: | write | Name: | DisplayVersion |
Value: 3.x | |||
| (PID) Process: | (2924) processhacker-3.0.3477-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ProcessHacker |
| Operation: | write | Name: | HelpLink |
Value: https://processhacker.sourceforge.io/ | |||
| (PID) Process: | (2924) processhacker-3.0.3477-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ProcessHacker |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Process Hacker\ | |||
| (PID) Process: | (2924) processhacker-3.0.3477-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ProcessHacker |
| Operation: | write | Name: | Publisher |
Value: Process Hacker | |||
| (PID) Process: | (2924) processhacker-3.0.3477-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ProcessHacker |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Process Hacker\\processhacker-setup.exe" -uninstall | |||
| (PID) Process: | (2924) processhacker-3.0.3477-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ProcessHacker |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
Executable files
15
Suspicious files
1
Text files
5
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | processhacker-3.0.3477-setup.exe | C:\Program Files\Process Hacker\capslist.txt | text | |
MD5:— | SHA256:— | |||
| 2924 | processhacker-3.0.3477-setup.exe | C:\Users\Public\Desktop\Process Hacker.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2924 | processhacker-3.0.3477-setup.exe | C:\Program Files\Process Hacker\processhacker-setup.exe | executable | |
MD5:— | SHA256:— | |||
| 2924 | processhacker-3.0.3477-setup.exe | C:\Program Files\Process Hacker\peview.exe | executable | |
MD5:— | SHA256:— | |||
| 2924 | processhacker-3.0.3477-setup.exe | C:\Program Files\Process Hacker\ProcessHacker.sig | binary | |
MD5:— | SHA256:— | |||
| 2924 | processhacker-3.0.3477-setup.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Process Hacker.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2924 | processhacker-3.0.3477-setup.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\PE Viewer.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2924 | processhacker-3.0.3477-setup.exe | C:\Program Files\Process Hacker\COPYRIGHT.txt | text | |
MD5:39B07060A5C6199730219E29C747C061 | SHA256:319CD301CF40BE03C00CD086560D4E810E0F6D0DBFDC2D28D6AF3522C027CF49 | |||
| 2924 | processhacker-3.0.3477-setup.exe | C:\Program Files\Process Hacker\LICENSE.txt | text | |
MD5:EB59E0A5D01D0A5B02DA0C9E7786969F | SHA256:C38E811F6F83428921D0CECD998A44B717149B577B4C1A63B66064F03C34E4E7 | |||
| 2924 | processhacker-3.0.3477-setup.exe | C:\Program Files\Process Hacker\plugins\ExtendedTools.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4004 | ProcessHacker.exe | 162.243.25.33:443 | wj32.org | Digital Ocean, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wj32.org |
| whitelisted |