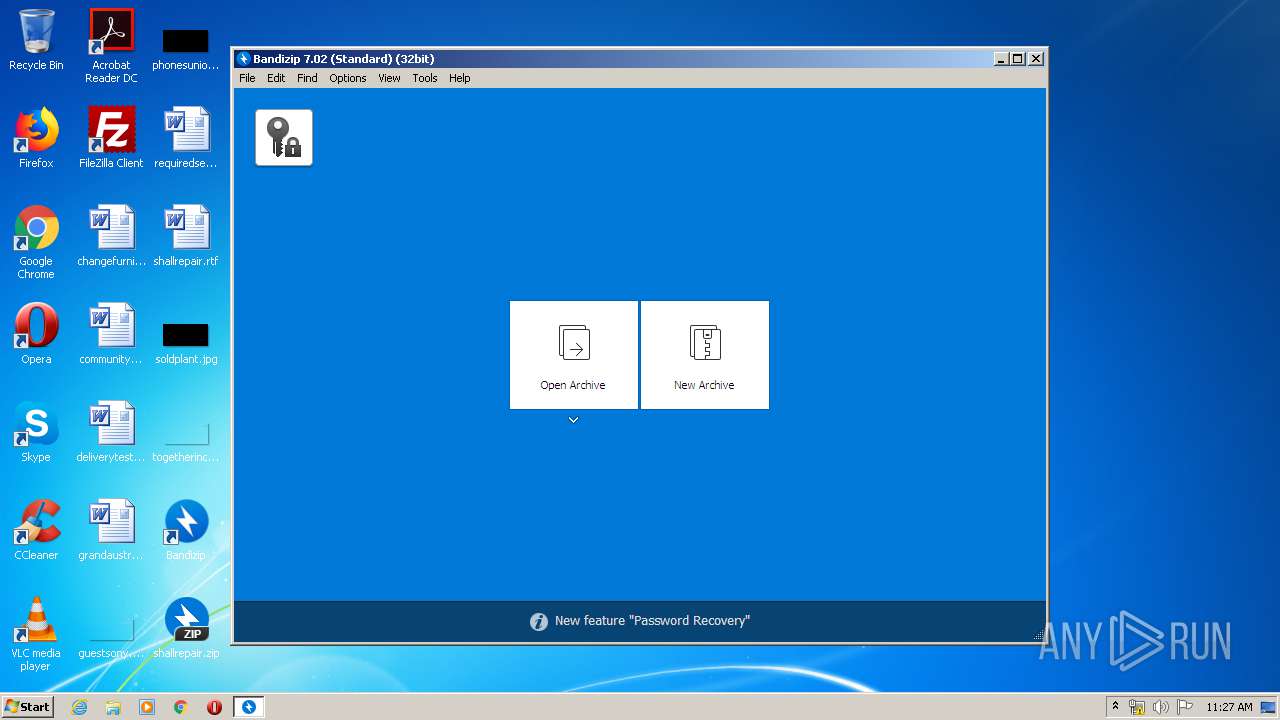
| File name: | BANDIZIP-SETUP-ONLINE.EXE |
| Full analysis: | https://app.any.run/tasks/9a01e2ba-7bd2-4777-9c5d-798f1c9b9e3a |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2020, 10:25:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A285C527EF73FED6954D7FA3481CEFC1 |
| SHA1: | C5DAC5ED4A9C94550AFF2D7DC0D235F1779CD131 |
| SHA256: | A78F7DB12D738DB195814A346E2B8CBE5A9CEF6D2379DBD1C6A383D075EDB6EC |
| SSDEEP: | 3072:E9iQ9ecdpA/z9ZGMy3u/OJIW9LAmAYDLUOKDBVsgnv51Jv5La2VBpThHIOi7Fpc8:0iKTpI3GMy+/OJIW9LnA2+X7J5cFpF |
MALICIOUS
Application was dropped or rewritten from another process
- RegDll.x86.exe (PID: 620)
- RegDll.x86.exe (PID: 3120)
- RegDll.x86.exe (PID: 2908)
- BANDIZIP-SETUP-STD-X86.EXE (PID: 3708)
- Bandizip.exe (PID: 3788)
- RegDll.x86.exe (PID: 3092)
- Bandizip.exe (PID: 3952)
- Bandizip.exe (PID: 3776)
- updater.exe (PID: 2104)
- RegDll.x86.exe (PID: 940)
- Bandizip.exe (PID: 2784)
- Bandizip.exe (PID: 2672)
- Bandizip.exe (PID: 1684)
Actions looks like stealing of personal data
- explorer.exe (PID: 372)
Loads dropped or rewritten executable
- RegDll.x86.exe (PID: 620)
- explorer.exe (PID: 372)
- svchost.exe (PID: 860)
- Bandizip.exe (PID: 2784)
- Bandizip.exe (PID: 2672)
- Bandizip.exe (PID: 1684)
Changes settings of System certificates
- BANDIZIP-SETUP-ONLINE.EXE (PID: 3812)
SUSPICIOUS
Reads Internet Cache Settings
- BANDIZIP-SETUP-ONLINE.EXE (PID: 3812)
- BANDIZIP-SETUP-STD-X86.EXE (PID: 3708)
- Bandizip.exe (PID: 3776)
- updater.exe (PID: 2104)
- Bandizip.exe (PID: 2784)
- Bandizip.exe (PID: 2672)
- Bandizip.exe (PID: 1684)
Changes IE settings (feature browser emulation)
- RegDll.x86.exe (PID: 3120)
- RegDll.x86.exe (PID: 2908)
Executable content was dropped or overwritten
- BANDIZIP-SETUP-ONLINE.EXE (PID: 3812)
- BANDIZIP-SETUP-STD-X86.EXE (PID: 3708)
Creates files in the program directory
- BANDIZIP-SETUP-STD-X86.EXE (PID: 3708)
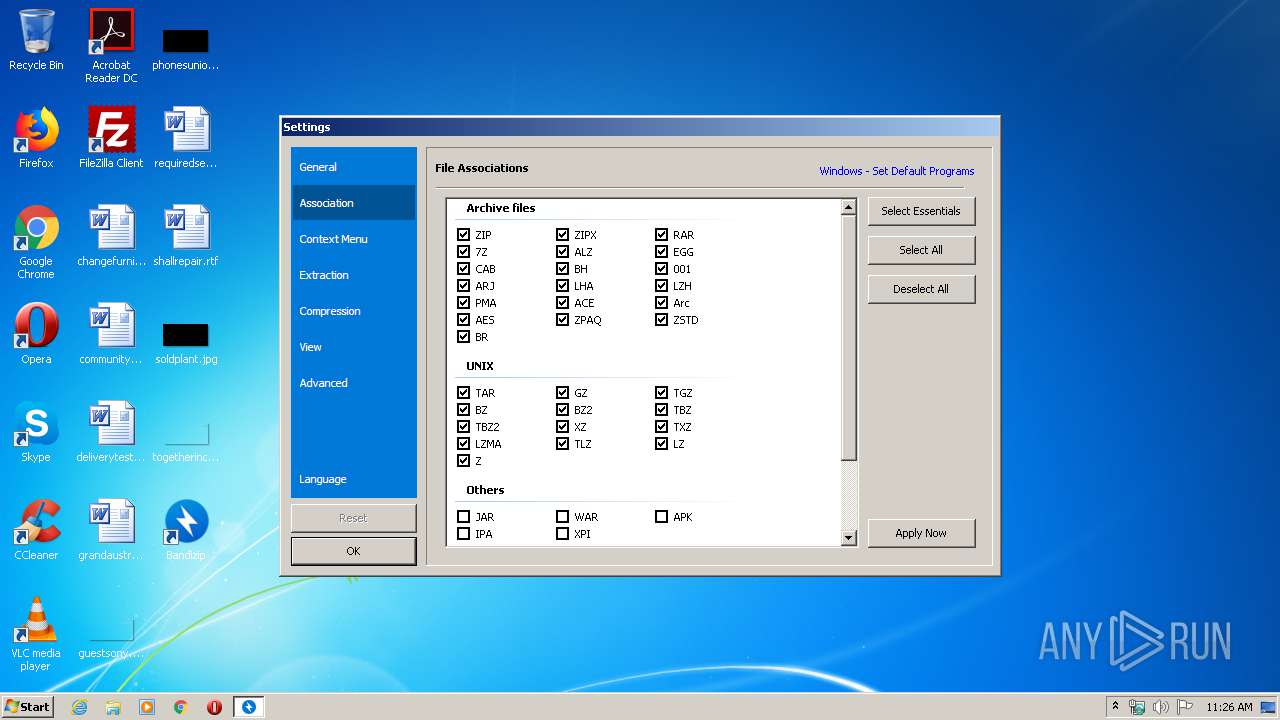
Modifies the open verb of a shell class
- BANDIZIP-SETUP-STD-X86.EXE (PID: 3708)
- Bandizip.exe (PID: 3952)
- Bandizip.exe (PID: 3788)
- Bandizip.exe (PID: 3776)
Executed via COM
- explorer.exe (PID: 604)
Creates a software uninstall entry
- BANDIZIP-SETUP-STD-X86.EXE (PID: 3708)
Creates COM task schedule object
- RegDll.x86.exe (PID: 620)
Application launched itself
- Bandizip.exe (PID: 3776)
Reads internet explorer settings
- updater.exe (PID: 2104)
Adds / modifies Windows certificates
- BANDIZIP-SETUP-ONLINE.EXE (PID: 3812)
INFO
Reads settings of System Certificates
- BANDIZIP-SETUP-ONLINE.EXE (PID: 3812)
- updater.exe (PID: 2104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:04:02 10:16:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 136192 |
| InitializedDataSize: | 109056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xebd3 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2020 08:16:27 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Apr-2020 08:16:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002120D | 0x00021400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59039 |
.rdata | 0x00023000 | 0x00008796 | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.25717 |
.data | 0x0002C000 | 0x00004CDC | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.44534 |
.rsrc | 0x00031000 | 0x0000C404 | 0x0000C600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.0173 |
.reloc | 0x0003E000 | 0x00002DEE | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.17651 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.34978 | 1117 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.98649 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.70614 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 7.93579 | 25953 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.54083 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.85764 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.54091 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
107 | 2.71858 | 104 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
109 | 2.19734 | 24 | Latin 1 / Western European | English - United States | RT_ACCELERATOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
WINTRUST.dll |
Total processes
58
Monitored processes
19
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 620 | "C:\Program Files\Bandizip\data/RegDll.x86.exe" /calldll "C:\Program Files\Bandizip\bdzshl.x86.dll" RegSvr | C:\Program Files\Bandizip\data\RegDll.x86.exe | — | BANDIZIP-SETUP-STD-X86.EXE | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | "C:\Program Files\Bandizip\data/RegDll.x86.exe" /addpath "C:\Program Files\Bandizip\" | C:\Program Files\Bandizip\data\RegDll.x86.exe | — | BANDIZIP-SETUP-STD-X86.EXE | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
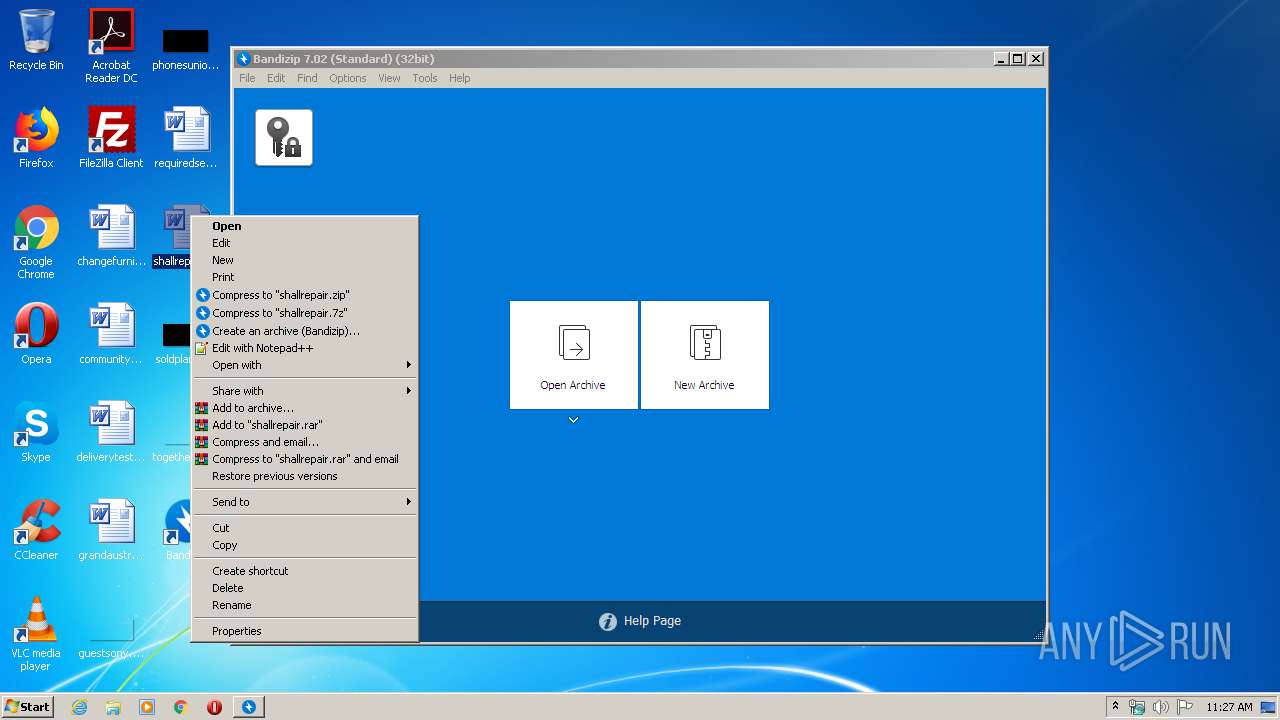
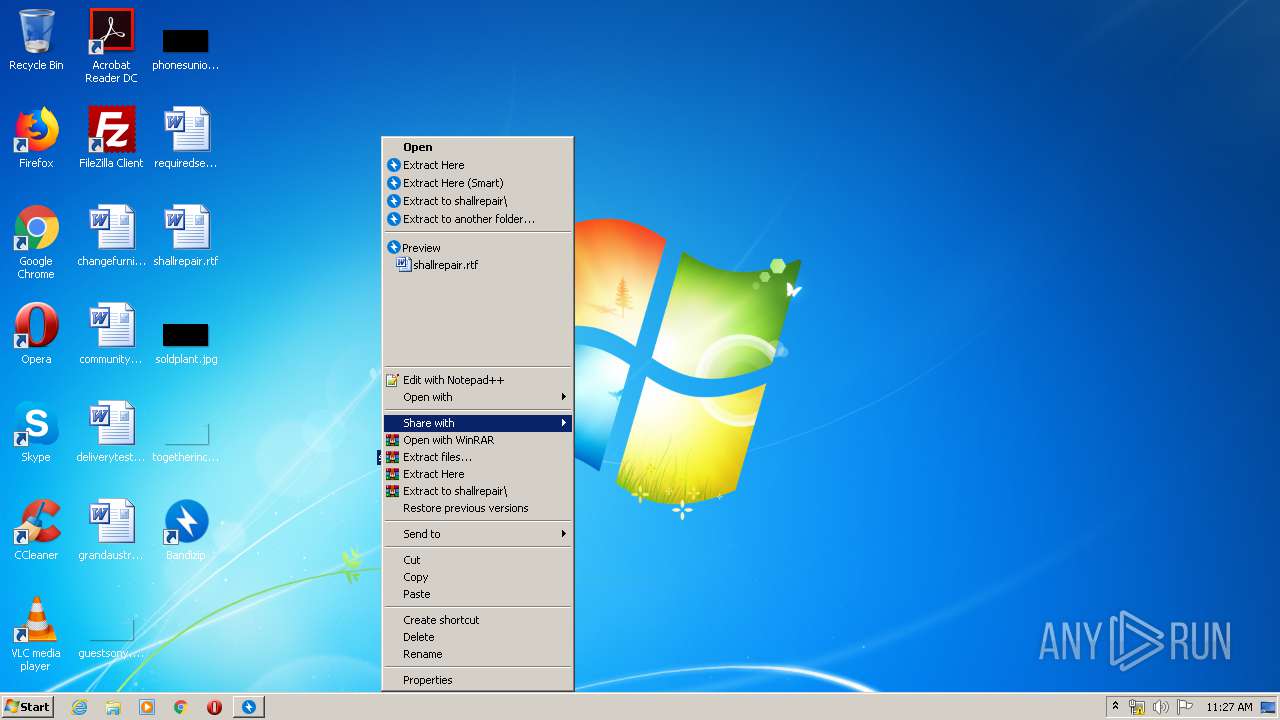
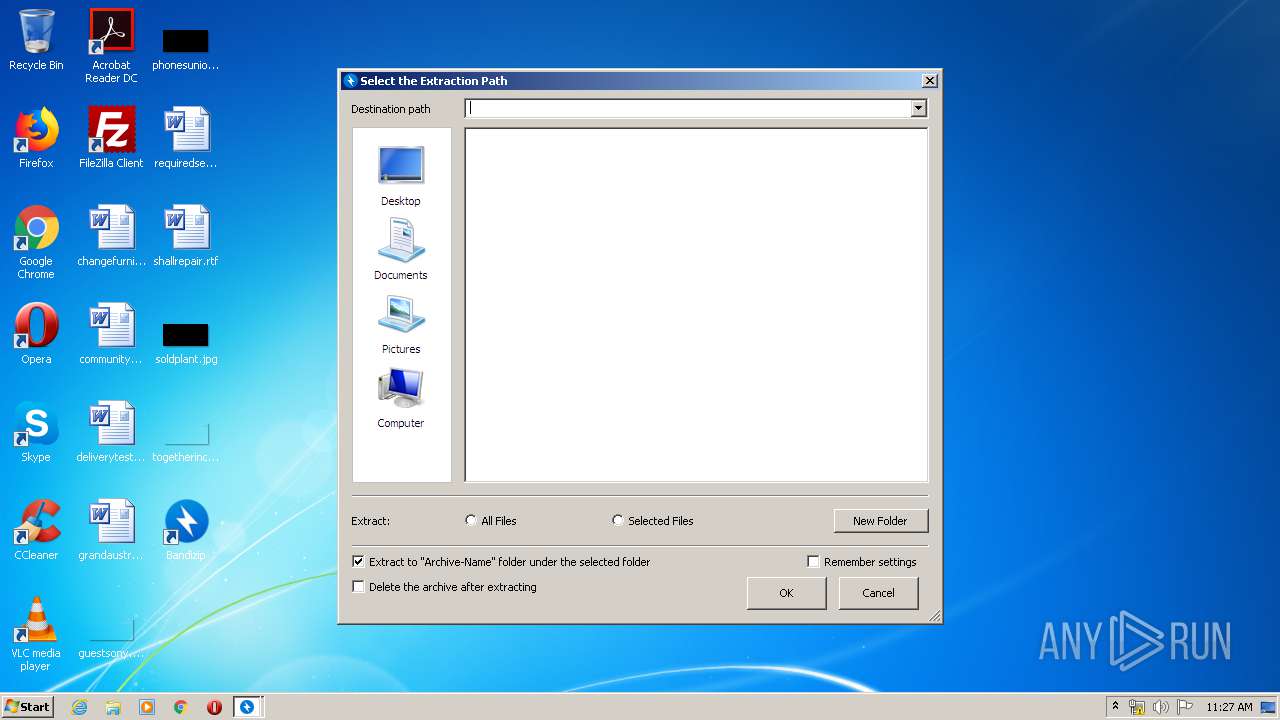
| 1684 | "C:\Program Files\Bandizip\Bandizip.exe" bx -target:dlg -o:"C:\Users\admin\Desktop\" "C:\Users\admin\Desktop\shallrepair.zip" | C:\Program Files\Bandizip\Bandizip.exe | — | explorer.exe | |||||||||||
User: admin Company: Bandisoft.com Integrity Level: MEDIUM Description: Bandizip Exit code: 0 Version: 7.2.0.1 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Bandizip\updater.exe" /nosleep | C:\Program Files\Bandizip\updater.exe | Bandizip.exe | ||||||||||||
User: admin Company: Bandisoft.com Integrity Level: MEDIUM Description: Bandizip Updater Exit code: 0 Version: 7.2.0.1 Modules
| |||||||||||||||
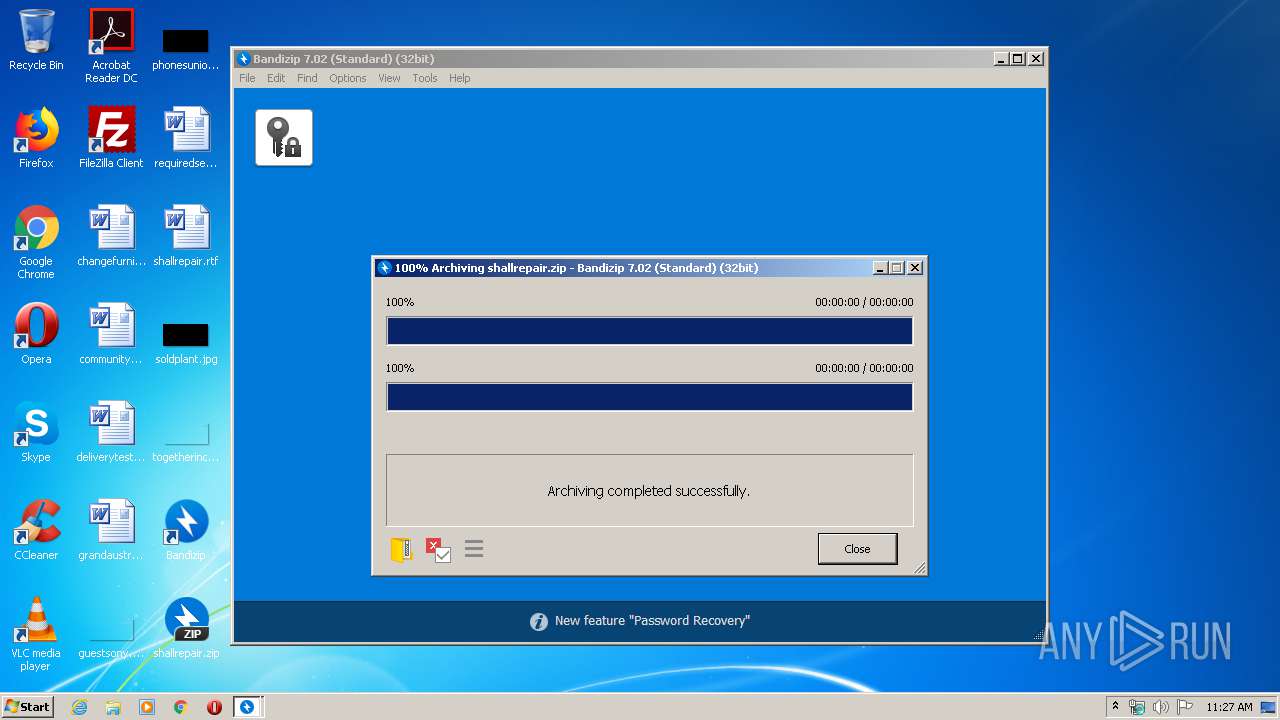
| 2672 | "C:\Program Files\Bandizip\Bandizip.exe" c "C:\Users\admin\Desktop\shallrepair.zip" "C:\Users\admin\Desktop\shallrepair.rtf" | C:\Program Files\Bandizip\Bandizip.exe | — | explorer.exe | |||||||||||
User: admin Company: Bandisoft.com Integrity Level: MEDIUM Description: Bandizip Exit code: 0 Version: 7.2.0.1 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Bandizip\Bandizip.exe" | C:\Program Files\Bandizip\Bandizip.exe | Bandizip.exe | ||||||||||||
User: admin Company: Bandisoft.com Integrity Level: MEDIUM Description: Bandizip Exit code: 0 Version: 7.2.0.1 Modules
| |||||||||||||||
| 2908 | "C:\Program Files\Bandizip\data/RegDll.x86.exe" /regieemulation Updater.exe | C:\Program Files\Bandizip\data\RegDll.x86.exe | — | BANDIZIP-SETUP-STD-X86.EXE | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
7 795
Read events
3 926
Write events
3 863
Delete events
6
Modification events
| (PID) Process: | (3812) BANDIZIP-SETUP-ONLINE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3812) BANDIZIP-SETUP-ONLINE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3812) BANDIZIP-SETUP-ONLINE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3812) BANDIZIP-SETUP-ONLINE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3812) BANDIZIP-SETUP-ONLINE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3812) BANDIZIP-SETUP-ONLINE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3812) BANDIZIP-SETUP-ONLINE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\ONAQVMVC-FRGHC-BAYVAR.RKR |
Value: 00000000000000000100000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004000000051000000A9C325000A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED01 | |||
| (PID) Process: | (3812) BANDIZIP-SETUP-ONLINE.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
11
Suspicious files
9
Text files
79
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3812 | BANDIZIP-SETUP-ONLINE.EXE | C:\Users\admin\AppData\Local\Temp\Cab4F2D.tmp | — | |
MD5:— | SHA256:— | |||
| 3812 | BANDIZIP-SETUP-ONLINE.EXE | C:\Users\admin\AppData\Local\Temp\Tar4F2E.tmp | — | |
MD5:— | SHA256:— | |||
| 3708 | BANDIZIP-SETUP-STD-X86.EXE | C:\Users\admin\AppData\Local\Temp\Cab60A2.tmp | — | |
MD5:— | SHA256:— | |||
| 3708 | BANDIZIP-SETUP-STD-X86.EXE | C:\Users\admin\AppData\Local\Temp\Tar60A3.tmp | — | |
MD5:— | SHA256:— | |||
| 860 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:9D8FC6D7D4BE05ECA3CFDA3A4290AD3D | SHA256:A3000F6B5ECDEA78C06CA08B65791B1DFD94A6F41A0A734F9817DAE59D098D69 | |||
| 3812 | BANDIZIP-SETUP-ONLINE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5457A8CE4B2A7499F8299A013B6E1C7C_CBB16B7A61CE4E298043181730D3CE9B | der | |
MD5:A277DD5FEE6DE56D8A374008AF5A4AF5 | SHA256:1D0CE9DEEBE8C3866F3E3B5FE4D90B00ED509B04ADE79F2DE620B6BCC79C8889 | |||
| 3812 | BANDIZIP-SETUP-ONLINE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\848460ED45F3AE6F6E6CD248AB519FED | binary | |
MD5:C104E8900E1A6170536C0CE6B0D5506A | SHA256:1E84C1B95E580525D6885167D70A59B5CD07714C6B9E5645236A160BF50E7749 | |||
| 3812 | BANDIZIP-SETUP-ONLINE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:2B0A46653E020FD6D98BDC8E5D67C2DA | SHA256:8F89022F69CA85FFBC36A3A23BC3F82DC654037E04013492952096344C0766A1 | |||
| 3812 | BANDIZIP-SETUP-ONLINE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\848460ED45F3AE6F6E6CD248AB519FED | der | |
MD5:5D73626C0CFA27BF4B6B0E9C5F9B3A26 | SHA256:E43008DBB6A36BD9719D80B36090BDD35D39D0400A0CF95C36FA90368F3B3287 | |||
| 3708 | BANDIZIP-SETUP-STD-X86.EXE | C:\Program Files\Bandizip\ark.x86.lgpl.dll | executable | |
MD5:FFC16807E001D64FDDF794426B6DA490 | SHA256:8D27236B023A7E39FCA7814193E4BCF04A1212B8746964D60A9A67FA1AFF11B0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
13
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3812 | BANDIZIP-SETUP-ONLINE.EXE | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3812 | BANDIZIP-SETUP-ONLINE.EXE | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
3812 | BANDIZIP-SETUP-ONLINE.EXE | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQDzHc2p4PYe%2BXbRnPTZ8TTX | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3812 | BANDIZIP-SETUP-ONLINE.EXE | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
3812 | BANDIZIP-SETUP-ONLINE.EXE | 52.78.169.250:443 | ver.bandisoft.com | Amazon.com, Inc. | KR | suspicious |
3812 | BANDIZIP-SETUP-ONLINE.EXE | 52.58.129.144:443 | dl.bandisoft.com | Amazon.com, Inc. | DE | unknown |
3812 | BANDIZIP-SETUP-ONLINE.EXE | 118.33.18.151:443 | kt-dl.bandisoft.com | Korea Telecom | KR | unknown |
3812 | BANDIZIP-SETUP-ONLINE.EXE | 54.39.129.170:443 | ca-dl.bandisoft.com | OVH SAS | FR | suspicious |
3708 | BANDIZIP-SETUP-STD-X86.EXE | 52.78.169.250:443 | ver.bandisoft.com | Amazon.com, Inc. | KR | suspicious |
2104 | updater.exe | 52.78.169.250:443 | ver.bandisoft.com | Amazon.com, Inc. | KR | suspicious |
2104 | updater.exe | 216.58.206.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2784 | Bandizip.exe | 52.58.129.144:443 | dl.bandisoft.com | Amazon.com, Inc. | DE | unknown |
2784 | Bandizip.exe | 52.78.169.250:443 | ver.bandisoft.com | Amazon.com, Inc. | KR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ver.bandisoft.com |
| suspicious |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
dl.bandisoft.com |
| suspicious |
kt-dl.bandisoft.com |
| unknown |
ca-dl.bandisoft.com |
| suspicious |
ver.bandi.so |
| suspicious |
log.bandi.so |
| suspicious |
ana.bandi.so |
| suspicious |
www.googletagmanager.com |
| whitelisted |