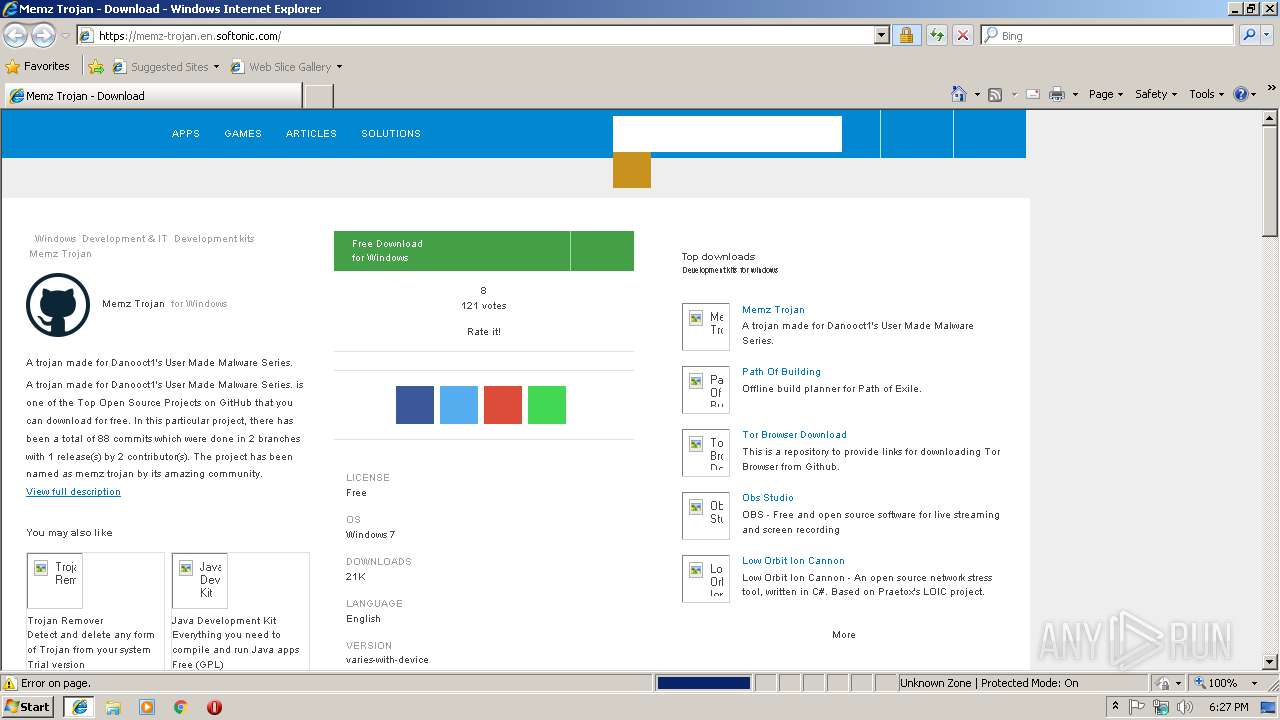
| URL: | https://memz-trojan.en.softonic.com/ |
| Full analysis: | https://app.any.run/tasks/b3656f61-c848-4f9e-a845-61d9936d6534 |
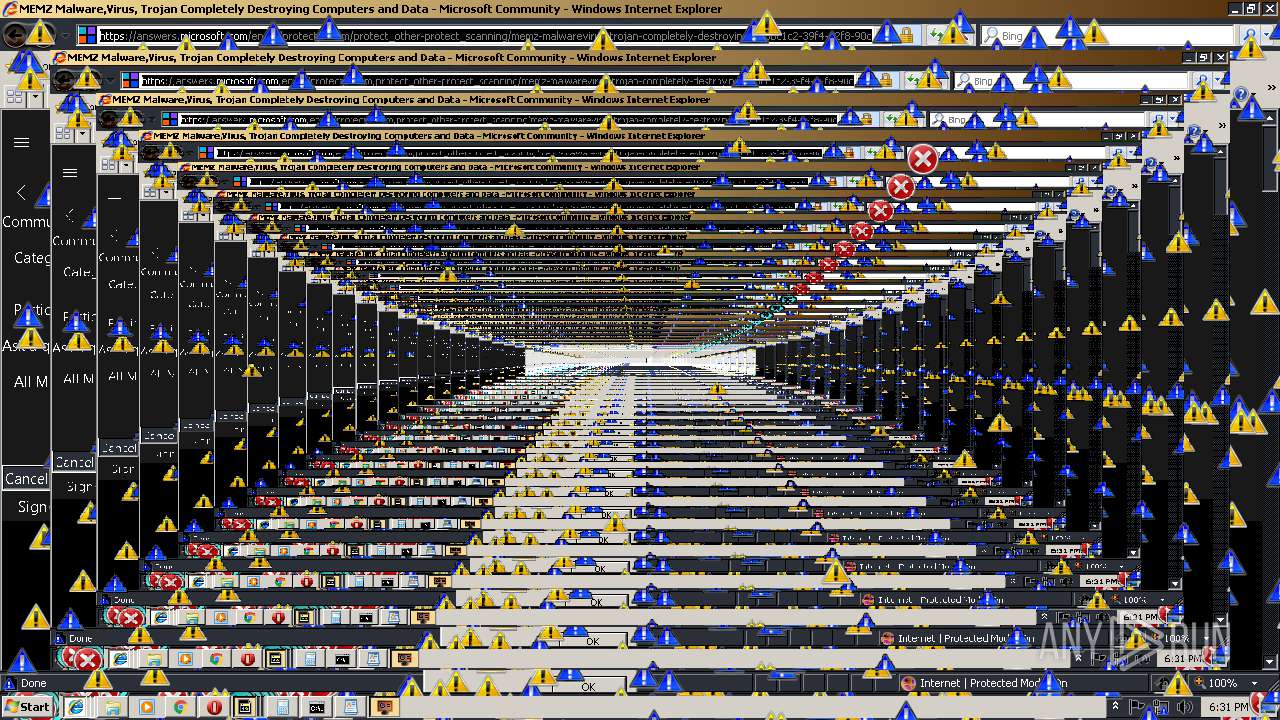
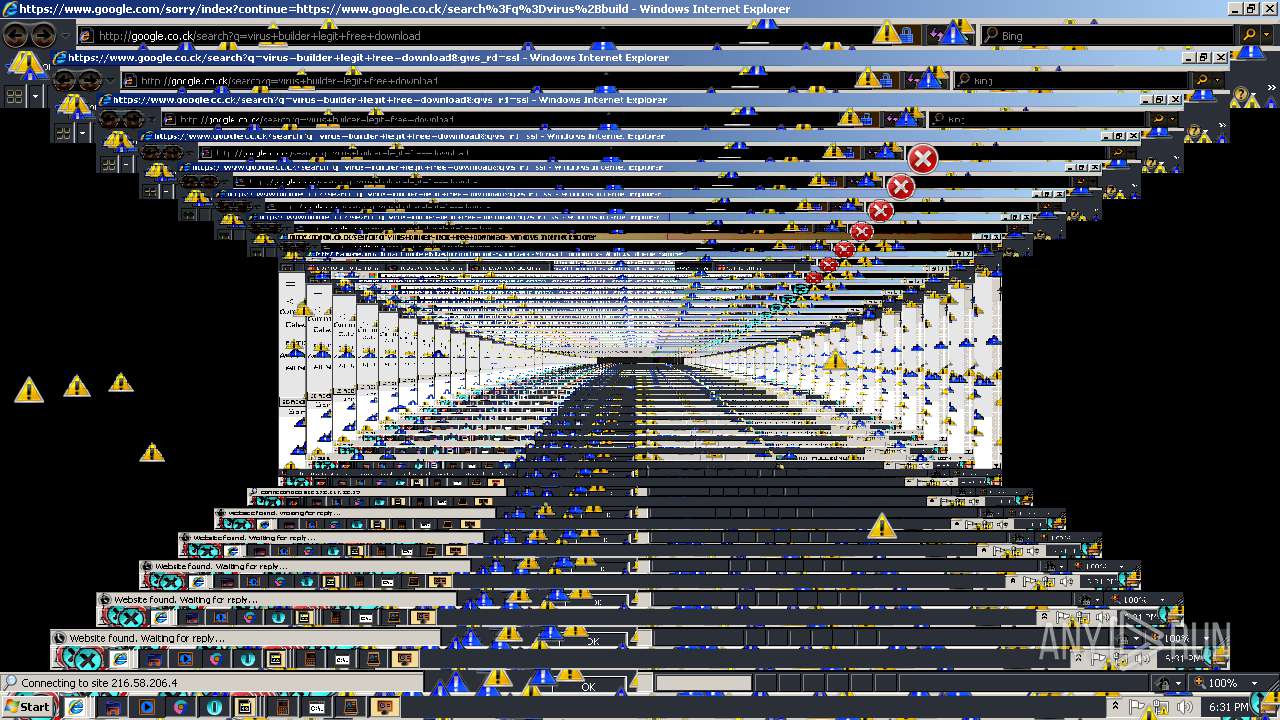
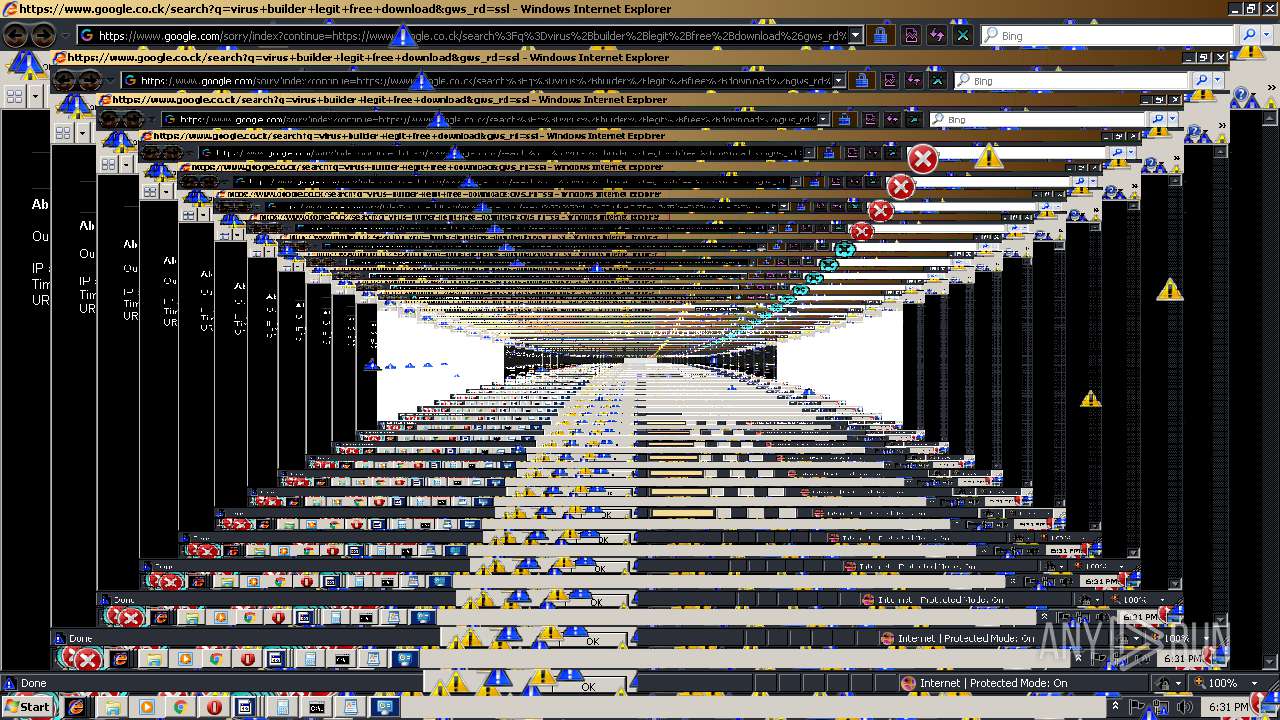
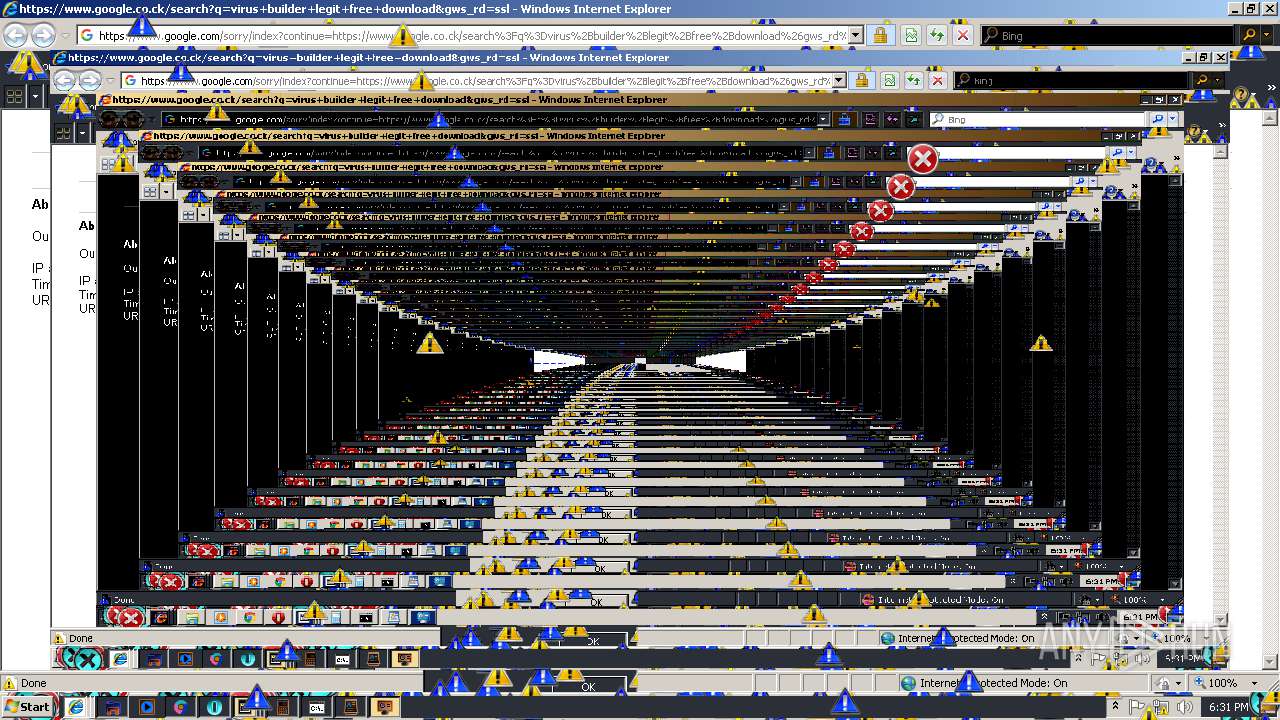
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2019, 18:27:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A05A75CBA0F744395ACCFA2E333C42E3 |
| SHA1: | C868C3BC51AD1D4870AF4F99ADD094AE5510A678 |
| SHA256: | A75FDA23DD7CE9A0B99CFB71FFF50FA03286337324BD9C600DDF2AD271AF147C |
| SSDEEP: | 3:N8VtIIHLGK3:2VqALGK3 |
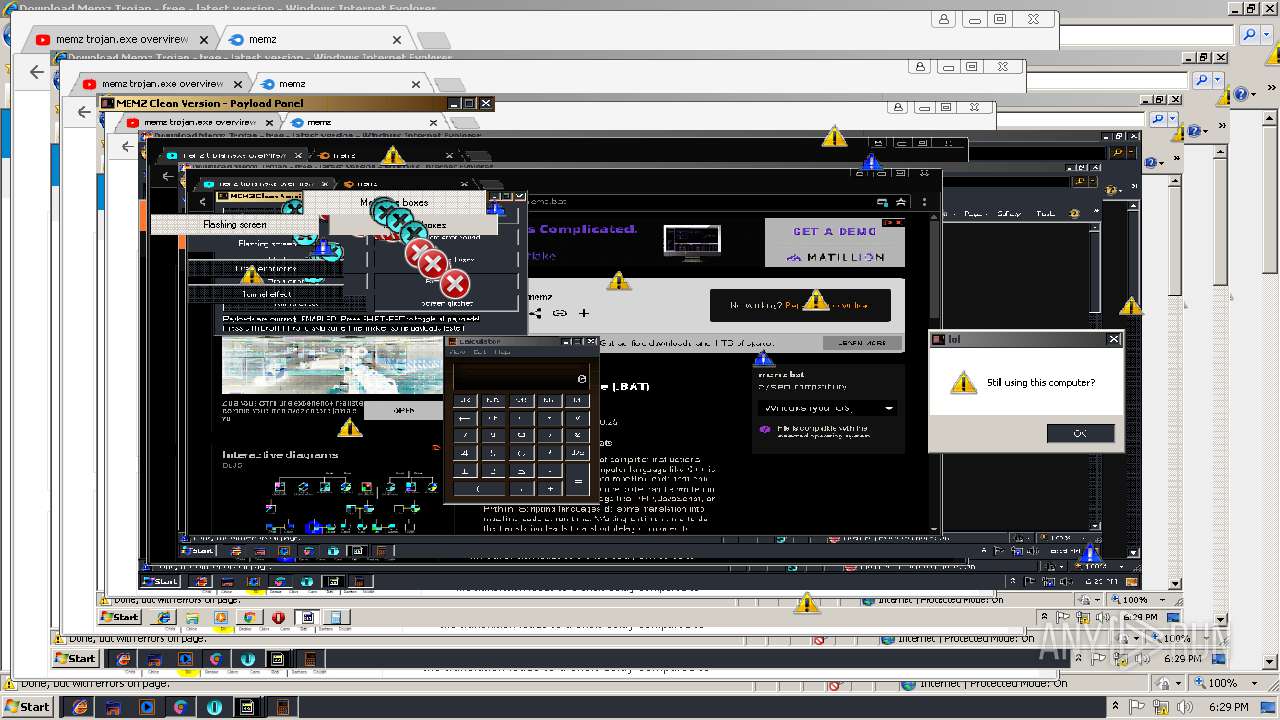
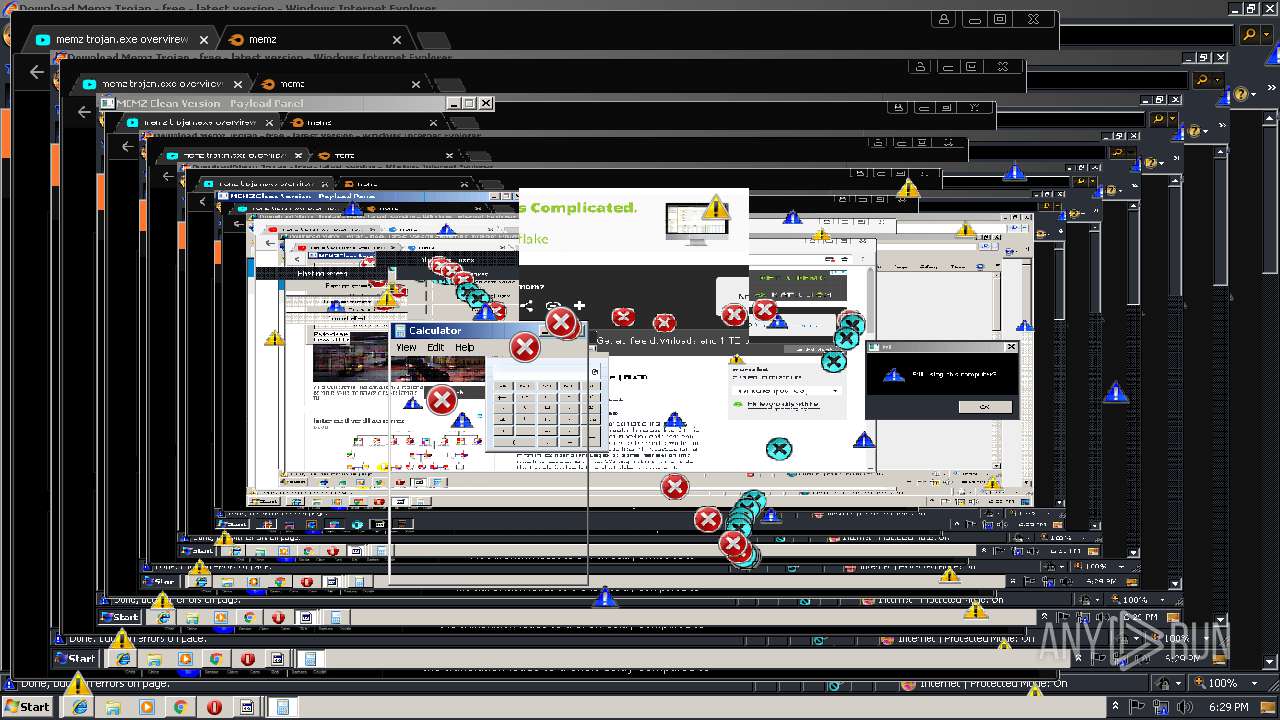
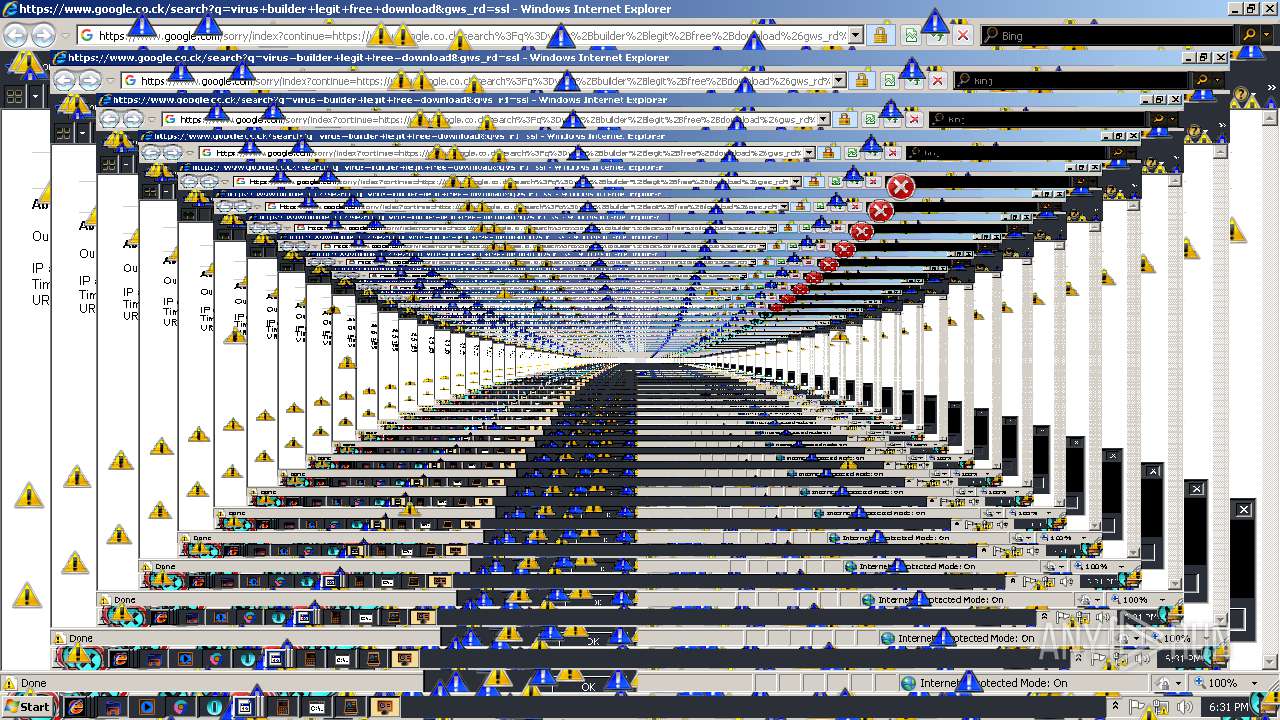
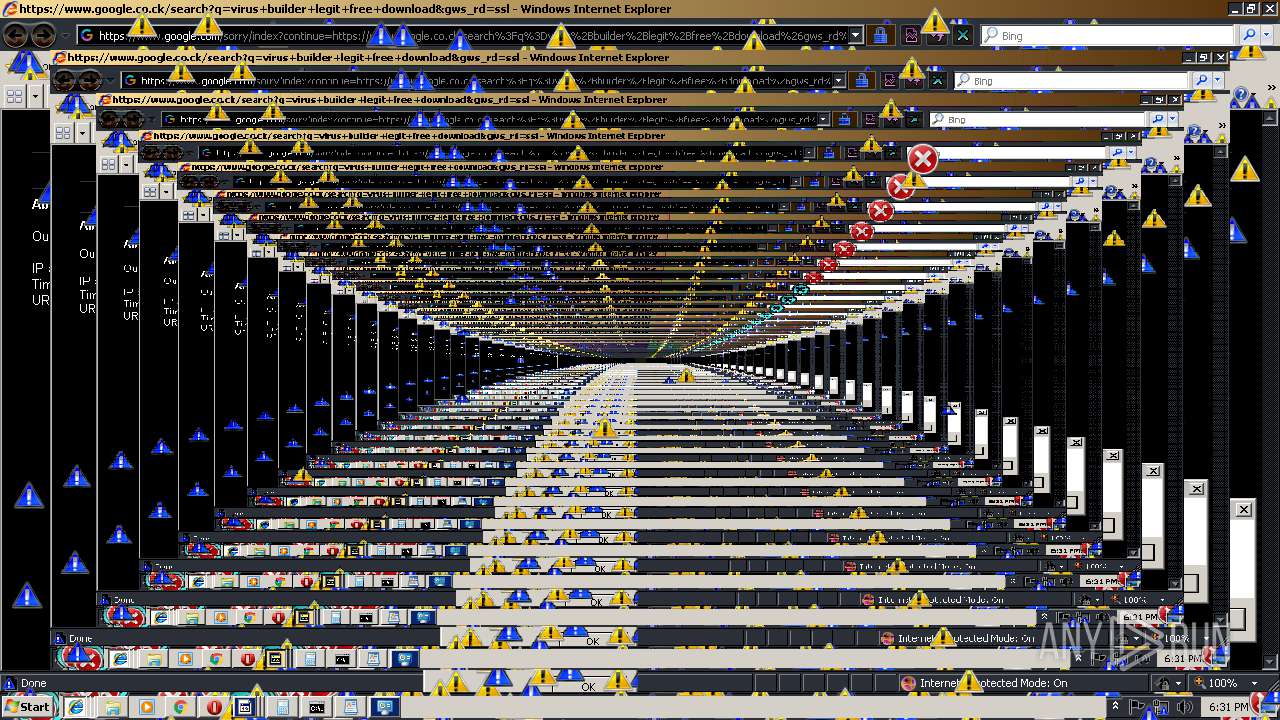
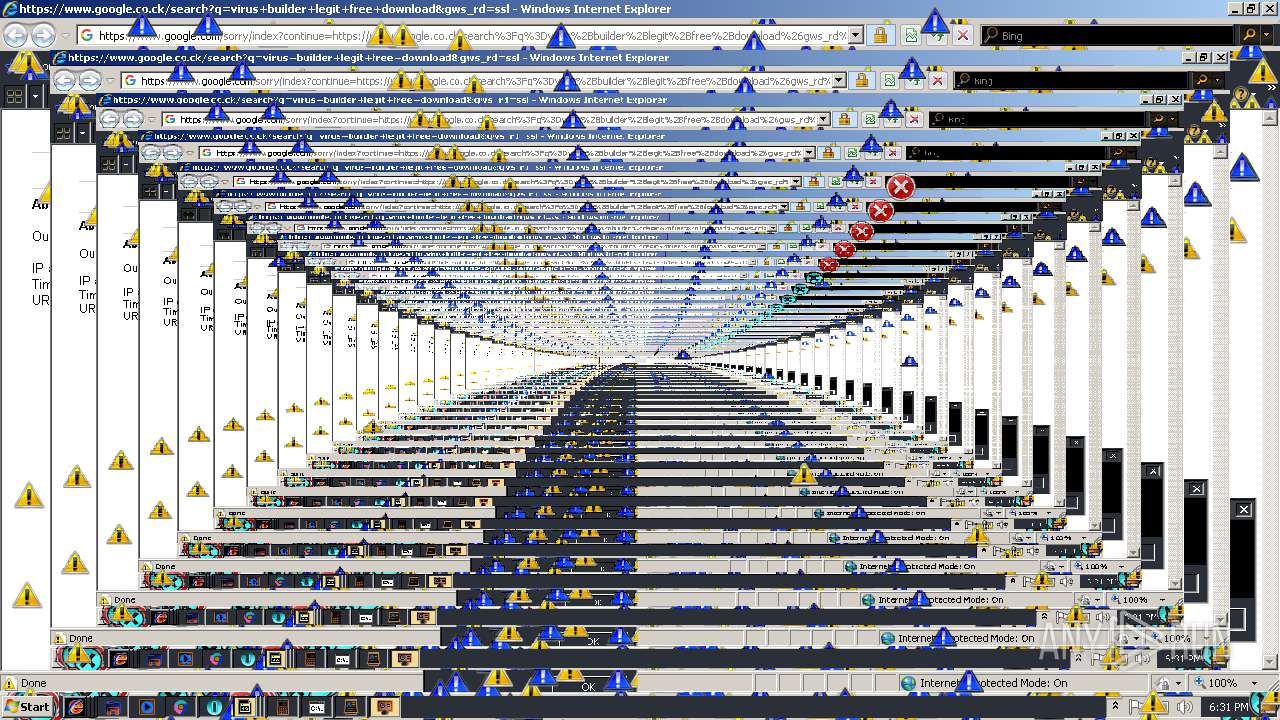
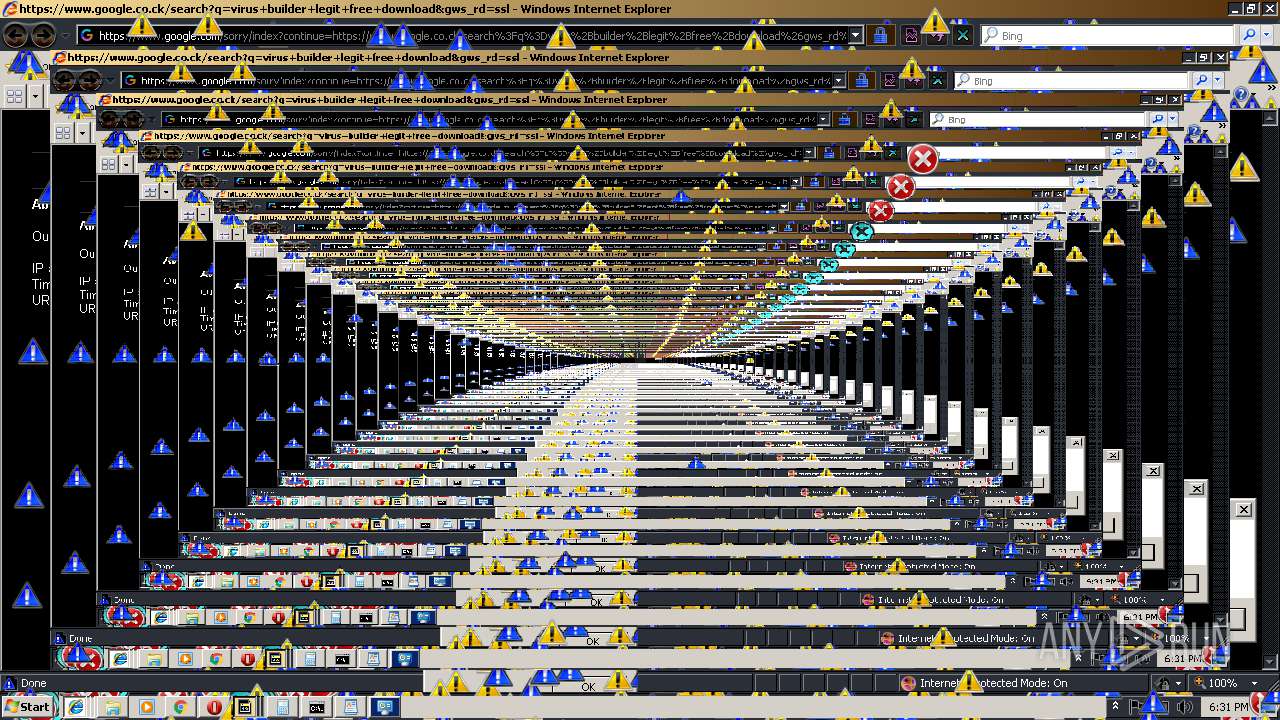
MALICIOUS
Application was dropped or rewritten from another process
- MEMZ.exe (PID: 3820)
Runs app for hidden code execution
- MEMZ.exe (PID: 3820)
SUSPICIOUS
Creates files in the user directory
- cscript.exe (PID: 3256)
- MEMZ.exe (PID: 3820)
Executes scripts
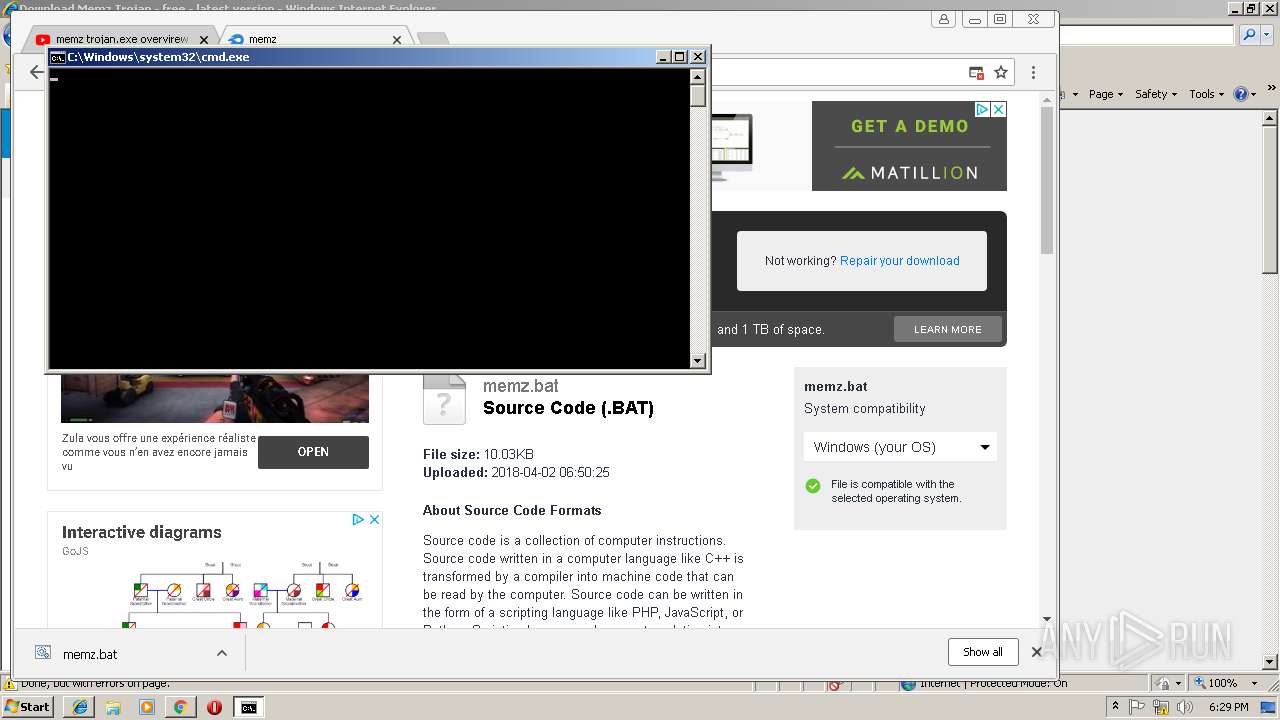
- cmd.exe (PID: 2560)
Executable content was dropped or overwritten
- cscript.exe (PID: 3256)
Starts CMD.EXE for commands execution
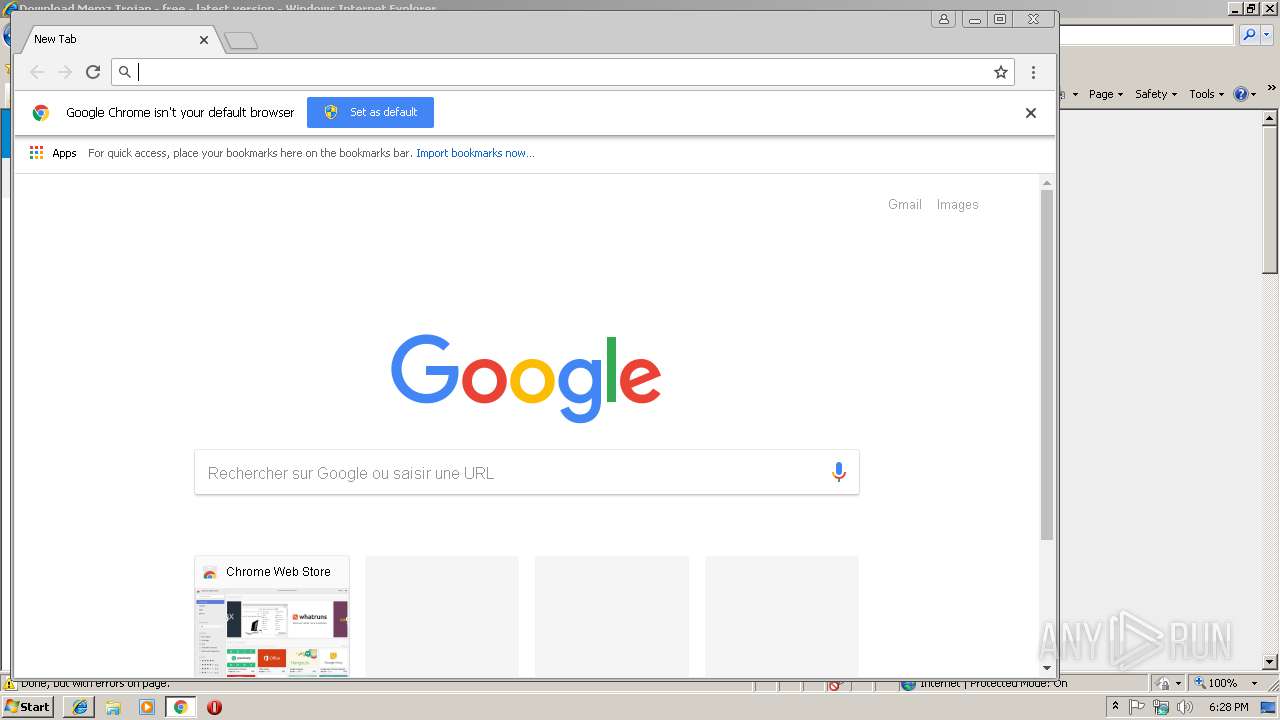
- chrome.exe (PID: 1156)
- MEMZ.exe (PID: 3820)
INFO
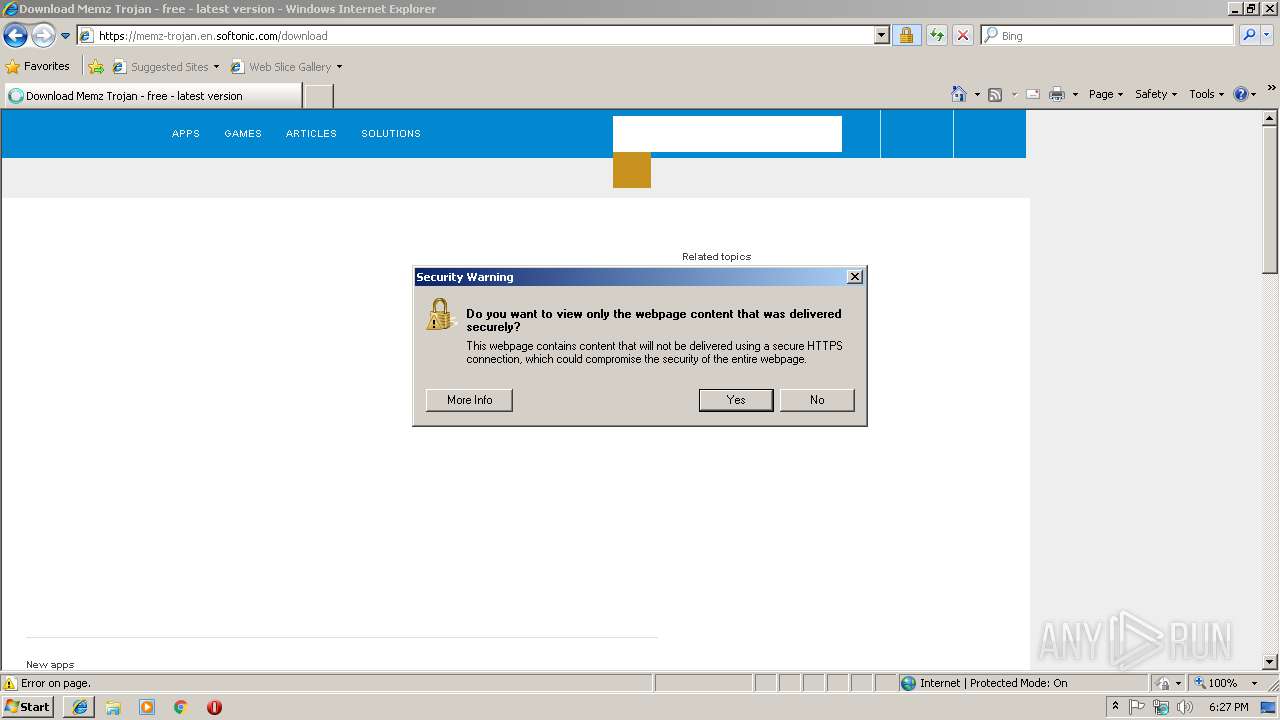
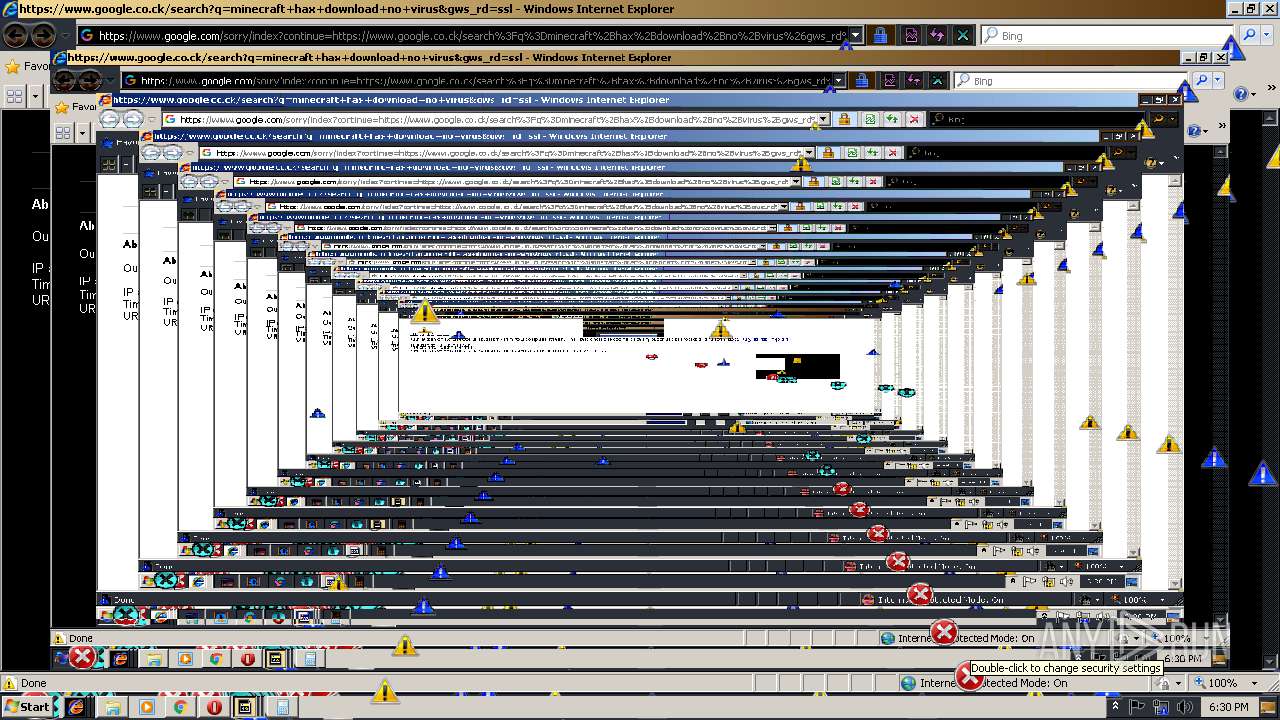
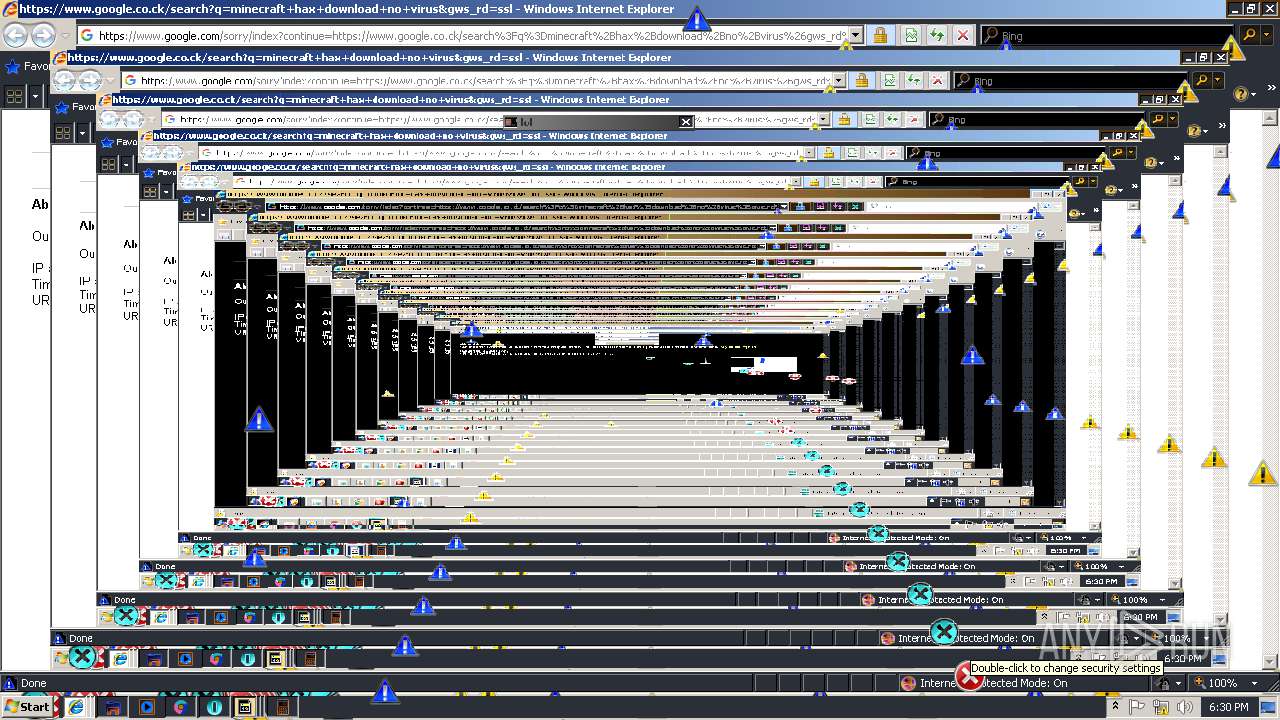
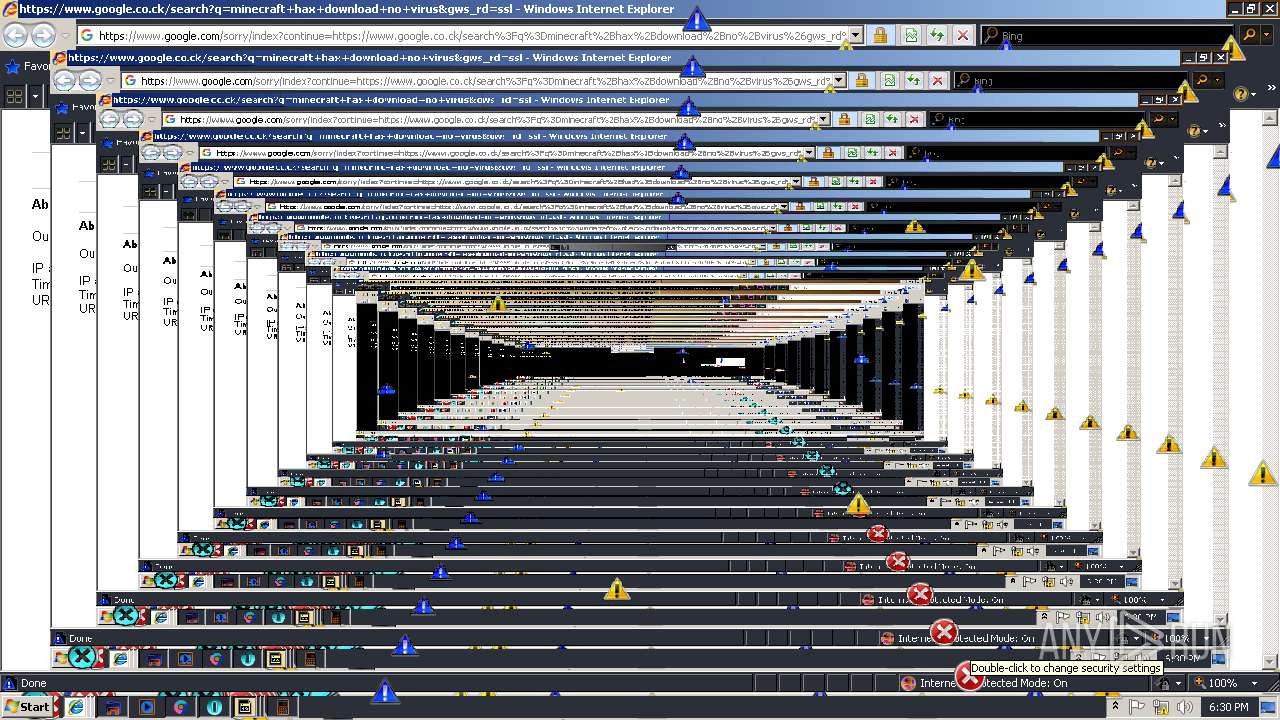
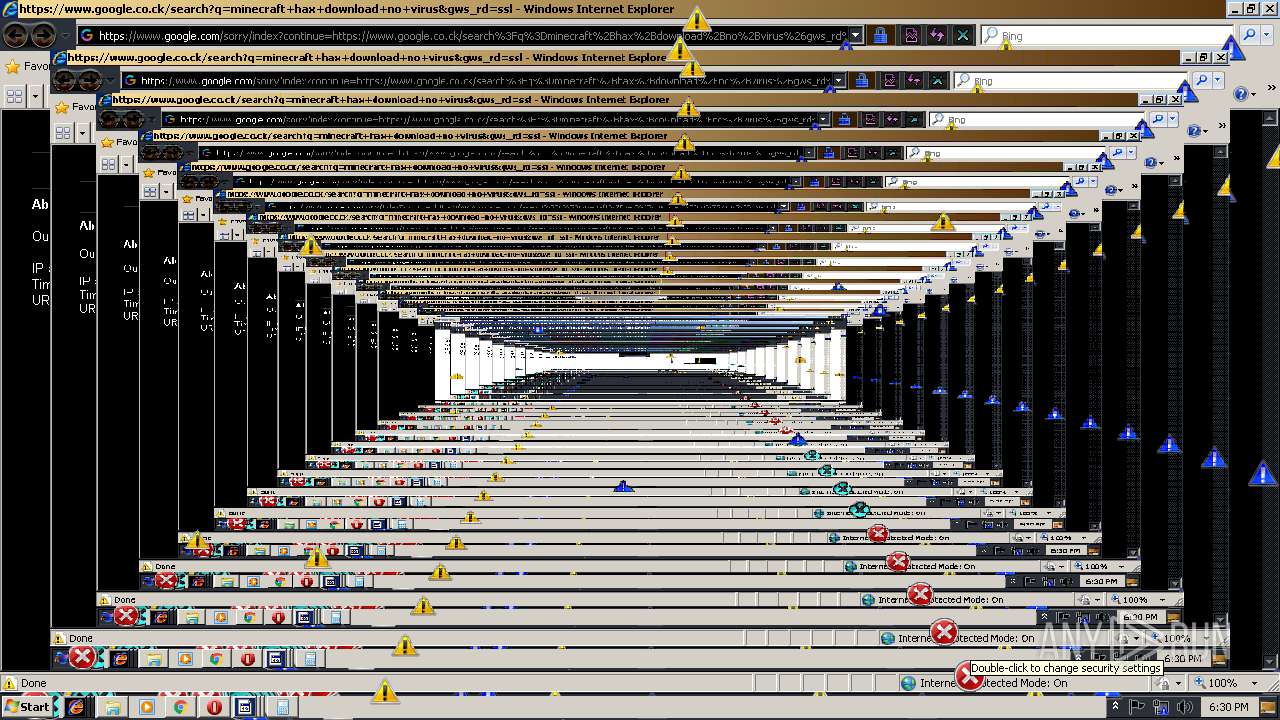
Reads Internet Cache Settings
- iexplore.exe (PID: 3432)
- chrome.exe (PID: 1156)
- iexplore.exe (PID: 2344)
- iexplore.exe (PID: 3864)
- iexplore.exe (PID: 1320)
- iexplore.exe (PID: 4032)
Changes settings of System certificates
- chrome.exe (PID: 1156)
- iexplore.exe (PID: 3248)
Reads internet explorer settings
- iexplore.exe (PID: 3432)
- iexplore.exe (PID: 2344)
- iexplore.exe (PID: 3864)
- iexplore.exe (PID: 4032)
- iexplore.exe (PID: 1320)
Changes internet zones settings
- iexplore.exe (PID: 3248)
Creates files in the user directory
- iexplore.exe (PID: 3432)
- iexplore.exe (PID: 2344)
- opera.exe (PID: 3932)
- iexplore.exe (PID: 3864)
- iexplore.exe (PID: 1320)
Application launched itself
- chrome.exe (PID: 1156)
- iexplore.exe (PID: 3248)
Reads settings of System Certificates
- chrome.exe (PID: 1156)
- iexplore.exe (PID: 3248)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
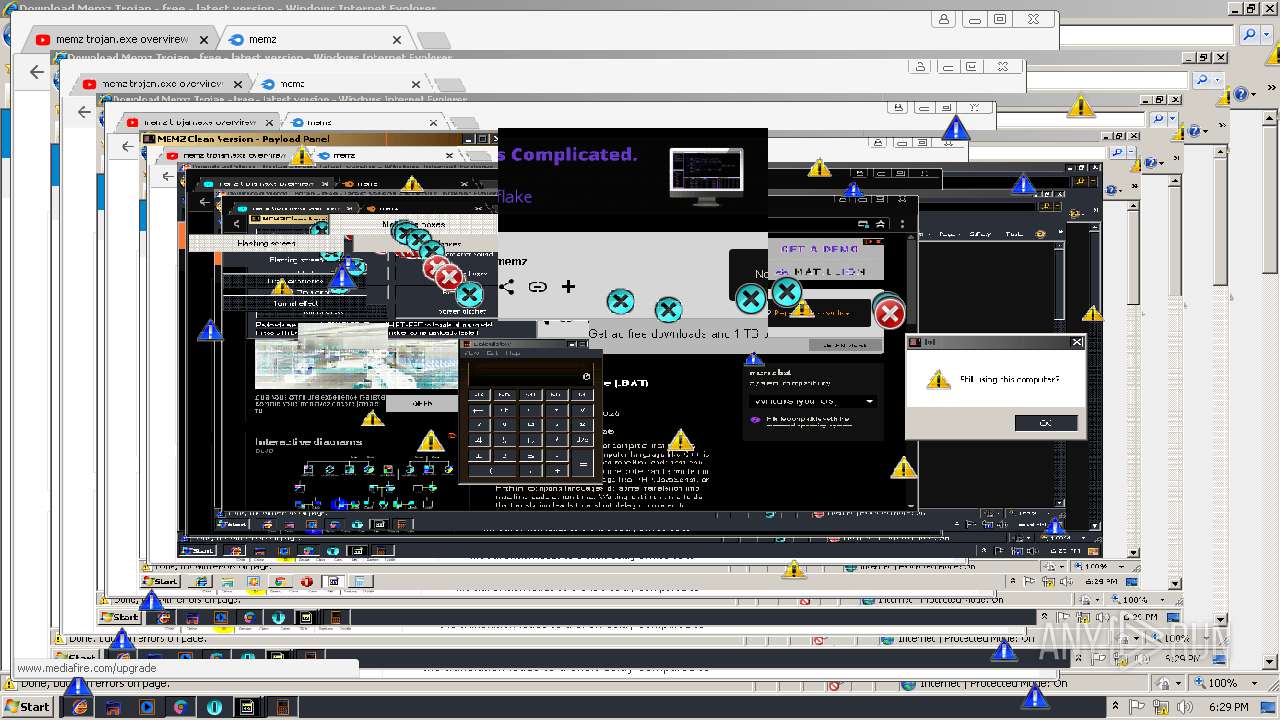
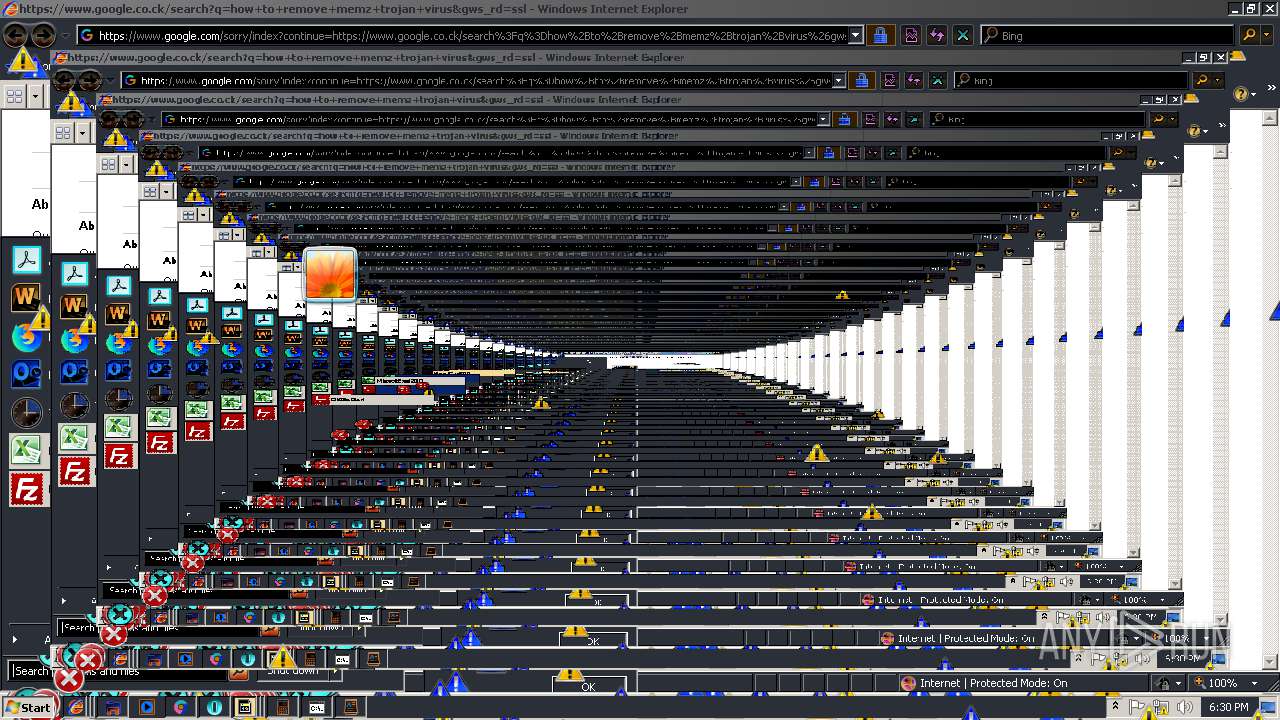
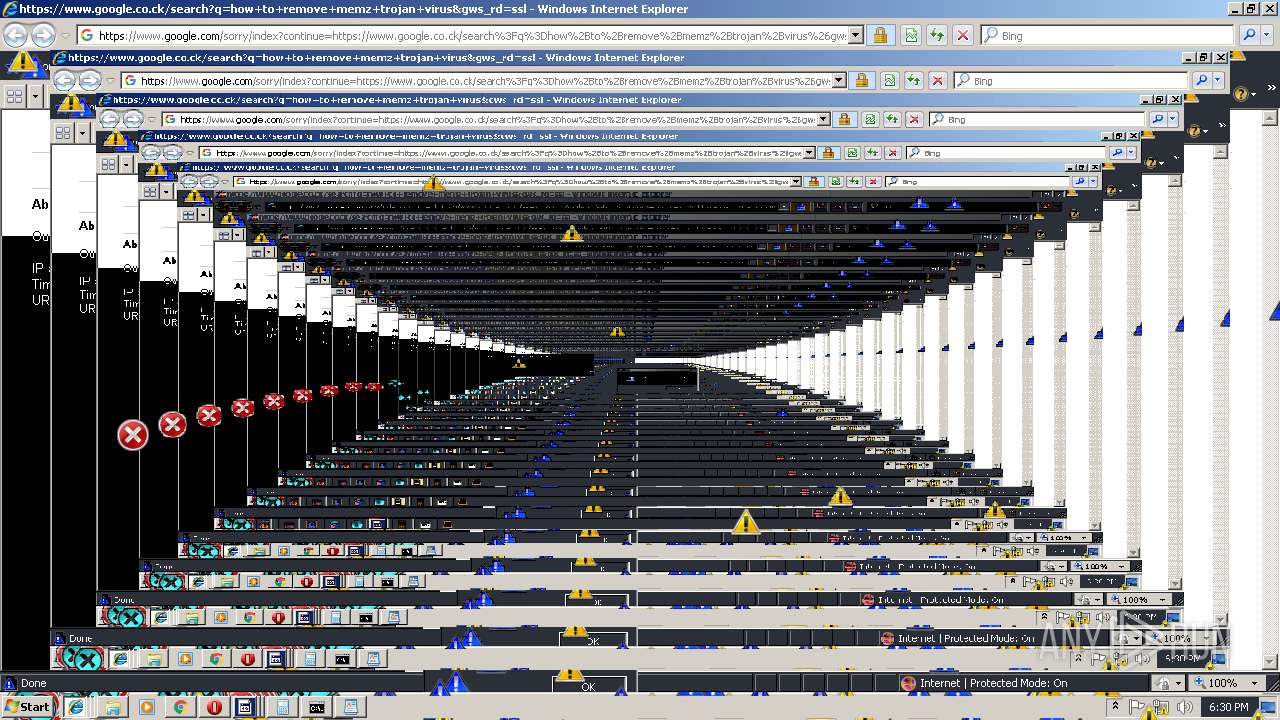
Total processes
69
Monitored processes
35
Malicious processes
0
Suspicious processes
3
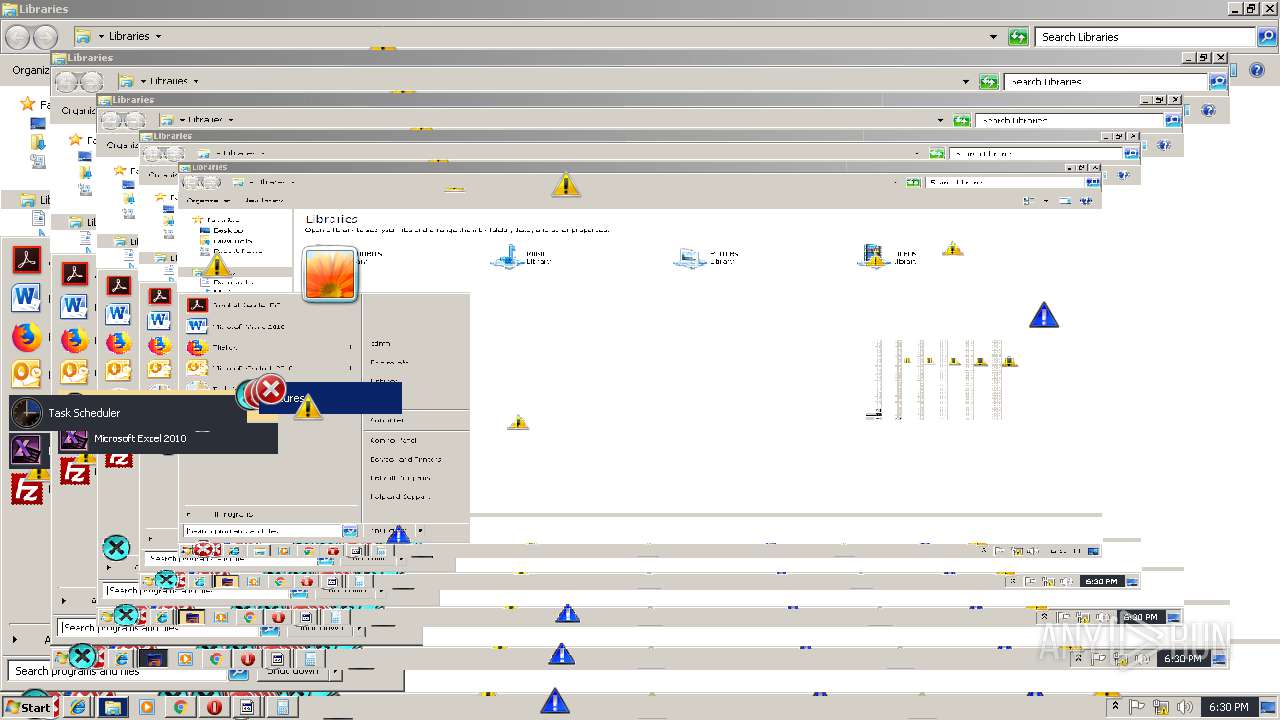
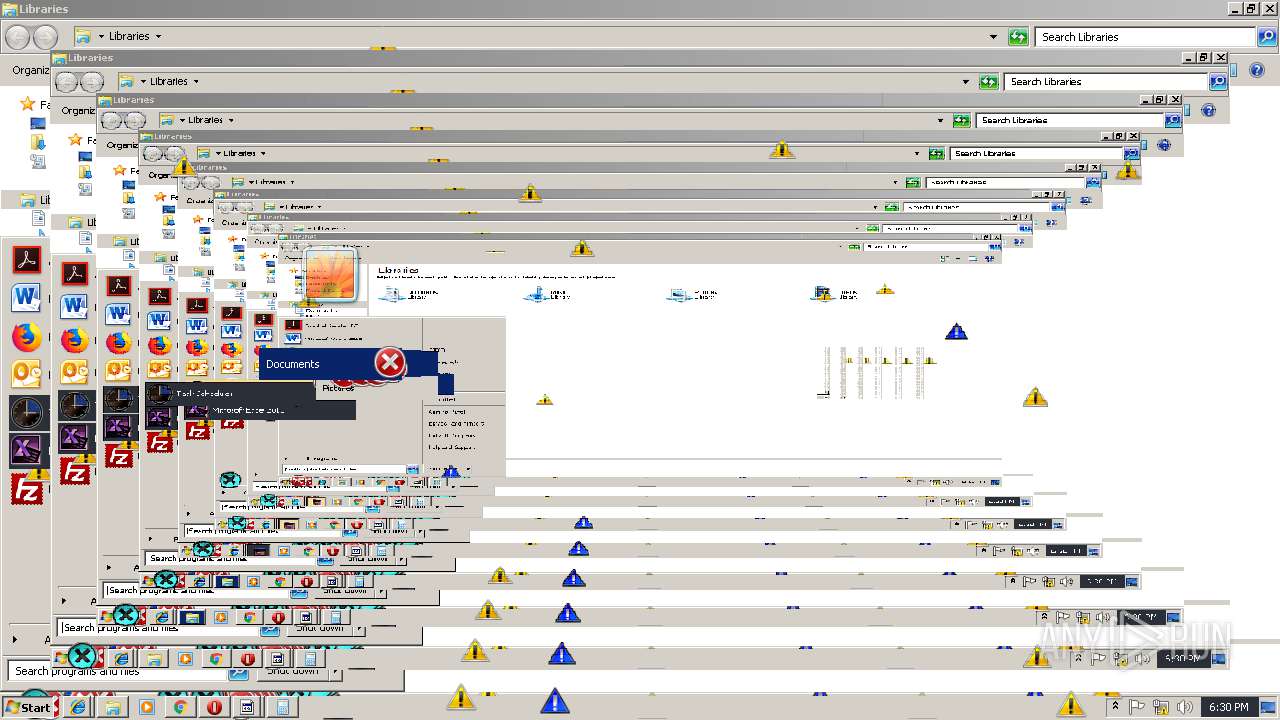
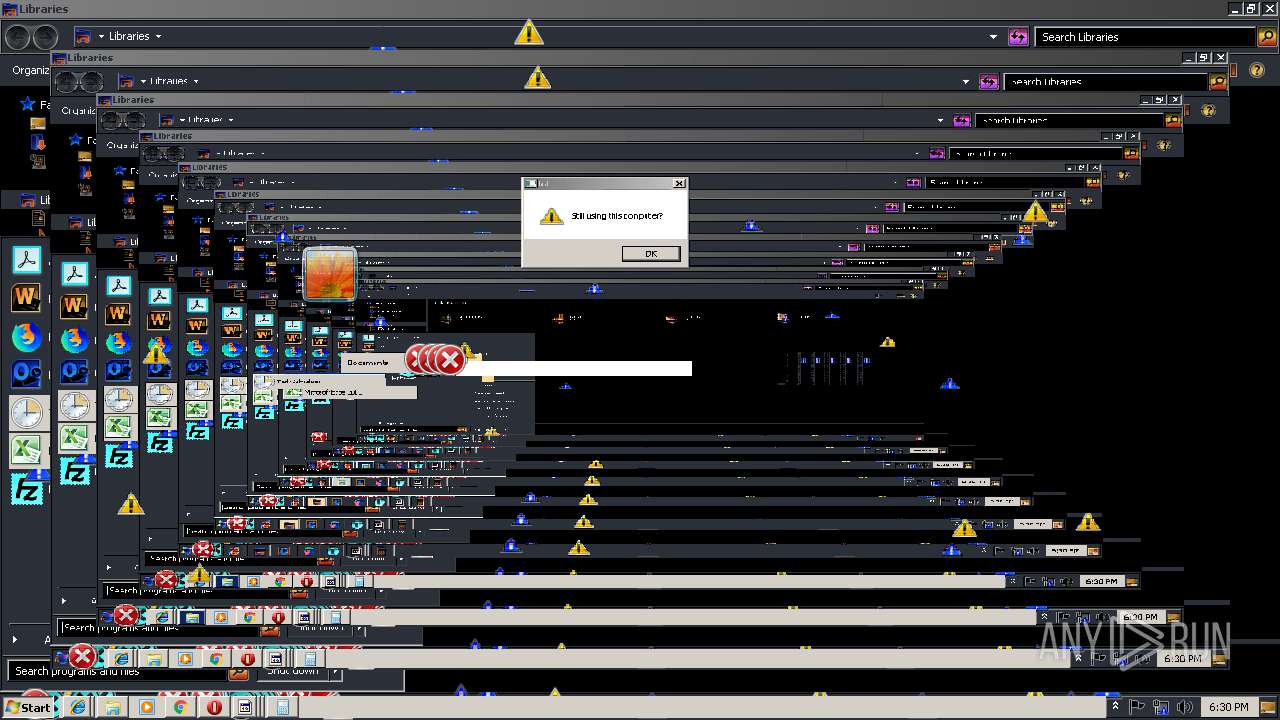
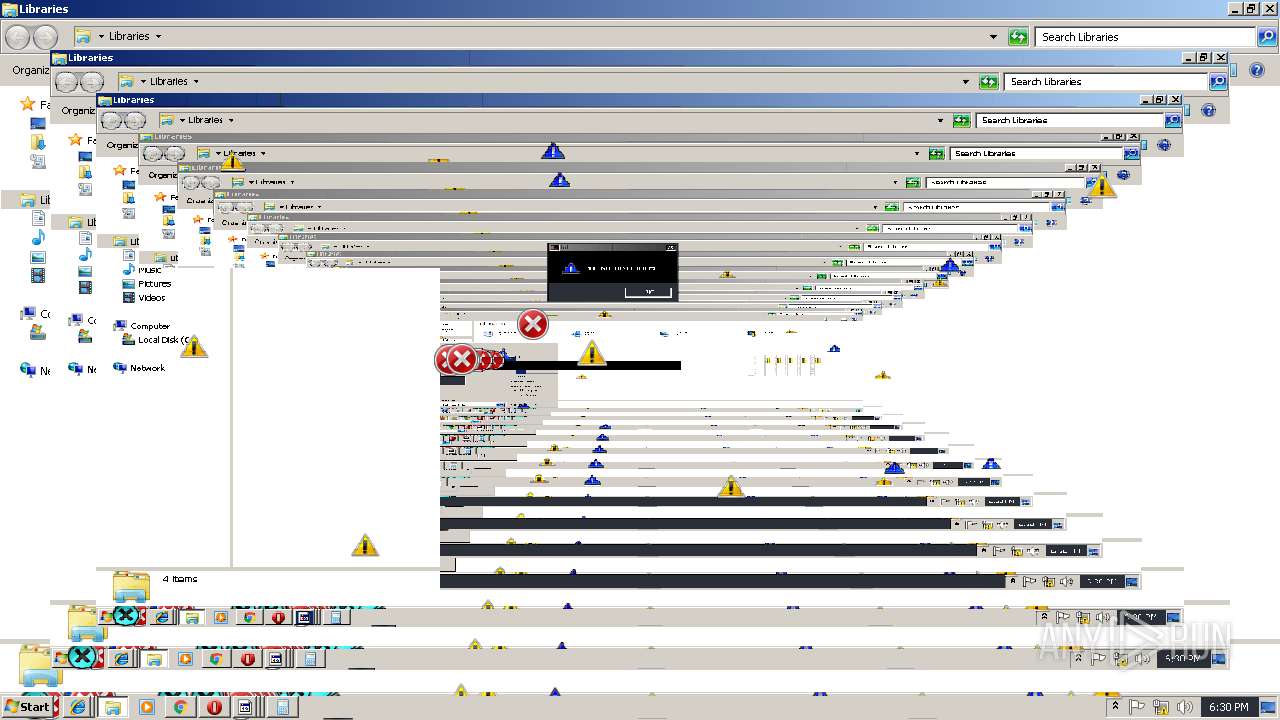
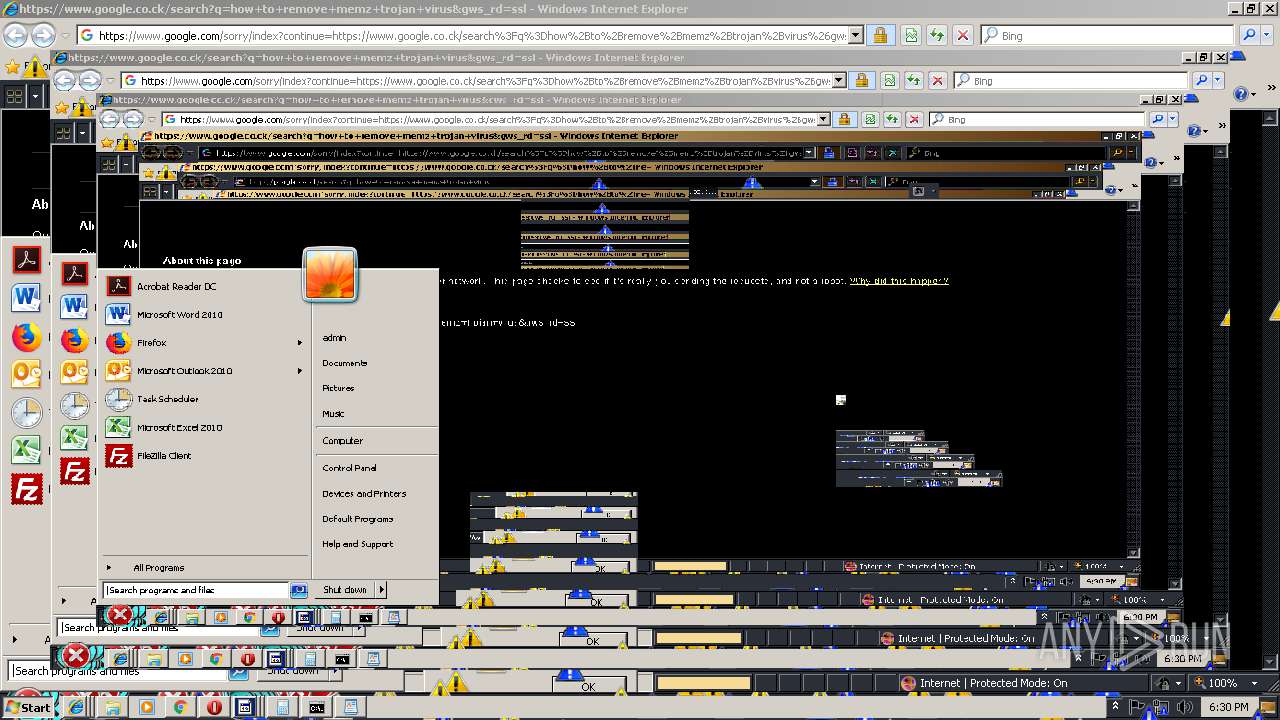
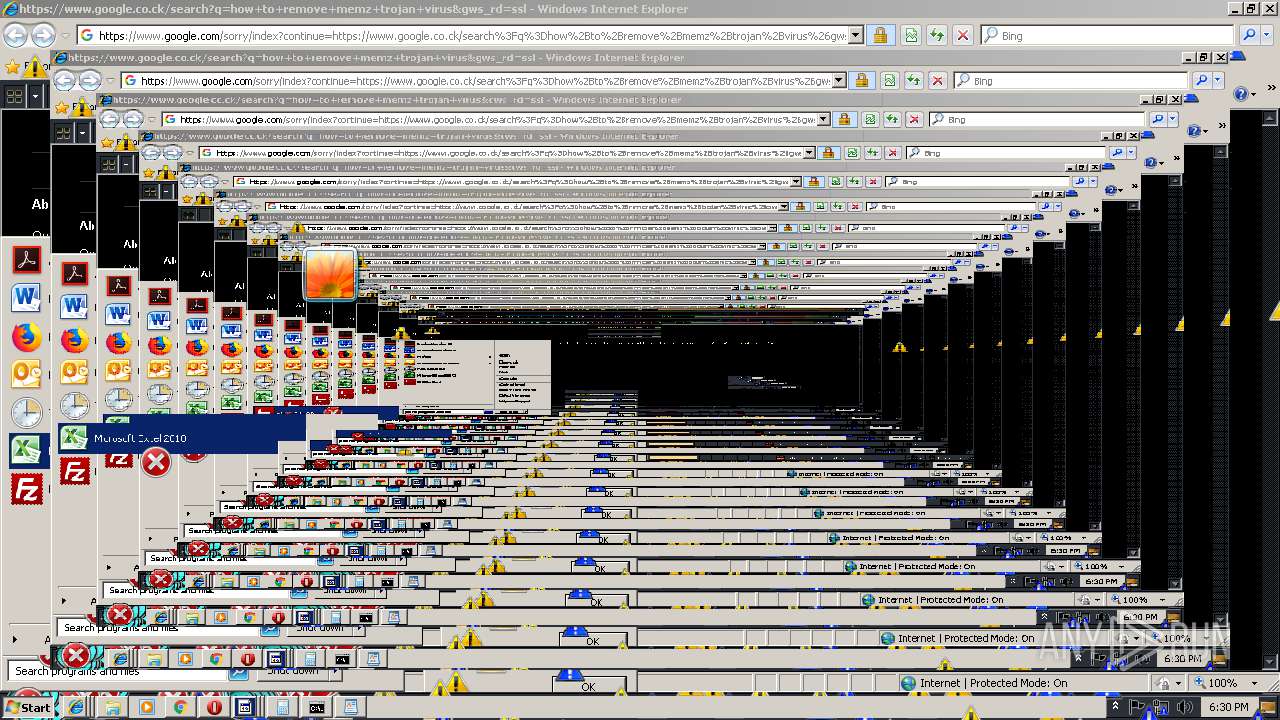
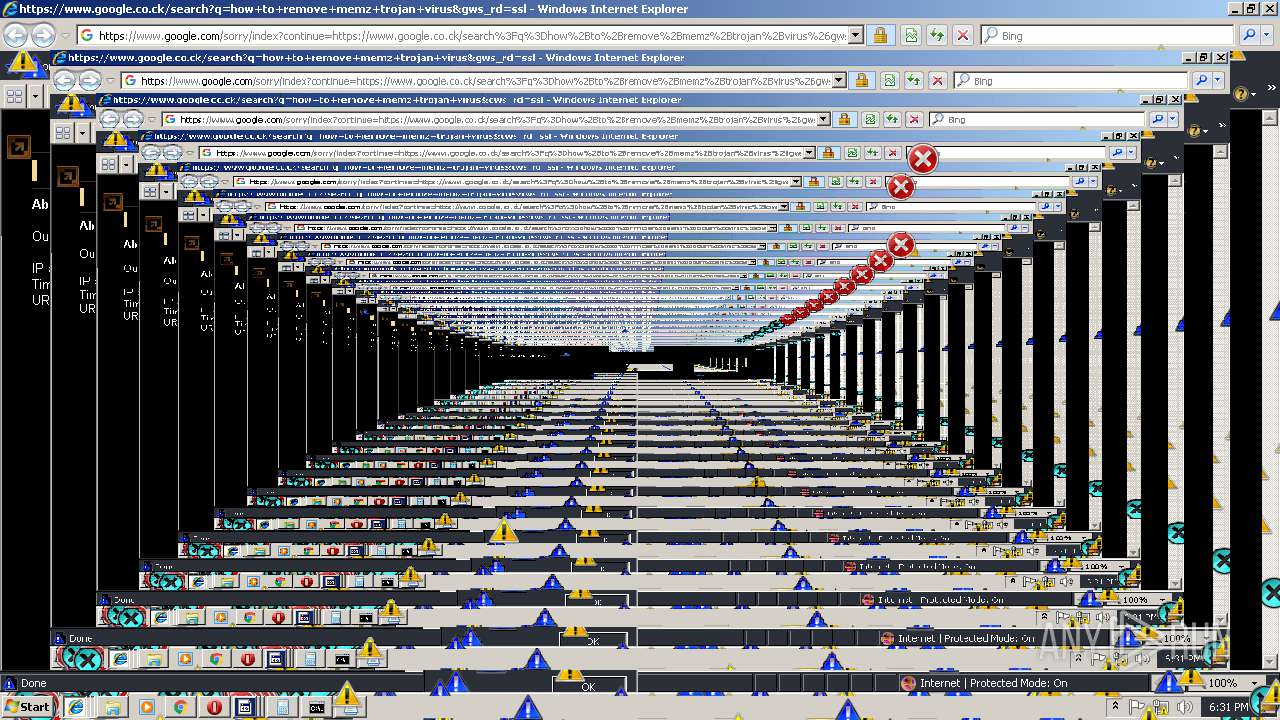
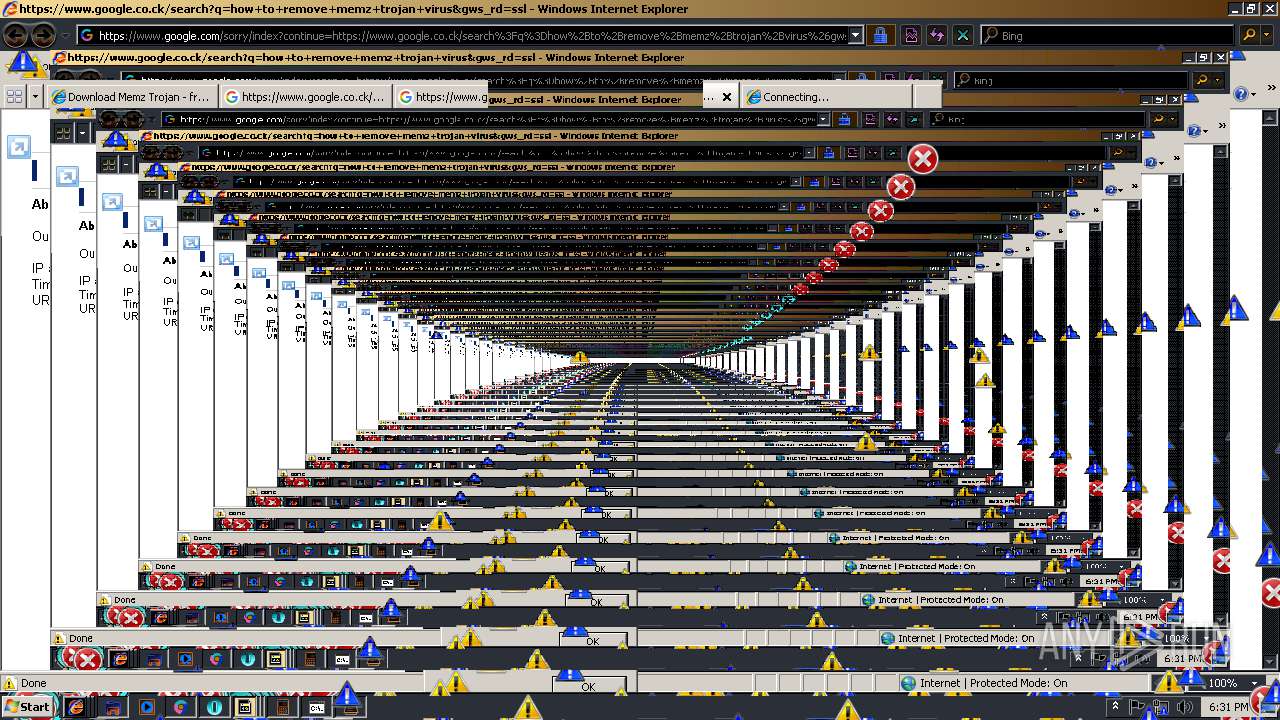
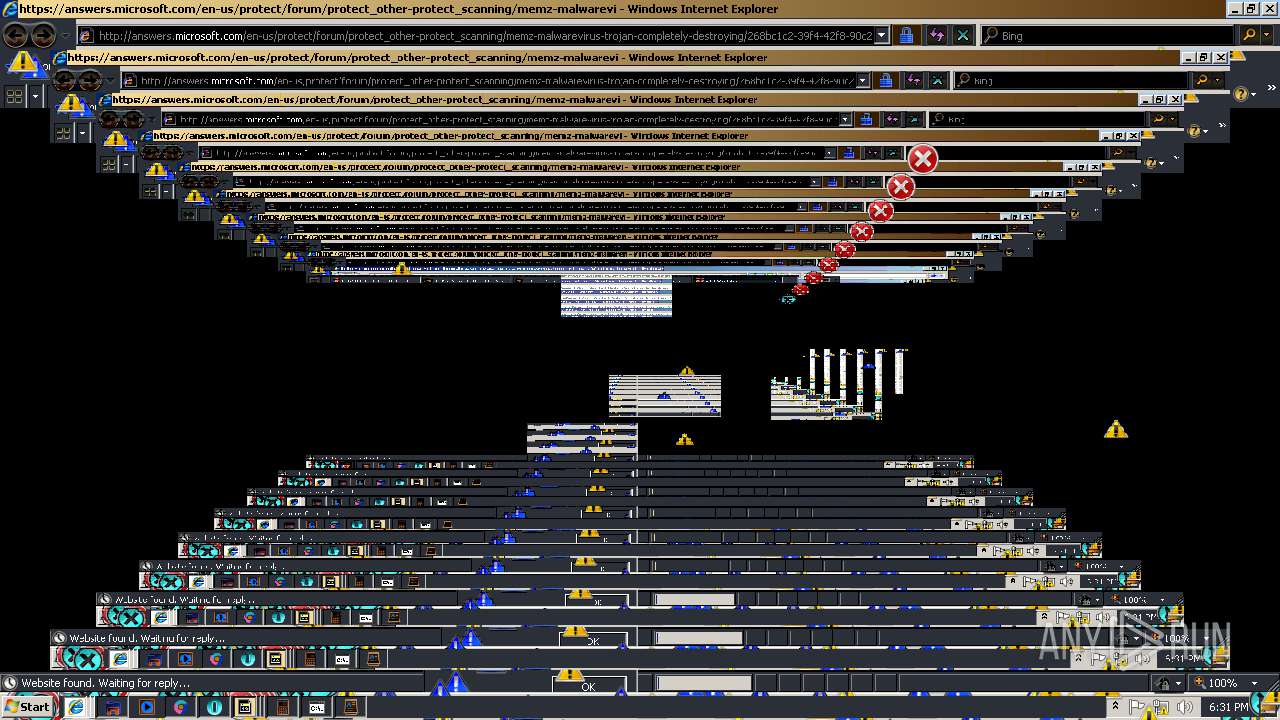
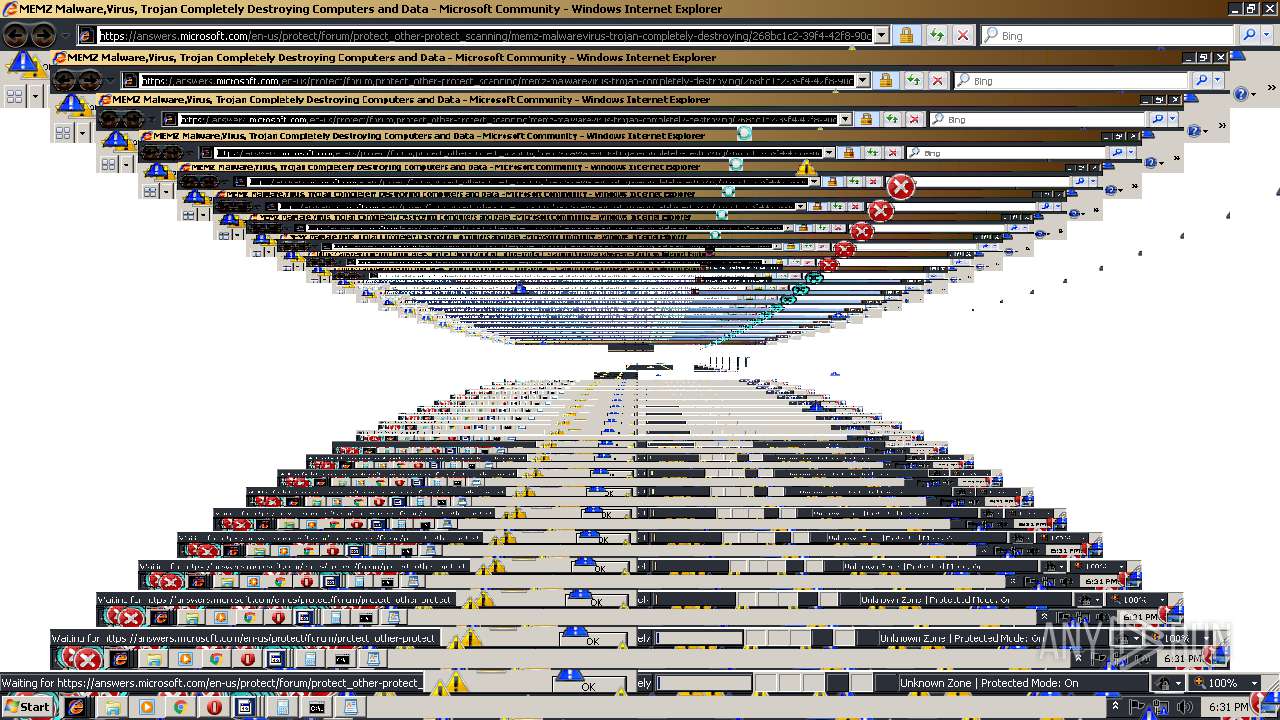
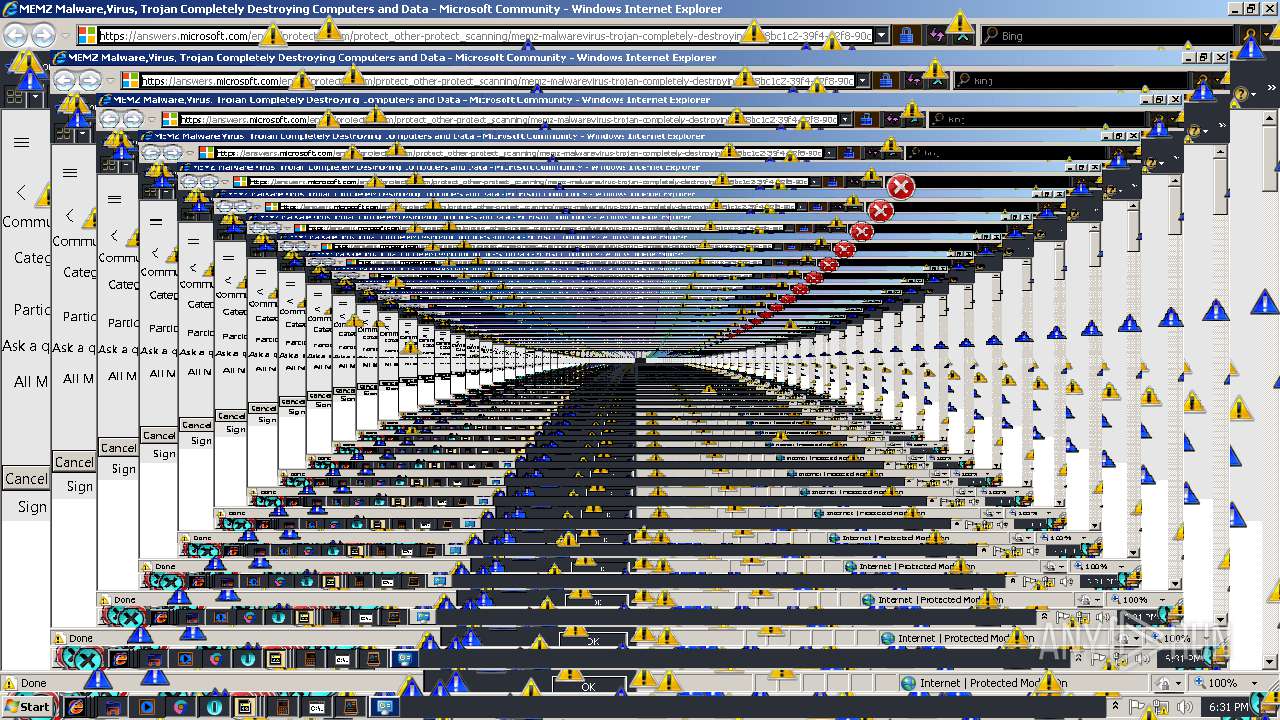
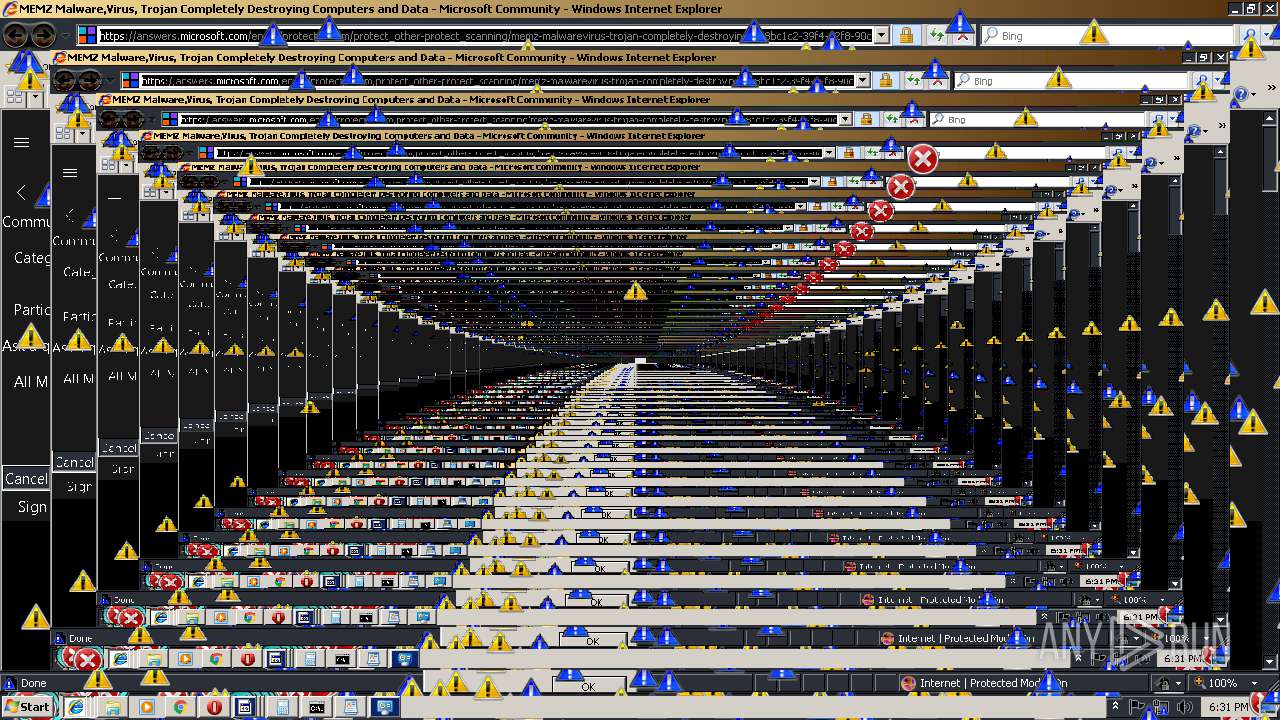
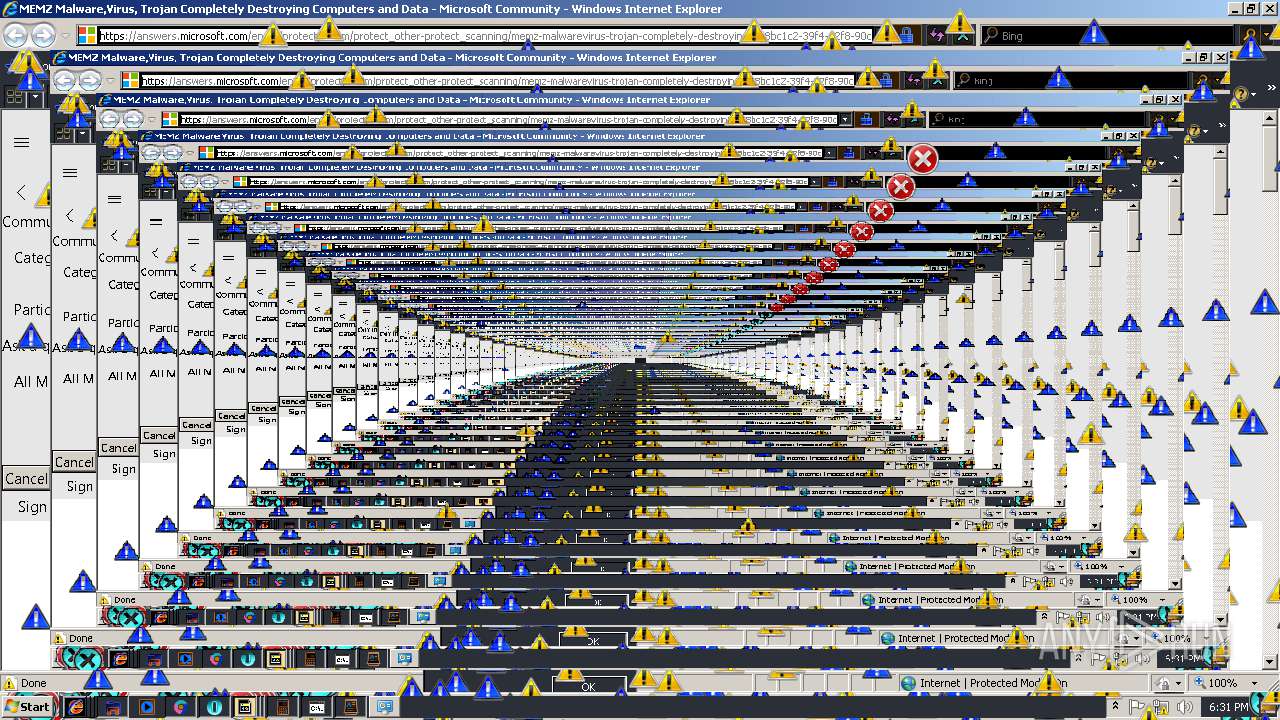
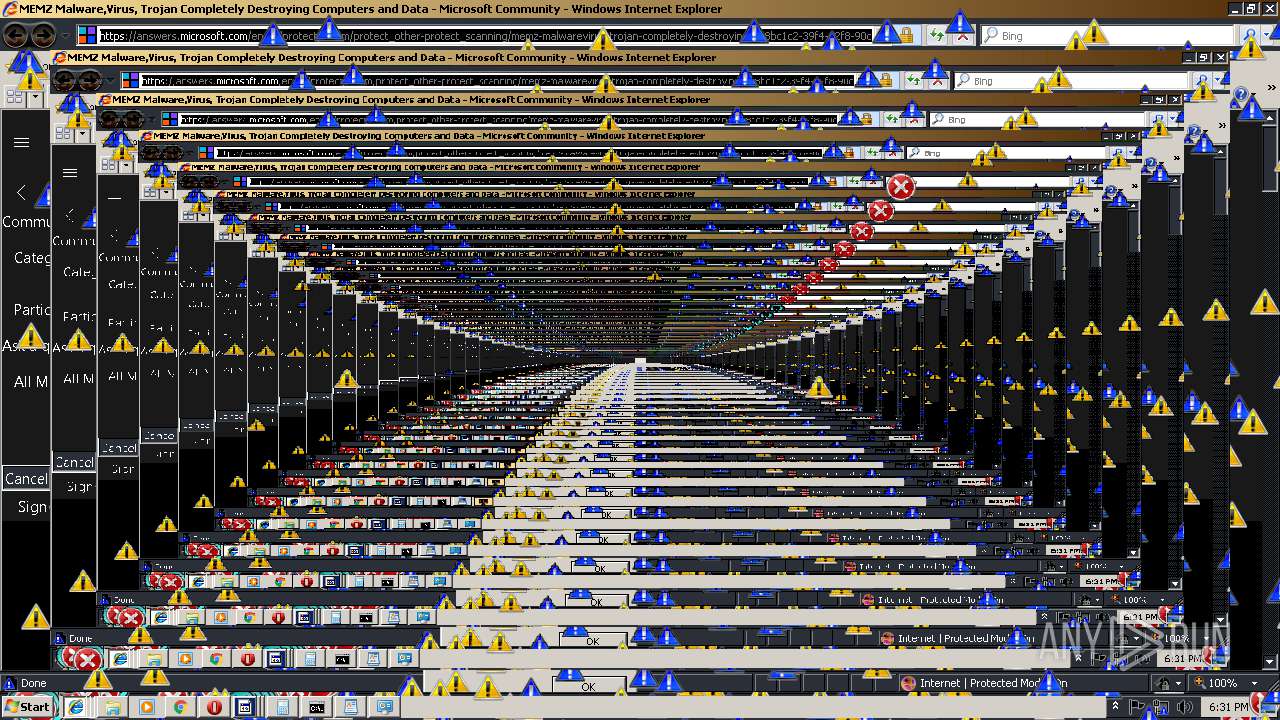
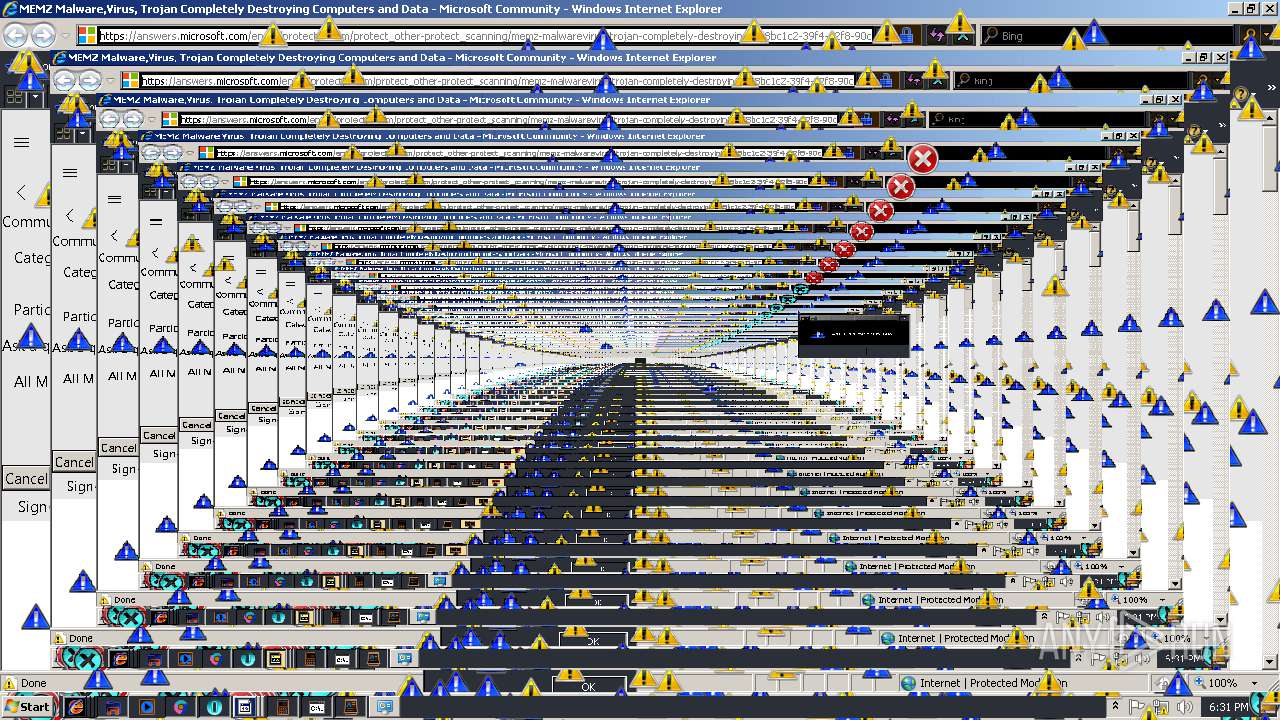
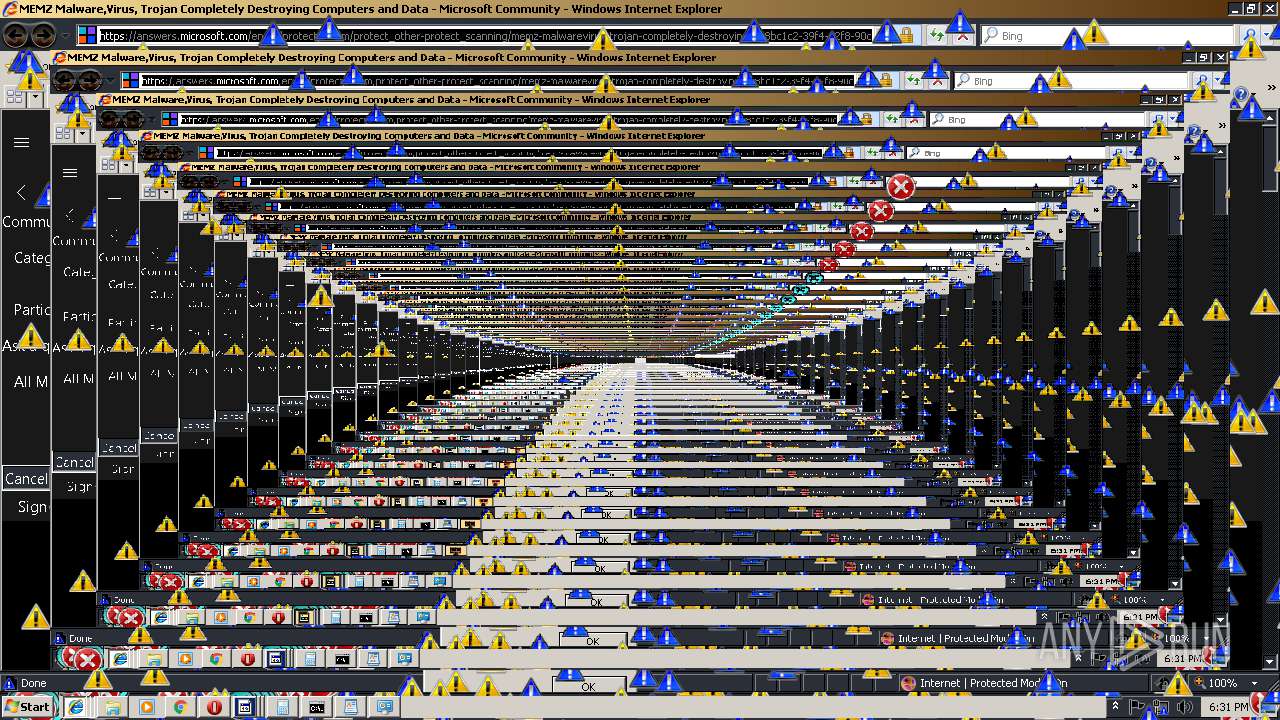
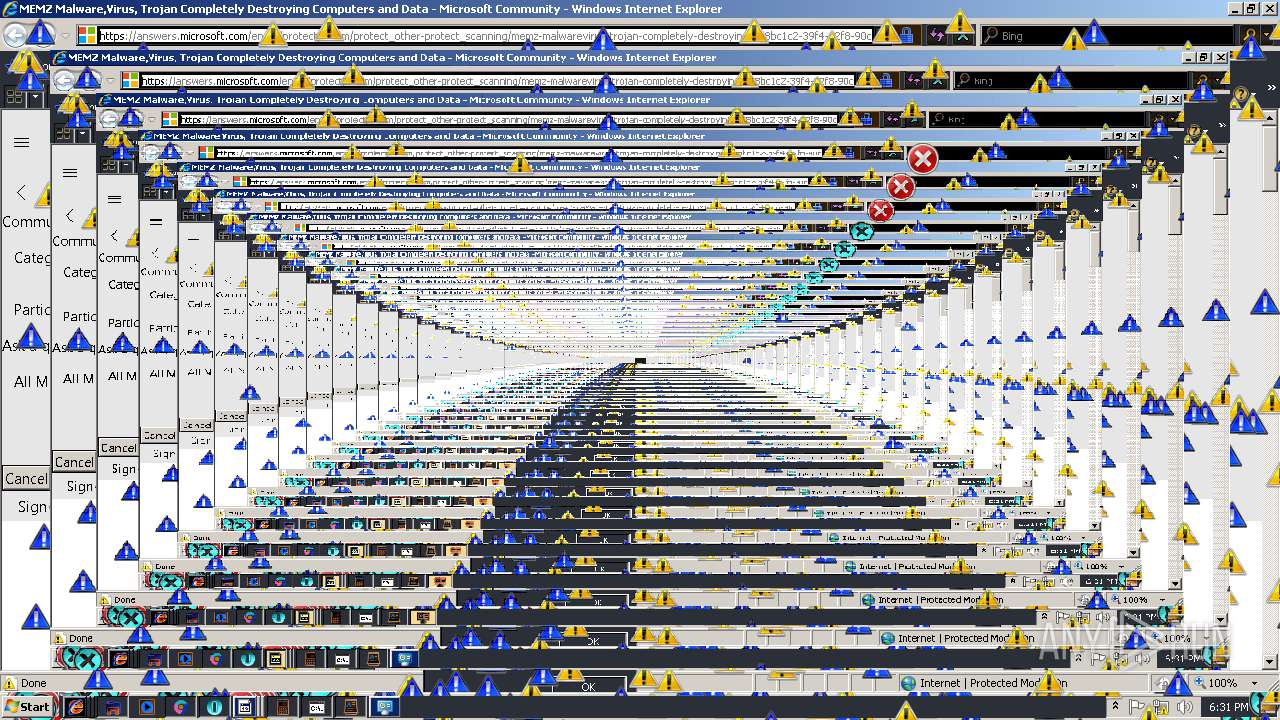
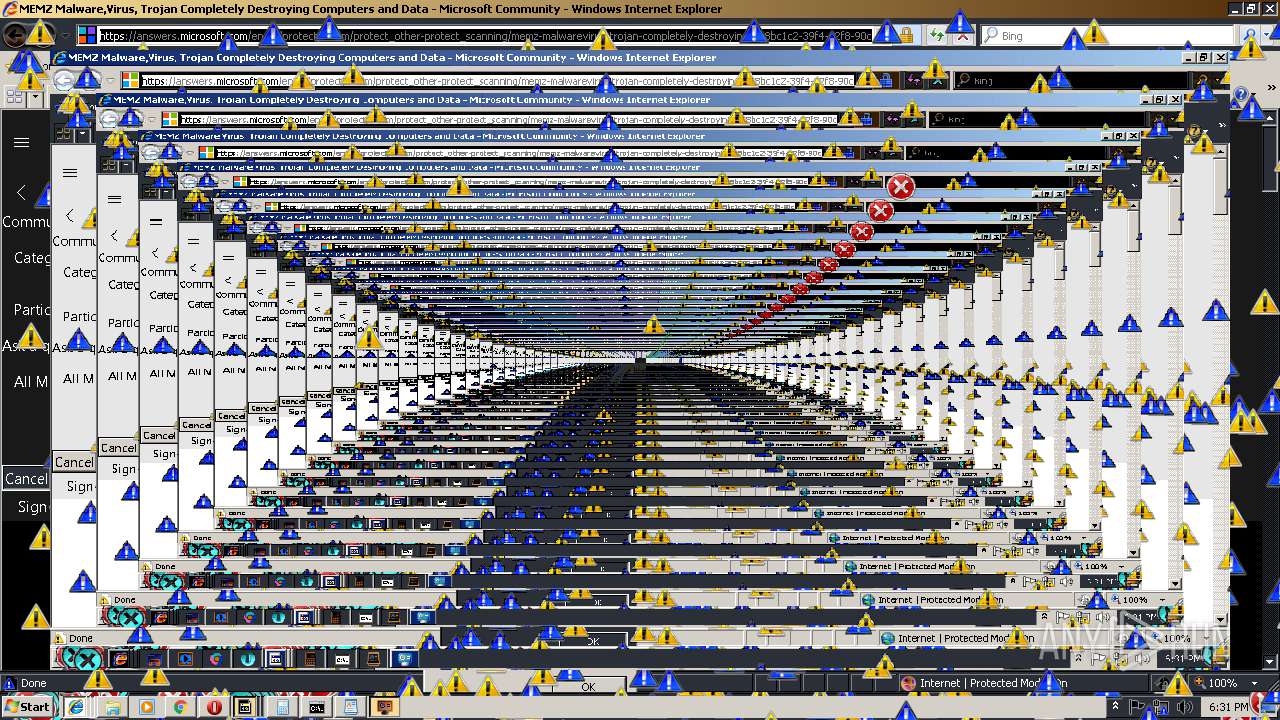
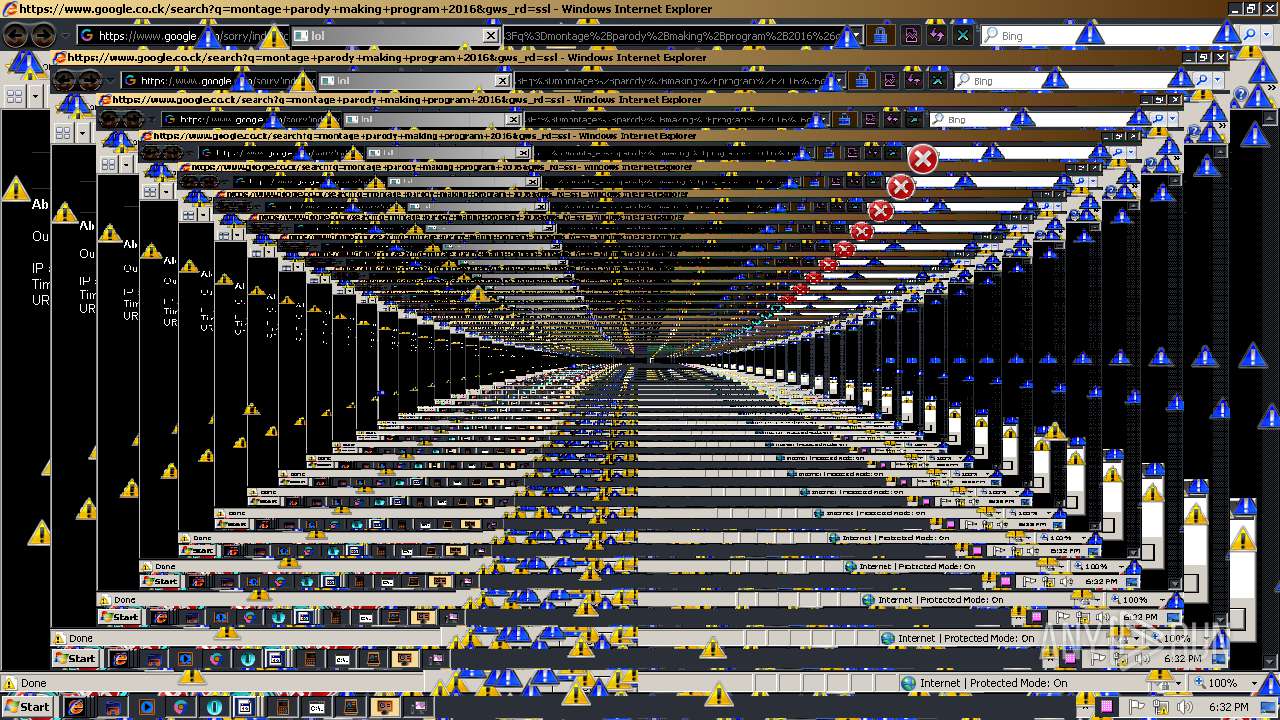
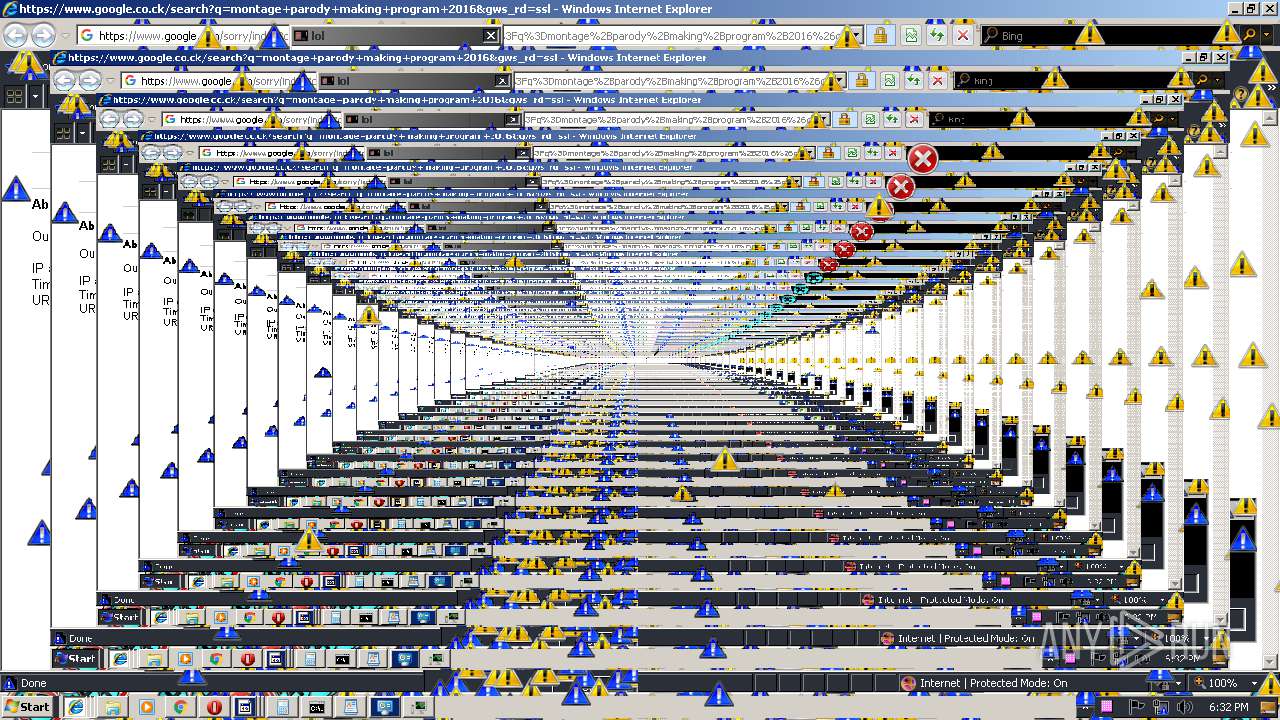
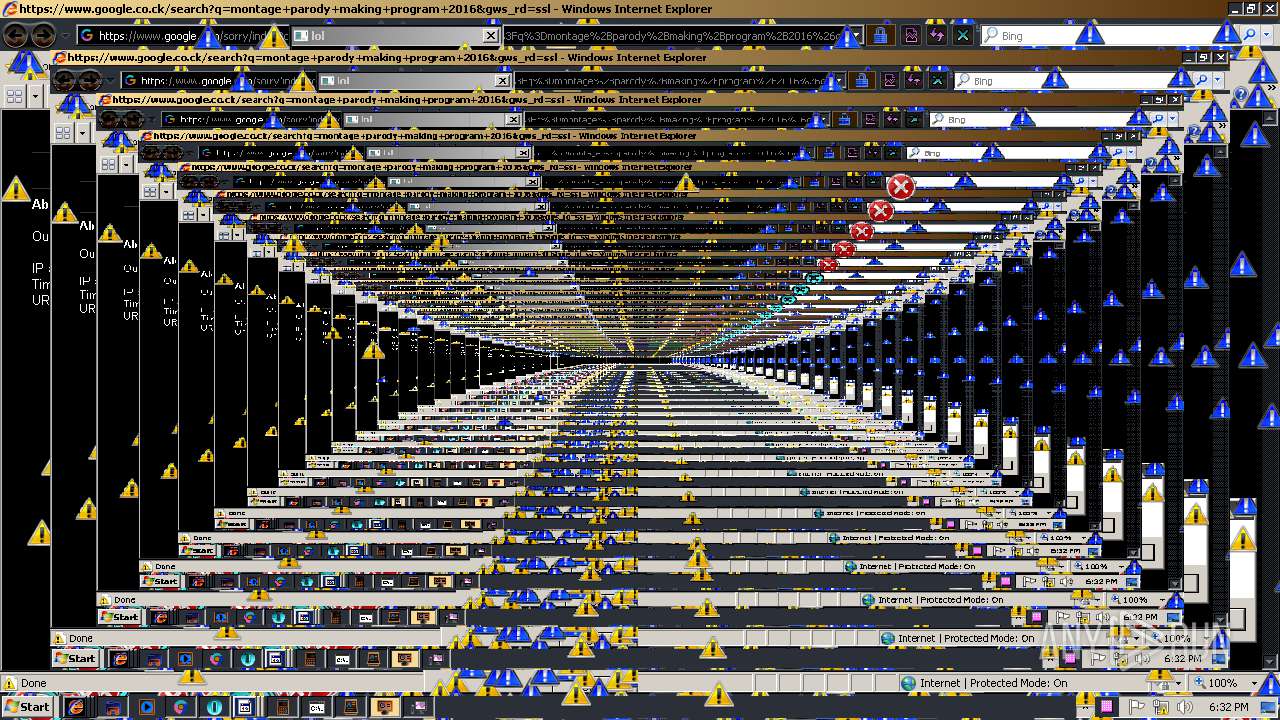
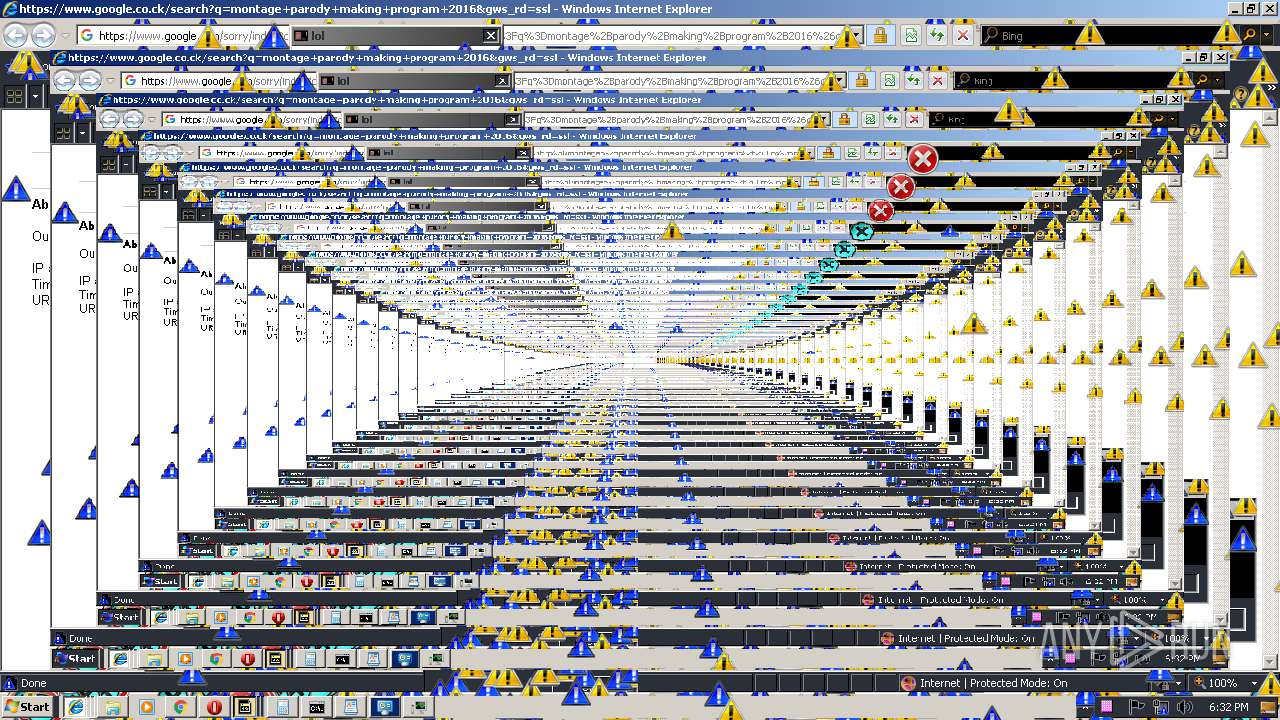
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1320 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3248 CREDAT:6422 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1840 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,13632618372041670391,9061678741372320899,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2C1D9FC1A93F72423FD21E4ED776D7F2 --mojo-platform-channel-handle=520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2244 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | MEMZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,13632618372041670391,9061678741372320899,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8E0D5829F5D7DA336A47D366448A2D33 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8E0D5829F5D7DA336A47D366448A2D33 --renderer-client-id=16 --mojo-platform-channel-handle=3856 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=908,13632618372041670391,9061678741372320899,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=F33746C12E2702B5BC6EF3D3BEEAAB60 --mojo-platform-channel-handle=4048 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3248 CREDAT:6407 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2196 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
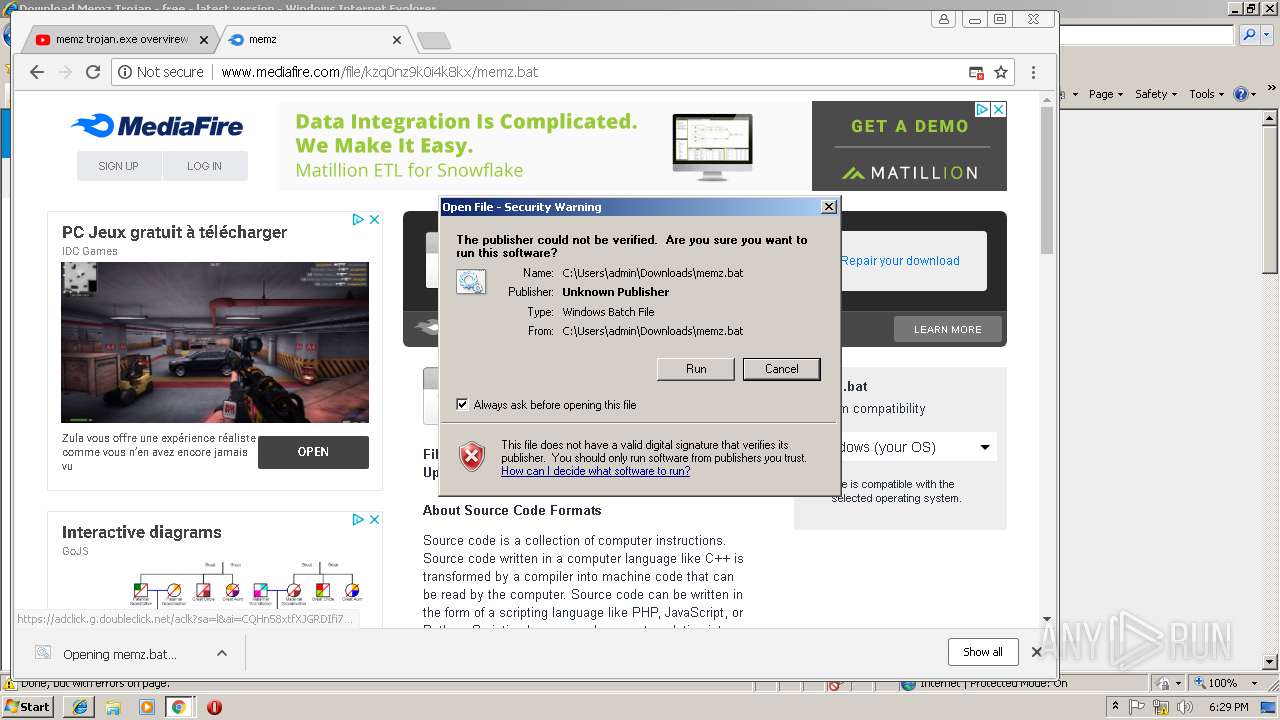
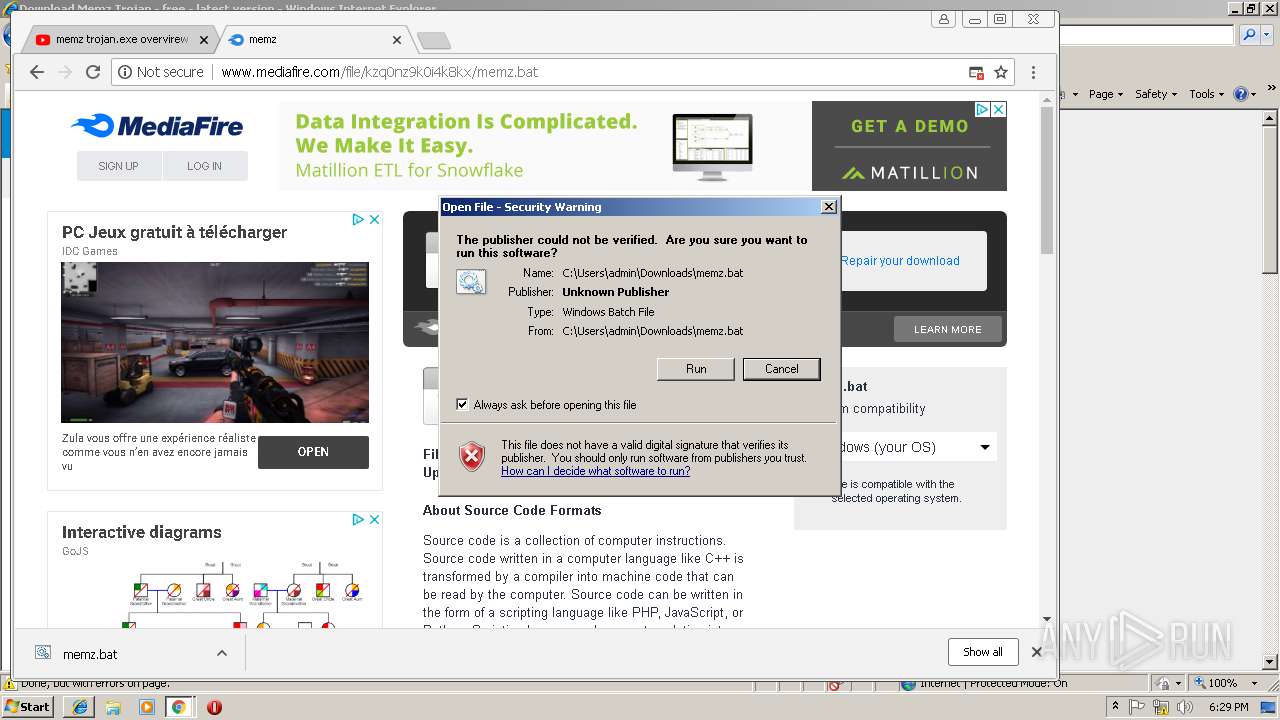
| 2560 | cmd /c ""C:\Users\admin\Downloads\memz.bat" " | C:\Windows\system32\cmd.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
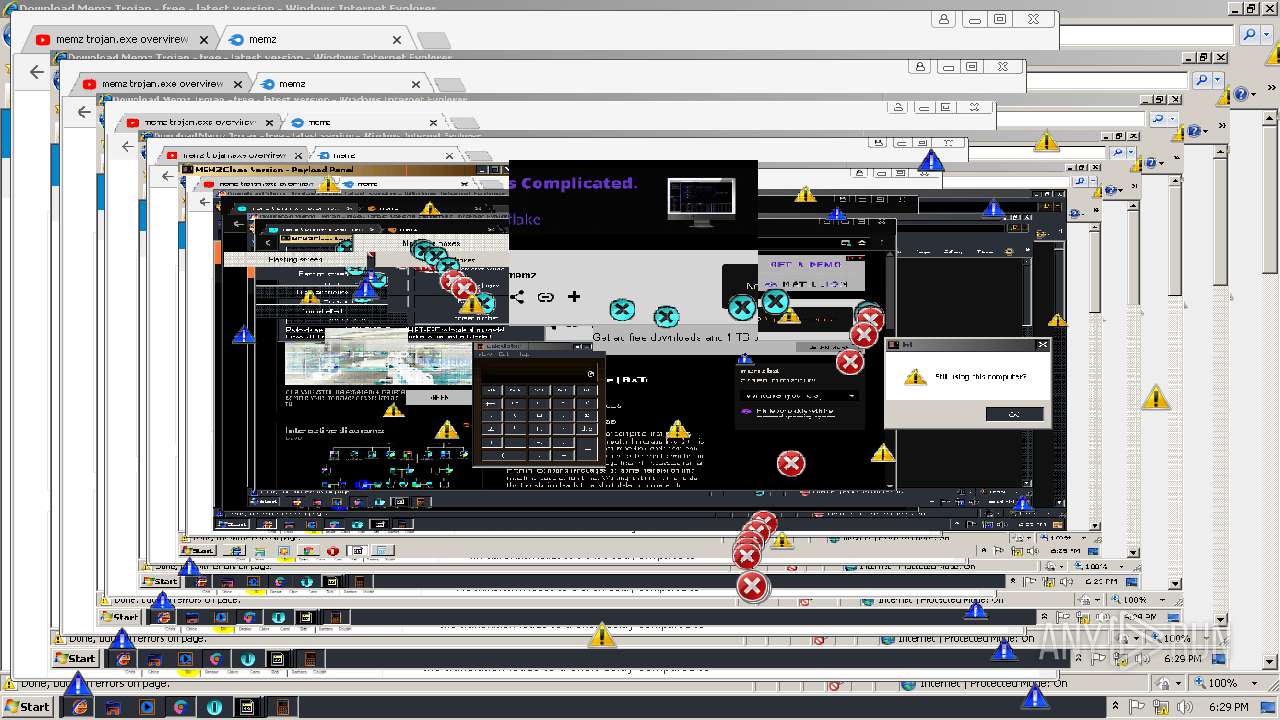
Total events
3 012
Read events
2 708
Write events
296
Delete events
8
Modification events
| (PID) Process: | (3248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {5C82C17B-2C98-11E9-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30702000600090012001B0020004A02 | |||
Executable files
1
Suspicious files
238
Text files
302
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\memz-trojan_en_softonic_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab5EAB.tmp | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar5EAC.tmp | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab5EBC.tmp | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar5EBD.tmp | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab5F4B.tmp | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar5F4C.tmp | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\gpt[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
117
TCP/UDP connections
300
DNS requests
165
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1156 | chrome.exe | GET | 200 | 172.217.16.174:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 726 b | whitelisted |
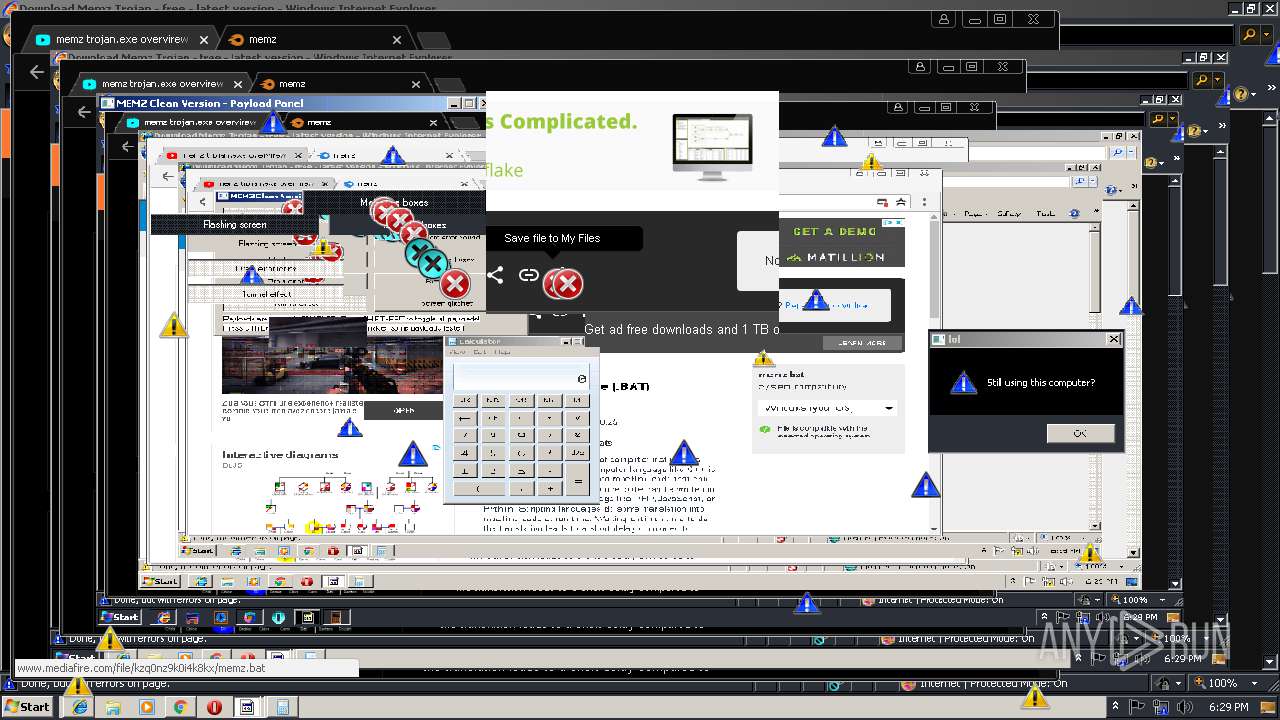
1156 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://static.mediafire.com/js/ads.js | US | text | 143 b | shared |
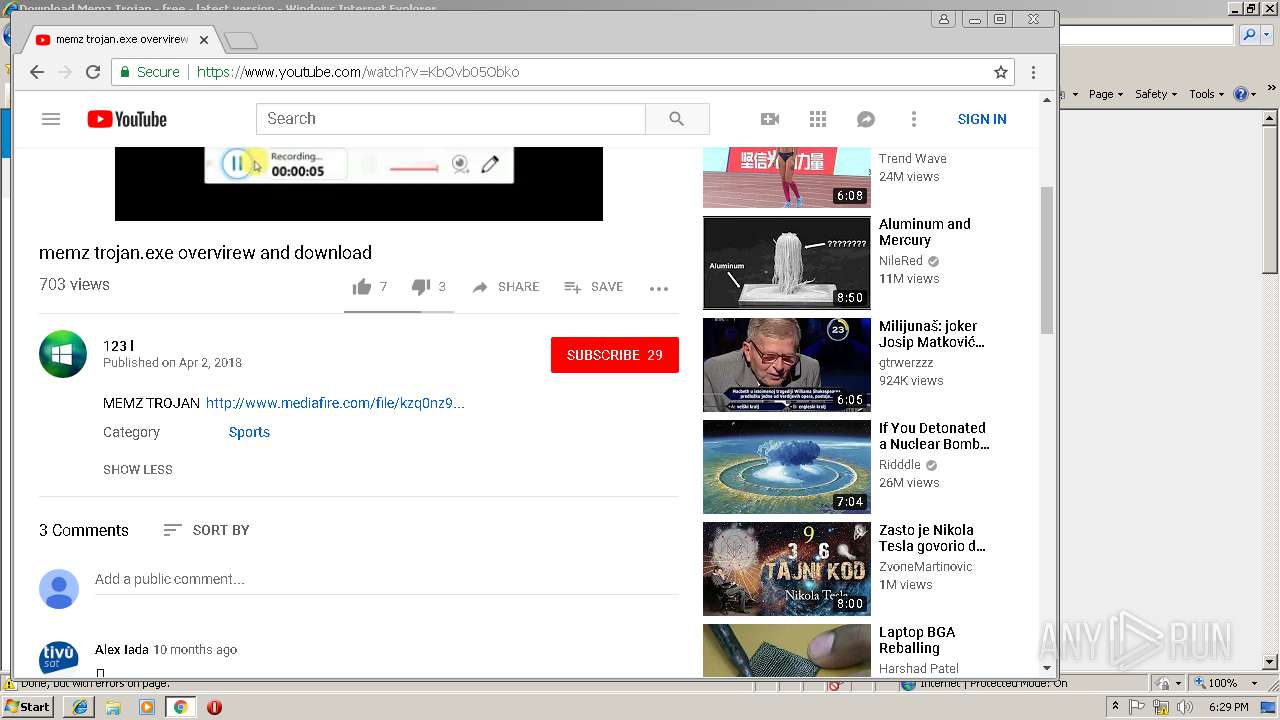
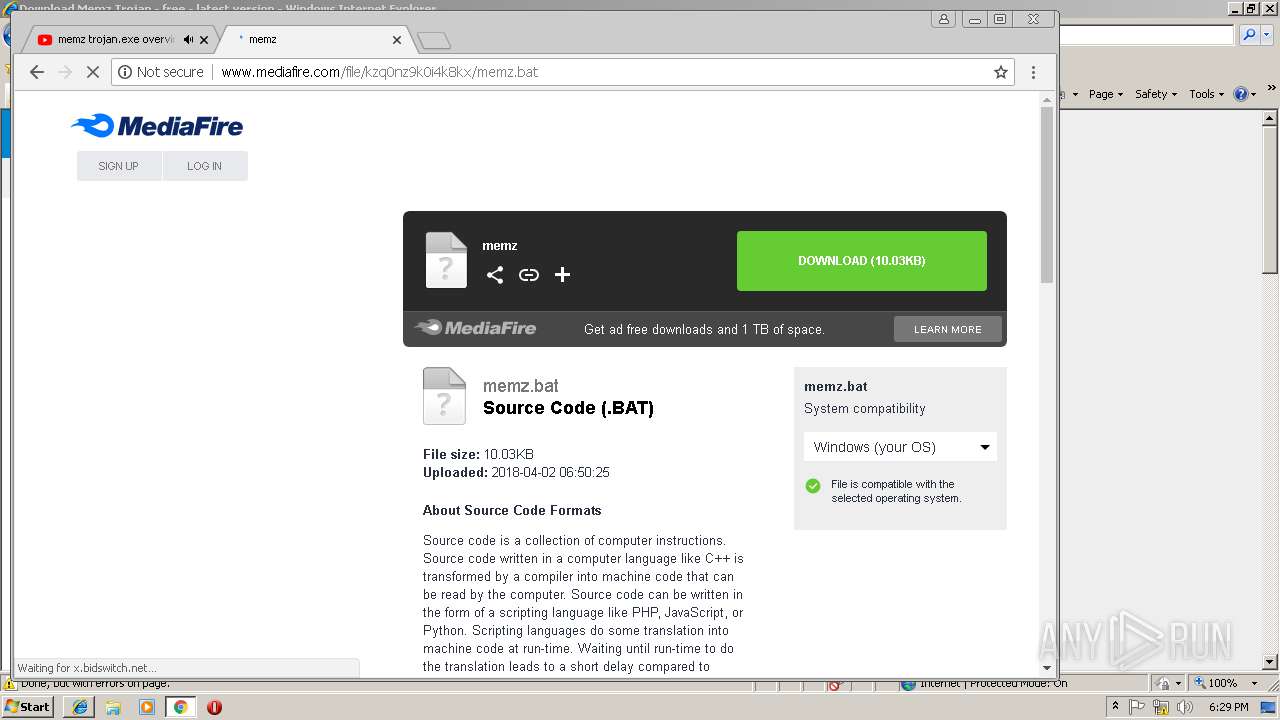
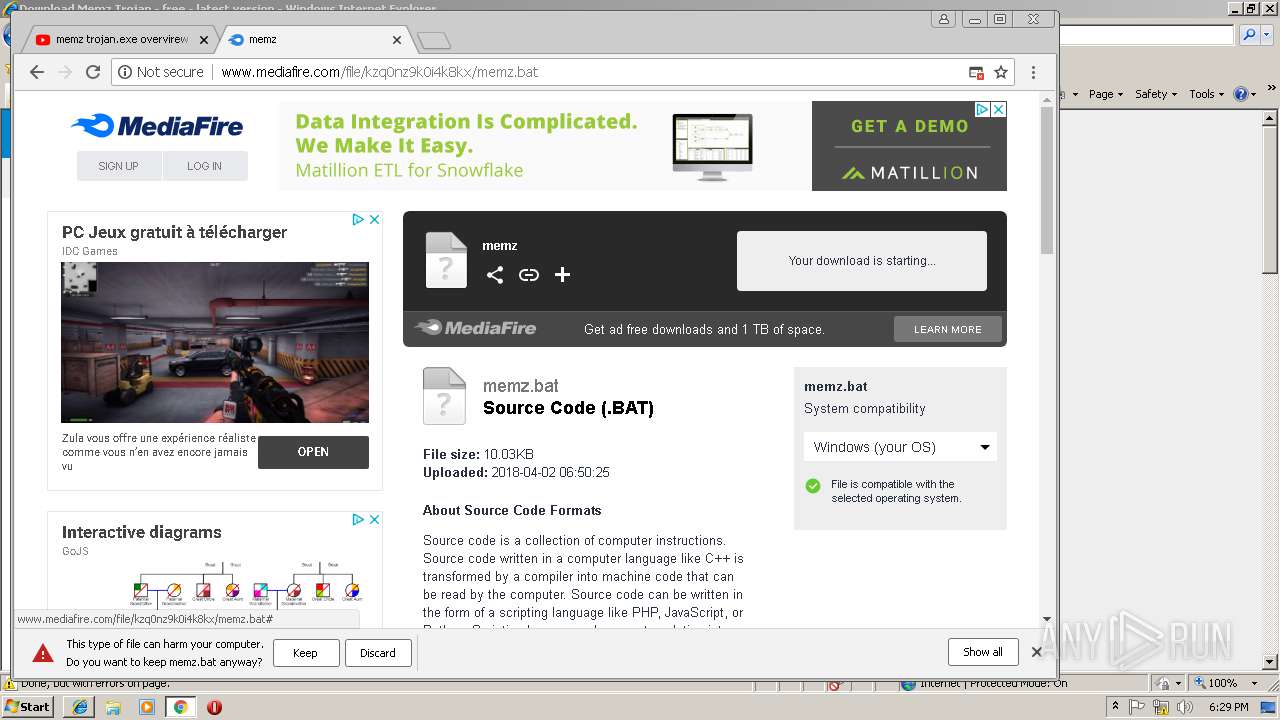
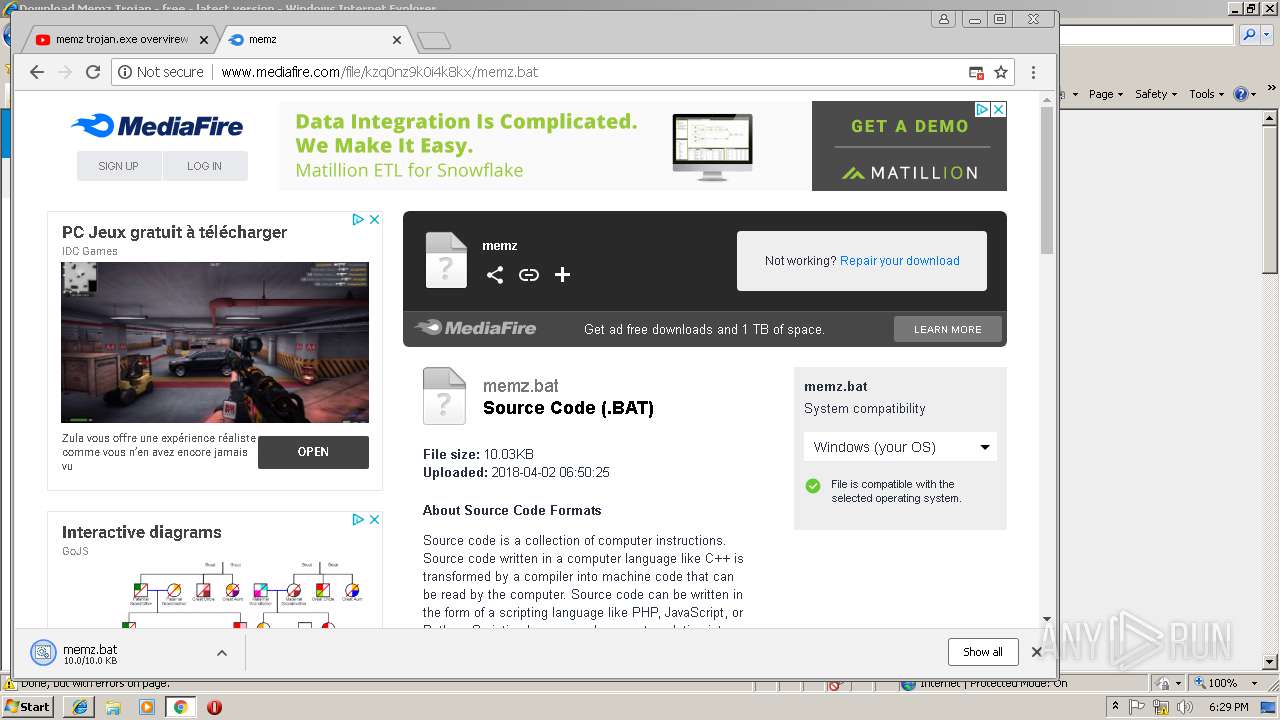
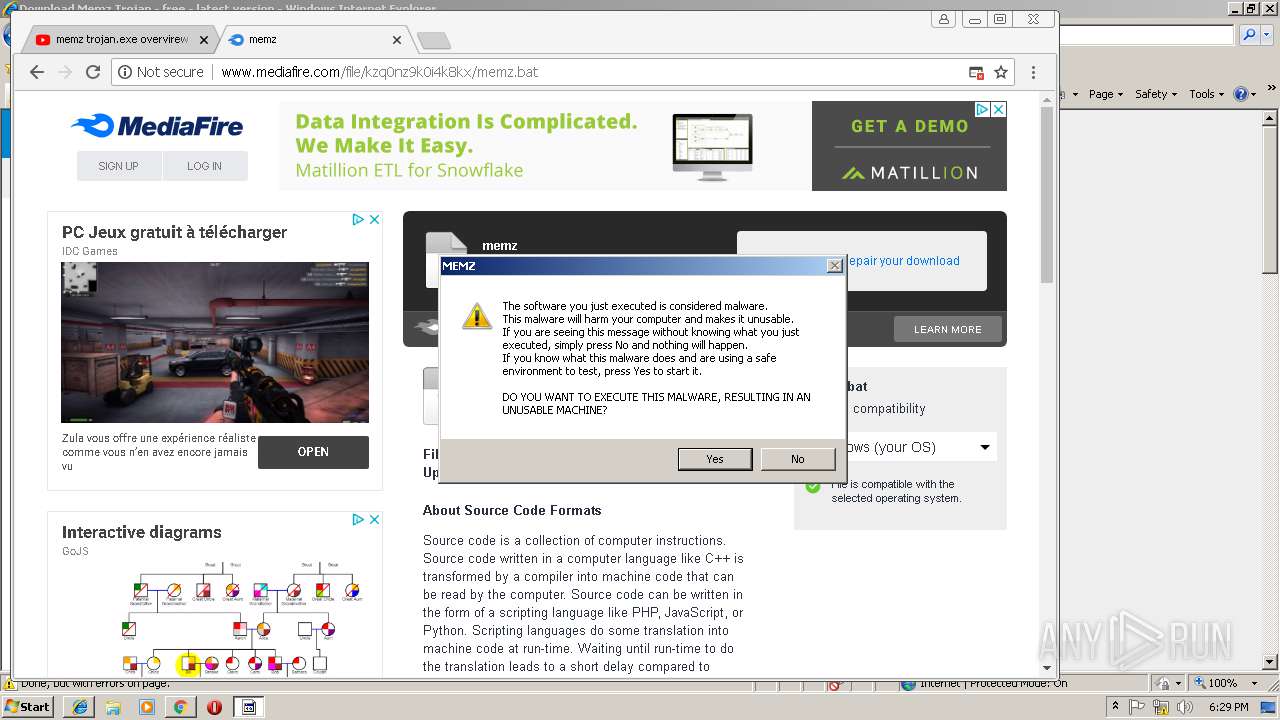
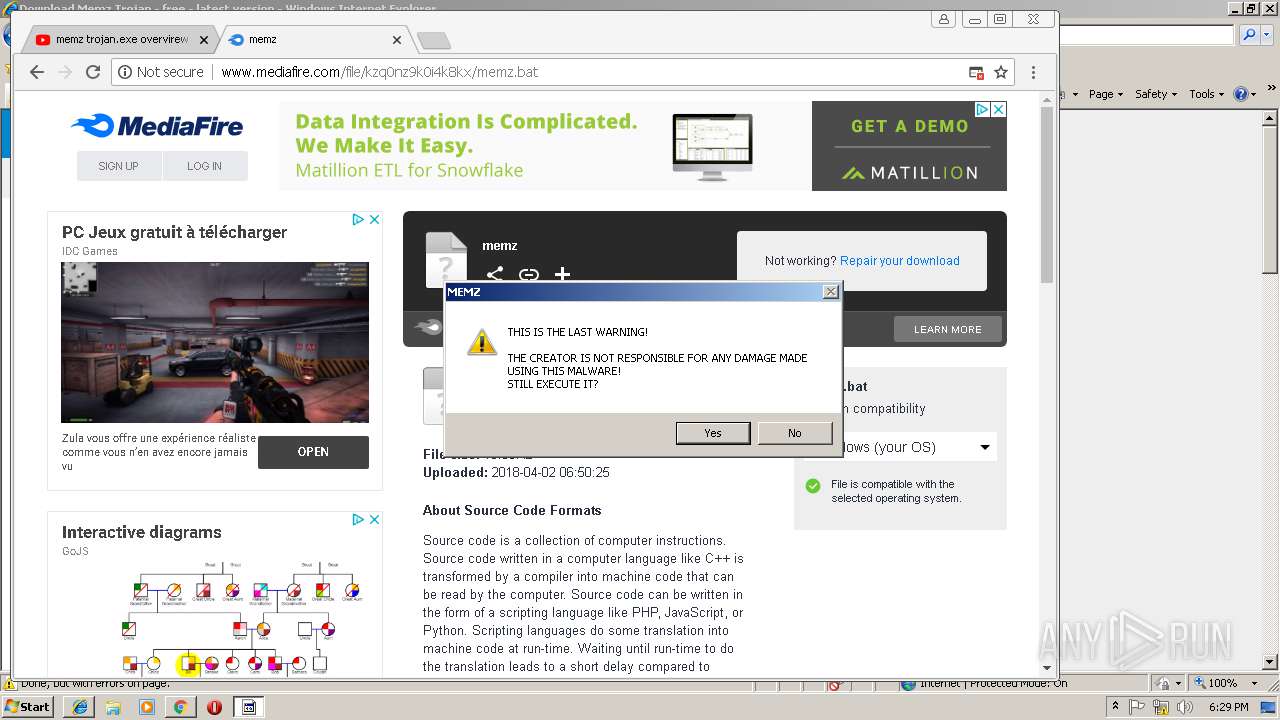
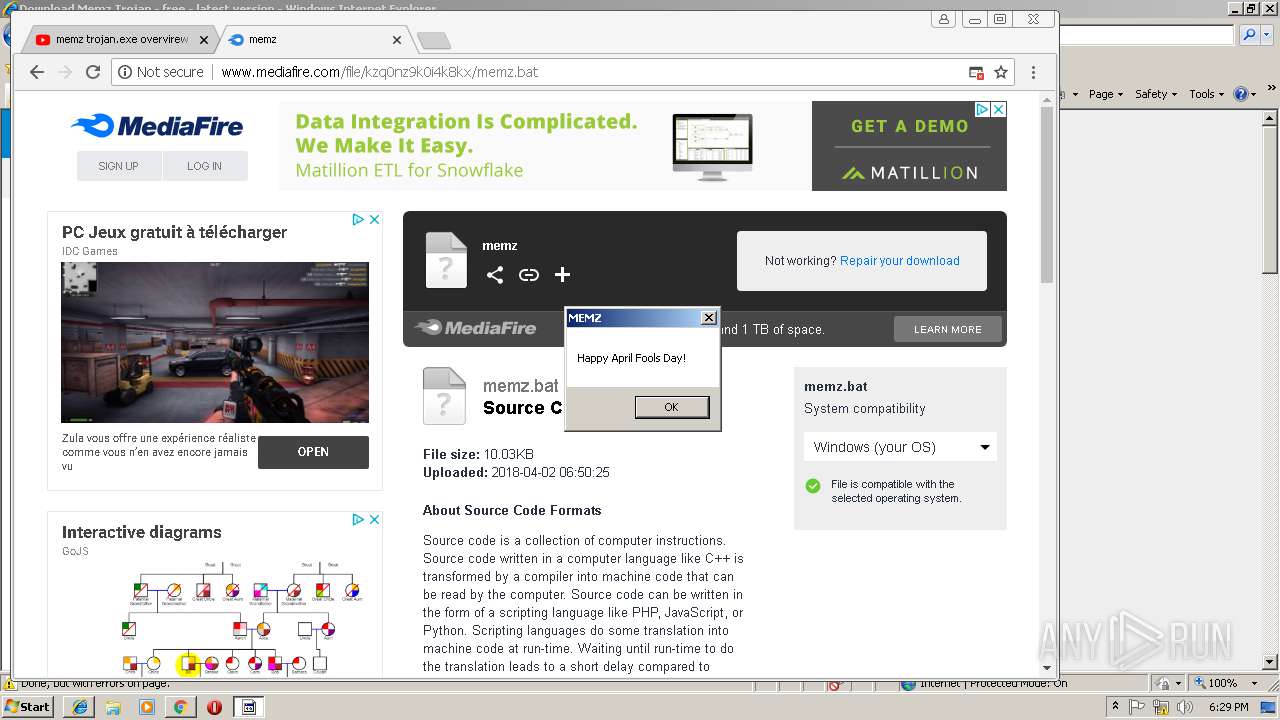
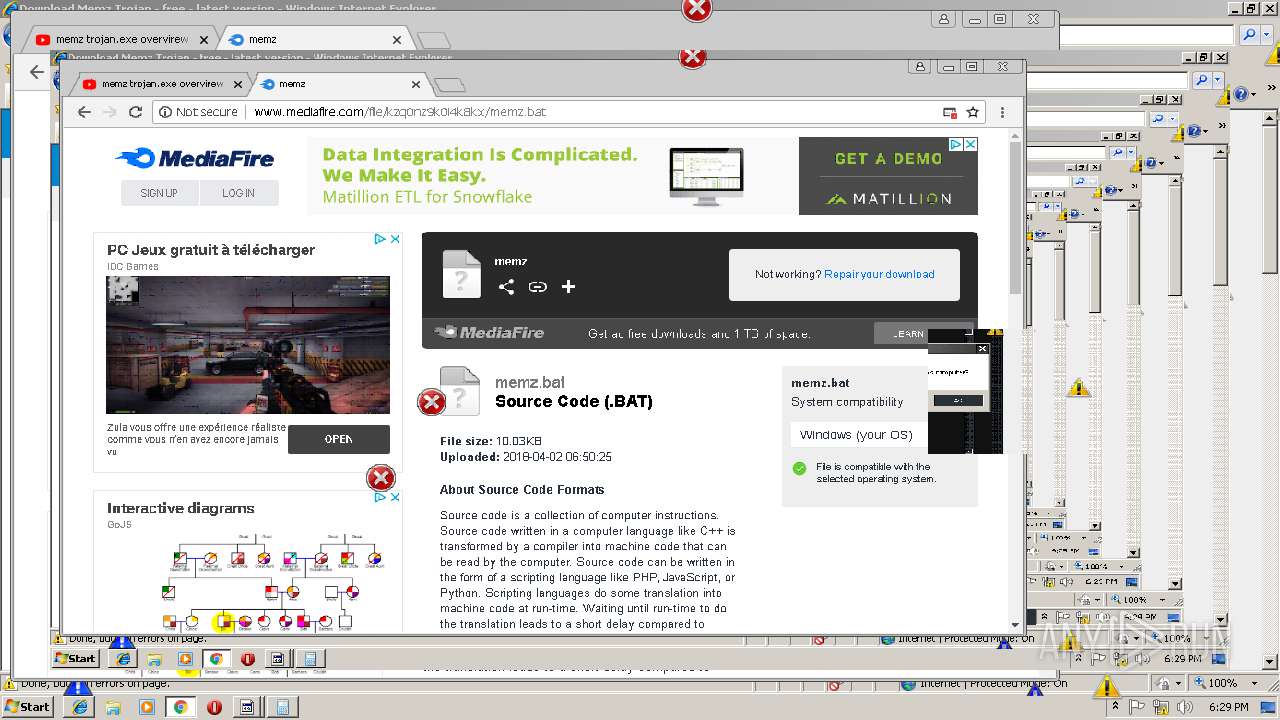
1156 | chrome.exe | GET | 200 | 104.19.195.29:80 | http://www.mediafire.com/file/kzq0nz9k0i4k8kx/memz.bat | US | html | 57.6 Kb | shared |
1156 | chrome.exe | GET | 200 | 104.19.195.29:80 | http://www.mediafire.com/templates/linkto/ads.php?o=0&d=1&t=0 | US | html | 3.25 Kb | shared |
1156 | chrome.exe | GET | 200 | 104.17.72.92:80 | http://cdn.engine.addroplet.com/Scripts/infinity.js.aspx?guid=5ff0fb62-0643-4ff1-aaee-c737f9ffc0e0 | US | text | 71.1 Kb | whitelisted |
1156 | chrome.exe | GET | 302 | 2.16.186.80:80 | http://b.scorecardresearch.com/b?c1=8&c2=18203330&rn=0.7359519805997803&c7=http%3A%2F%2Fwww.mediafire.com%2Ffile%2Fkzq0nz9k0i4k8kx%2Fmemz.bat&c3=1&c4=&c5=&c6=&c10=&c15=&c16=&c8=memz&c9=https%3A%2F%2Fwww.youtube.com%2F&cv=1.8 | unknown | compressed | 708 b | whitelisted |
3432 | iexplore.exe | GET | 200 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.2 Kb | whitelisted |
1156 | chrome.exe | GET | 200 | 172.217.18.162:80 | http://www.googletagservices.com/tag/js/gpt.js | US | text | 9.82 Kb | whitelisted |
1156 | chrome.exe | GET | 200 | 104.17.72.92:80 | http://engine.addroplet.com/Tag.engine?time=0&id=5ff0fb62-0643-4ff1-aaee-c737f9ffc0e0&rand=60708&ver=async&referrerUrl=https%3A%2F%2Fwww.youtube.com%2F&fingerPrint=123&abr=false&stdTime=0&fpe=1&bw=1040&bh=586&res=1280x720&curl=http%3A%2F%2Fwww.mediafire.com%2Ffile%2Fkzq0nz9k0i4k8kx%2Fmemz.bat&kw=online%20storage%2Cfree%20storage%2Ccloud%20storage%2Ccollaboration%2Cbackup%20file%20sharing%2Cshare%20files%2Cphoto%20backup%2Cphoto%20sharing%2Cftp%20replacement%2Ccross%20platform%2Cremote%20access%2Cmobile%20access%2Csend%20large%20files%2Crecover%20files%2Cfile%20versioning%2Cundelete%2Cwindows%2Cpc%2Cmac%2Cos%20x%2Clinux%2Ciphone | US | text | 2.61 Kb | shared |
1156 | chrome.exe | GET | 200 | 2.16.186.80:80 | http://b.scorecardresearch.com/beacon.js?c1=8&c2=18203330&c3=1 | unknown | text | 708 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3432 | iexplore.exe | 2.16.186.81:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3432 | iexplore.exe | 152.195.132.202:443 | cdn.cookielaw.org | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3432 | iexplore.exe | 63.215.202.80:443 | www.anrdoezrs.net | Conversant, Inc. | NL | malicious |
3432 | iexplore.exe | 205.185.208.52:443 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
3248 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3432 | iexplore.exe | 35.190.12.174:443 | memz-trojan.en.softonic.com | Google Inc. | US | malicious |
3432 | iexplore.exe | 172.217.18.162:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
3432 | iexplore.exe | 151.101.2.109:443 | cdn.polyfill.io | Fastly | US | suspicious |
3248 | iexplore.exe | 151.101.2.133:443 | sc.sftcdn.net | Fastly | US | malicious |
3432 | iexplore.exe | 13.35.254.34:80 | x.ss2.us | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
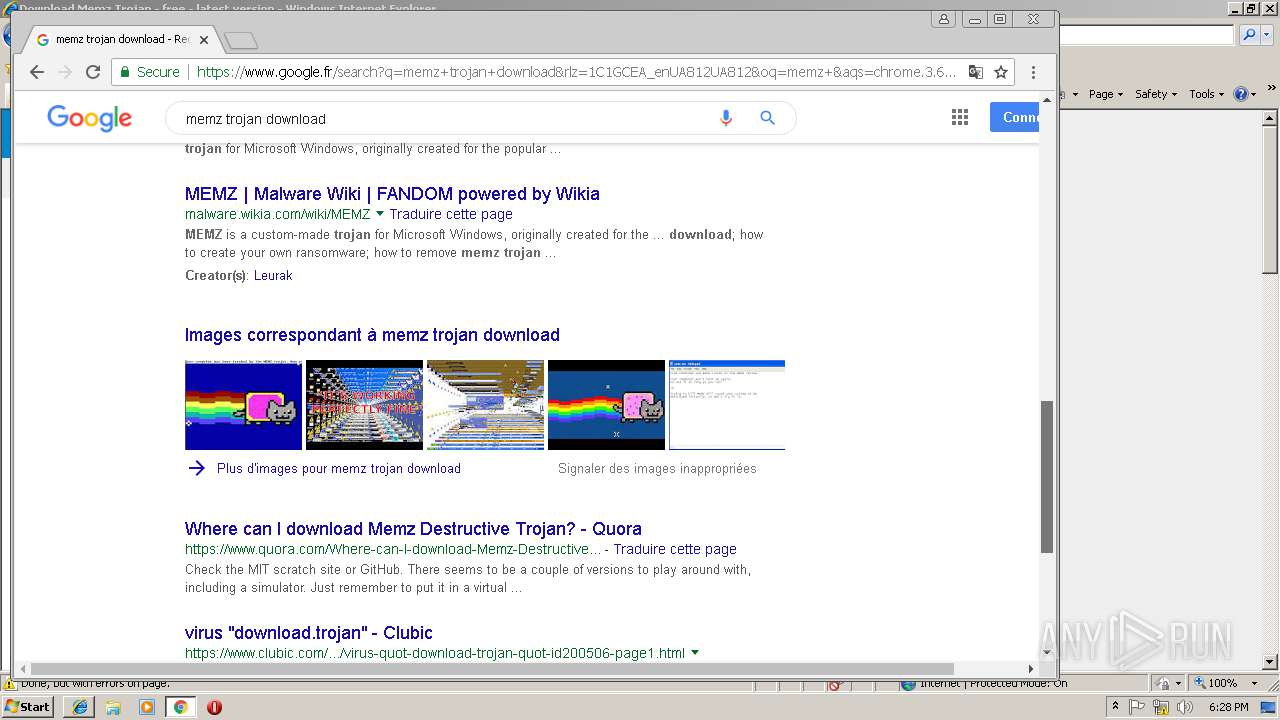
memz-trojan.en.softonic.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdn.polyfill.io |
| whitelisted |
sc.sftcdn.net |
| whitelisted |
www.googletagservices.com |
| whitelisted |
c.amazon-adsystem.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
images.sftcdn.net |
| whitelisted |
x.ss2.us |
| whitelisted |
www.anrdoezrs.net |
| whitelisted |