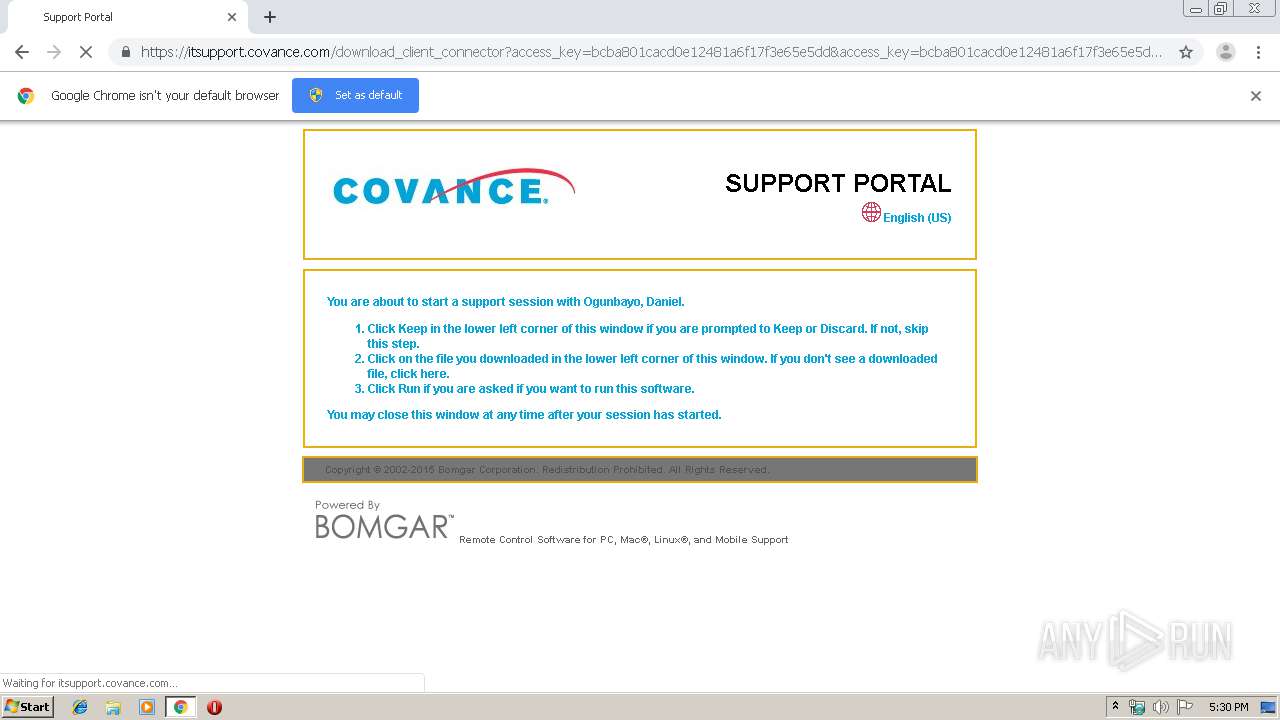
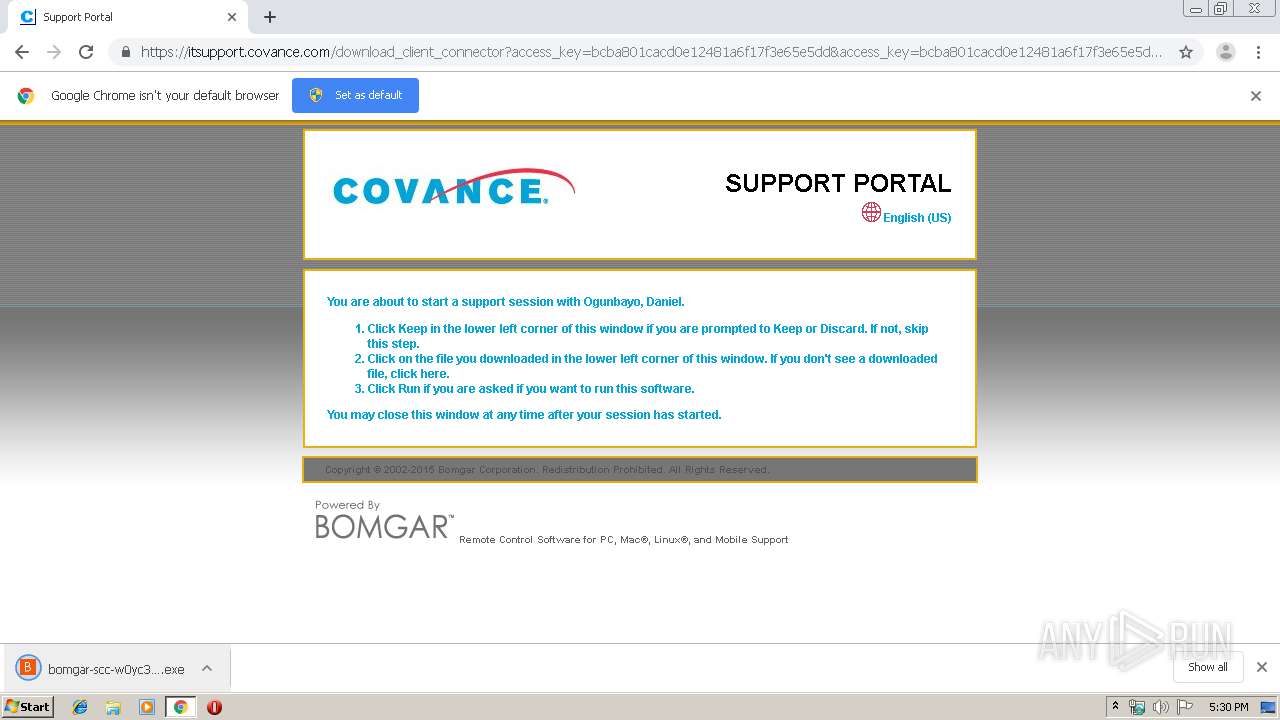
| URL: | https://itsupport.covance.com/?ak=bcba801cacd0e12481a6f17f3e65e5dd |
| Full analysis: | https://app.any.run/tasks/49051fc5-7639-416b-a9b9-2d94b1993aba |
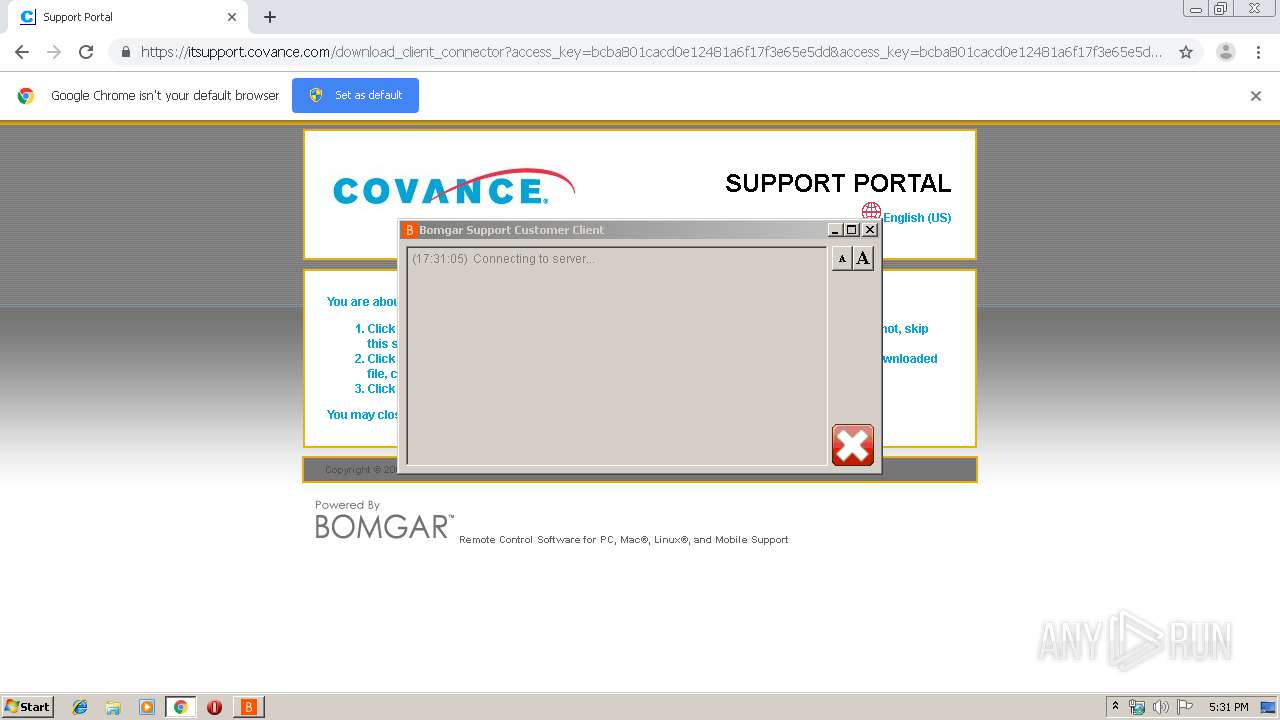
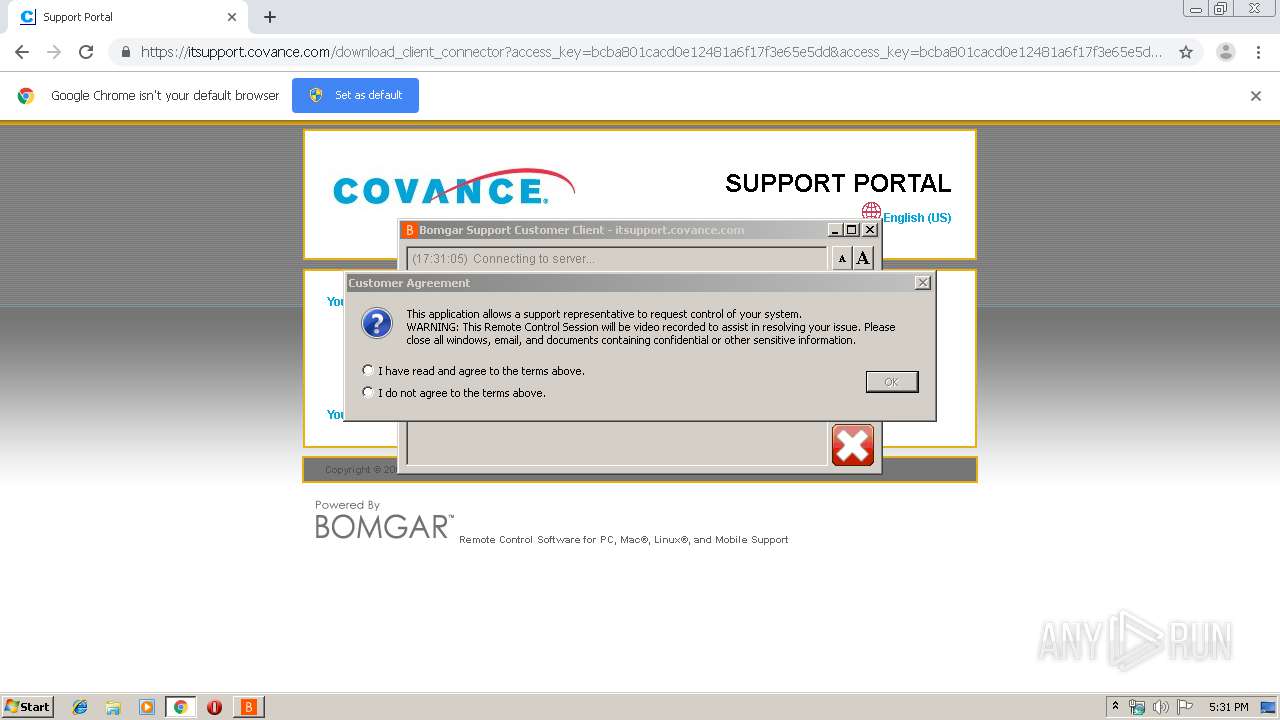
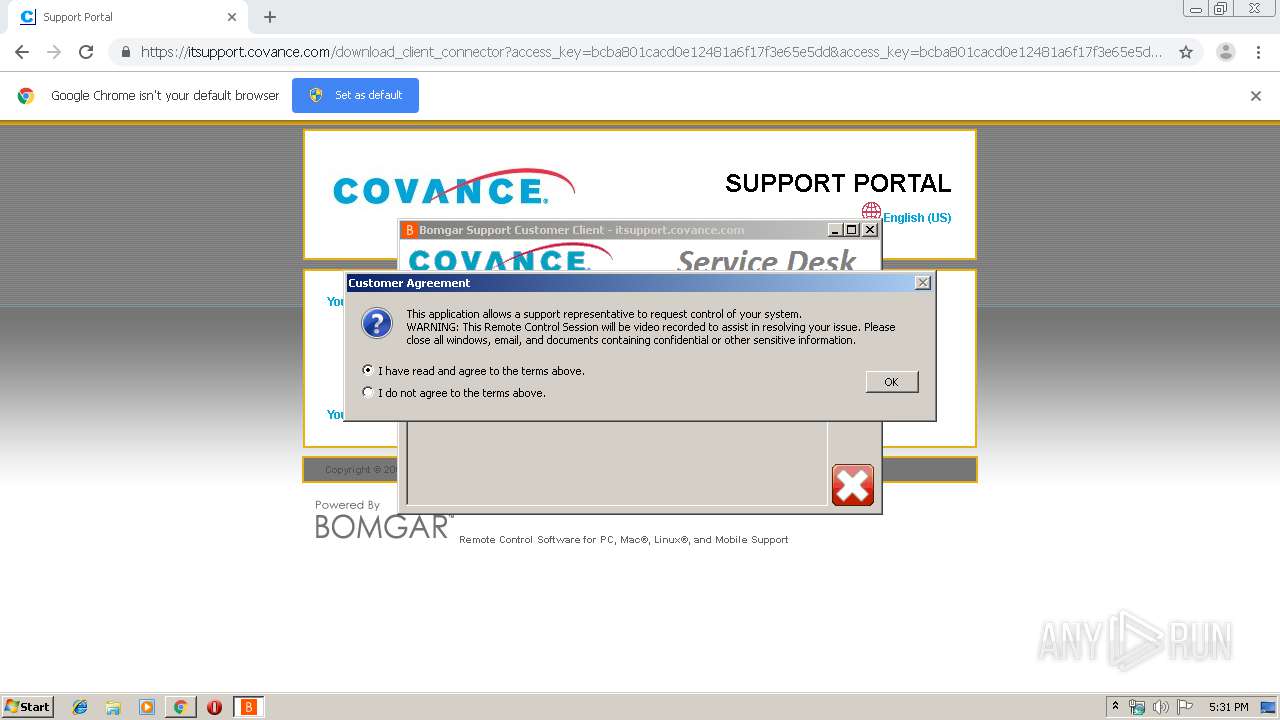
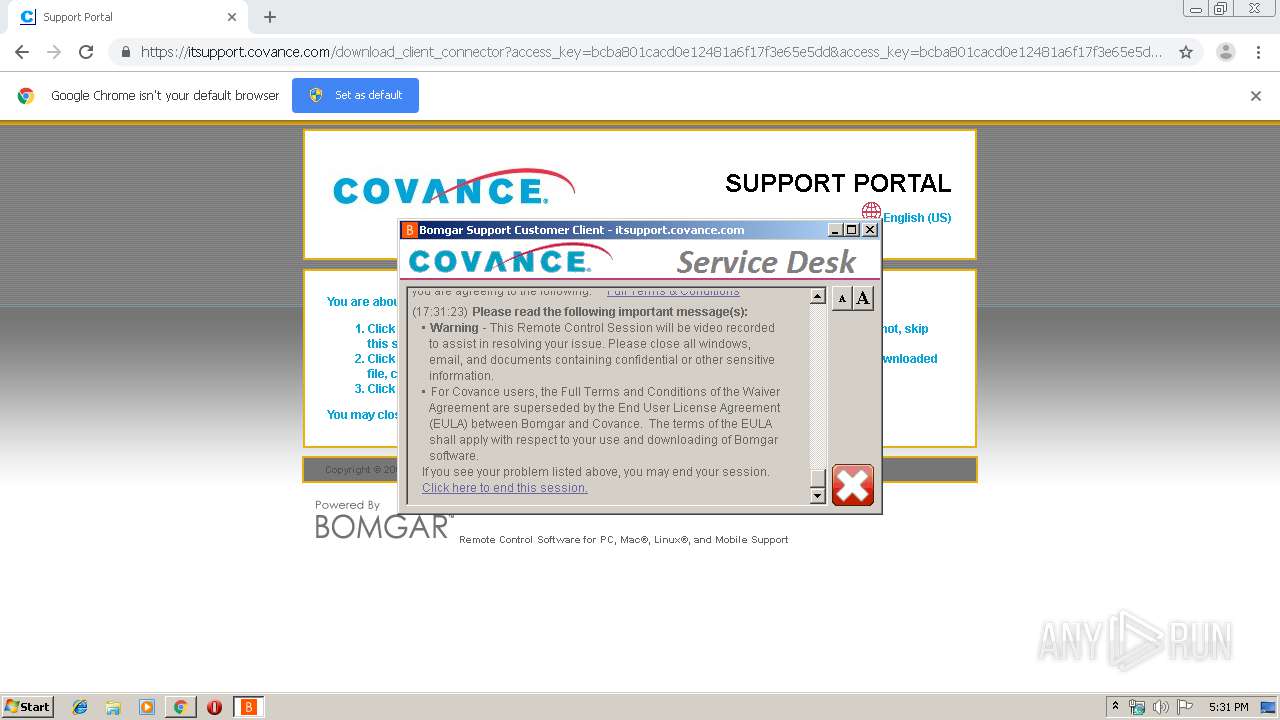
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2019, 16:30:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BA8012B4FF6EB6E6C89D92CE1628FDCB |
| SHA1: | 5AE8963262E0692AD7002B0880B927A35A777822 |
| SHA256: | A75BBA6BE96E27A5D2BB039ACBB1B0C65098768A1255A020CAB1885643C6CECE |
| SSDEEP: | 3:N8BBLGsALGAX8ORQSbxY:2HLGdGJ+HbxY |
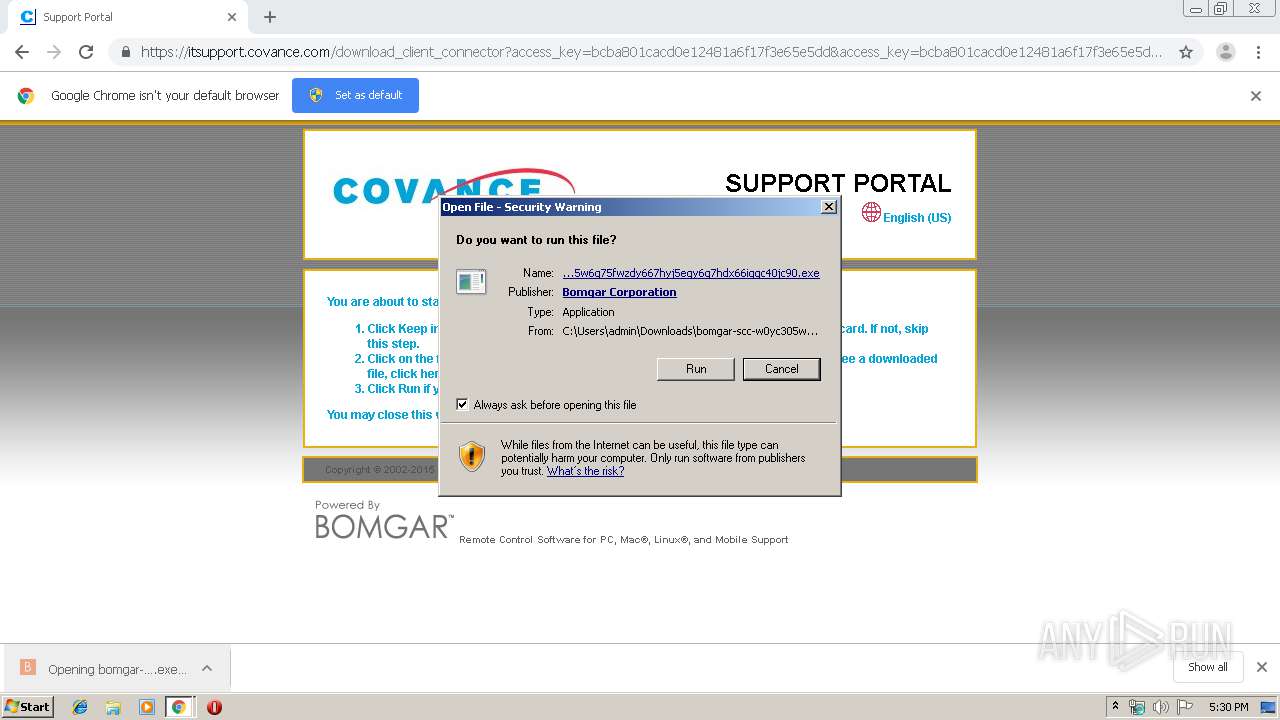
MALICIOUS
Application was dropped or rewritten from another process
- bomgar-scc-w0yc305w6g75fwzdy667hyj5egy6g7hdx66iggc40jc90.exe (PID: 3192)
- bomgar-scc.exe (PID: 2160)
- spinner.exe (PID: 3100)
- bomgar-scc.exe (PID: 3992)
- bomgar-scc.exe (PID: 2212)
- bomgar-scc.exe (PID: 2904)
- bomgar-scc.exe (PID: 2628)
- bomgar-scc.exe (PID: 2176)
- bomgar-scc.exe (PID: 2536)
Loads dropped or rewritten executable
- bomgar-scc-w0yc305w6g75fwzdy667hyj5egy6g7hdx66iggc40jc90.exe (PID: 3192)
Changes the autorun value in the registry
- bomgar-scc.exe (PID: 2212)
Loads the Task Scheduler COM API
- bomgar-scc.exe (PID: 2628)
Loads the Task Scheduler DLL interface
- bomgar-scc.exe (PID: 2628)
SUSPICIOUS
Creates files in the program directory
- bomgar-scc.exe (PID: 3992)
- bomgar-scc.exe (PID: 2212)
- bomgar-scc.exe (PID: 2628)
- bomgar-scc.exe (PID: 2904)
- bomgar-scc.exe (PID: 2176)
- bomgar-scc.exe (PID: 2160)
Executable content was dropped or overwritten
- bomgar-scc.exe (PID: 3992)
- chrome.exe (PID: 2220)
- chrome.exe (PID: 2872)
- bomgar-scc-w0yc305w6g75fwzdy667hyj5egy6g7hdx66iggc40jc90.exe (PID: 3192)
- bomgar-scc.exe (PID: 2212)
Starts CMD.EXE for commands execution
- bomgar-scc-w0yc305w6g75fwzdy667hyj5egy6g7hdx66iggc40jc90.exe (PID: 3192)
Starts itself from another location
- bomgar-scc.exe (PID: 3992)
Application launched itself
- bomgar-scc.exe (PID: 2212)
- bomgar-scc.exe (PID: 2628)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2872)
Connects to unusual port
- bomgar-scc.exe (PID: 2160)
Executed via Task Scheduler
- bomgar-scc.exe (PID: 2176)
INFO
Application launched itself
- chrome.exe (PID: 2872)
Reads Internet Cache Settings
- chrome.exe (PID: 2872)
Reads the hosts file
- chrome.exe (PID: 2220)
- chrome.exe (PID: 2872)
Reads Microsoft Office registry keys
- bomgar-scc.exe (PID: 2536)
Dropped object may contain Bitcoin addresses
- bomgar-scc.exe (PID: 2628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
33
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2056 | C:\Windows\system32\rstrui.exe | C:\Windows\system32\rstrui.exe | — | bomgar-scc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Windows System Restore Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2160 | C:\ProgramData\bomgar-scc-0x5d825bbf\bomgar-scc.exe -proxydetect | C:\ProgramData\bomgar-scc-0x5d825bbf\bomgar-scc.exe | bomgar-scc.exe | ||||||||||||
User: admin Company: Bomgar Integrity Level: MEDIUM Description: Bomgar Support Customer Client Exit code: 0 Version: 15.2.2 (59591) Modules
| |||||||||||||||
| 2176 | C:\ProgramData\bomgar-scc-0x5d825bbf\bomgar-scc.exe --cxn-factory-proxy-detect dfwpl2bgtrfc01.covance.com:443; 60 0 C:\ProgramData\proxy-1519.tmp | C:\ProgramData\bomgar-scc-0x5d825bbf\bomgar-scc.exe | taskeng.exe | ||||||||||||
User: admin Company: Bomgar Integrity Level: MEDIUM Description: Bomgar Support Customer Client Exit code: 0 Version: 15.2.2 (59591) Modules
| |||||||||||||||
| 2212 | C:\ProgramData\bomgar-scc-0x5d825bbf\bomgar-scc.exe C:\Users\admin\Downloads\bomgar-scc-w0yc305w6g75fwzdy667hyj5egy6g7hdx66iggc40jc90.exe -install2 C:\Users\admin\Downloads\bomgar-scc-w0yc305w6g75fwzdy667hyj5egy6g7hdx66iggc40jc90.exe C:\Users\admin\AppData\Local\Temp\nsyE546.tmpb\ C:\ProgramData\bomgar-scc-0x5d825bbf\ | C:\ProgramData\bomgar-scc-0x5d825bbf\bomgar-scc.exe | bomgar-scc.exe | ||||||||||||
User: admin Company: Bomgar Integrity Level: MEDIUM Description: Bomgar Support Customer Client Exit code: 0 Version: 15.2.2 (59591) Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=15221886263105775744 --mojo-platform-channel-handle=1516 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2148819416111765337 --mojo-platform-channel-handle=4724 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2400 | C:\Windows\regedit.exe | C:\Windows\regedit.exe | — | bomgar-scc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8523534288801747870 --mojo-platform-channel-handle=3812 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2536 | C:\ProgramData\bomgar-scc-0x5d825bbf\bomgar-scc.exe -exec enum_cp 1525812 | C:\ProgramData\bomgar-scc-0x5d825bbf\bomgar-scc.exe | — | bomgar-scc.exe | |||||||||||
User: admin Company: Bomgar Integrity Level: MEDIUM Description: Bomgar Support Customer Client Exit code: 0 Version: 15.2.2 (59591) Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7965243908479344513 --mojo-platform-channel-handle=4648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 650
Read events
1 478
Write events
167
Delete events
5
Modification events
| (PID) Process: | (2872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2872-13213297834804000 |
Value: 259 | |||
| (PID) Process: | (2872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2872) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
32
Suspicious files
18
Text files
404
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\544667de-7d77-443c-adcb-8644d40696a3.tmp | — | |
MD5:— | SHA256:— | |||
| 2872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF169d2f.TMP | text | |
MD5:— | SHA256:— | |||
| 2872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169c44.TMP | text | |
MD5:— | SHA256:— | |||
| 2872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169c25.TMP | text | |
MD5:— | SHA256:— | |||
| 2872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
26
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2628 | bomgar-scc.exe | GET | — | 162.253.7.40:80 | http://license.bomgar.com/?c=itsupport&v=15.2.2&a=x86&g=208.66.166.162&i=scc&l=en-us&O=336724225&o=6.1.7601.1&r=59591&s=453232&t=Windows%207%20Professional%20x86 | US | — | — | unknown |
2220 | chrome.exe | GET | 200 | 84.15.64.141:80 | http://r2---sn-cpux-8ov6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.206.166.82&mm=28&mn=sn-cpux-8ov6&ms=nvh&mt=1568823461&mv=u&mvi=1&pl=22&shardbypass=yes | LT | crx | 862 Kb | whitelisted |
2220 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2220 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 208.66.166.162:443 | itsupport.covance.com | COVANCE INC | US | unknown |
2220 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 172.217.16.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 172.217.22.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 216.58.208.46:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 84.15.64.141:80 | r2---sn-cpux-8ov6.gvt1.com | UAB Bite Lietuva | LT | whitelisted |
2220 | chrome.exe | 216.58.207.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
itsupport.covance.com |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
r2---sn-cpux-8ov6.gvt1.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
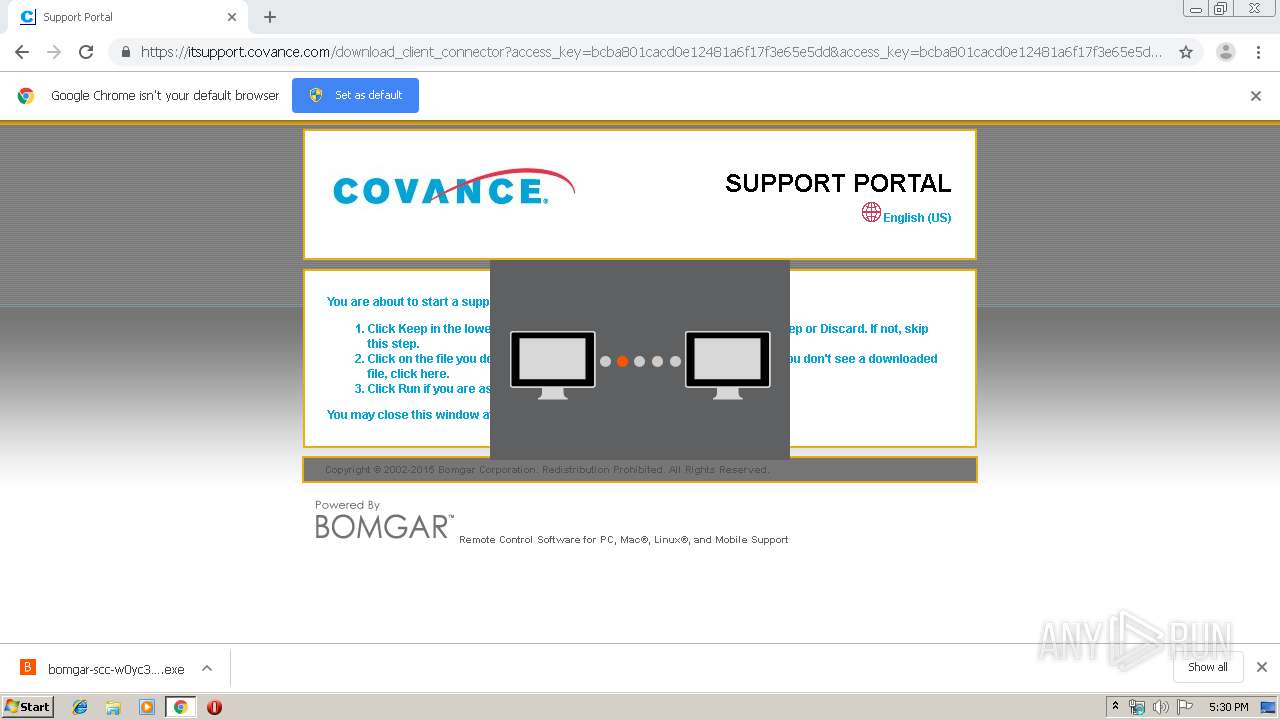
spinner.exe | SPN( c30):>CMainWindow::CMainWindow
|
spinner.exe | SPN( c30):image C:\Users\admin\AppData\Local\Temp\nsyE546.tmpspinner-1803031462\spinner-1.bmp
|
spinner.exe | SPN( c30):image C:\Users\admin\AppData\Local\Temp\nsyE546.tmpspinner-1803031462\spinner-2.bmp
|
spinner.exe | SPN( c30):image C:\Users\admin\AppData\Local\Temp\nsyE546.tmpspinner-1803031462\spinner-3.bmp
|
spinner.exe | SPN( c30):image C:\Users\admin\AppData\Local\Temp\nsyE546.tmpspinner-1803031462\spinner-4.bmp
|
spinner.exe | SPN( c30):image C:\Users\admin\AppData\Local\Temp\nsyE546.tmpspinner-1803031462\spinner-5.bmp
|
spinner.exe | SPN( c30):>CMainWindow::Create
|
spinner.exe | SPN( c30):>CMainWindow::Create
|
spinner.exe | SPN( c30):>CMainWindow::OnCreate
|
spinner.exe | SPN( c30):<CMainWindow::OnCreate
|