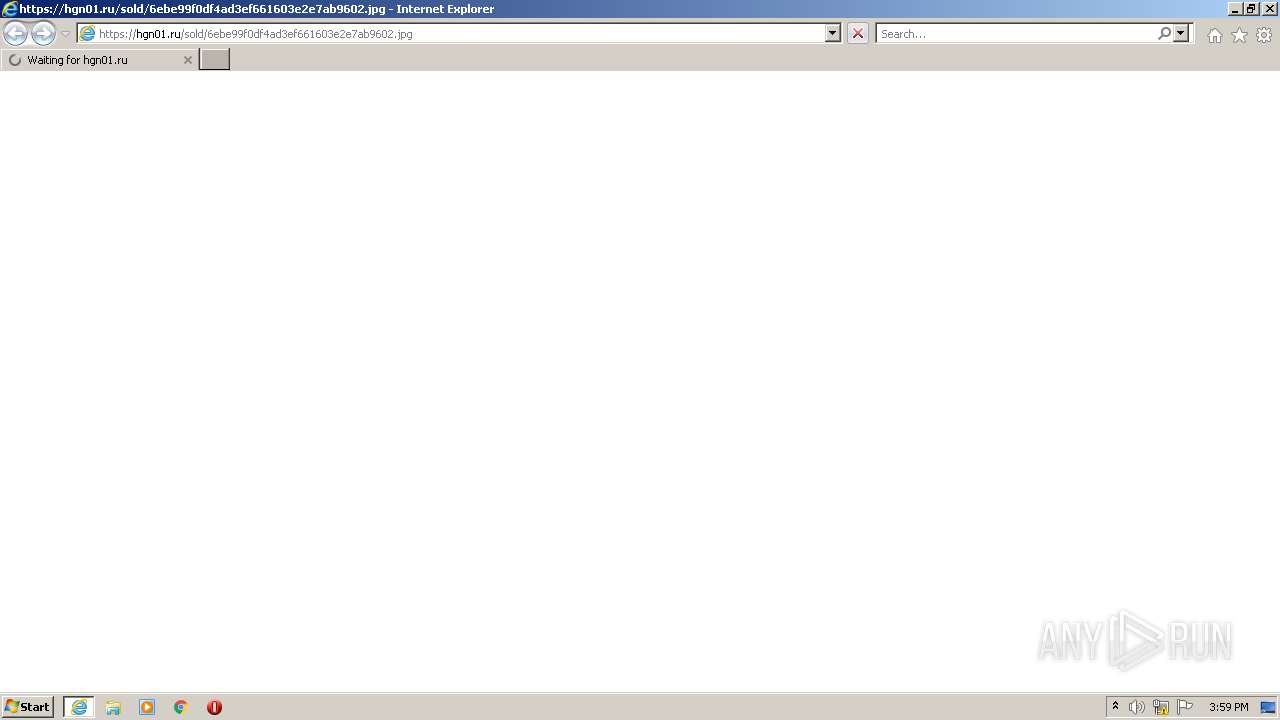
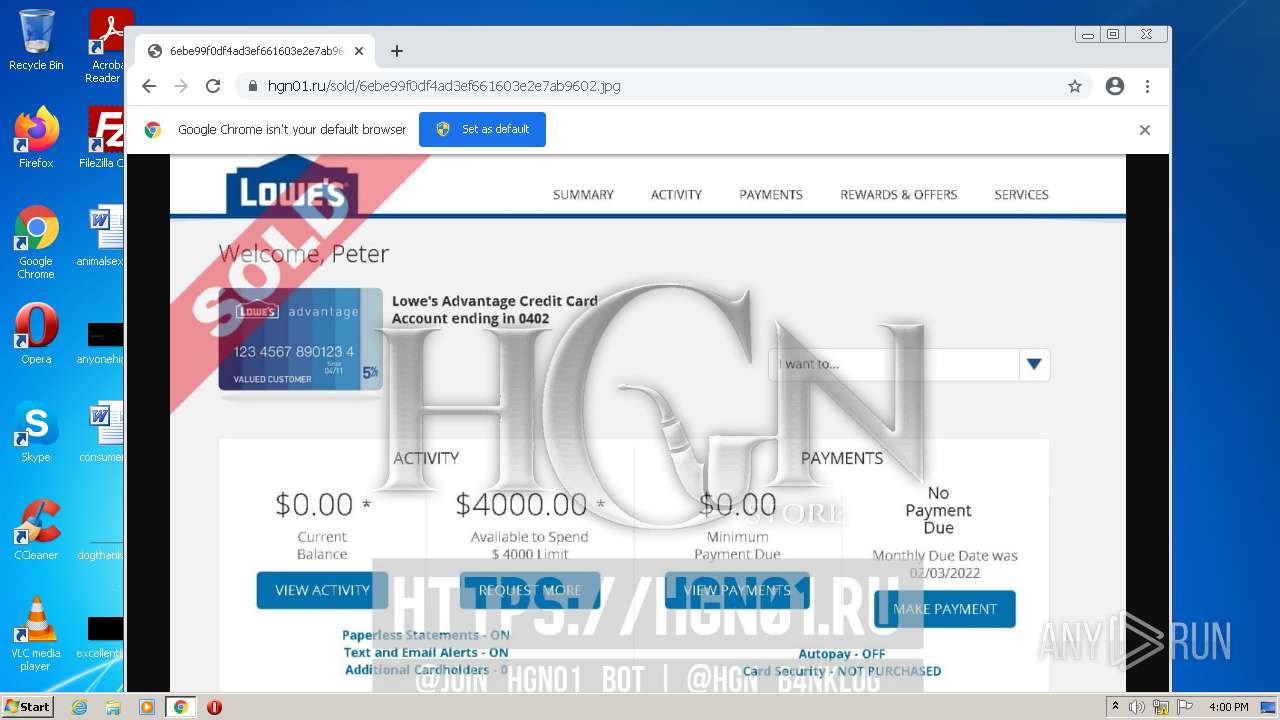
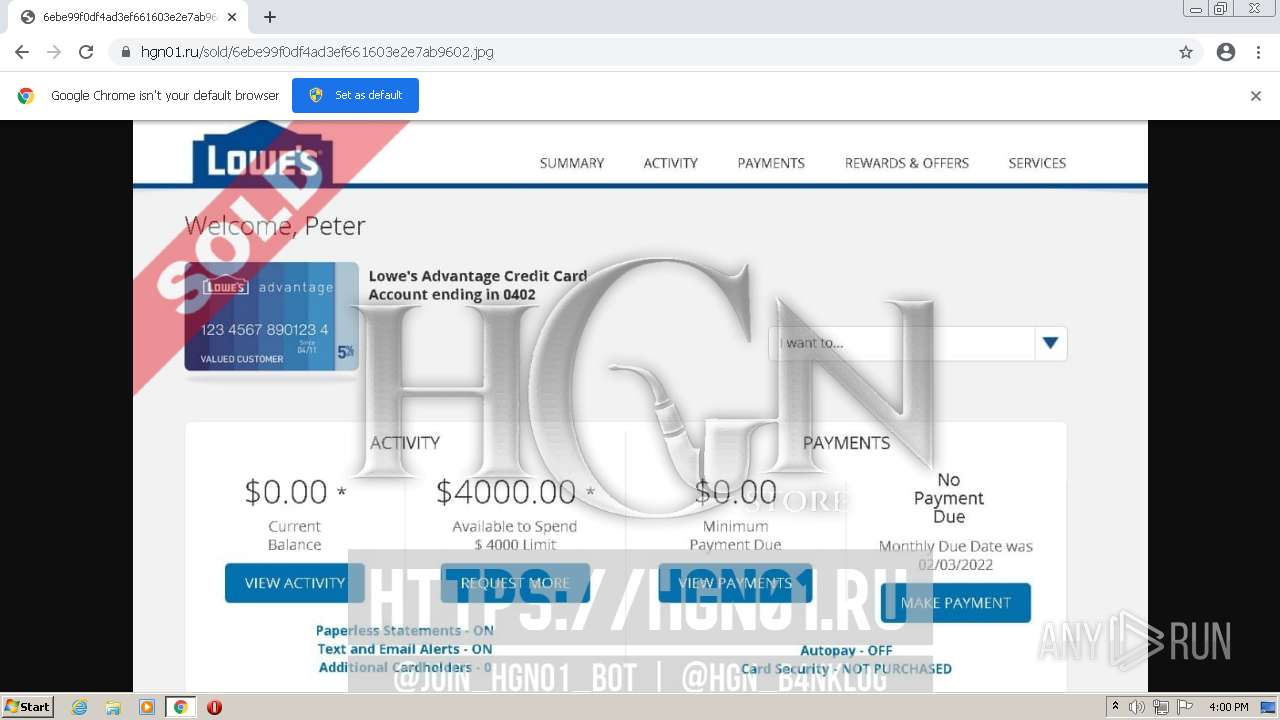
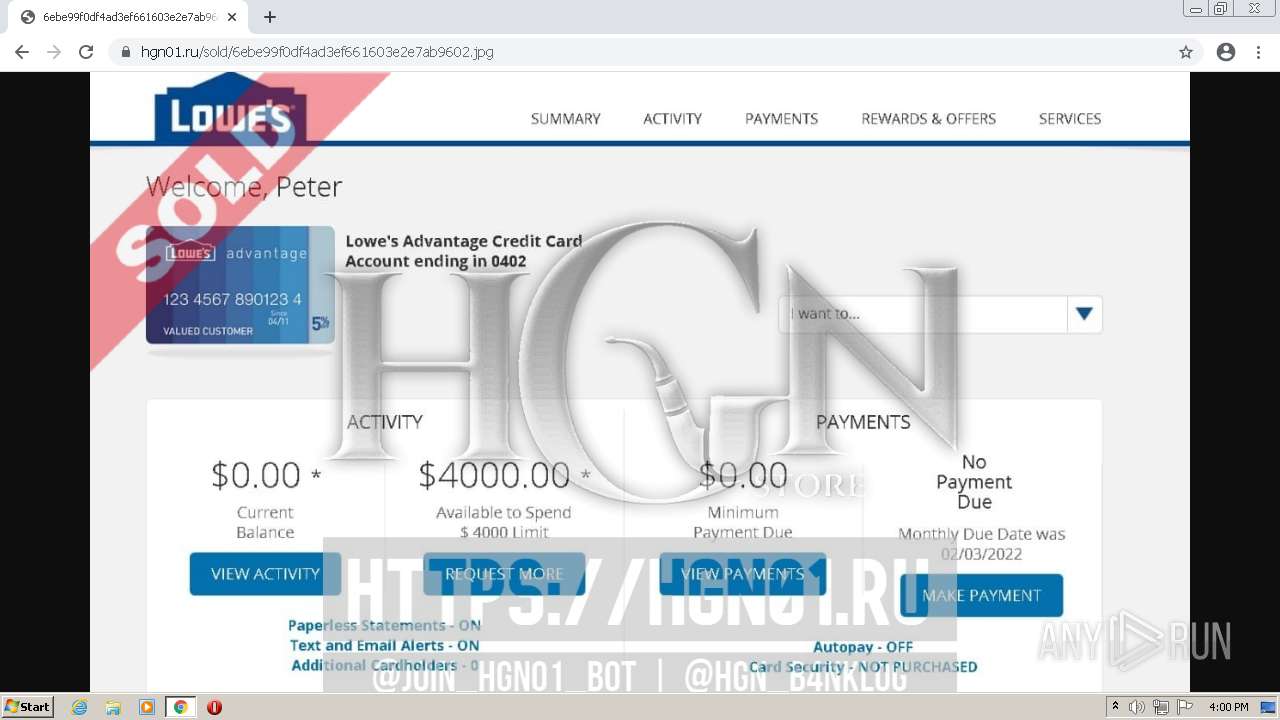
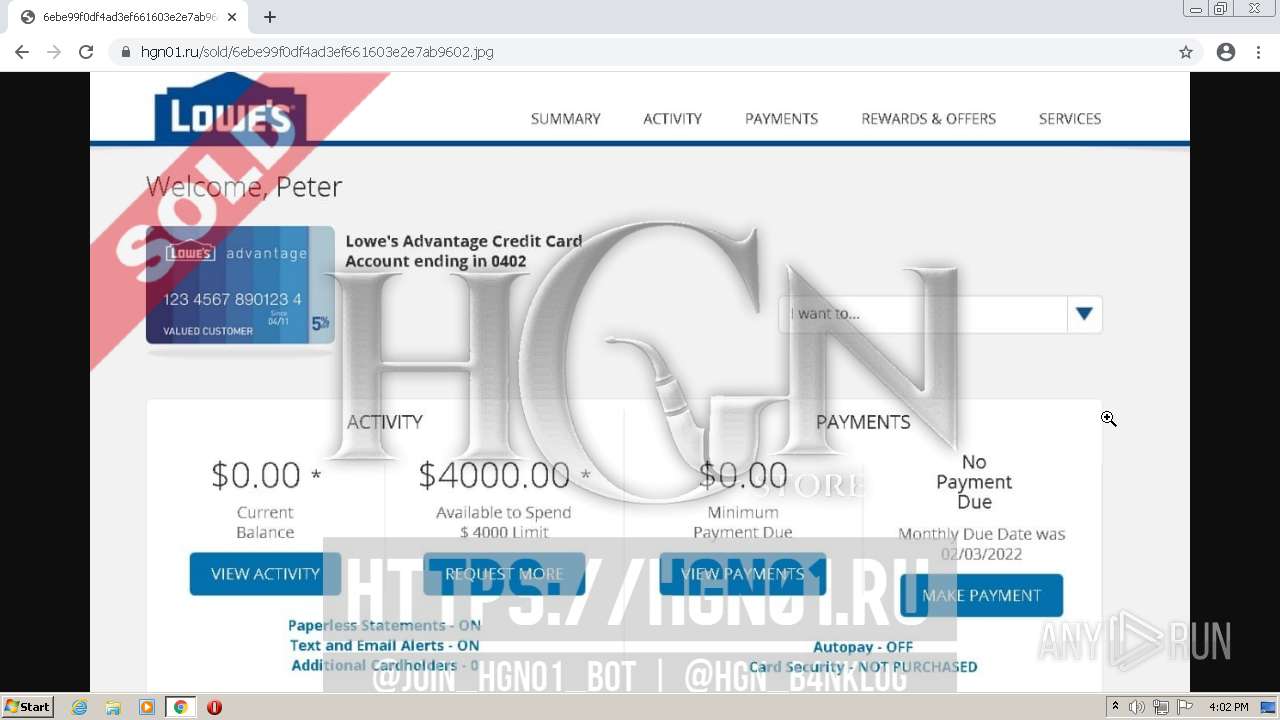
| URL: | https://hgn01.ru/sold/6ebe99f0df4ad3ef661603e2e7ab9602.jpg |
| Full analysis: | https://app.any.run/tasks/f41068e5-4337-482b-90ec-04c4ca482f71 |
| Verdict: | Malicious activity |
| Analysis date: | February 08, 2022, 15:59:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 06645D17EB0F1EAFDA242706CD5DC4A3 |
| SHA1: | 8F33094BFDD82263435BF158366F913D4F908CAC |
| SHA256: | A74BCCF1144D91D9679B63CC3B356A7340990B9EF47892F923C160DAE027317E |
| SSDEEP: | 3:N8+LVSTBKMyrNLAP+VWAXA3CVrVCn:2+hSYBBLA9CVron |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2120)
Modifies files in Chrome extension folder
- chrome.exe (PID: 892)
INFO
Checks supported languages
- iexplore.exe (PID: 1244)
- iexplore.exe (PID: 2120)
- chrome.exe (PID: 892)
- chrome.exe (PID: 1020)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 4060)
- chrome.exe (PID: 3544)
- chrome.exe (PID: 3824)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 528)
- chrome.exe (PID: 1372)
- chrome.exe (PID: 2416)
- chrome.exe (PID: 2356)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 292)
- chrome.exe (PID: 1476)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 432)
- chrome.exe (PID: 1968)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 3452)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3528)
- chrome.exe (PID: 3876)
- chrome.exe (PID: 900)
- chrome.exe (PID: 3196)
Reads the computer name
- iexplore.exe (PID: 1244)
- iexplore.exe (PID: 2120)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 892)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2356)
- chrome.exe (PID: 528)
- chrome.exe (PID: 292)
- chrome.exe (PID: 432)
- chrome.exe (PID: 3184)
Application launched itself
- iexplore.exe (PID: 1244)
- chrome.exe (PID: 892)
Changes internet zones settings
- iexplore.exe (PID: 1244)
Checks Windows Trust Settings
- iexplore.exe (PID: 1244)
Reads settings of System Certificates
- iexplore.exe (PID: 1244)
- chrome.exe (PID: 3004)
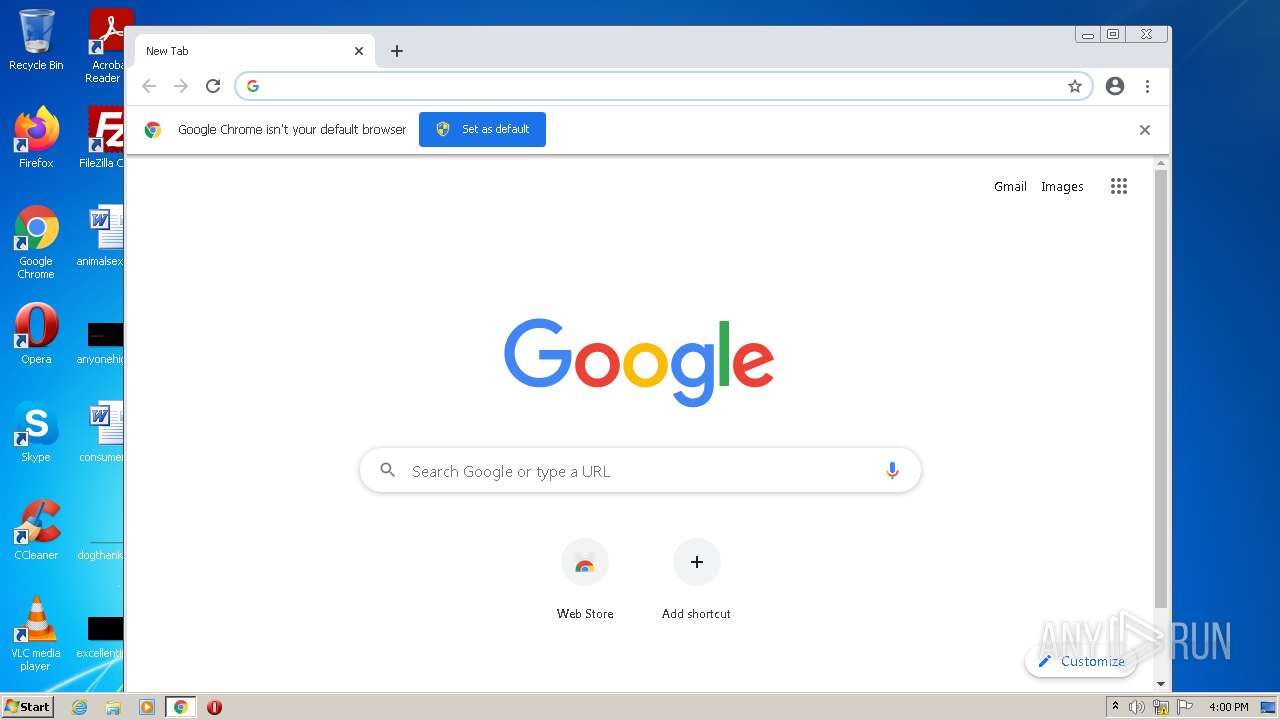
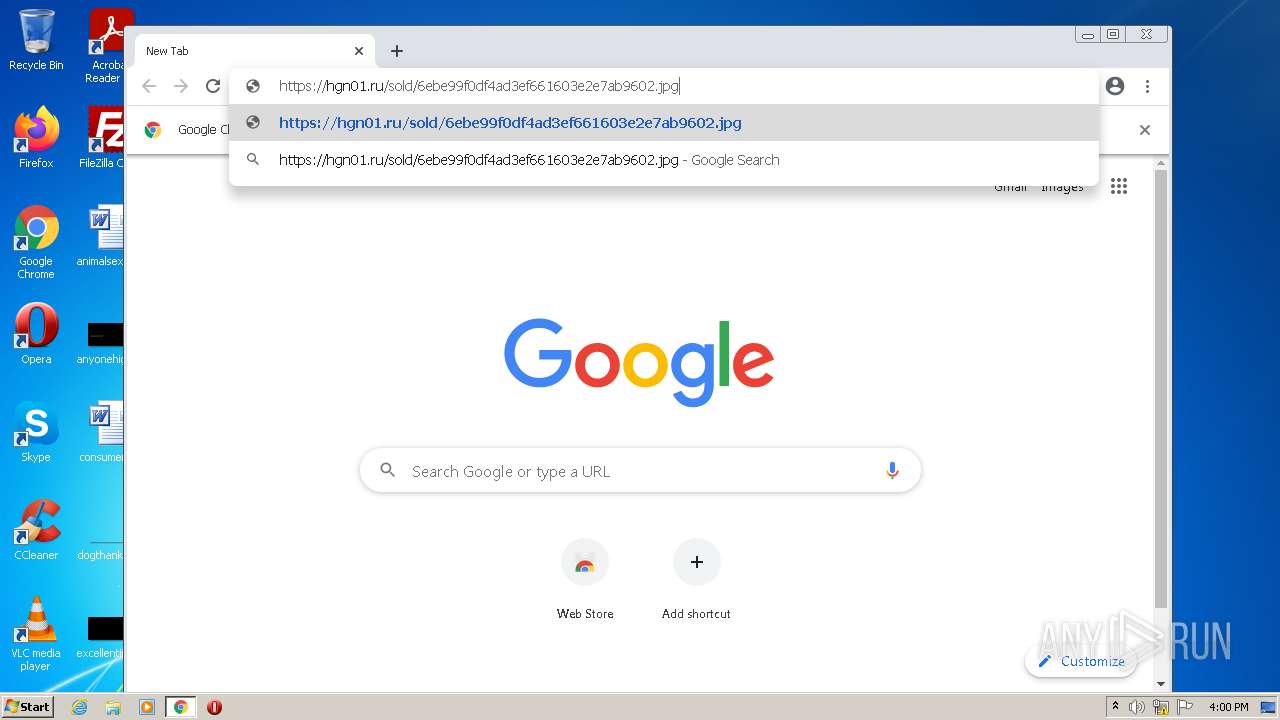
Manual execution by user
- chrome.exe (PID: 892)
Reads the hosts file
- chrome.exe (PID: 892)
- chrome.exe (PID: 3004)
Reads internet explorer settings
- iexplore.exe (PID: 2120)
Reads the date of Windows installation
- iexplore.exe (PID: 1244)
- chrome.exe (PID: 292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,14859614038525453202,17242982891423411900,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1704 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,14859614038525453202,17242982891423411900,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1748 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,14859614038525453202,17242982891423411900,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2128 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,14859614038525453202,17242982891423411900,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1712 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6edcd988,0x6edcd998,0x6edcd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1244 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://hgn01.ru/sold/6ebe99f0df4ad3ef661603e2e7ab9602.jpg" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
| 1372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,14859614038525453202,17242982891423411900,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3412 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,14859614038525453202,17242982891423411900,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=968 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,14859614038525453202,17242982891423411900,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
167
Text files
152
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6202937F-37C.pma | — | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5003BE94052EE047.TMP | gmc | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{26660CE4-88F8-11EC-9D0A-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{1CF47C6A-88F8-11EC-9D0A-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF6773A25985BB977.TMP | gmc | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA2D66F160D0A6AB9.TMP | gmc | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{26660CE3-88F8-11EC-9D0A-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA98BC6C14A07EC48.TMP | gmc | |
MD5:7362BD84D810EE0601E526AD84AEA0B5 | SHA256:D516E4DBBAFD5C7BE0DC2FCC8D769EB6E4FBD03BC6D0D465CF4BB73631AEF4E4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
41
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
872 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
1244 | iexplore.exe | GET | — | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e5f0d08207194a58 | US | — | — | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 21.1 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 18.6 Kb | whitelisted |
1244 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 38.7 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 179 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 9.93 Kb | whitelisted |
872 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acswg5tbkr2ithrql6kjeh6vvwrq_2022.1.24.1201/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.1.24.1201_all_oa3ppuxckzsaqpp445iqxhz4e4.crx3 | US | crx | 9.39 Kb | whitelisted |
872 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/insvgwbvfcm4727ldhaxkroq7u_2771/jflookgnkcckhobaglndicnbbgbonegd_2771_all_adxelikapyugbhji3y7xhxhjkwgq.crx3 | US | crx | 9.39 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1244 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1244 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3004 | chrome.exe | 142.250.185.100:443 | www.google.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 142.250.184.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 142.250.185.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 142.250.184.237:443 | accounts.google.com | Google Inc. | US | suspicious |
3004 | chrome.exe | 142.250.185.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 142.250.185.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 142.250.185.206:443 | apis.google.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 142.250.185.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hgn01.ru |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |