| File name: | Black Friday.docx |
| Full analysis: | https://app.any.run/tasks/35c236a2-6479-41a9-b412-72cf7109b413 |
| Verdict: | Malicious activity |
| Analysis date: | December 09, 2020, 15:31:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | D2C54126B71A2439DFC384930580786C |
| SHA1: | 7BB6EEBA638AA0EFCC0C29EBD4D8BA1E5A0FDA7E |
| SHA256: | A7447DB99BA60C2F7BFD9E9BCFADFB05A4FC0EA214450B76EA85D386DB1F727B |
| SSDEEP: | 768:yO1x/Hz3OxLC8HH13Ai+Gk2mTBgTHoNMYwF2kUqZg3:yO1xfzexN1w92Yg84W |
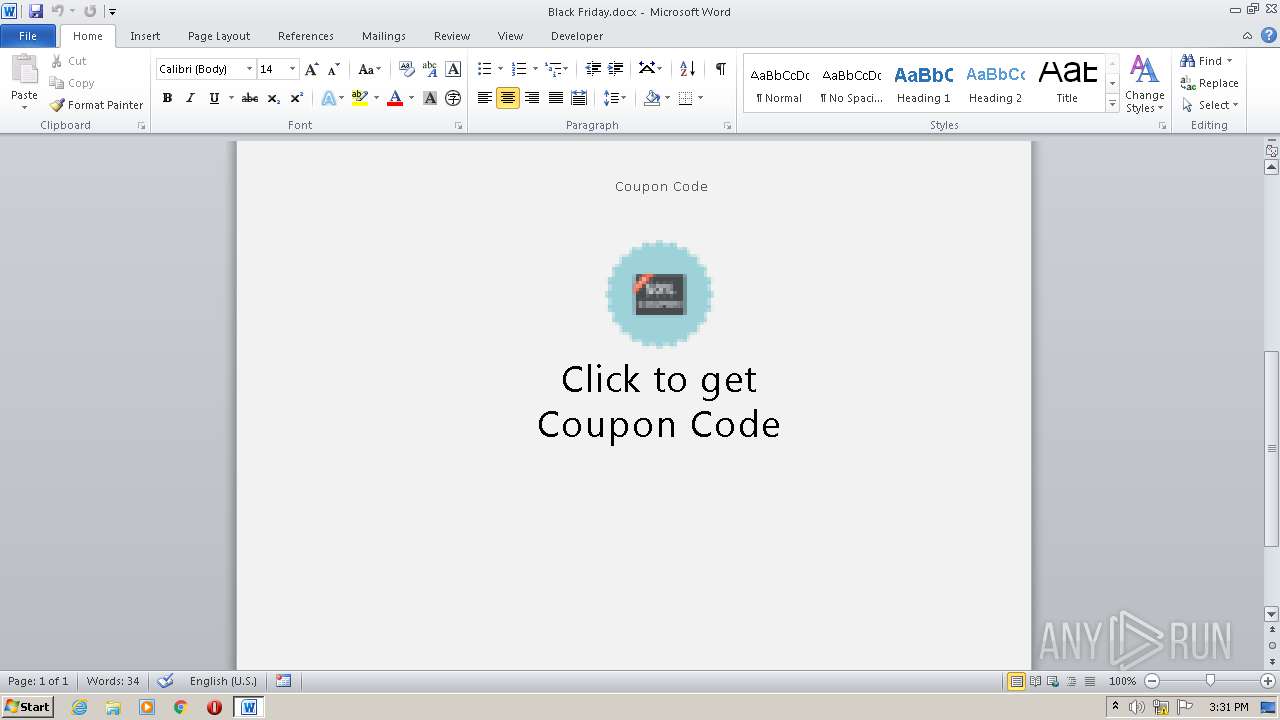
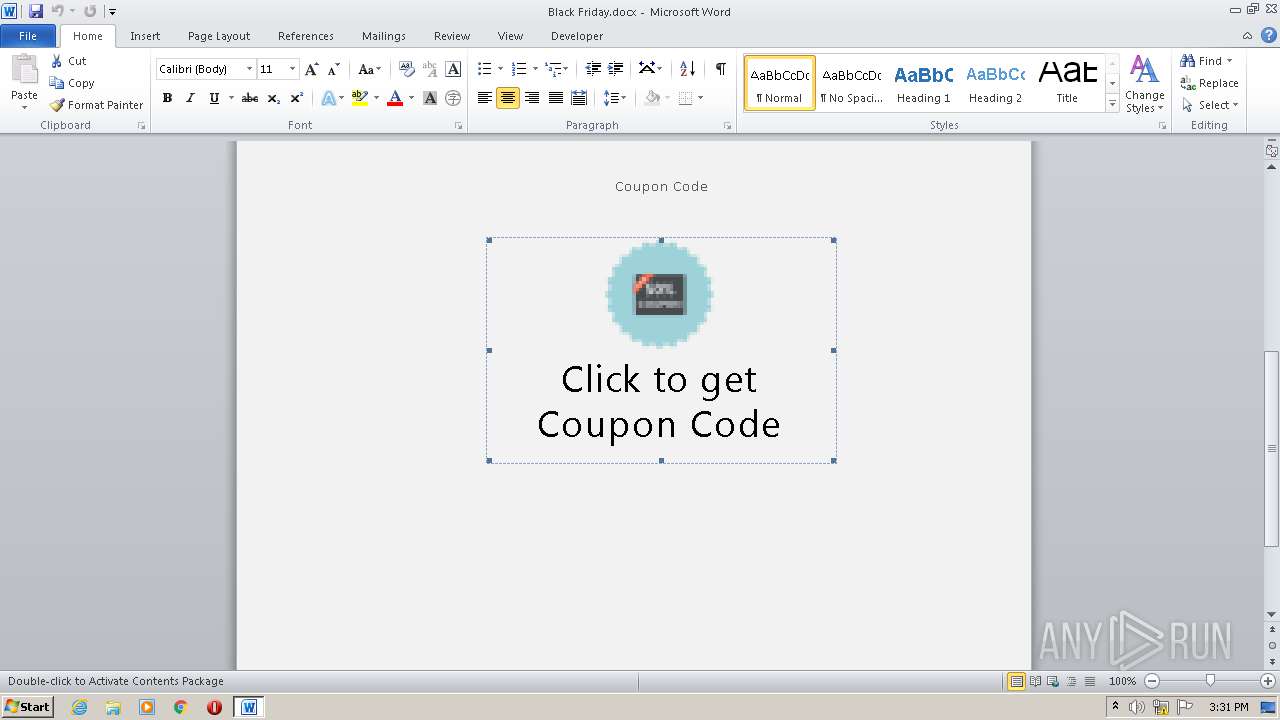
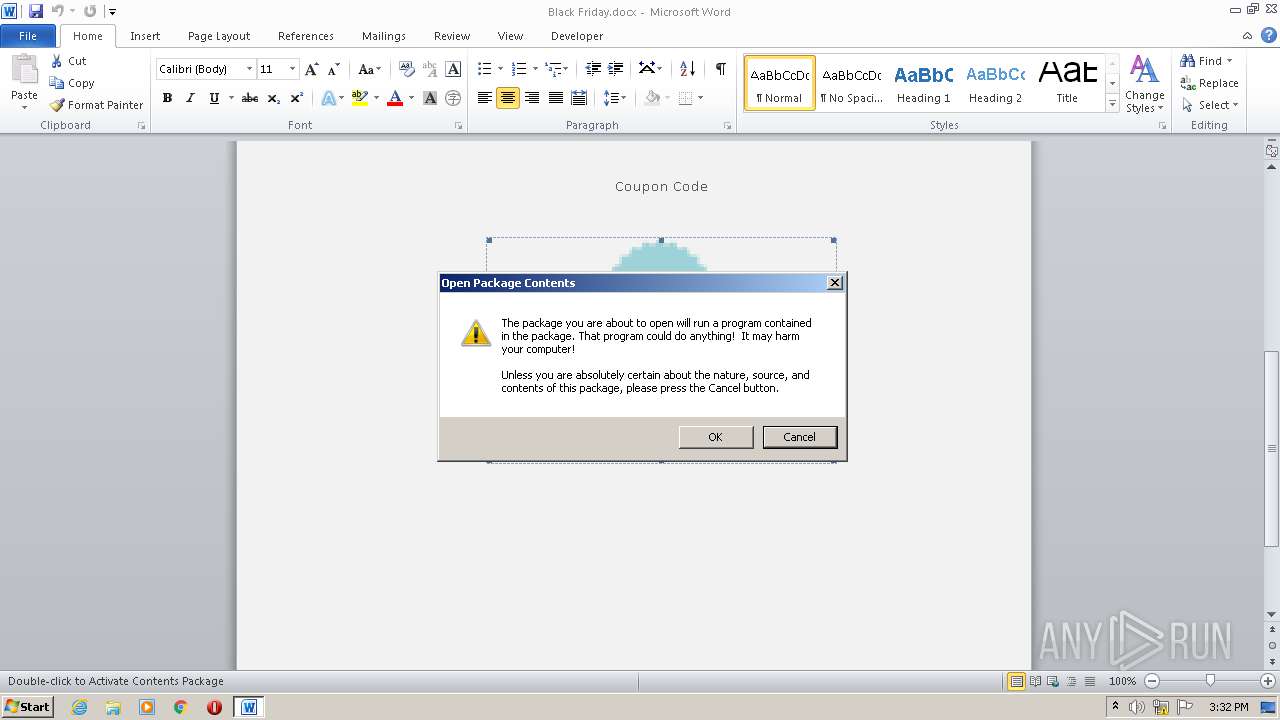
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2708)
Uses Task Scheduler to run other applications
- WScript.exe (PID: 376)
Executes scripts
- WINWORD.EXE (PID: 2708)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2728)
SUSPICIOUS
No suspicious indicators.INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2708)
Creates files in the user directory
- WINWORD.EXE (PID: 2708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xd7a58a60 |
| ZipCompressedSize: | 383 |
| ZipUncompressedSize: | 1511 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal |
|---|---|
| TotalEditTime: | 17 minutes |
| Pages: | 1 |
| Words: | 34 |
| Characters: | 199 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 232 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | Пользователь Windows |
| RevisionNumber: | 15 |
| CreateDate: | 2017:11:27 21:28:00Z |
| ModifyDate: | 2017:12:14 18:47:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | Пользователь Windows |
| Description: | - |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
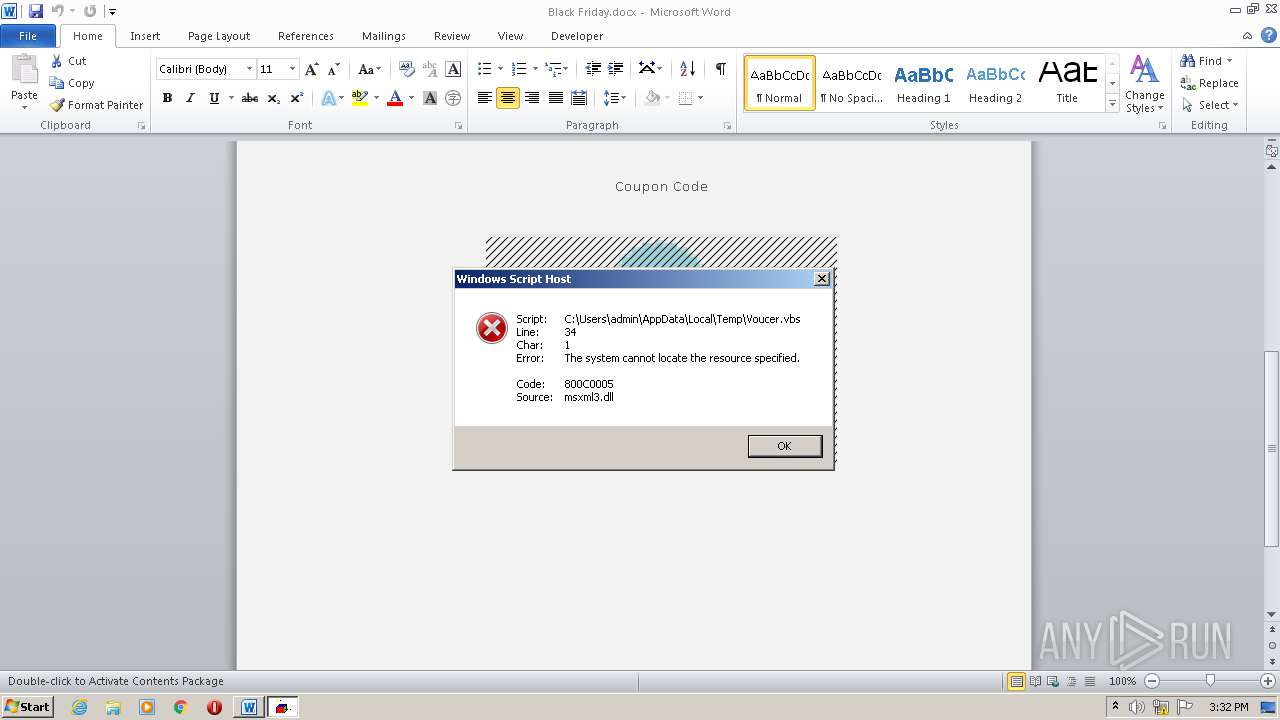
| 376 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Voucer.vbs" | C:\Windows\System32\WScript.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Black Friday.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2728 | "C:\Windows\System32\schtasks.exe" /create /tn Cclenears /SC HOURLY /MO 3 /tr "C:\Users\admin\AppData\Roaming\sys.exe" | C:\Windows\System32\schtasks.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 043
Read events
984
Write events
923
Delete events
136
Modification events
| (PID) Process: | (2708) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | $-; |
Value: 242D3B00940A0000010000000000000000000000 | |||
| (PID) Process: | (2708) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2708) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2708) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2708) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2708) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2708) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2708) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2708) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2708) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD184.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2708 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ack Friday.docx | pgc | |
MD5:— | SHA256:— | |||
| 2708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Voucer.vbs | text | |
MD5:BBB378AEC999760C29F973B32B252534 | SHA256:F67A2DE79ED8B4DA056619DC29E16824478EE028EFB86F53AAA94536F77EF742 | |||
| 2708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\70C0390F.emf | emf | |
MD5:FB813ED34231B6DE535CB1D3222B5656 | SHA256:A98E291138500445FC9829AA24AE87F1EDF056947321F7023F7B67F924F049F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
forum.cryptopia.gdn |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gdn Domain |