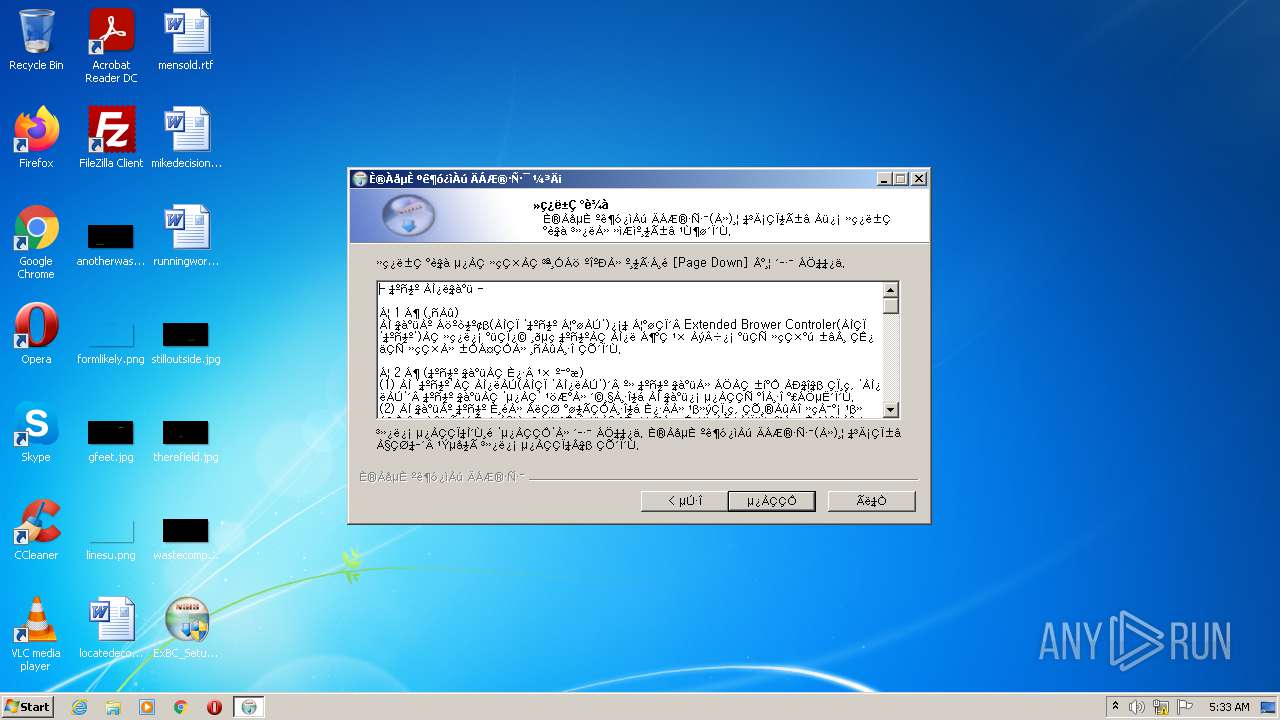
| File name: | ExBC_Setup.exe |
| Full analysis: | https://app.any.run/tasks/889f8da9-5c93-4af2-90b1-eda2c8b70fa5 |
| Verdict: | Malicious activity |
| Analysis date: | September 22, 2021, 04:33:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 8005C2A3EF8EC53EA2E88C0E47E03D47 |
| SHA1: | EB9B2CF9382058965D77E4AB7CA9746E0EFBB525 |
| SHA256: | A73C1CC1696C8749D34C3F9E906A6270A7F566C6435358B664CDD1BBF4FC9EFE |
| SSDEEP: | 98304:tv8xB8/sb/kABDOquug2T8V55K7hYU/57x+qWk:BkBksb/bBDrDg2T8VbKNt6qV |
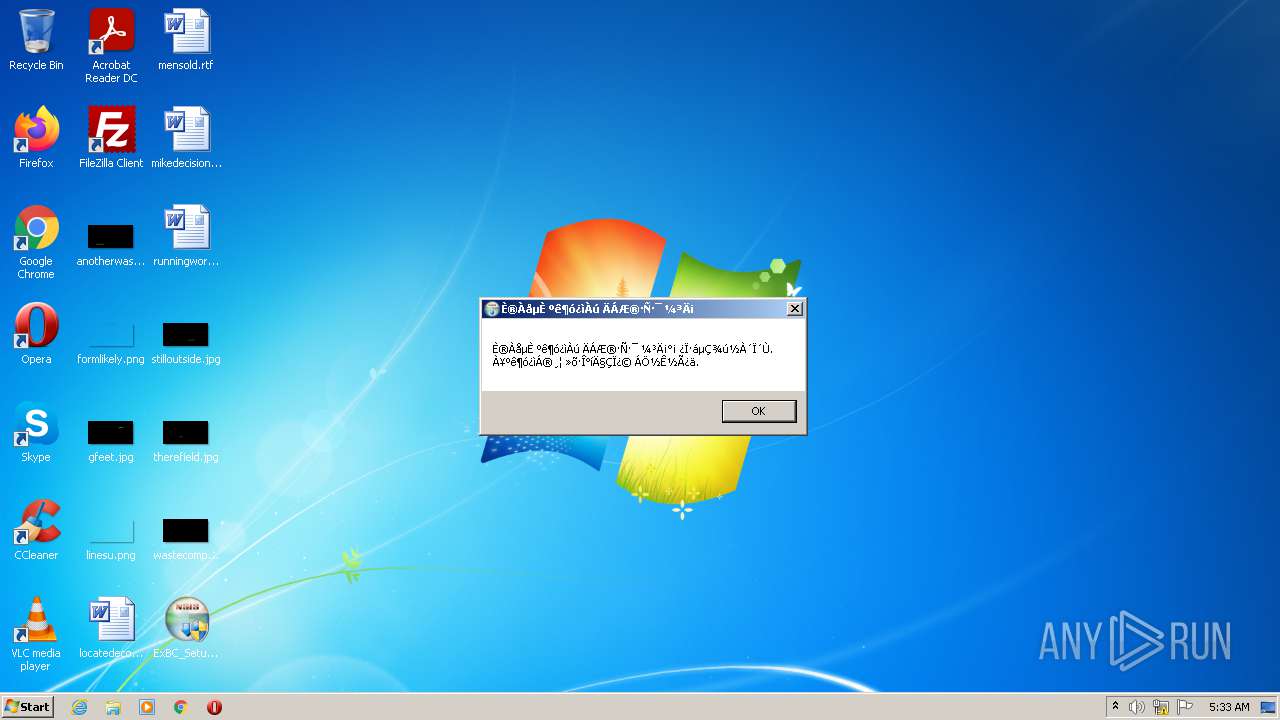
MALICIOUS
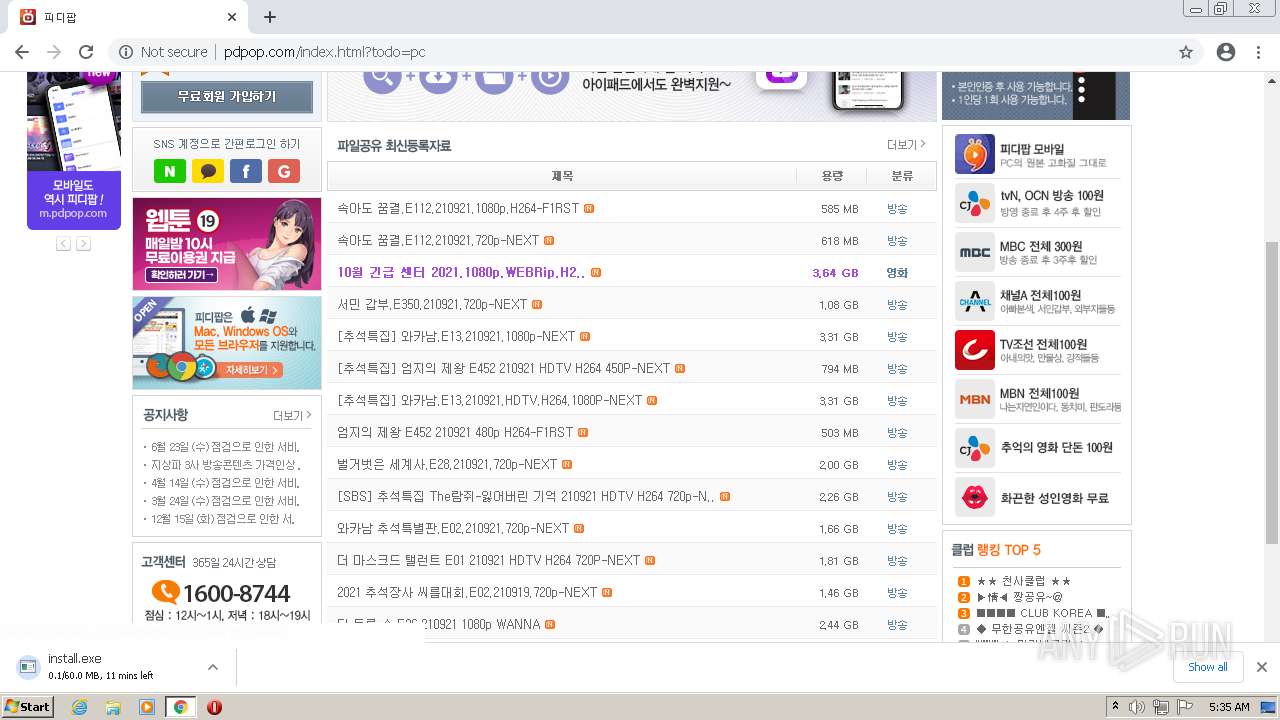
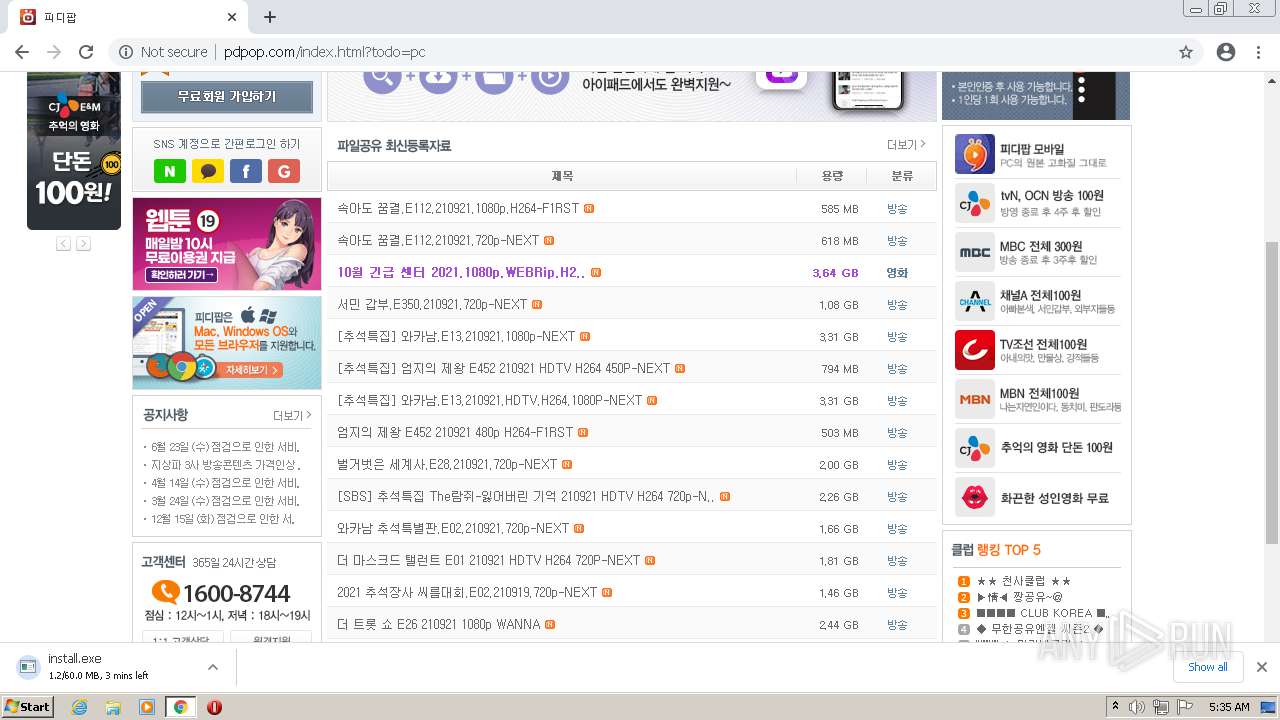
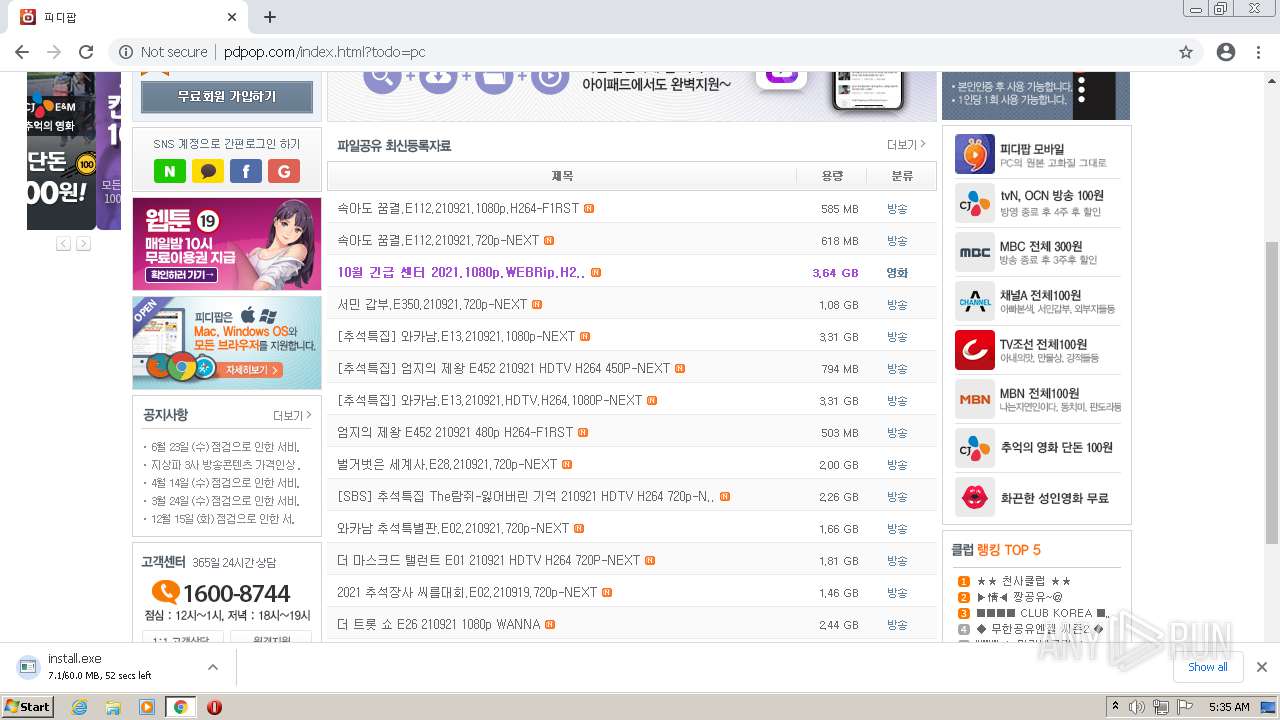
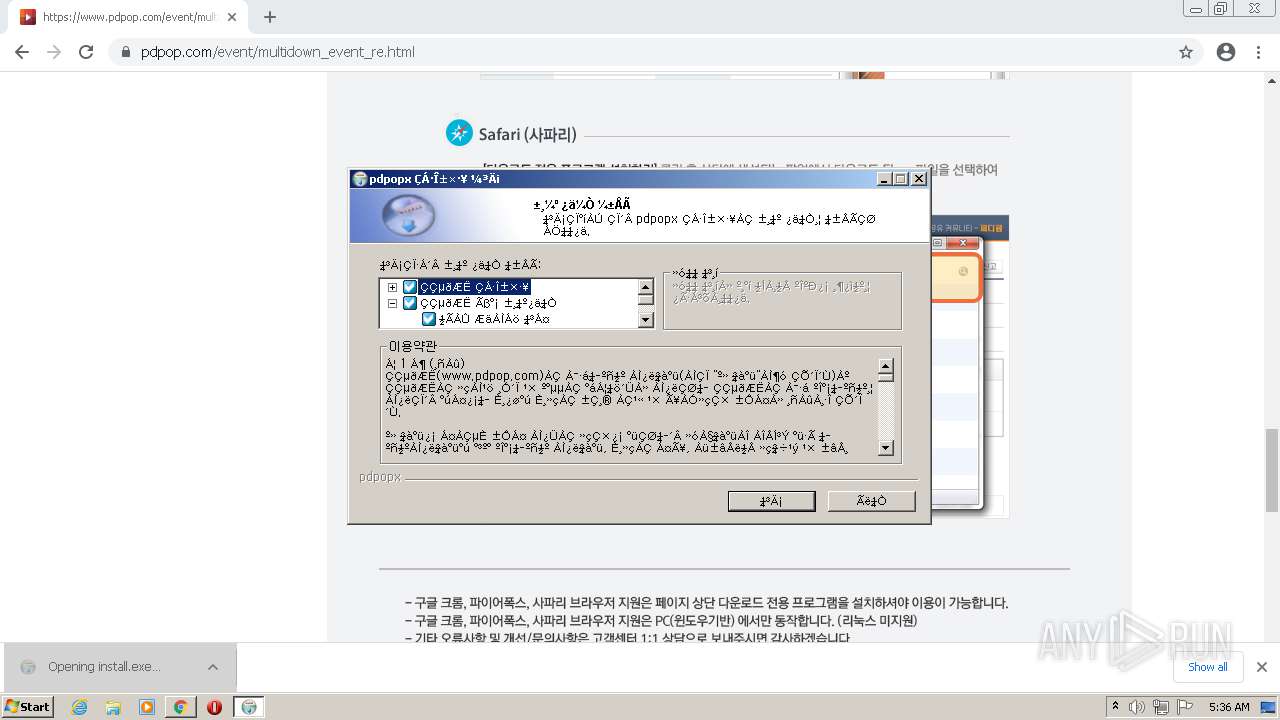
Drops executable file immediately after starts
- ExBC_Setup.exe (PID: 3136)
- install.exe (PID: 3784)
- CCDNService_Setup.exe (PID: 2512)
- ExBC_Setup.exe (PID: 2116)
- chrome.exe (PID: 2228)
Loads dropped or rewritten executable
- ExBC_Setup.exe (PID: 3136)
- install.exe (PID: 3784)
- CCDNService.exe (PID: 3664)
- CCDNService_Setup.exe (PID: 2512)
- CCDNService.exe (PID: 2672)
- ExBC_Setup.exe (PID: 2116)
Application was dropped or rewritten from another process
- ExBCSvc.exe (PID: 1624)
- ExBCSvc.exe (PID: 3676)
- install.exe (PID: 3784)
- install.exe (PID: 3868)
- CCDNService_Setup.exe (PID: 2512)
- CCDNService.exe (PID: 3664)
- CCDNService.exe (PID: 2672)
- ExBCSvc.exe (PID: 2732)
- ExBCSvc.exe (PID: 888)
- ExBCSvc.exe (PID: 3576)
SUSPICIOUS
Executable content was dropped or overwritten
- ExBC_Setup.exe (PID: 3136)
- chrome.exe (PID: 2664)
- install.exe (PID: 3784)
- CCDNService_Setup.exe (PID: 2512)
- ExBC_Setup.exe (PID: 2116)
- chrome.exe (PID: 2228)
Reads the computer name
- ExBC_Setup.exe (PID: 3136)
- ExBCSvc.exe (PID: 3676)
- ExBCSvc.exe (PID: 1624)
- install.exe (PID: 3784)
- CCDNService_Setup.exe (PID: 2512)
- CCDNService.exe (PID: 3664)
- CCDNService.exe (PID: 2672)
- ExBC_Setup.exe (PID: 2116)
- ExBCSvc.exe (PID: 888)
- ExBCSvc.exe (PID: 3576)
- ExBCSvc.exe (PID: 2732)
Drops a file that was compiled in debug mode
- ExBC_Setup.exe (PID: 3136)
- install.exe (PID: 3784)
- CCDNService_Setup.exe (PID: 2512)
- ExBC_Setup.exe (PID: 2116)
- chrome.exe (PID: 2228)
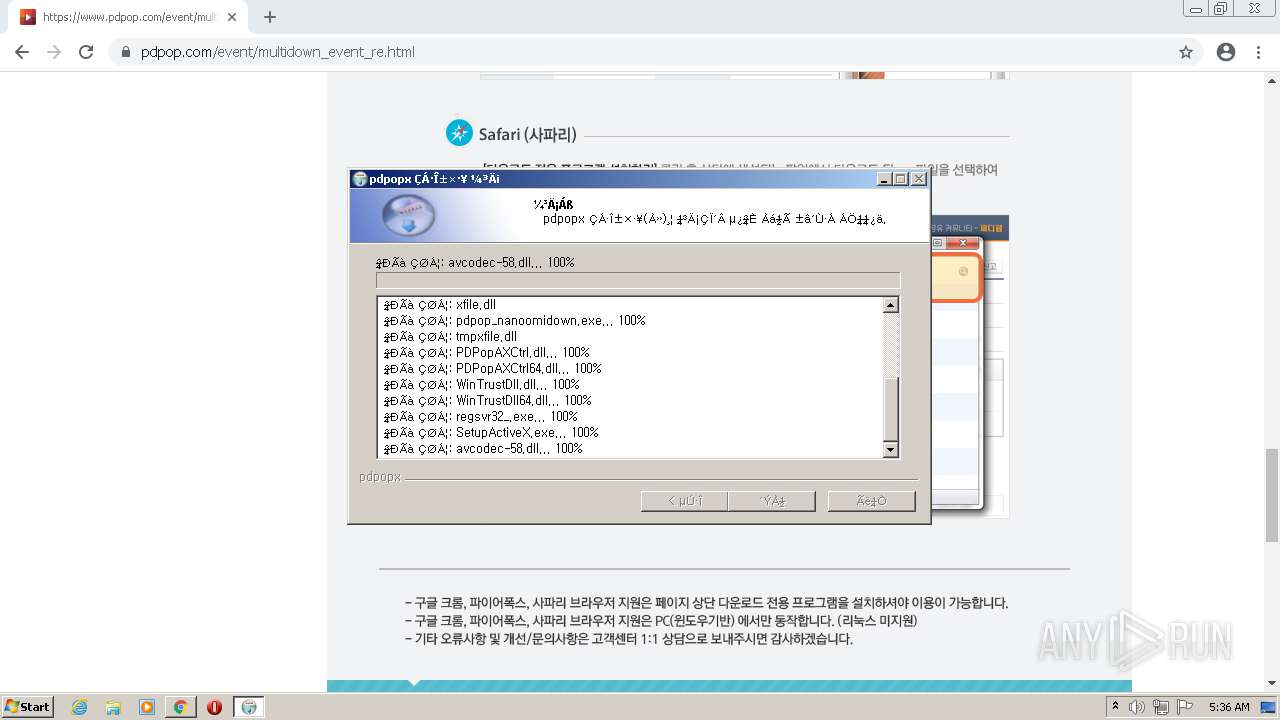
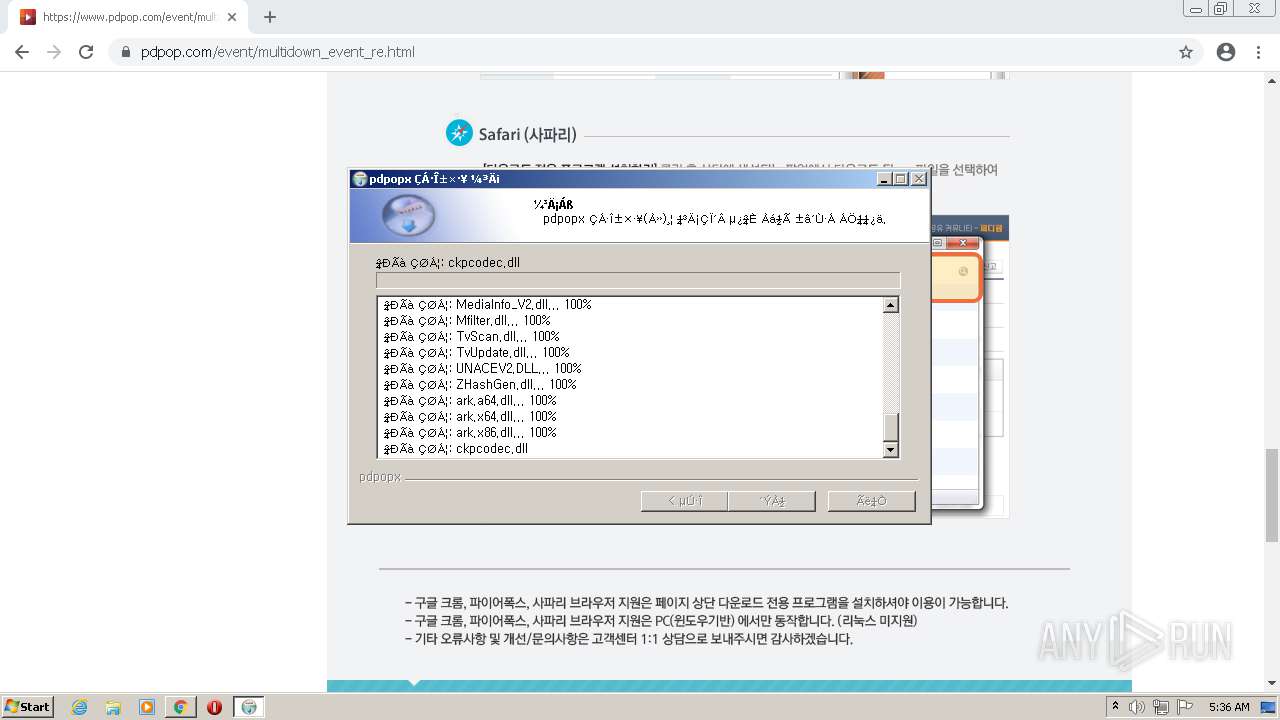
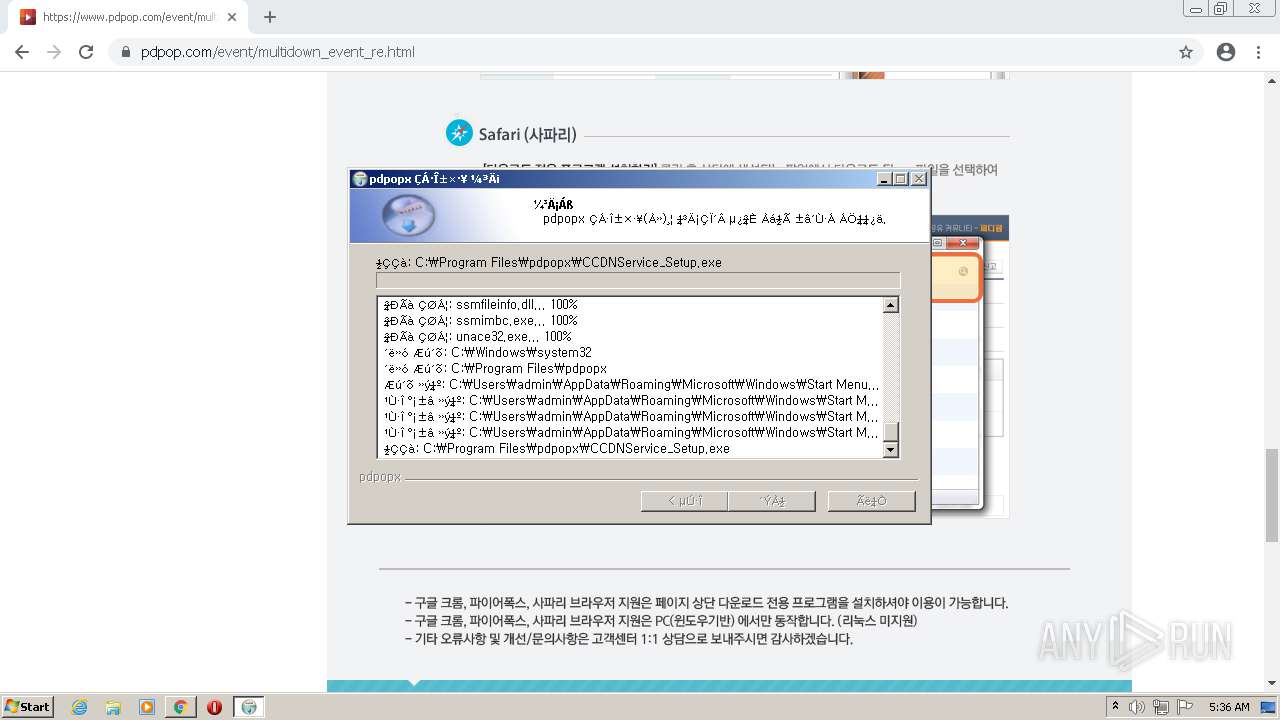
Creates a directory in Program Files
- ExBC_Setup.exe (PID: 3136)
- install.exe (PID: 3784)
- CCDNService_Setup.exe (PID: 2512)
Checks supported languages
- ExBC_Setup.exe (PID: 3136)
- ExBCSvc.exe (PID: 3676)
- ExBCSvc.exe (PID: 1624)
- install.exe (PID: 3784)
- CCDNService_Setup.exe (PID: 2512)
- ns9EF5.tmp (PID: 888)
- nsBC51.tmp (PID: 2096)
- ExBC_Setup.exe (PID: 2116)
- CCDNService.exe (PID: 3664)
- CCDNService.exe (PID: 2672)
- ExBCSvc.exe (PID: 888)
- ExBCSvc.exe (PID: 2732)
- ExBCSvc.exe (PID: 3576)
Creates files in the program directory
- ExBC_Setup.exe (PID: 3136)
- install.exe (PID: 3784)
- CCDNService_Setup.exe (PID: 2512)
- CCDNService.exe (PID: 2672)
- ExBC_Setup.exe (PID: 2116)
Executed as Windows Service
- ExBCSvc.exe (PID: 1624)
- CCDNService.exe (PID: 2672)
- ExBCSvc.exe (PID: 2732)
Creates a software uninstall entry
- ExBC_Setup.exe (PID: 3136)
- CCDNService_Setup.exe (PID: 2512)
- ExBC_Setup.exe (PID: 2116)
- install.exe (PID: 3784)
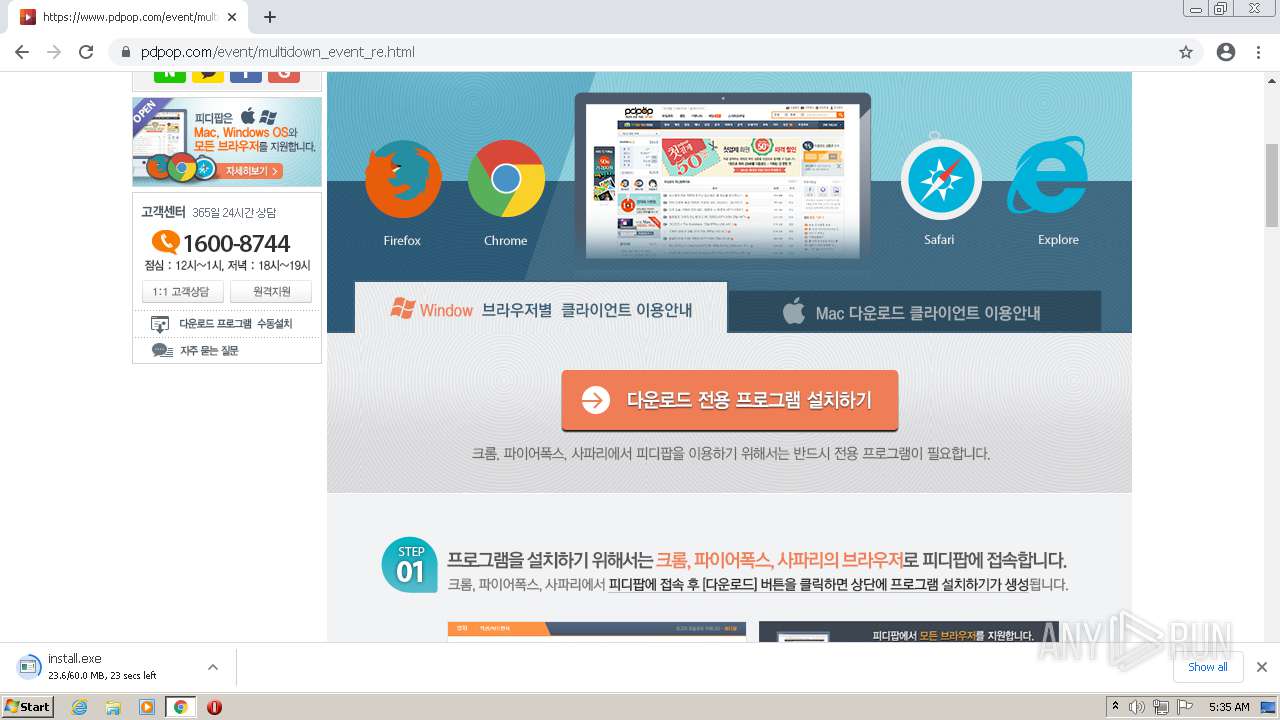
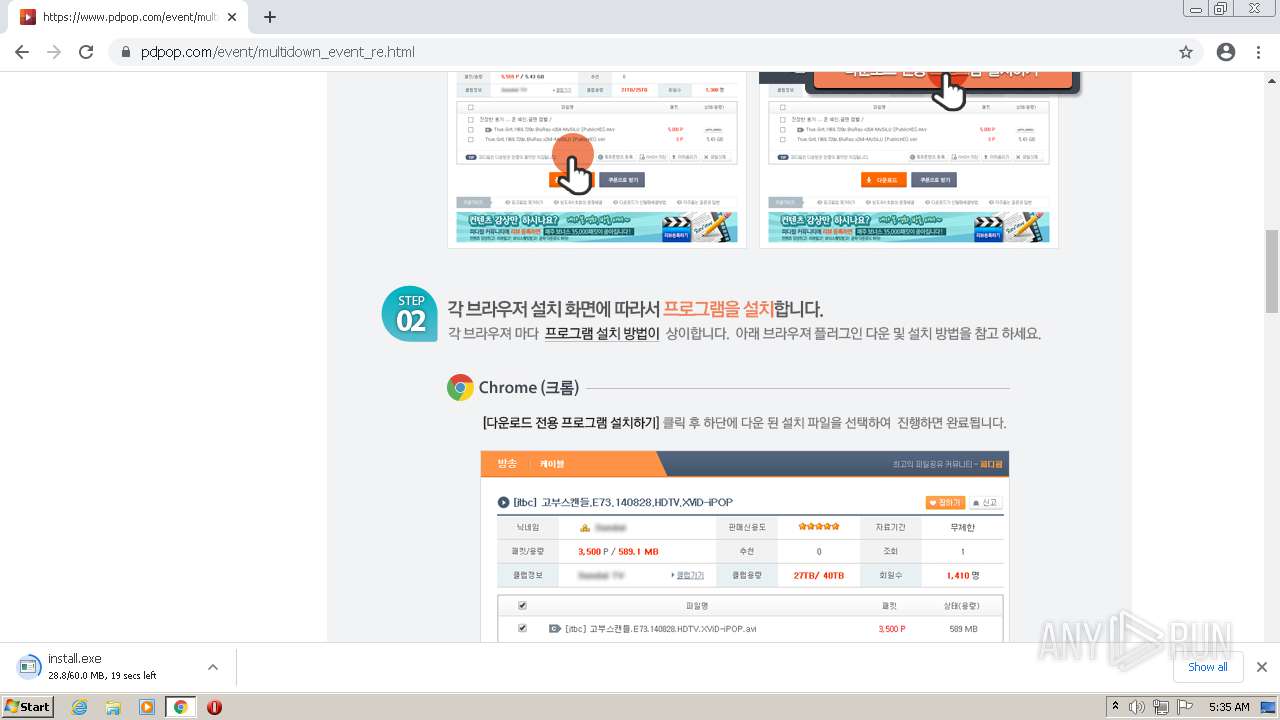
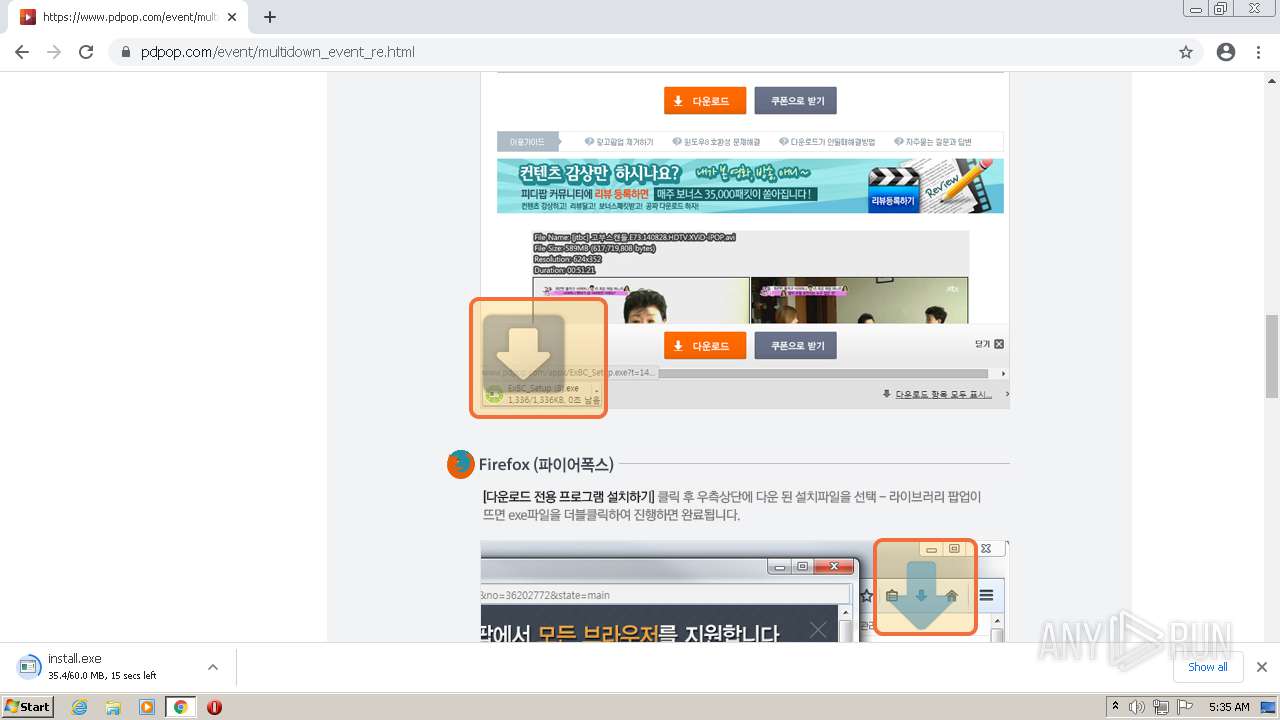
Modifies files in Chrome extension folder
- chrome.exe (PID: 2664)
Drops a file with too old compile date
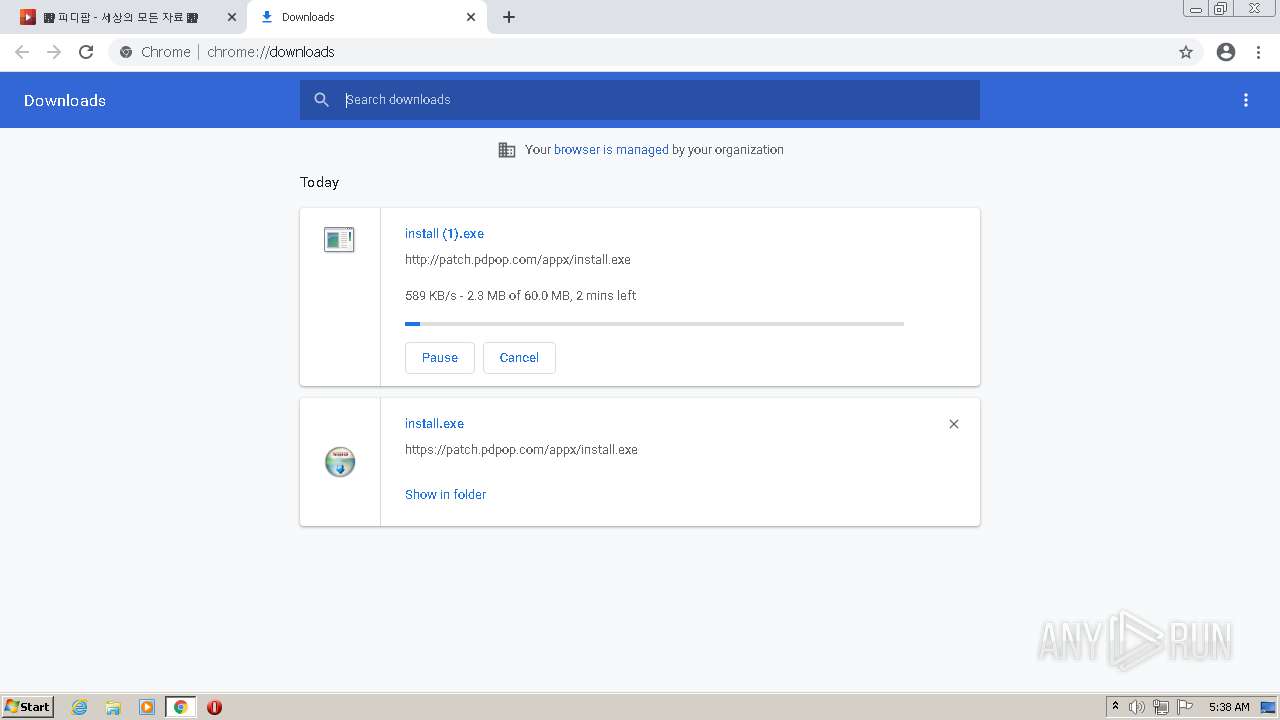
- install.exe (PID: 3784)
Creates files in the user directory
- install.exe (PID: 3784)
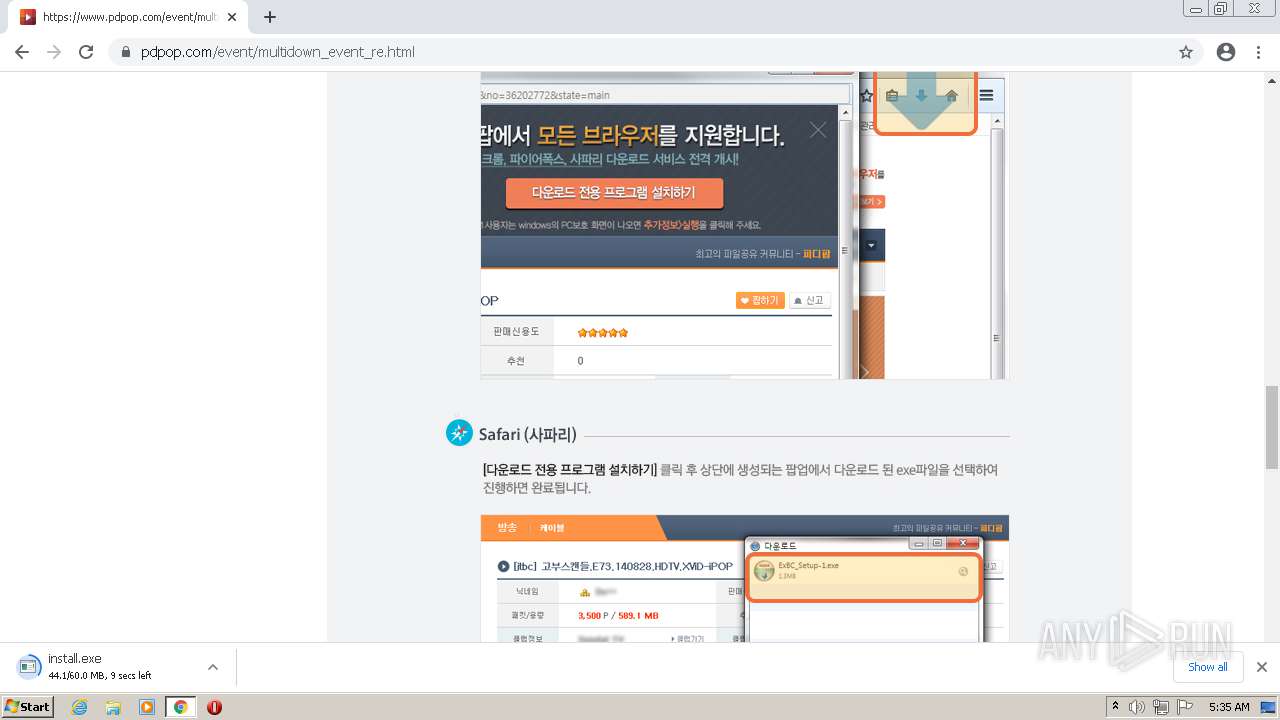
Starts application with an unusual extension
- CCDNService_Setup.exe (PID: 2512)
Uses TASKKILL.EXE to kill process
- ns9EF5.tmp (PID: 888)
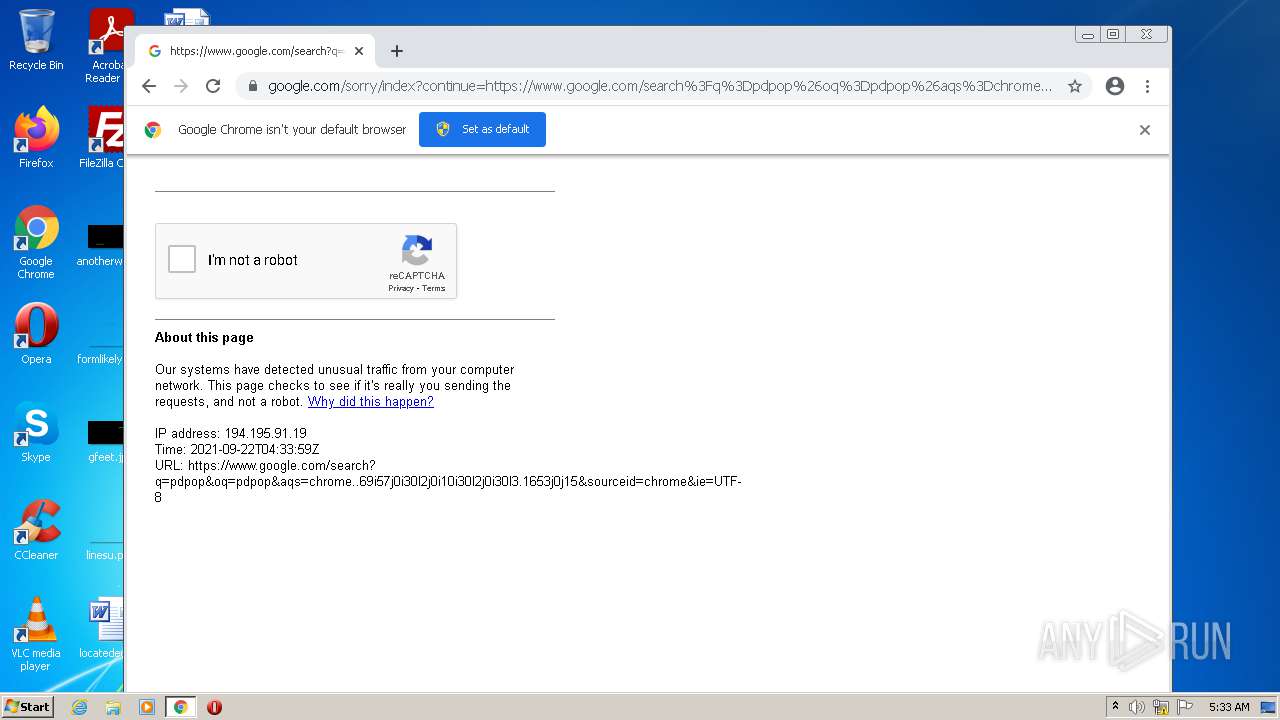
Changes the started page of IE
- install.exe (PID: 3784)
INFO
Checks supported languages
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 2116)
- chrome.exe (PID: 1296)
- chrome.exe (PID: 3808)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 1888)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 4084)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 704)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 1652)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 1008)
- chrome.exe (PID: 3308)
- chrome.exe (PID: 3868)
- chrome.exe (PID: 3640)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 1556)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 1160)
- taskkill.exe (PID: 3916)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 2204)
- chrome.exe (PID: 2424)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 3416)
- chrome.exe (PID: 3212)
Reads the computer name
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 1296)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 1008)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 1556)
- chrome.exe (PID: 2276)
- taskkill.exe (PID: 3916)
Manual execution by user
- chrome.exe (PID: 2664)
Application launched itself
- chrome.exe (PID: 2664)
Reads the hosts file
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3172)
Reads settings of System Certificates
- chrome.exe (PID: 3172)
- chrome.exe (PID: 2664)
Reads the date of Windows installation
- chrome.exe (PID: 1008)
Checks Windows Trust Settings
- chrome.exe (PID: 2664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 1.0.0.38 |
|---|---|
| LegalCopyright: | Copyright (C) 2016 Gvix Co.,Ltd |
| FileVersion: | 1.0.0.38 |
| FileDescription: | ExBC |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.0.0.38 |
| FileVersionNumber: | 1.0.0.38 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x31f1 |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 162816 |
| CodeSize: | 25600 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2017:08:01 02:34:02+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2017 00:34:02 |
| Detected languages: |
|
| FileDescription: | ExBC |
| FileVersion: | 1.0.0.38 |
| LegalCopyright: | Copyright (C) 2016 Gvix Co.,Ltd |
| ProductVersion: | 1.0.0.38 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2017 00:34:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006254 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43386 |
.rdata | 0x00008000 | 0x00001354 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23627 |
.data | 0x0000A000 | 0x00025518 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04463 |
.ndata | 0x00030000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00039000 | 0x00004490 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.87874 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2901 | 1072 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.62197 | 160 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.61 | 492 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
115
Monitored processes
62
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,13697001085253785756,6890443649921692714,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3128 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 888 | "C:\Users\admin\AppData\Local\Temp\nsd9EE4.tmp\ns9EF5.tmp" taskkill /f /im CCDNService.exe | C:\Users\admin\AppData\Local\Temp\nsd9EE4.tmp\ns9EF5.tmp | — | CCDNService_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 128 Modules
| |||||||||||||||
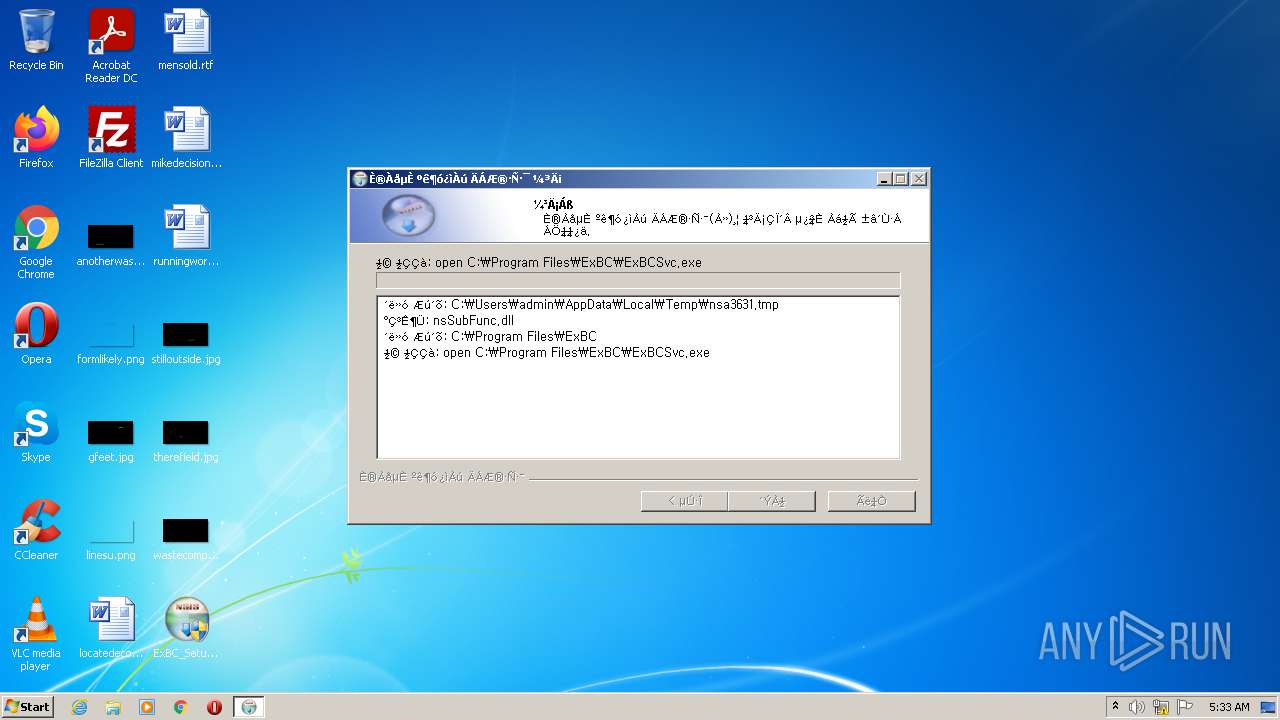
| 888 | "C:\Program Files\ExBC\ExBCSvc.exe" -u | C:\Program Files\ExBC\ExBCSvc.exe | — | ExBC_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Extended Brower Controler Service Exit code: 1 Version: 2.2.1.12 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1060,13697001085253785756,6890443649921692714,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3324 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,13697001085253785756,6890443649921692714,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1060,13697001085253785756,6890443649921692714,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2804 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1060,13697001085253785756,6890443649921692714,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3800 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\ExBC\ExBCSvc.exe" | C:\Program Files\ExBC\ExBCSvc.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: Extended Brower Controler Service Exit code: 0 Version: 2.2.1.12 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,13697001085253785756,6890443649921692714,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3276 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,13697001085253785756,6890443649921692714,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
23 264
Read events
23 002
Write events
254
Delete events
8
Modification events
| (PID) Process: | (3136) ExBC_Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3136) ExBC_Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3136) ExBC_Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3136) ExBC_Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3136) ExBC_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ExBC |
| Operation: | write | Name: | DisplayName |
Value: Ȯ��� ������ ��Ʈ�ѷ� | |||
| (PID) Process: | (3136) ExBC_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ExBC |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\ExBC\Uninstall.exe | |||
| (PID) Process: | (3136) ExBC_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ExBC |
| Operation: | write | Name: | URLInfoAbout |
Value: www.gvix.co.kr | |||
| (PID) Process: | (3136) ExBC_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ExBC |
| Operation: | write | Name: | Publisher |
Value: Gvix Co.,Ltd | |||
| (PID) Process: | (3136) ExBC_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\nsa3631.tmp\nsProcess.dll | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
77
Suspicious files
154
Text files
372
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-614AB22F-A68.pma | — | |
MD5:— | SHA256:— | |||
| 3136 | ExBC_Setup.exe | C:\Program Files\ExBC\ExBCSvc.exe | executable | |
MD5:— | SHA256:— | |||
| 3136 | ExBC_Setup.exe | C:\Program Files\ExBC\Uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | binary | |
MD5:— | SHA256:— | |||
| 3136 | ExBC_Setup.exe | C:\Program Files\ExBC\Launcher.exe | executable | |
MD5:— | SHA256:— | |||
| 3136 | ExBC_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsa3631.tmp\nsSubFunc.dll | executable | |
MD5:8C483EFF15D5F88FA4BF6DC3ACB83C81 | SHA256:E9DB0776E5772934C88545BBE9112E7BF44090223C90818EC2C63CC77C9DAF83 | |||
| 3136 | ExBC_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsa3631.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3136 | ExBC_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsa3631.tmp\System.dll | executable | |
MD5:55A26D7800446F1373056064C64C3CE8 | SHA256:904FD5481D72F4E03B01A455F848DEDD095D0FB17E33608E0D849F5196FB6FF8 | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | vxd | |
MD5:CF89D16BB9107C631DAABF0C0EE58EFB | SHA256:D6A5FE39CD672781B256E0E3102F7022635F1D4BB7CFCC90A80FFFE4D0F3877E | |||
| 3136 | ExBC_Setup.exe | C:\Program Files\ExBC\exbc_ver.dat | text | |
MD5:087BF119105039D2E62010E3F3C03C61 | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
173
TCP/UDP connections
108
DNS requests
54
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | — | — | whitelisted |
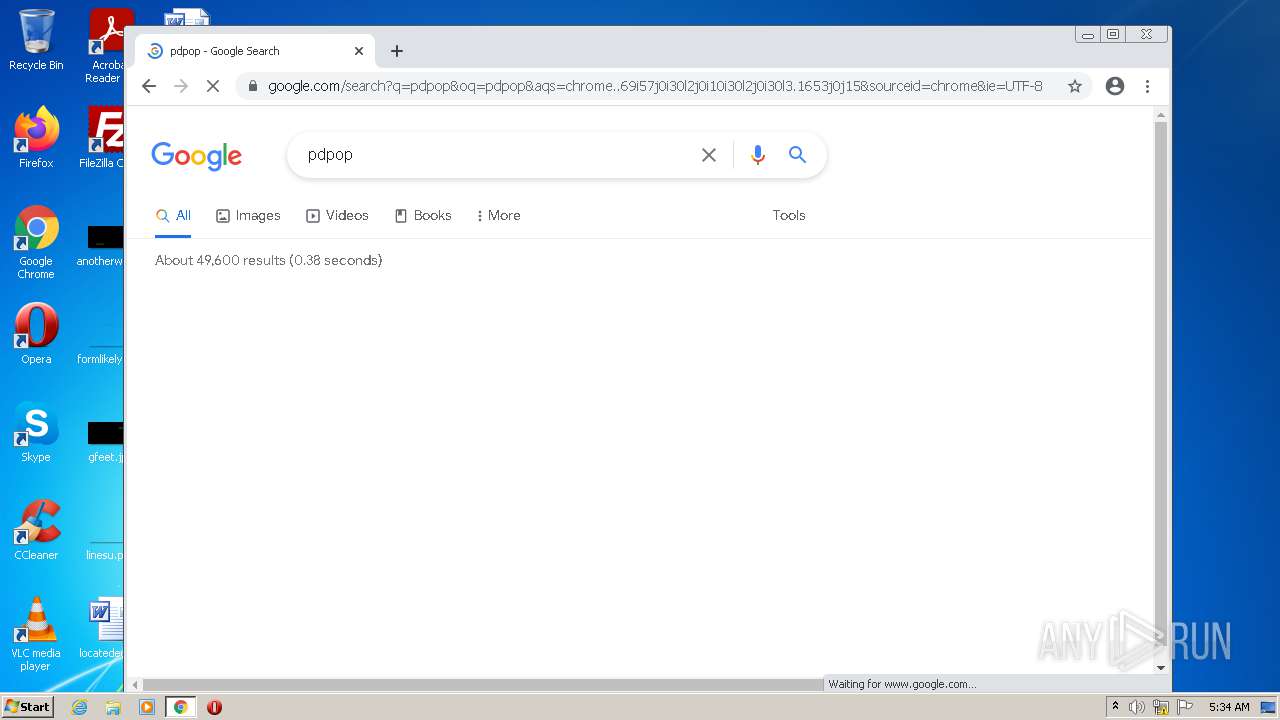
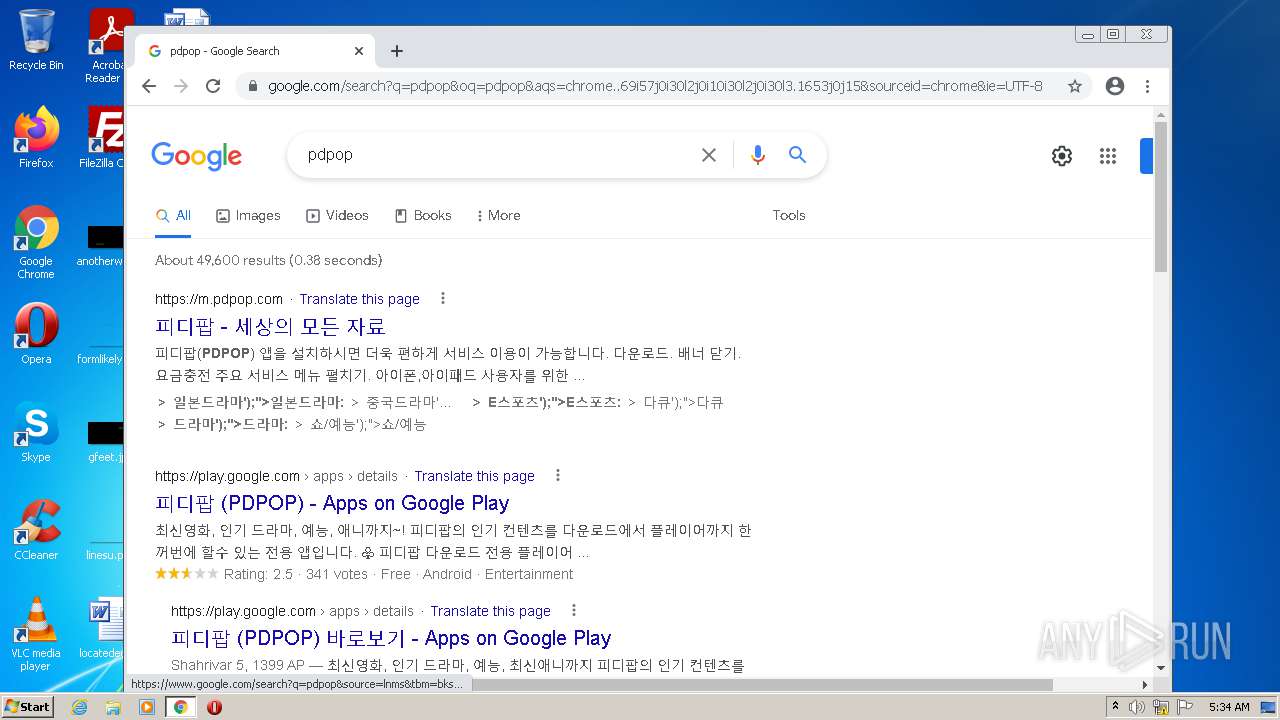
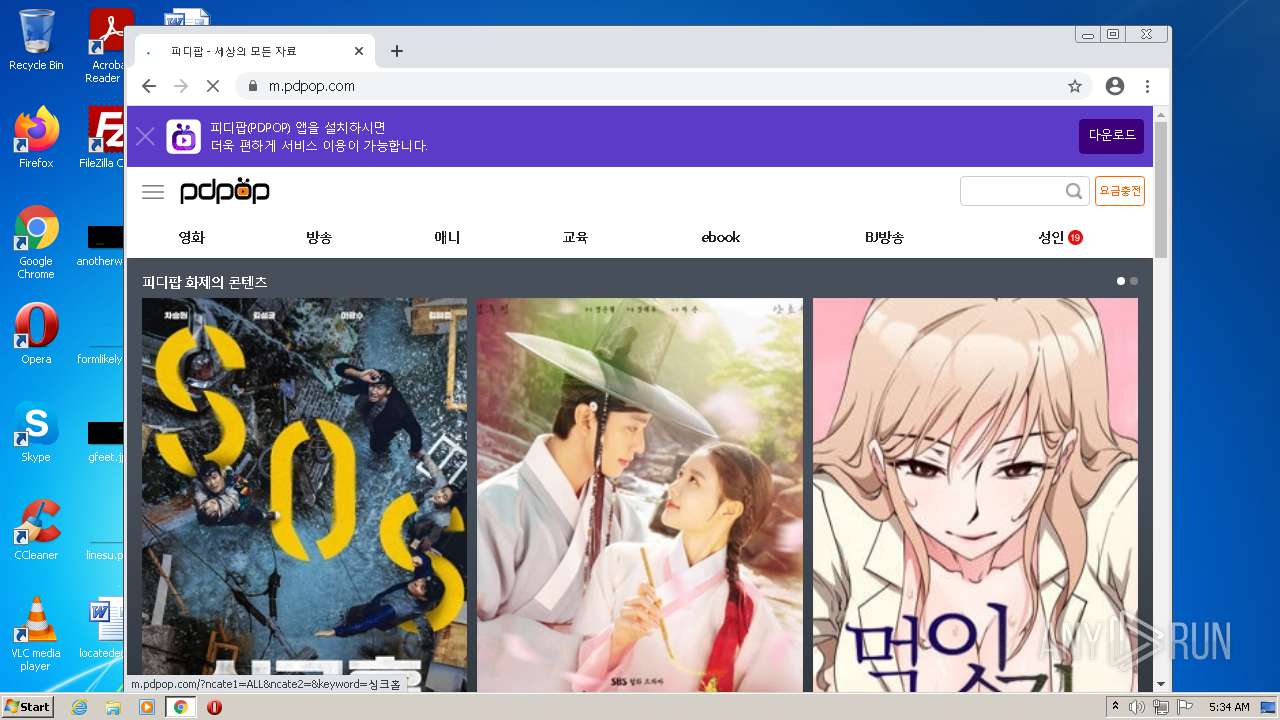
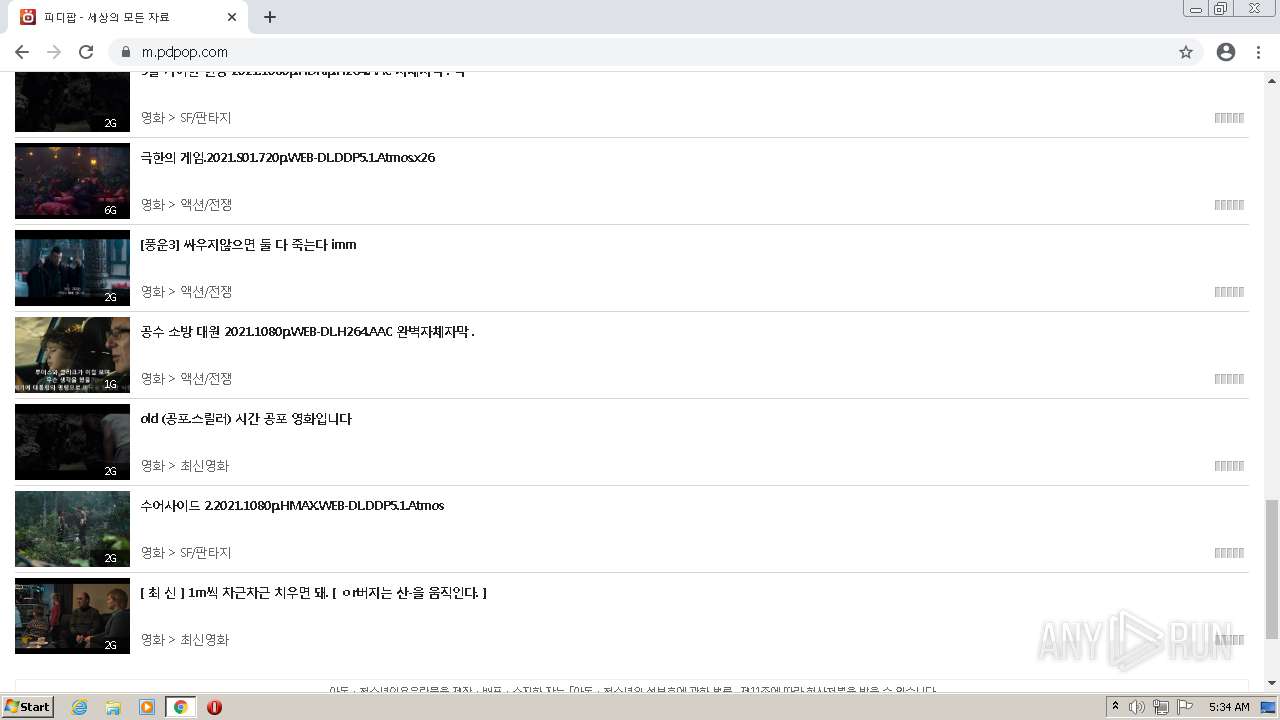
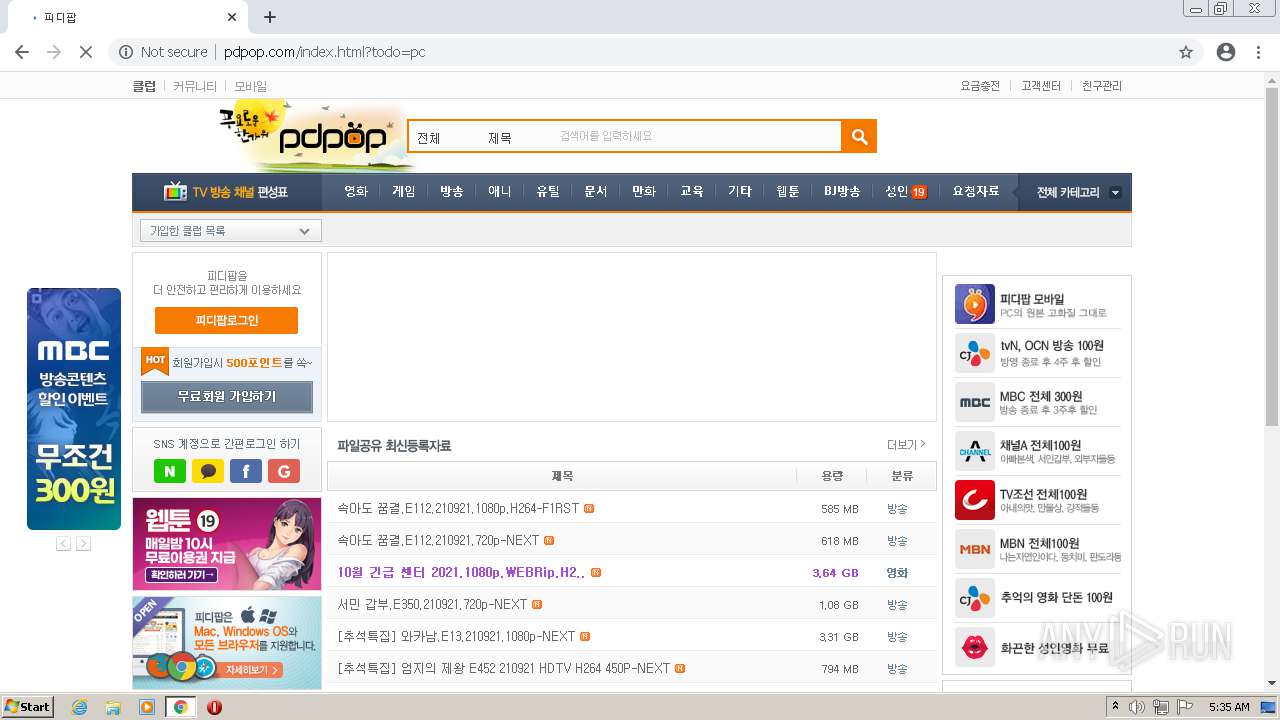
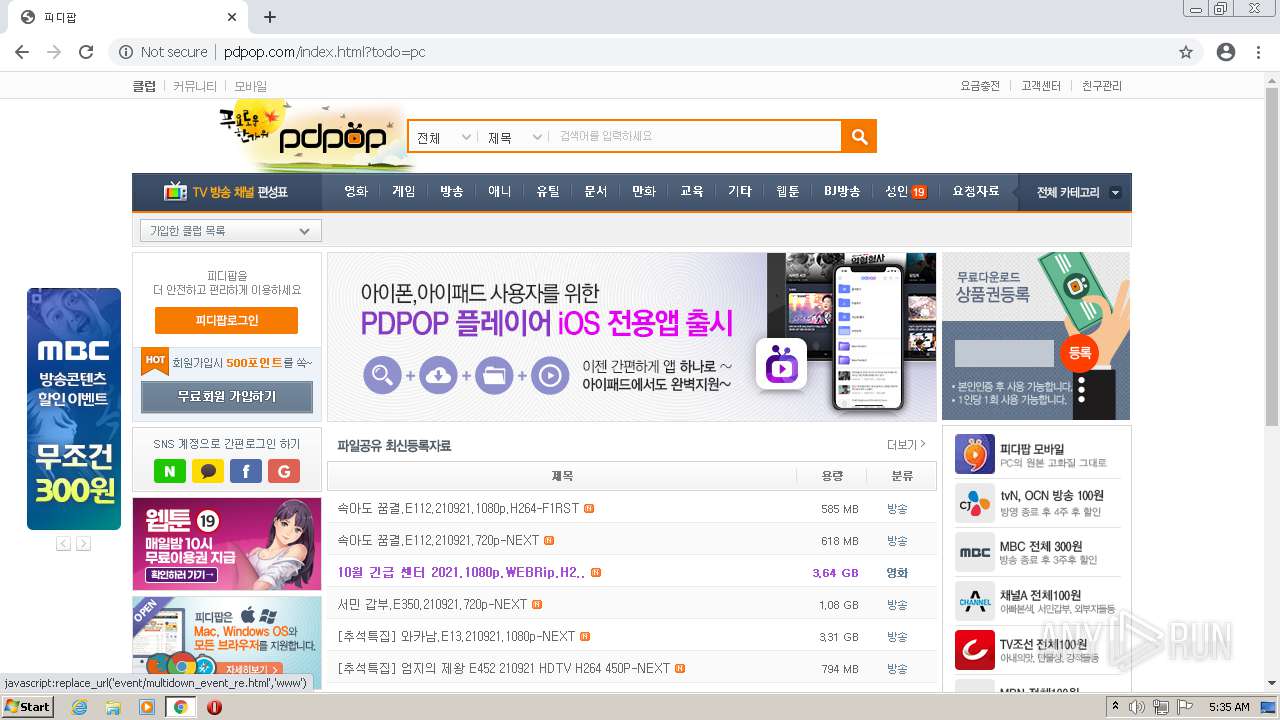
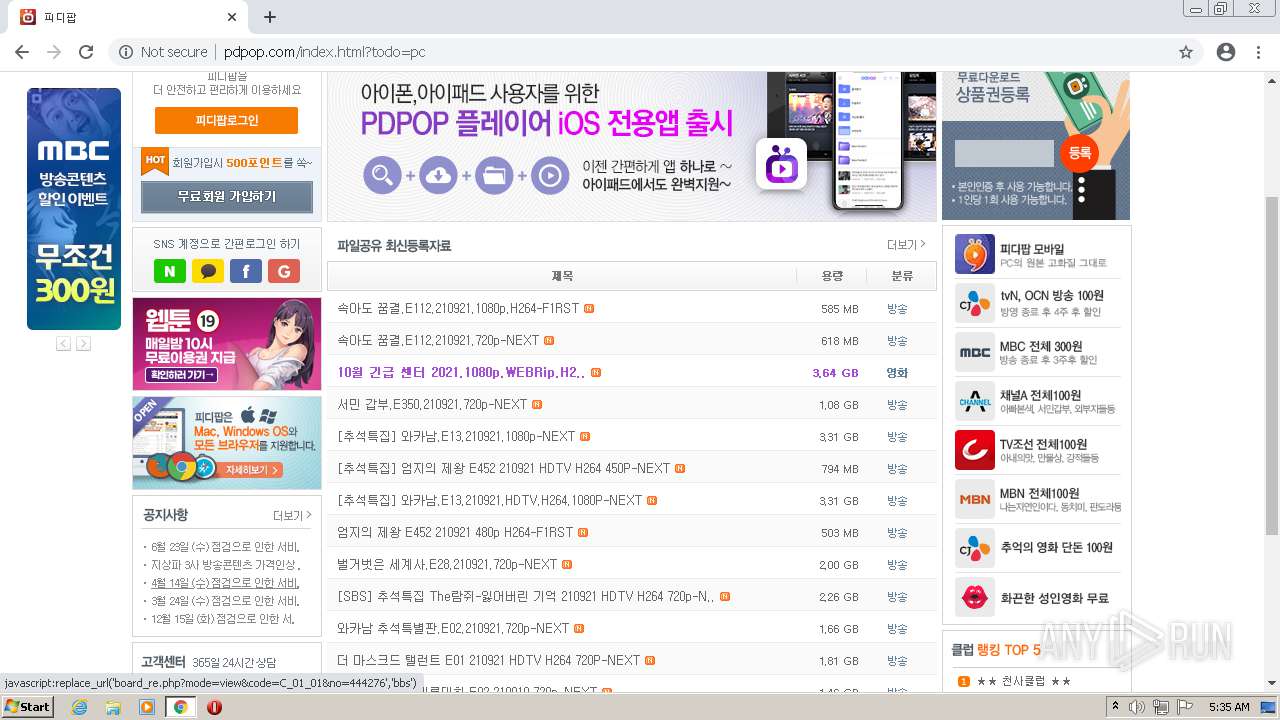
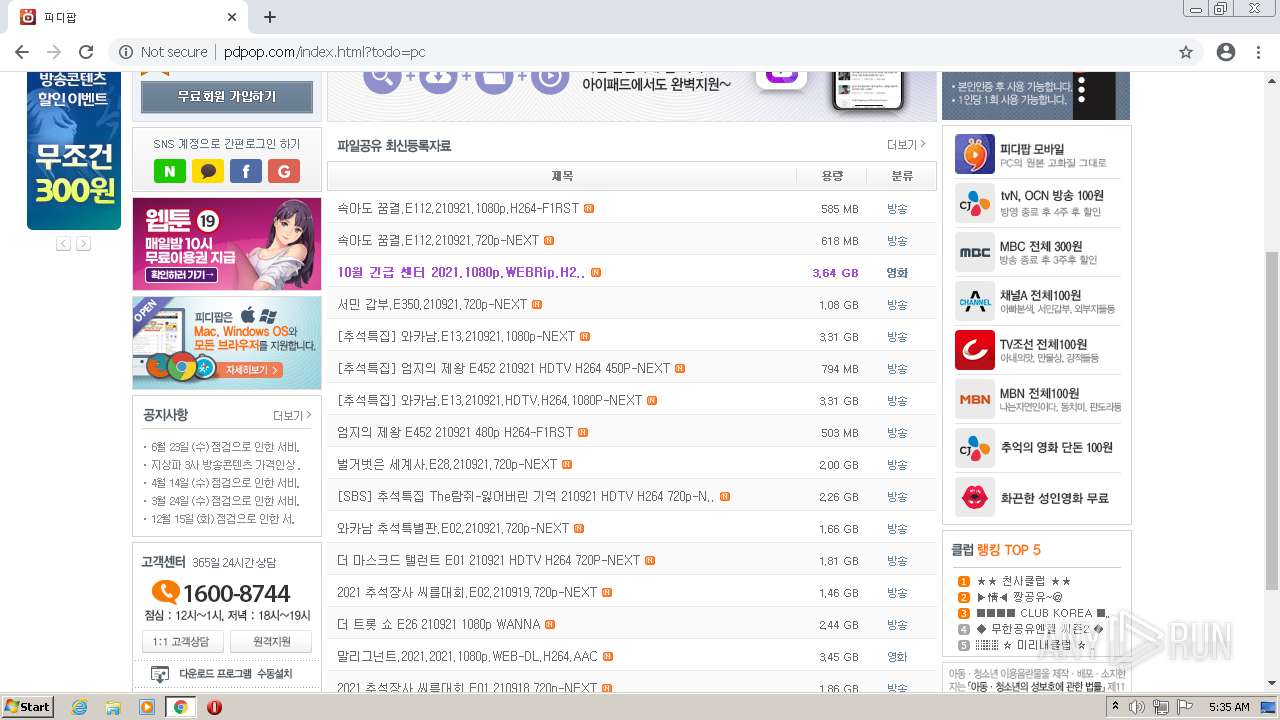
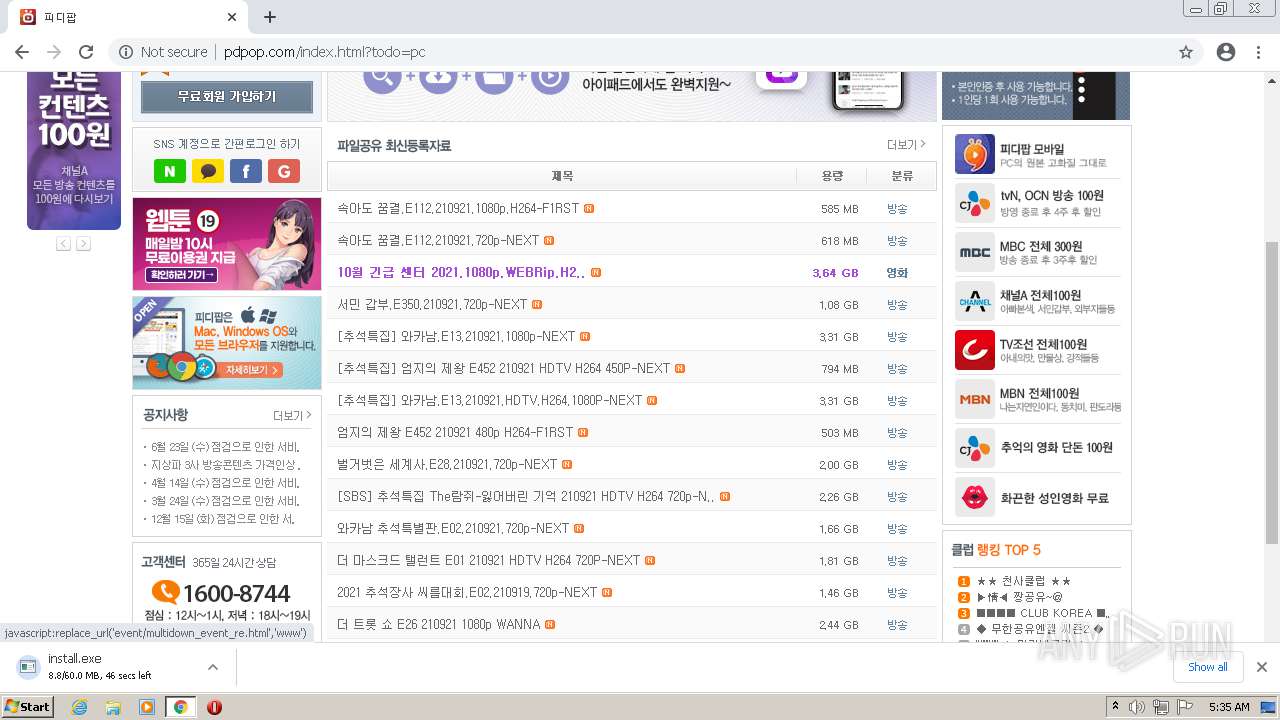
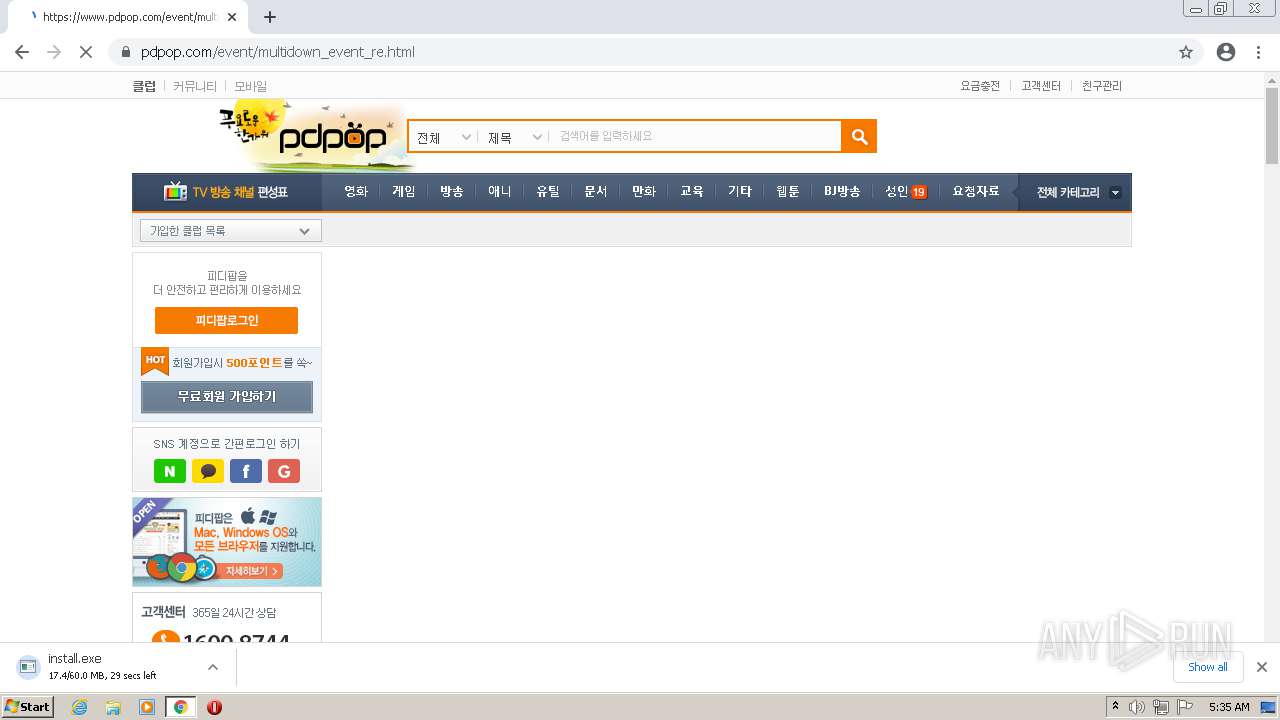
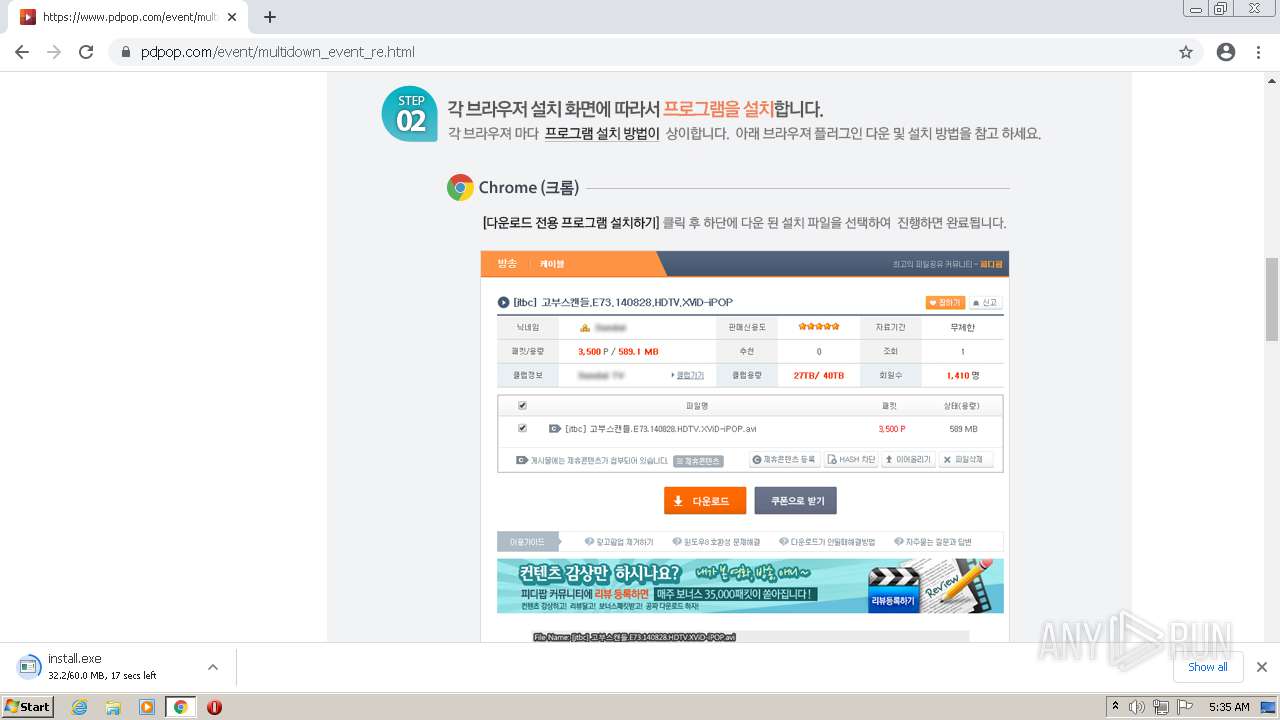
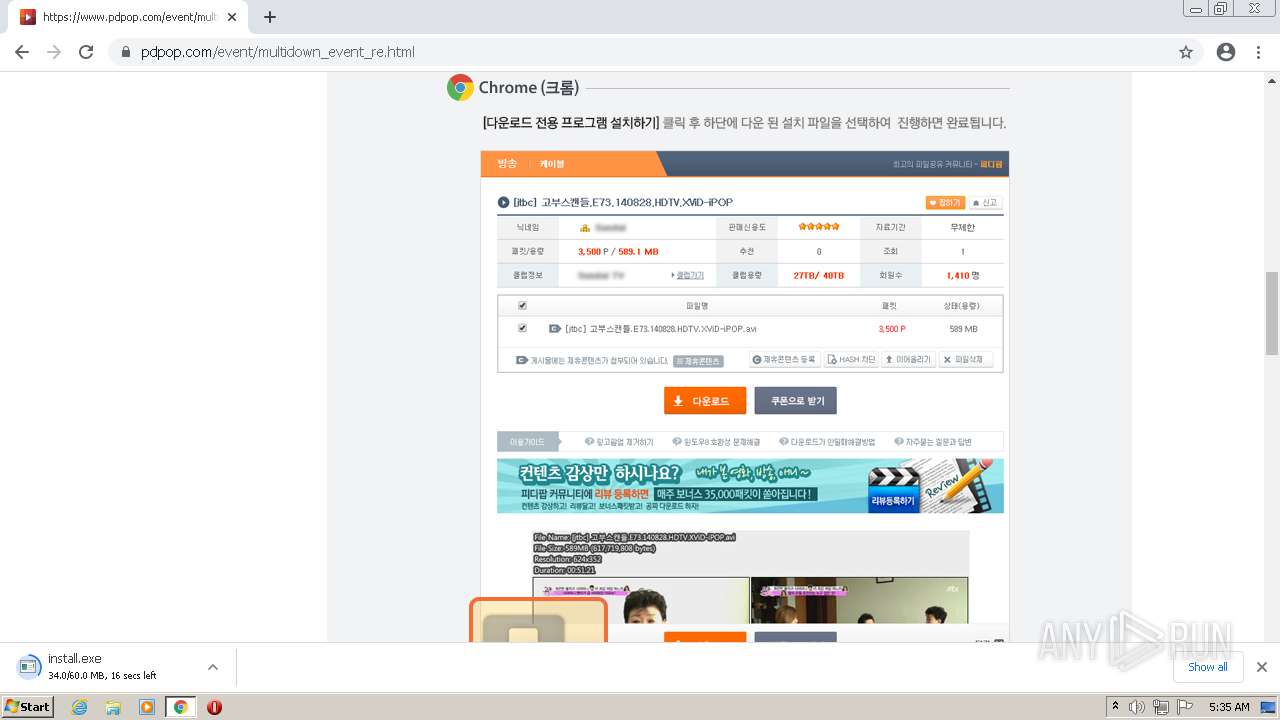
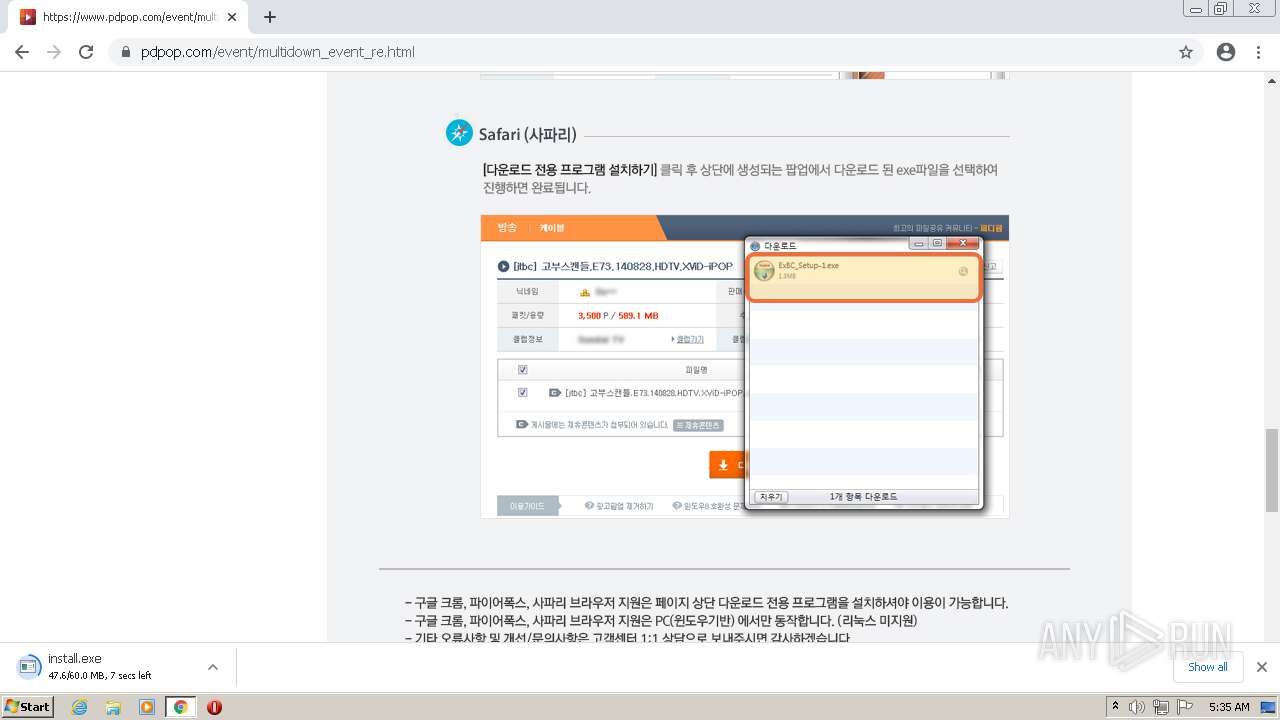
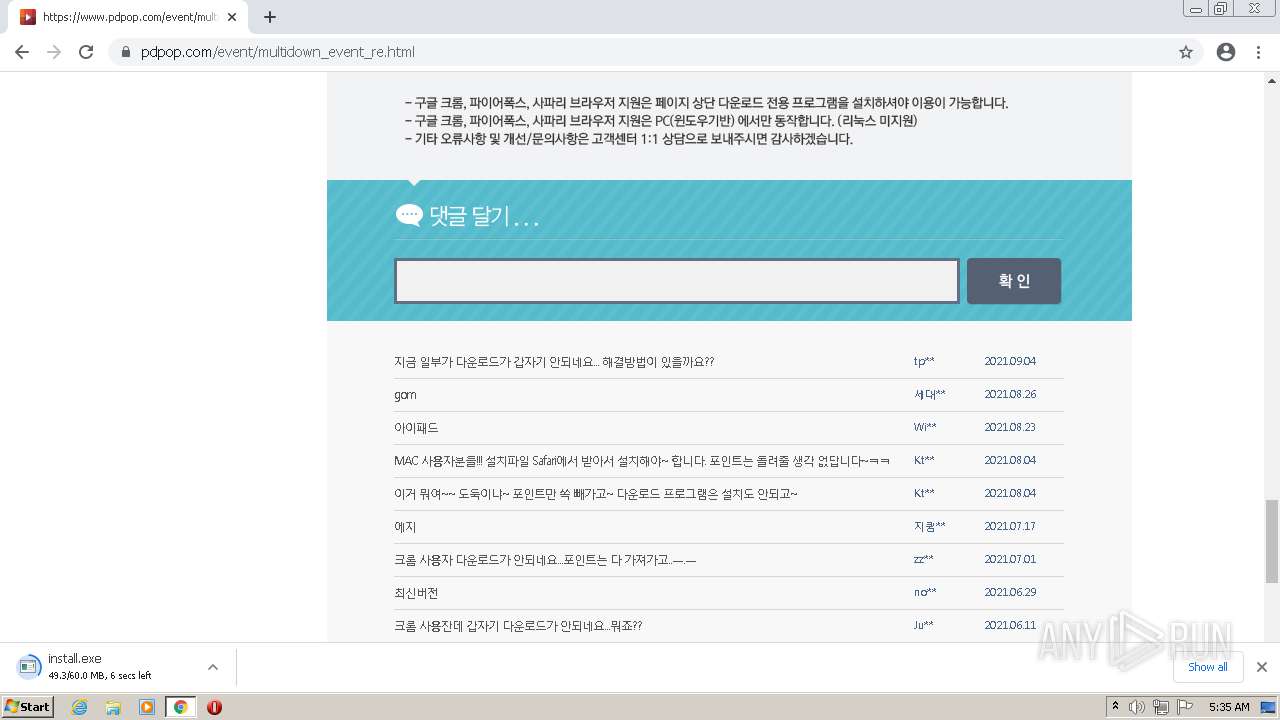
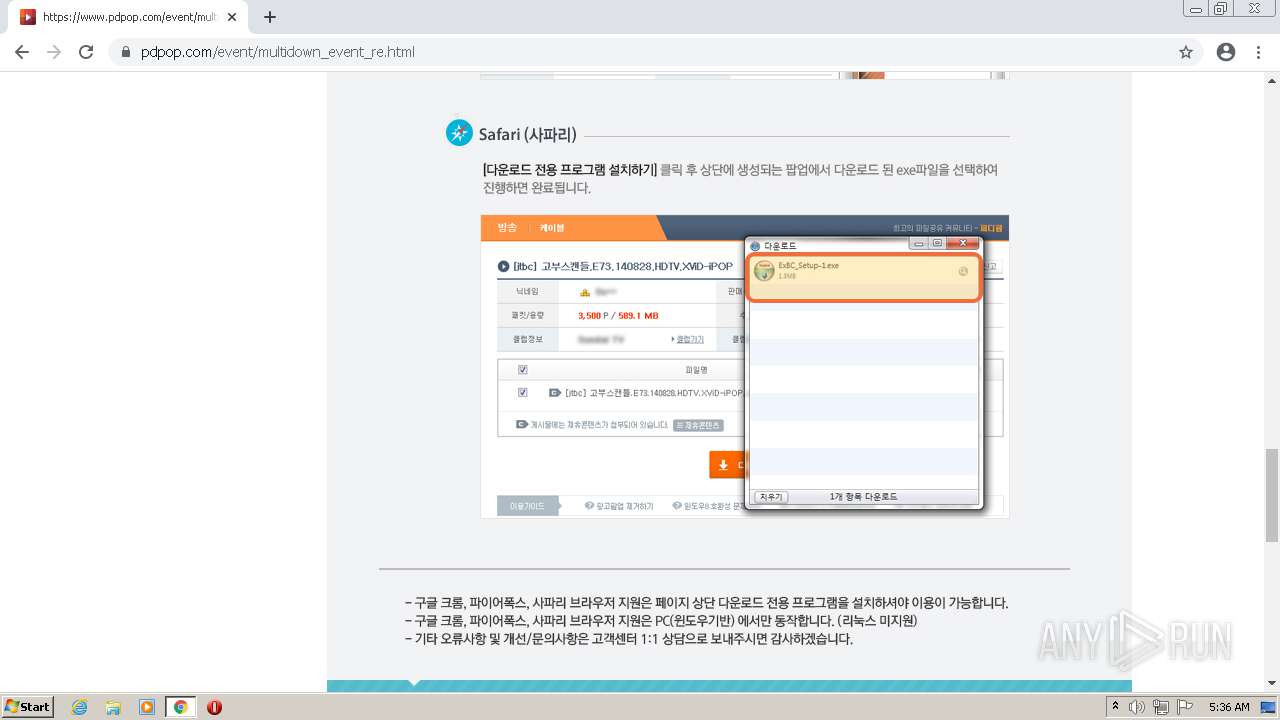
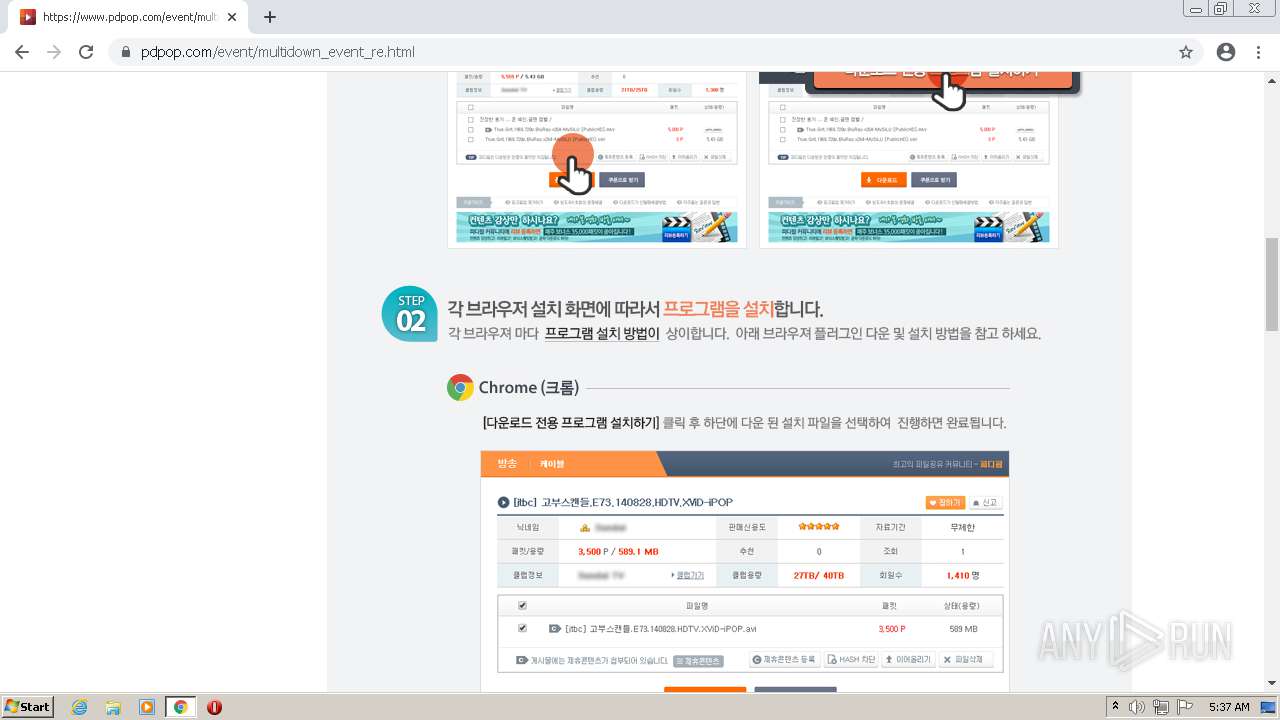
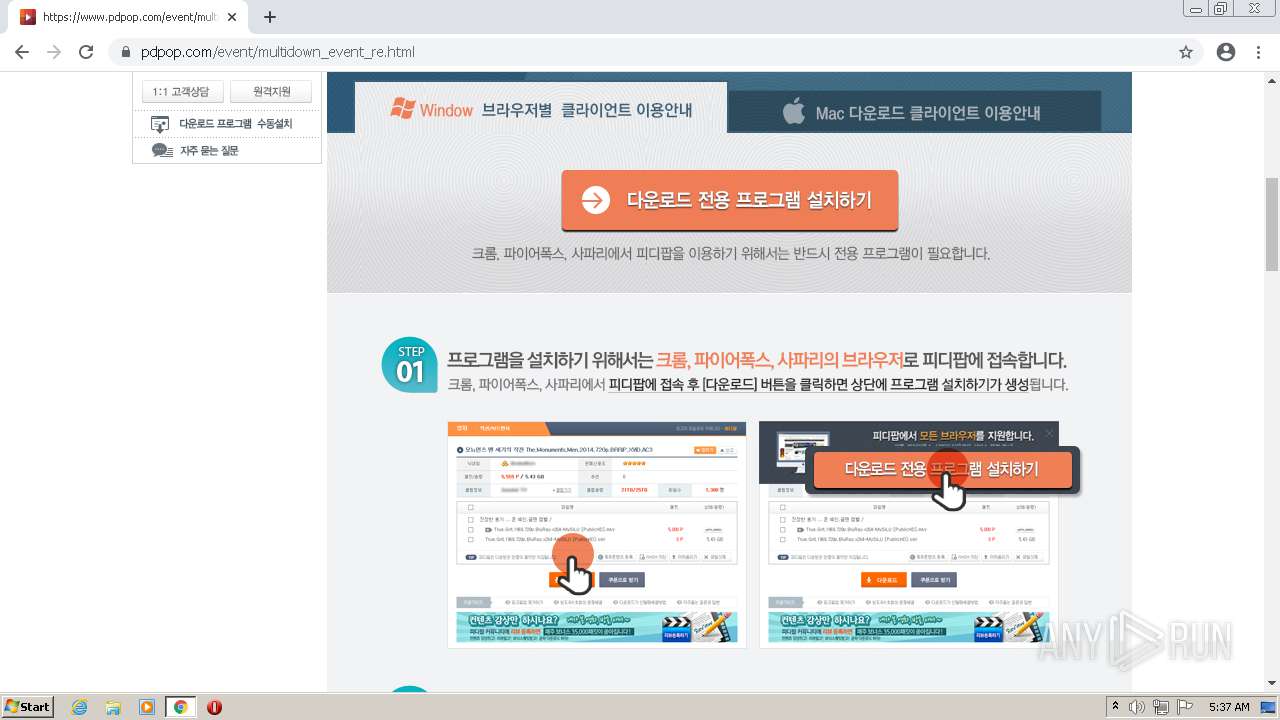
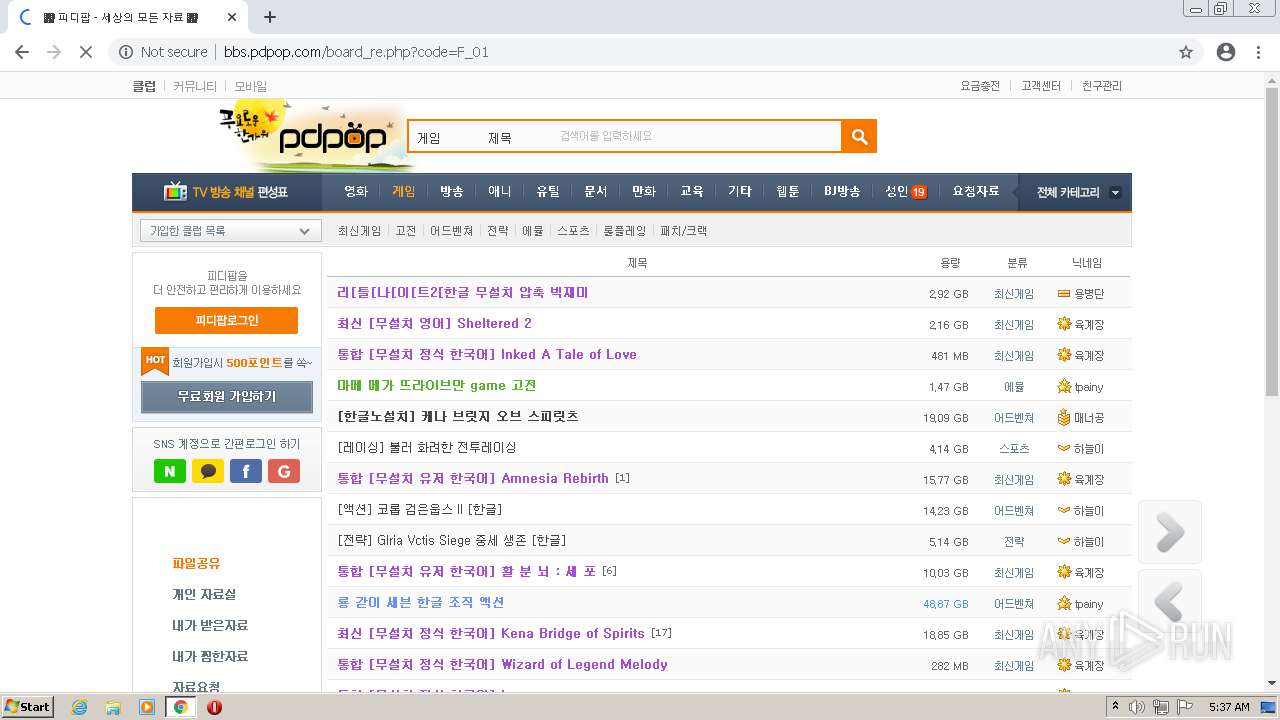
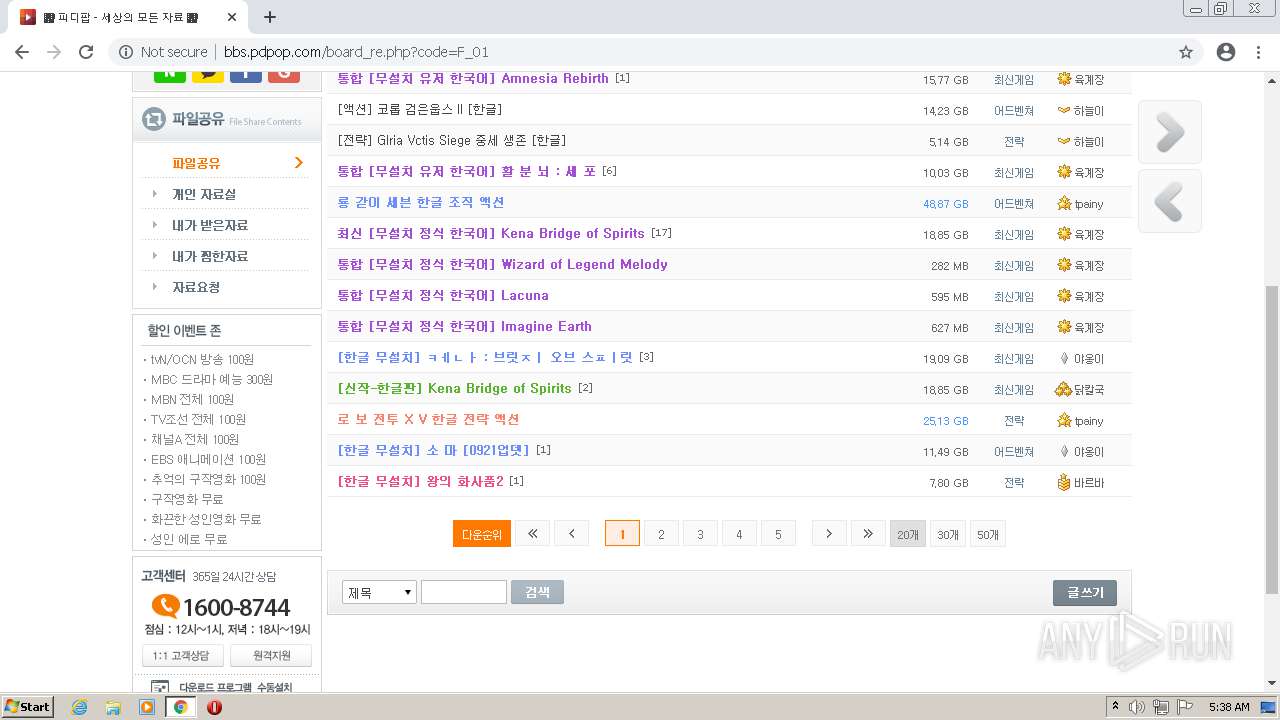
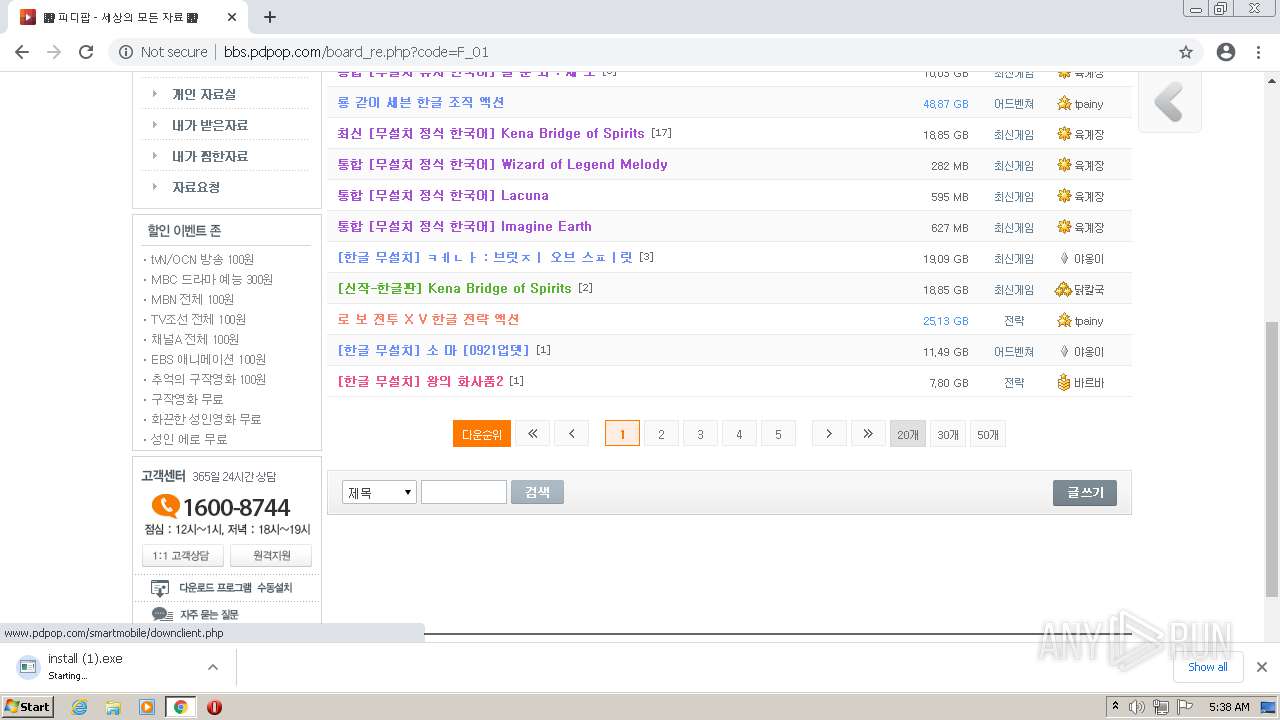
3172 | chrome.exe | GET | — | 1.240.12.15:80 | http://www.pdpop.com/images/script/jquery-1.7.1.min.js | KR | — | — | unknown |
— | — | HEAD | 302 | 142.250.186.78:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | — | — | whitelisted |
— | — | HEAD | 200 | 74.125.160.41:80 | http://r4---sn-4g5lznes.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3?cms_redirect=yes&mh=DH&mip=194.195.91.19&mm=28&mn=sn-4g5lznes&ms=nvh&mt=1632284359&mv=u&mvi=4&pl=24&rmhost=r1---sn-4g5lznes.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
3172 | chrome.exe | GET | 200 | 1.240.12.15:80 | http://www.pdpop.com/images/css/pd_common.css?v=20206120243 | KR | text | 80.7 Kb | unknown |
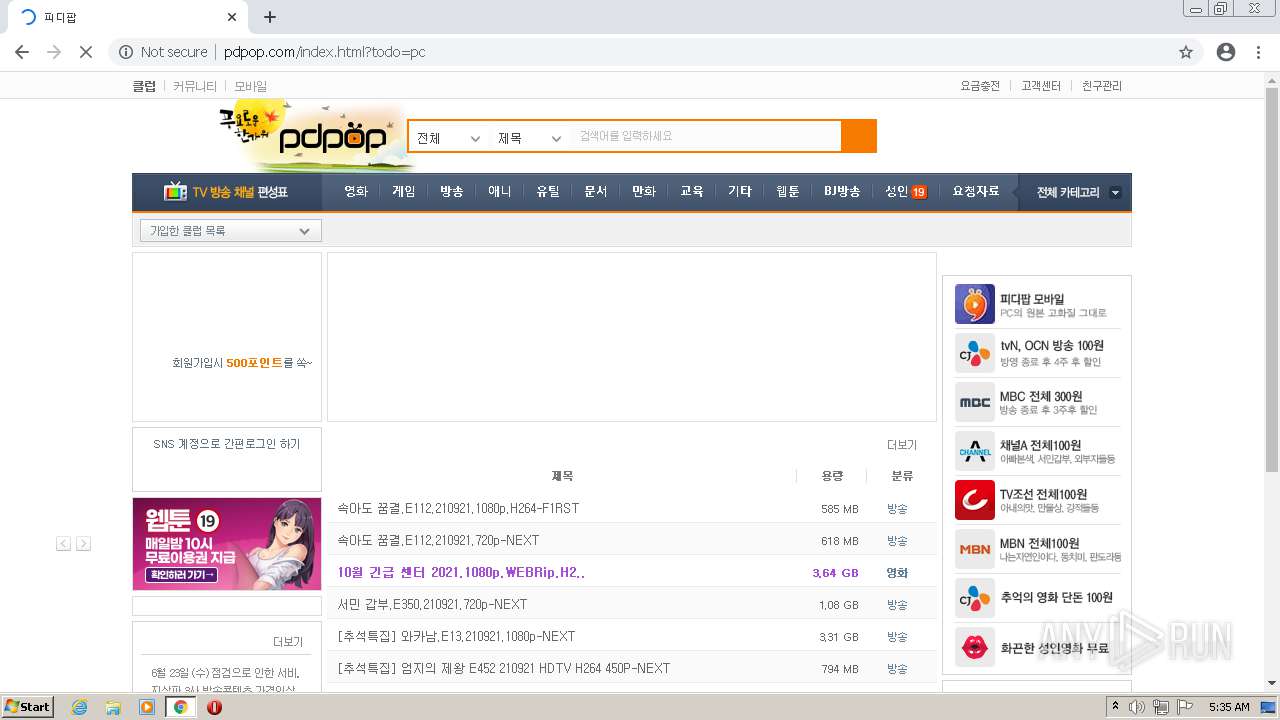
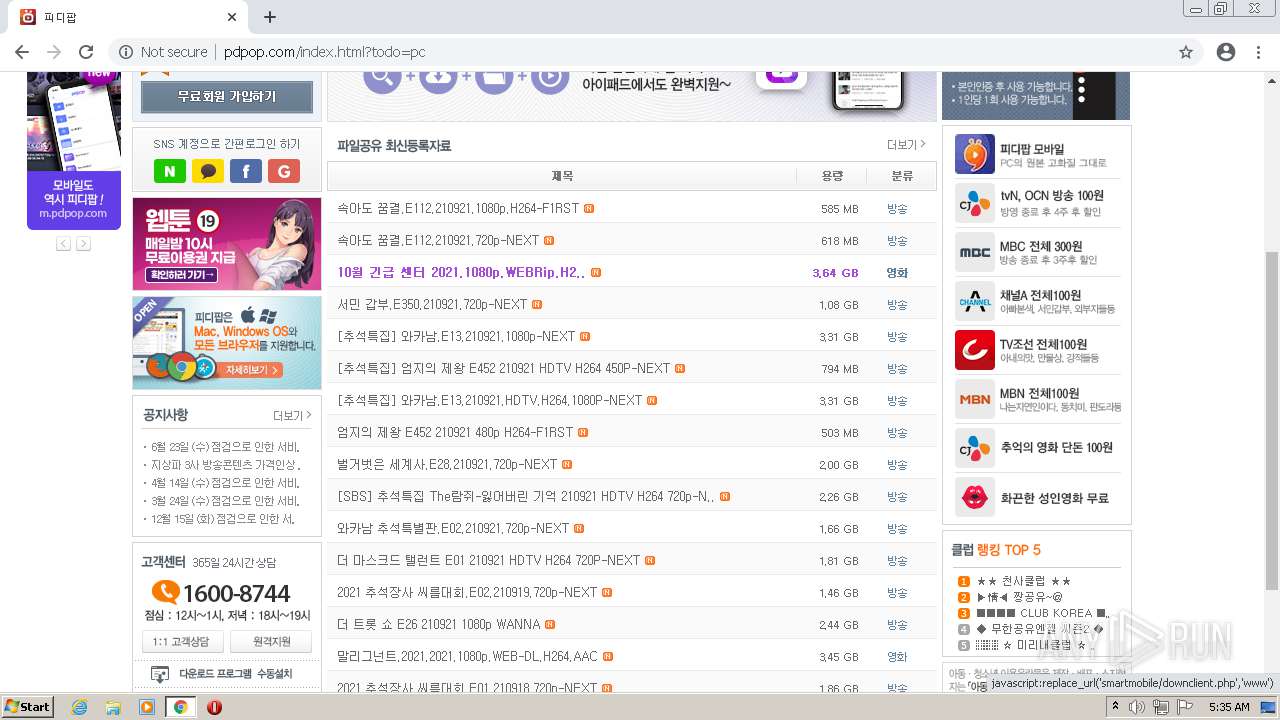
3172 | chrome.exe | GET | 200 | 1.240.12.15:80 | http://www.pdpop.com/index.html?todo=pc | KR | html | 59.5 Kb | unknown |
3172 | chrome.exe | GET | 200 | 1.240.12.15:80 | http://www.pdpop.com/images/css/slides2.css | KR | text | 852 b | unknown |
3172 | chrome.exe | GET | 200 | 1.240.12.15:80 | http://www.pdpop.com/images/css/pd_main2.css?v=202004161321 | KR | text | 10.6 Kb | unknown |
3172 | chrome.exe | GET | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 556 b | whitelisted |
3172 | chrome.exe | GET | 200 | 1.240.12.15:80 | http://www.pdpop.com/images/script/jquery.slides.js | KR | text | 26.7 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3172 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3172 | chrome.exe | 142.250.185.238:443 | apis.google.com | Google Inc. | US | whitelisted |
3172 | chrome.exe | 142.250.185.170:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
3172 | chrome.exe | 142.250.186.131:443 | update.googleapis.com | Google Inc. | US | whitelisted |
3172 | chrome.exe | 142.250.185.238:80 | apis.google.com | Google Inc. | US | whitelisted |
3172 | chrome.exe | 142.250.185.132:443 | www.google.com | Google Inc. | US | whitelisted |
3172 | chrome.exe | 142.250.186.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3172 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3172 | chrome.exe | 142.250.74.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3172 | chrome.exe | 1.240.12.50:443 | m.pdpop.com | SK Broadband Co Ltd | KR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3172 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |