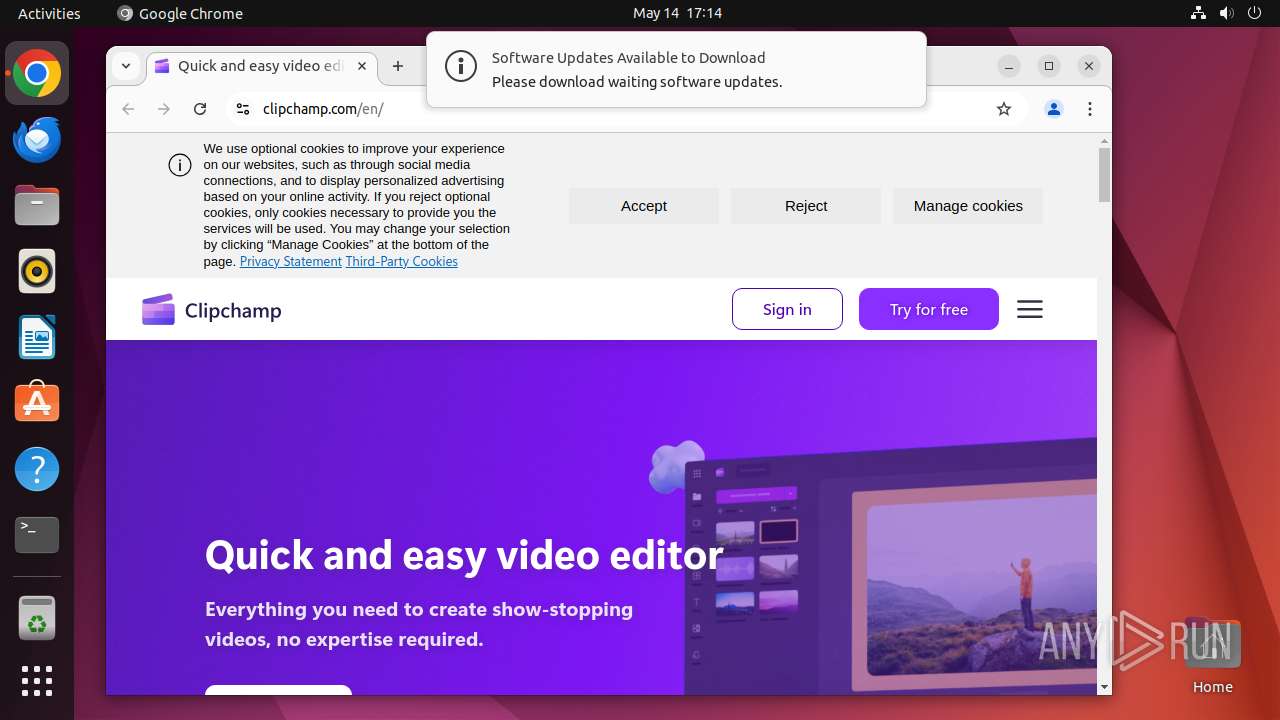
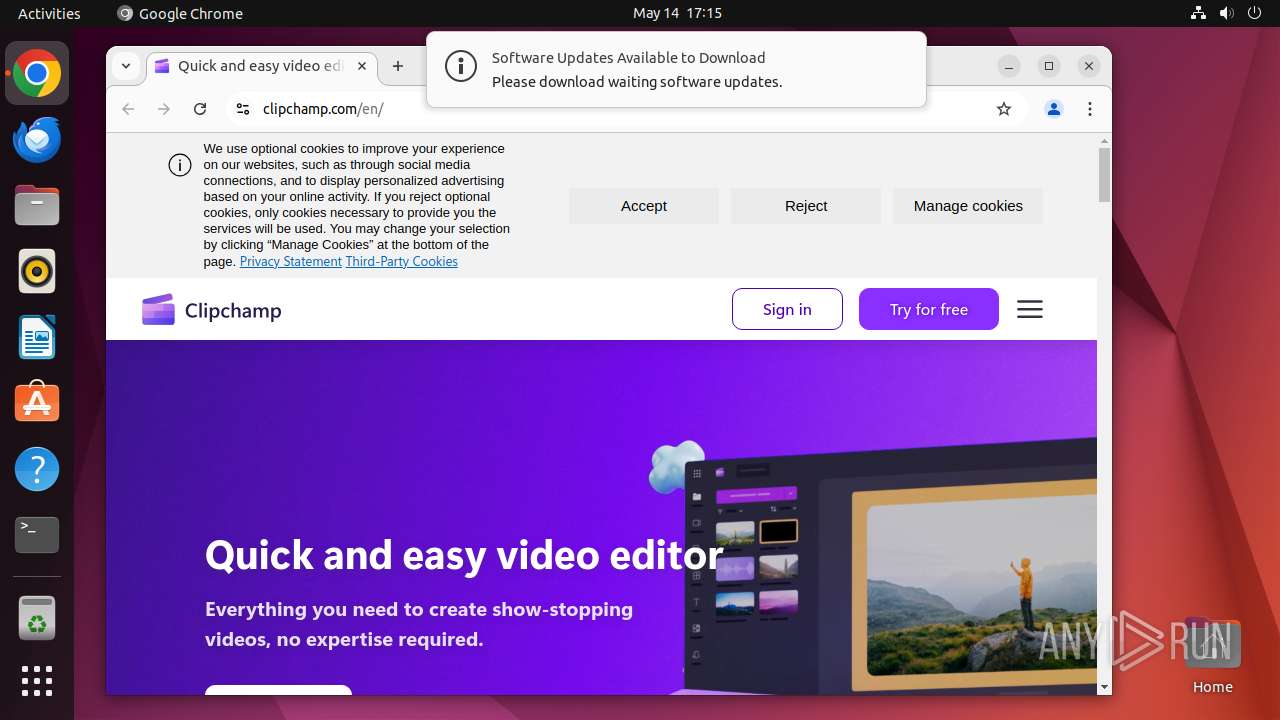
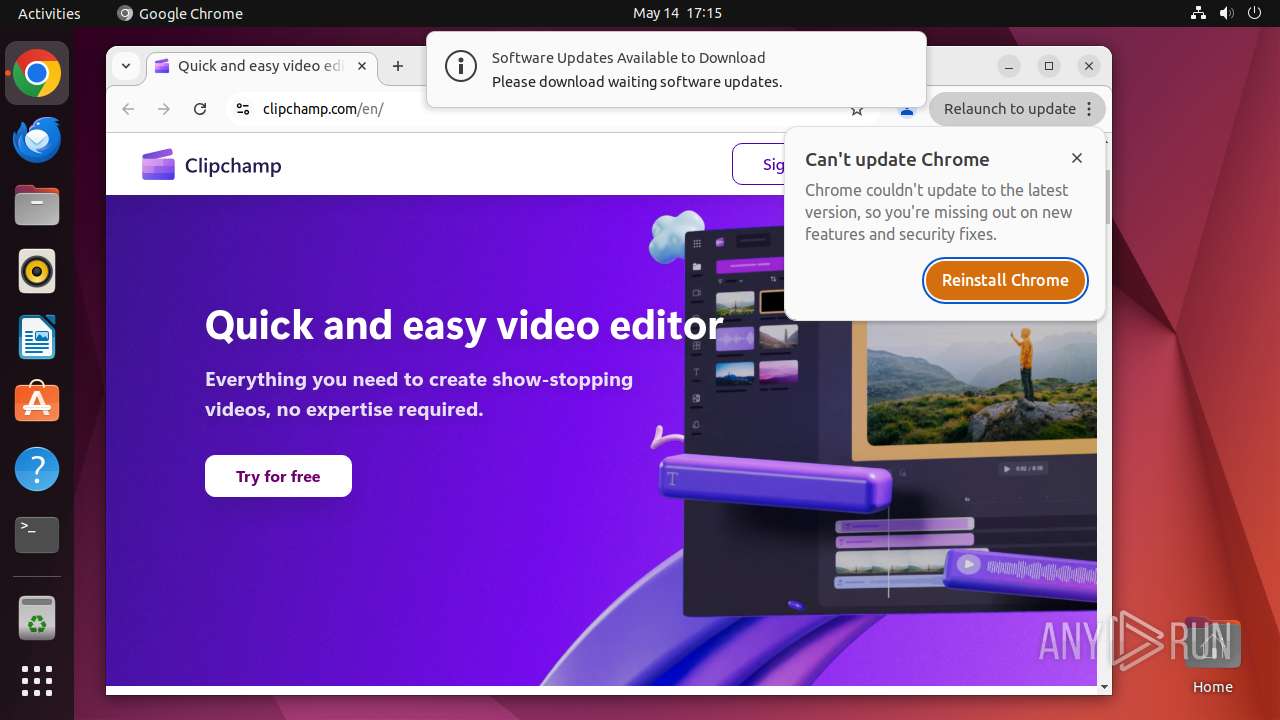
| URL: | http://clipchamp.com/ |
| Full analysis: | https://app.any.run/tasks/7e3bb35c-b9eb-402e-bc51-efecbd57d993 |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2025, 16:14:51 |
| OS: | Ubuntu 22.04.2 |
| MD5: | 32A1D9027E10B4C23E0B2BC972A17D6A |
| SHA1: | 0C7E57B18F44CACC5019031DD7EF6484DEECFC05 |
| SHA256: | A7395CB5FF632113207992EA51D32195FEAE3728E9625C7FE5E0B6298E15BB1A |
| SSDEEP: | 3:N1KdJMlIhR:C60 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes commands using command-line interpreter
- sudo (PID: 39491)
- chrome (PID: 39492)
INFO
Checks timezone
- chrome (PID: 39492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
301
Monitored processes
83
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 39490 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome http://clipchamp\.com/ " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 39491 | sudo -iu user google-chrome http://clipchamp.com/ | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 39492 | /usr/bin/google-chrome http://clipchamp.com/ | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 39493 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39494 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39495 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39496 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39497 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 39498 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 39499 | "/opt/google/chrome/chrome http://clipchamp\.co" | /opt/google/chrome/chrome | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
135
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 39492 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 39492 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 39492 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 39492 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 39492 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 39492 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 39538 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 39640 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 39492 | chrome | /home/user/.config/google-chrome/Default/History | sqlite | |
MD5:— | SHA256:— | |||
| 39492 | chrome | /home/user/.config/google-chrome/Default/DawnWebGPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
29
DNS requests
36
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 204 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.48:80 | — | Canonical Group Limited | GB | unknown |
— | — | 195.181.170.19:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
512 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
39540 | chrome | 172.217.16.202:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
39540 | chrome | 104.17.153.238:443 | clipchamp.com | — | — | whitelisted |
39540 | chrome | 142.250.186.163:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
39540 | chrome | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
39540 | chrome | 151.101.1.91:443 | google-ohttp-relay-safebrowsing.fastly-edge.com | FASTLY | US | unknown |
39540 | chrome | 13.107.246.45:443 | wcpstatic.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clipchamp.com |
| whitelisted |
accounts.google.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
wcpstatic.microsoft.com |
| whitelisted |
s-part-0017.t-0009.fb-t-msedge.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
39540 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39540 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39540 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39540 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39540 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39540 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39540 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39540 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39540 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39540 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |