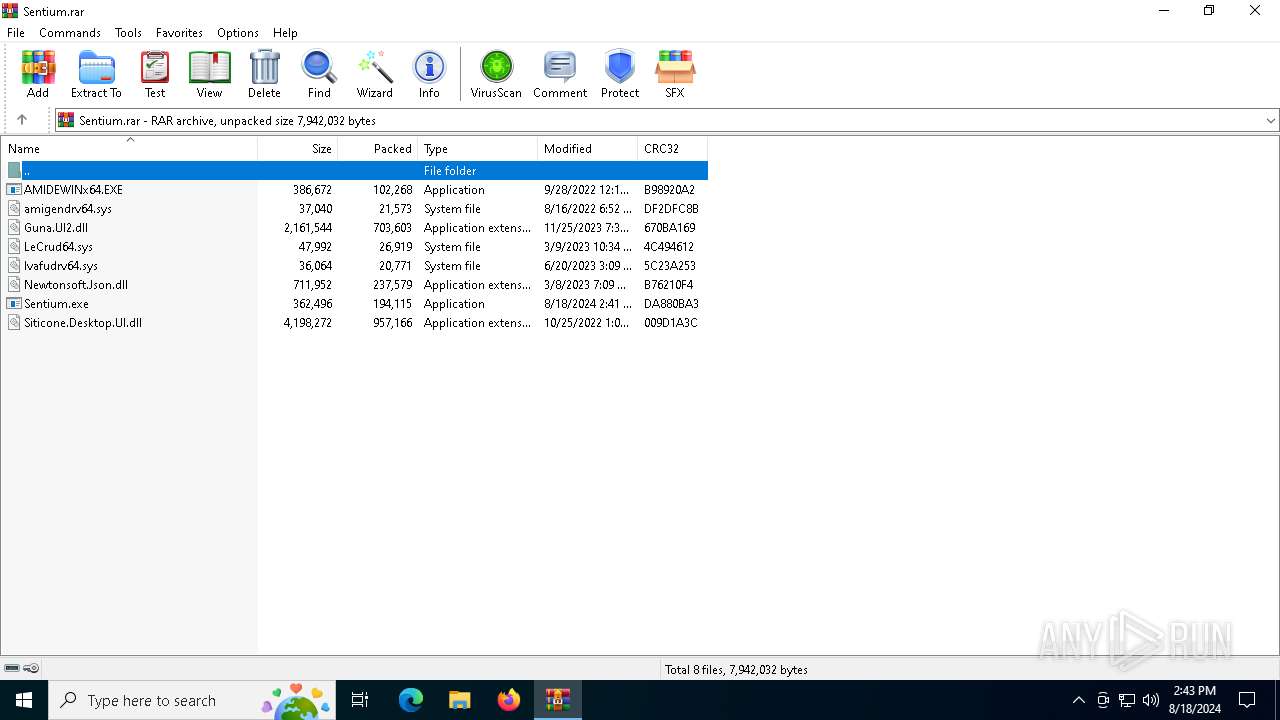
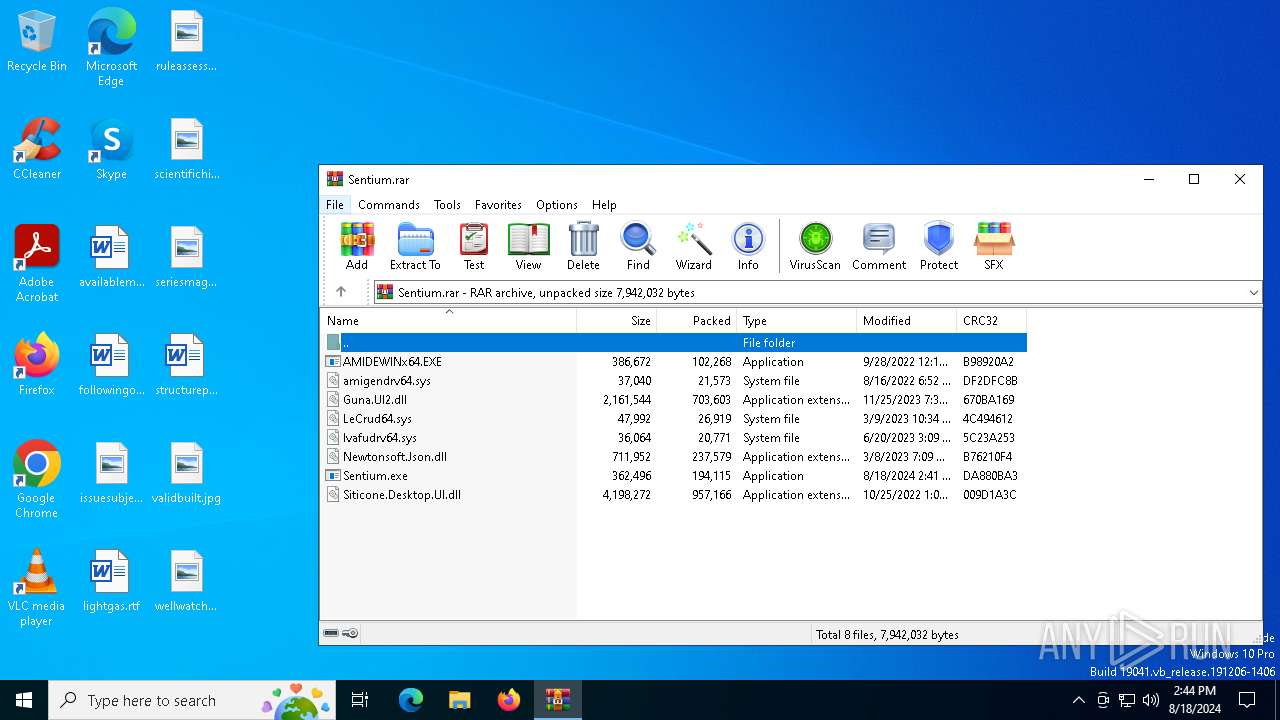
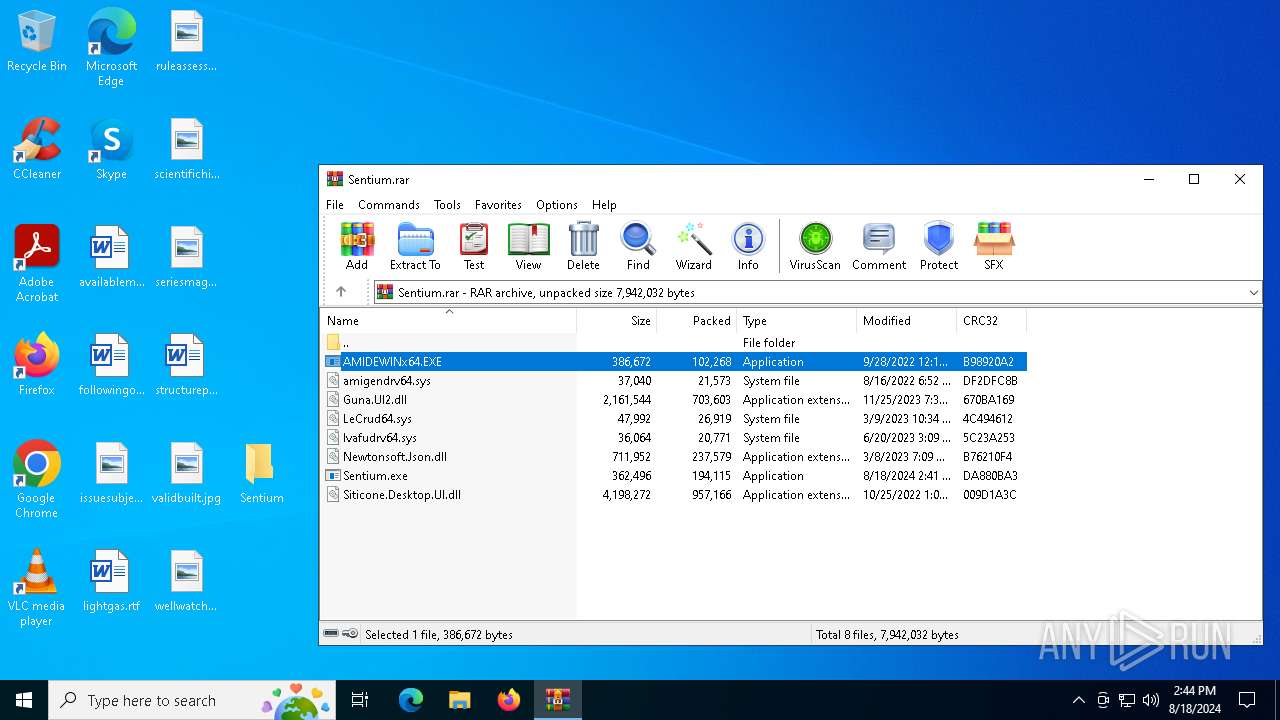
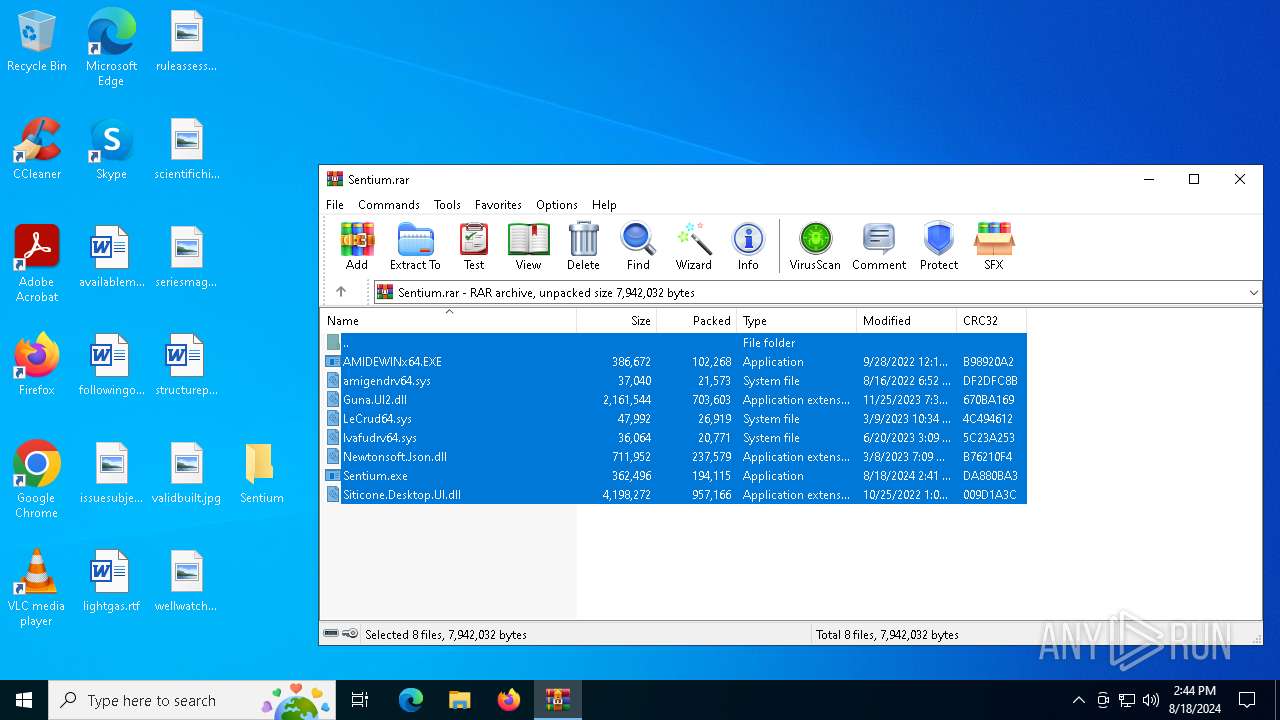
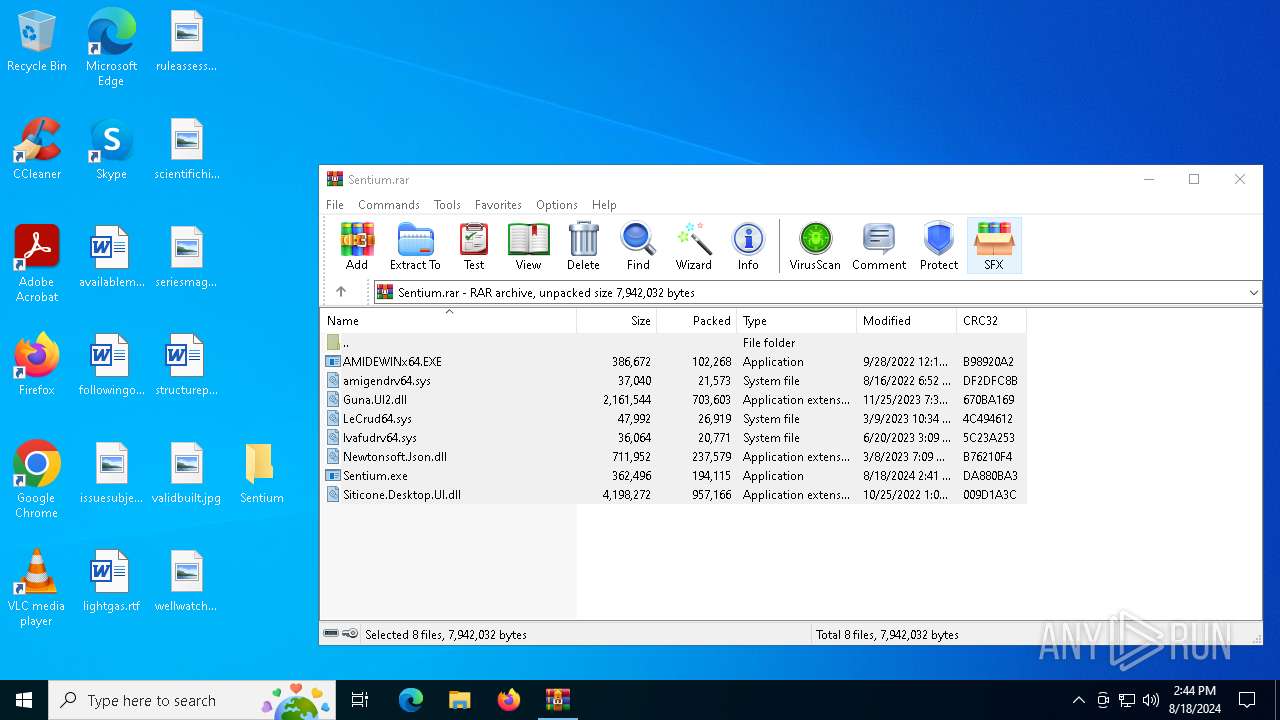
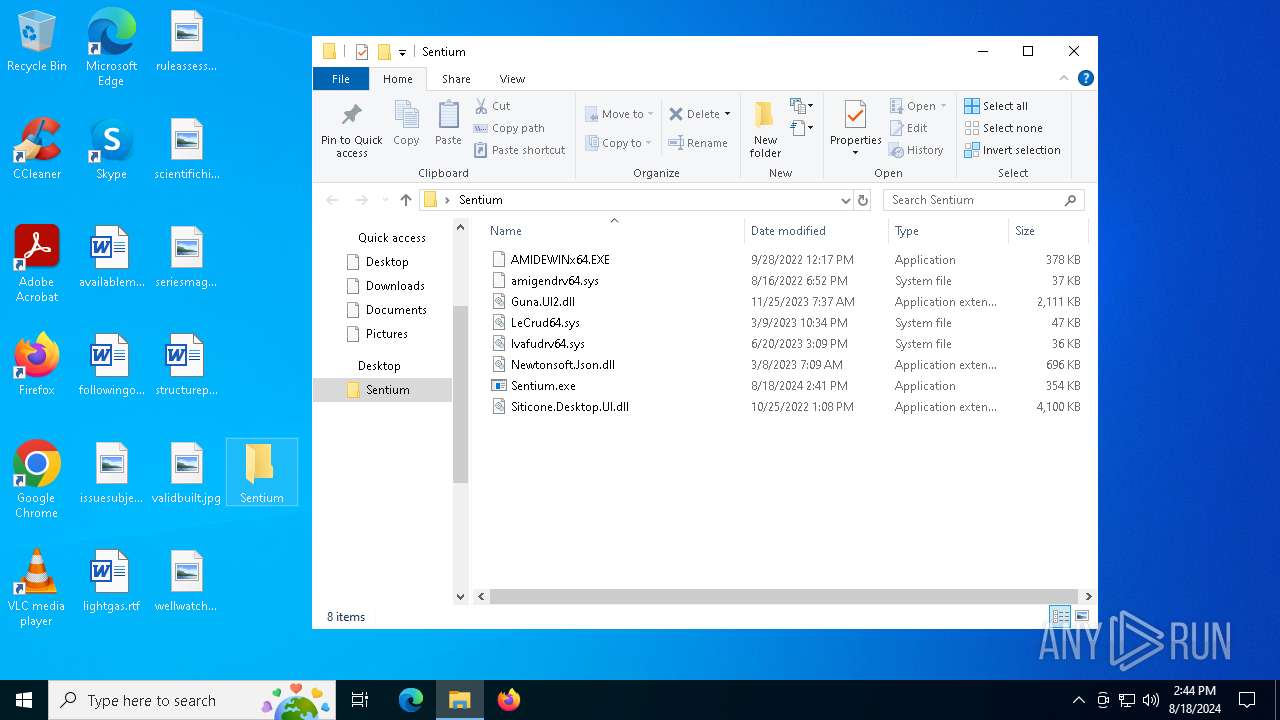
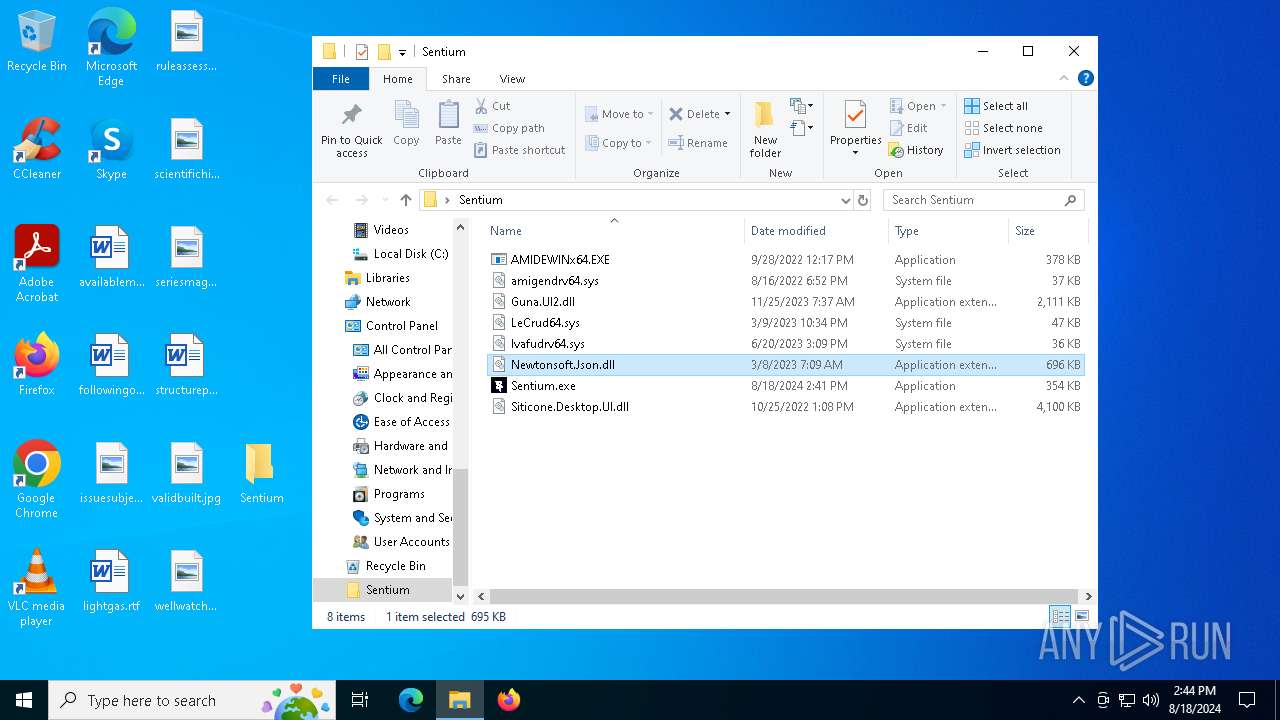
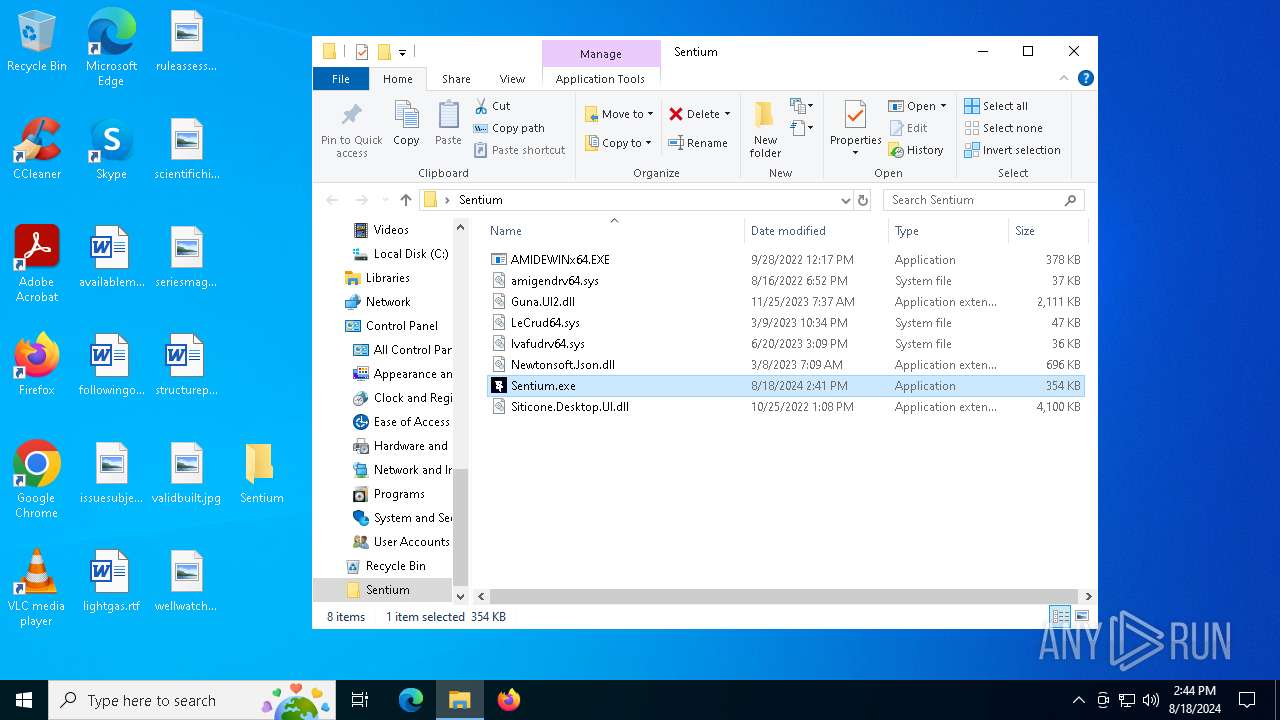
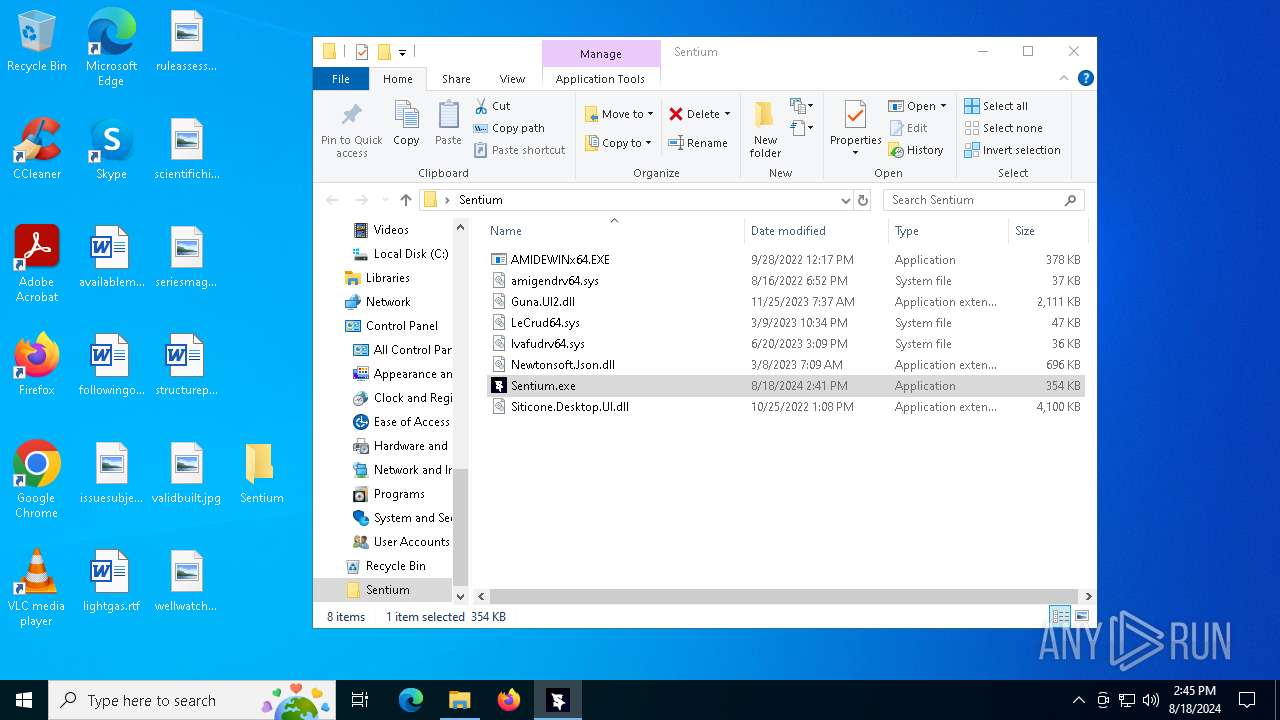
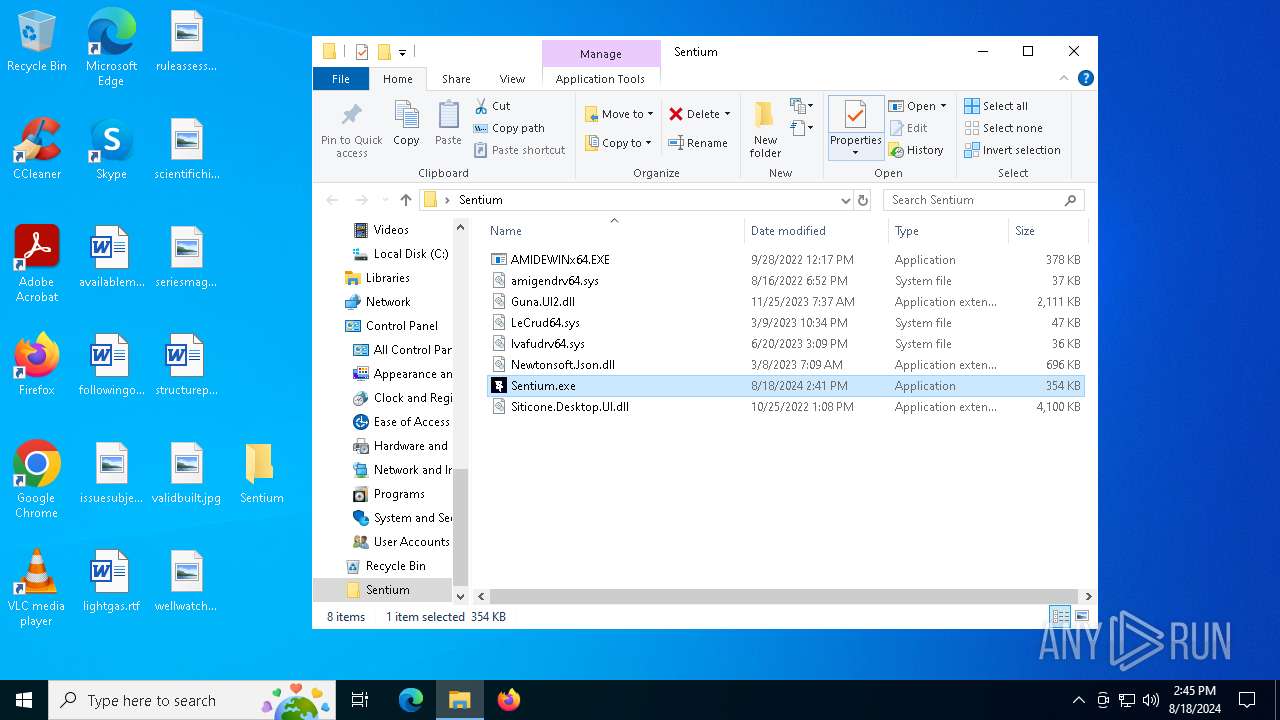
| File name: | Sentium.rar |
| Full analysis: | https://app.any.run/tasks/fbbd950b-cbbf-4969-beca-a2c1774e2b71 |
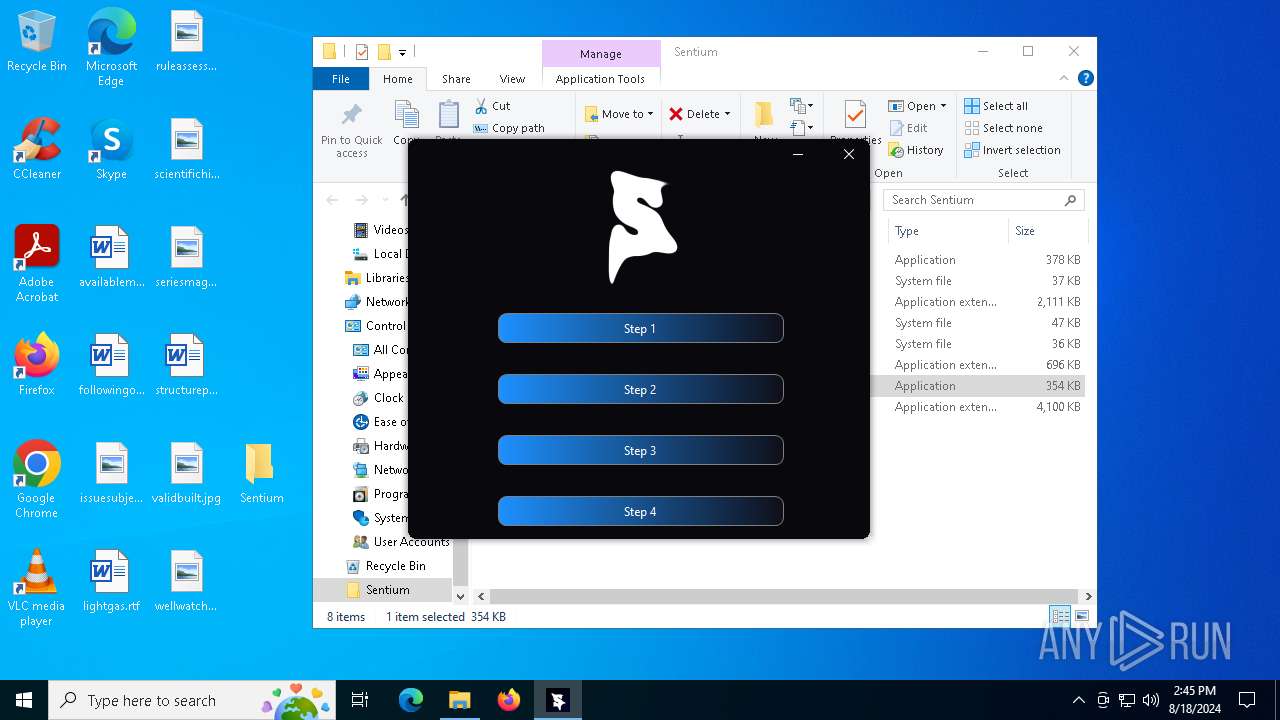
| Verdict: | Malicious activity |
| Analysis date: | August 18, 2024, 14:43:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | FB3CFD01571E188BCF0E86EC6B41F045 |
| SHA1: | 0CC0BAAE4307EA5E3F07777192039379EA68A161 |
| SHA256: | A734075B50DF605ED0A9B960ED81284292EA11DB3D1E58DCE59CF7013A682493 |
| SSDEEP: | 98304:RZio4mkGVTOancH+xSgTsyW8Hn2gBS4Zi1rxYs9qMzhIKmxfj9s1n0d0wMpHyxJa:RP0xL/ |
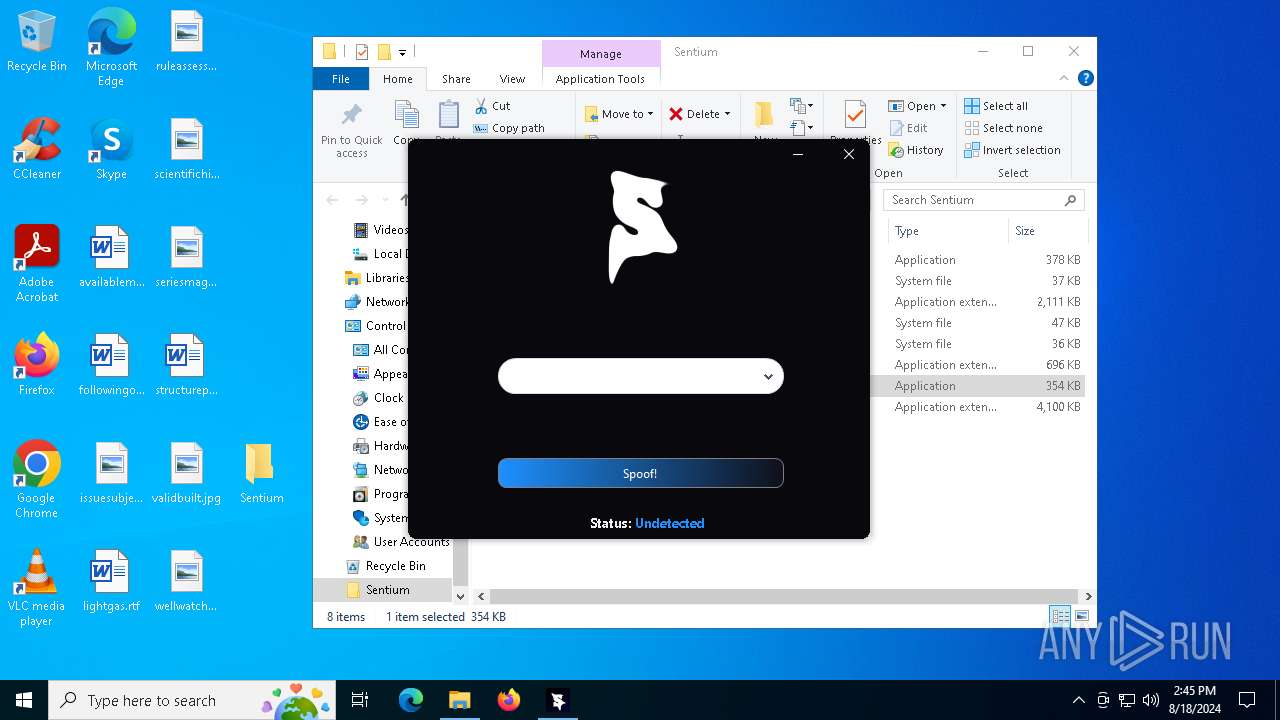
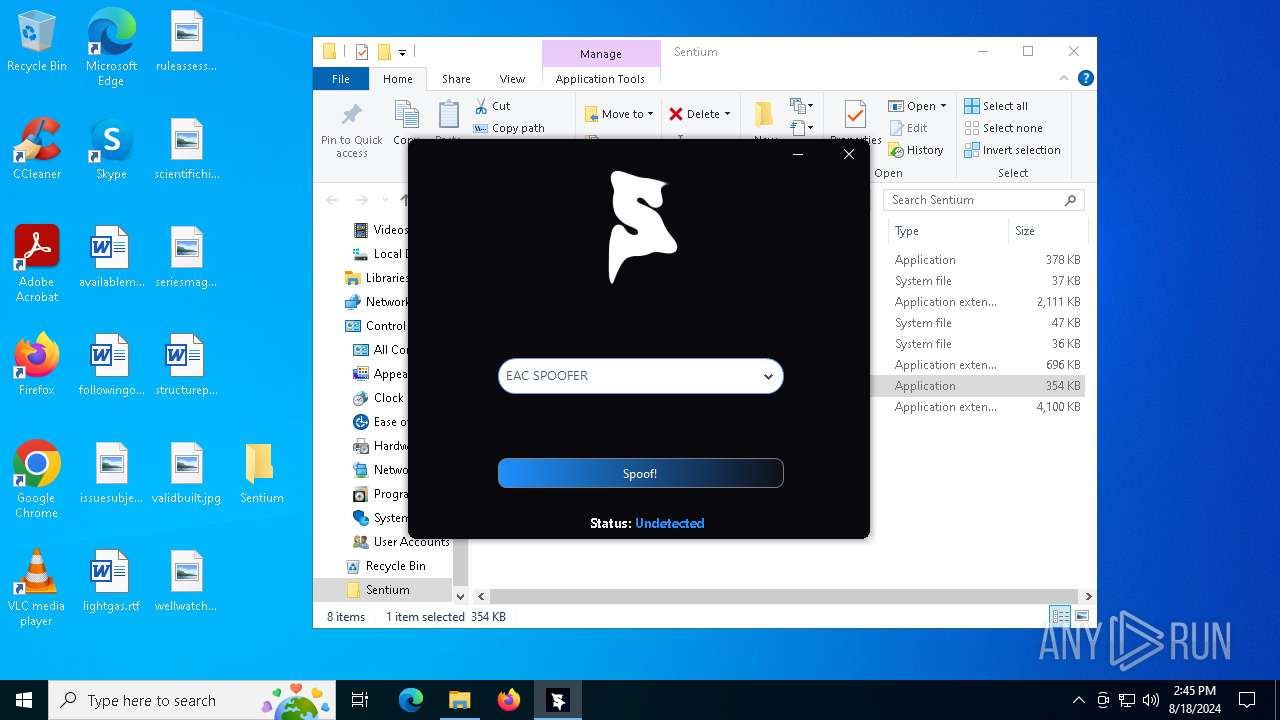
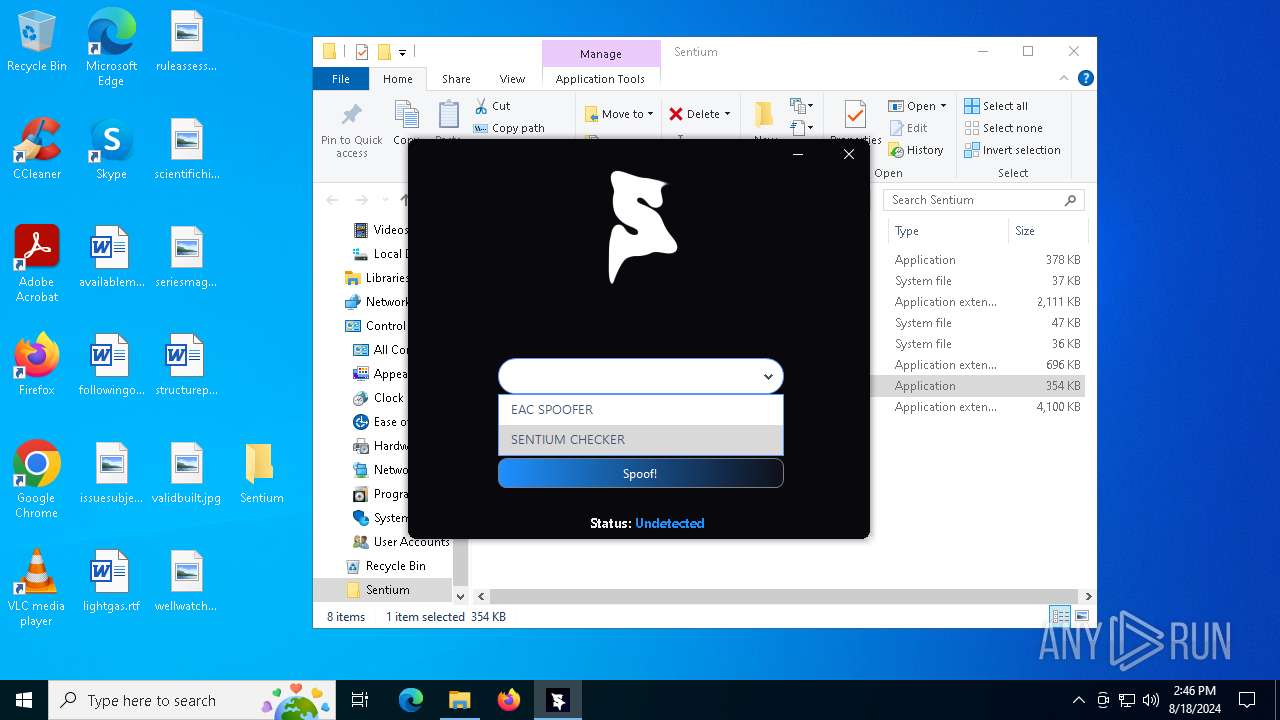
MALICIOUS
No malicious indicators.SUSPICIOUS
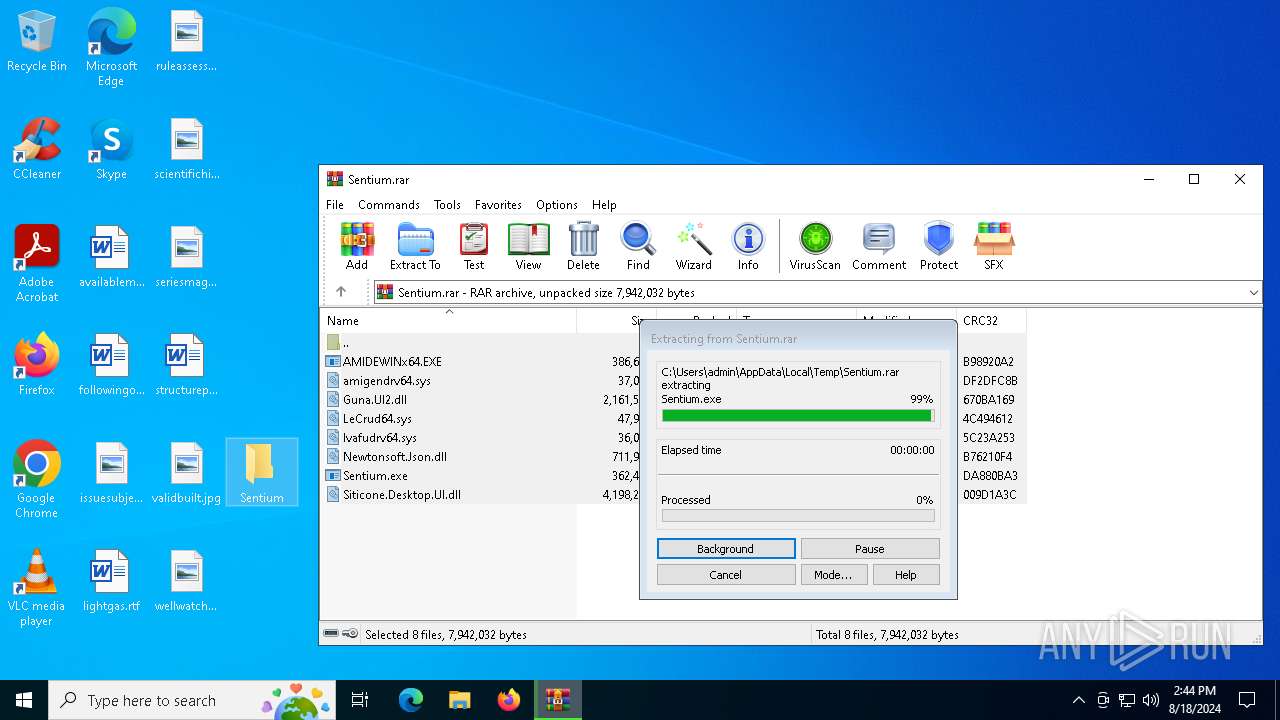
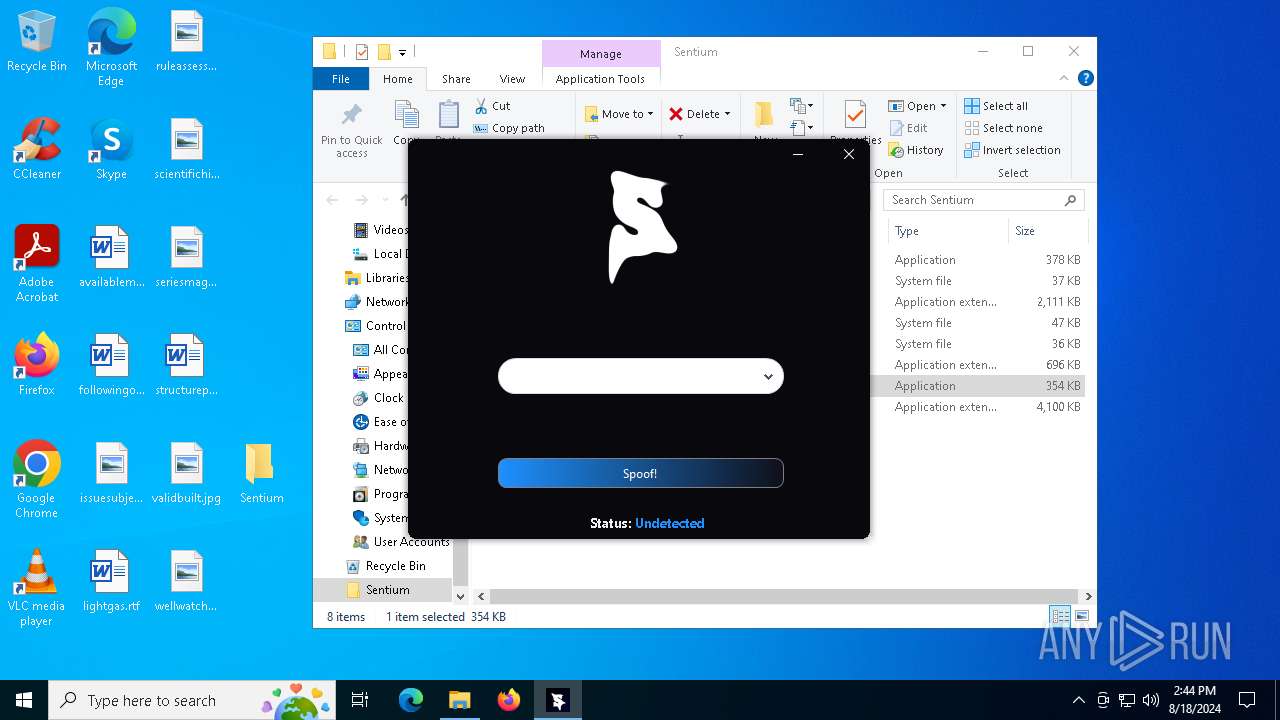
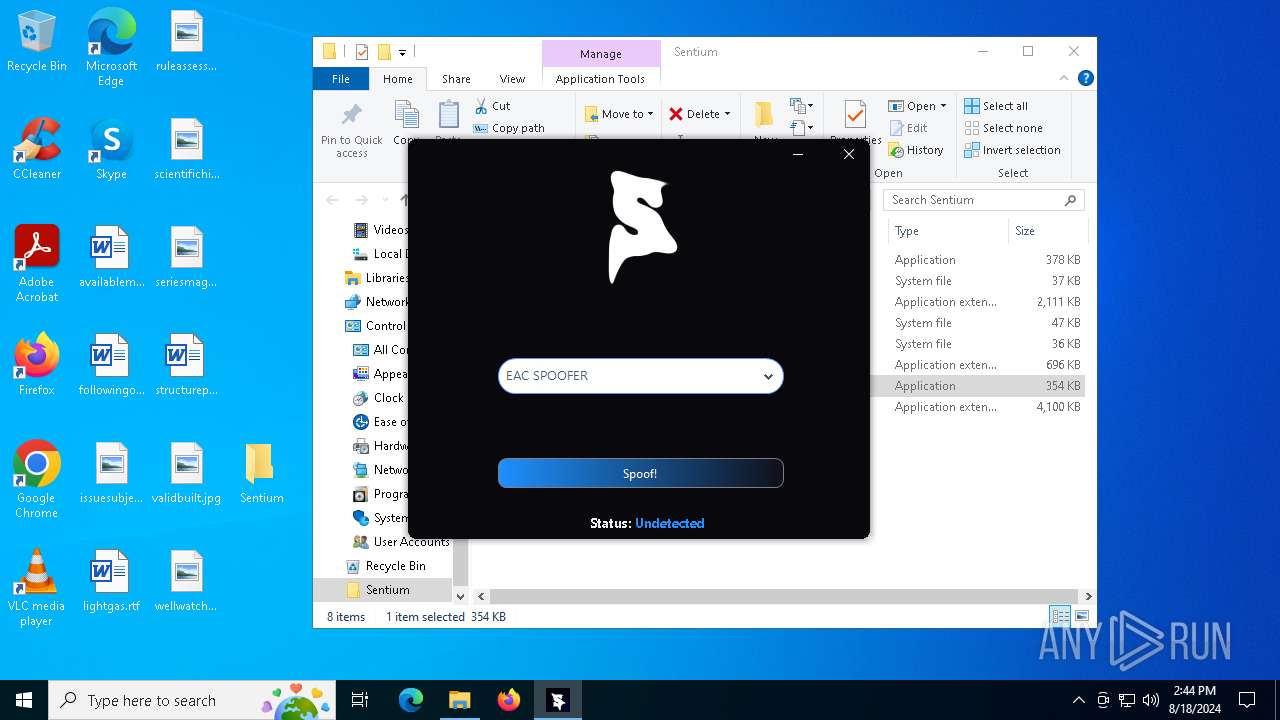
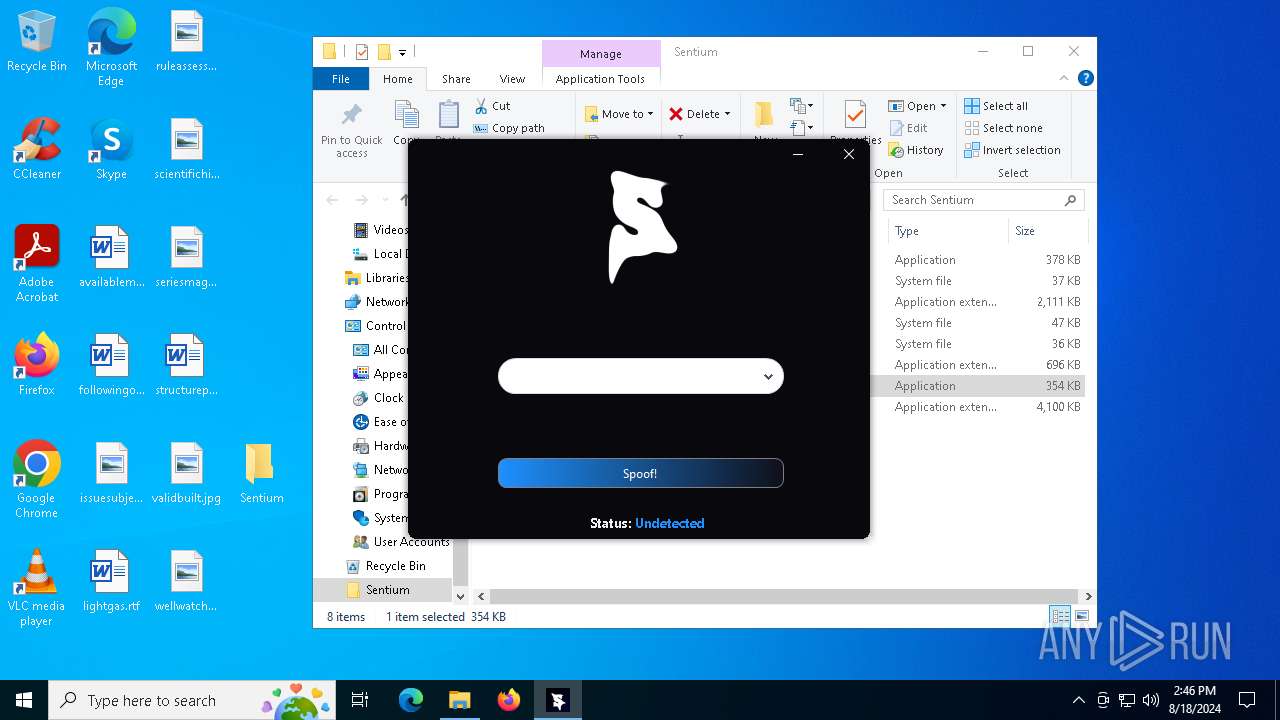
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6304)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6304)
Reads security settings of Internet Explorer
- Sentium.exe (PID: 3276)
- Sentium.exe (PID: 1372)
- Sentium.exe (PID: 5492)
There is functionality for taking screenshot (YARA)
- Sentium.exe (PID: 3276)
- Sentium.exe (PID: 1372)
- Sentium.exe (PID: 5492)
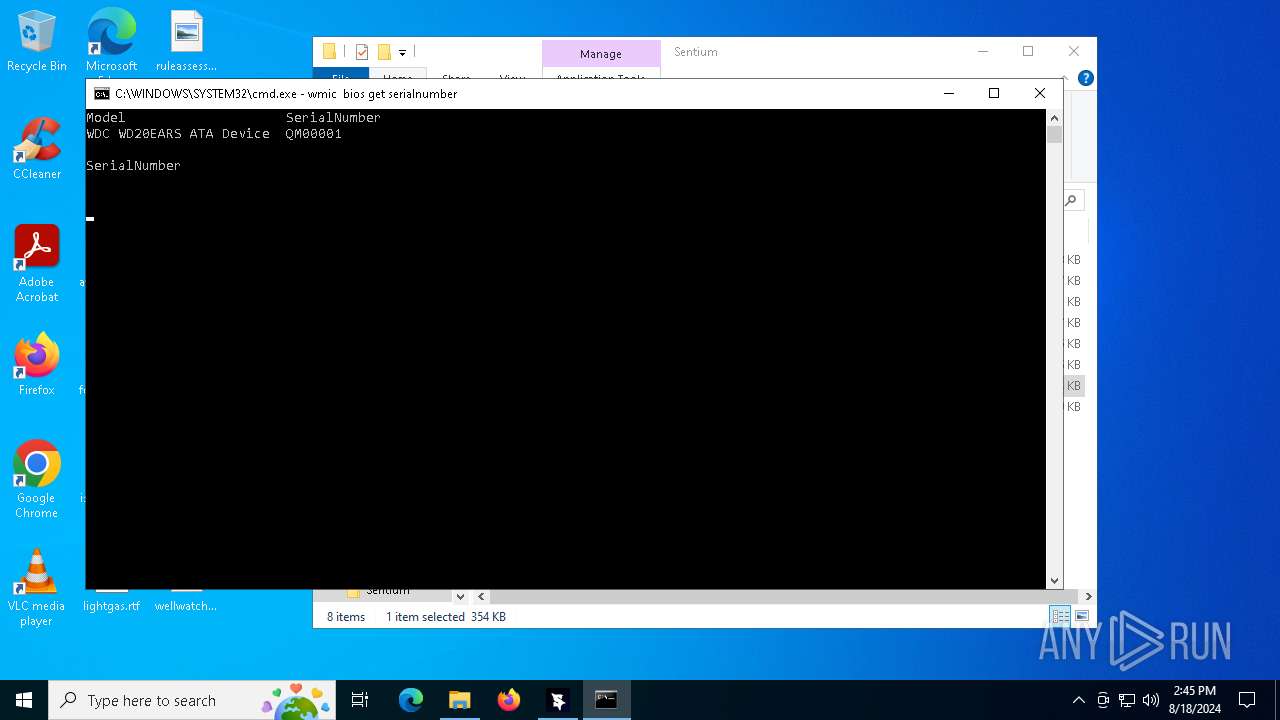
Hides command output
- cmd.exe (PID: 1168)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 1168)
Starts CMD.EXE for commands execution
- Sentium.exe (PID: 1372)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 1168)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 5552)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 1168)
Uses WMIC.EXE to obtain data on the base board management (motherboard or system board)
- cmd.exe (PID: 1168)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1168)
INFO
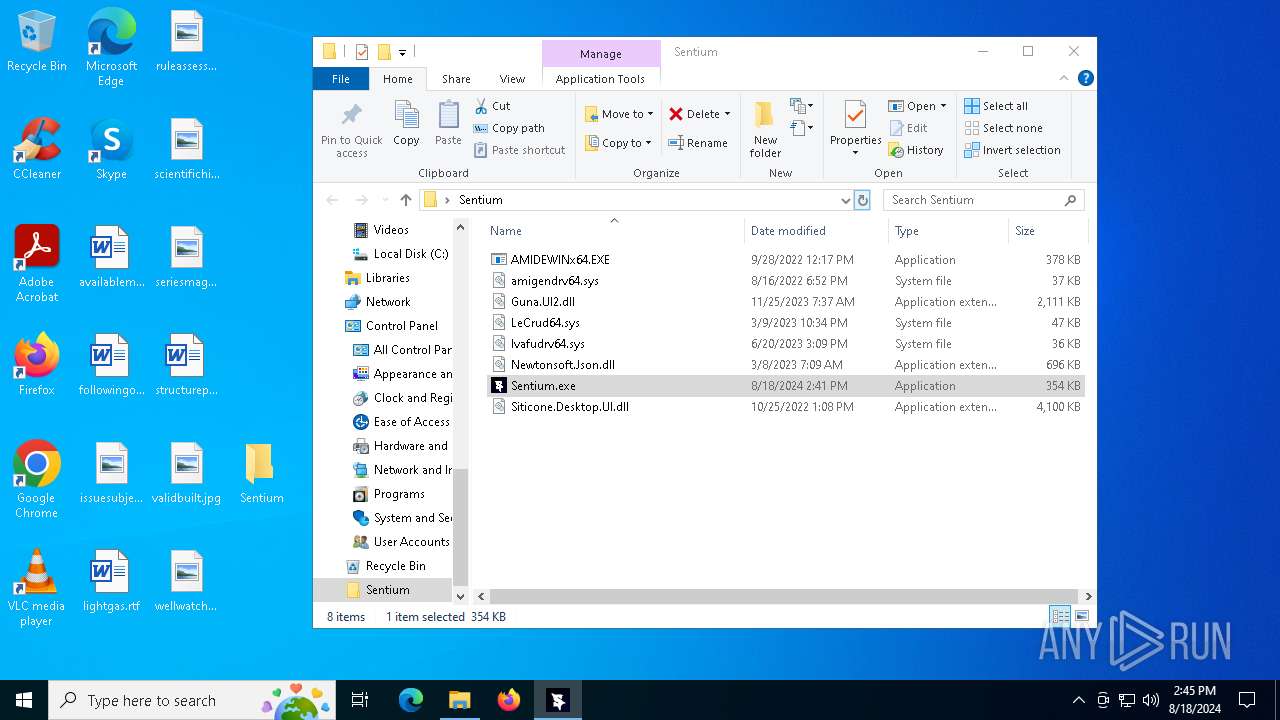
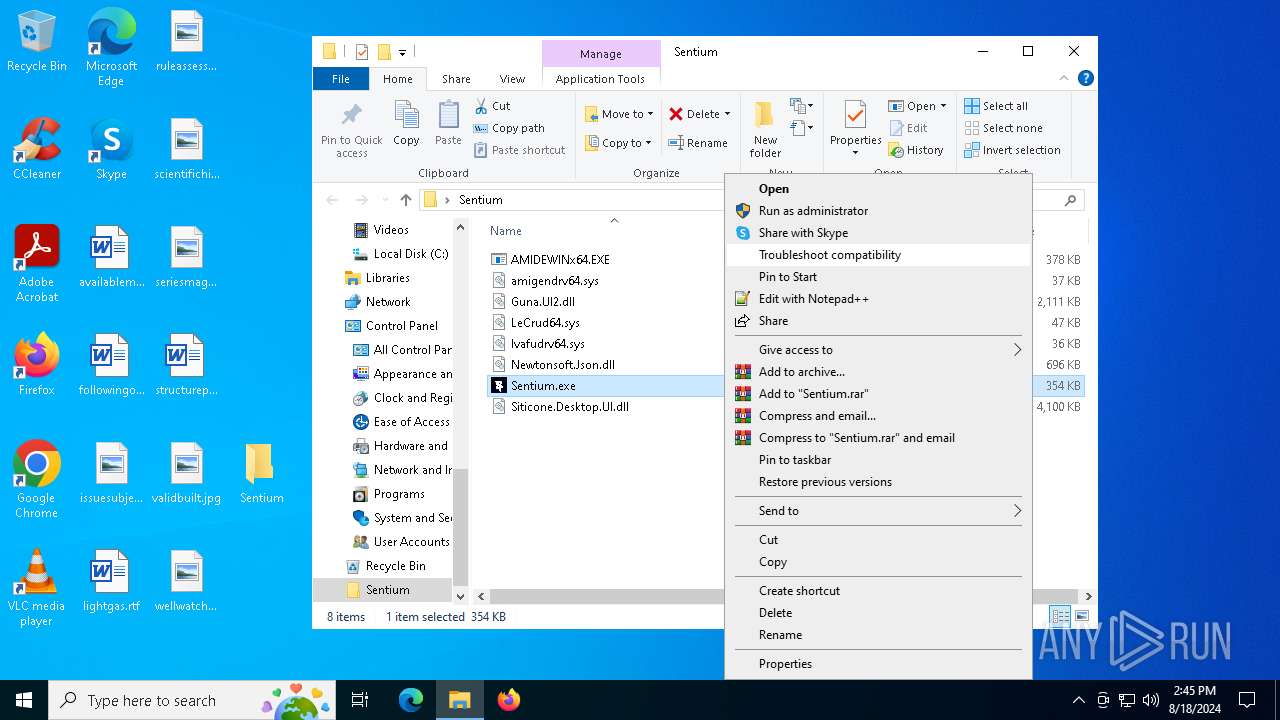
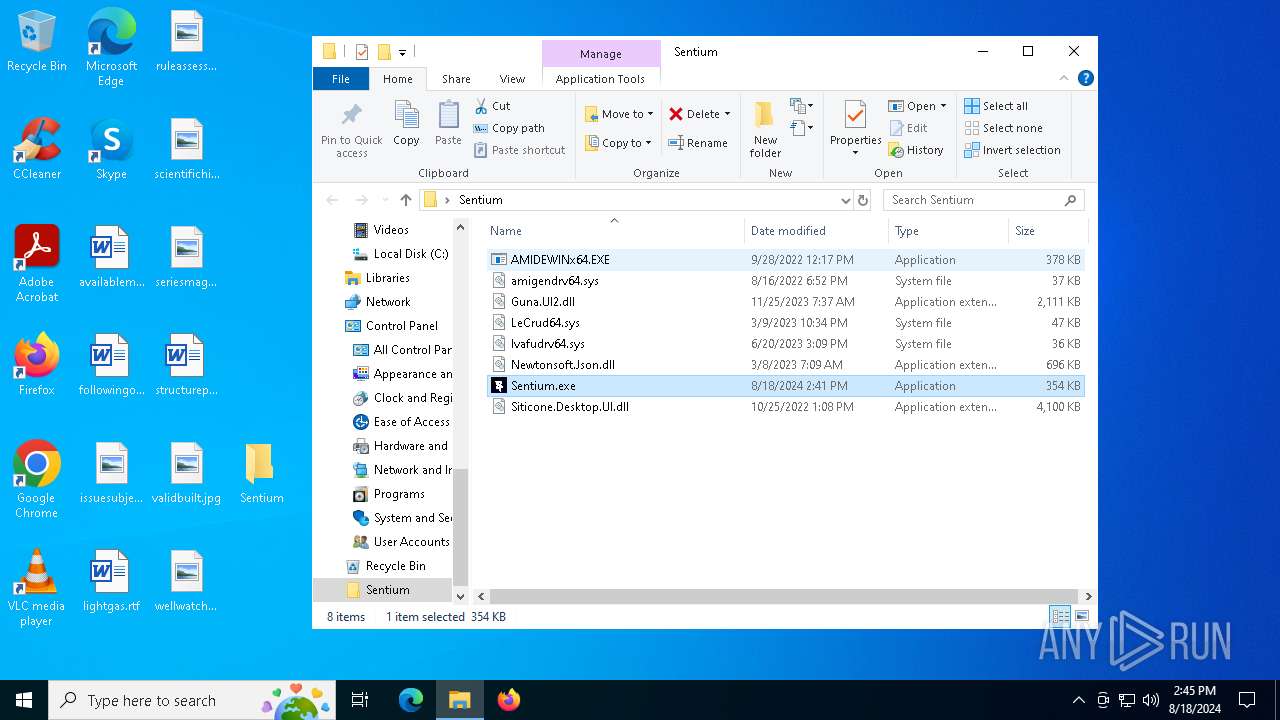
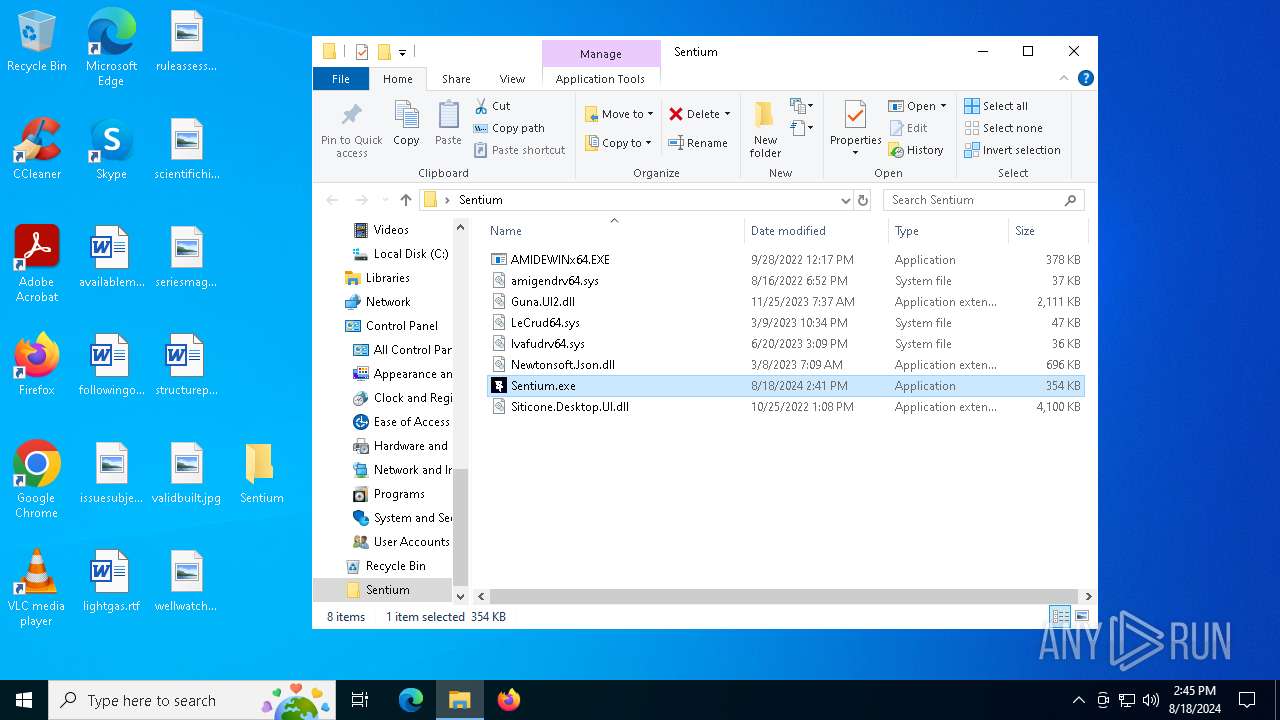
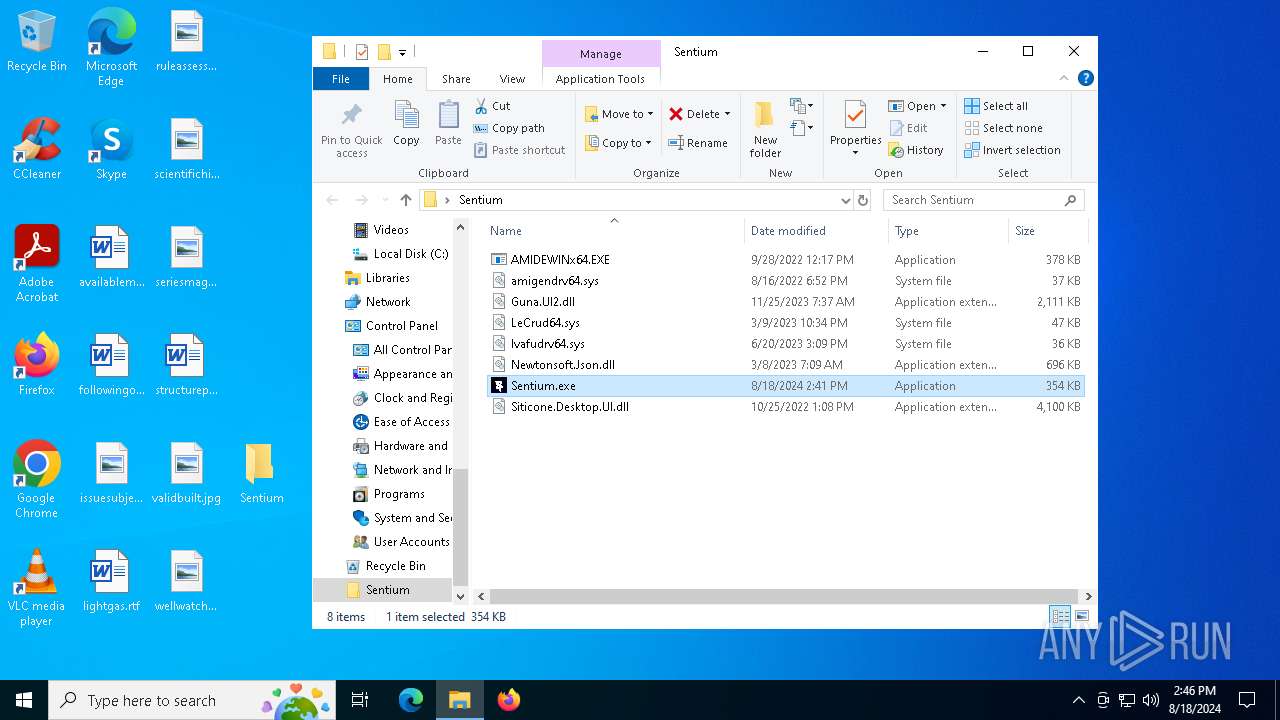
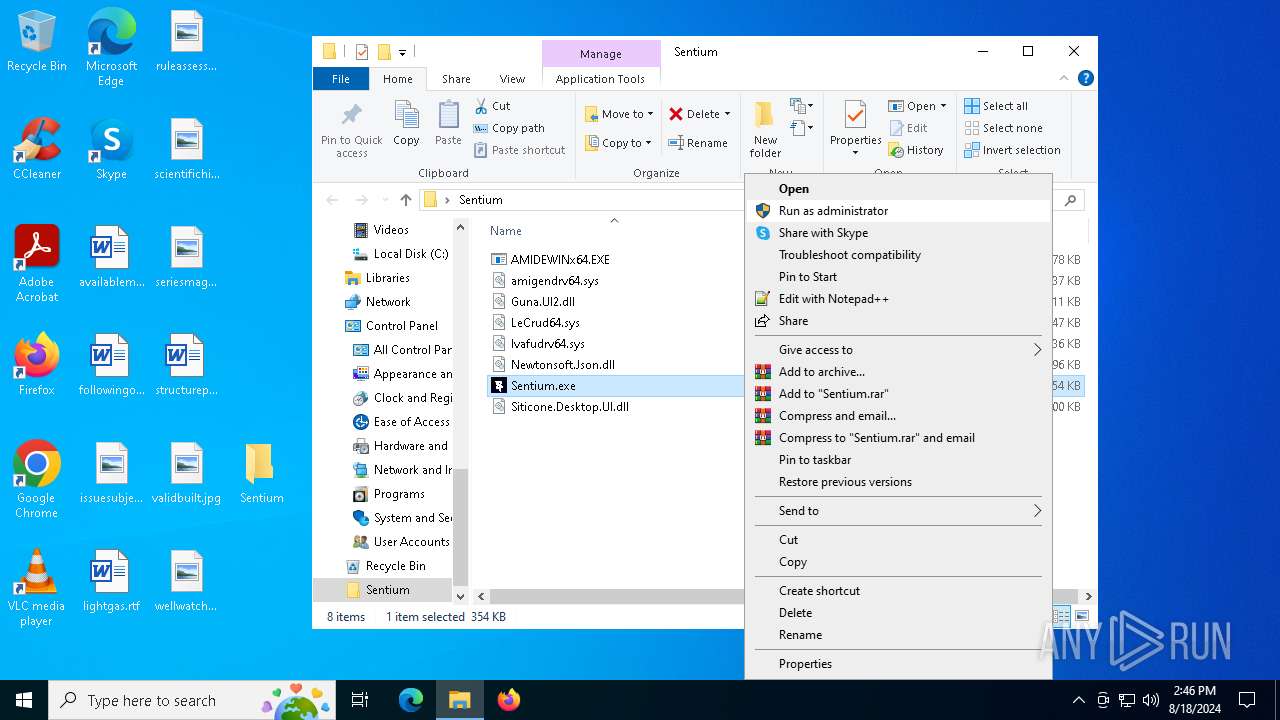
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6304)
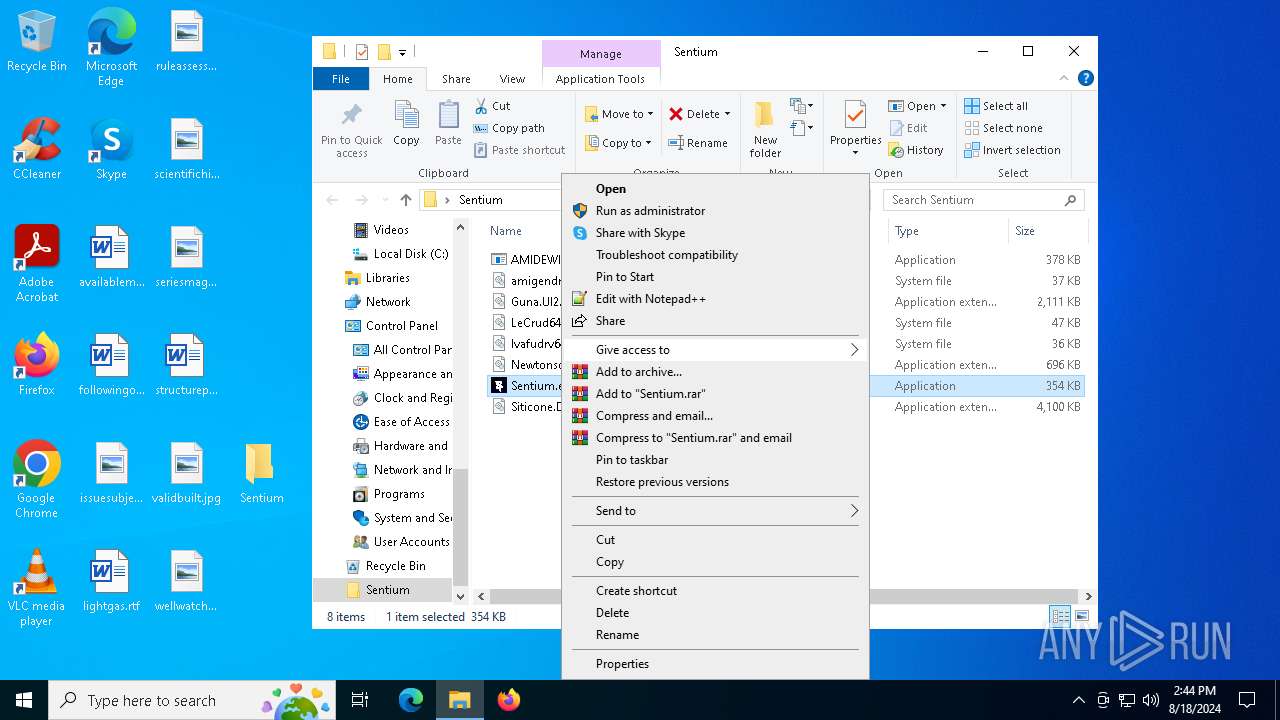
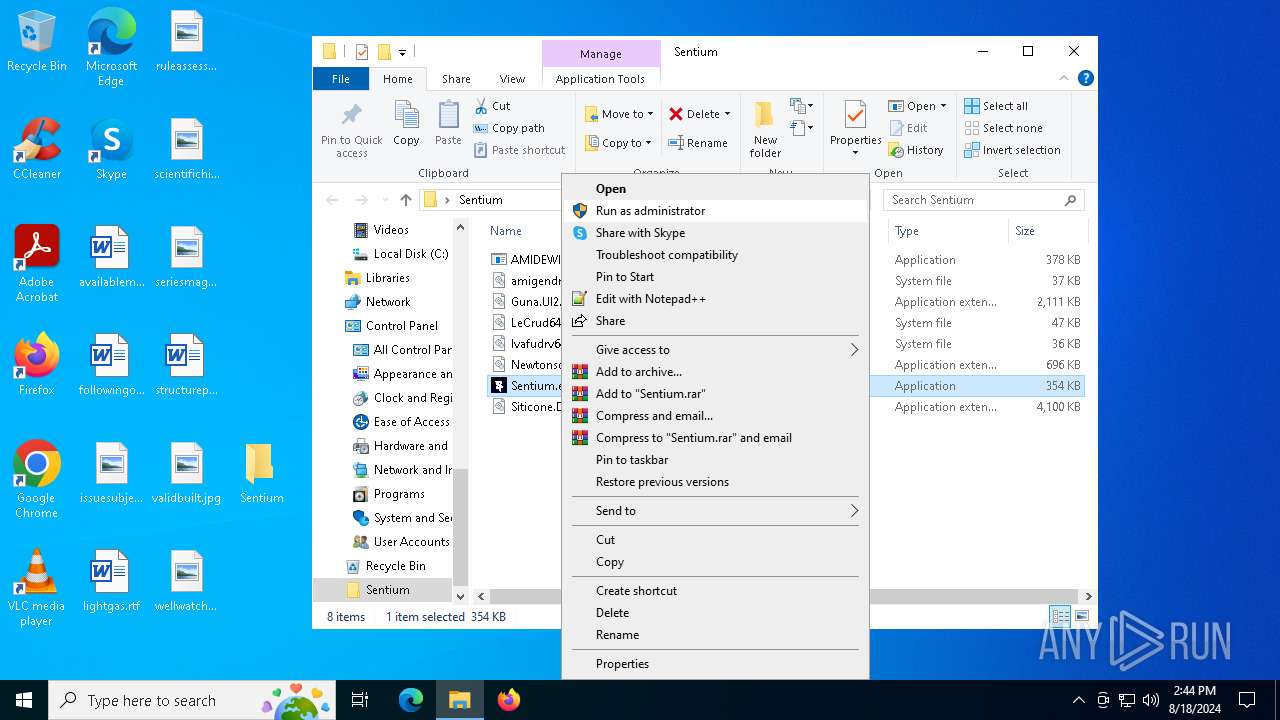
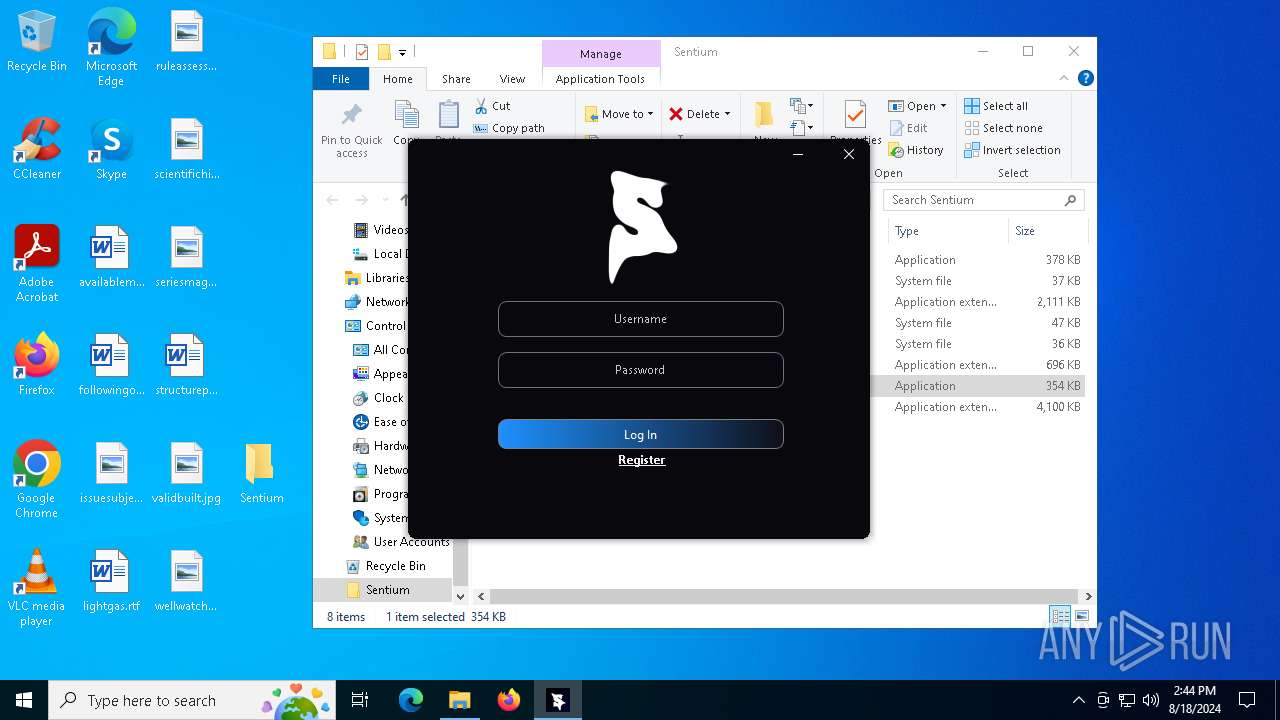
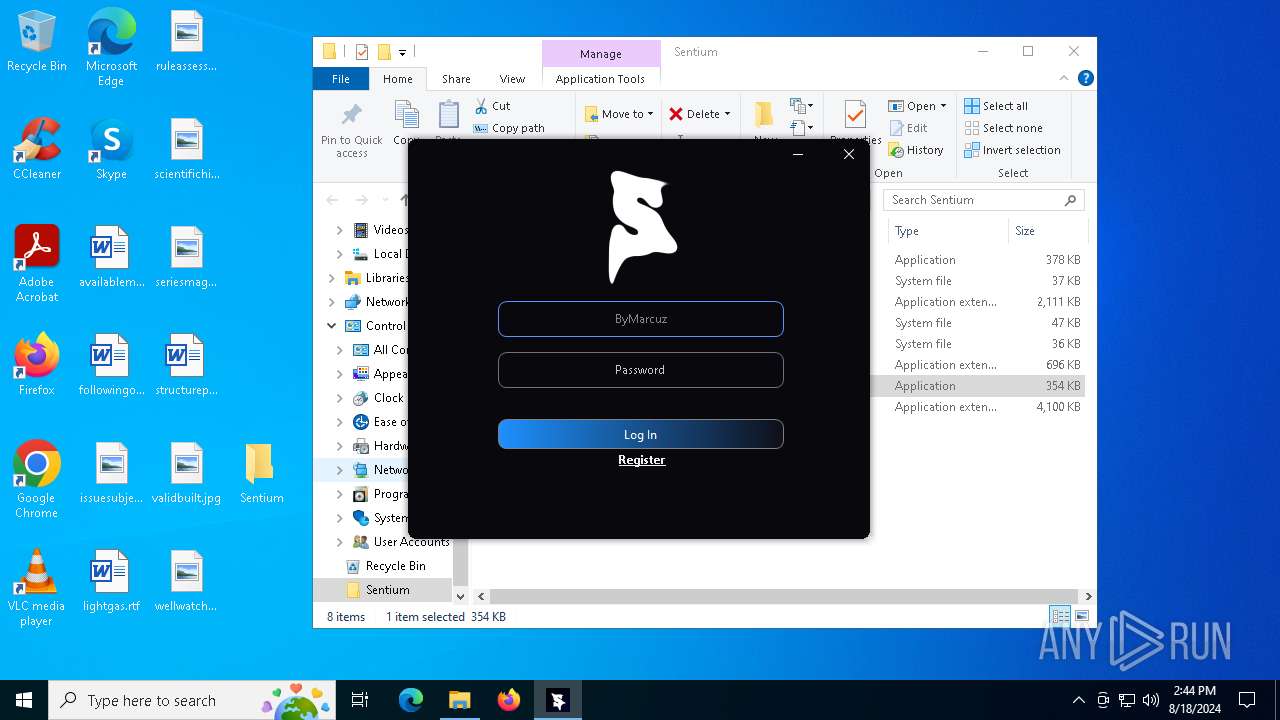
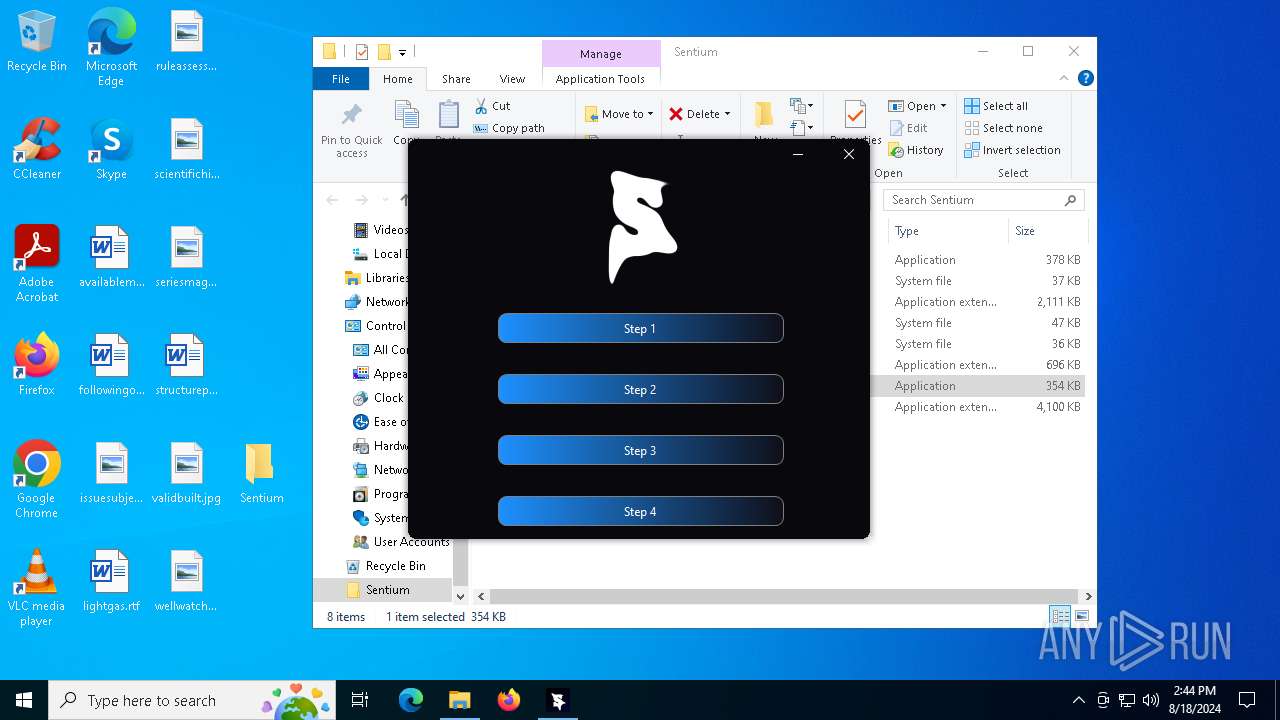
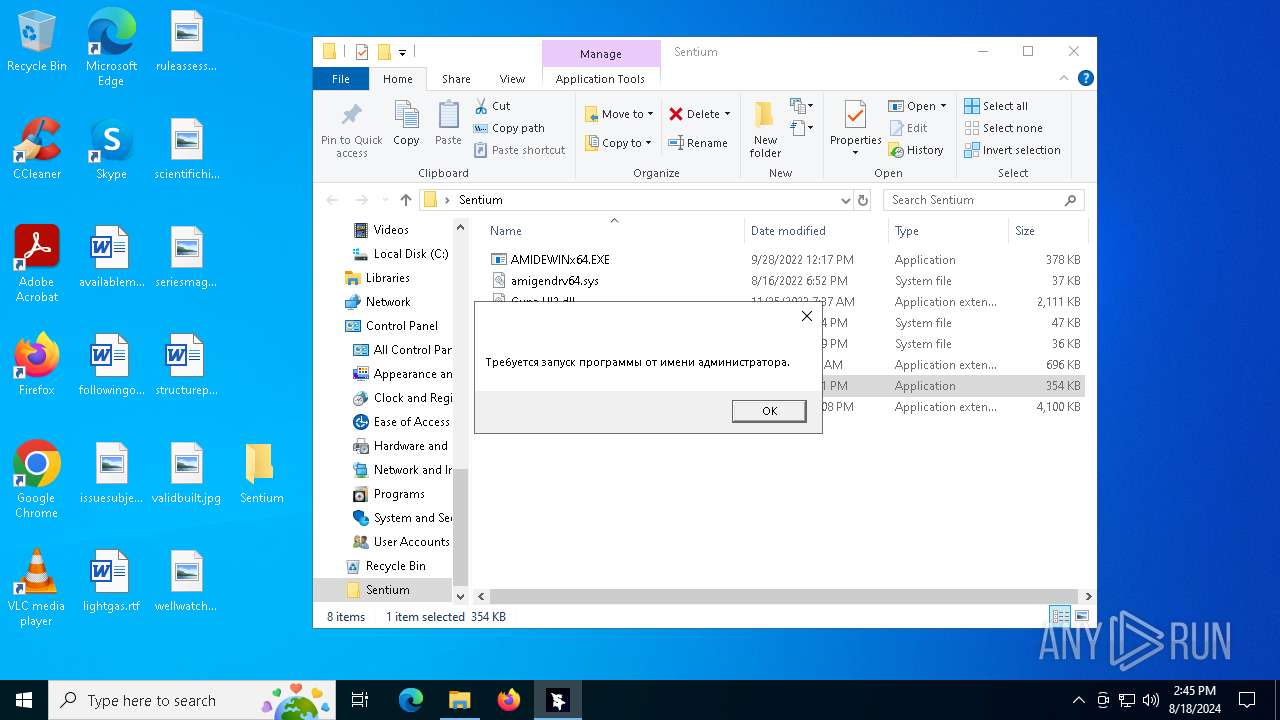
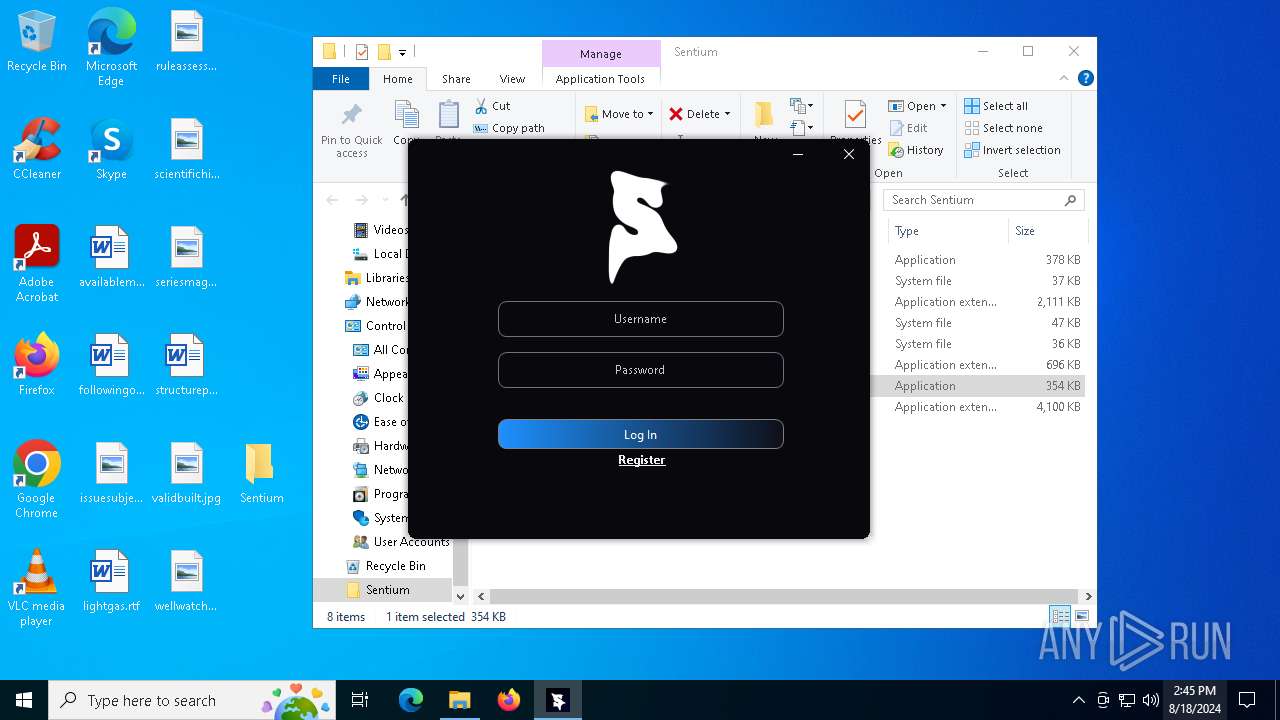
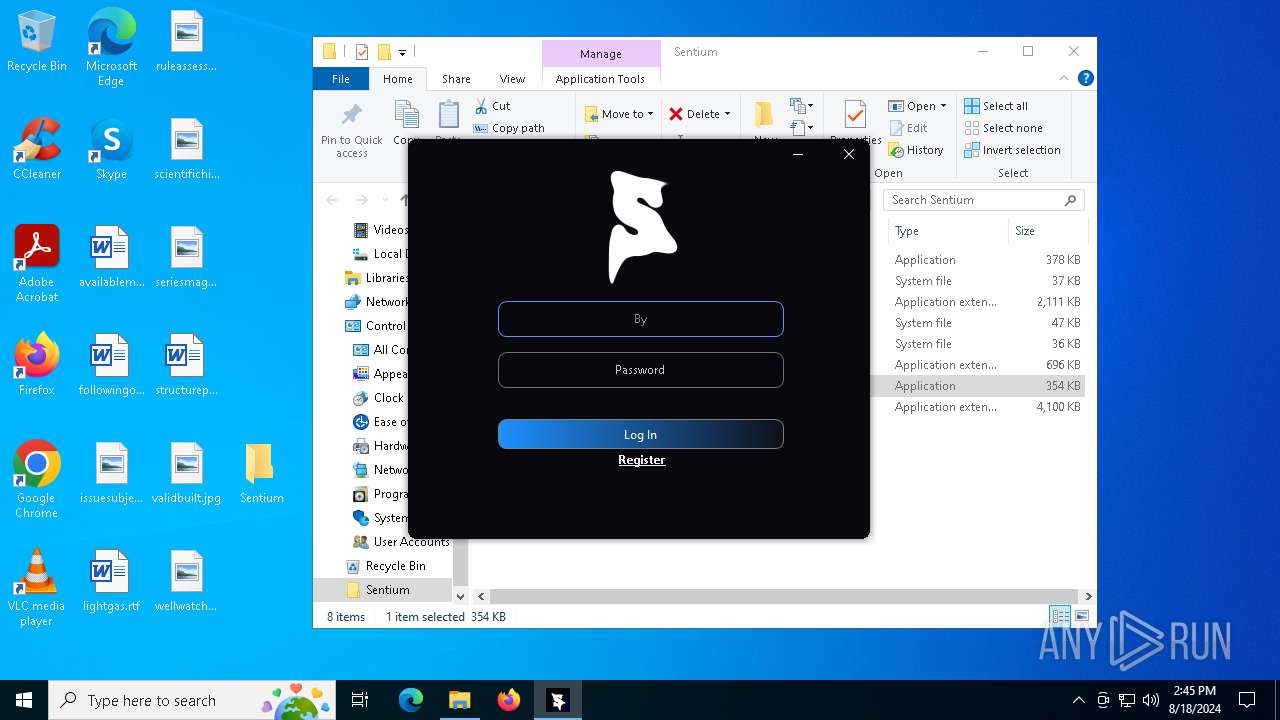
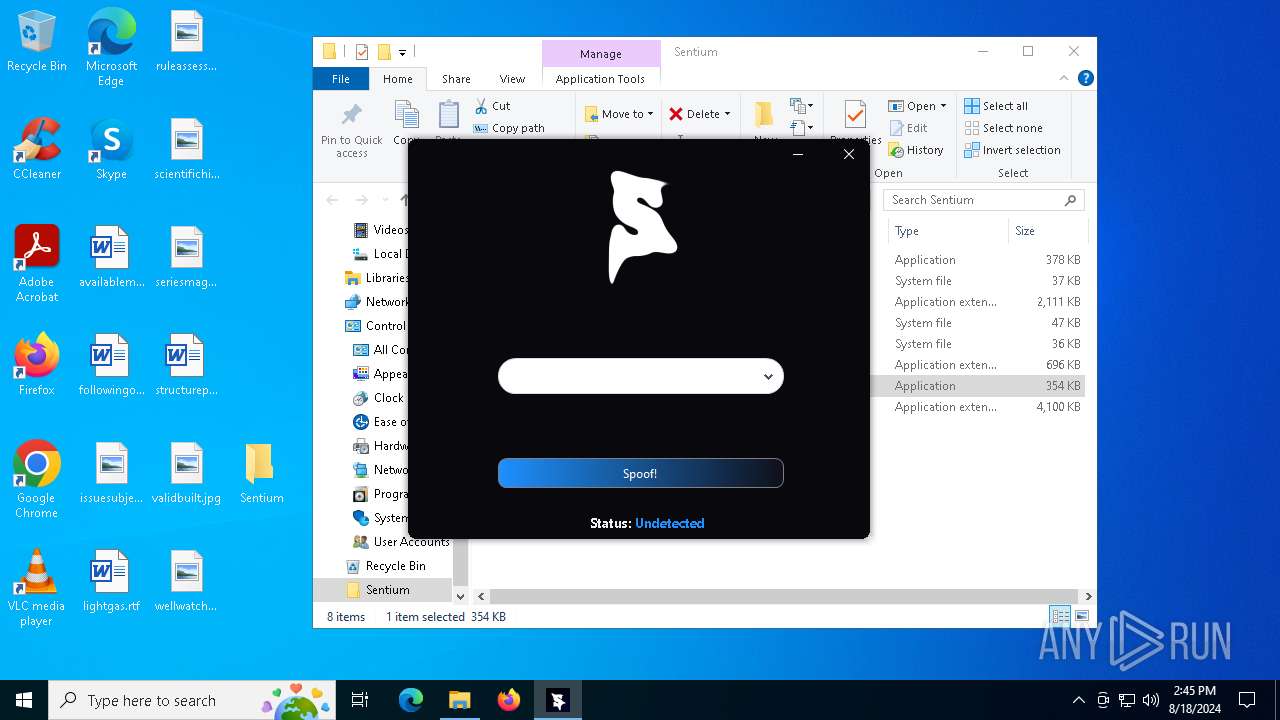
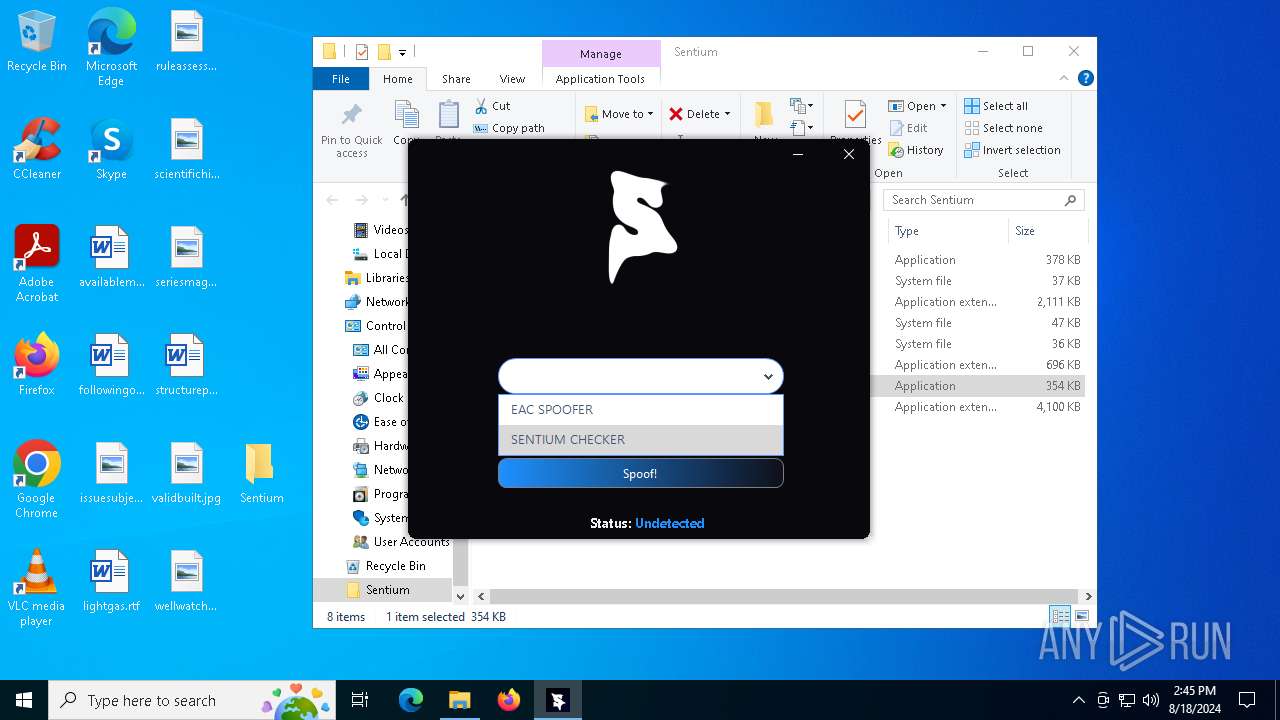
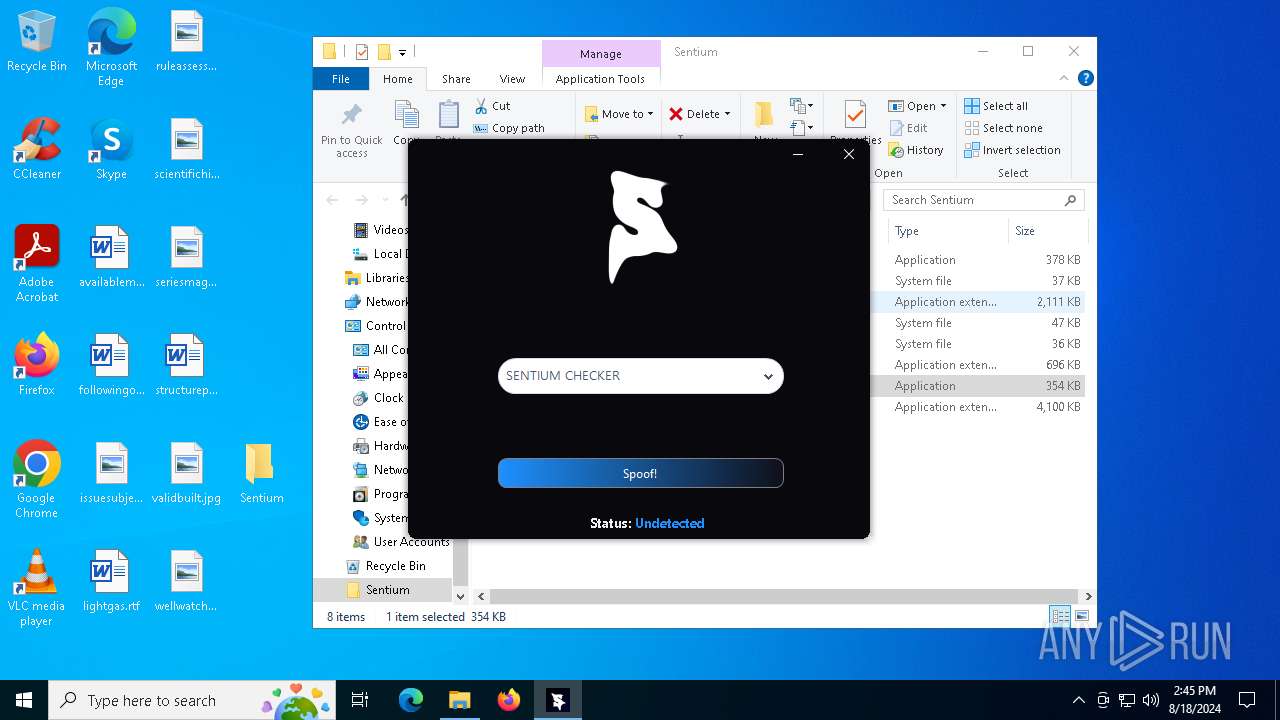
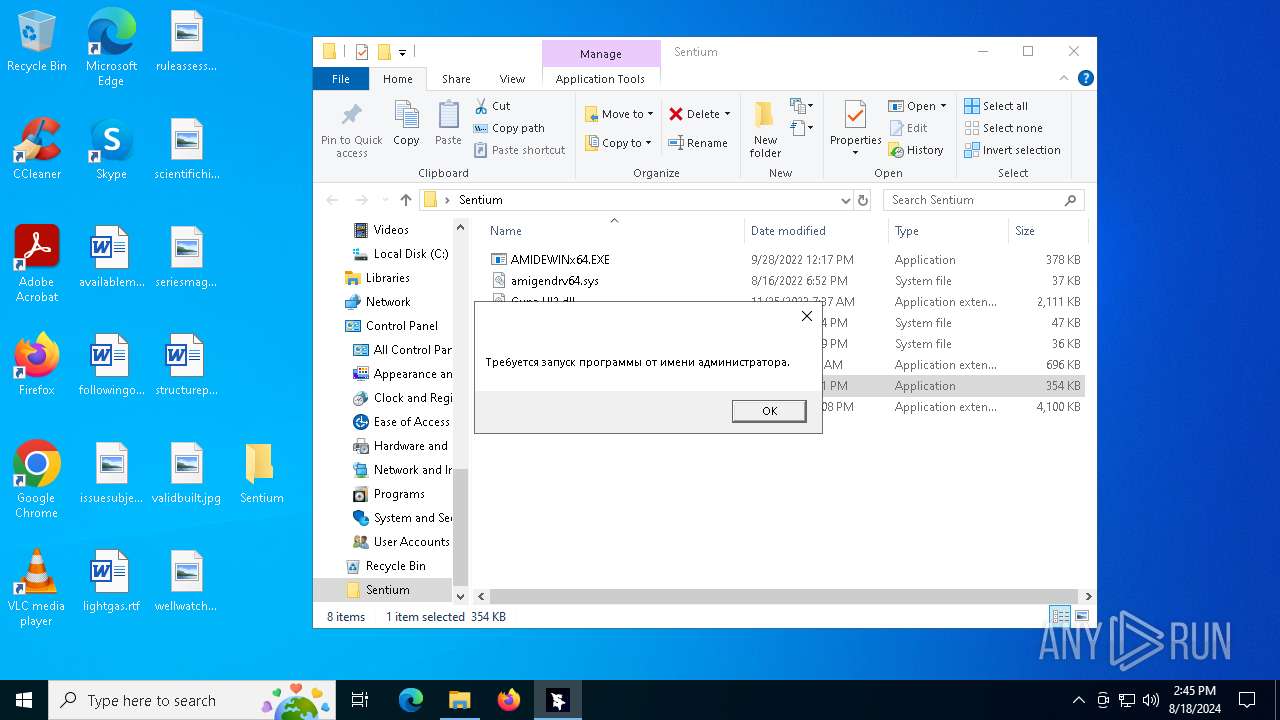
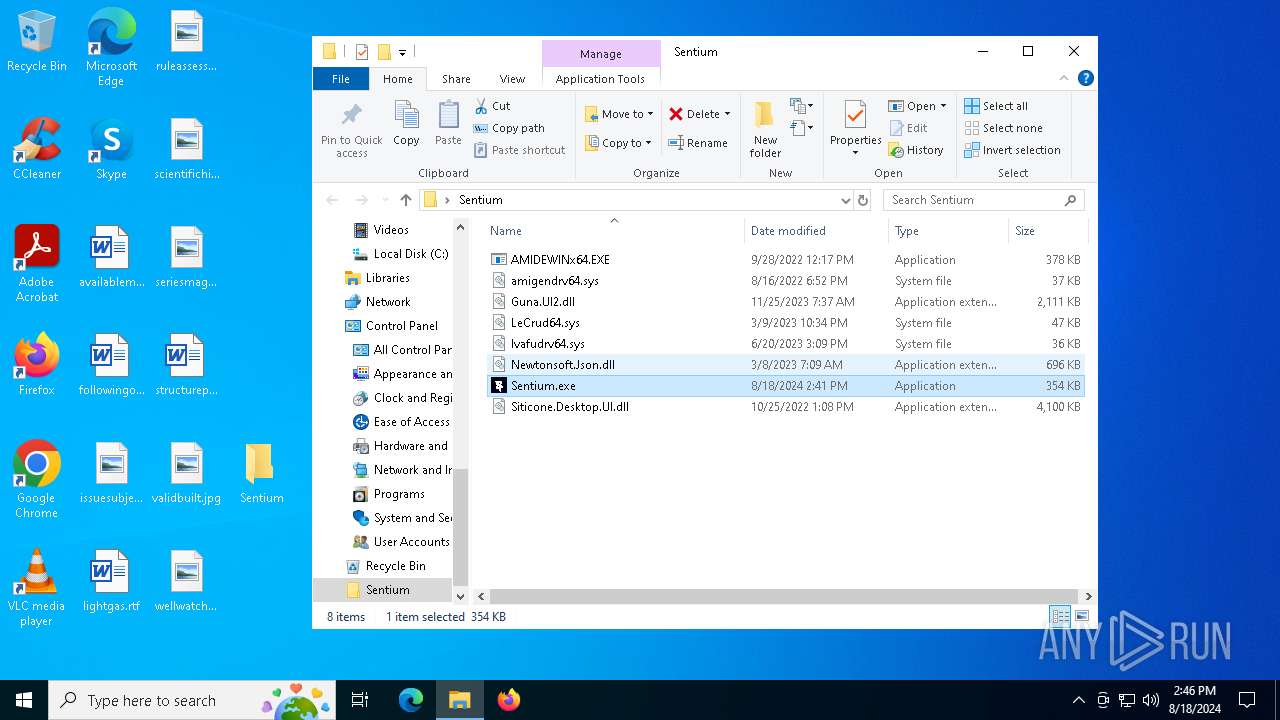
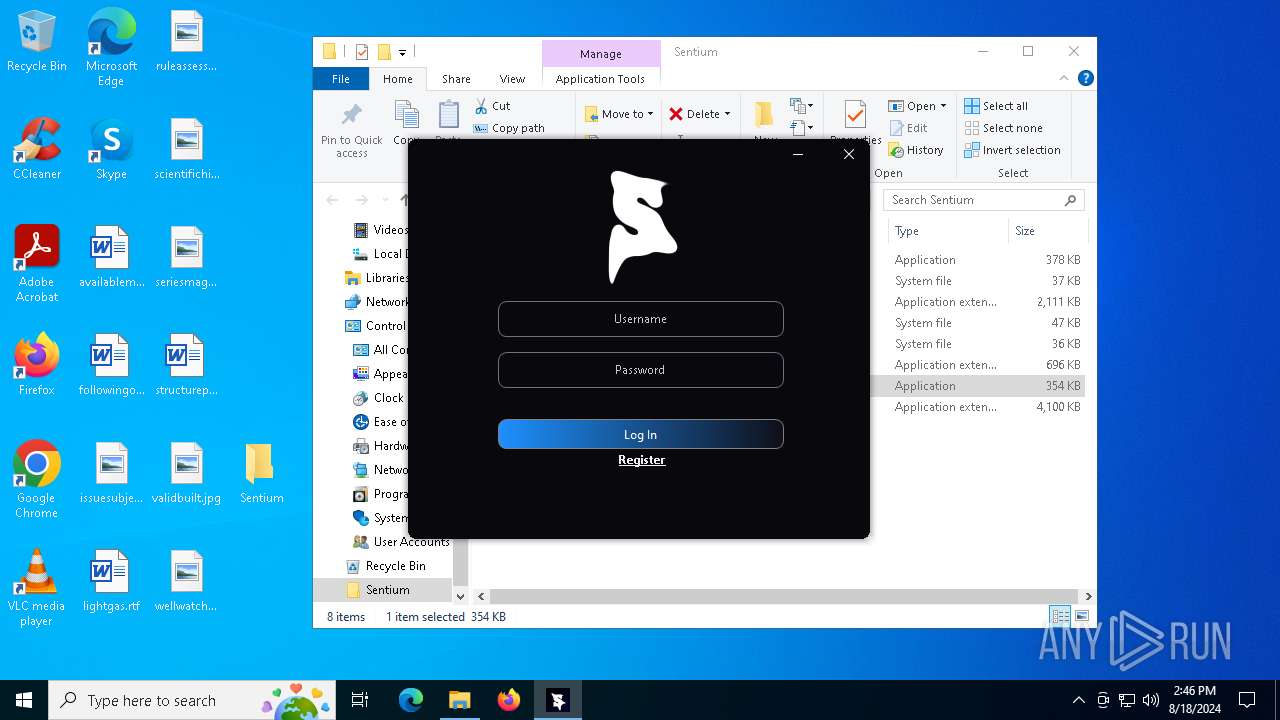
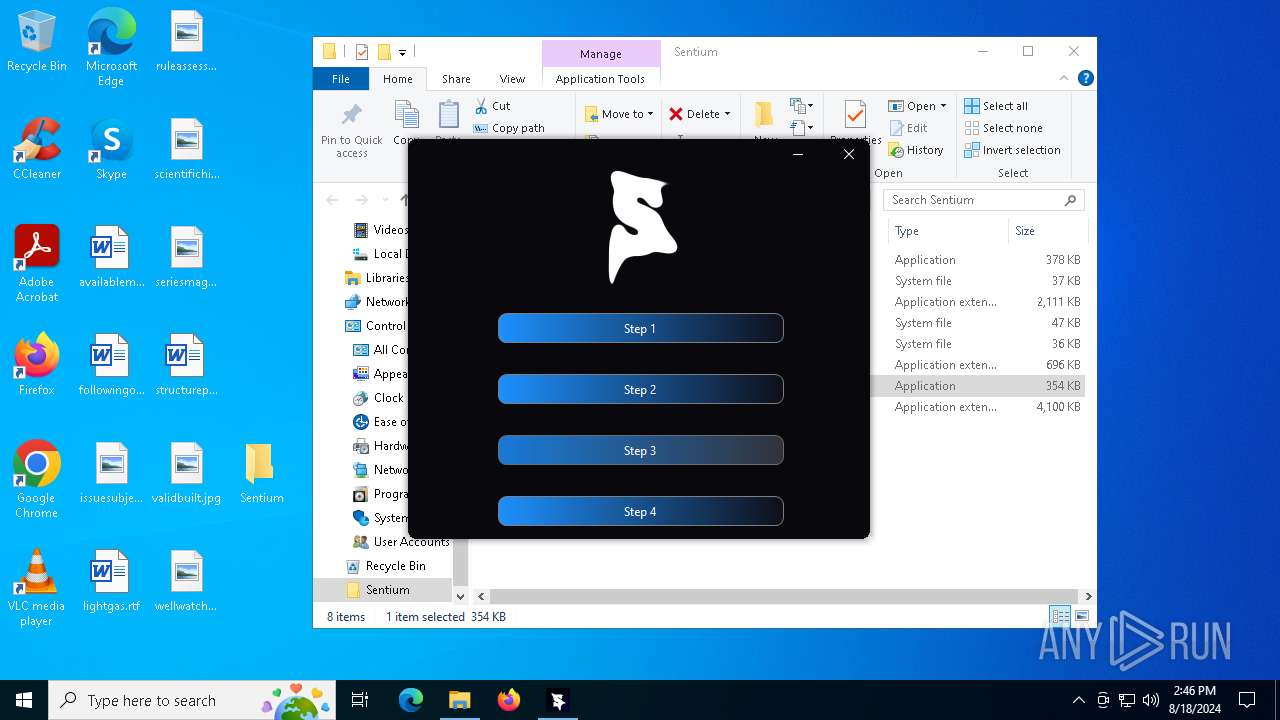
Manual execution by a user
- Sentium.exe (PID: 3276)
- Sentium.exe (PID: 6180)
- Sentium.exe (PID: 1372)
- Sentium.exe (PID: 2132)
- Sentium.exe (PID: 5492)
- msedge.exe (PID: 6244)
Reads the computer name
- TextInputHost.exe (PID: 6784)
- Sentium.exe (PID: 3276)
- identity_helper.exe (PID: 6468)
- Sentium.exe (PID: 6180)
- Sentium.exe (PID: 1372)
- identity_helper.exe (PID: 6432)
- Sentium.exe (PID: 2132)
- Sentium.exe (PID: 5492)
- identity_helper.exe (PID: 6664)
- AMIDEWINx64.EXE (PID: 6880)
- AMIDEWINx64.EXE (PID: 6640)
- AMIDEWINx64.EXE (PID: 5068)
- AMIDEWINx64.EXE (PID: 2524)
- AMIDEWINx64.EXE (PID: 6740)
- AMIDEWINx64.EXE (PID: 6544)
- AMIDEWINx64.EXE (PID: 6652)
- AMIDEWINx64.EXE (PID: 3068)
- AMIDEWINx64.EXE (PID: 6672)
- AMIDEWINx64.EXE (PID: 4276)
- AMIDEWINx64.EXE (PID: 2044)
- AMIDEWINx64.EXE (PID: 4200)
- AMIDEWINx64.EXE (PID: 2128)
- AMIDEWINx64.EXE (PID: 1920)
- AMIDEWINx64.EXE (PID: 1556)
- AMIDEWINx64.EXE (PID: 3068)
- AMIDEWINx64.EXE (PID: 3692)
- AMIDEWINx64.EXE (PID: 6176)
- AMIDEWINx64.EXE (PID: 6160)
- AMIDEWINx64.EXE (PID: 6692)
- AMIDEWINx64.EXE (PID: 4544)
- AMIDEWINx64.EXE (PID: 6496)
- AMIDEWINx64.EXE (PID: 2584)
- AMIDEWINx64.EXE (PID: 6424)
- AMIDEWINx64.EXE (PID: 7064)
- AMIDEWINx64.EXE (PID: 7144)
- AMIDEWINx64.EXE (PID: 936)
Checks supported languages
- TextInputHost.exe (PID: 6784)
- Sentium.exe (PID: 3276)
- Sentium.exe (PID: 6180)
- Sentium.exe (PID: 1372)
- identity_helper.exe (PID: 6468)
- identity_helper.exe (PID: 6432)
- Sentium.exe (PID: 2132)
- Sentium.exe (PID: 5492)
- identity_helper.exe (PID: 6664)
- AMIDEWINx64.EXE (PID: 6640)
- AMIDEWINx64.EXE (PID: 3068)
- AMIDEWINx64.EXE (PID: 6880)
- AMIDEWINx64.EXE (PID: 5068)
- AMIDEWINx64.EXE (PID: 6740)
- AMIDEWINx64.EXE (PID: 6652)
- AMIDEWINx64.EXE (PID: 6544)
- AMIDEWINx64.EXE (PID: 1920)
- AMIDEWINx64.EXE (PID: 2524)
- AMIDEWINx64.EXE (PID: 6672)
- AMIDEWINx64.EXE (PID: 4276)
- AMIDEWINx64.EXE (PID: 4200)
- AMIDEWINx64.EXE (PID: 2128)
- AMIDEWINx64.EXE (PID: 3068)
- AMIDEWINx64.EXE (PID: 3692)
- AMIDEWINx64.EXE (PID: 6176)
- AMIDEWINx64.EXE (PID: 6160)
- AMIDEWINx64.EXE (PID: 6692)
- AMIDEWINx64.EXE (PID: 7144)
- AMIDEWINx64.EXE (PID: 2044)
- AMIDEWINx64.EXE (PID: 4544)
- AMIDEWINx64.EXE (PID: 6496)
- AMIDEWINx64.EXE (PID: 2584)
- AMIDEWINx64.EXE (PID: 1556)
- AMIDEWINx64.EXE (PID: 936)
- AMIDEWINx64.EXE (PID: 6424)
- AMIDEWINx64.EXE (PID: 7064)
Reads the machine GUID from the registry
- Sentium.exe (PID: 3276)
- Sentium.exe (PID: 6180)
- Sentium.exe (PID: 1372)
- Sentium.exe (PID: 2132)
- Sentium.exe (PID: 5492)
Reads Environment values
- Sentium.exe (PID: 3276)
- identity_helper.exe (PID: 6468)
- Sentium.exe (PID: 1372)
- identity_helper.exe (PID: 6432)
- Sentium.exe (PID: 5492)
- identity_helper.exe (PID: 6664)
Disables trace logs
- Sentium.exe (PID: 3276)
- Sentium.exe (PID: 1372)
- Sentium.exe (PID: 5492)
Reads the software policy settings
- Sentium.exe (PID: 3276)
- Sentium.exe (PID: 1372)
- Sentium.exe (PID: 5492)
Checks proxy server information
- Sentium.exe (PID: 3276)
- Sentium.exe (PID: 1372)
- Sentium.exe (PID: 5492)
Application launched itself
- msedge.exe (PID: 6244)
- msedge.exe (PID: 2424)
- msedge.exe (PID: 6652)
- msedge.exe (PID: 1044)
- msedge.exe (PID: 3540)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2424)
- msedge.exe (PID: 6244)
- Sentium.exe (PID: 1372)
- msedge.exe (PID: 6652)
- Sentium.exe (PID: 5492)
- msedge.exe (PID: 1044)
- Sentium.exe (PID: 3276)
- msedge.exe (PID: 3540)
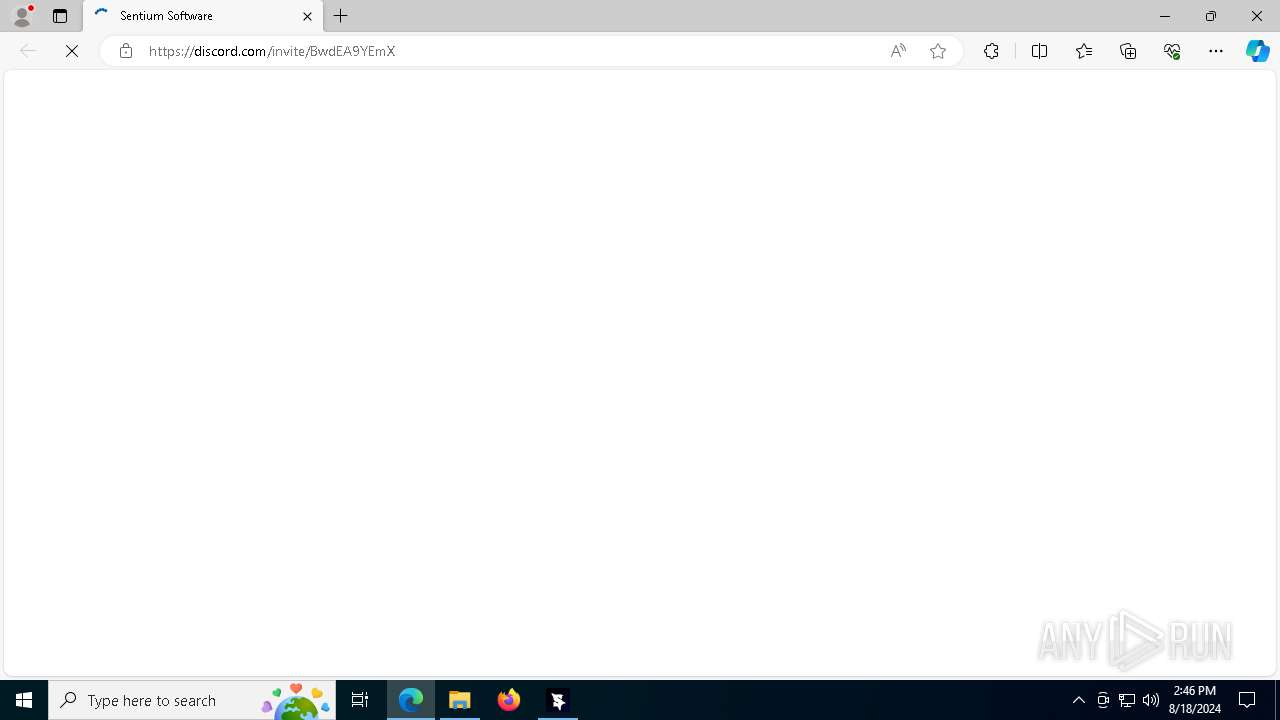
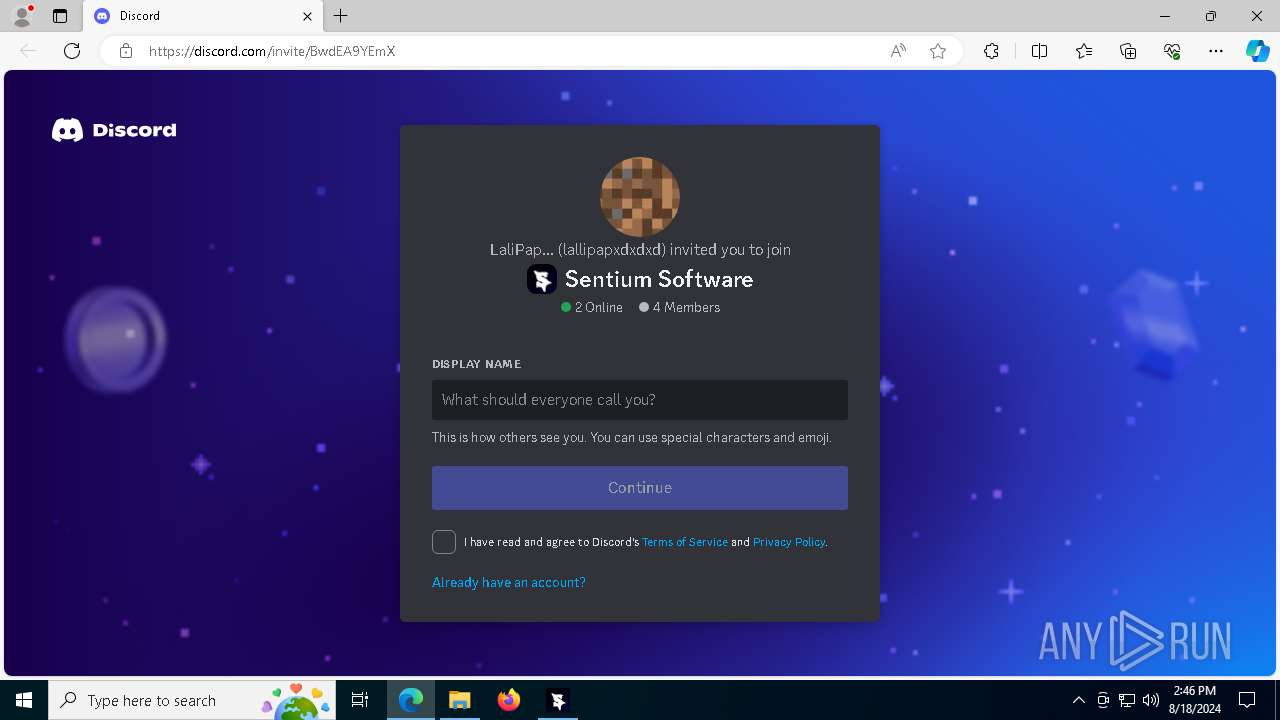
Attempting to use instant messaging service
- msedge.exe (PID: 6564)
- msedge.exe (PID: 7108)
- msedge.exe (PID: 5984)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5084)
- WMIC.exe (PID: 6608)
- WMIC.exe (PID: 2044)
- WMIC.exe (PID: 2248)
- WMIC.exe (PID: 5552)
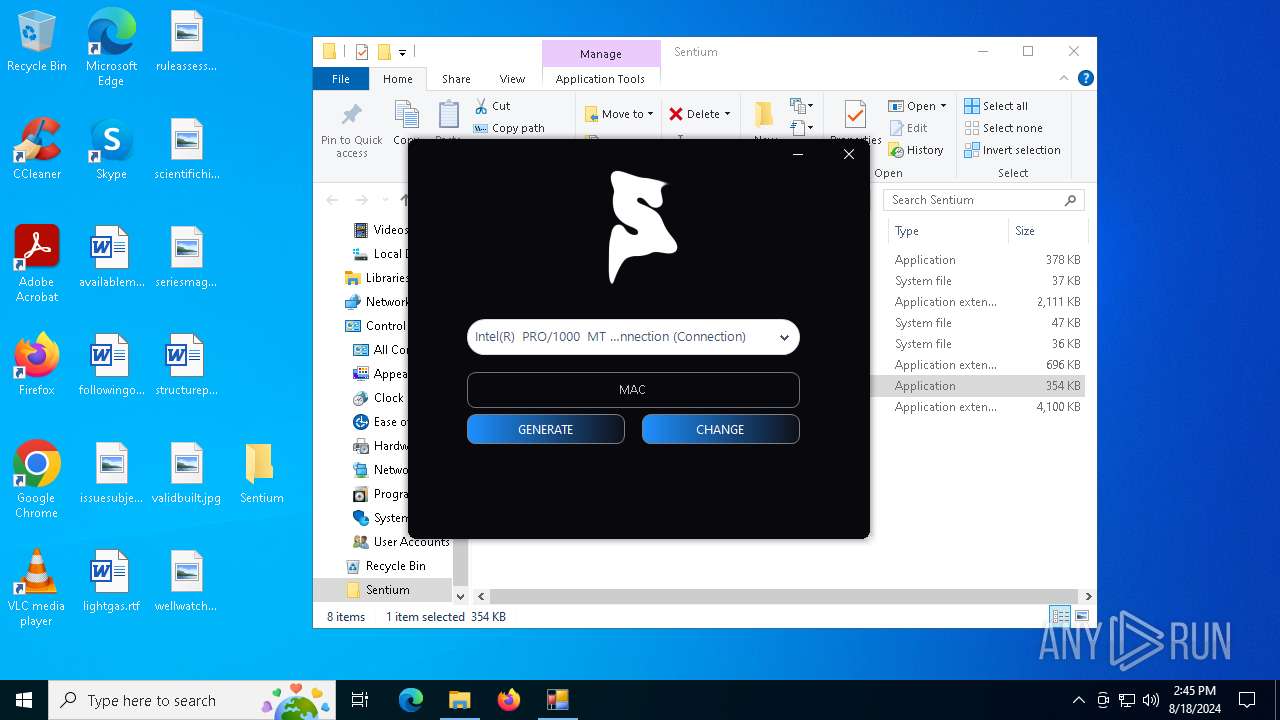
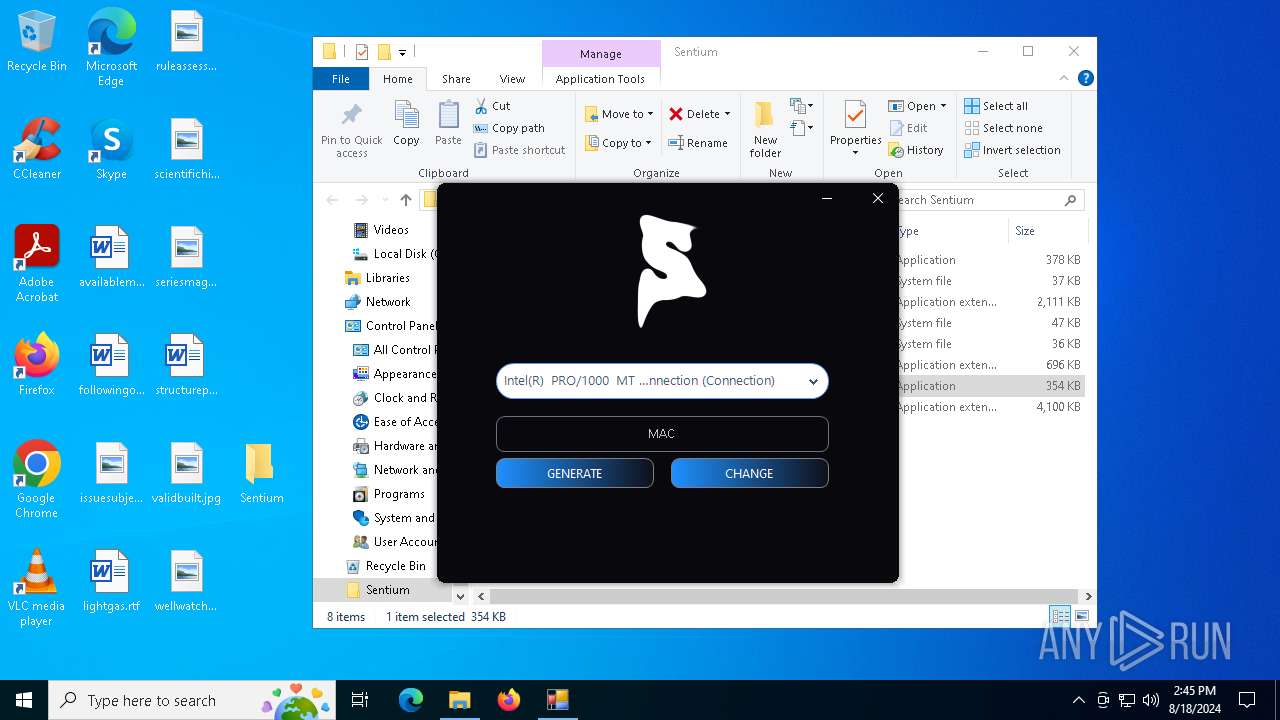
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 6908)
Creates files in the program directory
- Sentium.exe (PID: 3276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
303
Monitored processes
168
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=5640 --field-trial-handle=2392,i,16363469393603283197,15533983297080276429,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 532 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=4976 --field-trial-handle=2392,i,16363469393603283197,15533983297080276429,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 936 | "Amidewinx64.exe" /SCO 2 "Default string" | C:\Users\admin\Desktop\Sentium\AMIDEWINx64.EXE | — | Sentium.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 224 Modules
| |||||||||||||||
| 1044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1104 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x32c,0x330,0x334,0x324,0x33c,0x7fffd3035fd8,0x7fffd3035fe4,0x7fffd3035ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1104 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3416 --field-trial-handle=2376,i,9770863319792935857,15874177912180281103,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | "cmd.exe" /k "wmic diskdrive get model, serialnumber & wmic cpu get serialnumber & wmic bios get serialnumber & wmic baseboard get serialnumber & wmic path win32_computersystemproduct get uuid & getmac & echo Press any button if you want to close it :) & pause > nul & exit" | C:\Windows\SysWOW64\cmd.exe | — | Sentium.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5004 --field-trial-handle=2344,i,14119243313975618127,11230183405854162482,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1372 | "C:\Users\admin\Desktop\Sentium\Sentium.exe" | C:\Users\admin\Desktop\Sentium\Sentium.exe | explorer.exe | ||||||||||||
User: admin Company: Marcuz Integrity Level: HIGH Description: Sentium Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 1536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4960 --field-trial-handle=2376,i,9770863319792935857,15874177912180281103,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
50 186
Read events
49 949
Write events
231
Delete events
6
Modification events
| (PID) Process: | (6304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Sentium.rar | |||
| (PID) Process: | (6304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF37010000A4000000F70400008D020000 | |||
| (PID) Process: | (6304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
13
Suspicious files
175
Text files
150
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
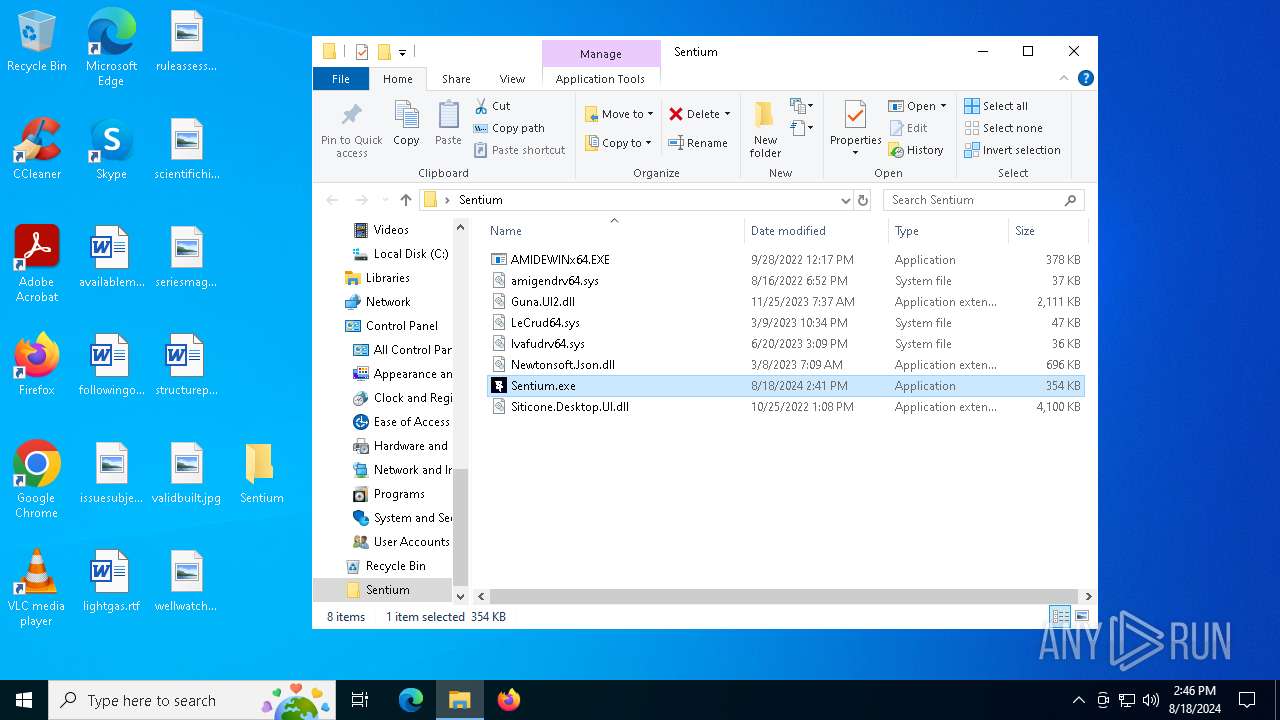
| 6304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6304.6485\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
| 6304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6304.6485\AMIDEWINx64.EXE | executable | |
MD5:6DEA36AE7A414E376B00829E16DA52E0 | SHA256:47C16703FA7DF006F9559FCA8B1482B4C59111017A0530C1EDAC3CAF0BDAAF39 | |||
| 6304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6304.6485\Sentium.exe | executable | |
MD5:3421D0C28849E4727653B329FDF19538 | SHA256:F6DBF2C91536444BF345D8BD1F3FFF38F4467BCF2B8FC0B86972D66EAC7BA7A9 | |||
| 6304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6304.6485\LeCrud64.sys | executable | |
MD5:3E5C48EE4BDD6229F6BEF52E940AF600 | SHA256:F3046CF53EF29E9882918978310680497A1A329076C046697B4A1312F590FC09 | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFf0e3f.TMP | — | |
MD5:— | SHA256:— | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFf0e3f.TMP | — | |
MD5:— | SHA256:— | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6304.6485\amigendrv64.sys | executable | |
MD5:9ACCEBD928A8926FECF317F53CD1C44E | SHA256:811E5D65DF60DFB8C6E1713DA708BE16D9A13EF8DFCD1022D8D1DDA52ED057B2 | |||
| 6304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6304.6485\Siticone.Desktop.UI.dll | executable | |
MD5:1582AA45D981E0E569C6E05698642B30 | SHA256:21EECAF504B7FE787A45F4AA8F8F36DACFC3AB1D75624DFB41827CDEF2A9A589 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
76
DNS requests
82
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
300 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6904 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6512 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3720 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3972 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3972 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
300 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
300 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
keyauth.win |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain in DNS Lookup (keyauth .win) |
3276 | Sentium.exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain (keyauth .win) in TLS SNI |
6564 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6564 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6564 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1372 | Sentium.exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain (keyauth .win) in TLS SNI |
7108 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
7108 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
7108 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7108 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |