| File name: | MrA.exe |
| Full analysis: | https://app.any.run/tasks/26da1969-c0f1-44ce-bae1-07720161f911 |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 08:20:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | C12B31821EF1588A70D7DDA5A6EB0821 |
| SHA1: | 91BDCFF4772295FF6AC39256B9059AEE5A7CFCFD |
| SHA256: | A72E906F5EF548FF885E9A0F26A43FBFDD2C611345E05DA8815C2A42CFE1089C |
| SSDEEP: | 6144:lk4qmIEnqNdG8fwUqsiQvN8If919yUgdkO329YX+a2:i9onadG8fIOvN59YkNYX+a |
MALICIOUS
Application was injected by another process
- explorer.exe (PID: 352)
Changes the autorun value in the registry
- MrA.exe (PID: 2172)
Runs injected code in another process
- MrA.exe (PID: 2172)
SUSPICIOUS
Creates files in the user directory
- MrA.exe (PID: 2172)
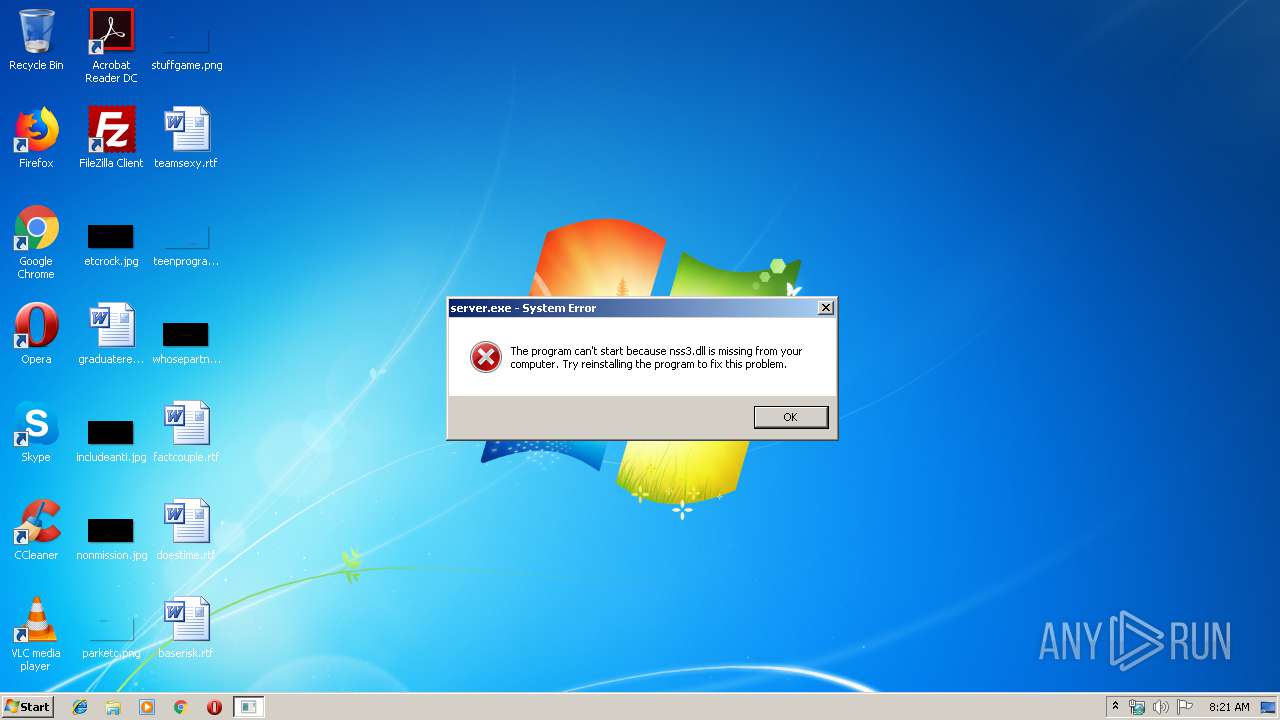
Loads DLL from Mozilla Firefox
- server.exe (PID: 4060)
Starts Internet Explorer
- MrA.exe (PID: 2172)
Executable content was dropped or overwritten
- MrA.exe (PID: 2172)
INFO
Creates files in the user directory
- iexplore.exe (PID: 1560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (38.2) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (37.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.2) |
| .exe | | | Win32 Executable (generic) (6.3) |
| .exe | | | Win16/32 Executable Delphi generic (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 278528 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 69632 |
| EntryPoint: | 0x55bb0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00011000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00012000 | 0x00044000 | 0x00043E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.75338 |
.rsrc | 0x00056000 | 0x00001000 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.57165 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.80709 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
50 | 7.82023 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
51 | 6.1418 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 7.34409 | 388 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
XX-XX-XX-XX | 7.72691 | 235267 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
ICON_STANDARD | 1.9815 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
MAINICON | 4.12193 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.DLL |
advapi32.dll |
crypt32.dll |
ole32.dll |
oleaut32.dll |
pstorec.dll |
rasapi32.dll |
shell32.dll |
user32.dll |
Total processes
36
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | MrA.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2172 | "C:\Users\admin\AppData\Local\Temp\MrA.exe" | C:\Users\admin\AppData\Local\Temp\MrA.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4060 | "C:\Users\admin\AppData\Roaming\spynet\server.exe" | C:\Users\admin\AppData\Roaming\spynet\server.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
517
Read events
452
Write events
65
Delete events
0
Modification events
| (PID) Process: | (2172) MrA.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | HKCU |
Value: C:\Users\admin\AppData\Roaming\spynet\server.exe | |||
| (PID) Process: | (1560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Server |
| Operation: | write | Name: | FirstExecution |
Value: 16/11/2019 -- 08:21 | |||
| (PID) Process: | (1560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Server |
| Operation: | write | Name: | NewIdentification |
Value: Server | |||
| (PID) Process: | (1560) iexplore.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
1
Text files
705
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2172 | MrA.exe | C:\Users\admin\AppData\Local\Temp\XX--XX--XX.txt | binary | |
MD5:— | SHA256:— | |||
| 2172 | MrA.exe | C:\Users\admin\AppData\Roaming\spynet\server.exe | executable | |
MD5:— | SHA256:— | |||
| 1560 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\UuU.uUu | text | |
MD5:B57DAA42A70DBF9A32A1A383DB01E45C | SHA256:F6F14F447E06494FBE442866D5F457011D1C467D3F1DA0A45147A77FBE8AB38E | |||
| 1560 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\XxX.xXx | text | |
MD5:B57DAA42A70DBF9A32A1A383DB01E45C | SHA256:F6F14F447E06494FBE442866D5F457011D1C467D3F1DA0A45147A77FBE8AB38E | |||
| 1560 | iexplore.exe | C:\Users\admin\AppData\Roaming\logs.dat | text | |
MD5:E21BD9604EFE8EE9B59DC7605B927A2A | SHA256:51A3FE220229AA3FDDDC909E20A4B107E7497320A00792A280A03389F2EACB46 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
max123242.ddns.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |