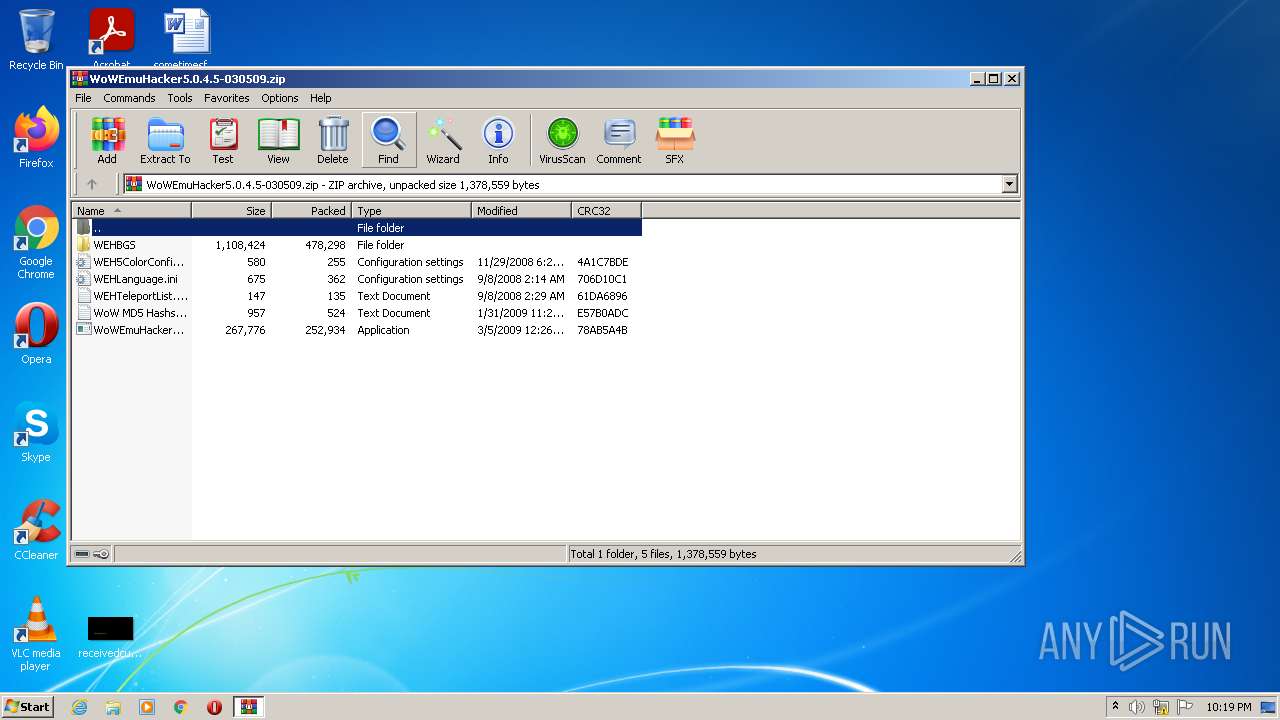
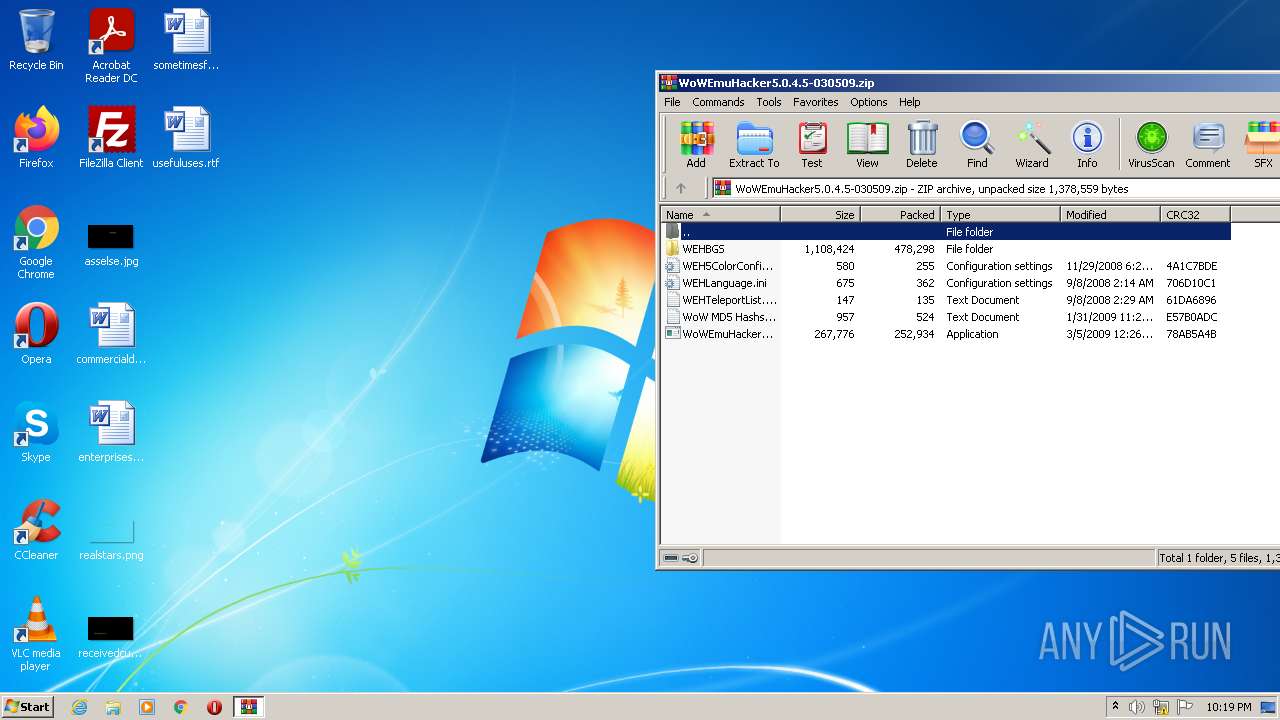
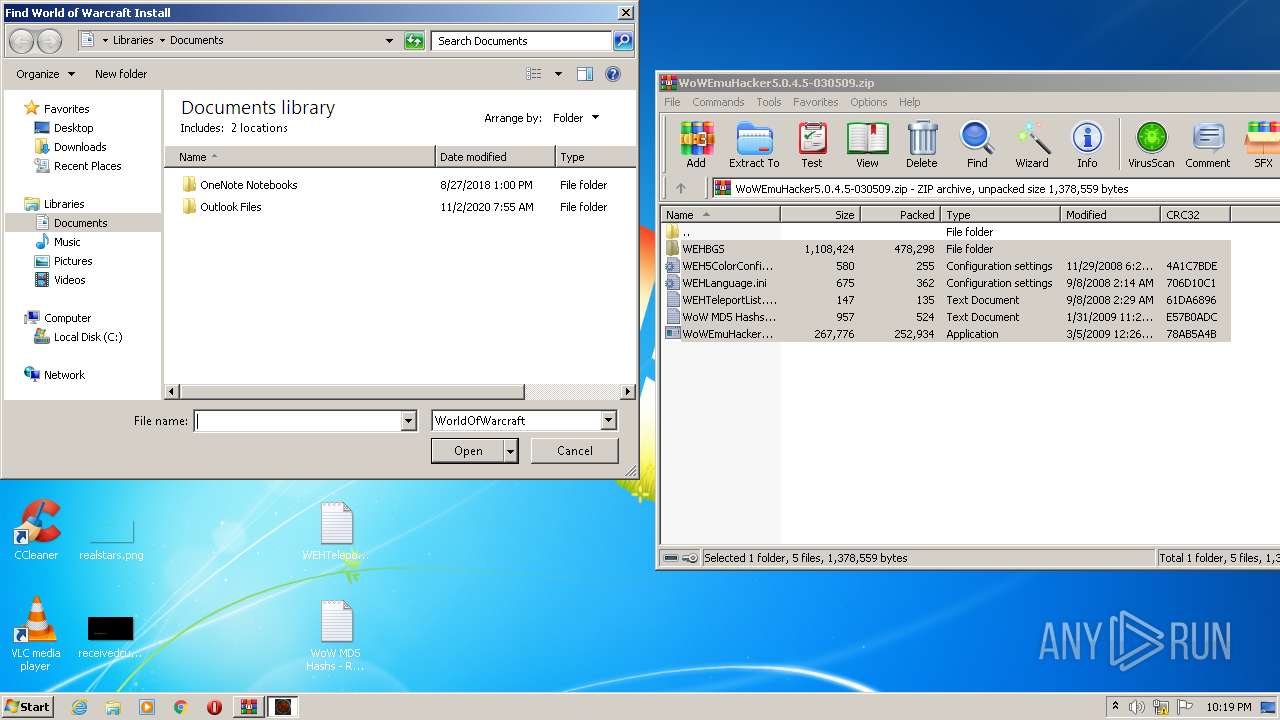
| File name: | WoWEmuHacker5.0.4.5-030509.zip |
| Full analysis: | https://app.any.run/tasks/adddb4cc-7a5e-4f93-b26e-4d3742c2a788 |
| Verdict: | Malicious activity |
| Analysis date: | June 10, 2022, 21:18:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D0501C688925F8FAD8E18DB65EB034F5 |
| SHA1: | 72257A762640E752175B4F1C09736276A6090D86 |
| SHA256: | A70846C29093B606698A9B4E8350CDB70FC8567B17B071A509A856C877003005 |
| SSDEEP: | 12288:lh7A8zK2knSxufD5G8R2qh5UA5xne+MWj1rC/2FO8xwrw7unvXcLie:lhO2knp8/2UATne+Mumzw7unEL5 |
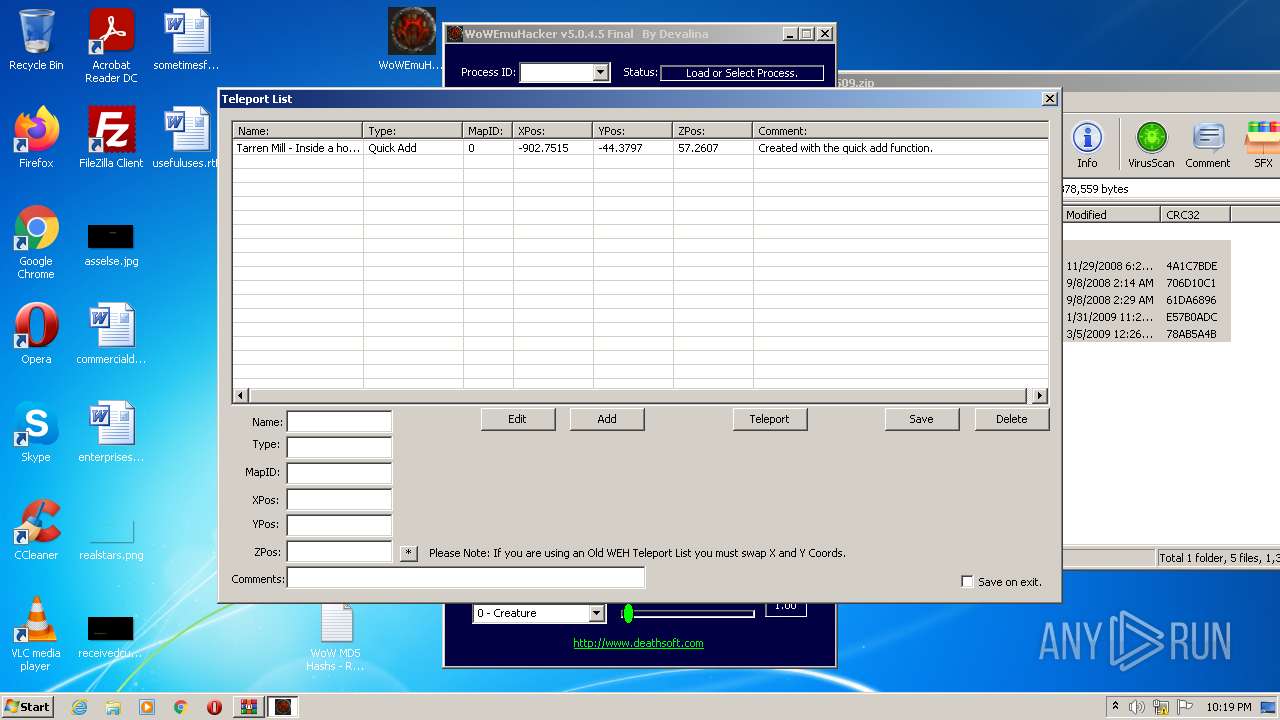
MALICIOUS
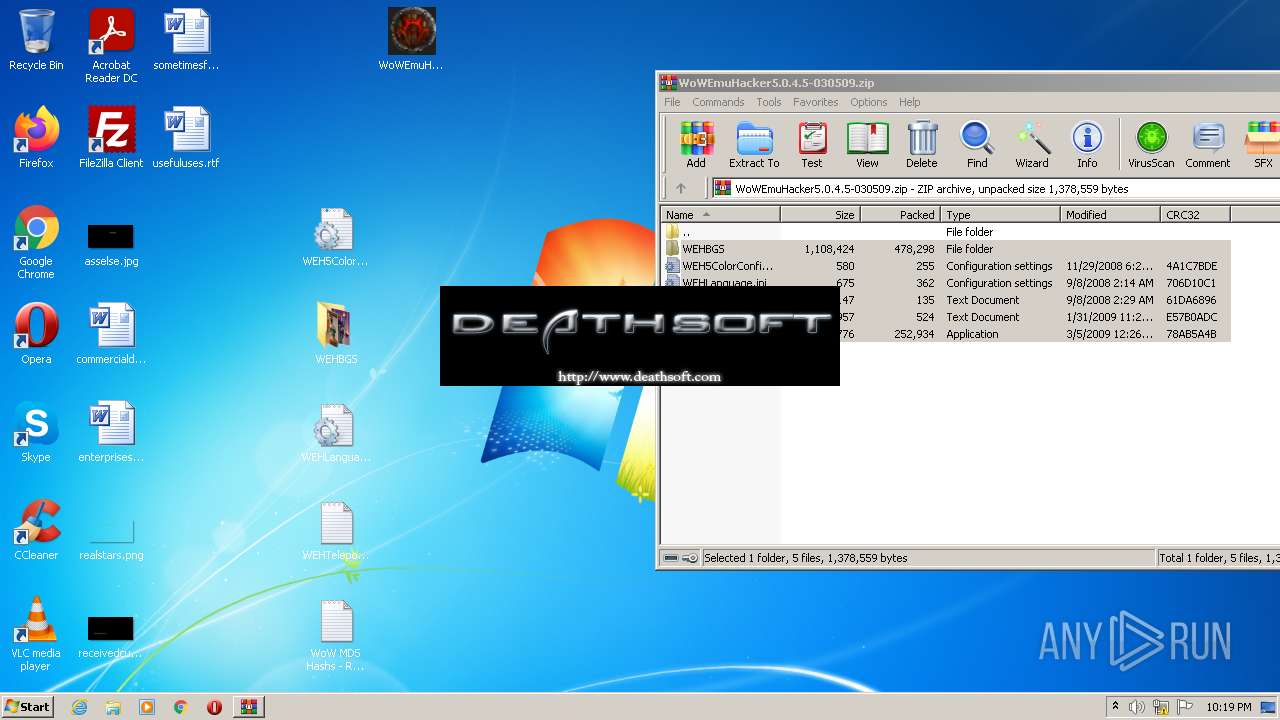
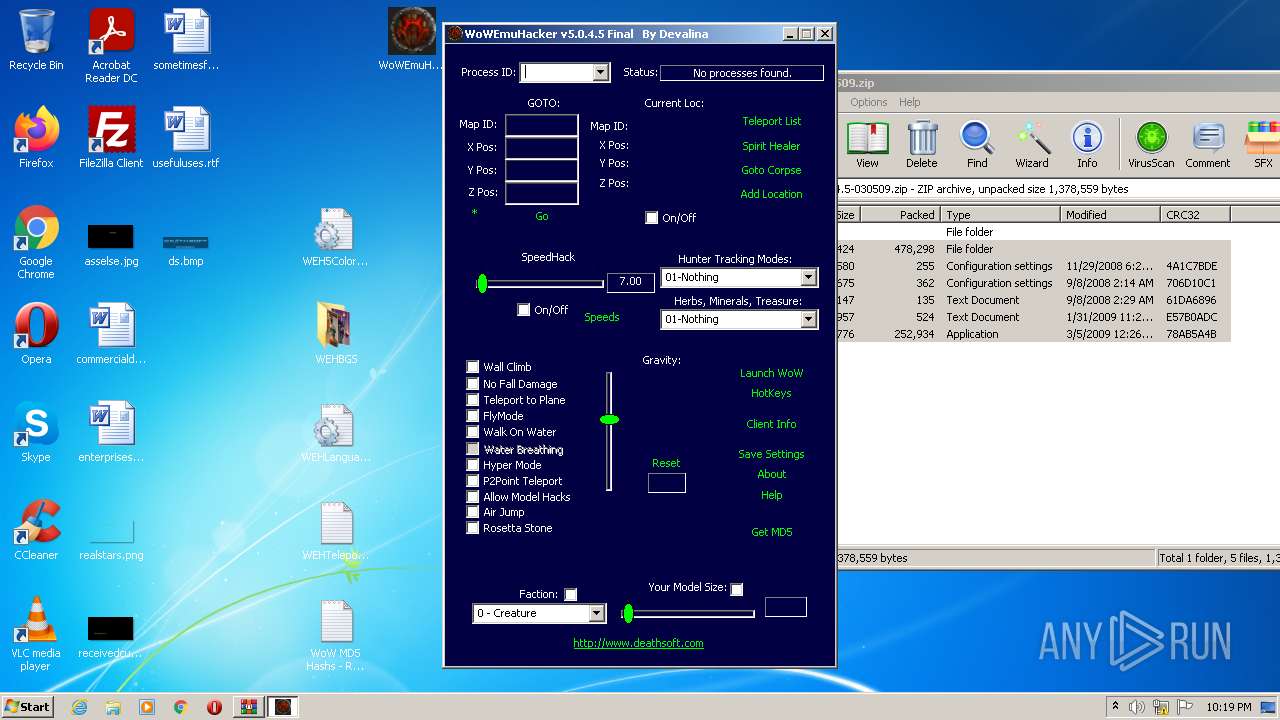
Application was dropped or rewritten from another process
- WoWEmuHacker5.exe (PID: 2396)
Drops executable file immediately after starts
- WinRAR.exe (PID: 2600)
SUSPICIOUS
Checks supported languages
- WoWEmuHacker5.exe (PID: 2396)
- WinRAR.exe (PID: 2600)
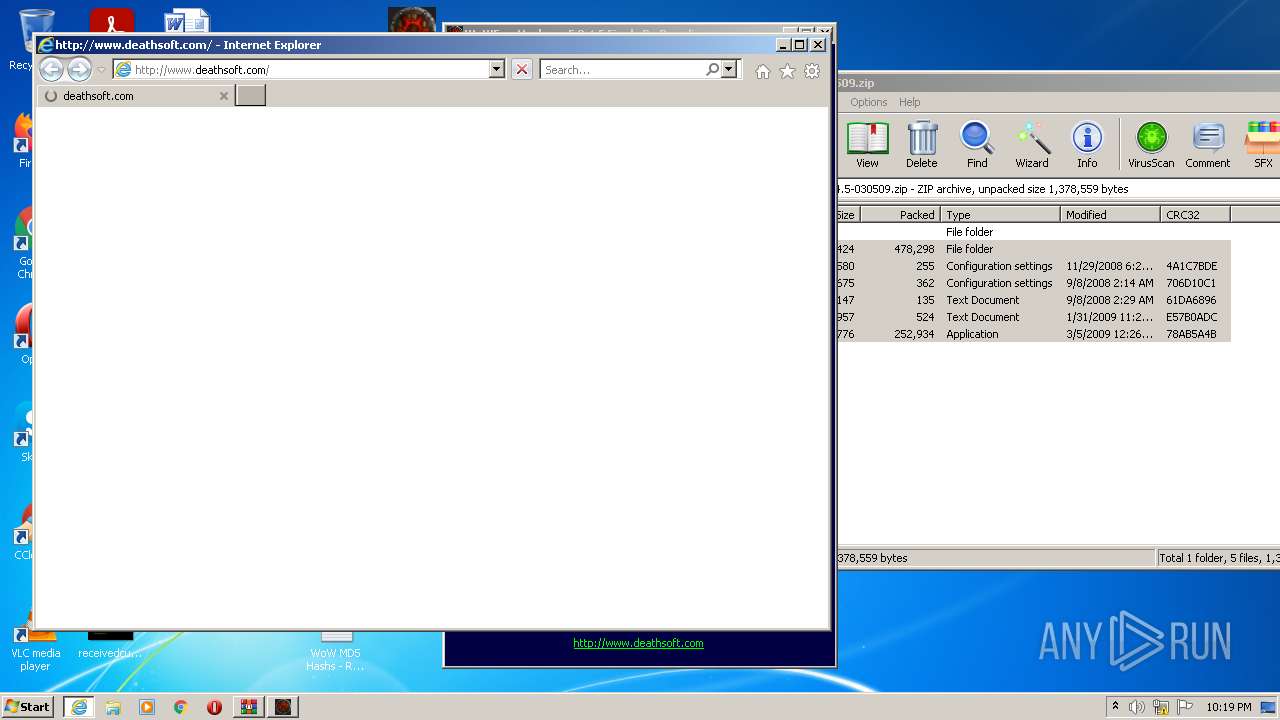
Starts Internet Explorer
- WoWEmuHacker5.exe (PID: 2396)
Reads the computer name
- WoWEmuHacker5.exe (PID: 2396)
- WinRAR.exe (PID: 2600)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2520)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2600)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2600)
INFO
Reads the computer name
- iexplore.exe (PID: 284)
- iexplore.exe (PID: 2520)
Checks supported languages
- iexplore.exe (PID: 284)
- iexplore.exe (PID: 2520)
Changes internet zones settings
- iexplore.exe (PID: 284)
Application launched itself
- iexplore.exe (PID: 284)
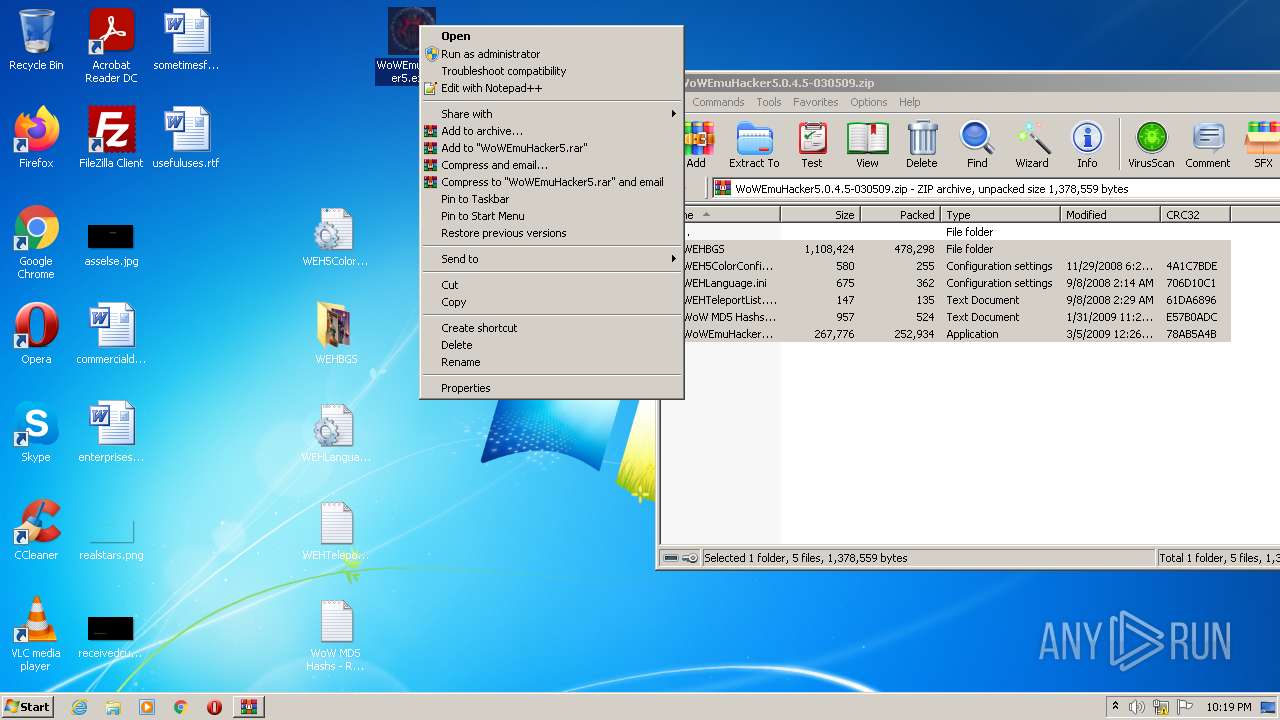
Manual execution by user
- WoWEmuHacker5.exe (PID: 2396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | WEHLanguage.ini |
|---|---|
| ZipUncompressedSize: | 675 |
| ZipCompressedSize: | 362 |
| ZipCRC: | 0x706d10c1 |
| ZipModifyDate: | 2008:09:08 02:14:24 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
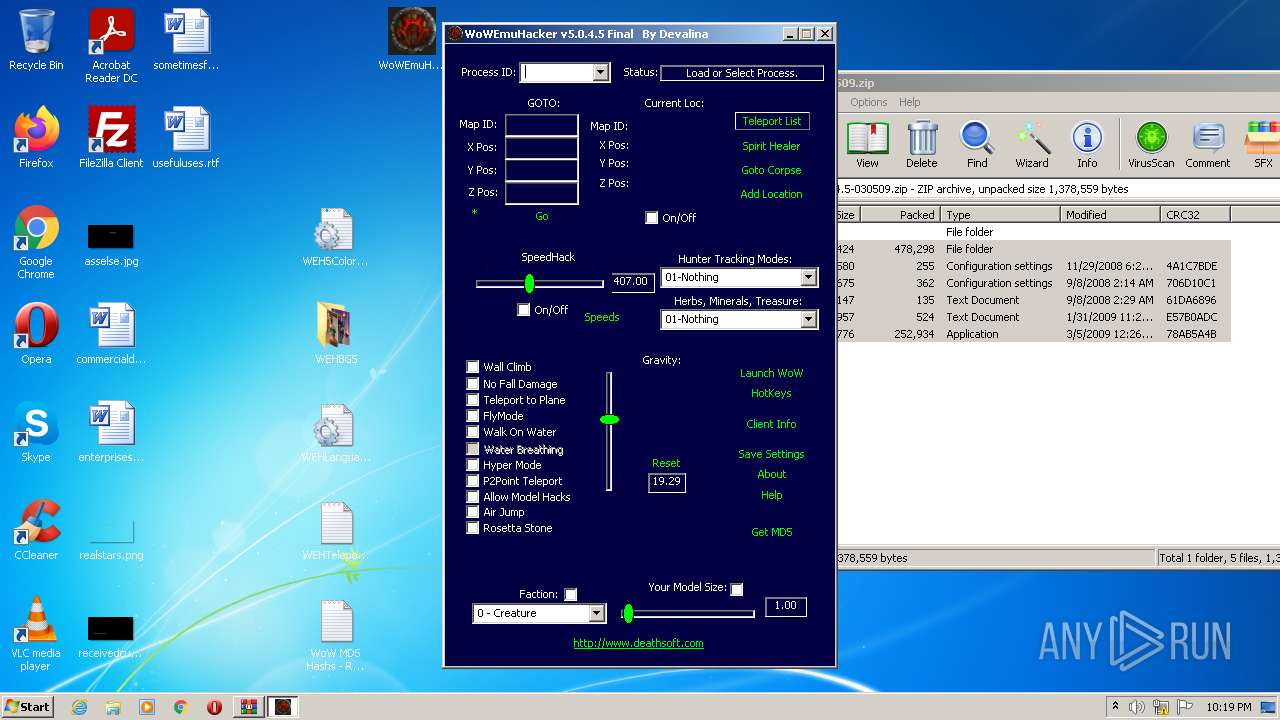
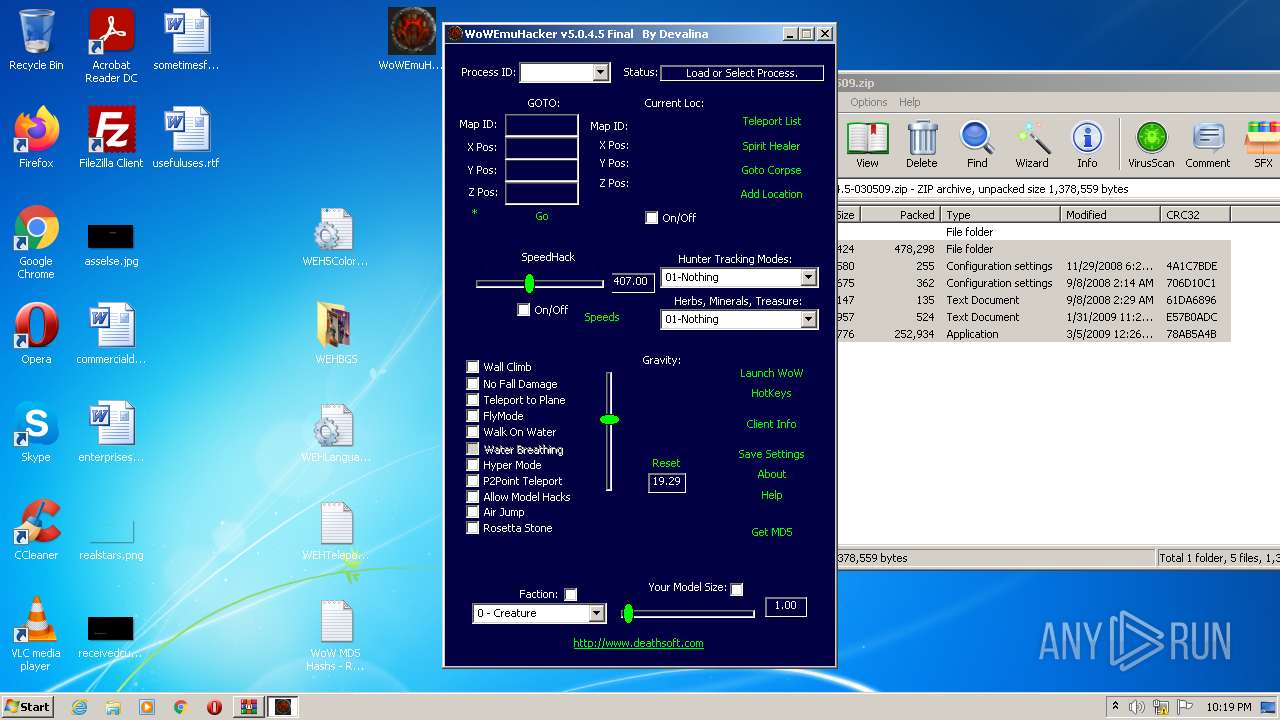
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.deathsoft.com/ | C:\Program Files\Internet Explorer\iexplore.exe | — | WoWEmuHacker5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2396 | "C:\Users\admin\Desktop\WoWEmuHacker5.exe" | C:\Users\admin\Desktop\WoWEmuHacker5.exe | Explorer.EXE | ||||||||||||
User: admin Company: DeathSoft™ Integrity Level: HIGH Description: WoWEmuHacker 5.0 Exit code: 0 Version: 5.0.4.5 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:284 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2600 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\WoWEmuHacker5.0.4.5-030509.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
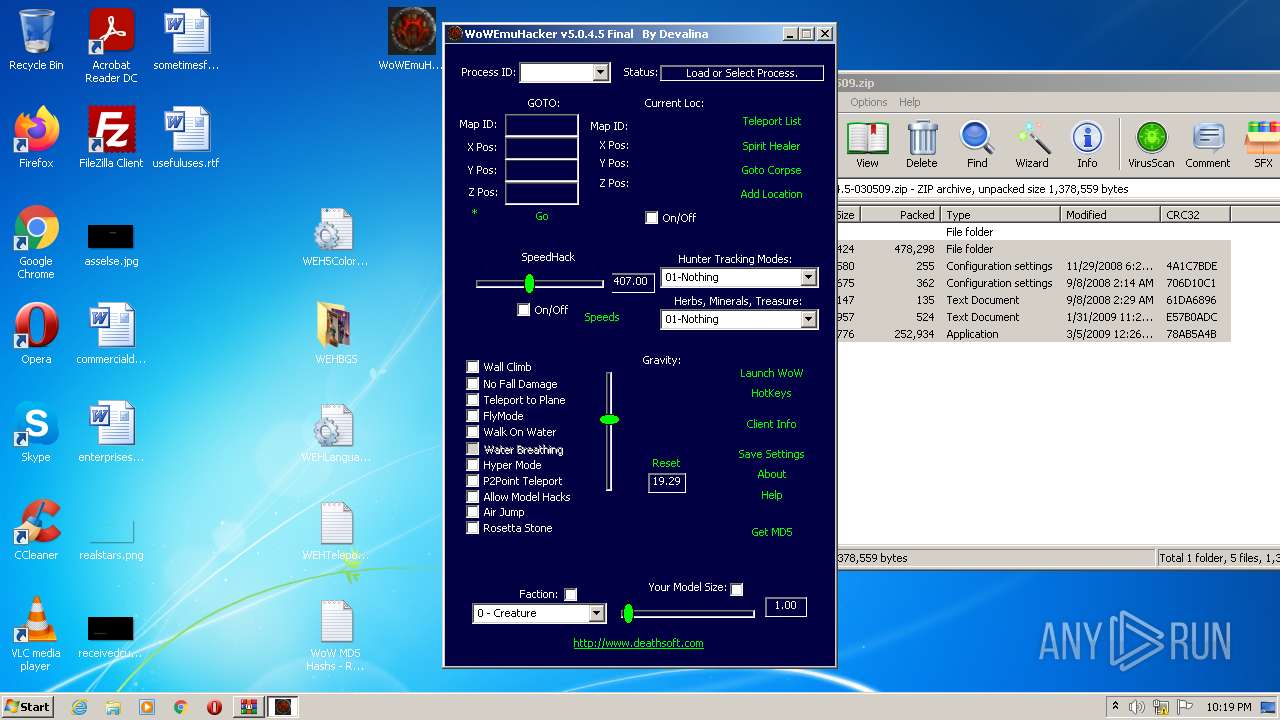
Total events
3 524
Read events
3 412
Write events
111
Delete events
1
Modification events
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\WoWEmuHacker5.0.4.5-030509.zip | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
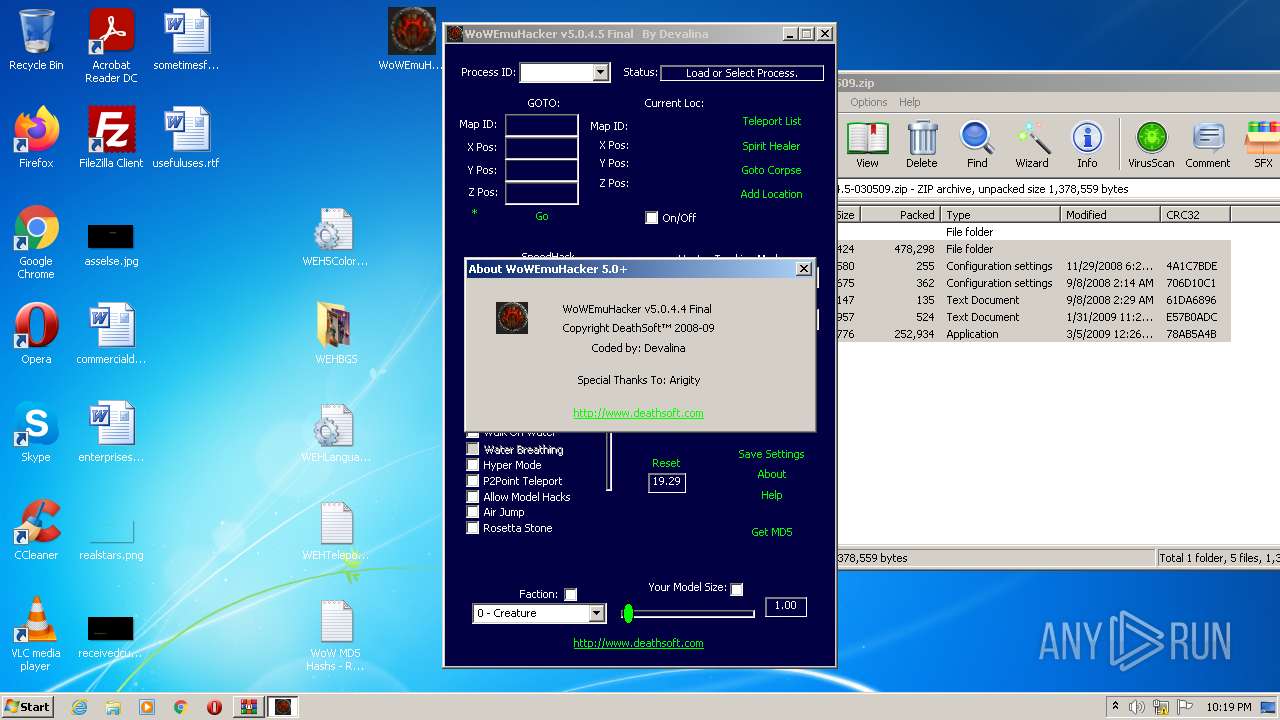
Executable files
1
Suspicious files
0
Text files
8
Unknown types
0
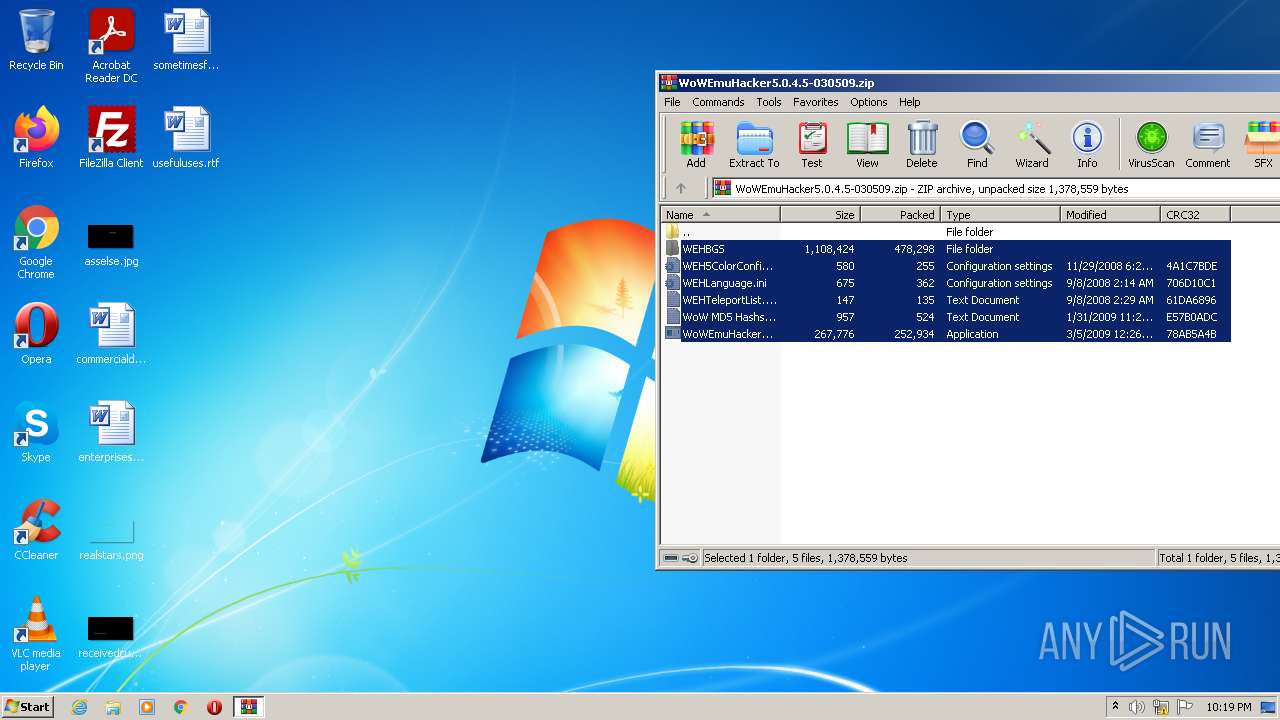
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2600.10379\WEHBGS\bg.bmp | image | |
MD5:— | SHA256:— | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2600.10379\WoW MD5 Hashs - README.txt | text | |
MD5:— | SHA256:— | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2600.10379\WEH5ColorConfig.ini | text | |
MD5:— | SHA256:— | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2600.10379\WEHLanguage.ini | text | |
MD5:— | SHA256:— | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2600.10379\WoWEmuHacker5.exe | executable | |
MD5:— | SHA256:— | |||
| 2396 | WoWEmuHacker5.exe | C:\Users\admin\Desktop\ds.bmp | image | |
MD5:— | SHA256:— | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2600.10379\WEHBGS\BG1B.bmp | image | |
MD5:— | SHA256:— | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2600.10379\WEHTeleportList.txt | text | |
MD5:— | SHA256:— | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2600.10379\WEHBGS\blackblue.bmp | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2520 | iexplore.exe | GET | — | 104.153.105.236:80 | http://www.deathsoft.com/ | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2520 | iexplore.exe | 104.153.105.236:80 | www.deathsoft.com | Nuclearfallout Enterprises, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.deathsoft.com |
| unknown |