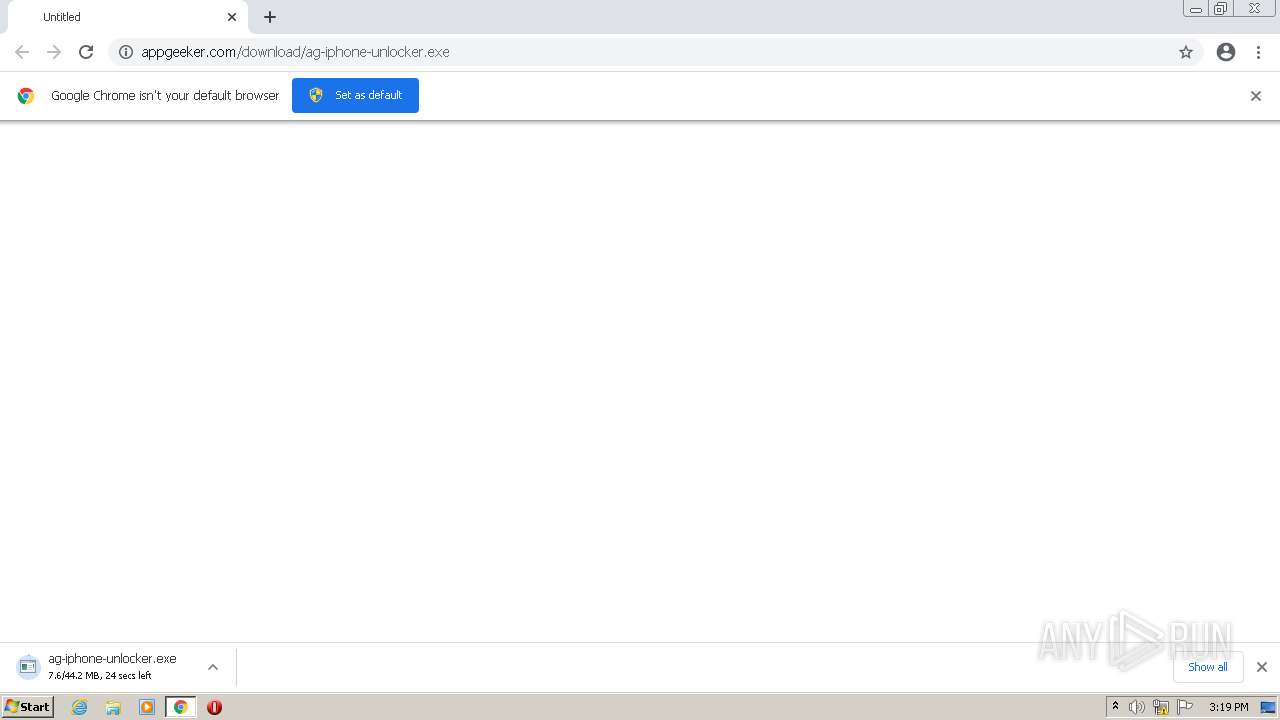
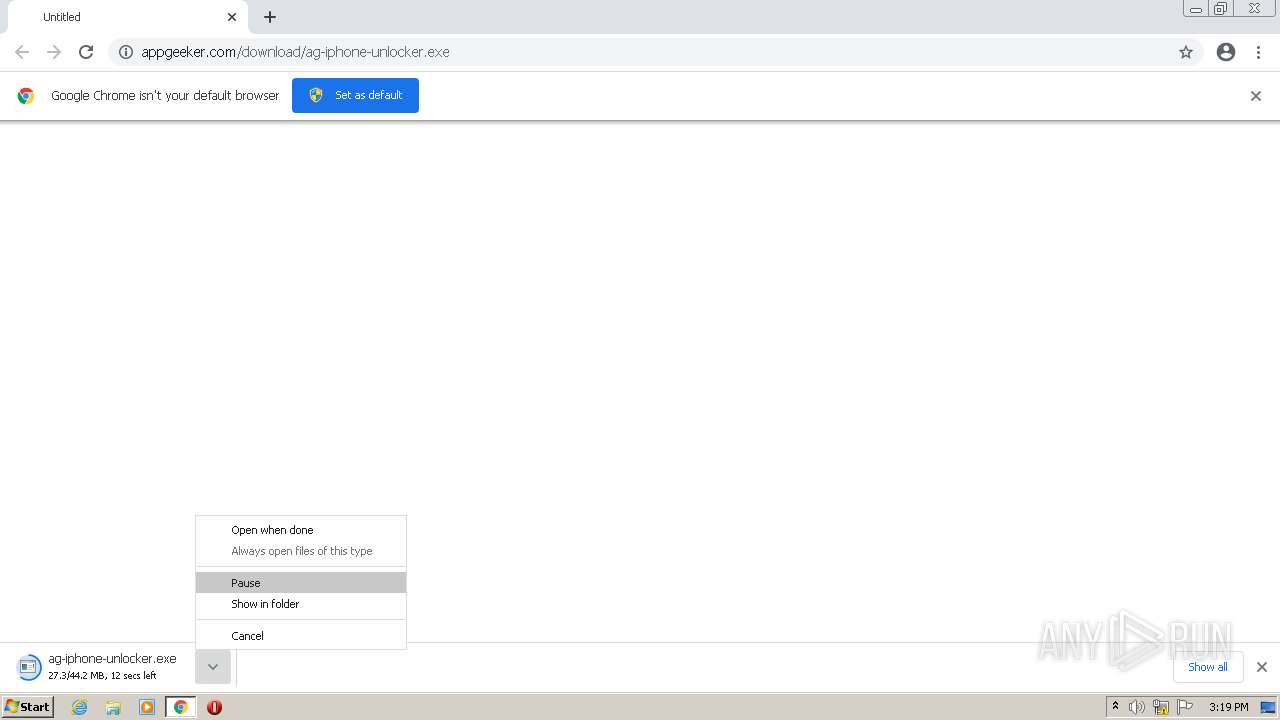
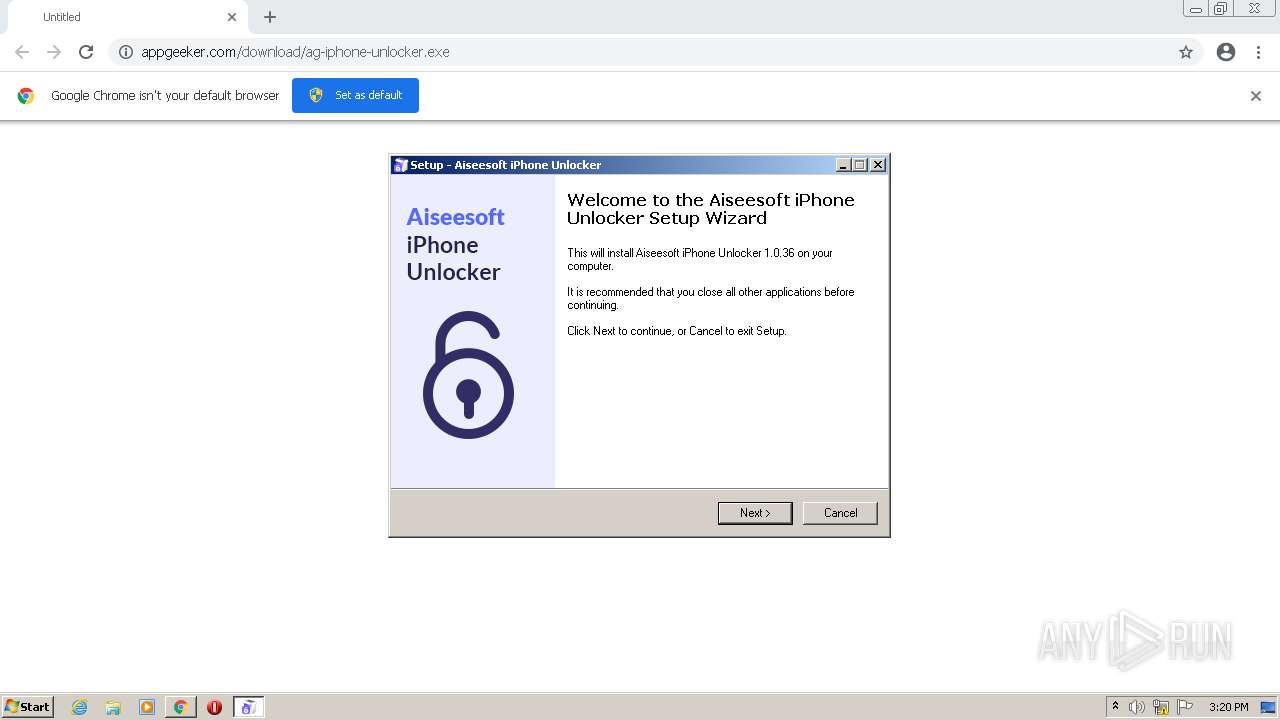
| URL: | https://www.appgeeker.com/download/ag-iphone-unlocker.exe |
| Full analysis: | https://app.any.run/tasks/3a21b90c-e584-4d9e-b216-84613e45b7a8 |
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2022, 14:18:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4A9B06C2C7DFB042E186513C8553E39E |
| SHA1: | A06423F0E67AD7CD702995AA79C6DB14557CB54C |
| SHA256: | A6FAFCD63B7B809CB11FC2D3821C1B72E966185A8BBBB96E51F2F4C298F07F13 |
| SSDEEP: | 3:N8DSLE/ymLrxniQLJd4A:2OLE/ym3xieJf |
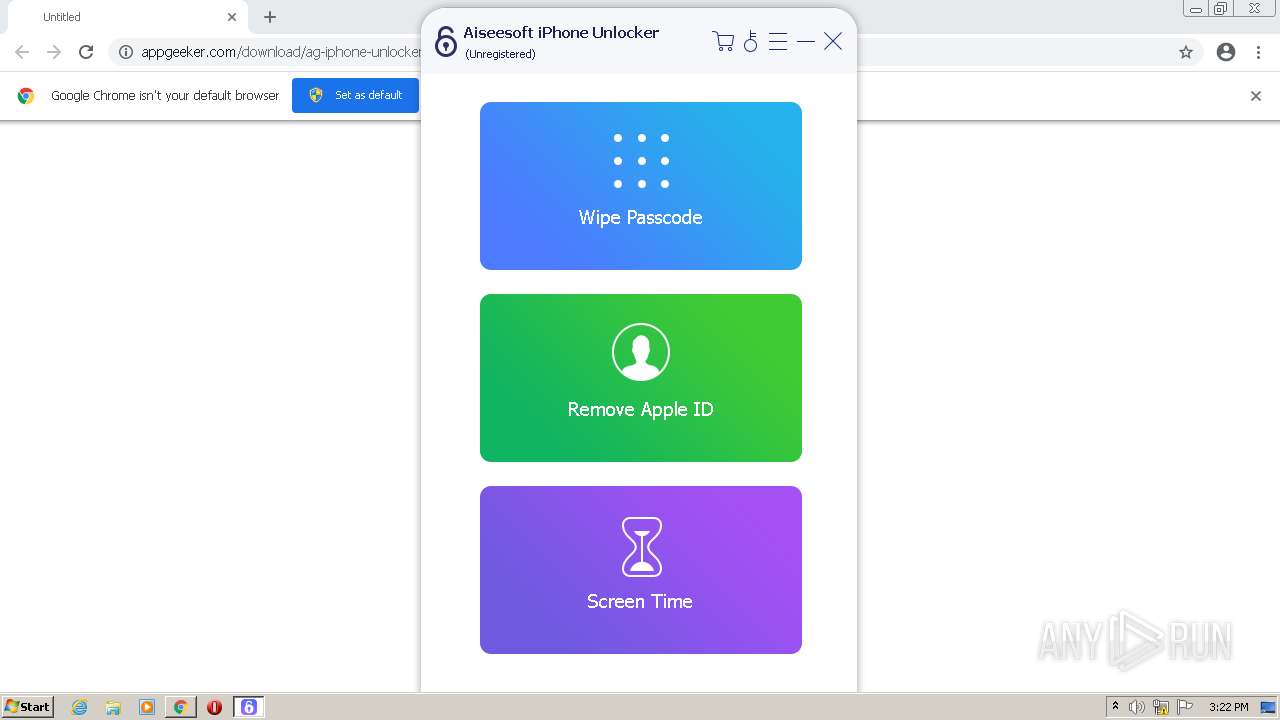
MALICIOUS
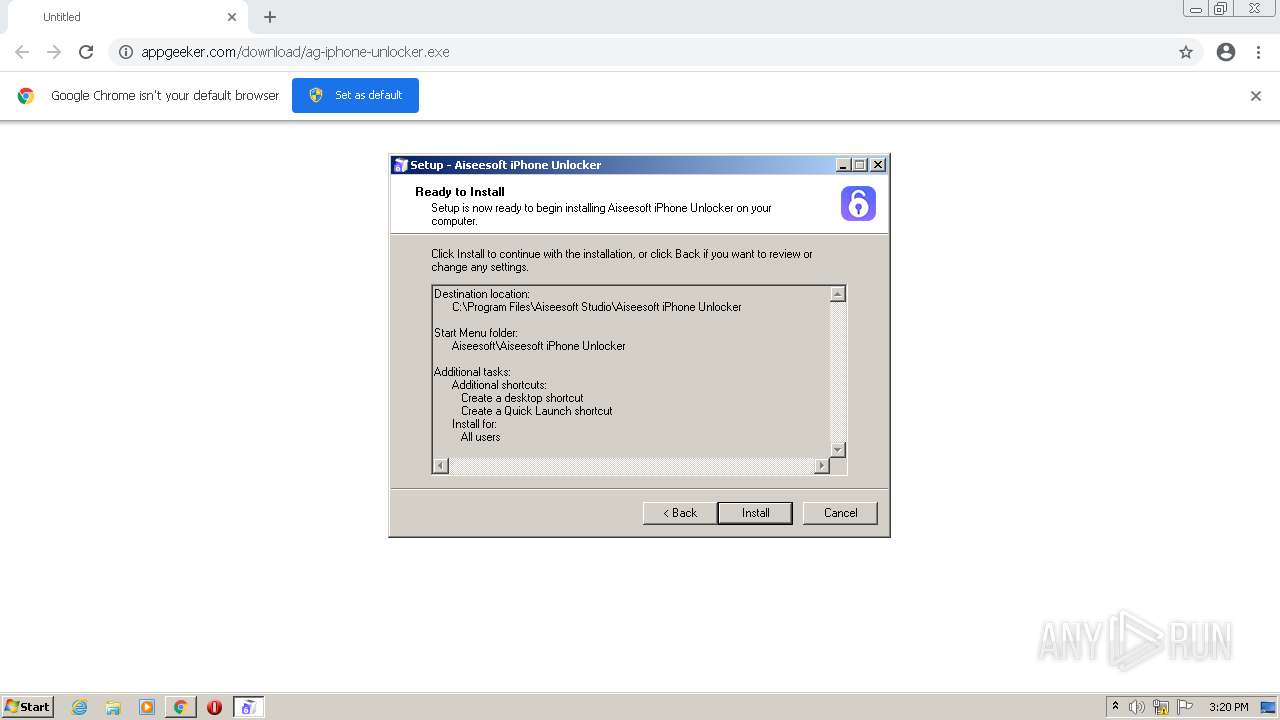
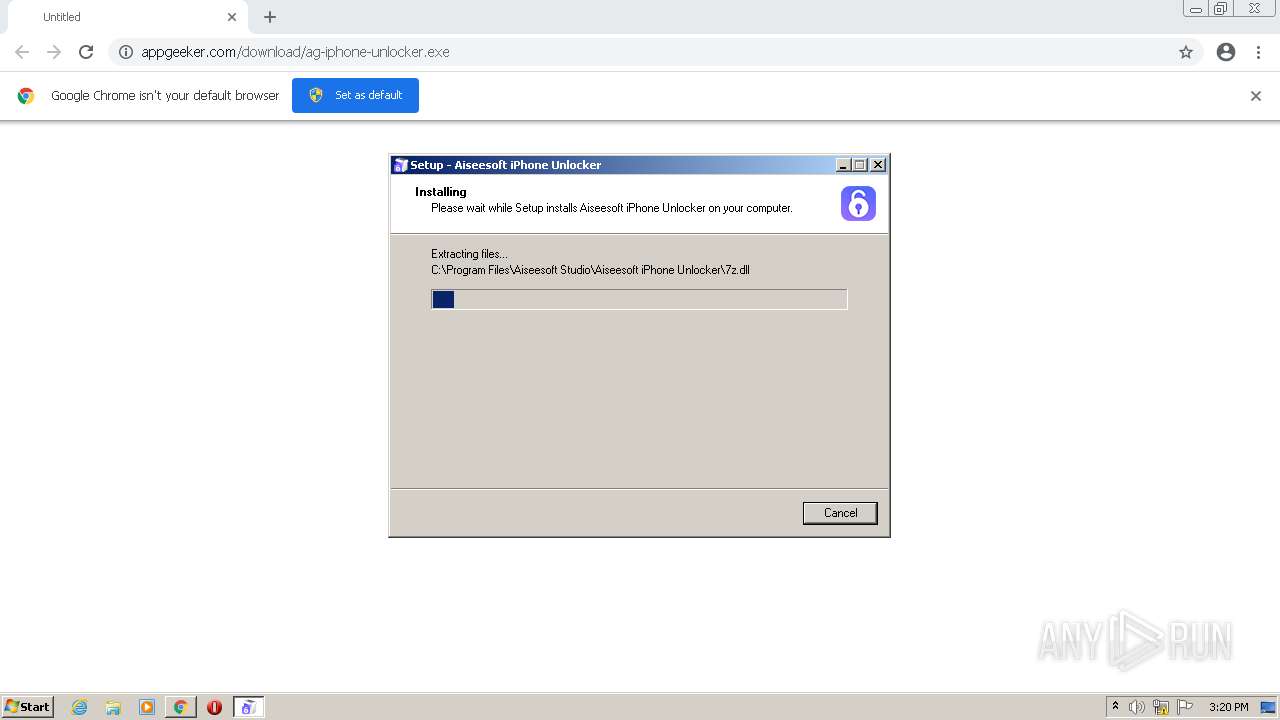
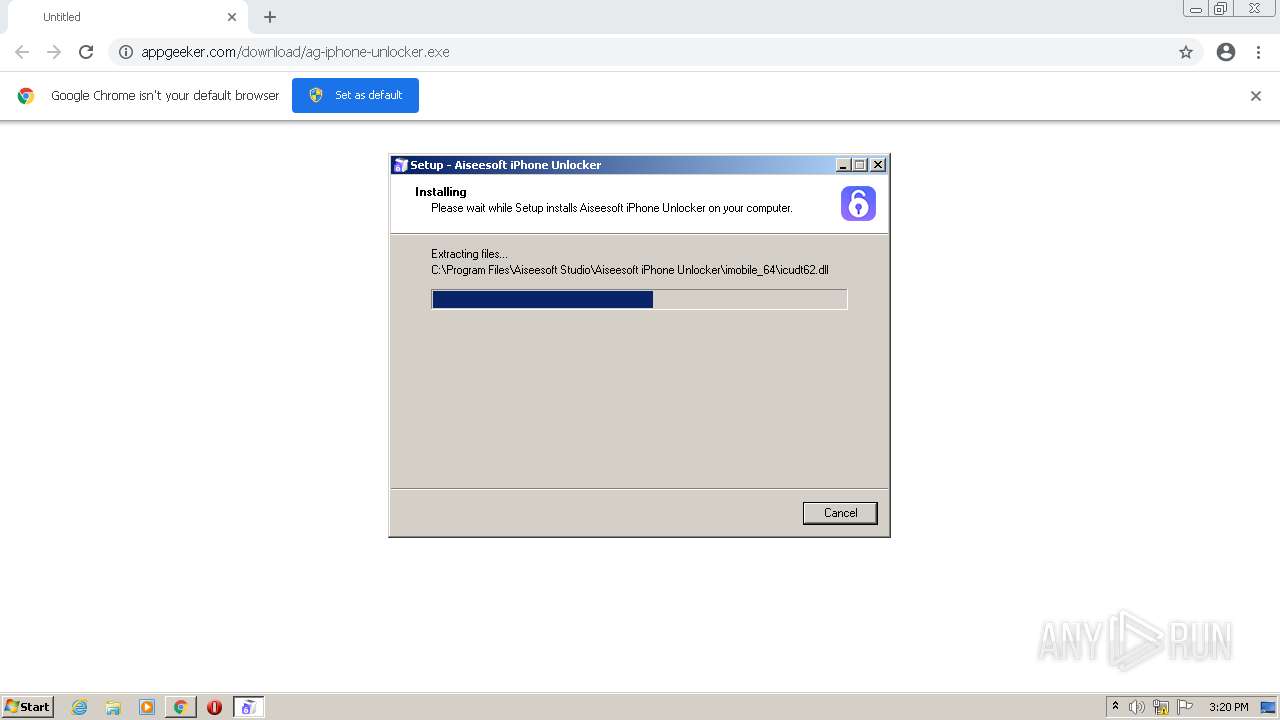
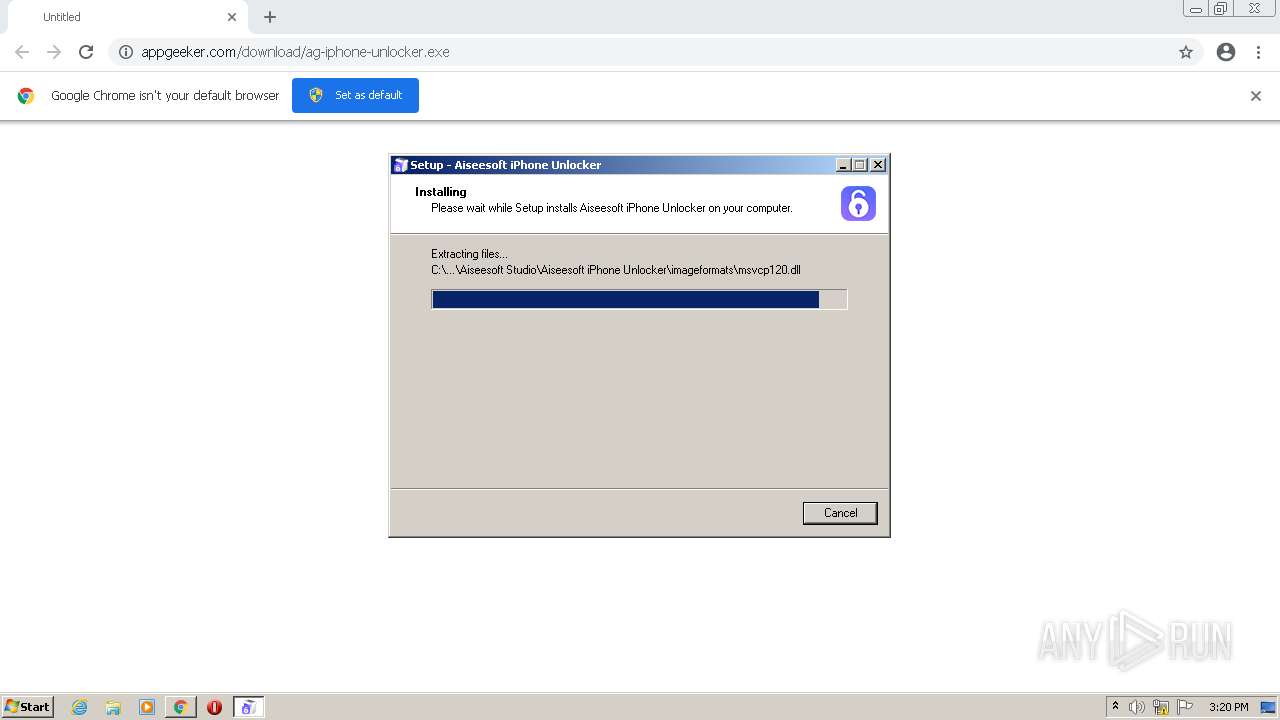
Drops executable file immediately after starts
- chrome.exe (PID: 2968)
- ag-iphone-unlocker.exe (PID: 1256)
- ag-iphone-unlocker.tmp (PID: 3160)
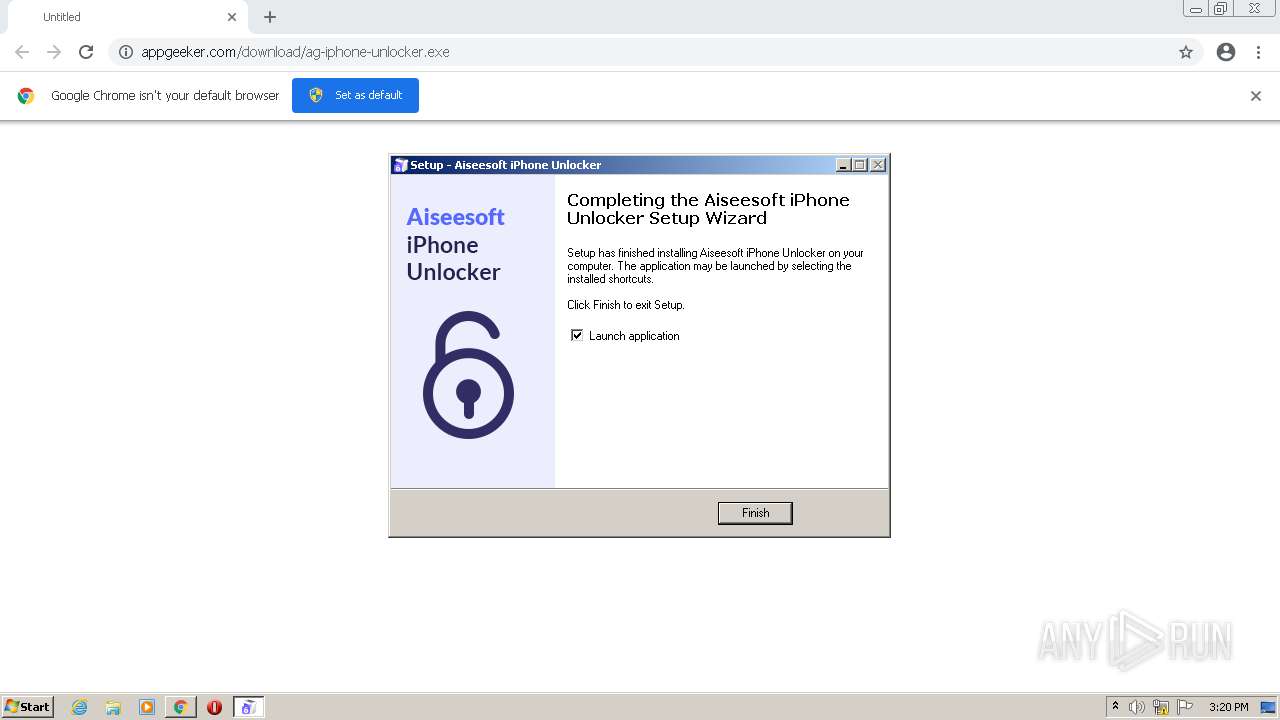
Application was dropped or rewritten from another process
- ag-iphone-unlocker.exe (PID: 3868)
- ag-iphone-unlocker.exe (PID: 1256)
- Aiseesoft iPhone Unlocker.exe (PID: 3644)
- Aiseesoft iPhone Unlocker.exe (PID: 1960)
- splashScreen.exe (PID: 2628)
- Aiseesoft iPhone Unlocker.exe (PID: 2560)
Loads dropped or rewritten executable
- Aiseesoft iPhone Unlocker.exe (PID: 3644)
- Aiseesoft iPhone Unlocker.exe (PID: 1960)
- Aiseesoft iPhone Unlocker.exe (PID: 2560)
- splashScreen.exe (PID: 2628)
Changes settings of System certificates
- Aiseesoft iPhone Unlocker.exe (PID: 1960)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2968)
Drops a file with a compile date too recent
- chrome.exe (PID: 2968)
- ag-iphone-unlocker.exe (PID: 1256)
- ag-iphone-unlocker.tmp (PID: 3160)
Executable content was dropped or overwritten
- chrome.exe (PID: 2968)
- ag-iphone-unlocker.exe (PID: 1256)
- ag-iphone-unlocker.tmp (PID: 3160)
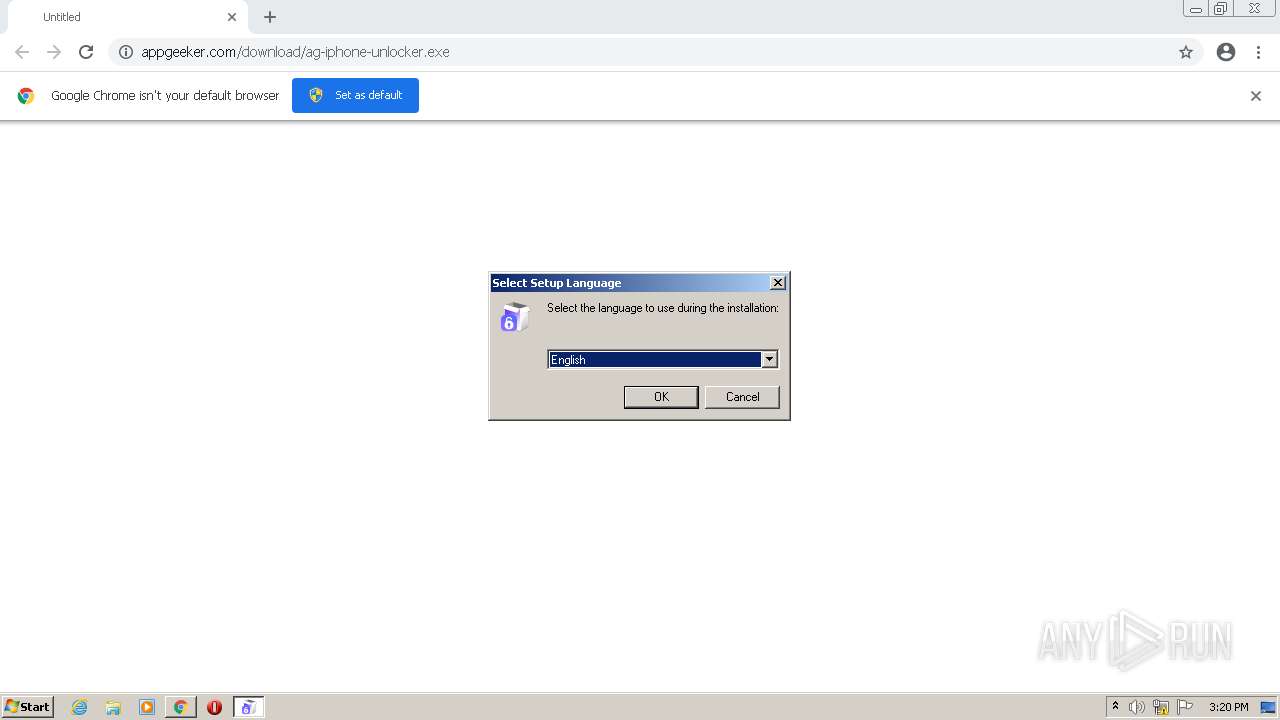
Checks supported languages
- ag-iphone-unlocker.exe (PID: 1256)
- ag-iphone-unlocker.tmp (PID: 3160)
- Aiseesoft iPhone Unlocker.exe (PID: 3644)
- Aiseesoft iPhone Unlocker.exe (PID: 1960)
- Aiseesoft iPhone Unlocker.exe (PID: 2560)
- splashScreen.exe (PID: 2628)
Reads Windows owner or organization settings
- ag-iphone-unlocker.tmp (PID: 3160)
Reads the Windows organization settings
- ag-iphone-unlocker.tmp (PID: 3160)
Reads the computer name
- ag-iphone-unlocker.tmp (PID: 3160)
- Aiseesoft iPhone Unlocker.exe (PID: 3644)
- Aiseesoft iPhone Unlocker.exe (PID: 2560)
- Aiseesoft iPhone Unlocker.exe (PID: 1960)
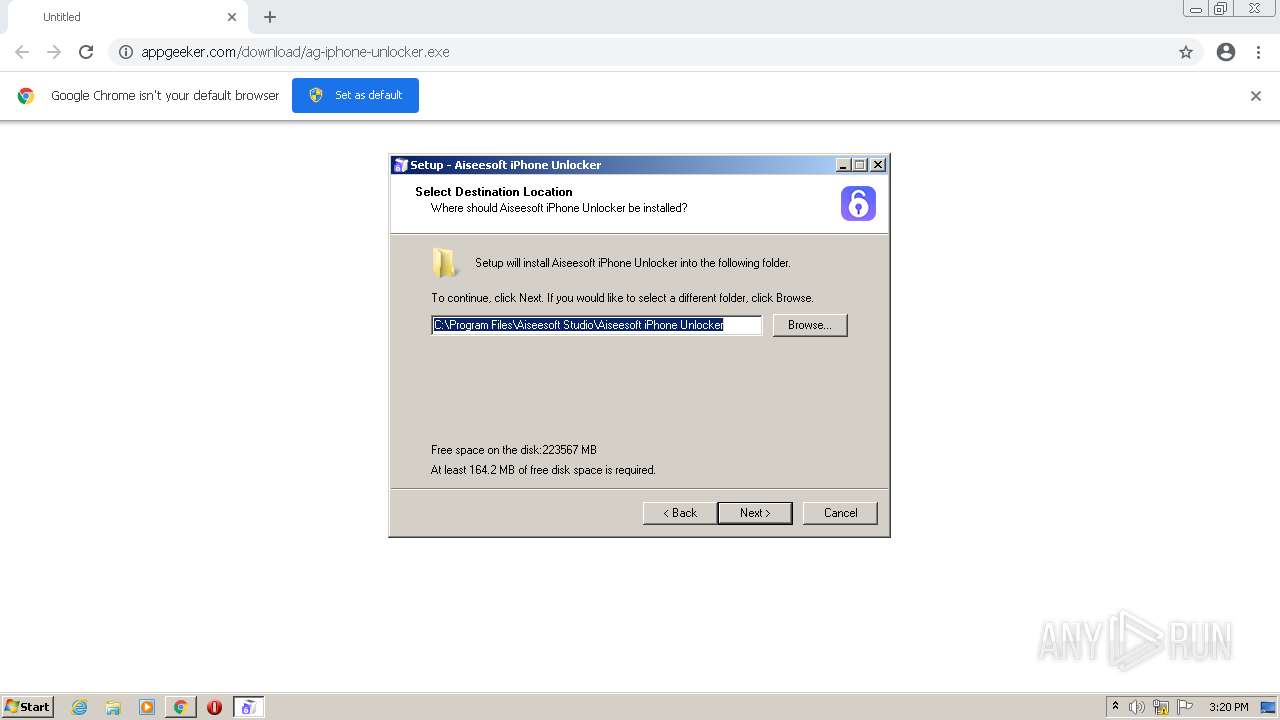
Creates a directory in Program Files
- ag-iphone-unlocker.tmp (PID: 3160)
Creates files in the user directory
- ag-iphone-unlocker.tmp (PID: 3160)
- Aiseesoft iPhone Unlocker.exe (PID: 1960)
Adds / modifies Windows certificates
- Aiseesoft iPhone Unlocker.exe (PID: 1960)
Creates files in the program directory
- Aiseesoft iPhone Unlocker.exe (PID: 1960)
INFO
Checks supported languages
- chrome.exe (PID: 2968)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 2180)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 3196)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 2108)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 1064)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 1864)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 1368)
Application launched itself
- chrome.exe (PID: 2968)
Reads the computer name
- chrome.exe (PID: 2968)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 2108)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 1864)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 1064)
Reads the hosts file
- chrome.exe (PID: 2968)
- chrome.exe (PID: 3704)
Reads settings of System Certificates
- chrome.exe (PID: 3704)
- chrome.exe (PID: 2968)
- Aiseesoft iPhone Unlocker.exe (PID: 2560)
- Aiseesoft iPhone Unlocker.exe (PID: 1960)
Reads the date of Windows installation
- chrome.exe (PID: 1064)
Checks Windows Trust Settings
- chrome.exe (PID: 2968)
- Aiseesoft iPhone Unlocker.exe (PID: 1960)
Application was dropped or rewritten from another process
- ag-iphone-unlocker.tmp (PID: 3160)
Dropped object may contain Bitcoin addresses
- ag-iphone-unlocker.tmp (PID: 3160)
- Aiseesoft iPhone Unlocker.exe (PID: 1960)
Creates a software uninstall entry
- ag-iphone-unlocker.tmp (PID: 3160)
Creates files in the program directory
- ag-iphone-unlocker.tmp (PID: 3160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
26
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,17785874611062118292,12929897628536221533,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1256 | "C:\Users\admin\Downloads\ag-iphone-unlocker.exe" | C:\Users\admin\Downloads\ag-iphone-unlocker.exe | chrome.exe | ||||||||||||
User: admin Company: Aiseesoft Studio Integrity Level: HIGH Description: Exit code: 0 Version: 1.0.36 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1044,17785874611062118292,12929897628536221533,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2488 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,17785874611062118292,12929897628536221533,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1960 | "C:\Program Files\Aiseesoft Studio\Aiseesoft iPhone Unlocker\Aiseesoft iPhone Unlocker.exe" | C:\Program Files\Aiseesoft Studio\Aiseesoft iPhone Unlocker\Aiseesoft iPhone Unlocker.exe | ag-iphone-unlocker.tmp | ||||||||||||
User: admin Company: Aiseesoft Integrity Level: HIGH Description: Aiseesoft iPhone Unlocker Exit code: 0 Version: 1.0.36.930 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,17785874611062118292,12929897628536221533,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3192 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,17785874611062118292,12929897628536221533,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1828 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,17785874611062118292,12929897628536221533,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Aiseesoft Studio\Aiseesoft iPhone Unlocker\Aiseesoft iPhone Unlocker.exe" --access_after_install_counting_url | C:\Program Files\Aiseesoft Studio\Aiseesoft iPhone Unlocker\Aiseesoft iPhone Unlocker.exe | ag-iphone-unlocker.tmp | ||||||||||||
User: admin Company: Aiseesoft Integrity Level: HIGH Description: Aiseesoft iPhone Unlocker Exit code: 0 Version: 1.0.36.930 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Aiseesoft Studio\Aiseesoft iPhone Unlocker\splashScreen.exe" -l ZW4= -m1 PGZvbnQgY29sb3IgPSAjMjgyNDU1PkxvYWRpbmcgbGFuZ3VhZ2UuLi48L2ZvbnQ+ -c PGZvbnQgY29sb3I9IzI4MjQ1NT5Db3B5cmlnaHQgPHNwYW4gc3R5bGU9ImZvbnQtZmFtaWx5OkFyaWFsOyI+JmNvcHk7PC9zcGFuPiAyMDIxIEFpc2Vlc29mdCBTdHVkaW8uIEFsbCByaWdodHMgcmVzZXJ2ZWQuPC9mb250Pg== -v PGI+PGZvbnQgY29sb3IgPSAjMjgyNDU1PlZlcnNpb246IDEuMC4zNjwvZm9udD4= -m2 PGZvbnQgY29sb3IgPSAjMjgyNDU1PkZyYW1ld29yayBpbml0aWFsaXppbmcuLi48L2ZvbnQ+ -m3 PGZvbnQgY29sb3IgPSAjMjgyNDU1PkxvYWRpbmcgc2tpbi4uLjwvZm9udD4= -m4 PGZvbnQgY29sb3IgPSAjMjgyNDU1PlByZXBhcmluZyBtYWluIHdpbmRvdy4uLjwvZm9udD4= -f VGFob21h | C:\Program Files\Aiseesoft Studio\Aiseesoft iPhone Unlocker\splashScreen.exe | — | Aiseesoft iPhone Unlocker.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 62097 Modules
| |||||||||||||||
Total events
22 919
Read events
22 678
Write events
230
Delete events
11
Modification events
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
403
Suspicious files
132
Text files
127
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62A0AFD1-B98.pma | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d7e2e392-b152-4b1d-b69c-baf230a25b34.tmp | text | |
MD5:900E45241ADADE7E3CDB178B8D6D3D9F | SHA256:27BB59C368CDF326F3D94277B43307DBF60AB141889B7654FEC88A953C7B7822 | |||
| 3192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:900E45241ADADE7E3CDB178B8D6D3D9F | SHA256:27BB59C368CDF326F3D94277B43307DBF60AB141889B7654FEC88A953C7B7822 | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFfd836.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFfd9dc.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
24
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 74.125.111.71:80 | http://r2---sn-5go7ynld.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3?cms_redirect=yes&mh=VX&mip=82.118.29.172&mm=28&mn=sn-5go7ynld&ms=nvh&mt=1654697540&mv=m&mvi=2&pl=24&shardbypass=sd&smhost=r3---sn-5go7yne6.gvt1.com | US | — | — | whitelisted |
— | — | GET | — | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
— | — | GET | 206 | 74.125.111.71:80 | http://r2---sn-5go7ynld.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3?cms_redirect=yes&mh=VX&mip=82.118.29.172&mm=28&mn=sn-5go7ynld&ms=nvh&mt=1654697540&mv=m&mvi=2&pl=24&shardbypass=sd&smhost=r3---sn-5go7yne6.gvt1.com | US | binary | 9.49 Kb | whitelisted |
— | — | GET | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | html | 574 b | whitelisted |
— | — | HEAD | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
— | — | GET | 206 | 74.125.111.71:80 | http://r2---sn-5go7ynld.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3?cms_redirect=yes&mh=VX&mip=82.118.29.172&mm=28&mn=sn-5go7ynld&ms=nvh&mt=1654697540&mv=m&mvi=2&pl=24&shardbypass=sd&smhost=r3---sn-5go7yne6.gvt1.com | US | binary | 5.64 Kb | whitelisted |
— | — | GET | 206 | 74.125.111.71:80 | http://r2---sn-5go7ynld.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3?cms_redirect=yes&mh=VX&mip=82.118.29.172&mm=28&mn=sn-5go7ynld&ms=nvh&mt=1654697540&mv=m&mvi=2&pl=24&shardbypass=sd&smhost=r3---sn-5go7yne6.gvt1.com | US | binary | 9.49 Kb | whitelisted |
— | — | GET | 206 | 74.125.111.71:80 | http://r2---sn-5go7ynld.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3?cms_redirect=yes&mh=VX&mip=82.118.29.172&mm=28&mn=sn-5go7ynld&ms=nvh&mt=1654697540&mv=m&mvi=2&pl=24&shardbypass=sd&smhost=r3---sn-5go7yne6.gvt1.com | US | binary | 9.49 Kb | whitelisted |
— | — | GET | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | html | 574 b | whitelisted |
— | — | GET | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | html | 574 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3704 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3704 | chrome.exe | 142.250.74.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
3704 | chrome.exe | 47.90.209.240:443 | www.appgeeker.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
3704 | chrome.exe | 216.58.212.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3704 | chrome.exe | 142.250.181.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3704 | chrome.exe | 142.250.186.131:443 | update.googleapis.com | Google Inc. | US | whitelisted |
— | — | 142.250.184.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
— | — | 74.125.111.71:80 | r2---sn-5go7ynld.gvt1.com | Google Inc. | US | whitelisted |
3704 | chrome.exe | 142.250.186.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3704 | chrome.exe | 142.250.186.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
www.appgeeker.com |
| unknown |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-5go7ynld.gvt1.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Aiseesoft iPhone Unlocker.exe | "C:\\Users\\admin\\AppData\\Local\\Aiseesoft Studio\\Aiseesoft iPhone Unlocker\\CEIP\\1654698145594.ceip"
|
Aiseesoft iPhone Unlocker.exe | MAIN_Font use font "Tahoma"
|
Aiseesoft iPhone Unlocker.exe | MAIN version "1.0.36"
|
Aiseesoft iPhone Unlocker.exe | libpng warning: iCCP: known incorrect sRGB profile
|
Aiseesoft iPhone Unlocker.exe | ASL checking for logging parameters in environment variable "Aiseesoft iPhone Unlocker.exe.log"
|
Aiseesoft iPhone Unlocker.exe | ASL checking for logging parameters in environment variable "asl.log"
|
Aiseesoft iPhone Unlocker.exe | ASL logging to file "C:\Users\admin\AppData\Roaming\Apple Computer\Logs\asl.152227_08Jun22.log"
|
Aiseesoft iPhone Unlocker.exe | [(unknown facility) Aiseesoft iPhone Unlocker.exe] _SubscribeForMuxNotifications (thread 1504): USBMuxListenerCreate: No such file or directory
|
Aiseesoft iPhone Unlocker.exe | [(unknown facility) Aiseesoft iPhone Unlocker.exe] AMDeviceNotificationSubscribeWithOptions (thread 1504): Failed to subscribe for mux notifications: 0xe8000063 (kAMDMuxCreateListenerError)
|
Aiseesoft iPhone Unlocker.exe | QLayout: Attempting to add QLayout "" to FrmRemoveAppleIDDownLoadIpsw "FrmWipePasscodeDownLoadIpsw", which already has a layout
|