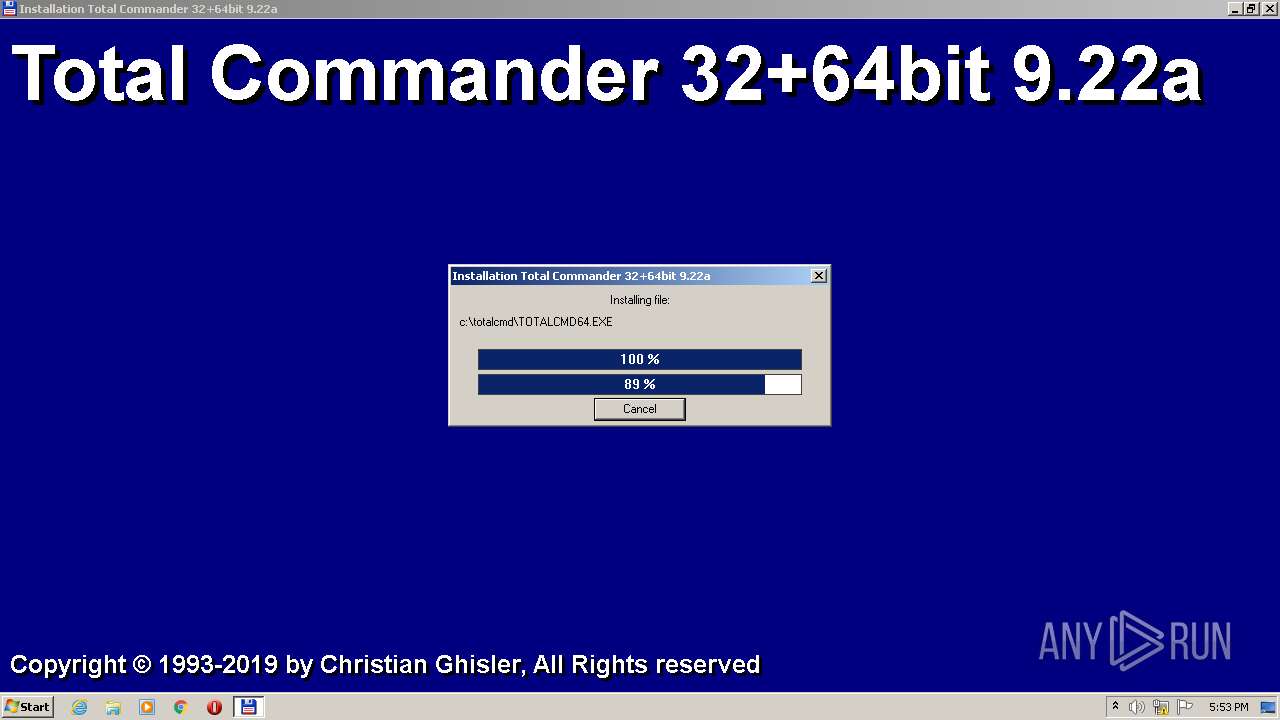
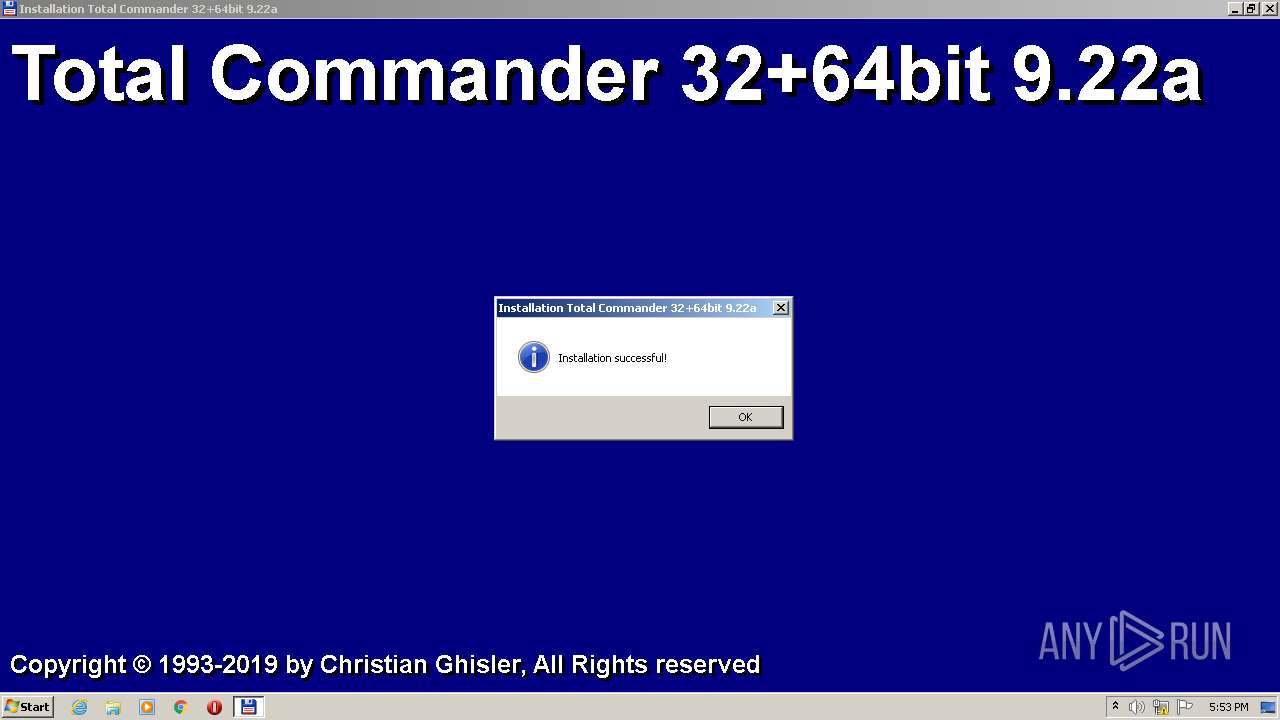
| File name: | tcmd922ax32_64.exe |
| Full analysis: | https://app.any.run/tasks/58430576-2ddc-404e-b39a-01163d25b5d5 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 16:52:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | DB7EDD4251CBDB4372D5A20915A41E9E |
| SHA1: | 2A8ED6E89DEE1DDF0401E4A84568EEBB8213B8E5 |
| SHA256: | A6F497F17FF9A0D64C1F37817EA00964F67EFDFD4F9F00B7D96867D046C90EE7 |
| SSDEEP: | 98304:oc+h9Vkx2Pl22sPo/KnN9Q5oX9aw+Y4ukPLI1EWcdTa7lp5Ptn6JRN0LwUb:BOTkx2t22rKnN9a+/UPLL7w5Ptn6rAwk |
MALICIOUS
Application was dropped or rewritten from another process
- TOTALCMD.EXE (PID: 3048)
- TOTALCMD.EXE (PID: 3508)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- tcmd922ax32_64.exe (PID: 3392)
The process creates files with name similar to system file names
- tcmd922ax32_64.exe (PID: 3392)
Executable content was dropped or overwritten
- tcmd922ax32_64.exe (PID: 3392)
Reads Microsoft Outlook installation path
- TOTALCMD.EXE (PID: 3508)
Reads Internet Explorer settings
- TOTALCMD.EXE (PID: 3508)
Reads the Internet Settings
- TOTALCMD.EXE (PID: 3508)
INFO
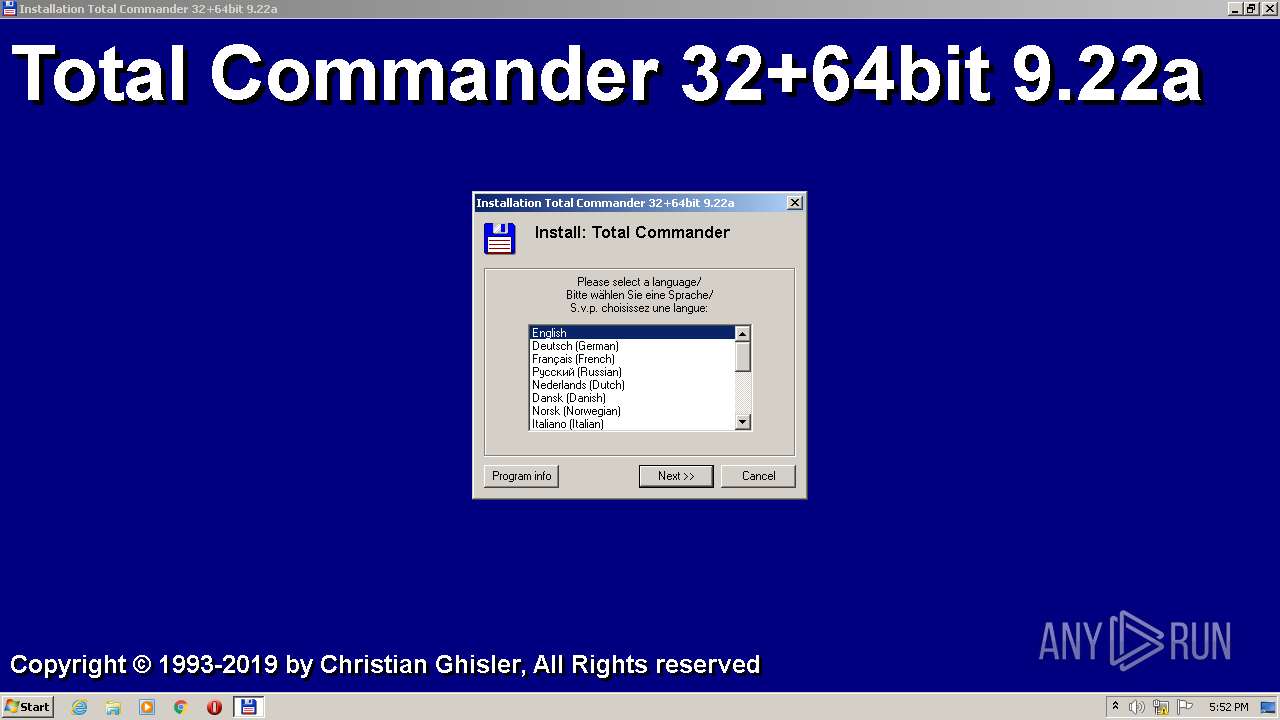
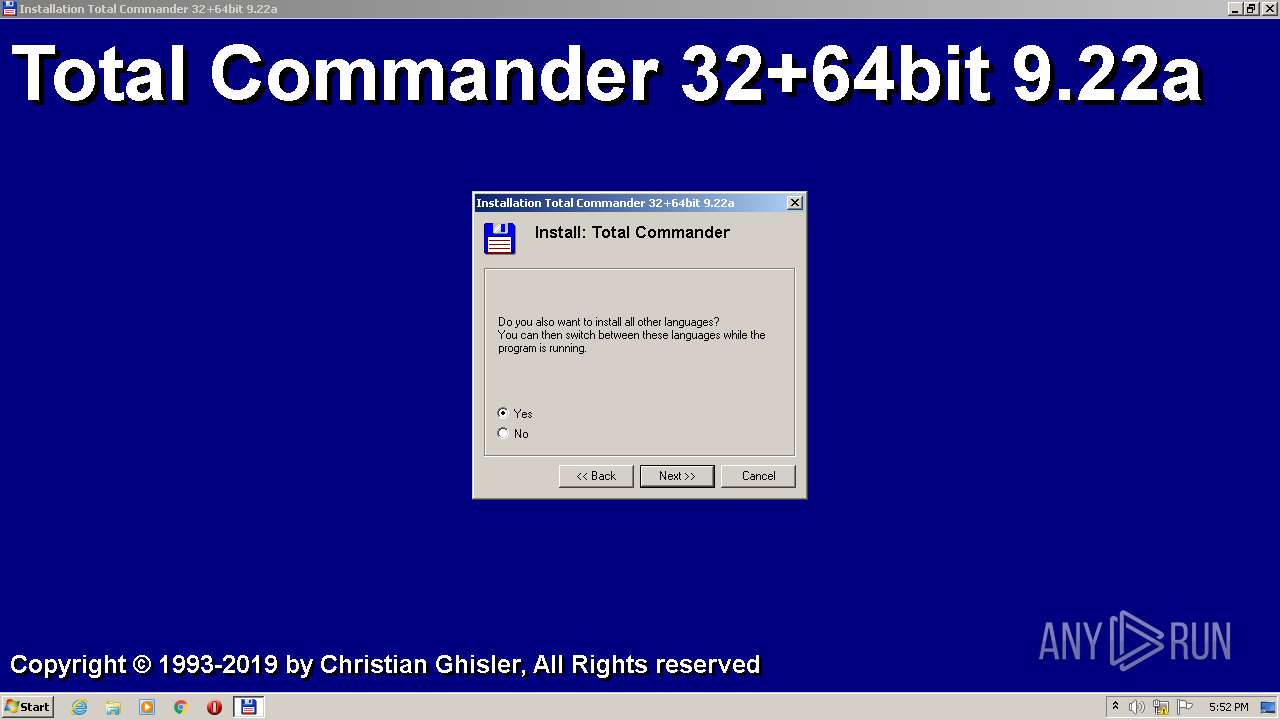
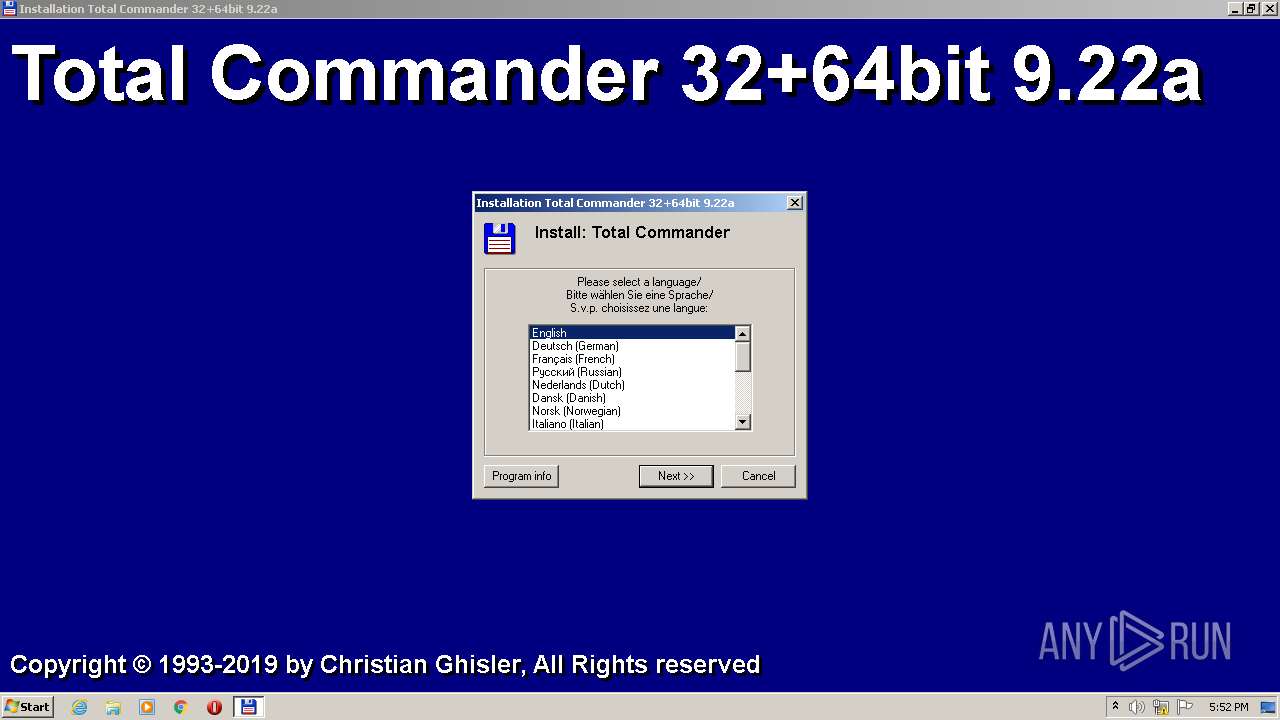
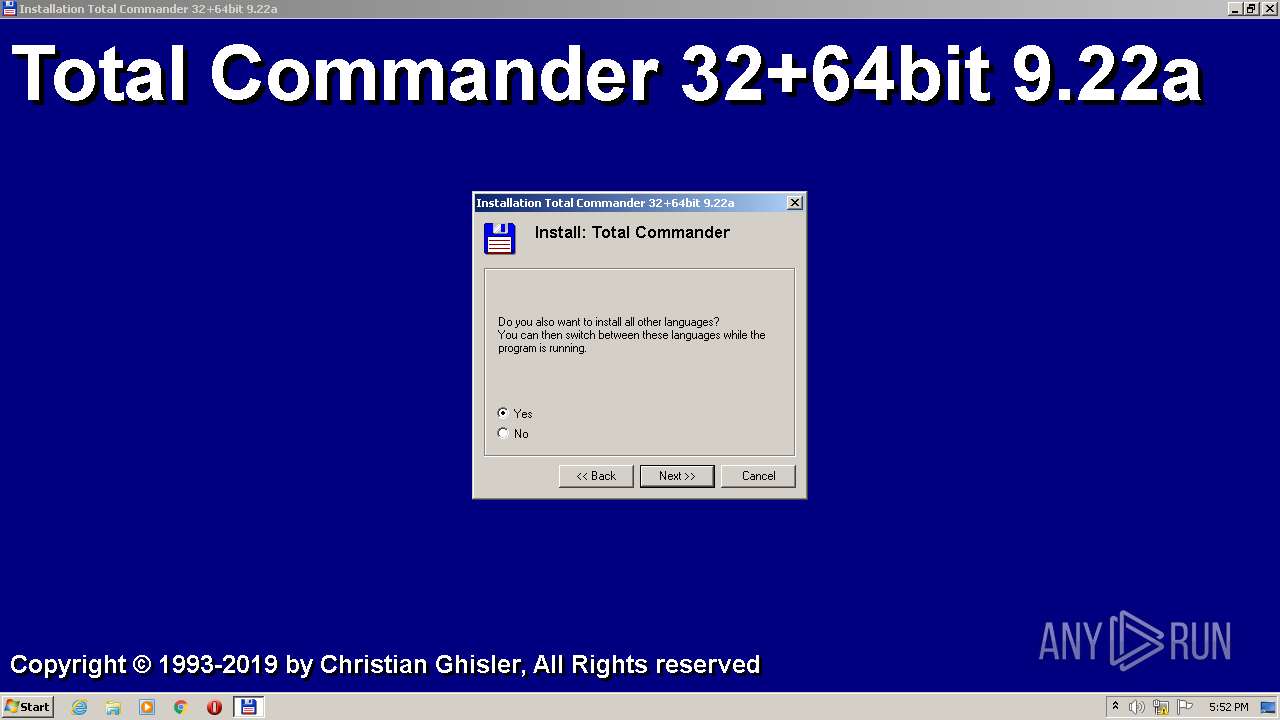
Checks supported languages
- tcmd922ax32_64.exe (PID: 3392)
- TOTALCMD.EXE (PID: 3048)
- TOTALCMD.EXE (PID: 3508)
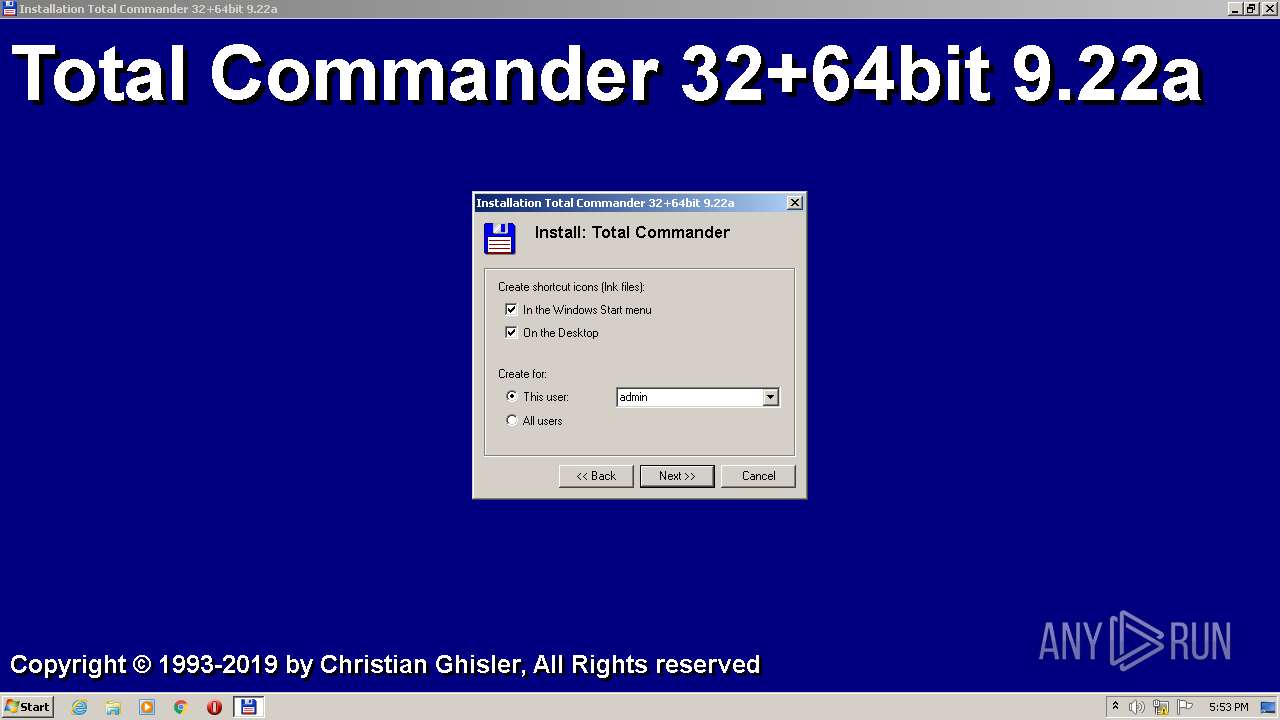
Creates files or folders in the user directory
- tcmd922ax32_64.exe (PID: 3392)
- TOTALCMD.EXE (PID: 3508)
The process checks LSA protection
- tcmd922ax32_64.exe (PID: 3392)
- TOTALCMD.EXE (PID: 3048)
- TOTALCMD.EXE (PID: 3508)
Reads the computer name
- tcmd922ax32_64.exe (PID: 3392)
- TOTALCMD.EXE (PID: 3048)
- TOTALCMD.EXE (PID: 3508)
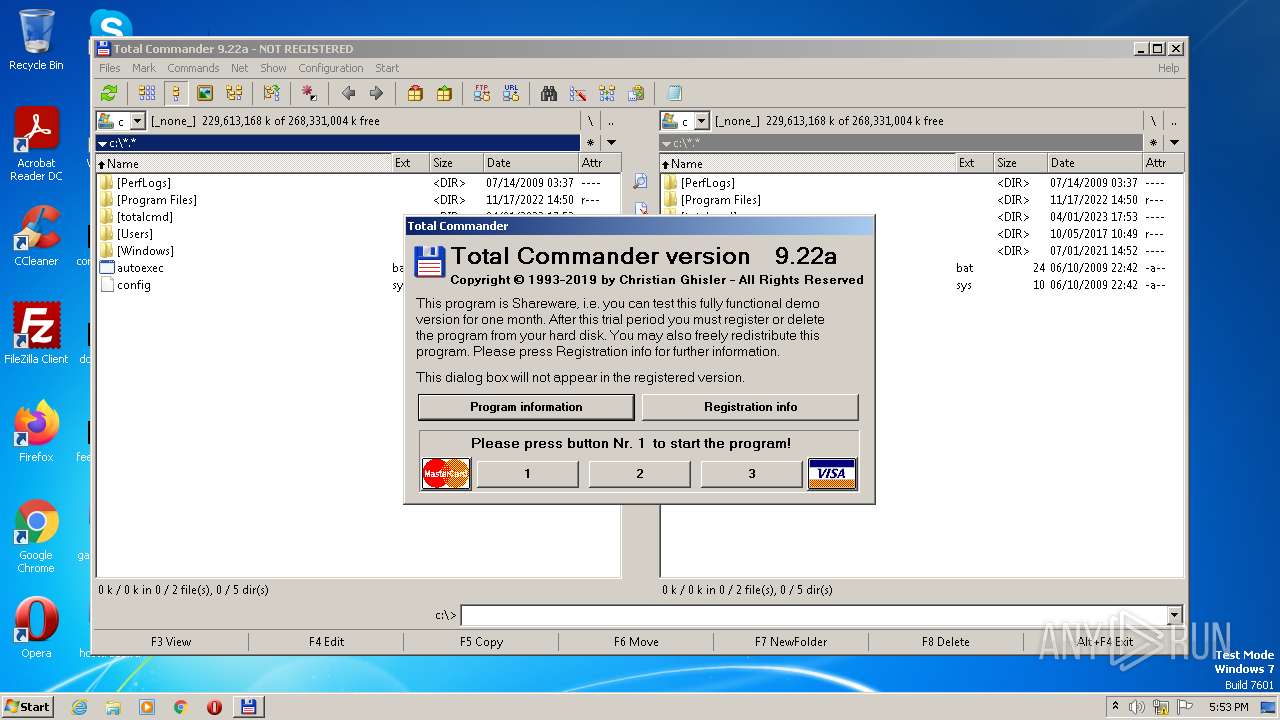
Manual execution by a user
- TOTALCMD.EXE (PID: 3048)
- TOTALCMD.EXE (PID: 3508)
Process checks are UAC notifies on
- TOTALCMD.EXE (PID: 3048)
- TOTALCMD.EXE (PID: 3508)
Reads the machine GUID from the registry
- TOTALCMD.EXE (PID: 3508)
Create files in a temporary directory
- TOTALCMD.EXE (PID: 3508)
Checks proxy server information
- TOTALCMD.EXE (PID: 3508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| SpecialBuild: | - |
|---|---|
| ProductVersion: | 9, 2, 2, 0 |
| ProductName: | - |
| PrivateBuild: | - |
| OriginalFileName: | install.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © Ghisler Software GmbH 1993-2019 |
| InternalName: | INSTALL |
| FileVersion: | 9.22 |
| FileDescription: | Total Commander Installer |
| CompanyName: | Ghisler Software GmbH |
| Comments: | - |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 9.2.2.0 |
| FileVersionNumber: | 9.2.2.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x10df5 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 57344 |
| CodeSize: | 90112 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2018:07:25 10:43:55+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jul-2018 10:43:55 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Ghisler Software GmbH |
| FileDescription: | Total Commander Installer |
| FileVersion: | 9.22 |
| InternalName: | INSTALL |
| LegalCopyright: | Copyright © Ghisler Software GmbH 1993-2019 |
| LegalTrademarks: | - |
| OriginalFilename: | install.exe |
| PrivateBuild: | - |
| ProductName: | - |
| ProductVersion: | 9, 2, 2, 0 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 25-Jul-2018 10:43:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001504B | 0x00016000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46249 |
.rdata | 0x00017000 | 0x0000174C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.61032 |
.data | 0x00019000 | 0x00008B7C | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.6939 |
.rsrc | 0x00022000 | 0x00002788 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.80346 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.16857 | 1646 | UNKNOWN | German - Switzerland | RT_MANIFEST |
2 | 3.43362 | 296 | UNKNOWN | German - Switzerland | RT_ICON |
3 | 3.16448 | 1384 | UNKNOWN | German - Switzerland | RT_ICON |
CREATELNKDLG | 3.50578 | 658 | UNKNOWN | German - Switzerland | RT_DIALOG |
DLG2FILEACTIONMIN | 2.96201 | 202 | UNKNOWN | German - Switzerland | RT_DIALOG |
INILOCATION | 3.58674 | 1154 | UNKNOWN | German - Switzerland | RT_DIALOG |
LANGUAGEDIALOG | 3.428 | 506 | UNKNOWN | German - Switzerland | RT_DIALOG |
MESSAGEBOXDLG | 3.14063 | 362 | UNKNOWN | German - Switzerland | RT_DIALOG |
MYINPUTDIALOG | 3.09404 | 342 | UNKNOWN | German - Switzerland | RT_DIALOG |
TEXTBOXDLG | 3.05155 | 110 | UNKNOWN | German - Switzerland | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
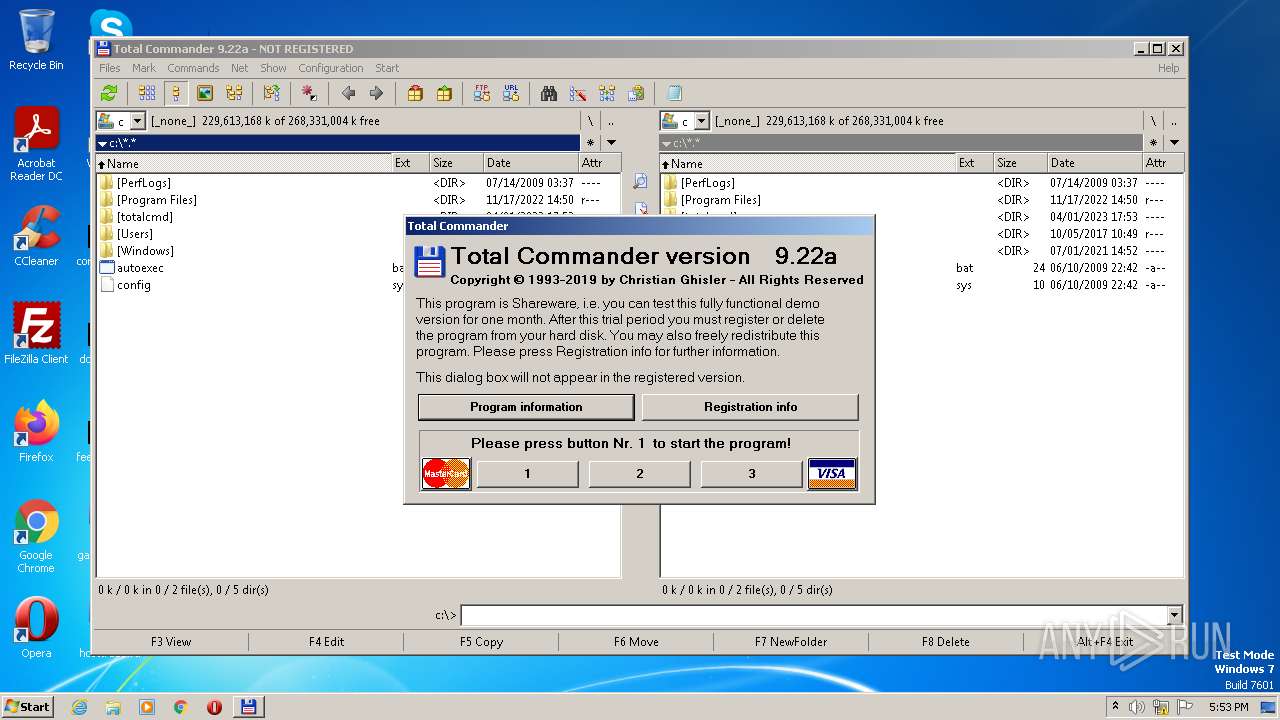
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2960 | "C:\Users\admin\Downloads\tcmd922ax32_64.exe" | C:\Users\admin\Downloads\tcmd922ax32_64.exe | — | explorer.exe | |||||||||||
User: admin Company: Ghisler Software GmbH Integrity Level: MEDIUM Description: Total Commander Installer Exit code: 3221226540 Version: 9.22 Modules
| |||||||||||||||
| 3048 | "C:\totalcmd\TOTALCMD.EXE" | C:\totalcmd\TOTALCMD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Ghisler Software GmbH Integrity Level: MEDIUM Description: Total Commander 32 bit Exit code: 0 Version: 9.22a Modules
| |||||||||||||||
| 3392 | "C:\Users\admin\Downloads\tcmd922ax32_64.exe" | C:\Users\admin\Downloads\tcmd922ax32_64.exe | explorer.exe | ||||||||||||
User: admin Company: Ghisler Software GmbH Integrity Level: HIGH Description: Total Commander Installer Exit code: 0 Version: 9.22 Modules
| |||||||||||||||
| 3508 | "C:\totalcmd\TOTALCMD.EXE" | C:\totalcmd\TOTALCMD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Ghisler Software GmbH Integrity Level: MEDIUM Description: Total Commander 32 bit Exit code: 0 Version: 9.22a Modules
| |||||||||||||||
Total events
4 404
Read events
4 378
Write events
26
Delete events
0
Modification events
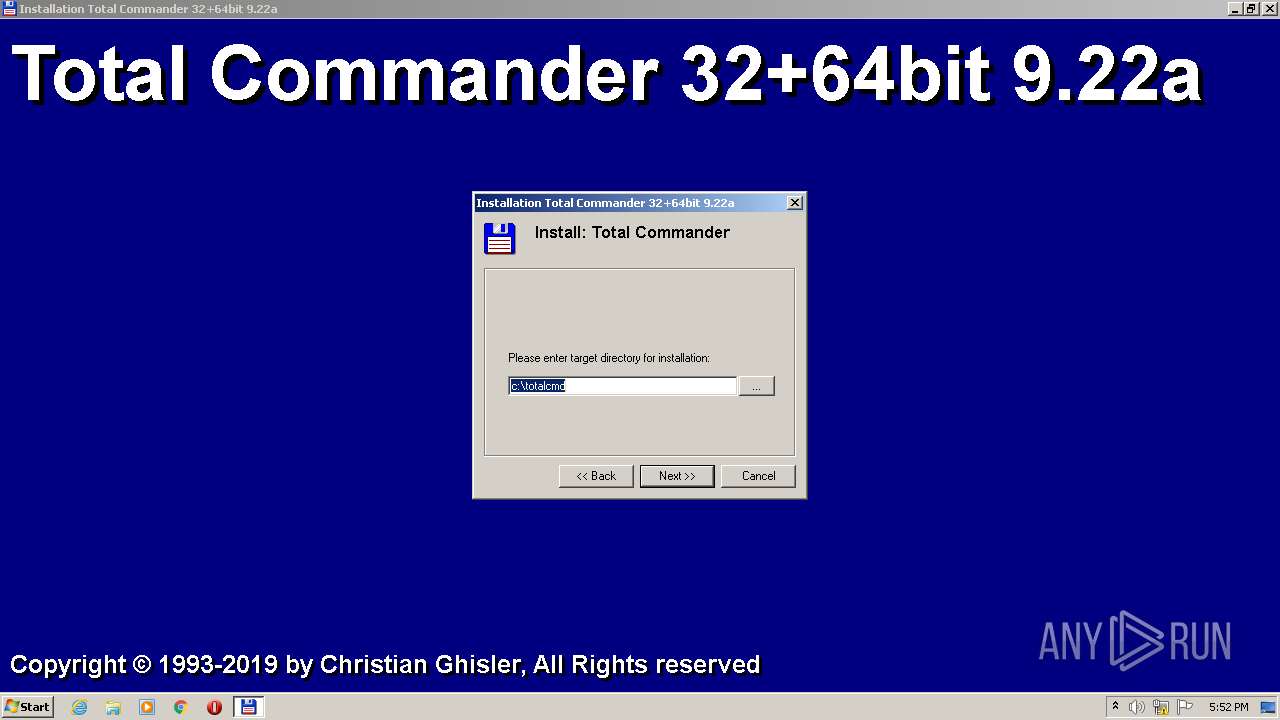
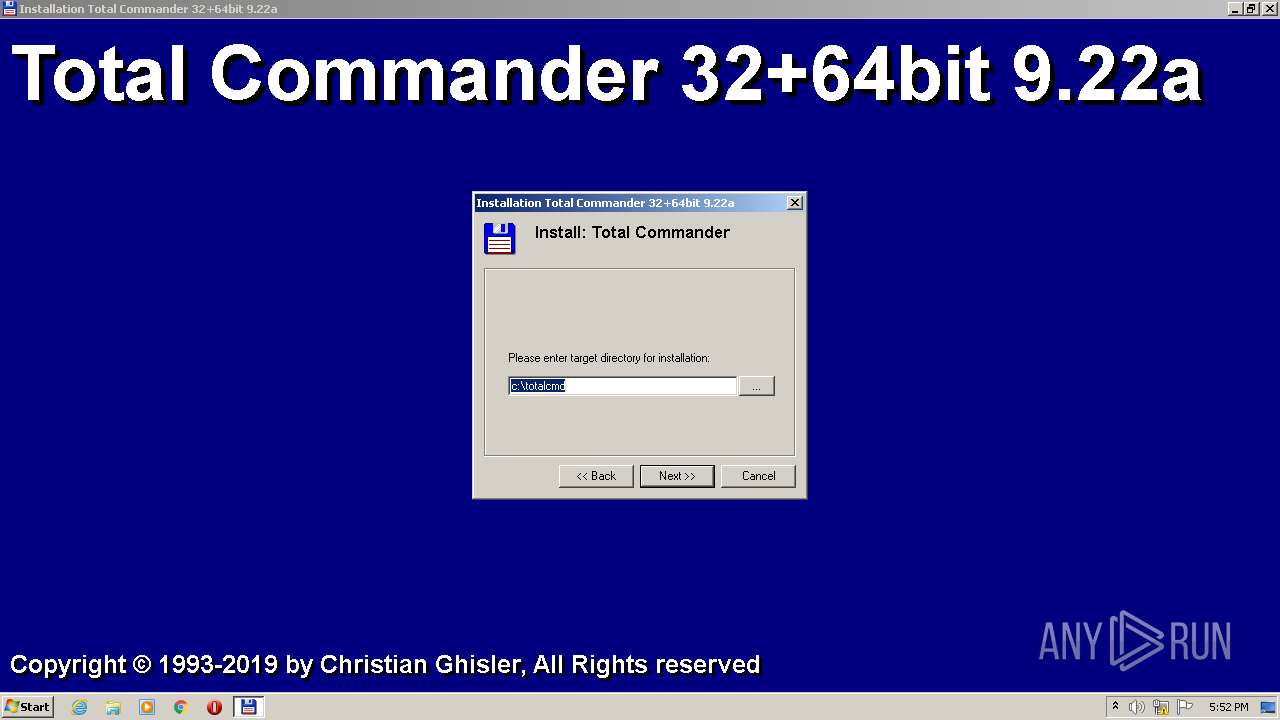
| (PID) Process: | (3392) tcmd922ax32_64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ghisler\Total Commander |
| Operation: | write | Name: | IniFileName |
Value: %APPDATA%\GHISLER\wincmd.ini | |||
| (PID) Process: | (3392) tcmd922ax32_64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ghisler\Total Commander |
| Operation: | write | Name: | FtpIniName |
Value: %APPDATA%\GHISLER\wcx_ftp.ini | |||
| (PID) Process: | (3392) tcmd922ax32_64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ghisler\Total Commander |
| Operation: | write | Name: | InstallDir |
Value: c:\totalcmd | |||
| (PID) Process: | (3508) TOTALCMD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3508) TOTALCMD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3508) TOTALCMD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3508) TOTALCMD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3508) TOTALCMD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3508) TOTALCMD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
66
Suspicious files
4
Text files
42
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | tcmd922ax32_64.exe | C:\totalcmd\HISTORY.TXT | text | |
MD5:— | SHA256:— | |||
| 3392 | tcmd922ax32_64.exe | C:\Users\admin\AppData\Roaming\GHISLER\wincmd.ini | text | |
MD5:926EB45A00D3C2C4AFEF6CE8AC07691B | SHA256:BF16FB4BAC9923E4327E3DD4F8398F0996B7395509123830F52A9B6EF66E3467 | |||
| 3392 | tcmd922ax32_64.exe | C:\totalcmd\UNRAR64.DLL | executable | |
MD5:— | SHA256:— | |||
| 3392 | tcmd922ax32_64.exe | C:\totalcmd\WCMZIP64.DLL | executable | |
MD5:47FA6B8B41A57B41127C4061CC721035 | SHA256:A60EF1EC218FADE1BDCA252B5CEB50EB6EF45B75EDFE07CAEE3F50AFFCFED9FB | |||
| 3392 | tcmd922ax32_64.exe | C:\totalcmd\TCUNIN64.WUL | text | |
MD5:3D51B5D4365B3D43E5B44D0B7377AC14 | SHA256:6A563B945A7527AF53A40F2CA4F67988F1B4018FE5E8D803E467A0BFF341708F | |||
| 3392 | tcmd922ax32_64.exe | C:\totalcmd\WCUNINST.WUL | text | |
MD5:551A9FB9B1EB85562B7BBB63D250DAA2 | SHA256:F442DA9DAA63BACFC8911B226941D0408E0BA0A891115C4F44BE3D70AD98CD48 | |||
| 3392 | tcmd922ax32_64.exe | C:\totalcmd\TCUNZL64.DLL | executable | |
MD5:5B2ED0ECADF3F7D25132B143987BEB95 | SHA256:806C77E162ACD673095ED7A9035CAC5770795235BBA3647CA351EA8D675B87DB | |||
| 3392 | tcmd922ax32_64.exe | C:\totalcmd\WCMICONS.INC | text | |
MD5:EE007FE2C0767D99EA41DC14053CB087 | SHA256:A2AA6A6A622331EF483D7CF144B3E676A4699FDCDFB101B4FF3C6A7EF294D437 | |||
| 3392 | tcmd922ax32_64.exe | C:\totalcmd\WCMICON2.DLL | executable | |
MD5:A62B33507EF138E251E1A530D91824EE | SHA256:4E8C92B0BF809B3C9D54AB3CE8820ECB70F394EBC7E2E9089D1CA8D862201725 | |||
| 3392 | tcmd922ax32_64.exe | C:\totalcmd\SIZE!.TXT | text | |
MD5:9C46B722FA1FFAB6EAD573859ABB32BB | SHA256:2EA390F71ED637935463CFEB1E4B02BB83364A157E443644087E6D61DEAE12F7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report