| File name: | hrsword.exe |
| Full analysis: | https://app.any.run/tasks/8994b11f-f837-4eeb-84e3-f85672bbed52 |
| Verdict: | Malicious activity |
| Analysis date: | May 04, 2020, 19:09:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 32DAD2ACCE51B9474545EFD6D3B49C06 |
| SHA1: | 77FF0EC1AFA6758B52BEDB5E920F2AE16155A878 |
| SHA256: | A6EB7A7372C462B2E181014540491A062C540EDC4BA0F65A9169CFBFB473E6C7 |
| SSDEEP: | 49152:uy+7vlXiY0zkUuut9O1IpxpBUCchsxt4XqEkxqaVgNaVb5gc:uyadCzkUbNLTiVdkxxt |
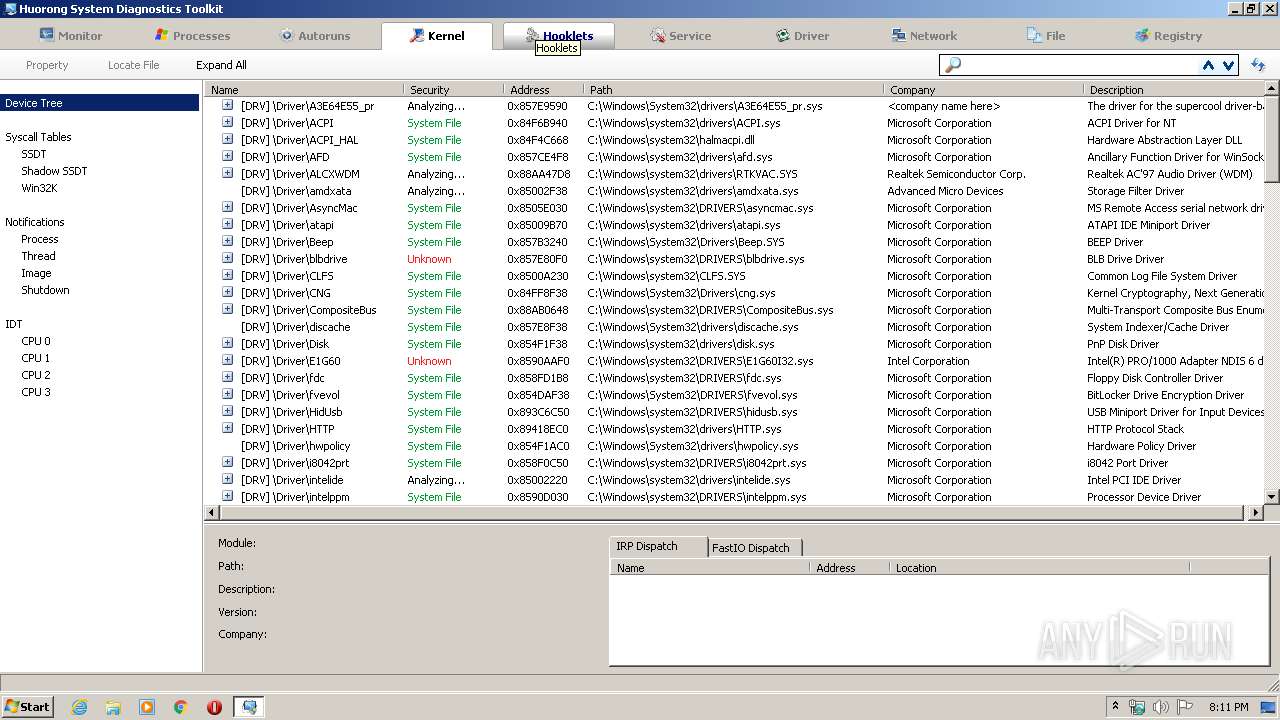
MALICIOUS
Loads dropped or rewritten executable
- hrsword.exe (PID: 3128)
- usysdiag.exe (PID: 1916)
- usysdiag.exe (PID: 2960)
- sysdiag-gui.exe (PID: 3444)
Application was dropped or rewritten from another process
- usysdiag.exe (PID: 1916)
- sysdiag-gui.exe (PID: 3132)
- sysdiag-gui.exe (PID: 3444)
- usysdiag.exe (PID: 2960)
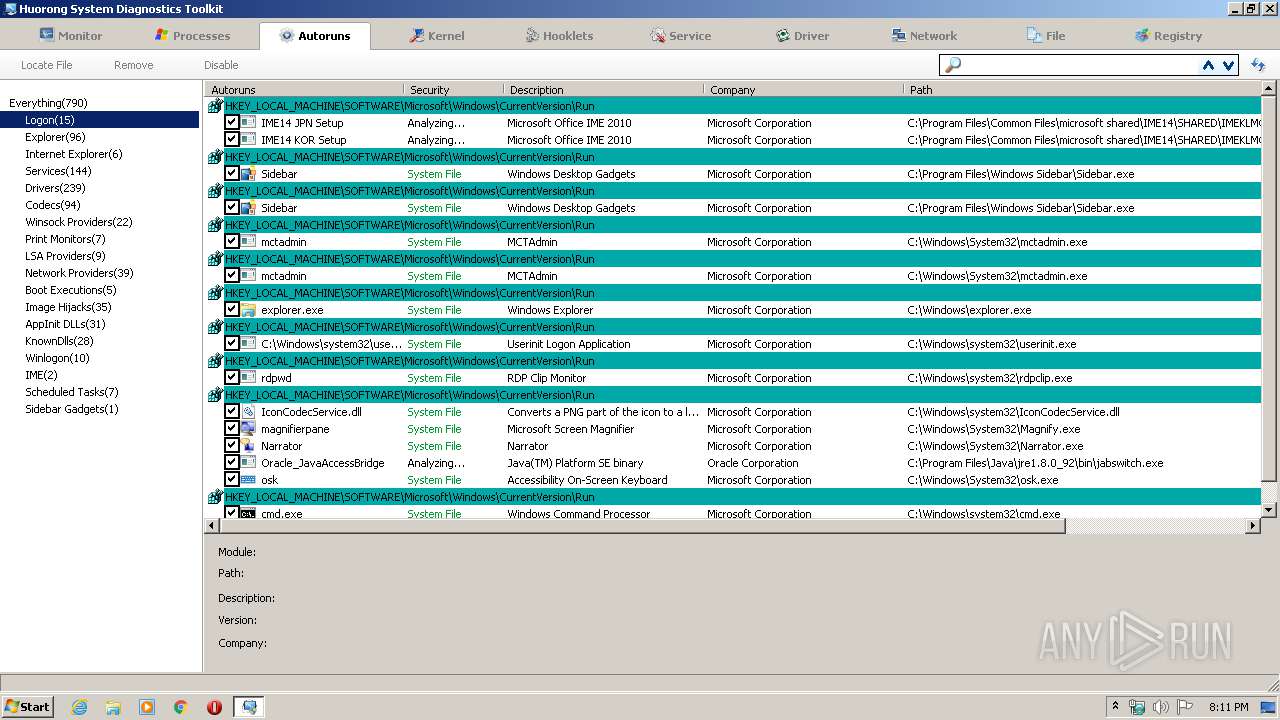
Loads the Task Scheduler COM API
- sysdiag-gui.exe (PID: 3444)
Actions looks like stealing of personal data
- sysdiag-gui.exe (PID: 3444)
Changes settings of System certificates
- usysdiag.exe (PID: 2960)
SUSPICIOUS
Executable content was dropped or overwritten
- hrsword.exe (PID: 3128)
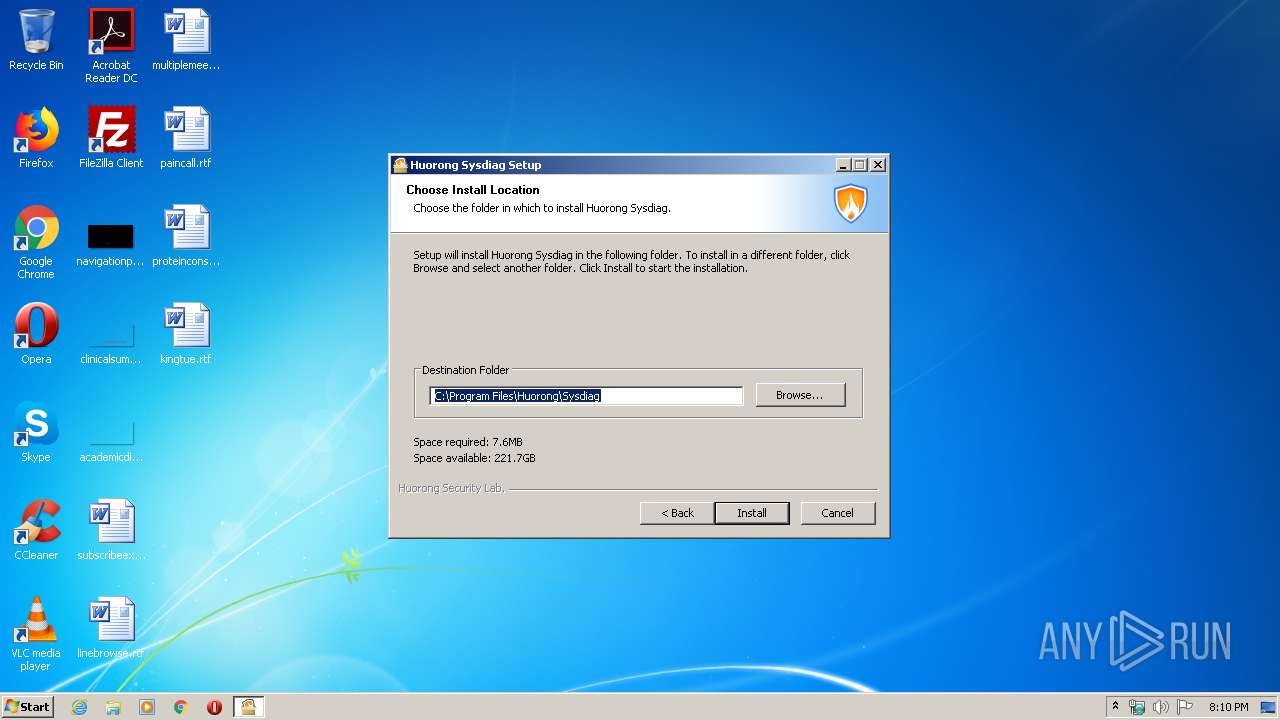
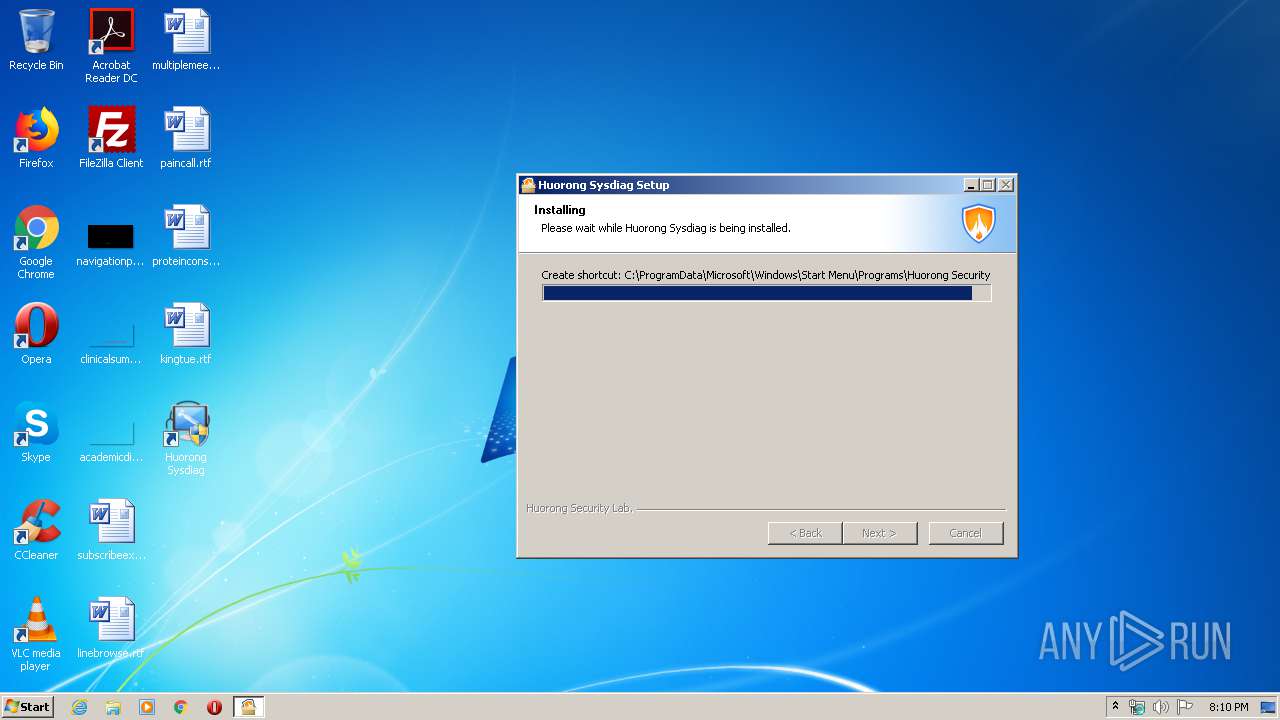
Creates a software uninstall entry
- hrsword.exe (PID: 3128)
Creates files in the program directory
- hrsword.exe (PID: 3128)
- sysdiag-gui.exe (PID: 3444)
Creates files in the driver directory
- hrsword.exe (PID: 3128)
Creates files in the Windows directory
- hrsword.exe (PID: 3128)
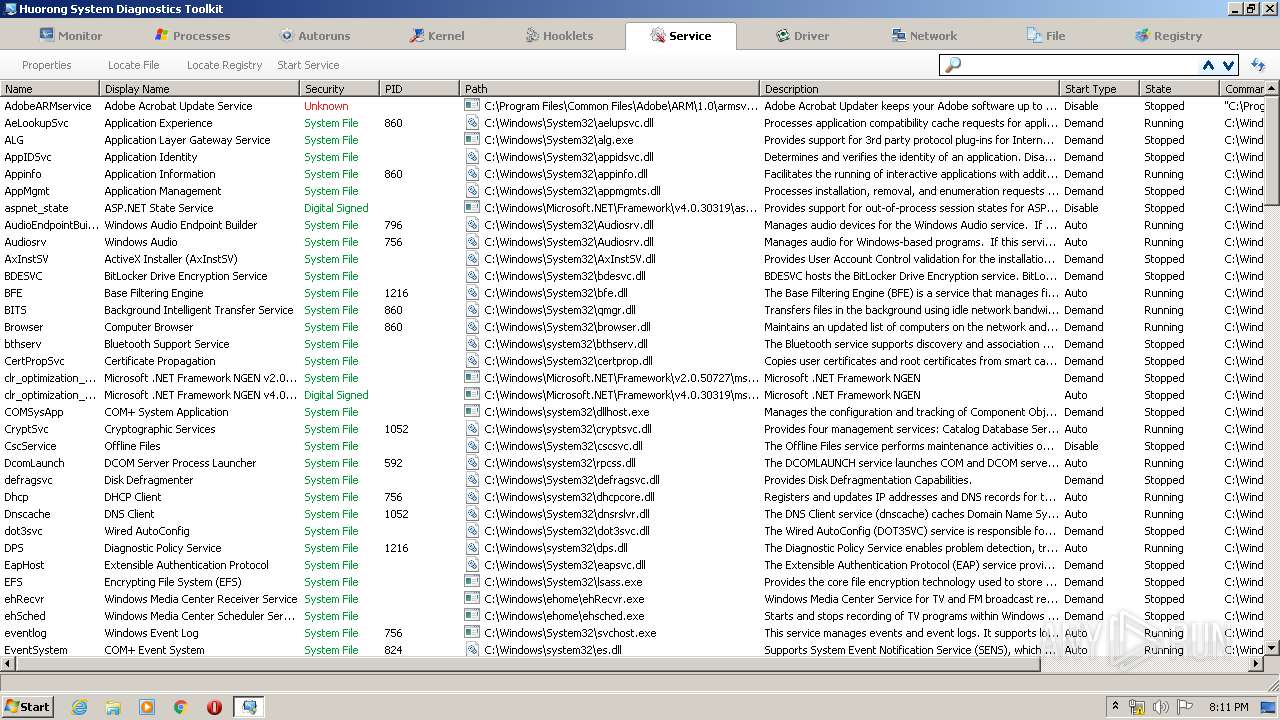
Creates or modifies windows services
- hrsword.exe (PID: 3128)
Reads Internet Cache Settings
- sysdiag-gui.exe (PID: 3444)
Adds / modifies Windows certificates
- usysdiag.exe (PID: 2960)
INFO
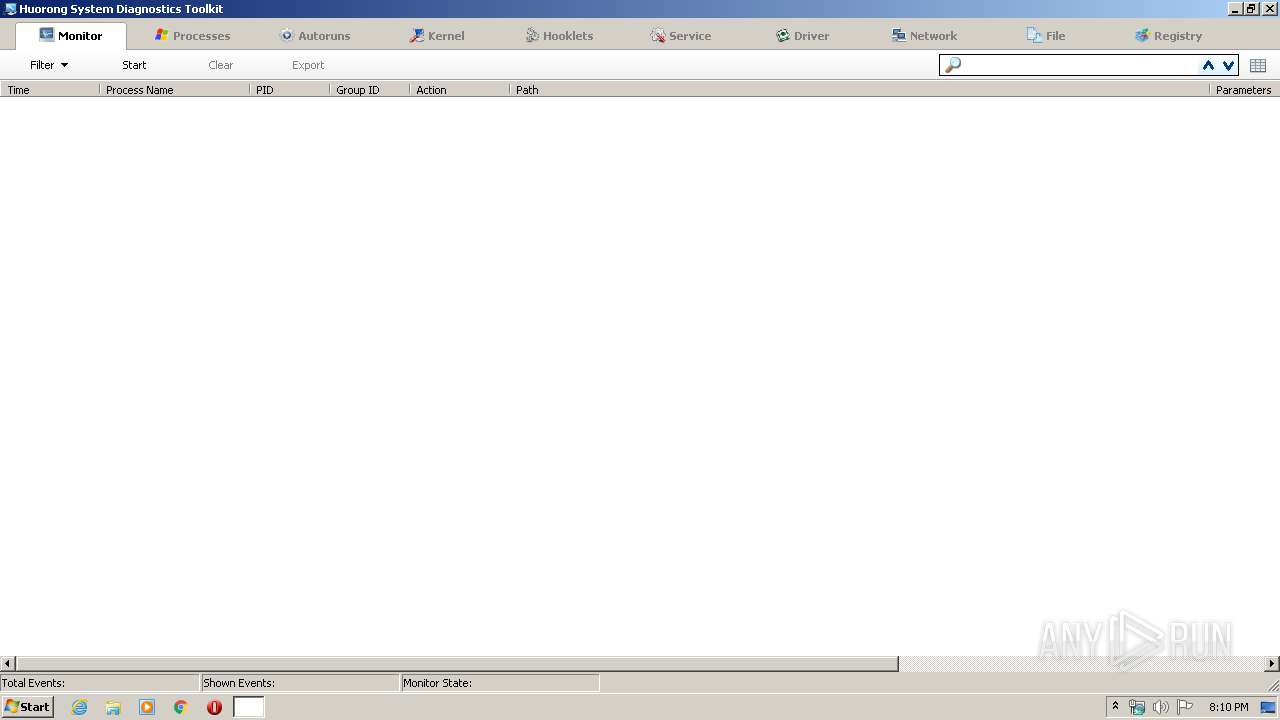
Manual execution by user
- sysdiag-gui.exe (PID: 3444)
- sysdiag-gui.exe (PID: 3132)
Reads settings of System Certificates
- usysdiag.exe (PID: 2960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.14 |
| ProductVersionNumber: | 2.0.0.14 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
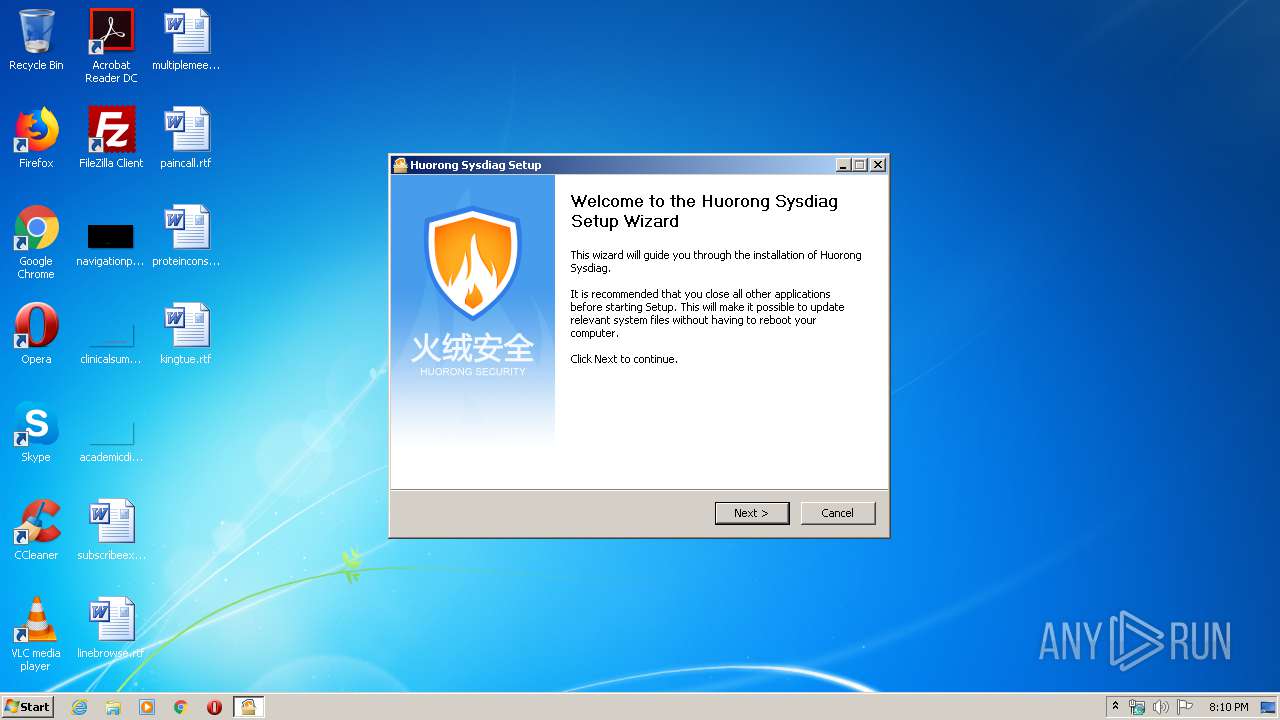
| CompanyName: | Huorong Borui (Beijing) Technology Co., Ltd. |
| FileDescription: | Huorong System Diagnostics Suite |
| FileVersion: | 2.0.0.14 |
| LegalCopyright: | Huorong Security Lab. |
| ProductName: | Huorong System Diagnostics Suite |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
| CompanyName: | 火绒博锐(北京)科技有限公司 |
| FileDescription: | 火绒剑 |
| FileVersion: | 2.0.0.14 |
| LegalCopyright: | 火绒安全实验室 |
| ProductName: | 火绒剑 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00015000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00039000 | 0x0001B250 | 0x0001A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.03998 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21482 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.14589 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 5.14538 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 5.39497 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.51898 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68372 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
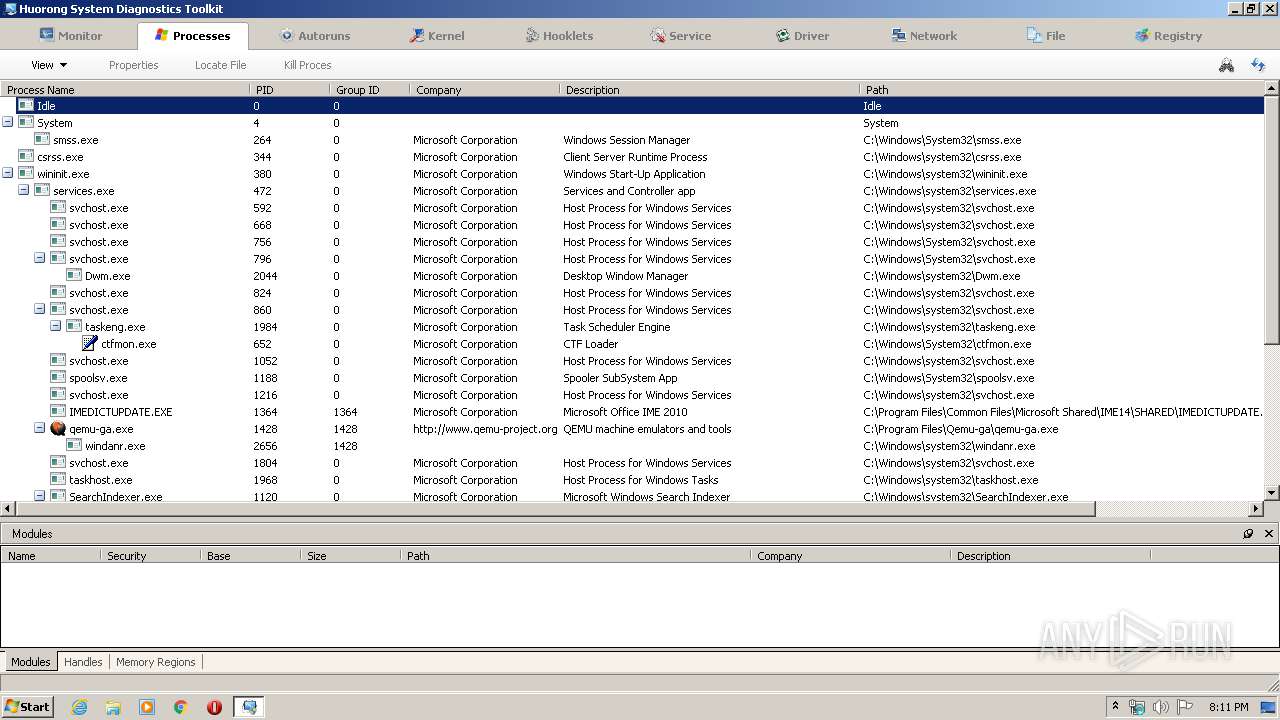
Total processes
48
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1916 | "C:\Program Files\Huorong\Sysdiag\bin\usysdiag.exe" 672 | C:\Program Files\Huorong\Sysdiag\bin\usysdiag.exe | — | hrsword.exe | |||||||||||
User: admin Company: Huorong Borui (Beijing) Technology Co., Ltd. Integrity Level: HIGH Description: Huorong Sysdiag Helper Exit code: 8 Version: 0, 1, 0, 11 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Huorong\Sysdiag\bin\usysdiag.exe" 284 | C:\Program Files\Huorong\Sysdiag\bin\usysdiag.exe | sysdiag-gui.exe | ||||||||||||
User: admin Company: Huorong Borui (Beijing) Technology Co., Ltd. Integrity Level: HIGH Description: Huorong Sysdiag Helper Exit code: 0 Version: 0, 1, 0, 11 Modules
| |||||||||||||||
| 3004 | "C:\Users\admin\AppData\Local\Temp\hrsword.exe" | C:\Users\admin\AppData\Local\Temp\hrsword.exe | — | explorer.exe | |||||||||||
User: admin Company: Huorong Borui (Beijing) Technology Co., Ltd. Integrity Level: MEDIUM Description: Huorong System Diagnostics Suite Exit code: 3221226540 Version: 2.0.0.14 Modules
| |||||||||||||||
| 3128 | "C:\Users\admin\AppData\Local\Temp\hrsword.exe" | C:\Users\admin\AppData\Local\Temp\hrsword.exe | explorer.exe | ||||||||||||
User: admin Company: Huorong Borui (Beijing) Technology Co., Ltd. Integrity Level: HIGH Description: Huorong System Diagnostics Suite Exit code: 0 Version: 2.0.0.14 Modules
| |||||||||||||||
| 3132 | "C:\Program Files\Huorong\Sysdiag\bin\sysdiag-gui.exe" | C:\Program Files\Huorong\Sysdiag\bin\sysdiag-gui.exe | — | explorer.exe | |||||||||||
User: admin Company: Huorong Borui (Beijing) Technology Co., Ltd. Integrity Level: MEDIUM Description: Huorong Sysdiag GUI Frontend Exit code: 3221226540 Version: 0, 1, 0, 36 Modules
| |||||||||||||||
| 3444 | "C:\Program Files\Huorong\Sysdiag\bin\sysdiag-gui.exe" | C:\Program Files\Huorong\Sysdiag\bin\sysdiag-gui.exe | explorer.exe | ||||||||||||
User: admin Company: Huorong Borui (Beijing) Technology Co., Ltd. Integrity Level: HIGH Description: Huorong Sysdiag GUI Frontend Exit code: 0 Version: 0, 1, 0, 36 Modules
| |||||||||||||||
Total events
3 002
Read events
1 061
Write events
1 941
Delete events
0
Modification events
| (PID) Process: | (3128) hrsword.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | DebugLevel |
Value: 1 | |||
| (PID) Process: | (3128) hrsword.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | DependOnService |
Value: FltMgr | |||
| (PID) Process: | (3128) hrsword.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (3128) hrsword.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Start |
Value: 1 | |||
| (PID) Process: | (3128) hrsword.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (3128) hrsword.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Tag |
Value: 2 | |||
| (PID) Process: | (3128) hrsword.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Group |
Value: PNP_TDI | |||
| (PID) Process: | (3128) hrsword.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | ImagePath |
Value: system32\DRIVERS\sysdiag.sys | |||
| (PID) Process: | (3128) hrsword.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | DisplayName |
Value: Huorong Network Security Core Kext | |||
| (PID) Process: | (3128) hrsword.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Description |
Value: Huorong Network Security Core Kext | |||
Executable files
15
Suspicious files
7
Text files
4
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3128 | hrsword.exe | C:\Program Files\Huorong\Sysdiag\bin\uactmon.dll | executable | |
MD5:FFAE295CC48606BA15FD9AC07C0C112F | SHA256:FAD77B24478F5EC8AA7F6018E000CF504D6227FE217D1543D4B4CBE5F8A3B1AC | |||
| 3128 | hrsword.exe | C:\Users\admin\AppData\Local\Temp\nsvF99D.tmp\AccessControl.dll | executable | |
MD5:971A1632F3F6ED6942B22B6D77692A12 | SHA256:87309681B4D29399CF333FFC4FD3E3A9690C25F265DEDC8779FBBDF2C246C648 | |||
| 3128 | hrsword.exe | C:\Users\admin\AppData\Local\Temp\nsfF98C.tmp | — | |
MD5:— | SHA256:— | |||
| 2960 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\CabD583.tmp | — | |
MD5:— | SHA256:— | |||
| 2960 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\CabD584.tmp | — | |
MD5:— | SHA256:— | |||
| 2960 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\TarD585.tmp | — | |
MD5:— | SHA256:— | |||
| 2960 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\TarD586.tmp | — | |
MD5:— | SHA256:— | |||
| 2960 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\CabD75C.tmp | — | |
MD5:— | SHA256:— | |||
| 2960 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\TarD75D.tmp | — | |
MD5:— | SHA256:— | |||
| 3128 | hrsword.exe | C:\Users\admin\AppData\Local\Temp\nsvF99D.tmp\installer-helper.dll | executable | |
MD5:BFDE6B61201B95A2892E63ADFCE22769 | SHA256:9F6363712CE45C4A09E5B1C35271EEA64EA160F6ED5679BF809AD257CBA51BBF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
6
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2960 | usysdiag.exe | GET | — | 194.55.116.71:80 | http://www.trustcenter.de/certservices/cacerts/tc_class2-II_L1_CA_IV.crt | DE | — | — | unknown |
2960 | usysdiag.exe | GET | 304 | 23.55.163.75:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
2960 | usysdiag.exe | GET | 304 | 23.55.163.75:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
2960 | usysdiag.exe | GET | 200 | 23.55.163.75:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.9 Kb | whitelisted |
2960 | usysdiag.exe | GET | 304 | 23.55.163.75:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.9 Kb | whitelisted |
2960 | usysdiag.exe | GET | 304 | 23.55.163.75:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.9 Kb | whitelisted |
2960 | usysdiag.exe | GET | 304 | 23.55.163.75:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.9 Kb | whitelisted |
2960 | usysdiag.exe | GET | 304 | 23.55.163.75:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 194.55.116.71:80 | www.trustcenter.de | Vodafone GmbH | DE | unknown |
3444 | sysdiag-gui.exe | 104.214.40.16:443 | vsblobprodscussu5shard19.blob.core.windows.net | Microsoft Corporation | US | whitelisted |
2960 | usysdiag.exe | 23.55.163.75:80 | www.download.windowsupdate.com | Akamai International B.V. | US | unknown |
3444 | sysdiag-gui.exe | 204.79.197.219:80 | msdl.microsoft.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
msdl.microsoft.com |
| whitelisted |
vsblobprodscussu5shard19.blob.core.windows.net |
| unknown |
vsblobprodscussu5shard56.blob.core.windows.net |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
www.trustcenter.de |
| unknown |