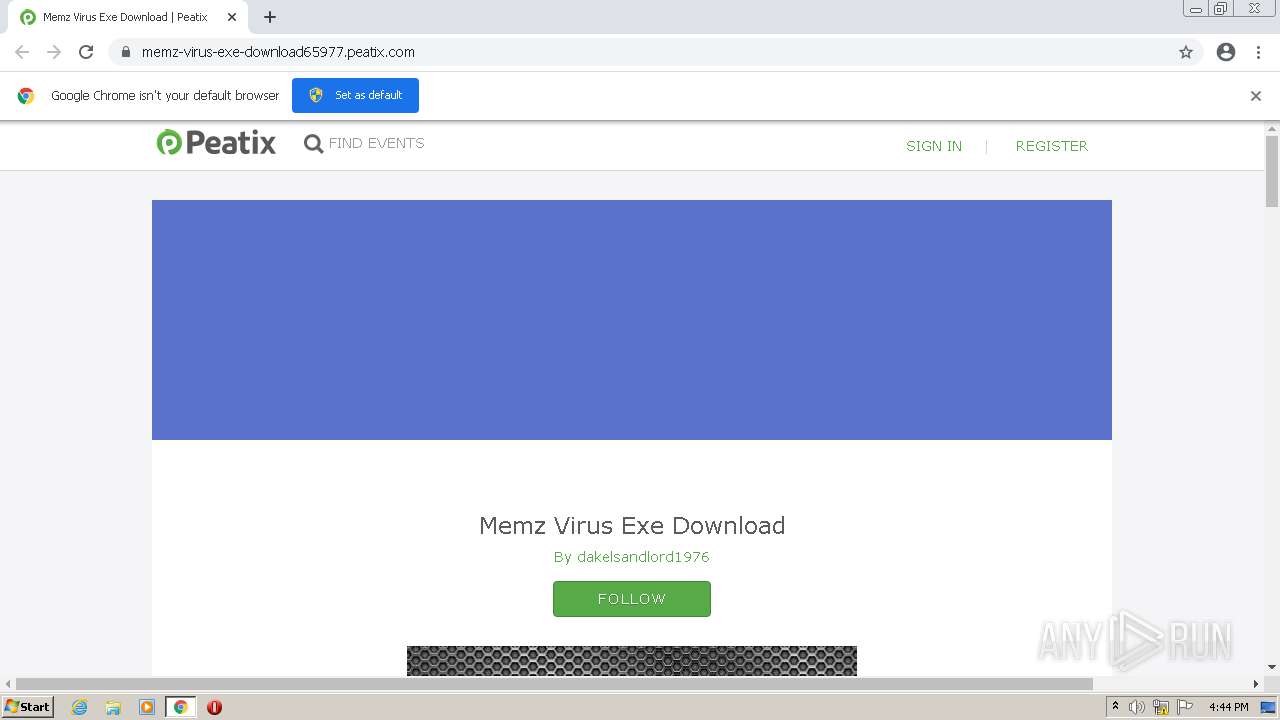
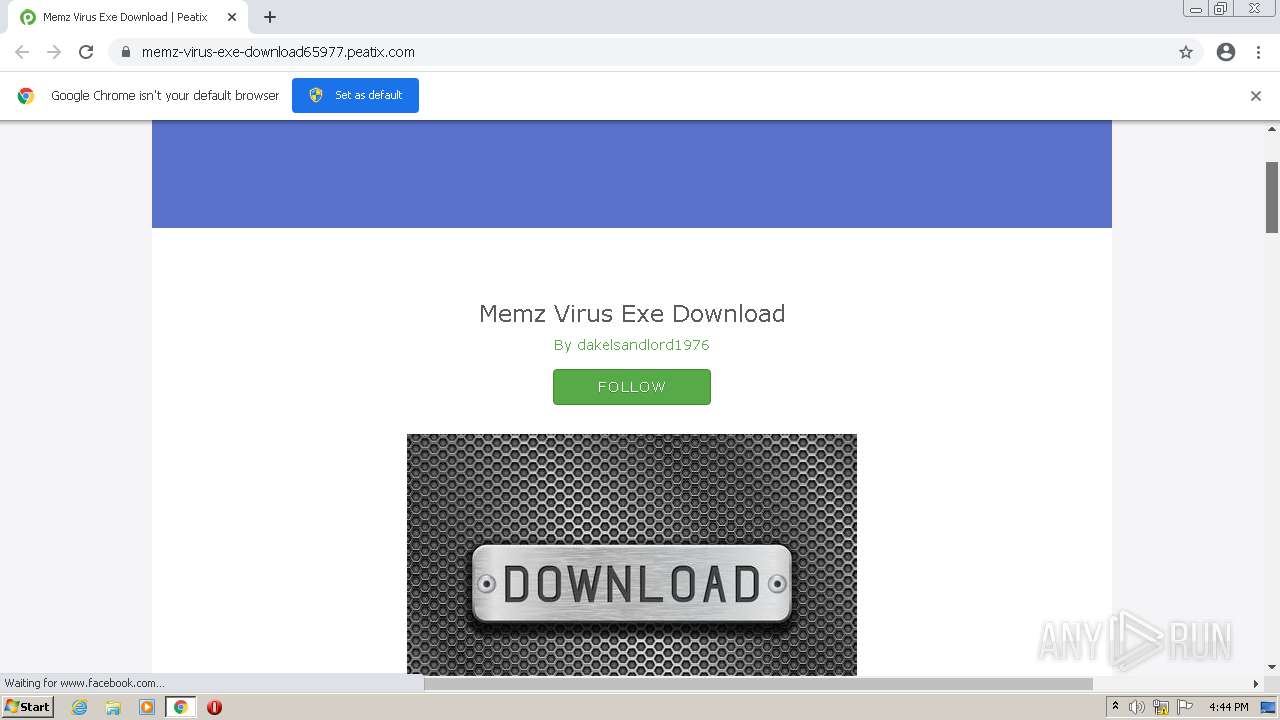
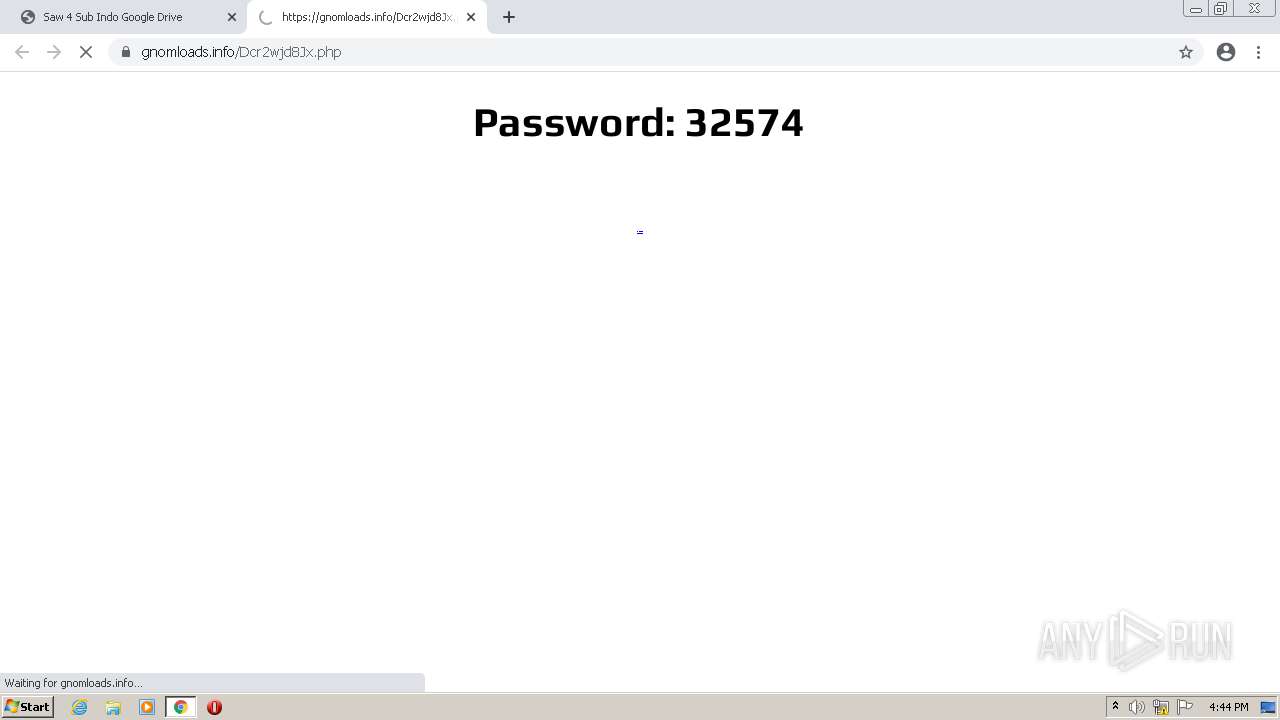
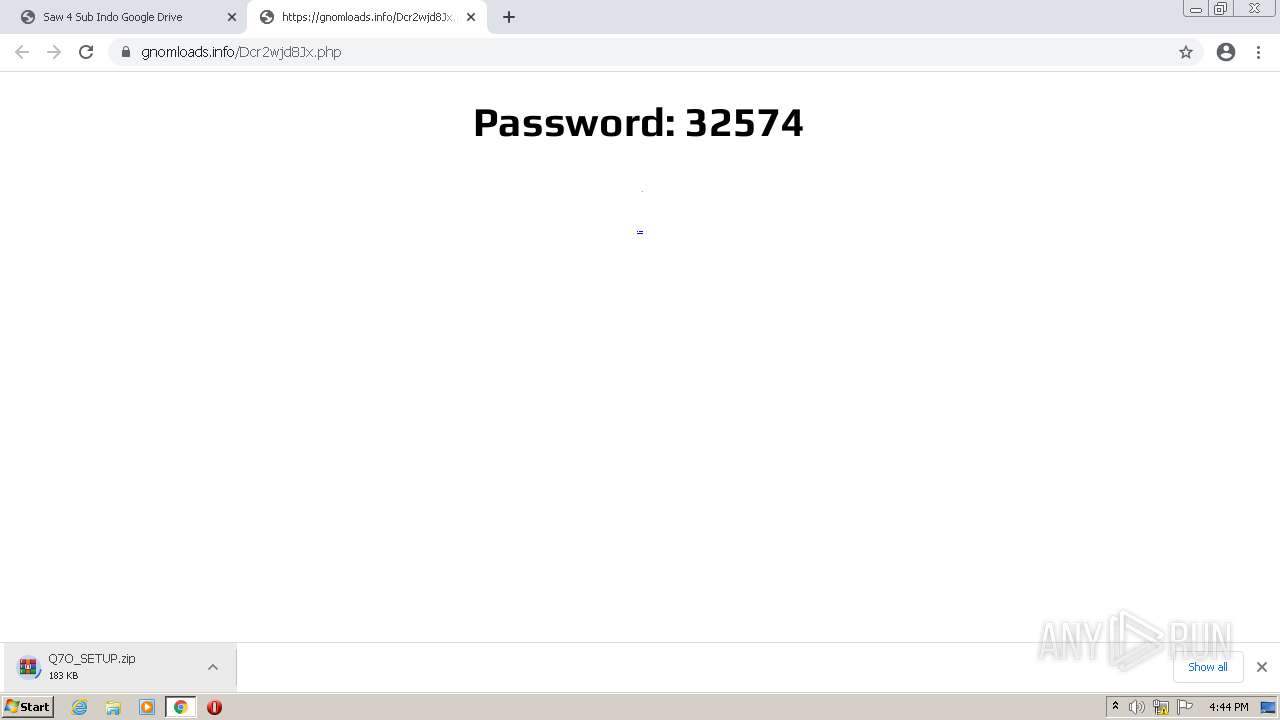
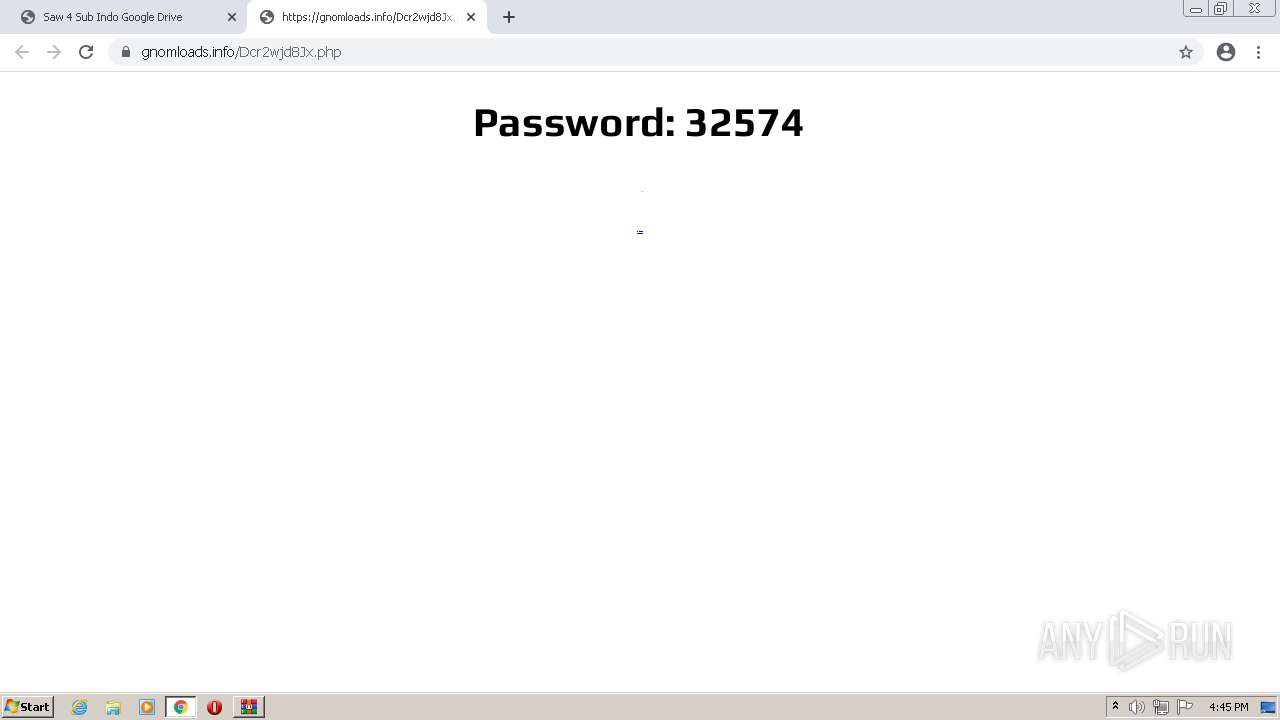
| URL: | https://memz-virus-exe-download65977.peatix.com/ |
| Full analysis: | https://app.any.run/tasks/1772b8fc-22f2-4e91-bc9a-41f9fd42a62f |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2021, 15:43:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E769E7F60958C7837897AAB2FAADB134 |
| SHA1: | 2692B4977B17EDD0EEF3AF4C991506DA677EB69D |
| SHA256: | A6EB0A658E12D76B87618AC501F2F6BB5060CF53F1C6F24AD46D6EEB88D83478 |
| SSDEEP: | 3:N8XMM2L/ctERMdLGTKn:2Xl2bctE8GTKn |
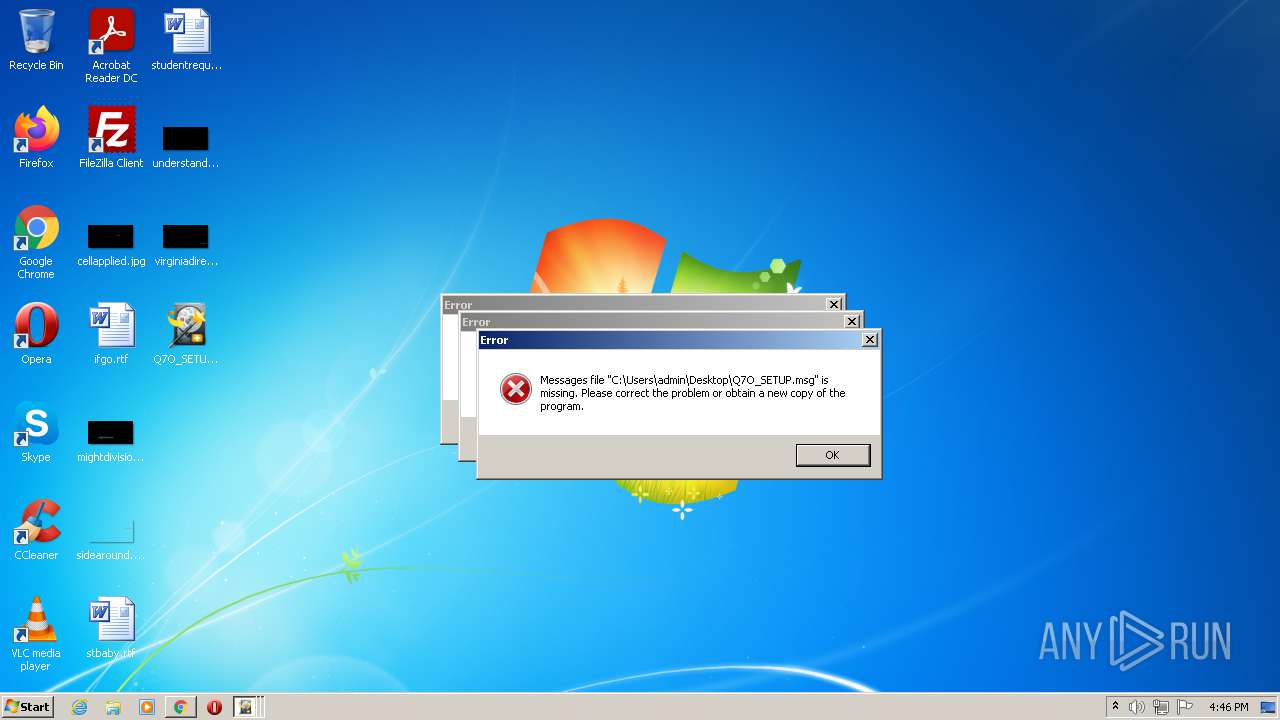
MALICIOUS
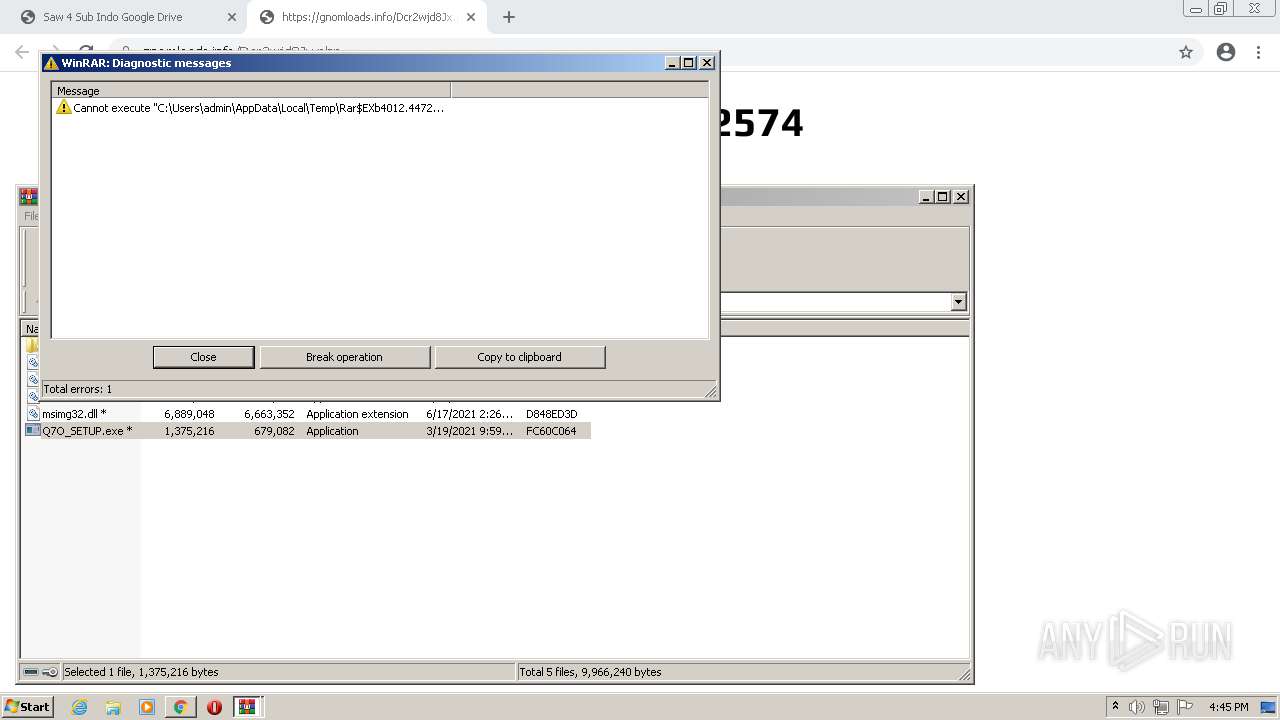
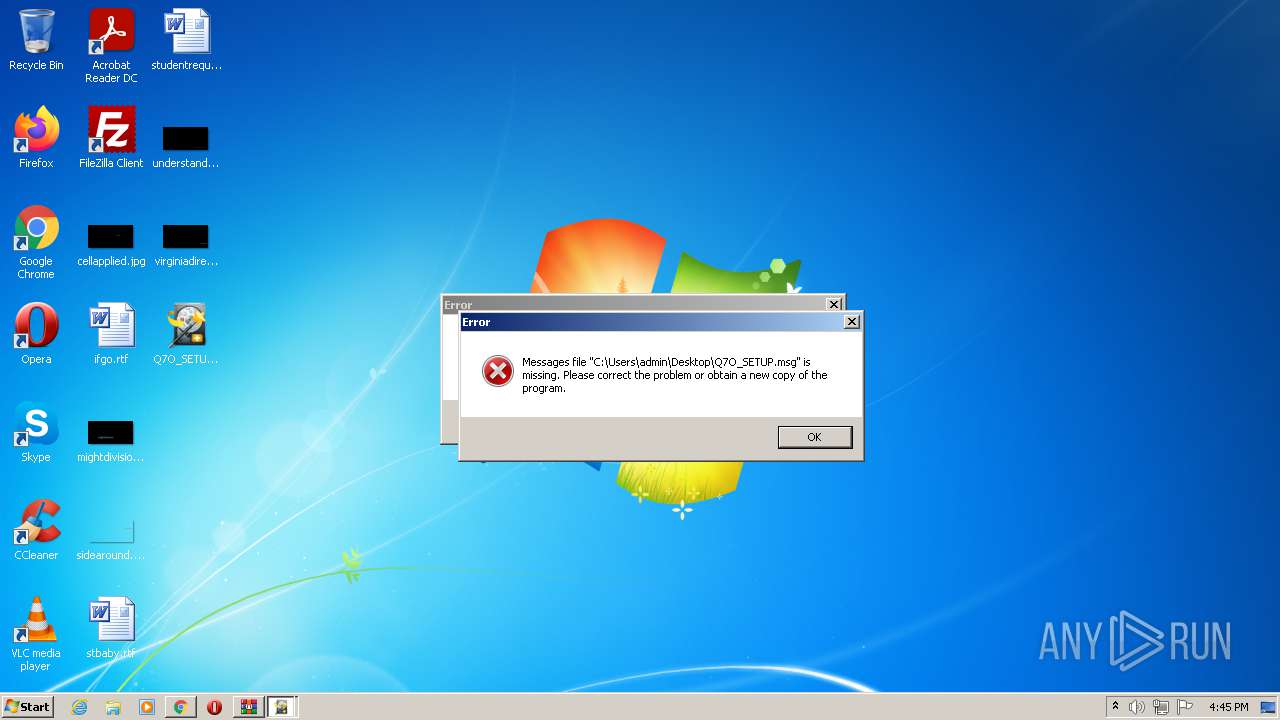
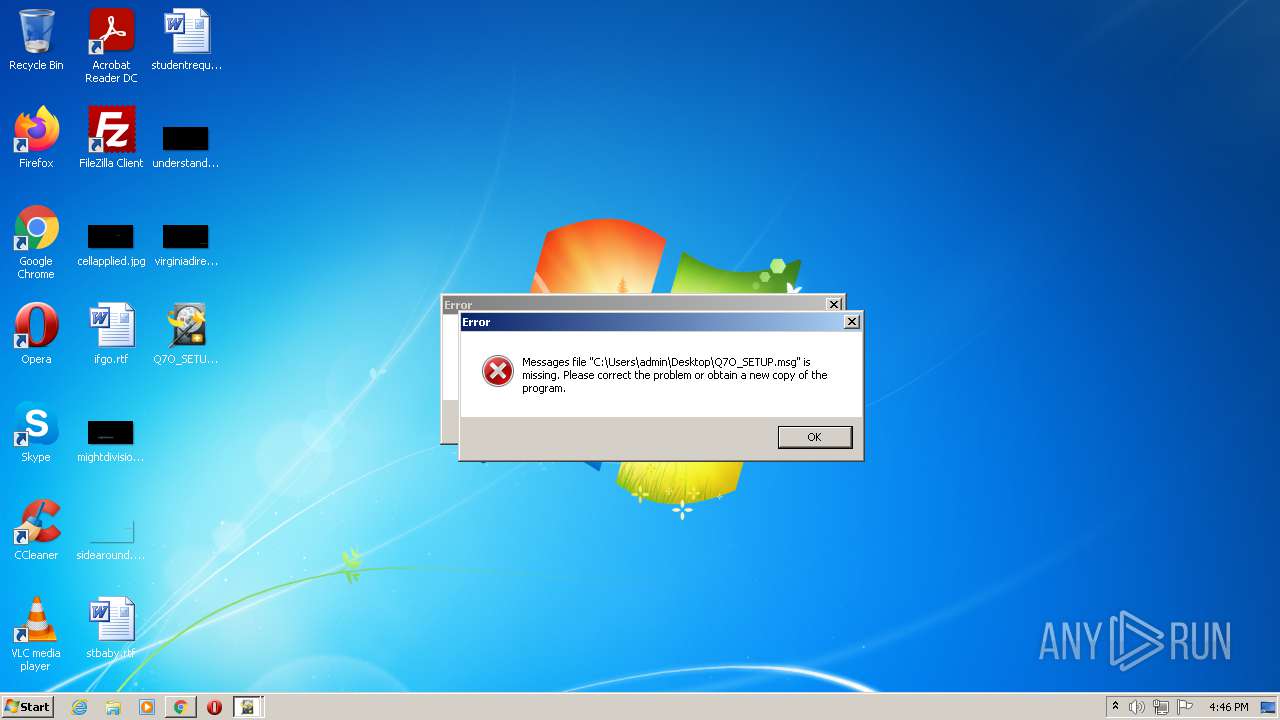
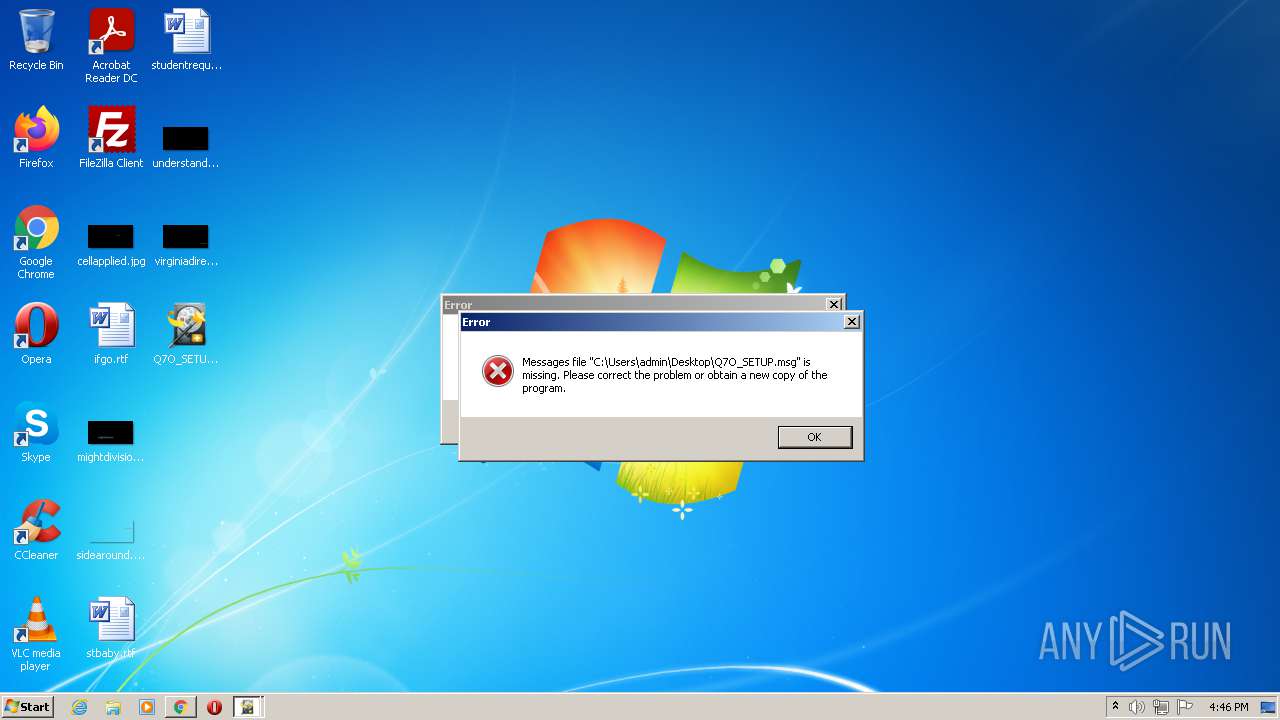
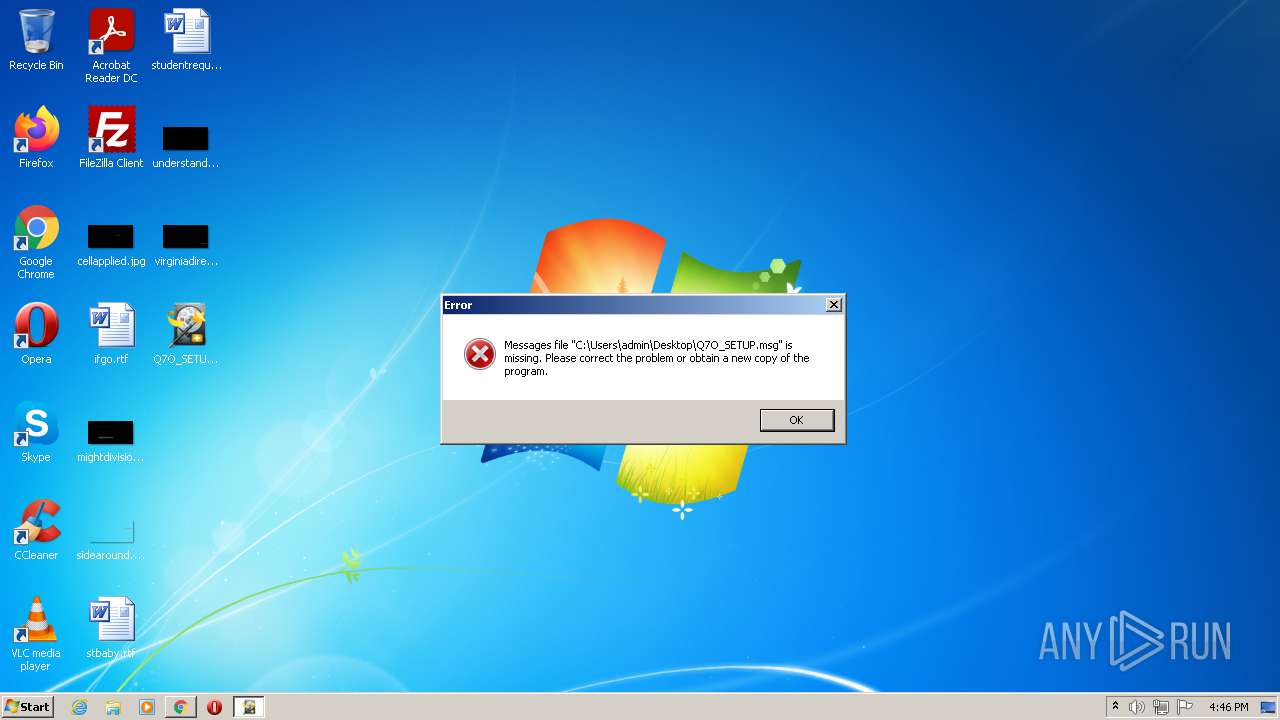
Application was dropped or rewritten from another process
- Q7O_SETUP.exe (PID: 3276)
- Q7O_SETUP.exe (PID: 756)
- Q7O_SETUP.exe (PID: 1560)
- Q7O_SETUP.exe (PID: 2452)
- Q7O_SETUP.exe (PID: 860)
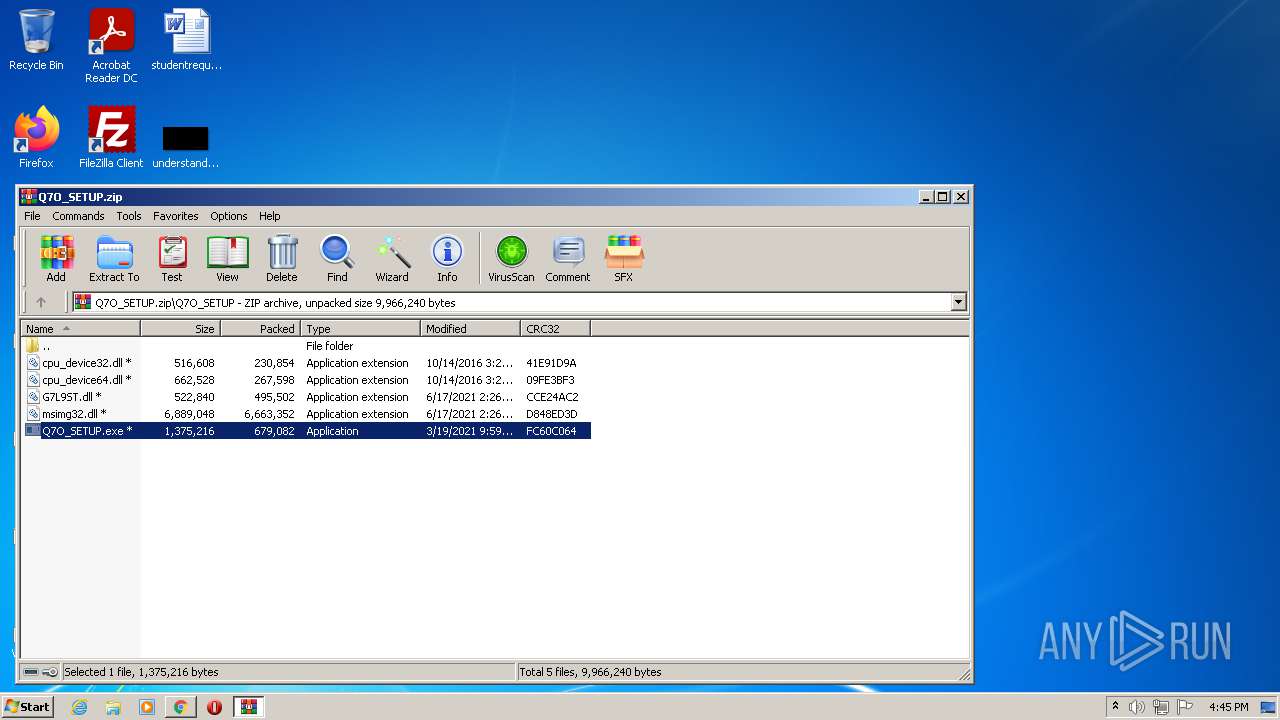
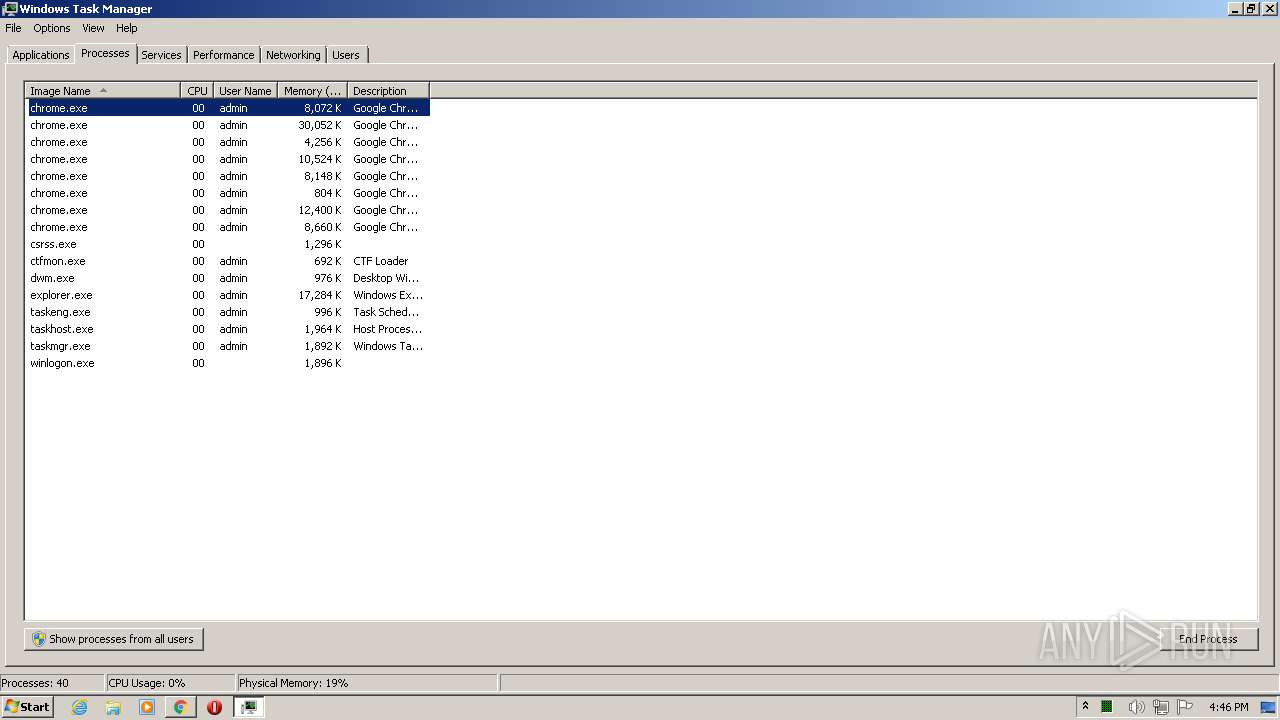
Drops executable file immediately after starts
- chrome.exe (PID: 2428)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 4012)
Checks supported languages
- WinRAR.exe (PID: 4012)
- Q7O_SETUP.exe (PID: 3276)
- Q7O_SETUP.exe (PID: 756)
- Q7O_SETUP.exe (PID: 1560)
- Q7O_SETUP.exe (PID: 2452)
- Q7O_SETUP.exe (PID: 860)
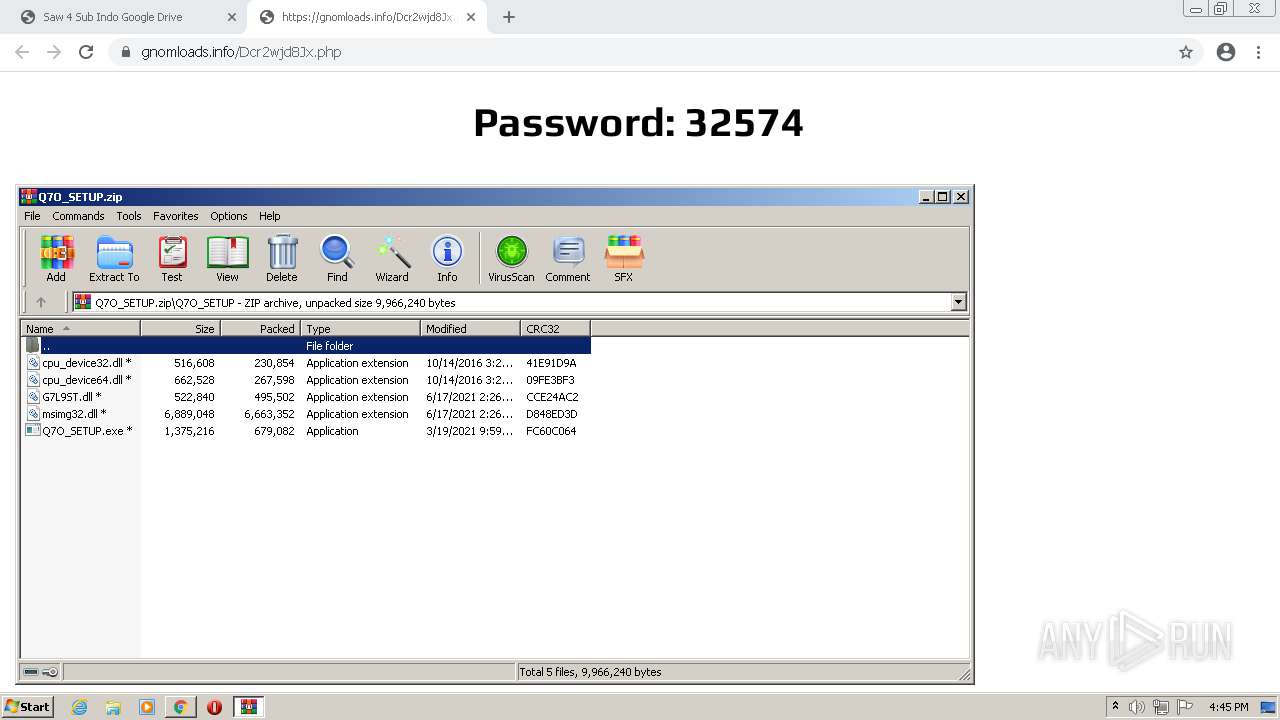
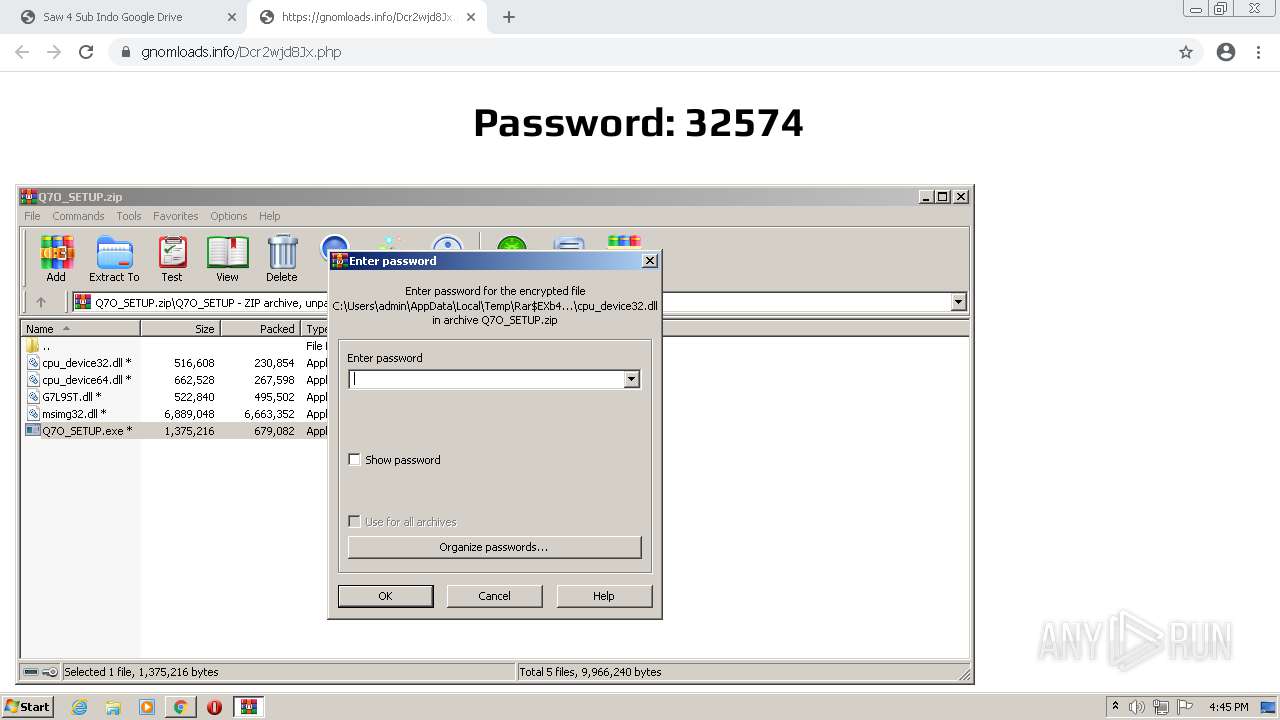
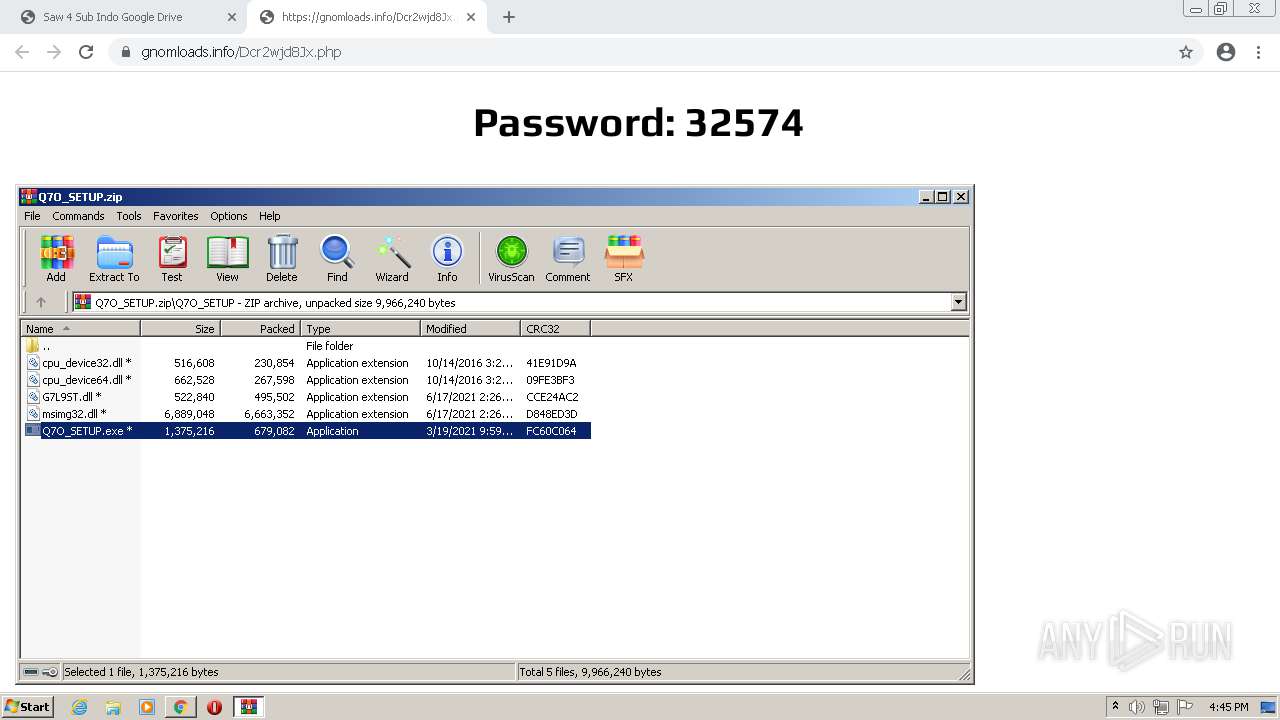
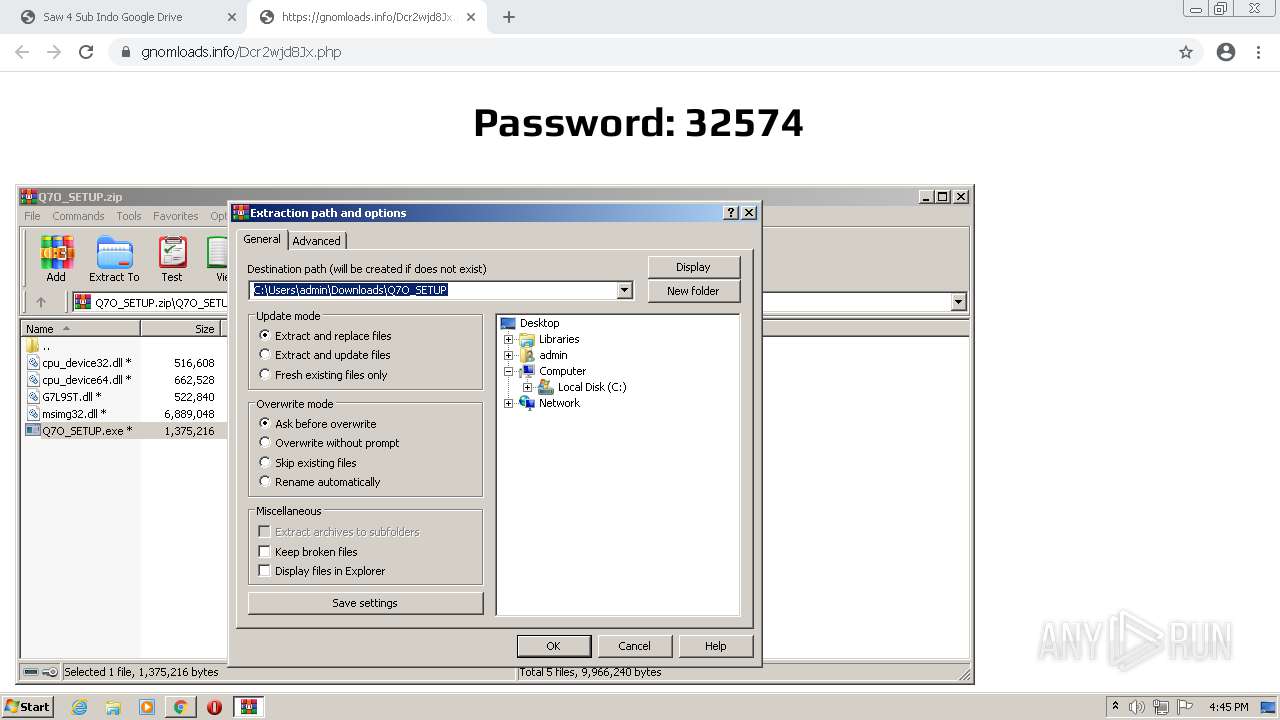
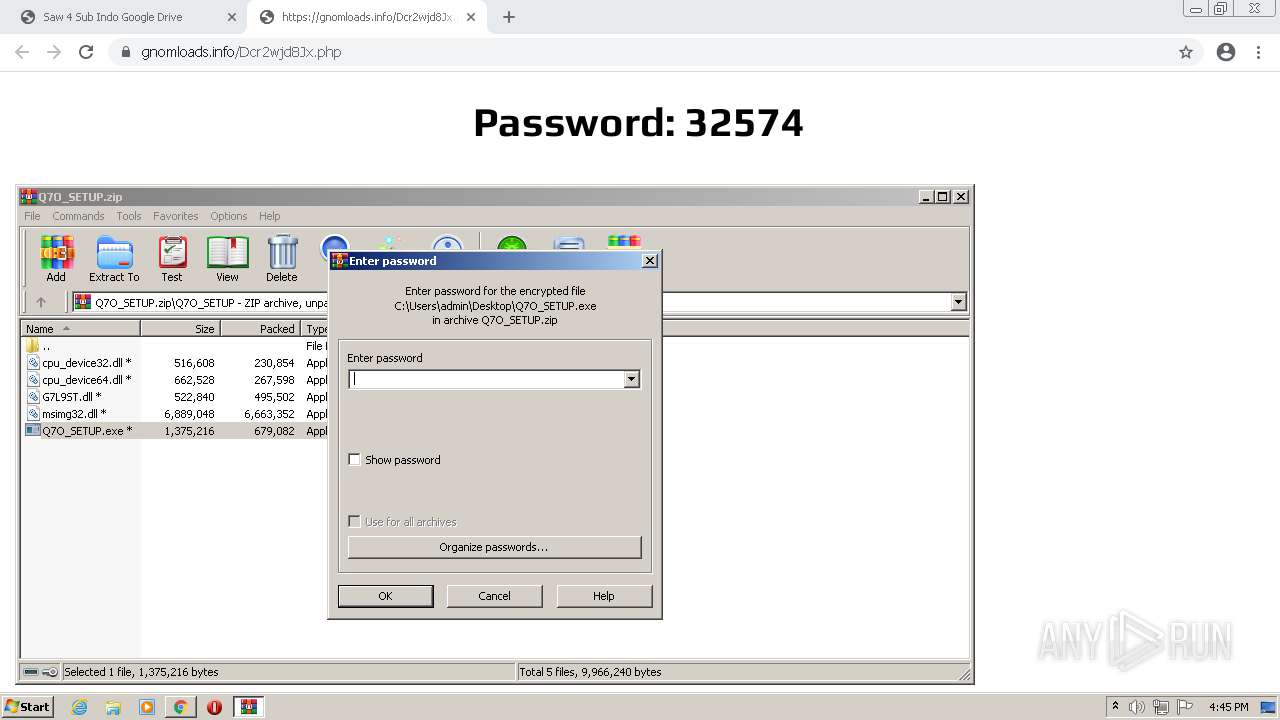
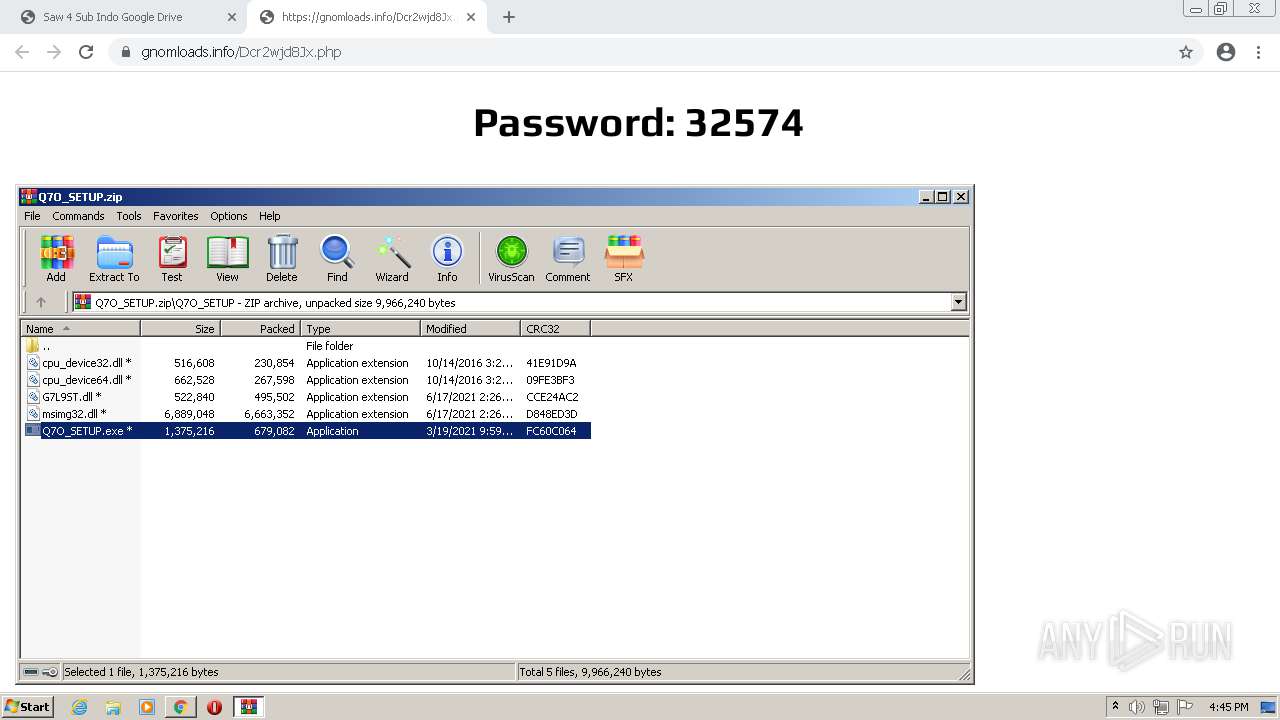
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4012)
- chrome.exe (PID: 2428)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2428)
INFO
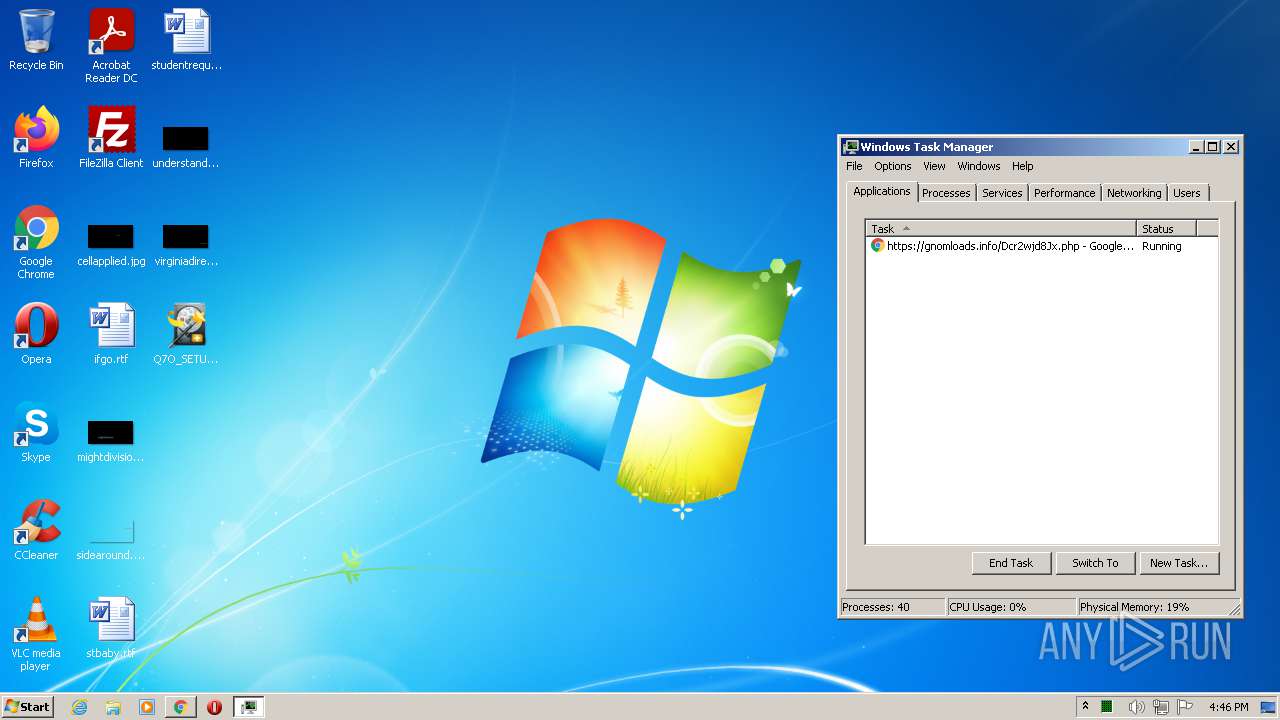
Application launched itself
- chrome.exe (PID: 1108)
Checks supported languages
- chrome.exe (PID: 3100)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 4032)
- chrome.exe (PID: 1108)
- chrome.exe (PID: 4076)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 2220)
- chrome.exe (PID: 892)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 780)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 1660)
- chrome.exe (PID: 3368)
- chrome.exe (PID: 3144)
- chrome.exe (PID: 1500)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 1936)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 2428)
- taskmgr.exe (PID: 1728)
Reads the hosts file
- chrome.exe (PID: 1108)
- chrome.exe (PID: 2944)
Reads the computer name
- chrome.exe (PID: 3044)
- chrome.exe (PID: 1108)
- chrome.exe (PID: 4076)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 3368)
- chrome.exe (PID: 3144)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 1936)
- taskmgr.exe (PID: 1728)
Reads settings of System Certificates
- chrome.exe (PID: 2944)
Reads the date of Windows installation
- chrome.exe (PID: 3280)
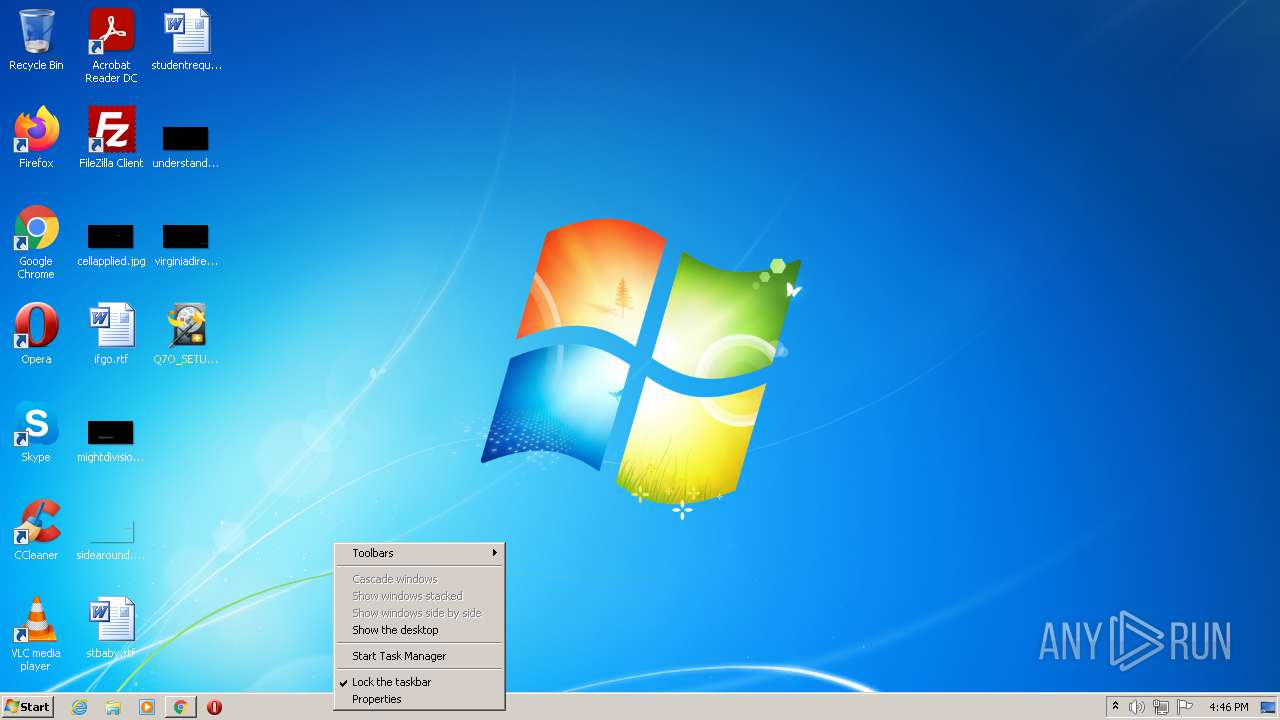
Manual execution by user
- Q7O_SETUP.exe (PID: 3276)
- Q7O_SETUP.exe (PID: 756)
- Q7O_SETUP.exe (PID: 1560)
- Q7O_SETUP.exe (PID: 860)
- taskmgr.exe (PID: 1728)
- Q7O_SETUP.exe (PID: 2452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
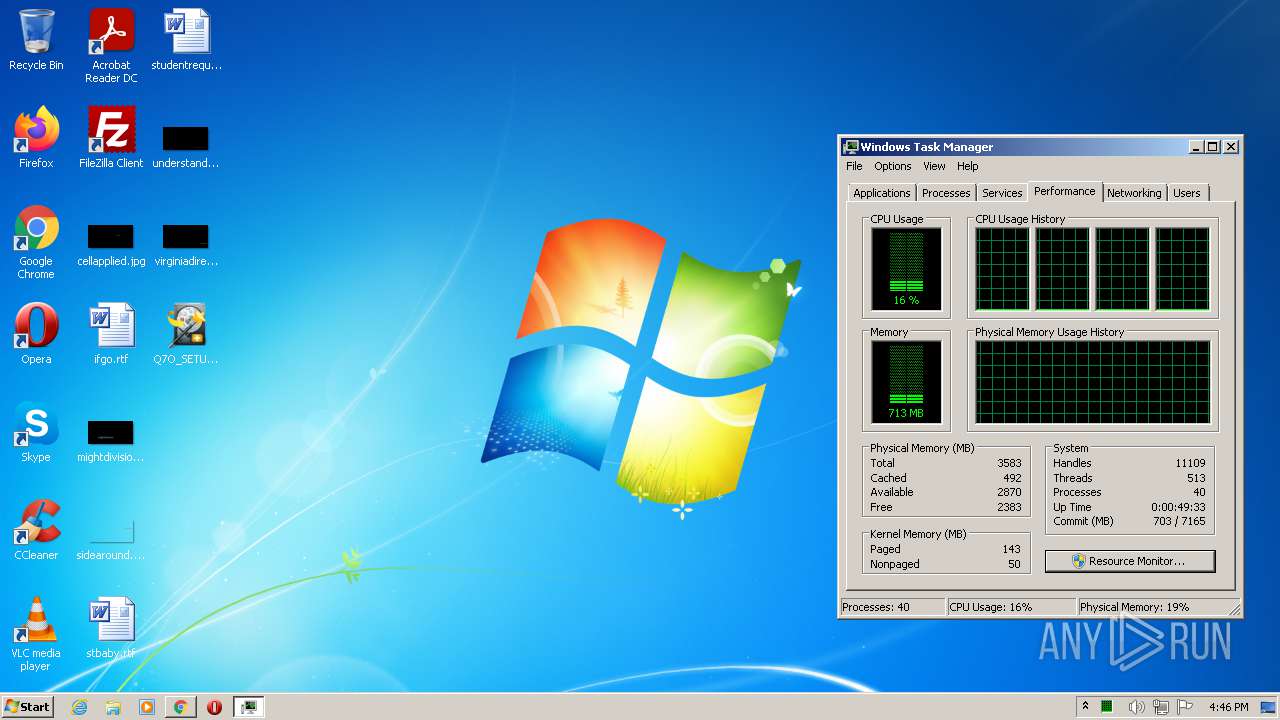
Total processes
65
Monitored processes
29
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
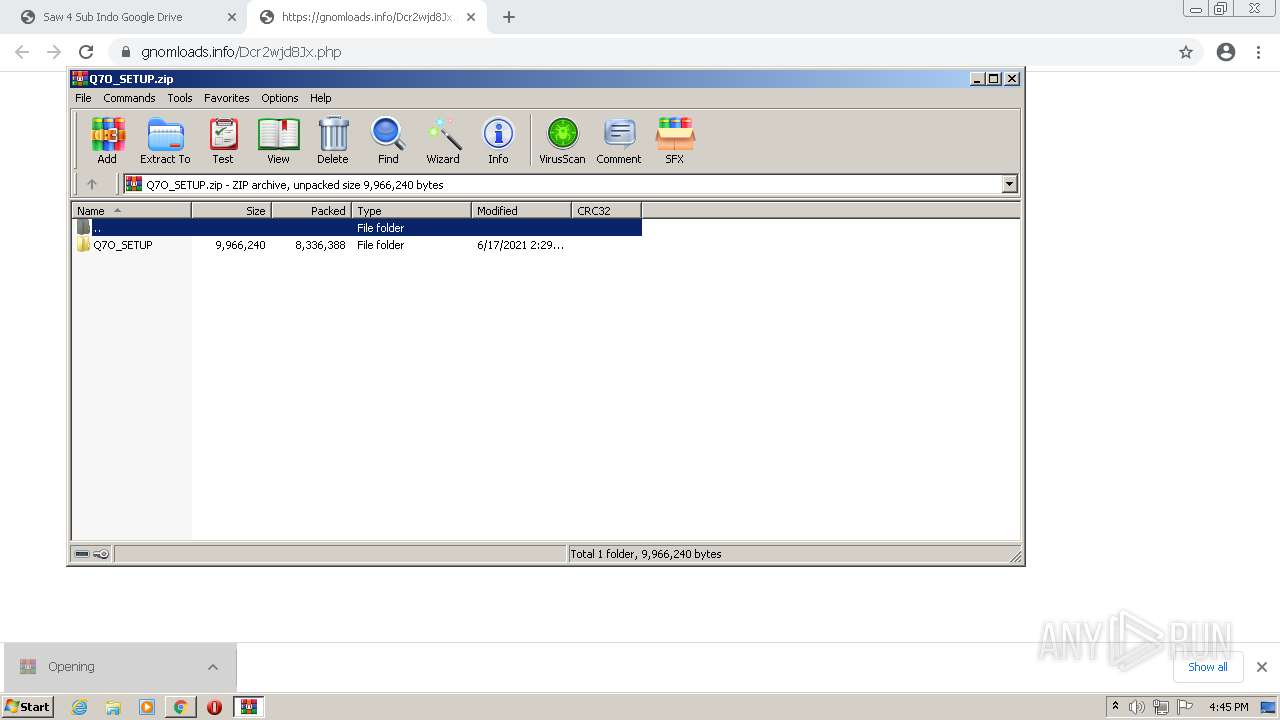
| 756 | "C:\Users\admin\Desktop\Q7O_SETUP.exe" | C:\Users\admin\Desktop\Q7O_SETUP.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 860 | "C:\Users\admin\Desktop\Q7O_SETUP.exe" | C:\Users\admin\Desktop\Q7O_SETUP.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://memz-virus-exe-download65977.peatix.com/" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --field-trial-handle=1040,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2776 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\Desktop\Q7O_SETUP.exe" | C:\Users\admin\Desktop\Q7O_SETUP.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1728 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1040,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=584 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
12 908
Read events
12 768
Write events
135
Delete events
5
Modification events
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
2
Suspicious files
28
Text files
111
Unknown types
2
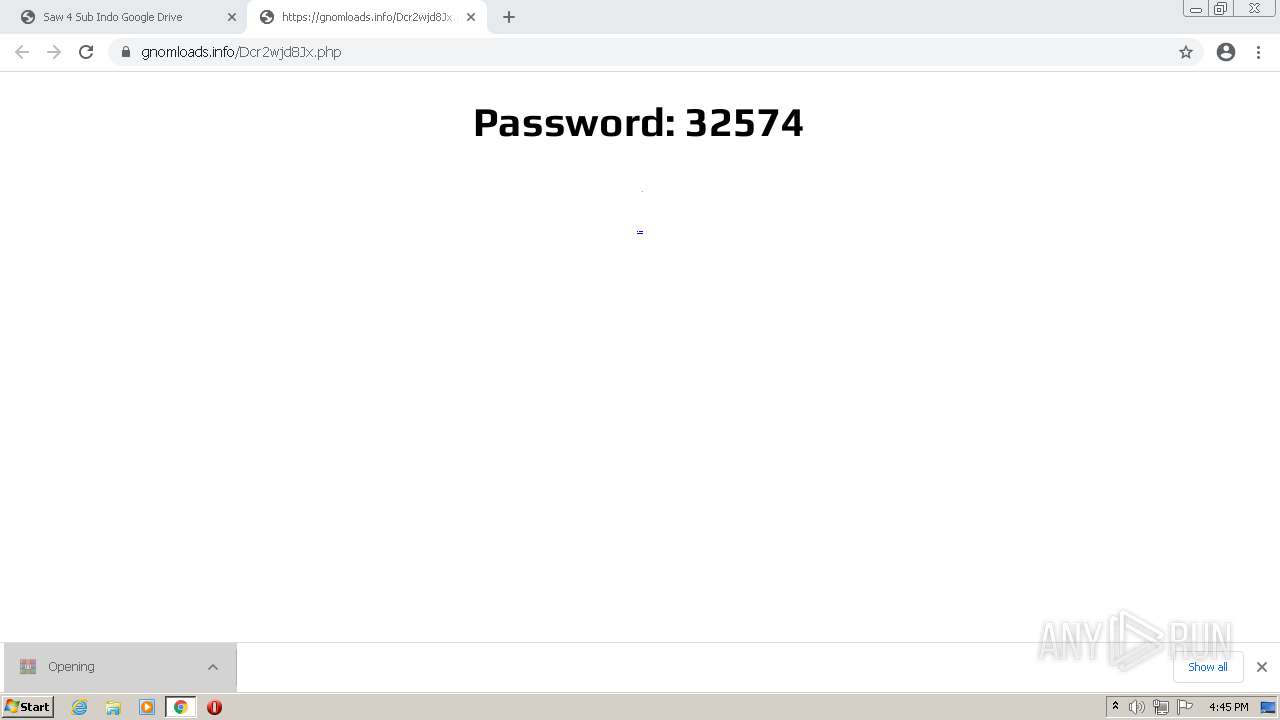
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60CCBF51-454.pma | — | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\64e7a333-9b54-4145-8df7-f93e95c8c180.tmp | text | |
MD5:— | SHA256:— | |||
| 3100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2b3ae5.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4f76d879-022d-4de2-b35c-ffc5067cdb06.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
99
DNS requests
47
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | — | — | whitelisted |
— | — | HEAD | 200 | 173.194.150.183:80 | http://r1---sn-5goeen7d.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=196.244.192.14&mm=28&mn=sn-5goeen7d&ms=nvh&mt=1624030825&mv=m&mvi=1&pl=25&rmhost=r6---sn-5goeen7d.gvt1.com&shardbypass=yes&smhost=r1---sn-5goeen7y.gvt1.com | US | — | — | whitelisted |
2944 | chrome.exe | GET | 301 | 93.184.221.225:80 | http://i.ebayimg.com/00/s/MTA0M1gxNDQ5/z/bD8AAOSwXetZQGmh/$_57.JPG?set_id=8800005007 | US | — | — | whitelisted |
— | — | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | html | 550 b | whitelisted |
— | — | GET | 206 | 173.194.150.183:80 | http://r1---sn-5goeen7d.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=196.244.192.14&mm=28&mn=sn-5goeen7d&ms=nvh&mt=1624030825&mv=m&mvi=1&pl=25&rmhost=r6---sn-5goeen7d.gvt1.com&shardbypass=yes&smhost=r1---sn-5goeen7y.gvt1.com | US | binary | 9.66 Kb | whitelisted |
— | — | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | html | 550 b | whitelisted |
— | — | GET | 206 | 173.194.150.183:80 | http://r1---sn-5goeen7d.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=196.244.192.14&mm=28&mn=sn-5goeen7d&ms=nvh&mt=1624030825&mv=m&mvi=1&pl=25&rmhost=r6---sn-5goeen7d.gvt1.com&shardbypass=yes&smhost=r1---sn-5goeen7y.gvt1.com | US | binary | 5.76 Kb | whitelisted |
— | — | GET | 206 | 173.194.150.183:80 | http://r1---sn-5goeen7d.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=196.244.192.14&mm=28&mn=sn-5goeen7d&ms=nvh&mt=1624030825&mv=m&mvi=1&pl=25&rmhost=r6---sn-5goeen7d.gvt1.com&shardbypass=yes&smhost=r1---sn-5goeen7y.gvt1.com | US | binary | 9.72 Kb | whitelisted |
— | — | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | html | 550 b | whitelisted |
— | — | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | html | 550 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2944 | chrome.exe | 142.250.181.226:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
2944 | chrome.exe | 23.21.75.226:443 | i.kissmetrics.com | Amazon.com, Inc. | US | unknown |
2944 | chrome.exe | 13.35.173.235:443 | scripts.kissmetrics.com | — | US | unknown |
2944 | chrome.exe | 153.120.118.122:443 | uabizprd.ukw.jp | SAKURA Internet Inc. | JP | unknown |
2944 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
2944 | chrome.exe | 54.64.125.130:443 | memz-virus-exe-download65977.peatix.com | Amazon.com, Inc. | JP | unknown |
2944 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2944 | chrome.exe | 104.18.6.120:443 | cookie-cdn.cookiepro.com | Cloudflare Inc | US | suspicious |
2944 | chrome.exe | 142.250.186.74:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
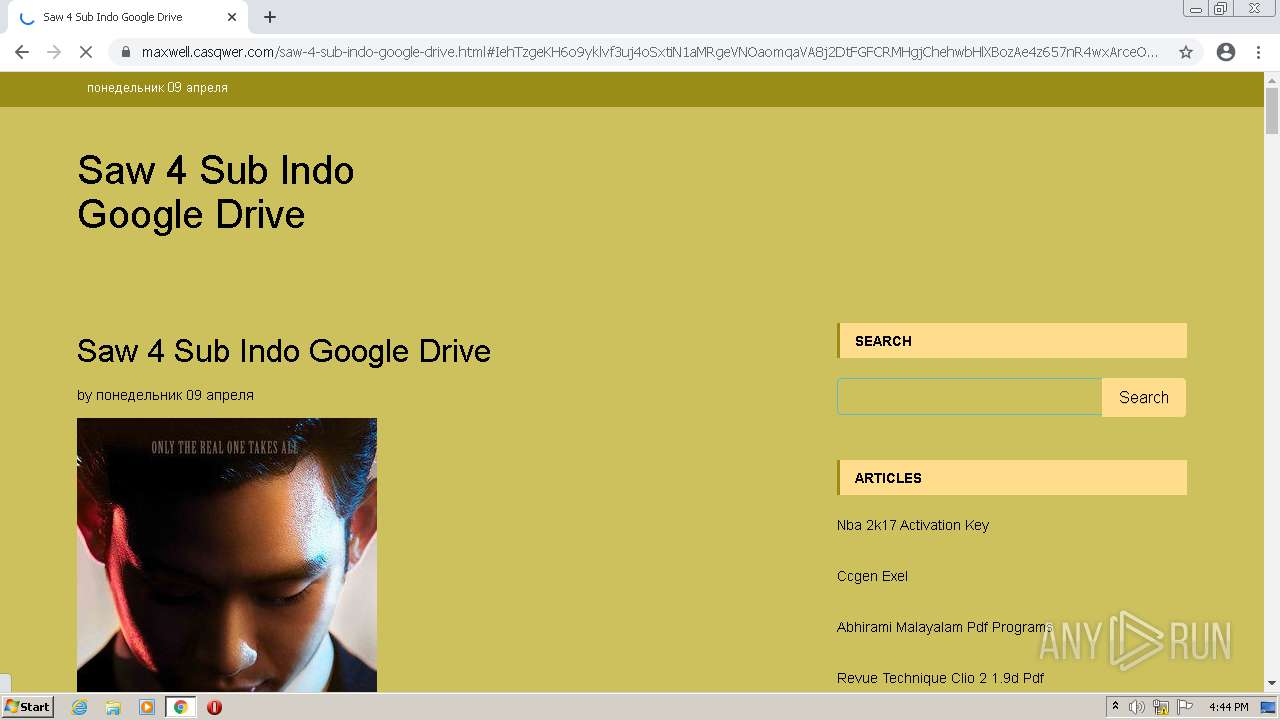
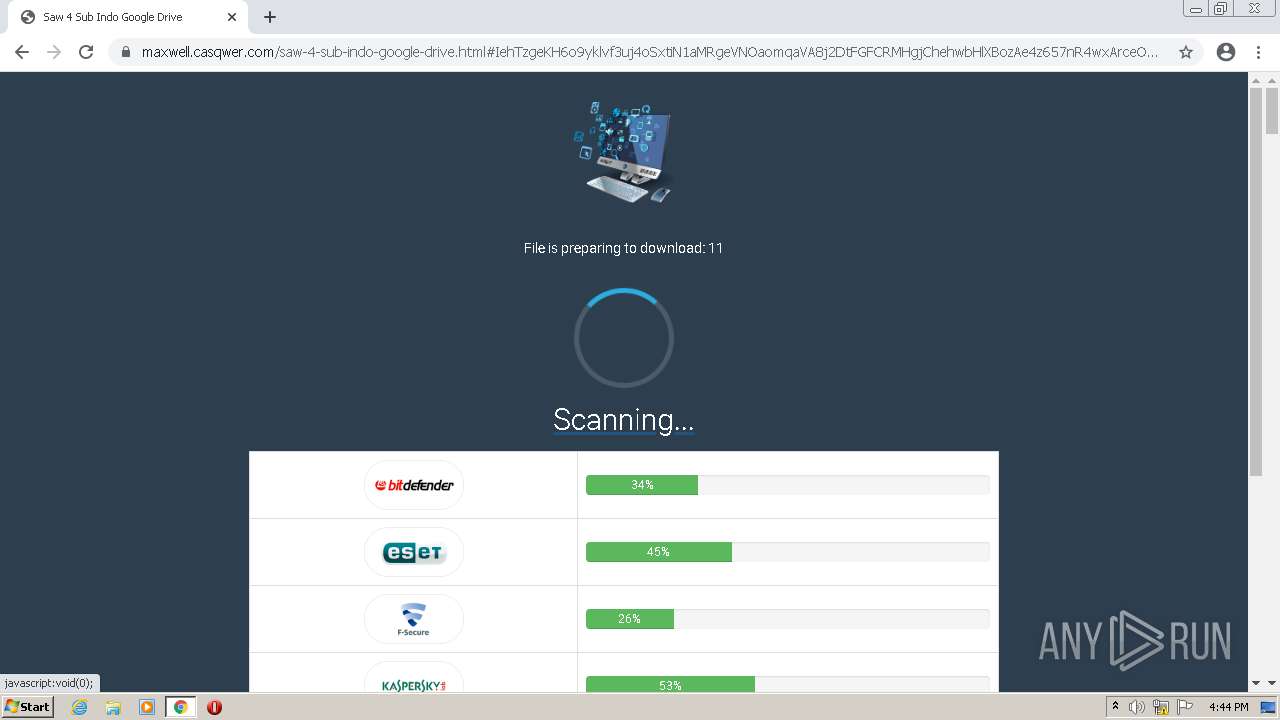
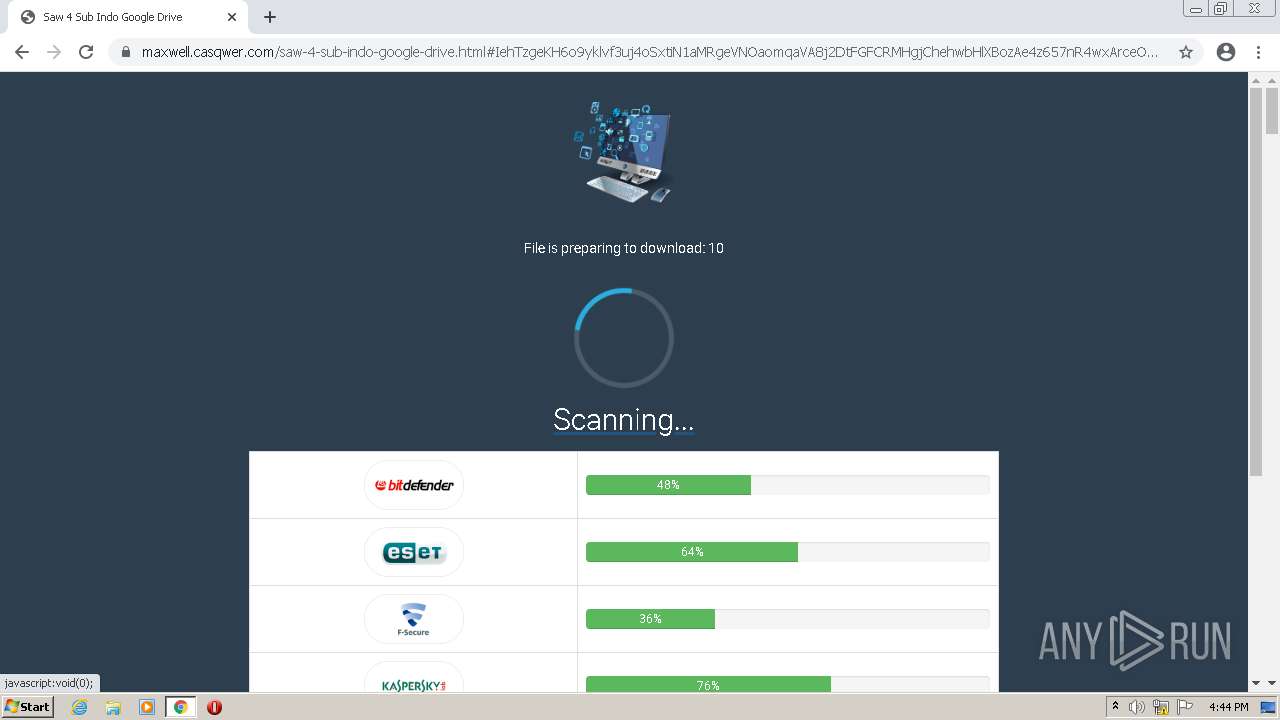
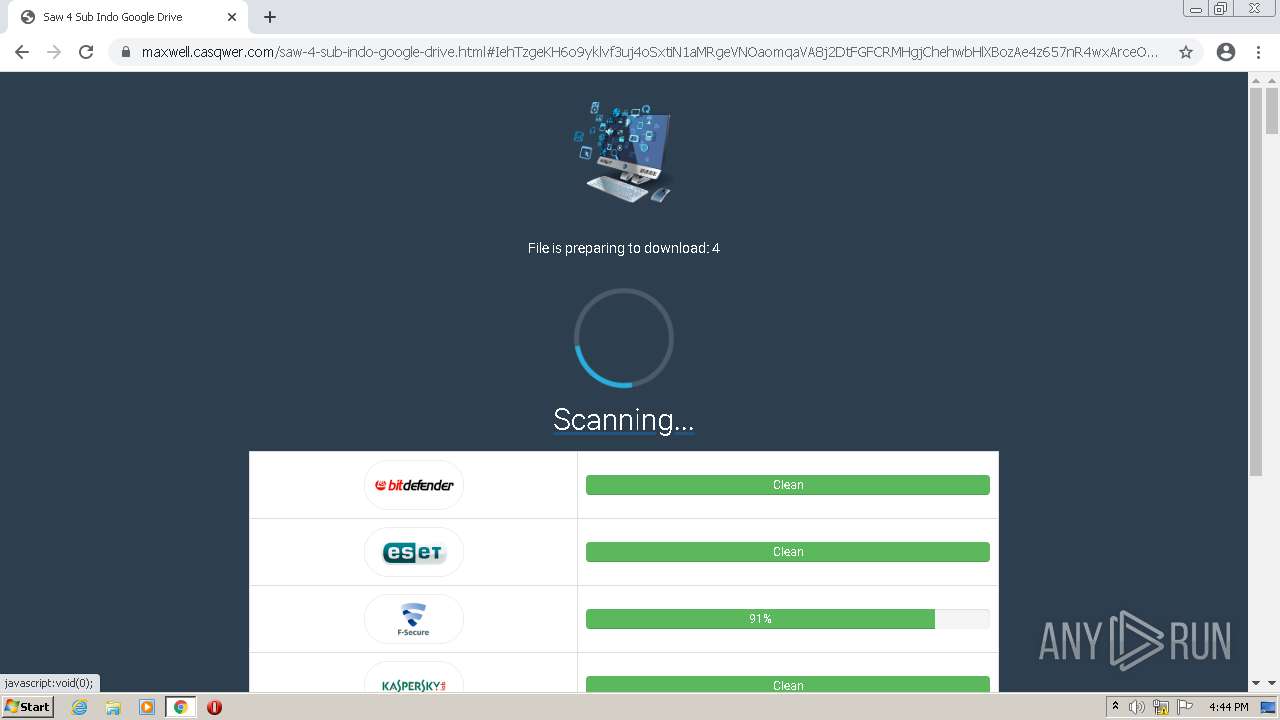
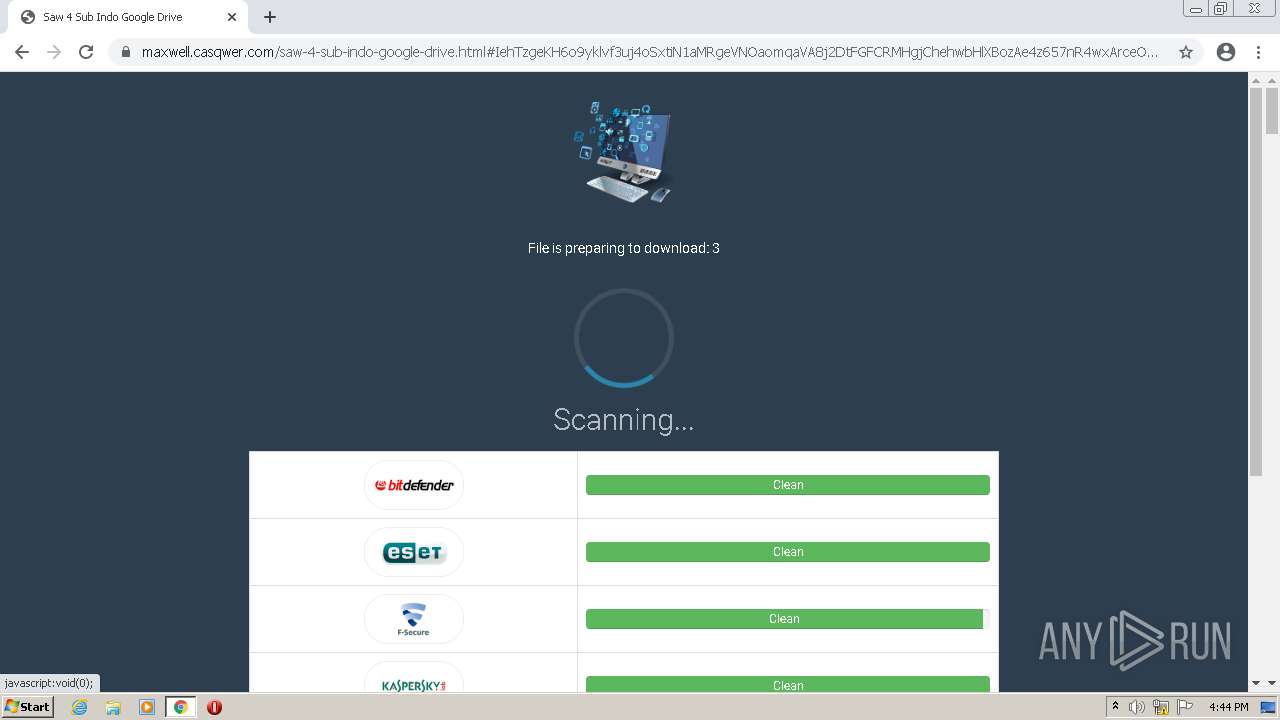
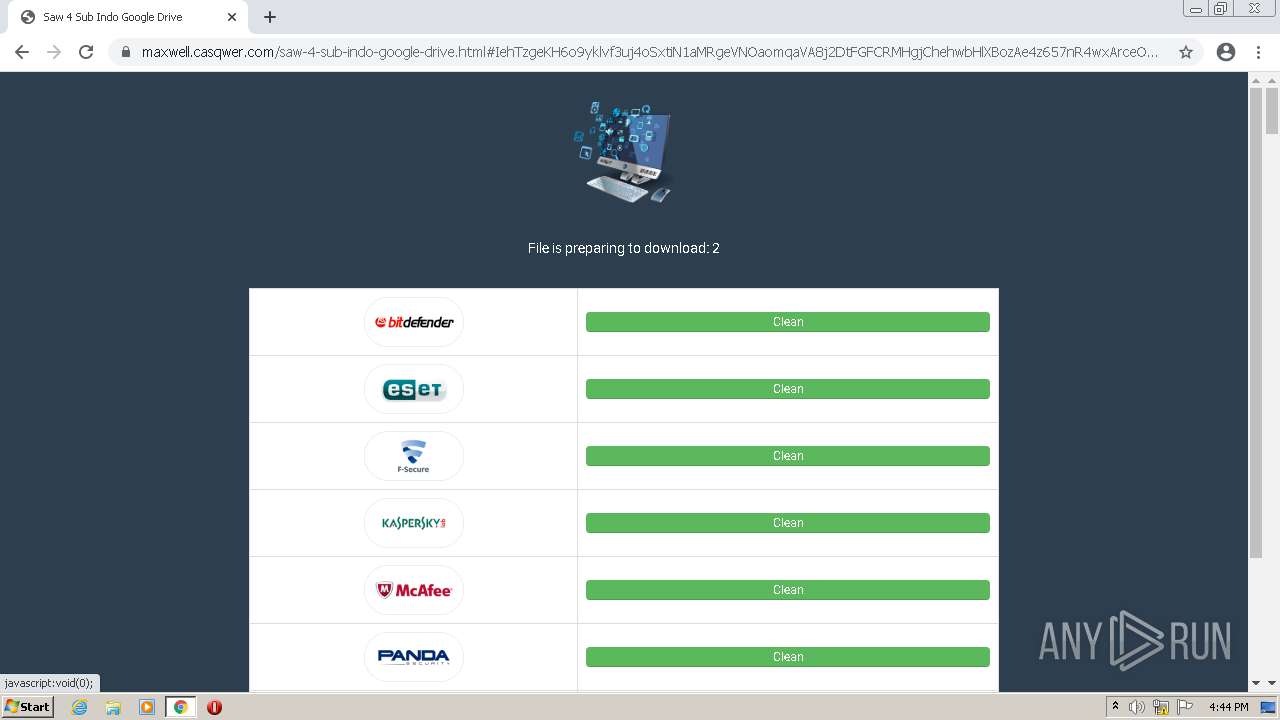
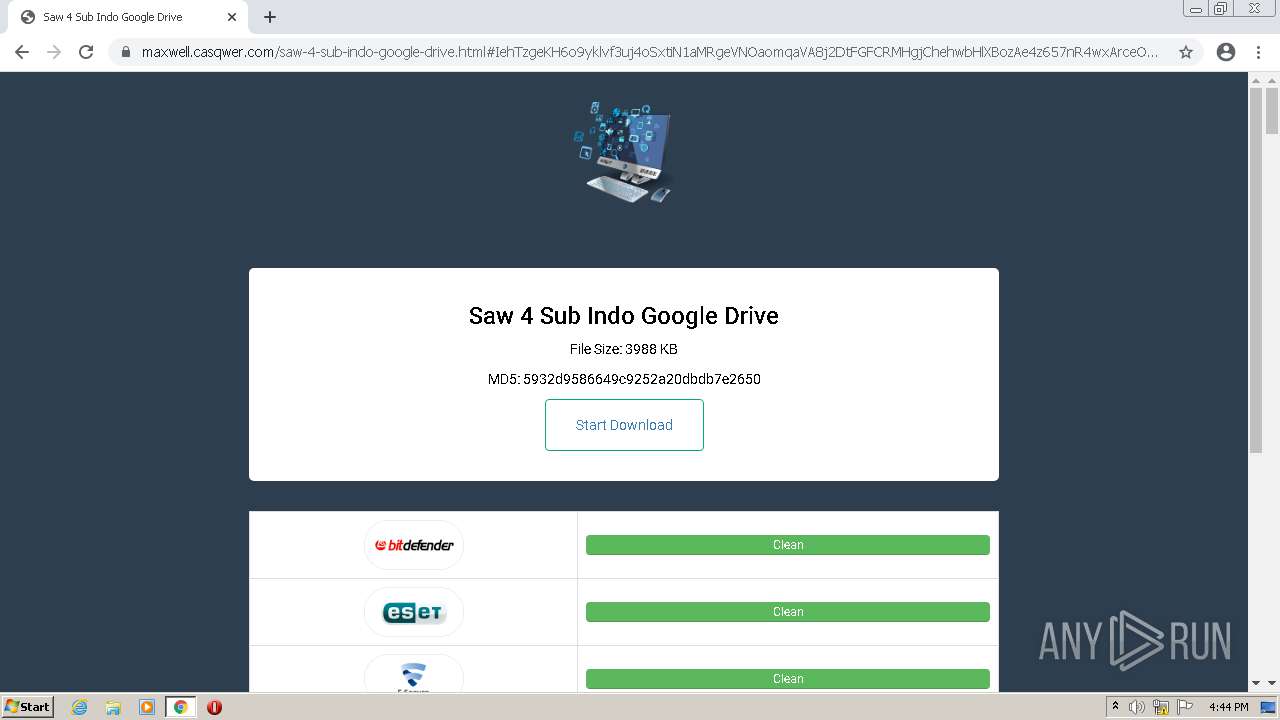
2944 | chrome.exe | 104.21.28.117:443 | maxwell.casqwer.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
memz-virus-exe-download65977.peatix.com |
| unknown |
clients2.google.com |
| whitelisted |
cookie-cdn.cookiepro.com |
| whitelisted |
peatix.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
maxwell.casqwer.com |
| malicious |
i.ytimg.com |
| whitelisted |
geolocation.onetrust.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2944 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2944 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2944 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2944 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2944 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2944 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2944 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2944 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2944 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2944 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |