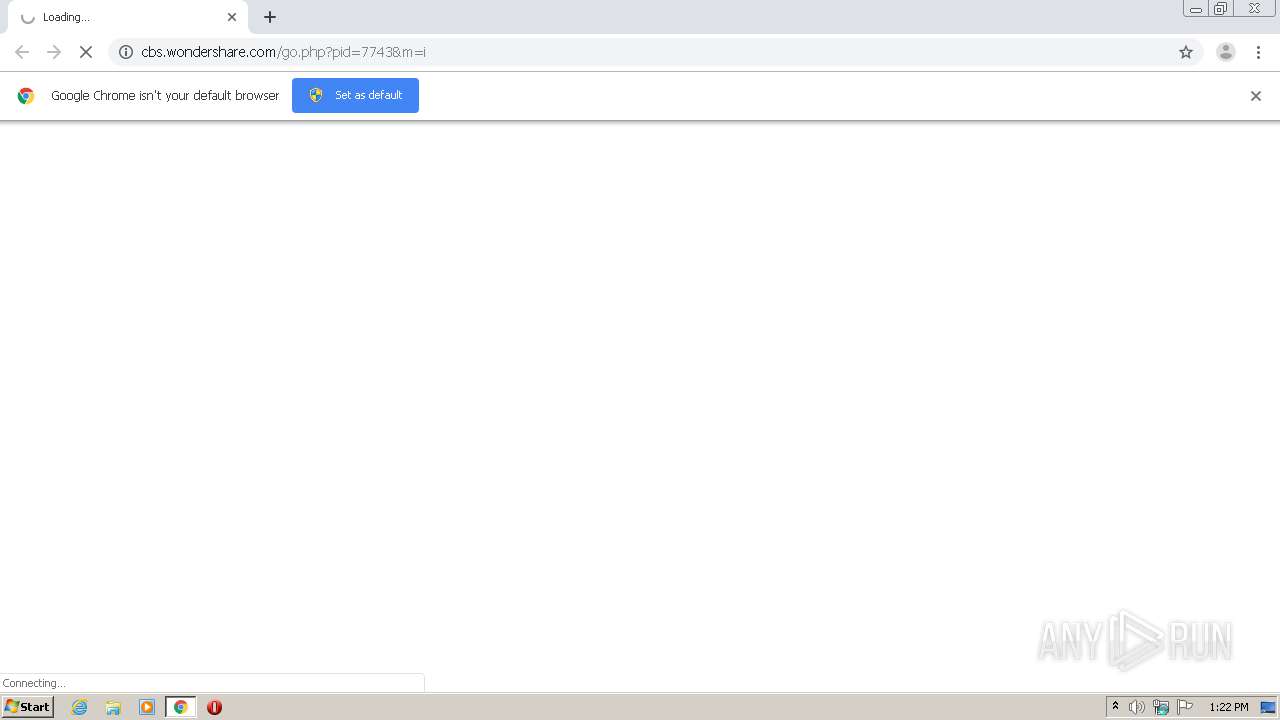
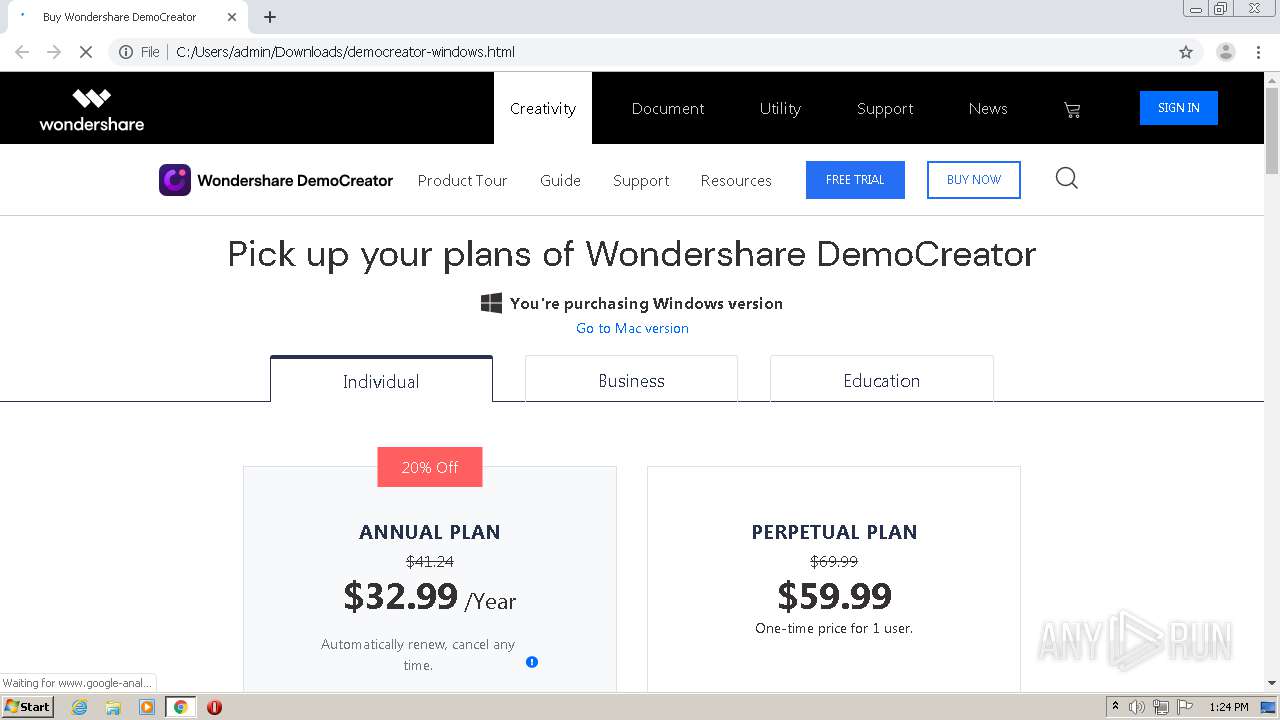
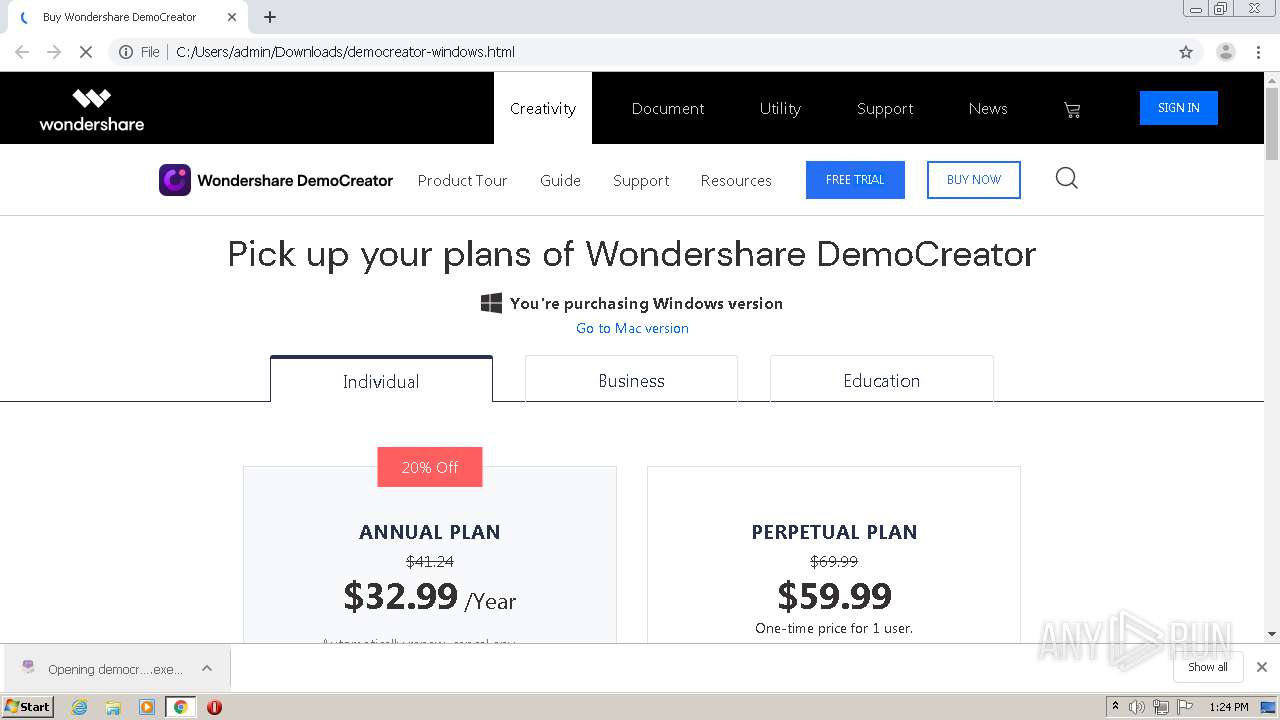
| URL: | http://cbs.wondershare.com/go.php?pid=7743&m=i |
| Full analysis: | https://app.any.run/tasks/3088ed54-20ce-4c33-9333-168d4abec632 |
| Verdict: | Malicious activity |
| Analysis date: | March 09, 2021, 13:21:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 699CE2616076B183936977F0A6C6E528 |
| SHA1: | 782BC3C9110749BF4CD3EBF661C199E75688A017 |
| SHA256: | A6E705DDC0FB34F8A610275BFBB6432DEA246ECEC119FA4EE7E49950F64B2524 |
| SSDEEP: | 3:N1KdHMUPQLGKyKLV62YhvYM:CqIQLGVQgD |
MALICIOUS
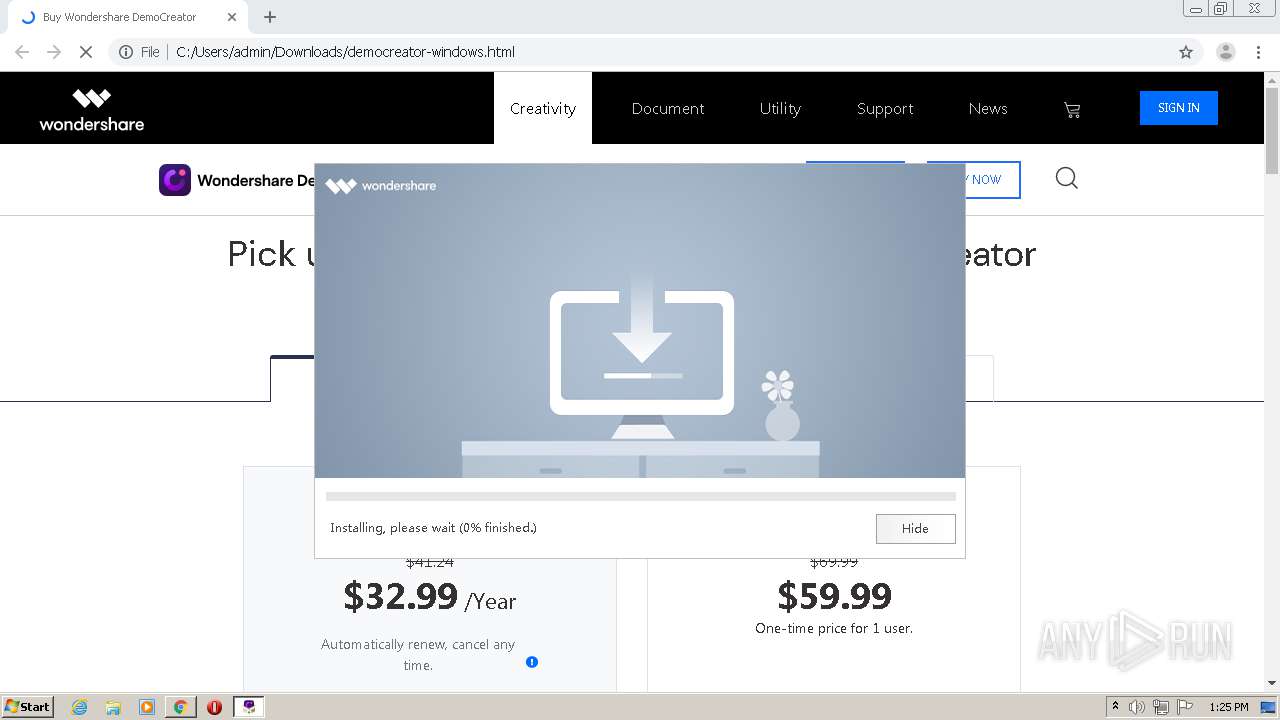
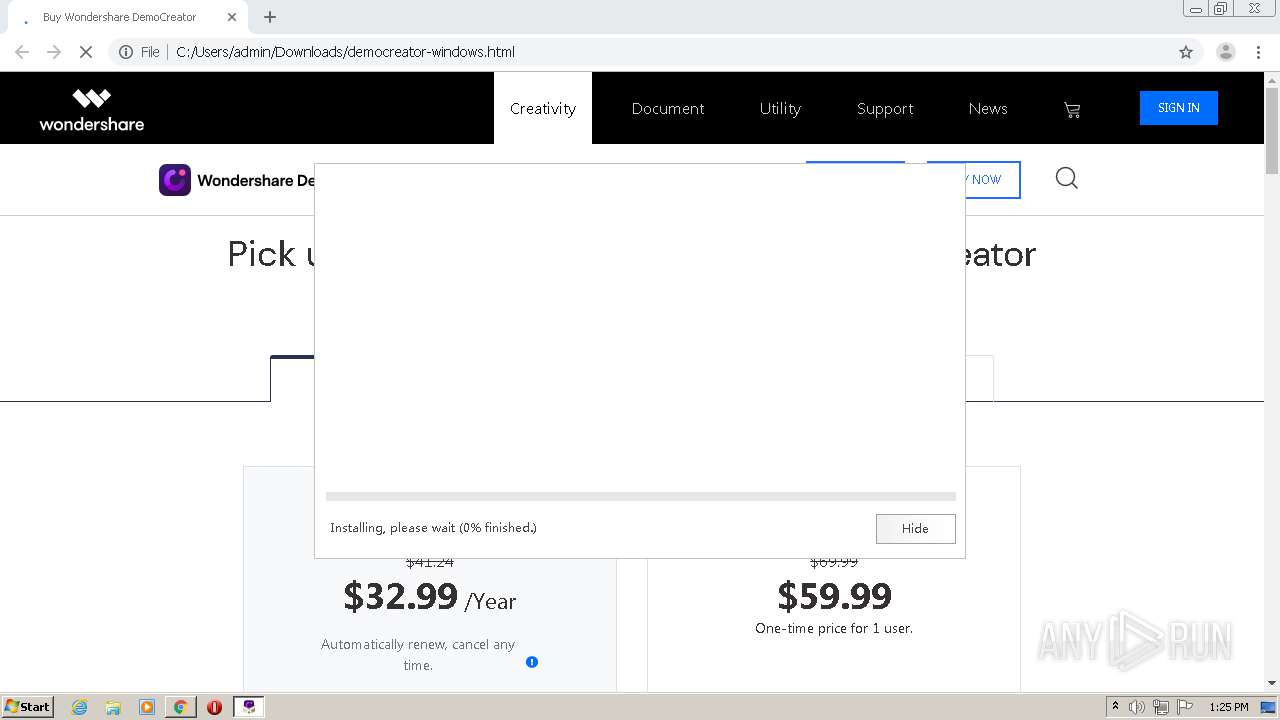
Application was dropped or rewritten from another process
- democreator_setup_full7743.exe (PID: 2540)
- democreator_setup_full7743.exe (PID: 4020)
- NFWCHK.exe (PID: 2664)
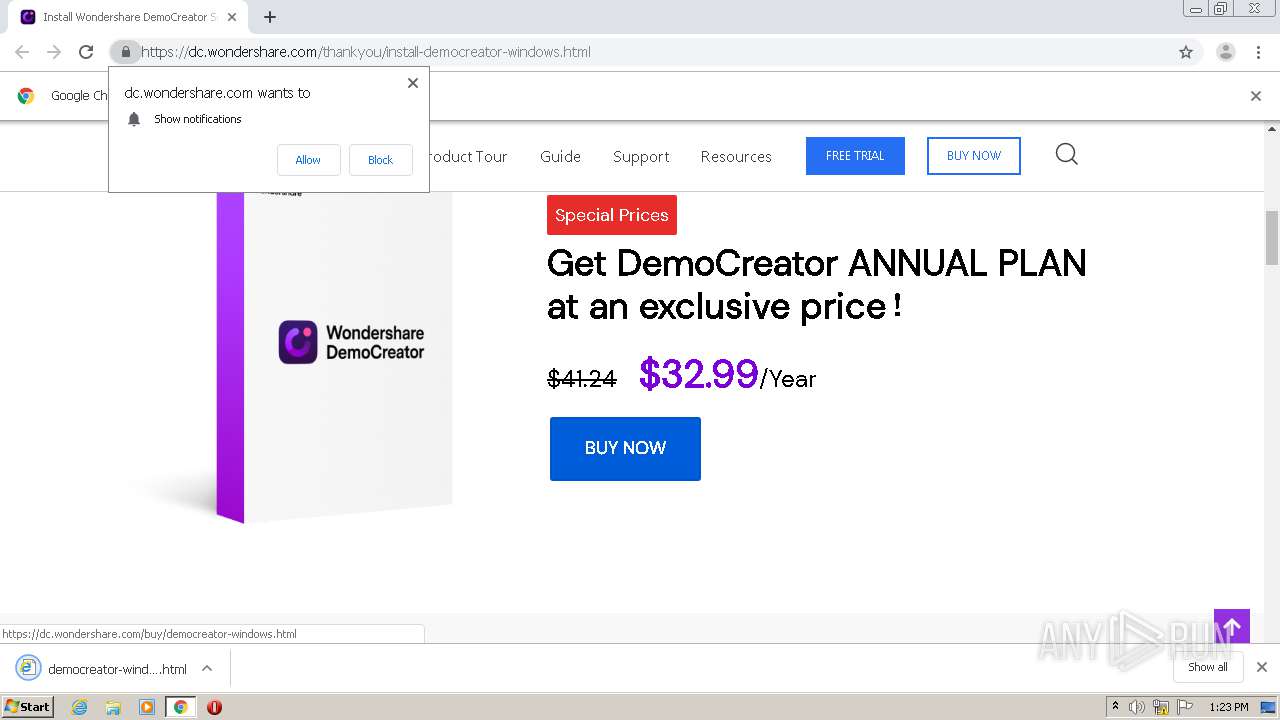
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 920)
- democreator_setup_full7743.exe (PID: 2540)
Low-level read access rights to disk partition
- democreator_setup_full7743.exe (PID: 2540)
Drops a file that was compiled in debug mode
- democreator_setup_full7743.exe (PID: 2540)
- chrome.exe (PID: 920)
Reads internet explorer settings
- democreator_setup_full7743.exe (PID: 2540)
INFO
Reads the hosts file
- chrome.exe (PID: 920)
- chrome.exe (PID: 2820)
Application launched itself
- chrome.exe (PID: 920)
Reads settings of System Certificates
- chrome.exe (PID: 920)
Creates files in the user directory
- chrome.exe (PID: 920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
19
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://cbs.wondershare.com/go.php?pid=7743&m=i" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,3837990918009412064,1231807031555614926,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3272812921414084684 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2732 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,3837990918009412064,1231807031555614926,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6467410497494296128 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,3837990918009412064,1231807031555614926,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15661544992164118159 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2752 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,3837990918009412064,1231807031555614926,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13048064318497730604 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,3837990918009412064,1231807031555614926,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4389509756256590484 --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,3837990918009412064,1231807031555614926,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4145674574620152094 --mojo-platform-channel-handle=2936 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
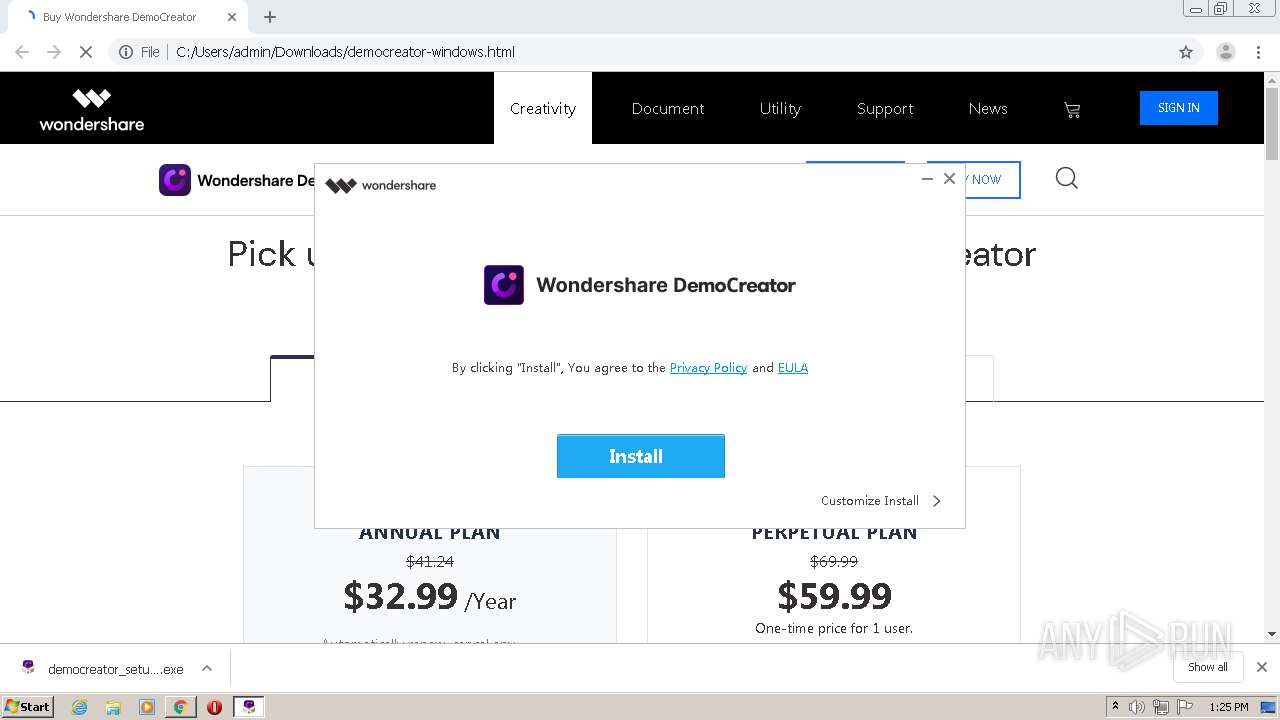
| 2540 | "C:\Users\admin\Downloads\democreator_setup_full7743.exe" | C:\Users\admin\Downloads\democreator_setup_full7743.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: wondershare-democreator_setup_full7743.exe Exit code: 0 Version: 2.1.7.4 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,3837990918009412064,1231807031555614926,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13179135758687811314 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2884 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2664 | C:\Users\Public\Documents\Wondershare\NFWCHK.exe | C:\Users\Public\Documents\Wondershare\NFWCHK.exe | — | democreator_setup_full7743.exe | |||||||||||
User: admin Company: Wondershare Integrity Level: HIGH Description: .NET Framework Checker Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 109
Read events
1 015
Write events
91
Delete events
3
Modification events
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 920-13259769716829875 |
Value: 259 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
4
Suspicious files
81
Text files
563
Unknown types
0
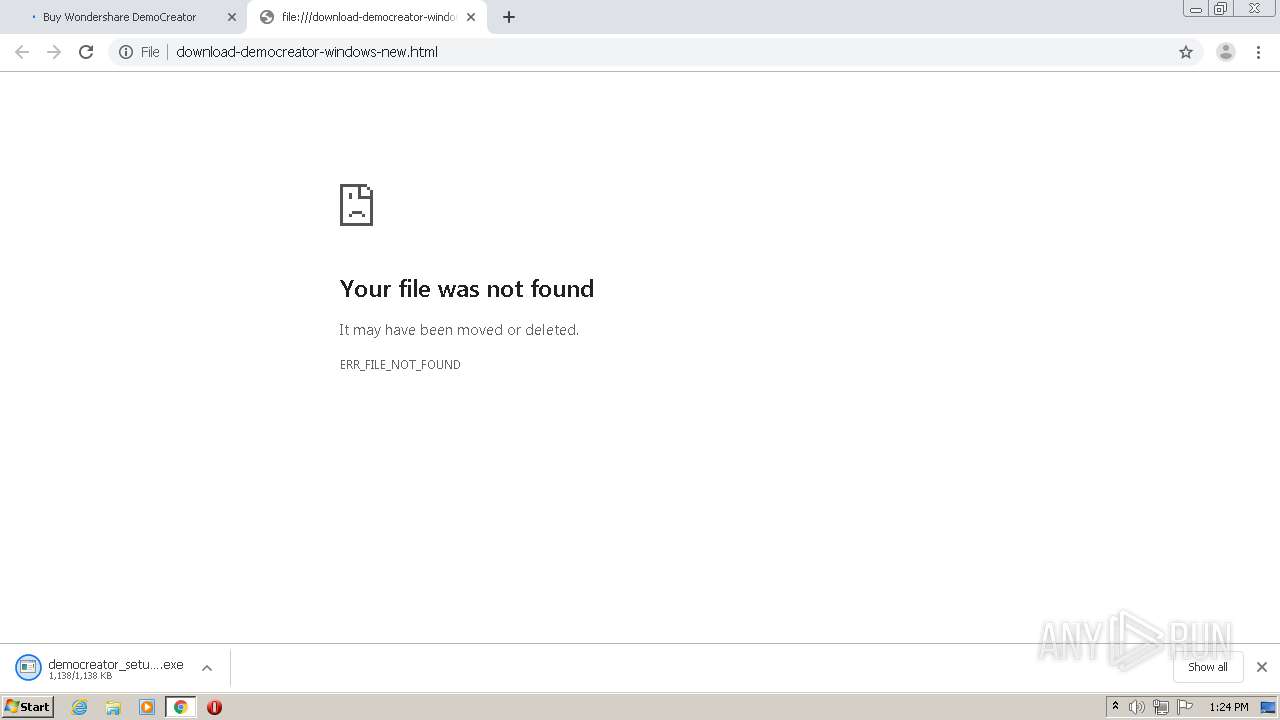
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60477675-398.pma | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dd3c77c0-a29a-4310-9a79-66386ab4b95b.tmp | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF12c7ec.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
113
DNS requests
65
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
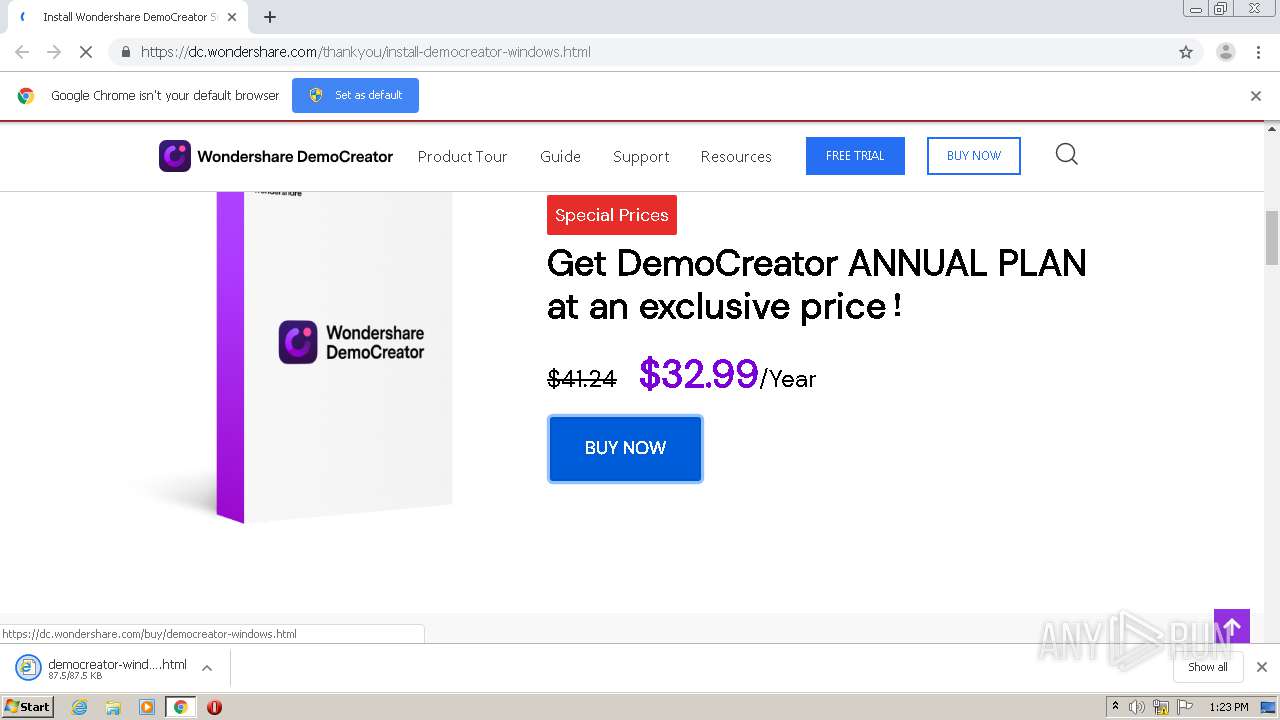
2540 | democreator_setup_full7743.exe | GET | — | 47.246.43.209:80 | http://download.wondershare.com/cbs_down/democreator_full7743.exe | US | — | — | whitelisted |
2540 | democreator_setup_full7743.exe | GET | — | 47.246.43.209:80 | http://download.wondershare.com/cbs_down/democreator_full7743.exe | US | — | — | whitelisted |
2540 | democreator_setup_full7743.exe | GET | — | 47.91.67.36:80 | http://dlinst.wondershare.com/player/style/orbit-1.3.0.css | US | — | — | suspicious |
2540 | democreator_setup_full7743.exe | GET | — | 47.246.43.209:80 | http://download.wondershare.com/cbs_down/democreator_full7743.exe | US | — | — | whitelisted |
2540 | democreator_setup_full7743.exe | HEAD | 200 | 47.246.43.209:80 | http://download.wondershare.com/cbs_down/democreator_full7743.exe | US | — | — | whitelisted |
2540 | democreator_setup_full7743.exe | GET | — | 47.246.43.209:80 | http://download.wondershare.com/cbs_down/democreator_full7743.exe | US | — | — | whitelisted |
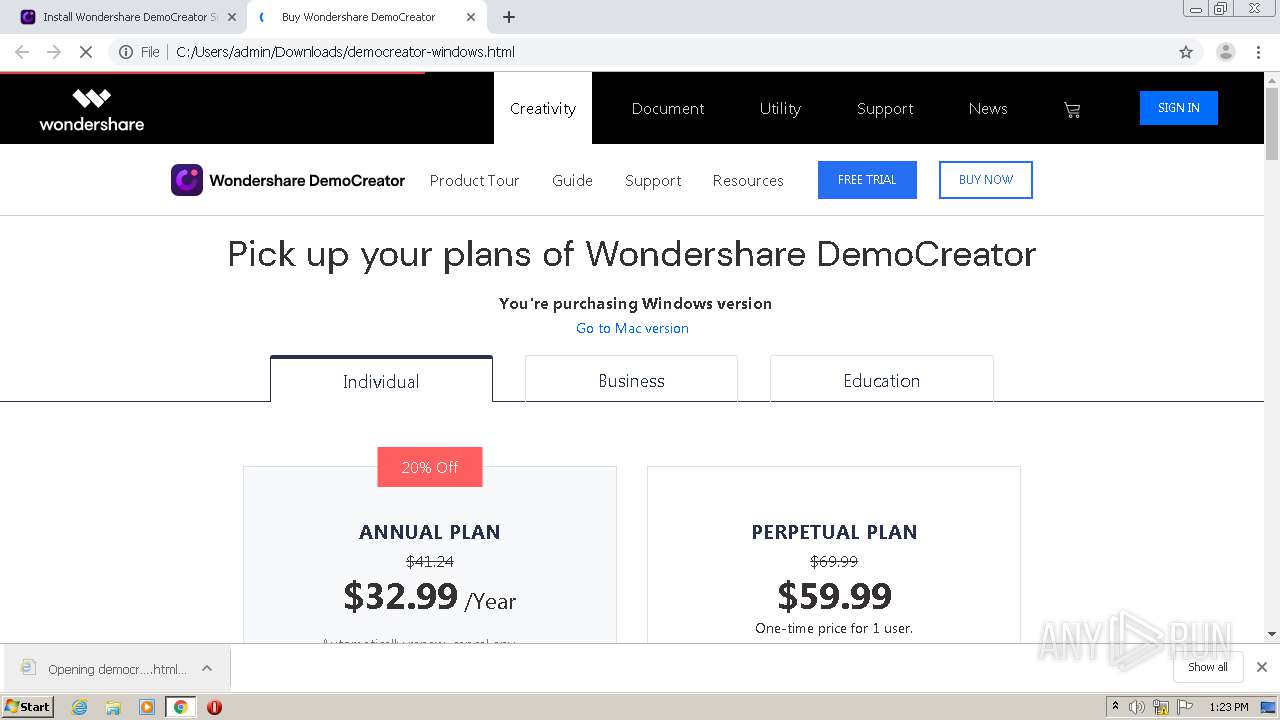
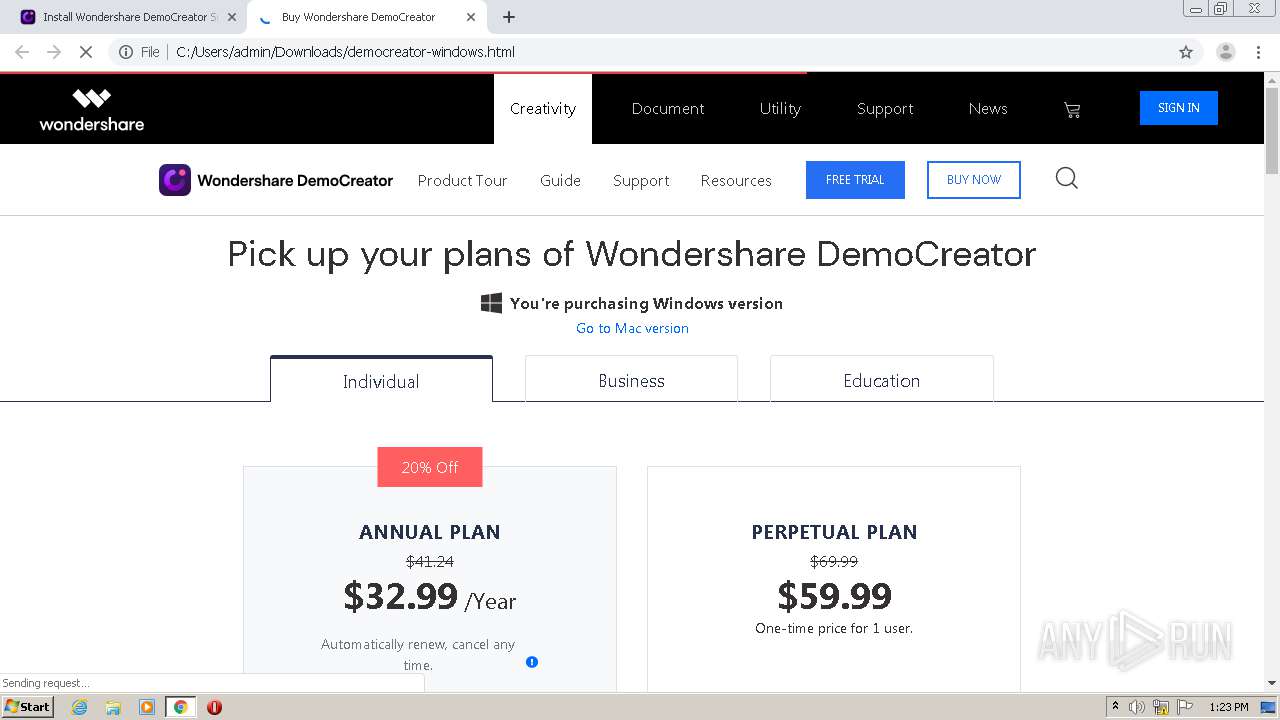
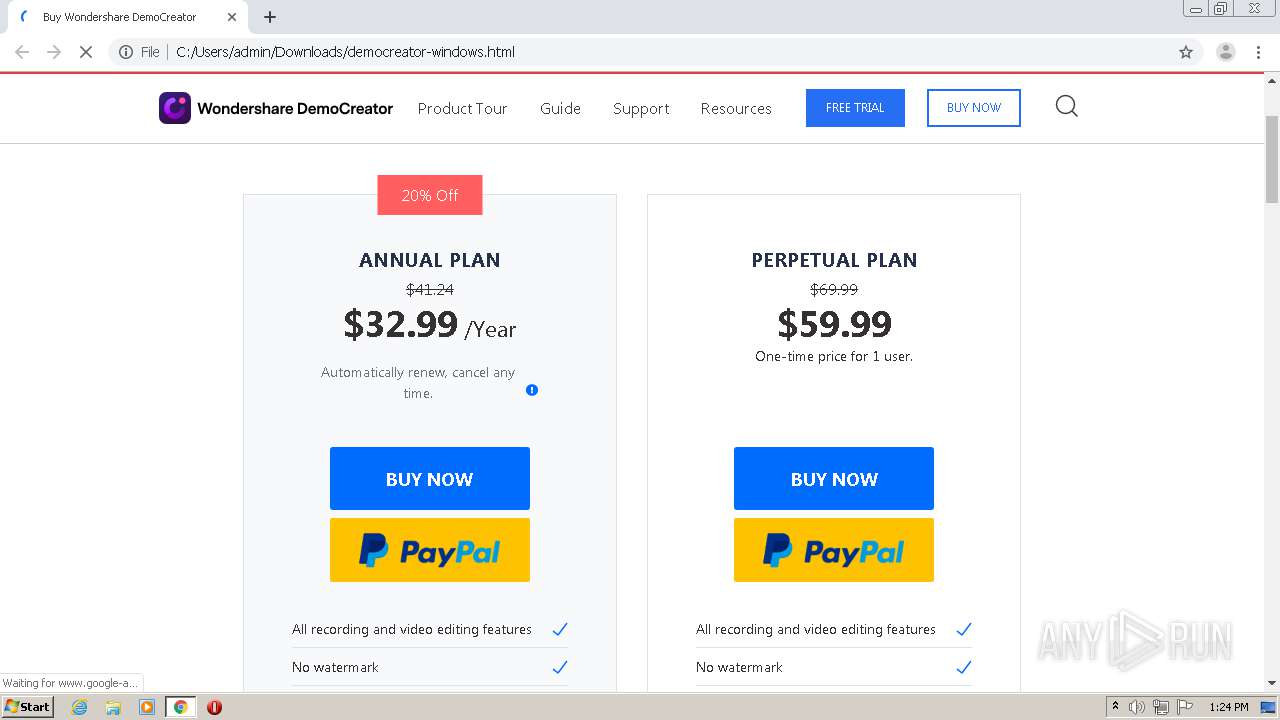
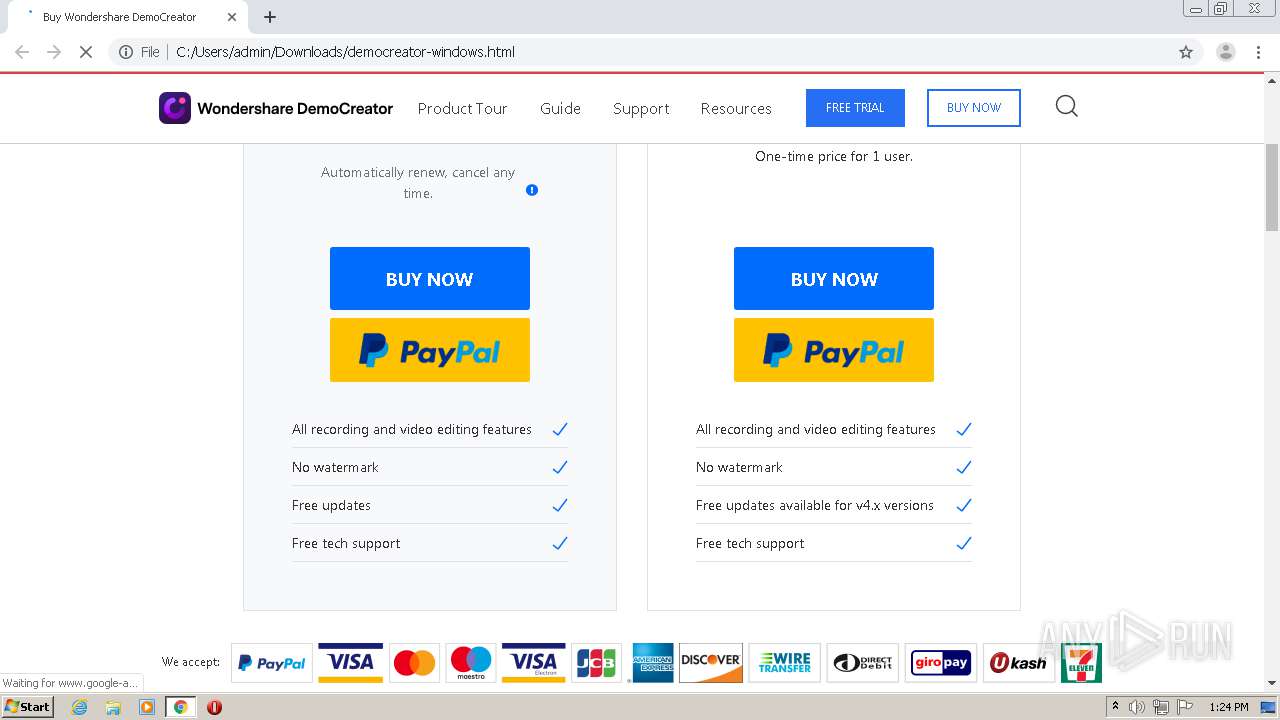
2820 | chrome.exe | GET | 200 | 95.101.18.179:80 | http://images.wondershare.com/democreator/article/btn-paypal.png | unknown | image | 8.06 Kb | whitelisted |
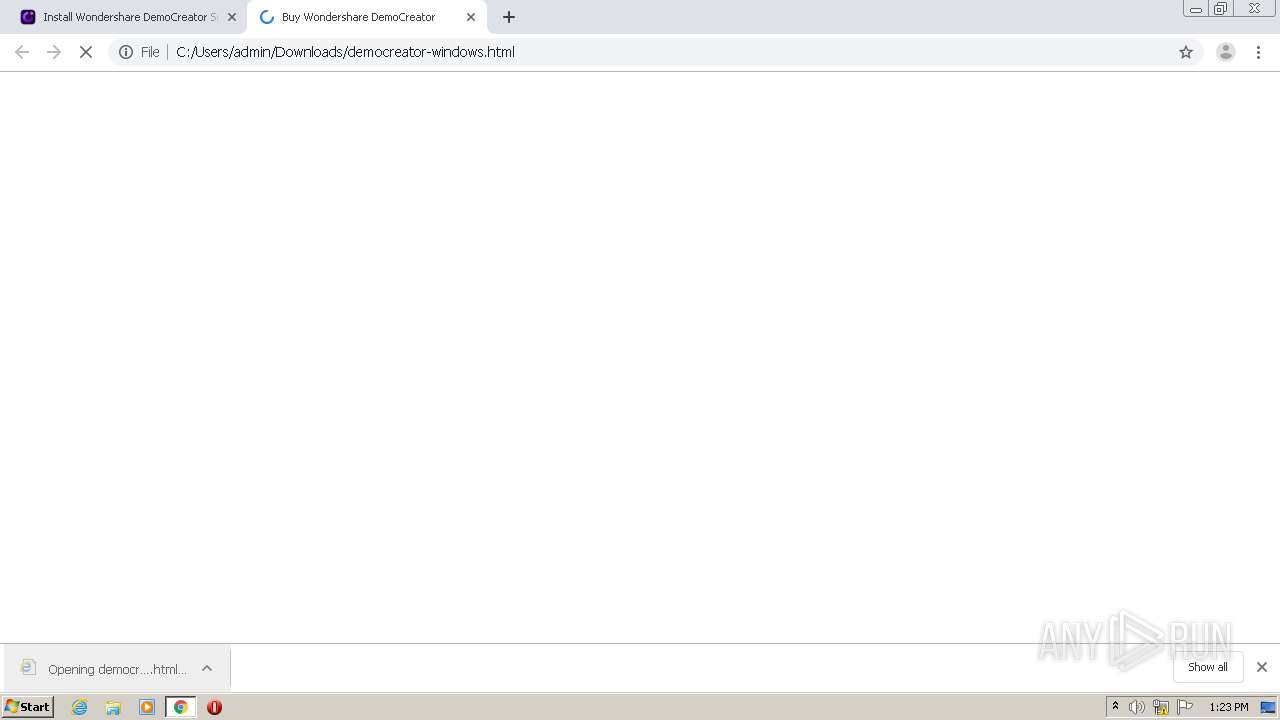
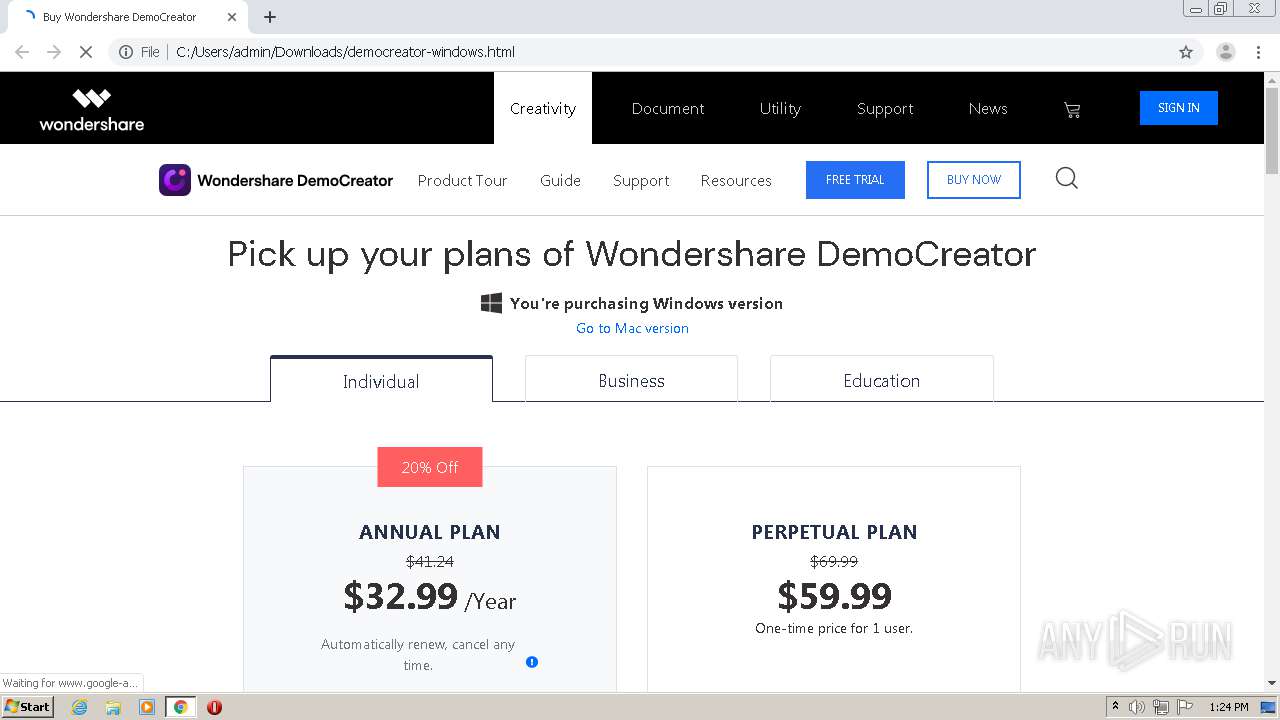
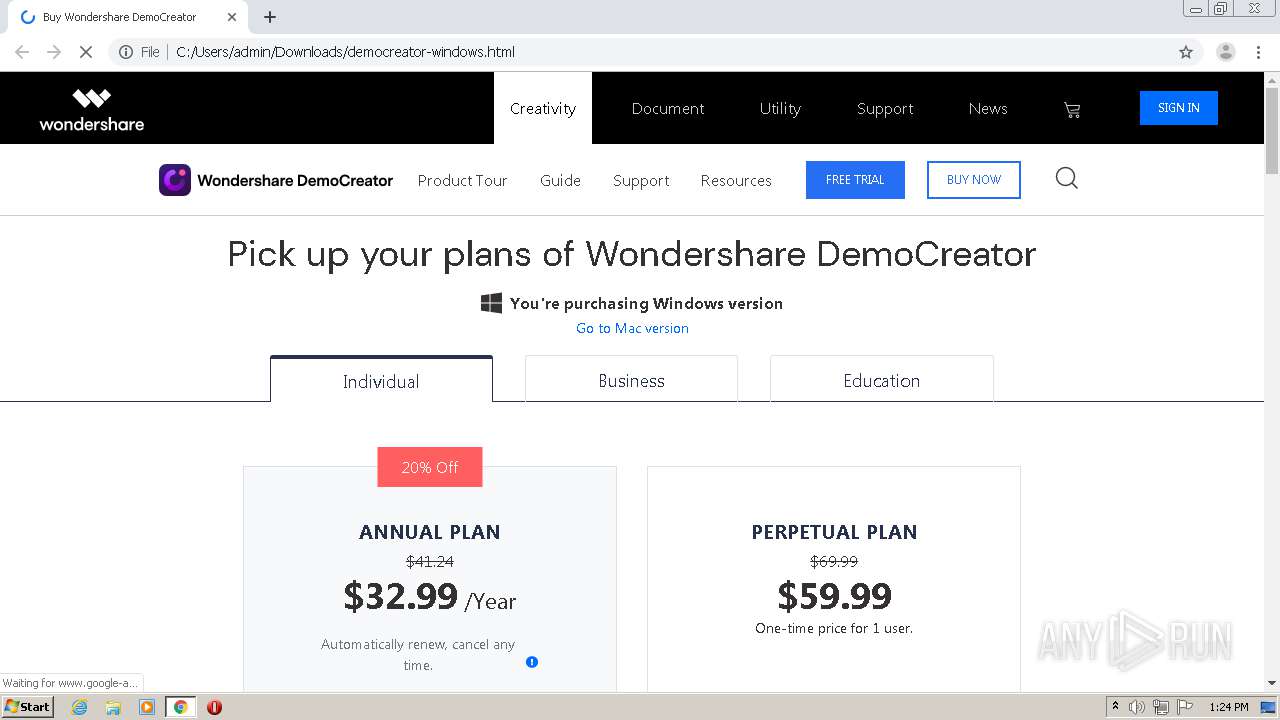
2820 | chrome.exe | GET | 200 | 3.230.28.201:80 | http://www.avmws.com/1020181/?url=file%3A%2F%2F%2FC%3A%2FUsers%2Fadmin%2FDownloads%2Fdemocreator-windows.html&ref=&name=Buy%20Wondershare%20DemoCreator&avmws=0&rand=0.7742616253067005&lib=1 | US | text | 200 b | shared |
2540 | democreator_setup_full7743.exe | GET | 200 | 47.91.67.36:80 | http://dlinst.wondershare.com/player/7743-20201208090512.html | US | html | 886 b | suspicious |
2540 | democreator_setup_full7743.exe | GET | 200 | 47.91.67.36:80 | http://platform.wondershare.com/rest/v2/downloader/runtime/?client_sign={C4BA3647-0000-0QM0-0001-1203334A04AF}&product_id=7743 | US | xml | 1.76 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
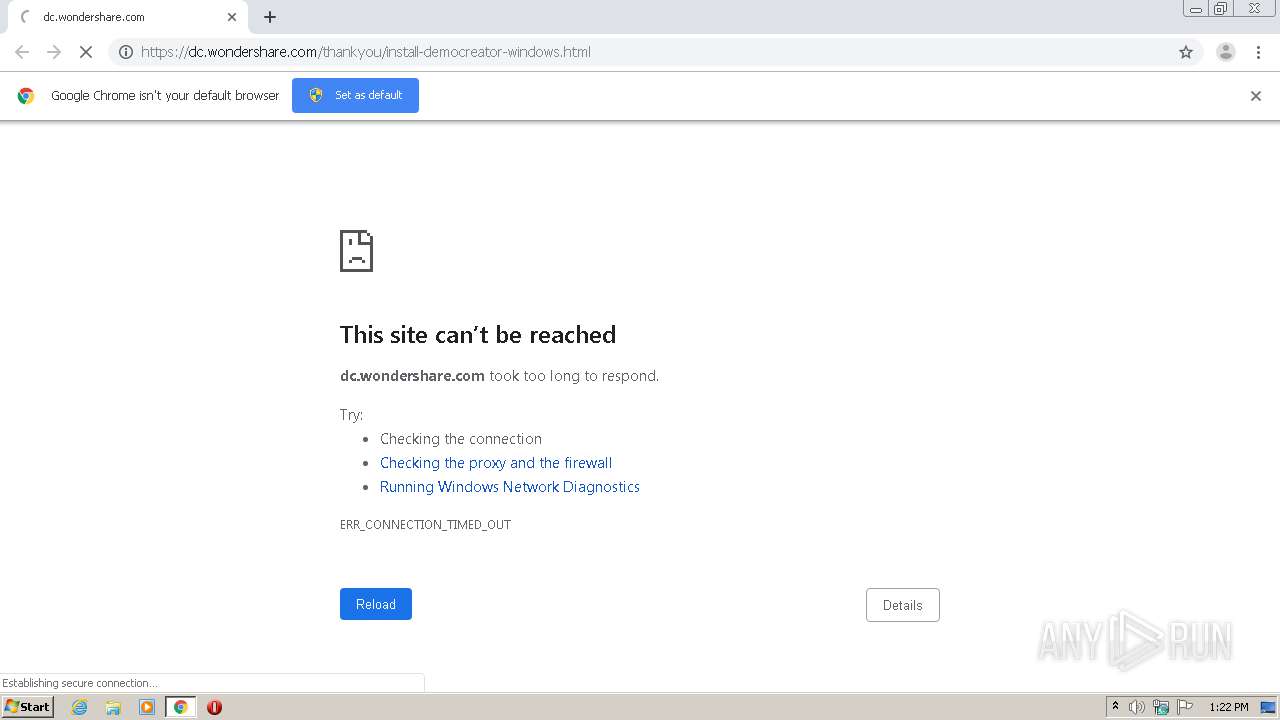
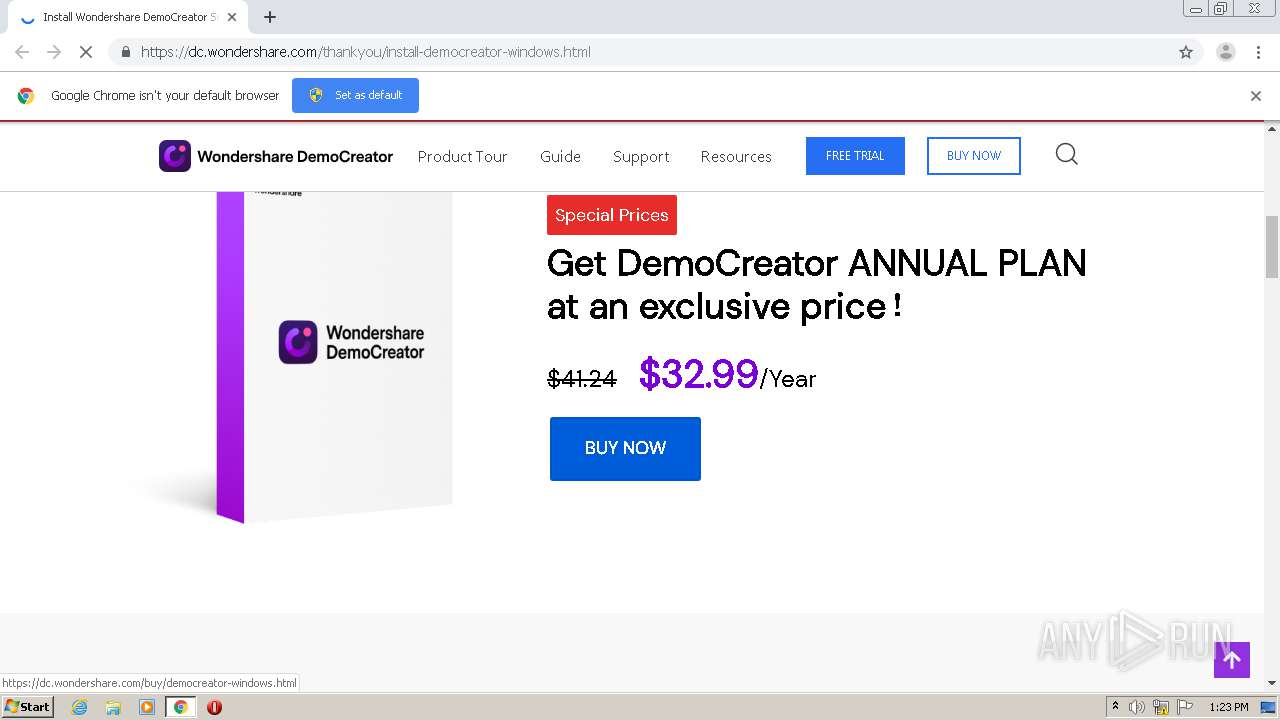
2820 | chrome.exe | 70.39.188.24:443 | dc.wondershare.com | QUANTIL, INC | US | unknown |
2820 | chrome.exe | 142.250.185.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2820 | chrome.exe | 47.91.91.66:80 | cbs.wondershare.com | Alibaba (China) Technology Co., Ltd. | US | malicious |
2820 | chrome.exe | 23.217.253.53:443 | images.wondershare.com | Akamai International B.V. | NL | unknown |
2820 | chrome.exe | 47.91.89.20:80 | cbs.wondershare.com | Alibaba (China) Technology Co., Ltd. | US | malicious |
2820 | chrome.exe | 142.250.185.66:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
2820 | chrome.exe | 157.240.20.19:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
2820 | chrome.exe | 13.107.21.200:443 | bat.bing.com | Microsoft Corporation | US | whitelisted |
2820 | chrome.exe | 65.9.58.98:443 | www.dwin1.com | AT&T Services, Inc. | US | suspicious |
2820 | chrome.exe | 143.204.207.30:443 | cdn.avmws.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cbs.wondershare.com |
| whitelisted |
accounts.google.com |
| shared |
dc.wondershare.com |
| suspicious |
ssl.gstatic.com |
| whitelisted |
neveragain.allstatics.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
images.wondershare.com |
| whitelisted |
www.wondershare.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2540 | democreator_setup_full7743.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
2540 | democreator_setup_full7743.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
2540 | democreator_setup_full7743.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
2540 | democreator_setup_full7743.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2540 | democreator_setup_full7743.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
2540 | democreator_setup_full7743.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
2540 | democreator_setup_full7743.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
2540 | democreator_setup_full7743.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
2540 | democreator_setup_full7743.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |