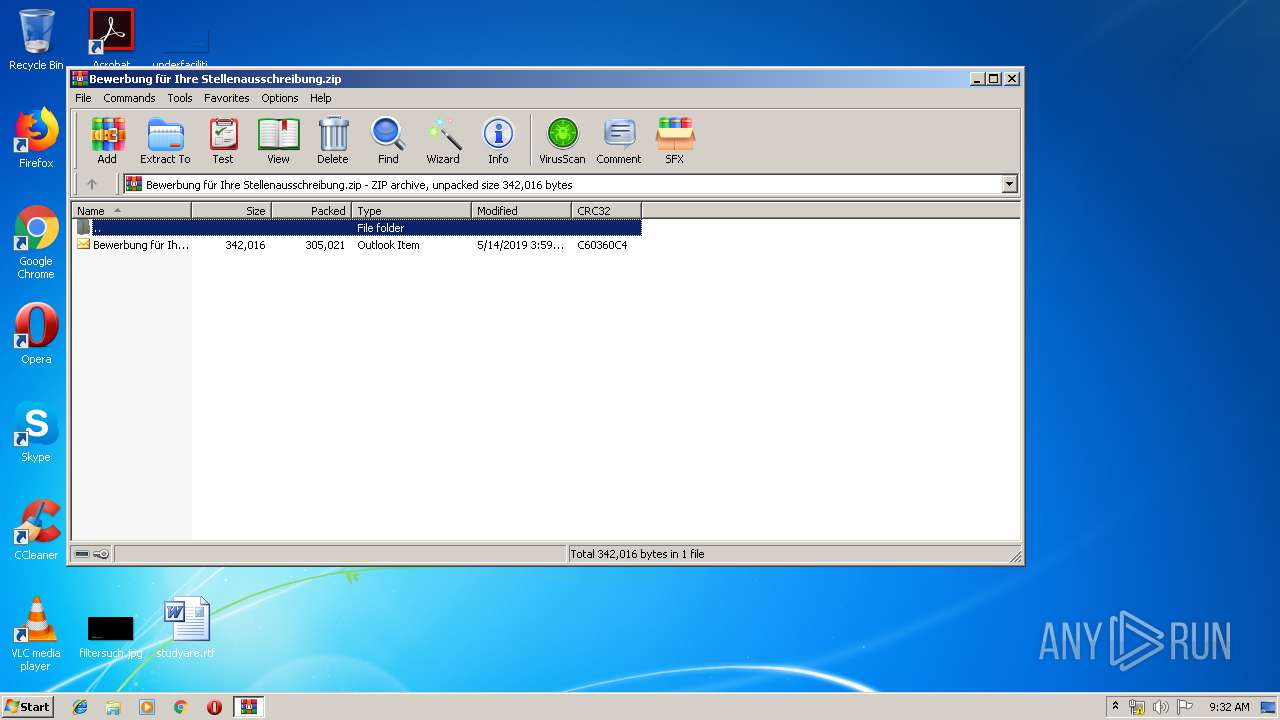
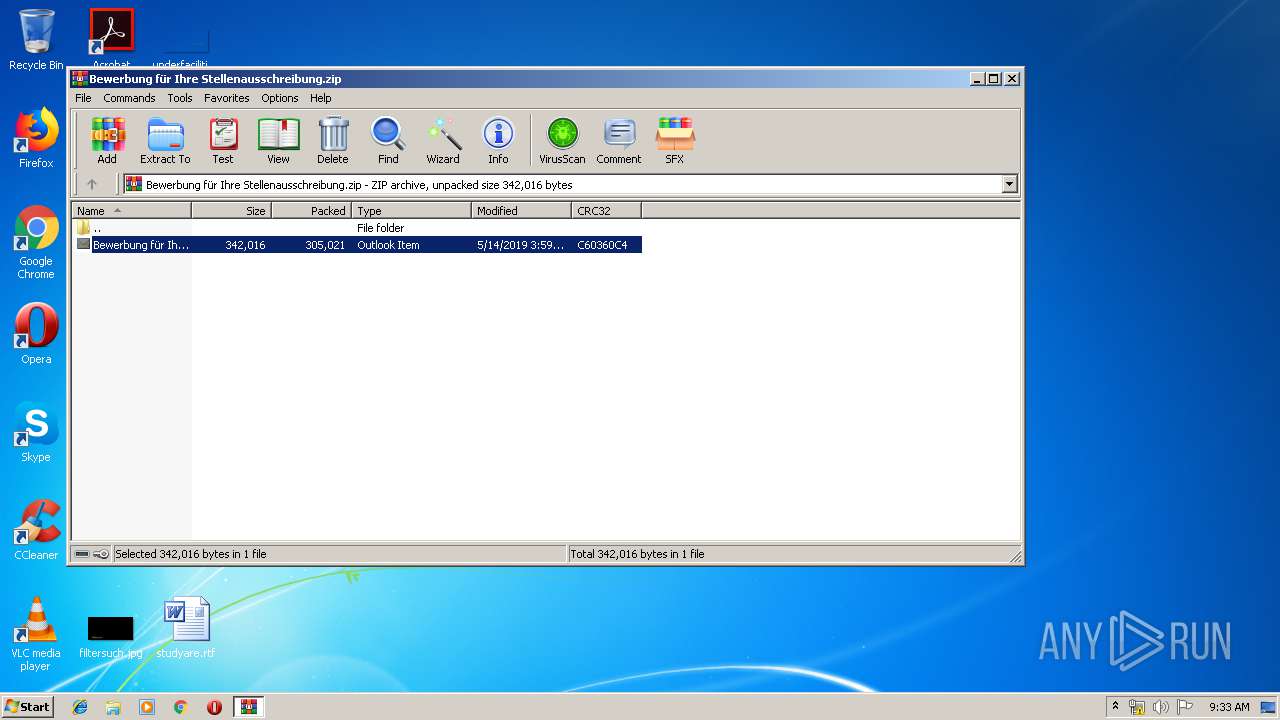
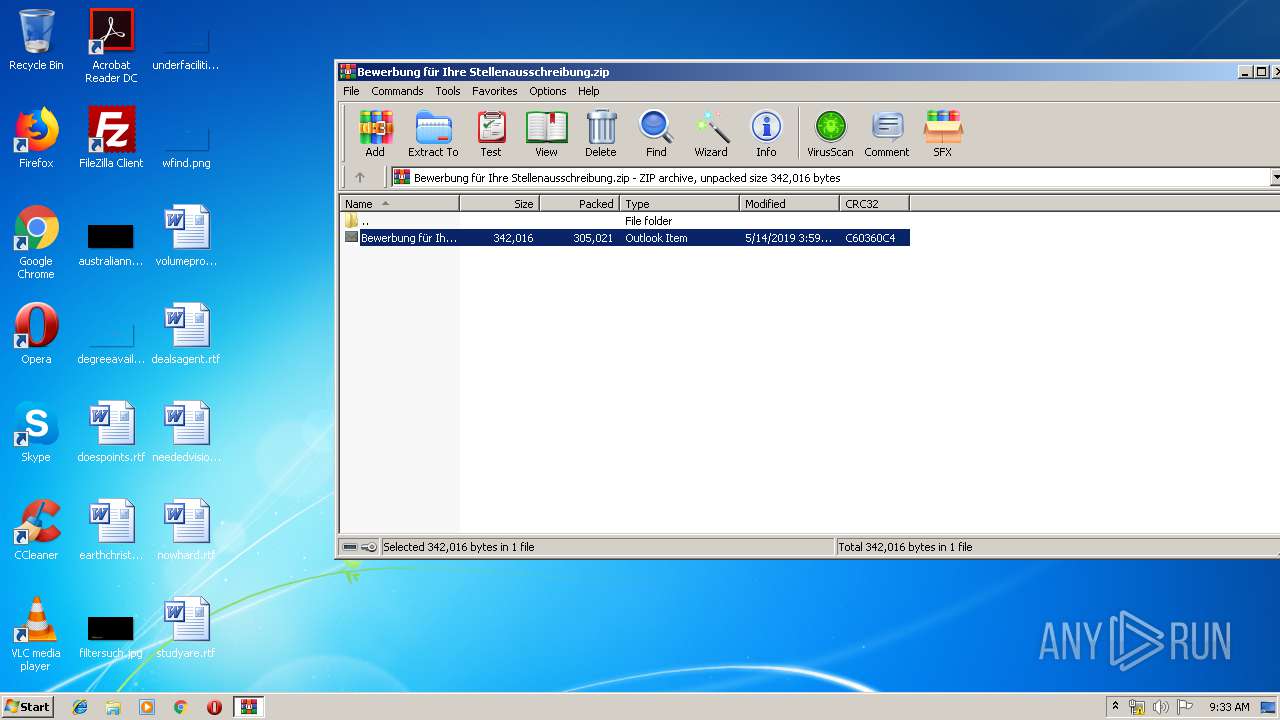
| File name: | Bewerbung für Ihre Stellenausschreibung.zip |
| Full analysis: | https://app.any.run/tasks/9867ade6-e28a-4bd2-b0db-5d78e872913d |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | May 15, 2019, 08:32:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 304520739774B737F5810263B7DD0663 |
| SHA1: | FE60482E2DC133F551278AFDCC55BC80E415EFEA |
| SHA256: | A6BD5E9B3EBA2CF7B95CB74525E9FB896C0F744DDF33722D33DADC84F3CB2FF4 |
| SSDEEP: | 6144:MUjLcLpGskiy2VysRUwBbjy3aR0rAk/EVS0SnHfUYEtcIWnv0oRQtVsakpESFhY:3fiykZbh0rAksk0A/9AcIWnsoRQtqakq |
MALICIOUS
Actions looks like stealing of personal data
- bbbb1.ccc (PID: 3132)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3984)
Executable content was dropped or overwritten
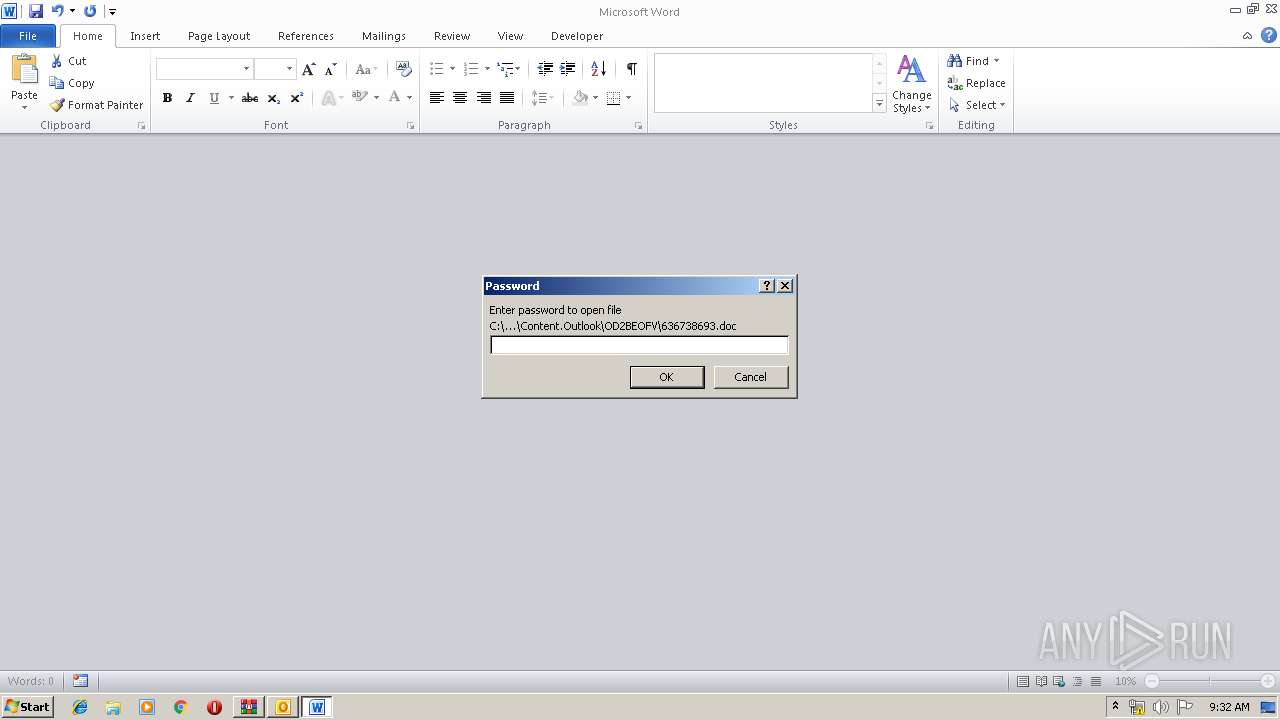
- WINWORD.EXE (PID: 3984)
Application was dropped or rewritten from another process
- bbbb1.ccc (PID: 3132)
Writes file to Word startup folder
- bbbb1.ccc (PID: 3132)
GANDCRAB detected
- bbbb1.ccc (PID: 3132)
SUSPICIOUS
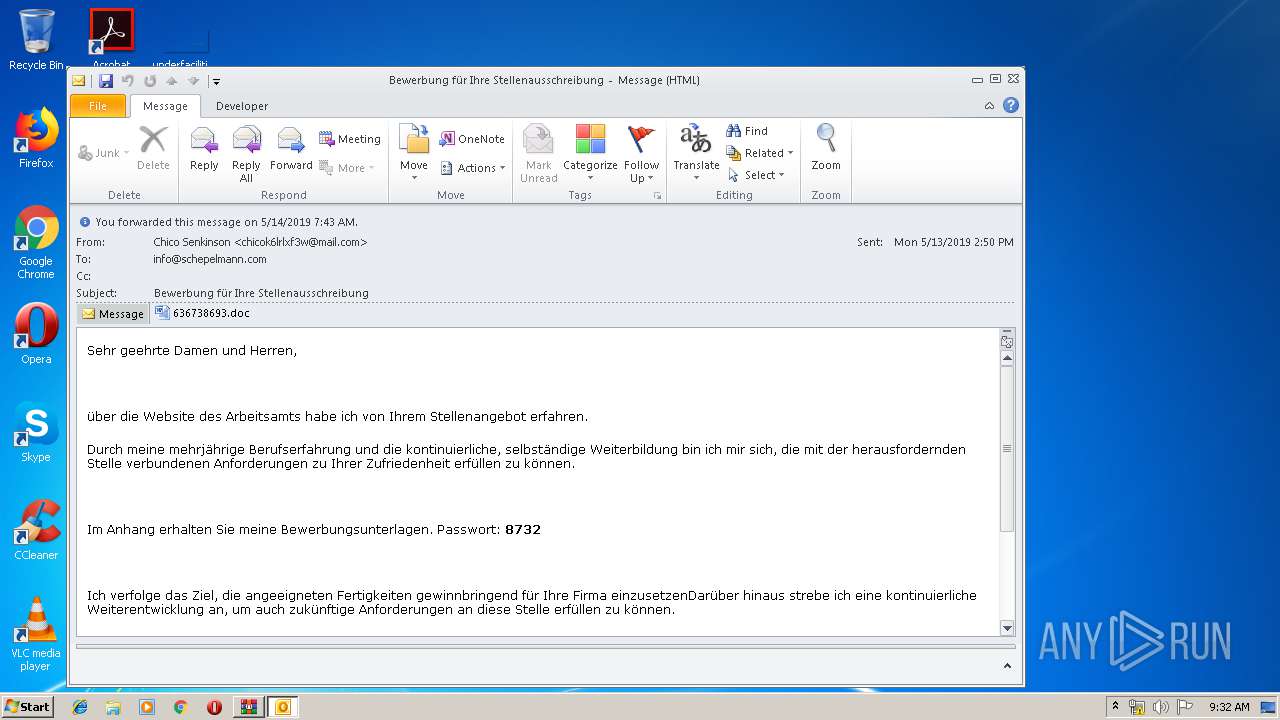
Starts Microsoft Office Application
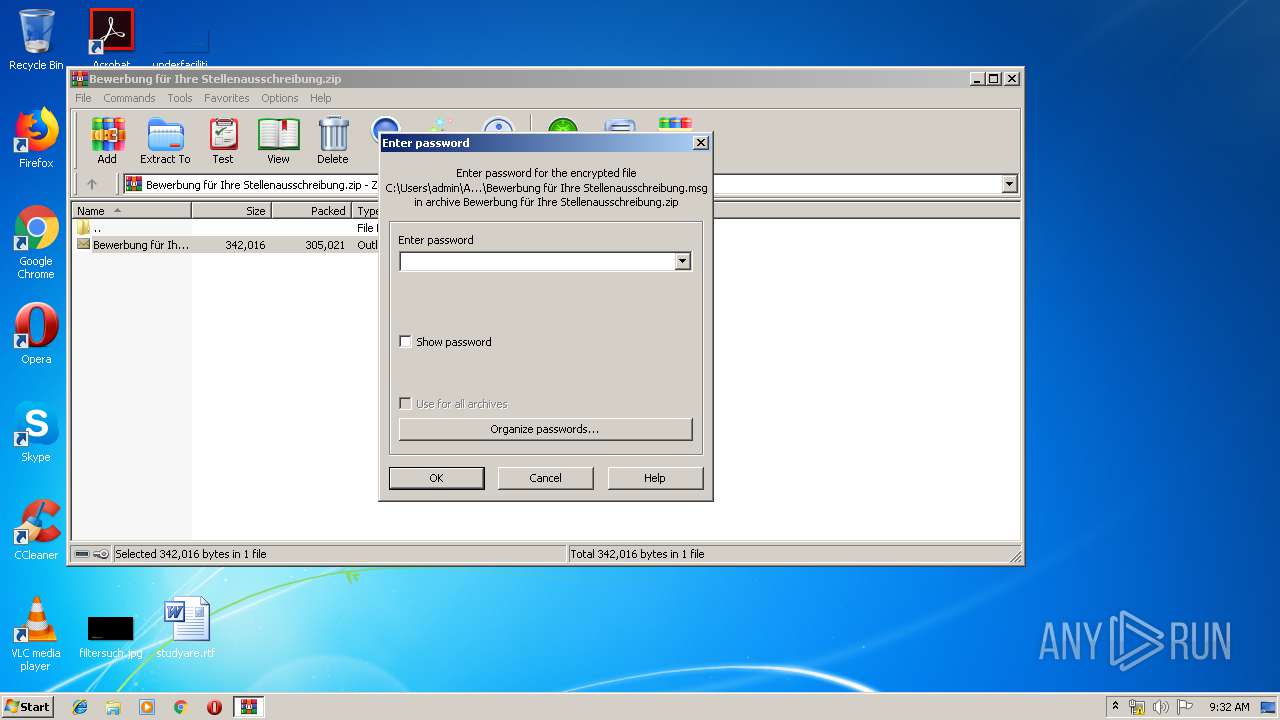
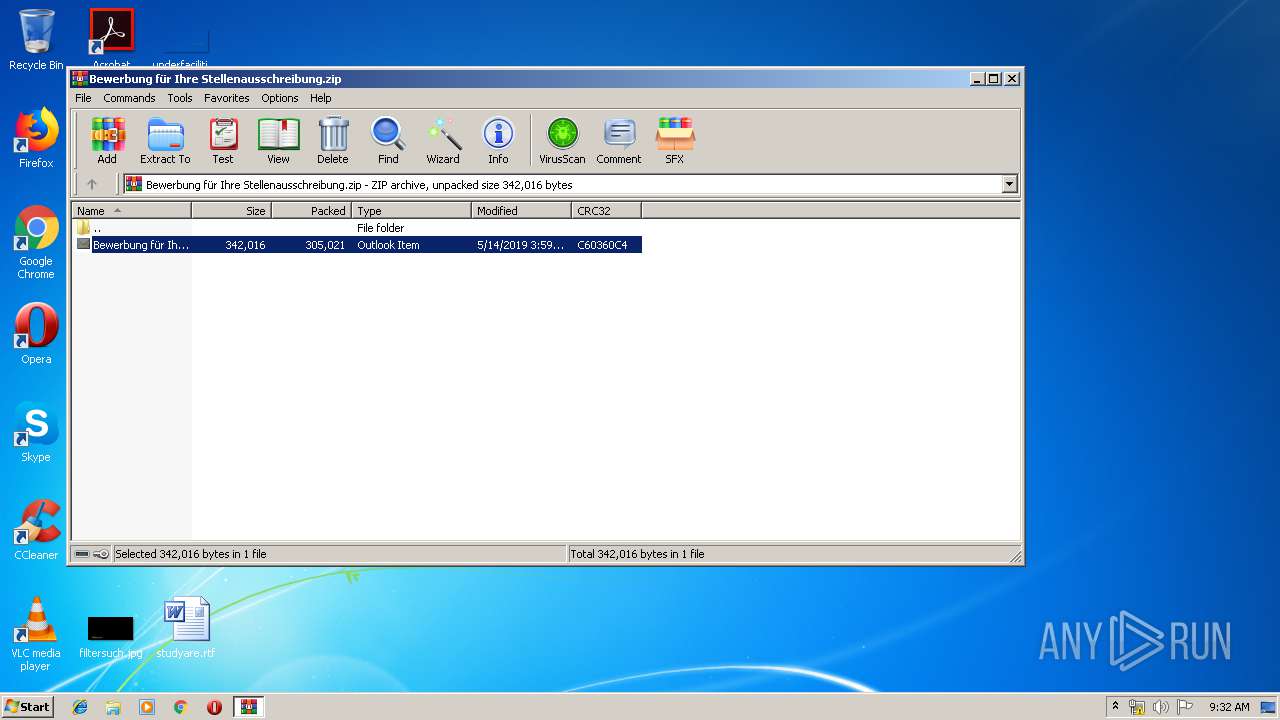
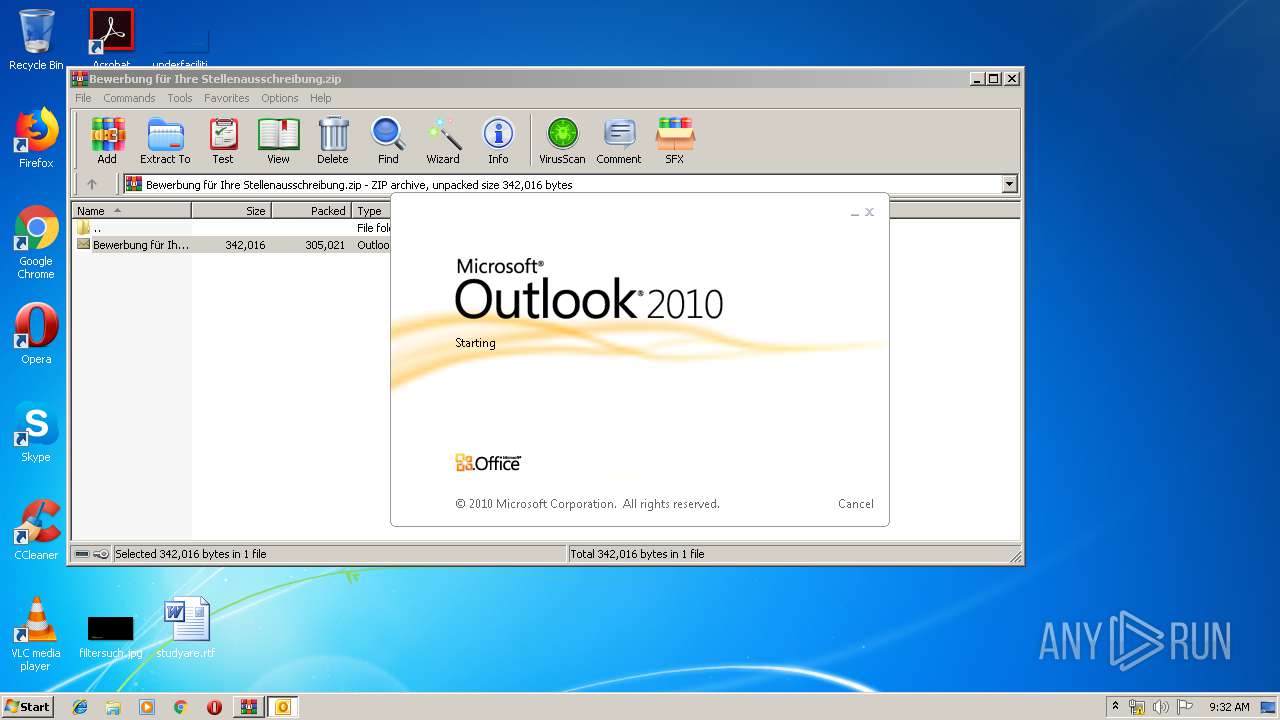
- WinRAR.exe (PID: 3328)
- OUTLOOK.EXE (PID: 2008)
- WINWORD.EXE (PID: 3984)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2008)
- bbbb1.ccc (PID: 3132)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2008)
- WINWORD.EXE (PID: 3984)
Application launched itself
- WINWORD.EXE (PID: 3984)
Starts application with an unusual extension
- WINWORD.EXE (PID: 3984)
Creates files in the Windows directory
- WINWORD.EXE (PID: 3984)
Creates files in the program directory
- bbbb1.ccc (PID: 3132)
Reads the cookies of Mozilla Firefox
- bbbb1.ccc (PID: 3132)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3984)
- WINWORD.EXE (PID: 2656)
- OUTLOOK.EXE (PID: 2008)
Creates files in the user directory
- WINWORD.EXE (PID: 3984)
Dropped object may contain Bitcoin addresses
- bbbb1.ccc (PID: 3132)
Dropped object may contain TOR URL's
- bbbb1.ccc (PID: 3132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:14 16:59:21 |
| ZipCRC: | 0xc60360c4 |
| ZipCompressedSize: | 305021 |
| ZipUncompressedSize: | 342016 |
| ZipFileName: | Bewerbung f?r Ihre Stellenausschreibung.msg |
Total processes
38
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
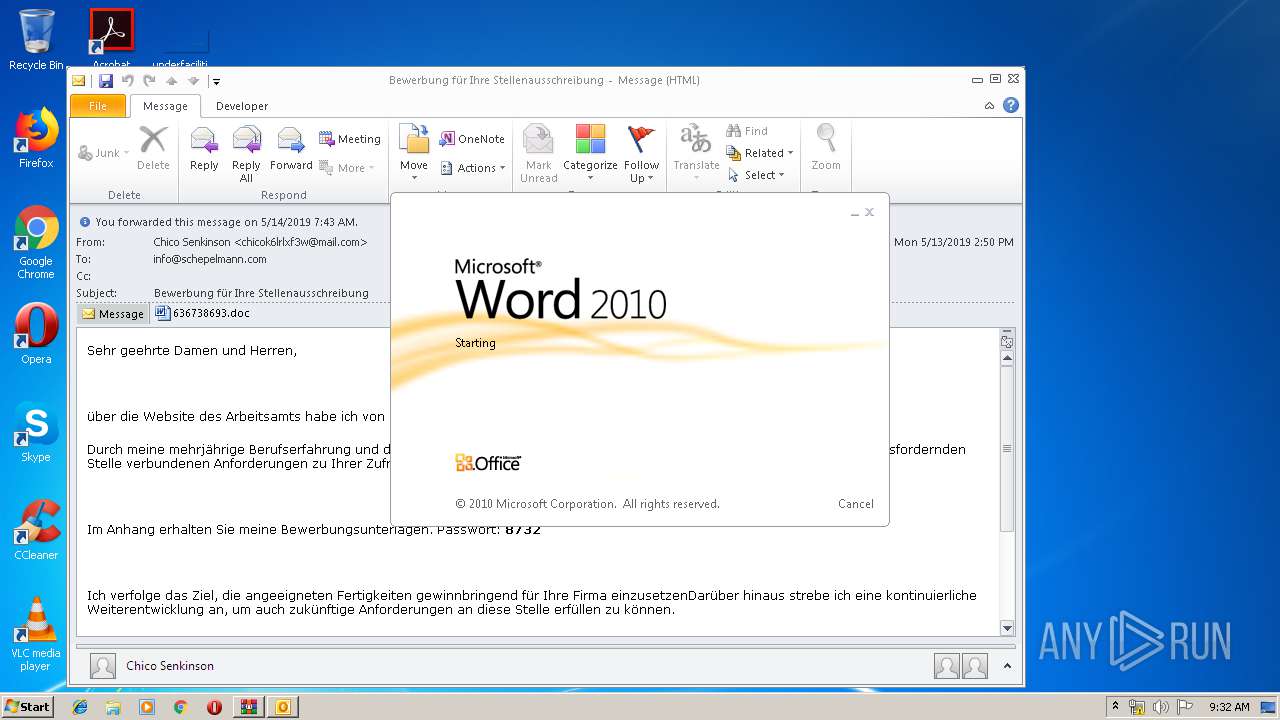
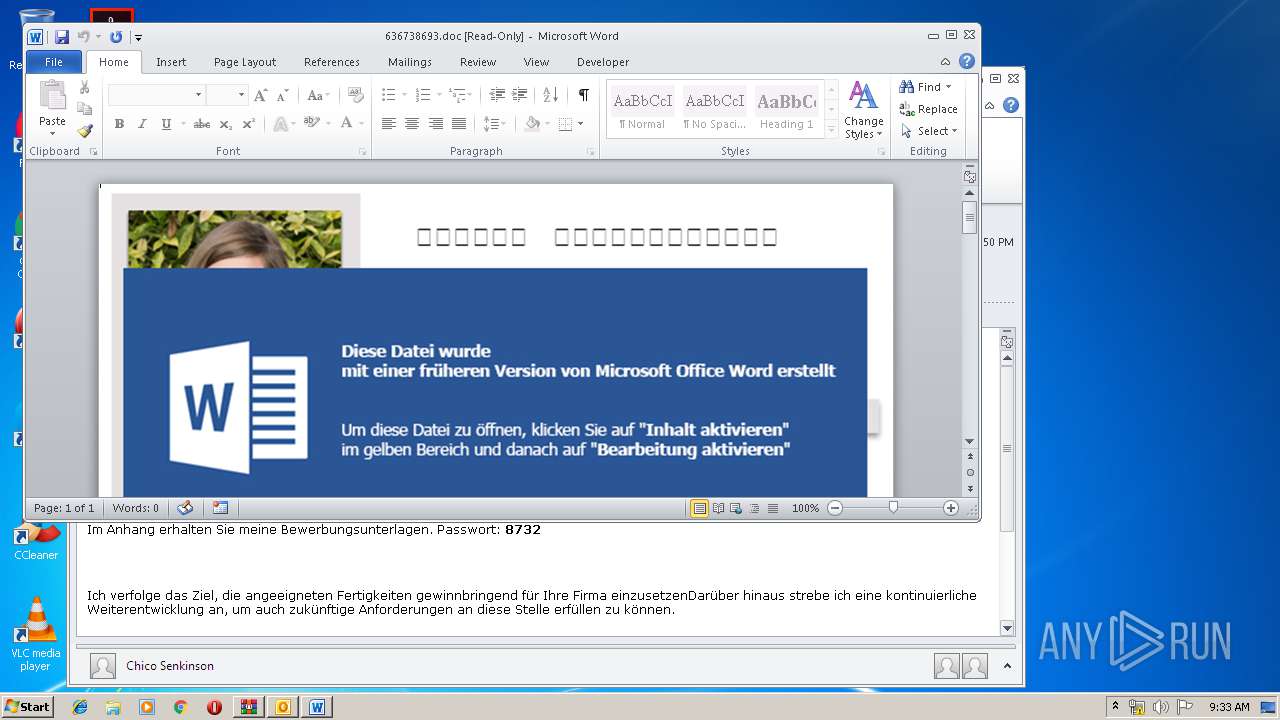
| 2008 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Rar$DIb3328.15984\Bewerbung für Ihre Stellenausschreibung.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3132 | C:\Windows\Temp\bbbb1.ccc | C:\Windows\Temp\bbbb1.ccc | WINWORD.EXE | ||||||||||||
User: admin Company: Hootsuite Integrity Level: MEDIUM Description: Tunnels Mix Attracted Slightly Pen Exit code: 0 Modules
| |||||||||||||||
| 3328 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Bewerbung für Ihre Stellenausschreibung.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
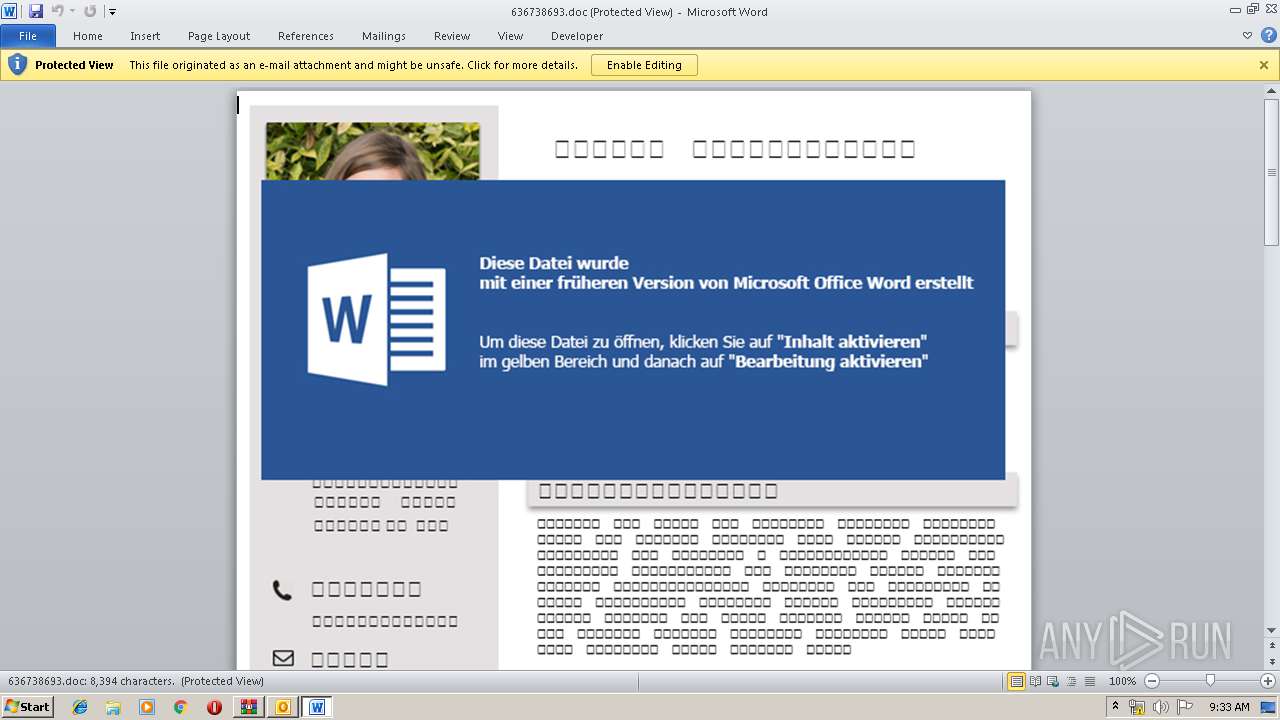
| 3984 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\OD2BEOFV\636738693.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 512
Read events
3 025
Write events
460
Delete events
27
Modification events
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Bewerbung für Ihre Stellenausschreibung.zip | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214FA-0000-0000-C000-000000000046} 0xFFFF |
Value: 010000000000000044E2D0BFF80AD501 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214EB-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000F8A6D5BFF80AD501 | |||
Executable files
2
Suspicious files
124
Text files
129
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2008 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR210D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2008 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF5BAB7116FD7151C1.TMP | — | |
MD5:— | SHA256:— | |||
| 2008 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\OD2BEOFV\636738693 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3984 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4994.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3984 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFE4BC7A1A19C4E39D.TMP | — | |
MD5:— | SHA256:— | |||
| 3984 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF3B0641F17F9633D1.TMP | — | |
MD5:— | SHA256:— | |||
| 3984 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF84047E915C42563B.TMP | — | |
MD5:— | SHA256:— | |||
| 3984 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFC6671B605E00A738.TMP | — | |
MD5:— | SHA256:— | |||
| 3984 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF6D43A1EFB543C72C.TMP | — | |
MD5:— | SHA256:— | |||
| 3984 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFBCCB94D75694FC9E.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2008 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2008 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3984 | WINWORD.EXE | 51.77.146.231:443 | zircoilerexelandr.info | — | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
zircoilerexelandr.info |
| suspicious |