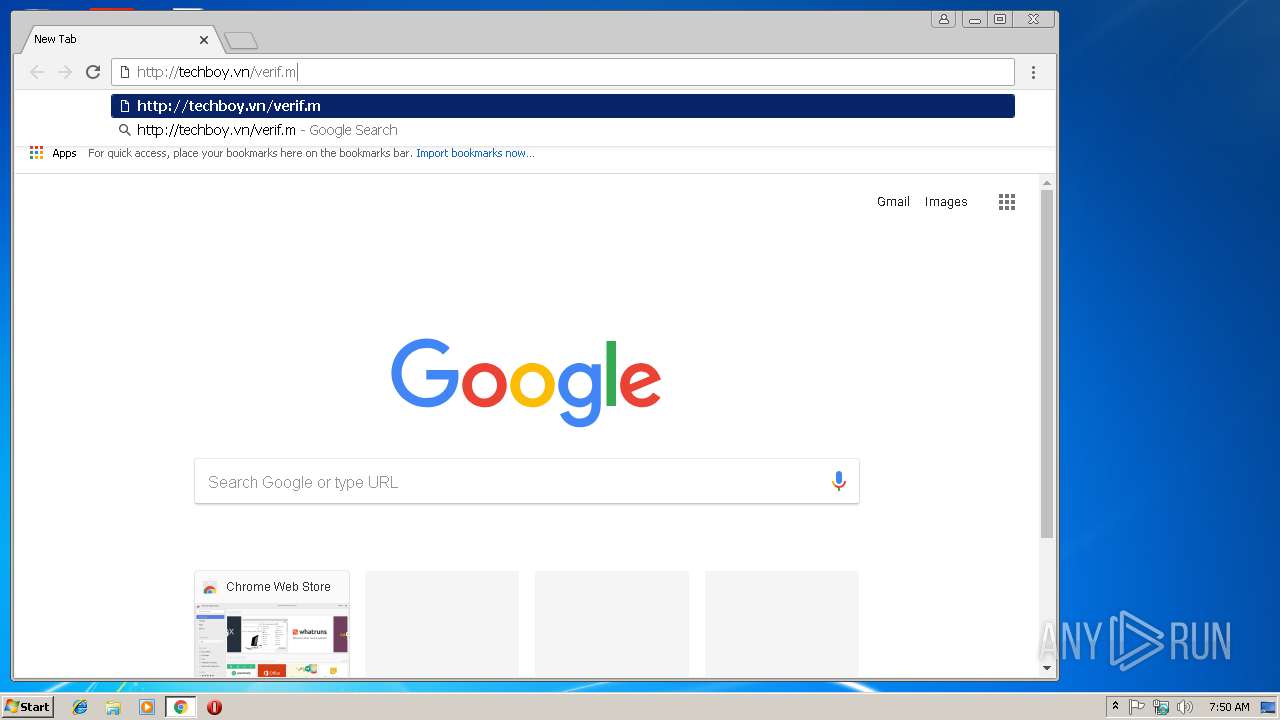
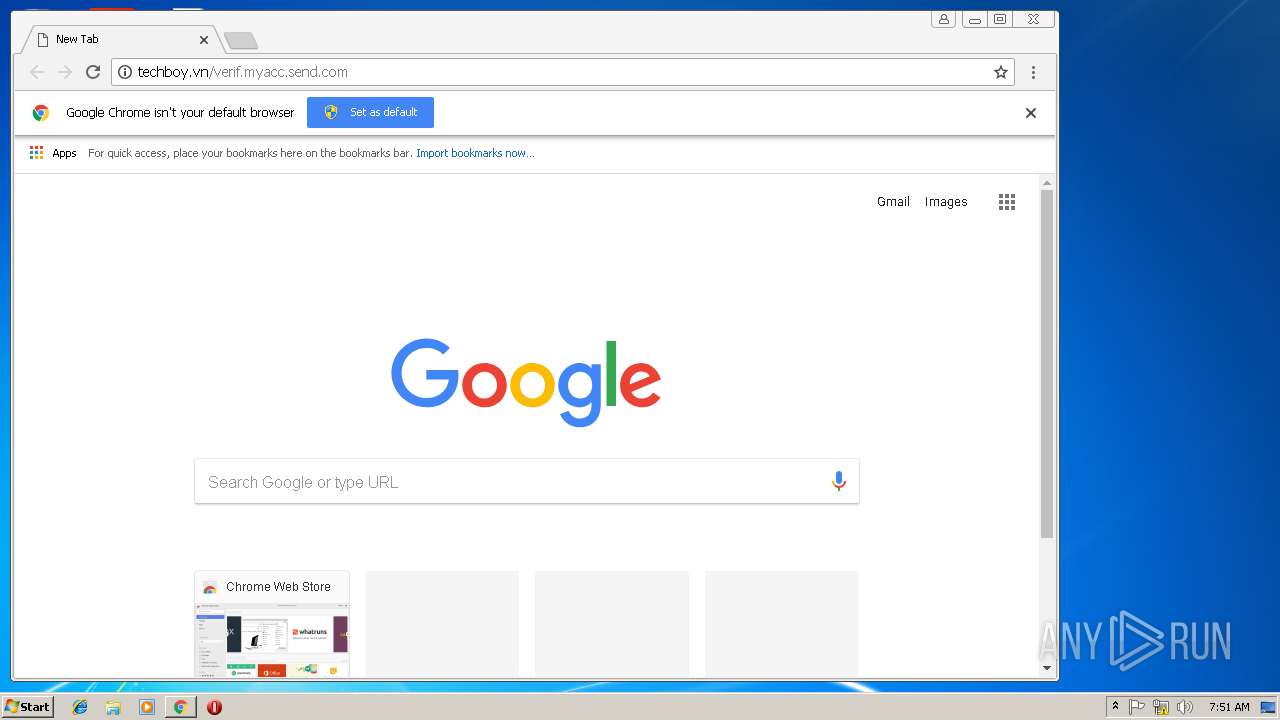
| download: | verif.myacc.send.com |
| Full analysis: | https://app.any.run/tasks/f51c623d-8142-4071-8f60-045c4d773b09 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 19, 2019, 07:49:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Feb 19 07:17:00 2019, Last Saved Time/Date: Tue Feb 19 07:17:00 2019, Number of Pages: 1, Number of Words: 1, Number of Characters: 12, Security: 0 |
| MD5: | BDA163E2B6F66EF06D5D9AE35FE98BE8 |
| SHA1: | 2A3677E032CE34406002CD88A06B0FB5A3B45B49 |
| SHA256: | A6AFEF3779E21DBB92B668D00488B27EC33742AD4C94DD5DC29CA208E63D581E |
| SSDEEP: | 6144:+G5/BnVfRFJ7KK9aHScdX9znGUEJmo2jo2nvuizWwUZZ1SUF:+2n9R/lA5dX9znGU1Bj9UZ15F |
MALICIOUS
Application was dropped or rewritten from another process
- 25.exe (PID: 2292)
- wabmetagen.exe (PID: 2220)
- 25.exe (PID: 3584)
- wabmetagen.exe (PID: 2628)
Emotet process was detected
- wabmetagen.exe (PID: 2220)
Downloads executable files from the Internet
- powersheLl.exe (PID: 3792)
EMOTET was detected
- wabmetagen.exe (PID: 2628)
Connects to CnC server
- wabmetagen.exe (PID: 2628)
SUSPICIOUS
Creates files in the user directory
- powersheLl.exe (PID: 3792)
Starts itself from another location
- 25.exe (PID: 3584)
Starts Microsoft Office Application
- chrome.exe (PID: 3060)
- WINWORD.EXE (PID: 3152)
Application launched itself
- WINWORD.EXE (PID: 3152)
- wabmetagen.exe (PID: 2220)
Executable content was dropped or overwritten
- powersheLl.exe (PID: 3792)
- 25.exe (PID: 3584)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3152)
- WINWORD.EXE (PID: 3464)
Application launched itself
- chrome.exe (PID: 3060)
Reads settings of System Certificates
- chrome.exe (PID: 3060)
Reads Internet Cache Settings
- chrome.exe (PID: 3060)
Creates files in the user directory
- chrome.exe (PID: 3060)
- WINWORD.EXE (PID: 3152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:02:19 07:17:00 |
| ModifyDate: | 2019:02:19 07:17:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 12 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 12 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
54
Monitored processes
20
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2220 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 25.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2292 | "C:\Users\admin\25.exe" | C:\Users\admin\25.exe | — | powersheLl.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=908,12277141311165040025,4549092249178412732,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=3D7CEA94AD4043EF58B5F278882999DE --mojo-platform-channel-handle=936 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,12277141311165040025,4549092249178412732,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7522C8DF036E8A77F4373F5061AF75A7 --mojo-platform-channel-handle=3836 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=908,12277141311165040025,4549092249178412732,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=0C0CAA7FAD240DF884C153534D52DA5B --mojo-platform-channel-handle=3932 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,12277141311165040025,4549092249178412732,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9373B18F99AF94EC48F1B51B77D14E6A --mojo-platform-channel-handle=4128 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2628 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,12277141311165040025,4549092249178412732,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=713B8FA891277148266691A555303ED4 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=713B8FA891277148266691A555303ED4 --renderer-client-id=6 --mojo-platform-channel-handle=1656 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,12277141311165040025,4549092249178412732,131072 --enable-features=PasswordImport --service-pipe-token=E9E019628884EFBF033B28C954CD7900 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E9E019628884EFBF033B28C954CD7900 --renderer-client-id=5 --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 331
Read events
2 835
Write events
477
Delete events
19
Modification events
| (PID) Process: | (3060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3060-13195036216907875 |
Value: 259 | |||
| (PID) Process: | (3060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3060) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3060-13195036216907875 |
Value: 259 | |||
| (PID) Process: | (3060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
75
Text files
89
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3076 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs6BCA.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs6BCB.tmp | — | |
MD5:— | SHA256:— | |||
| 3060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c4cf804f-3a7c-4e99-8c13-5f4b538948f8.tmp | — | |
MD5:— | SHA256:— | |||
| 3060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\47940bbc-764a-425e-be58-40764f1f2245.tmp | — | |
MD5:— | SHA256:— | |||
| 3060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 3060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF2490a8.TMP | text | |
MD5:— | SHA256:— | |||
| 3060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
25
DNS requests
14
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2628 | wabmetagen.exe | GET | — | 189.251.40.71:8080 | http://189.251.40.71:8080/ | MX | — | — | malicious |
2628 | wabmetagen.exe | GET | — | 70.24.147.245:443 | http://70.24.147.245:443/ | CA | — | — | malicious |
2628 | wabmetagen.exe | GET | — | 88.225.226.91:443 | http://88.225.226.91:443/ | TR | — | — | malicious |
2628 | wabmetagen.exe | GET | — | 208.180.246.147:80 | http://208.180.246.147/ | US | — | — | malicious |
3792 | powersheLl.exe | GET | 200 | 45.252.248.16:80 | http://tongdailyson.com/xep5fMwX/ | VN | executable | 214 Kb | malicious |
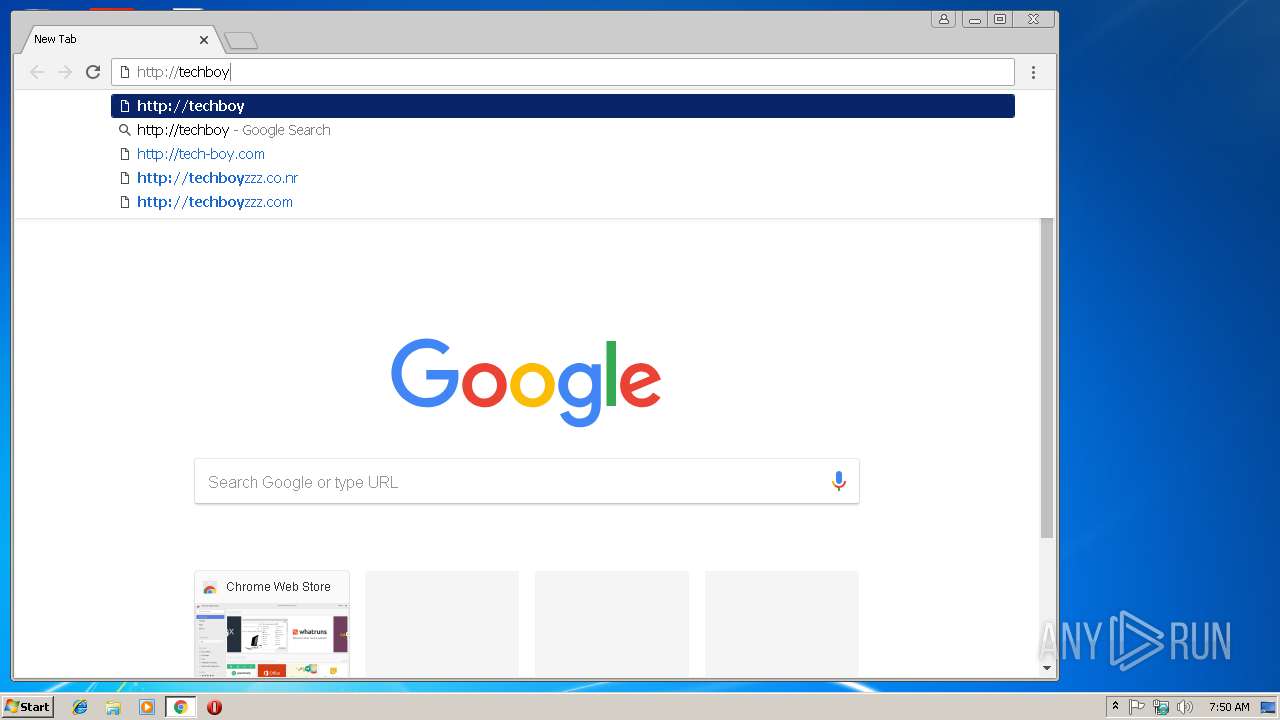
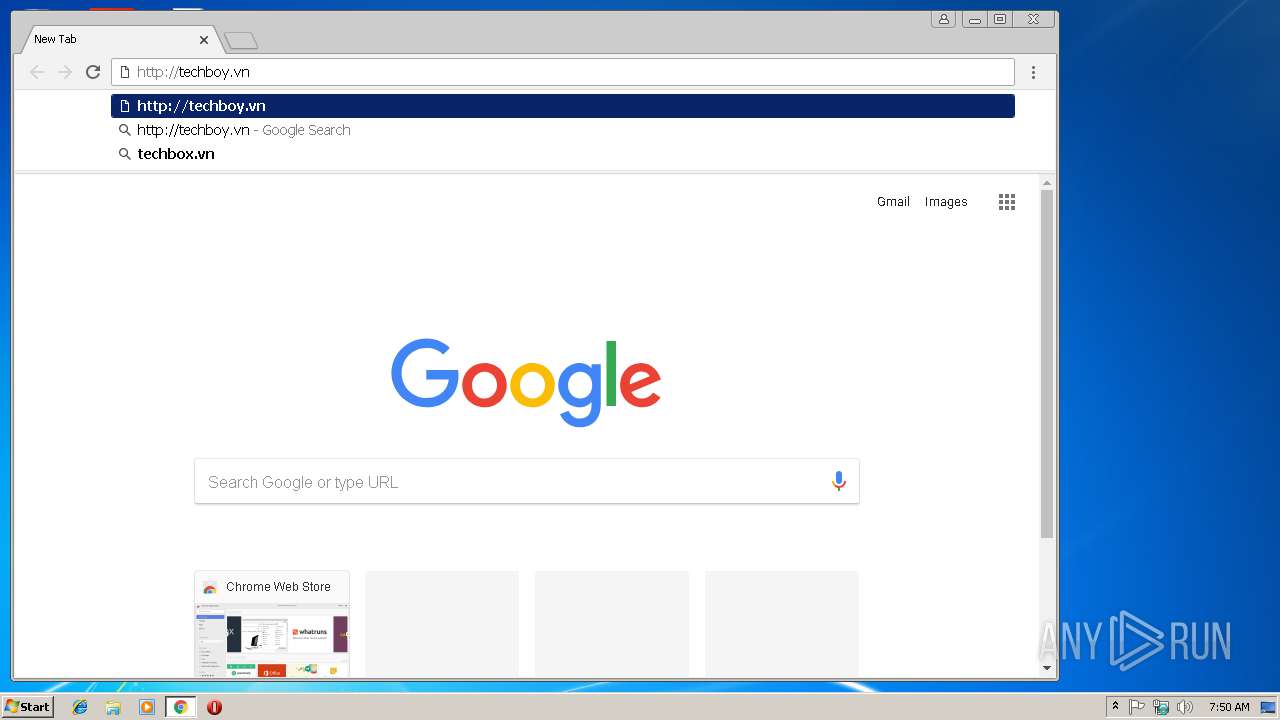
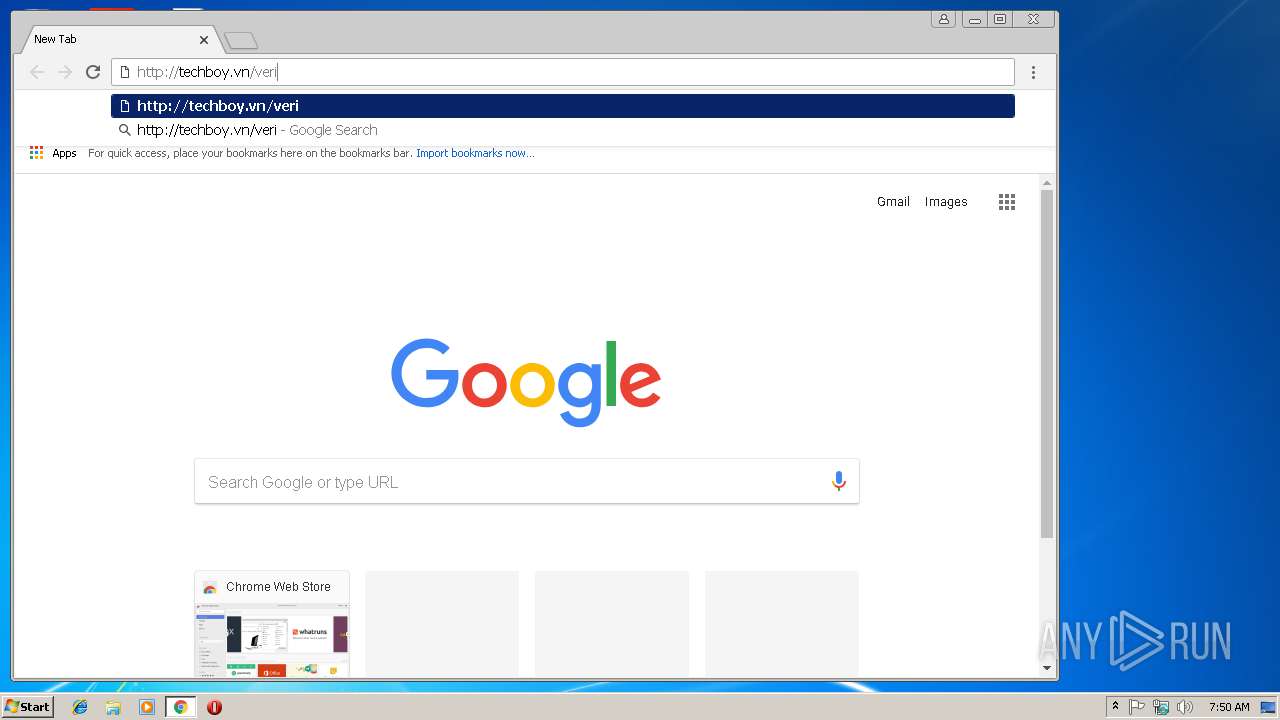
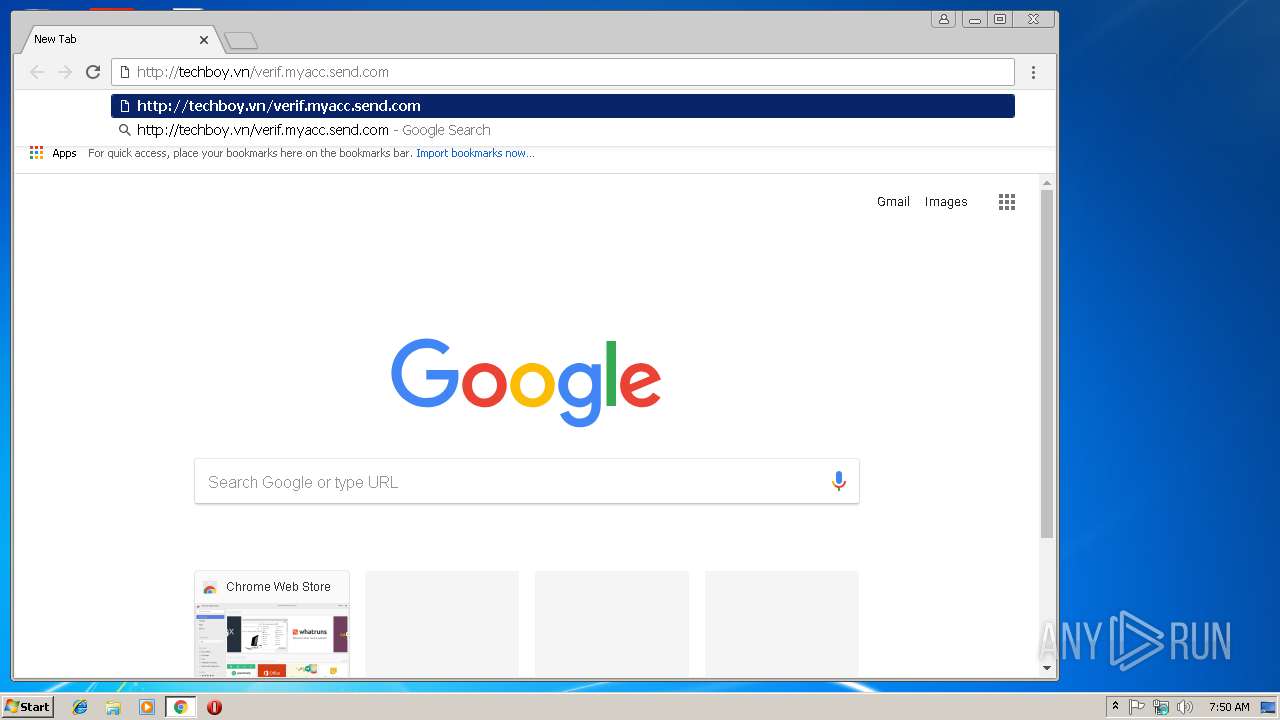
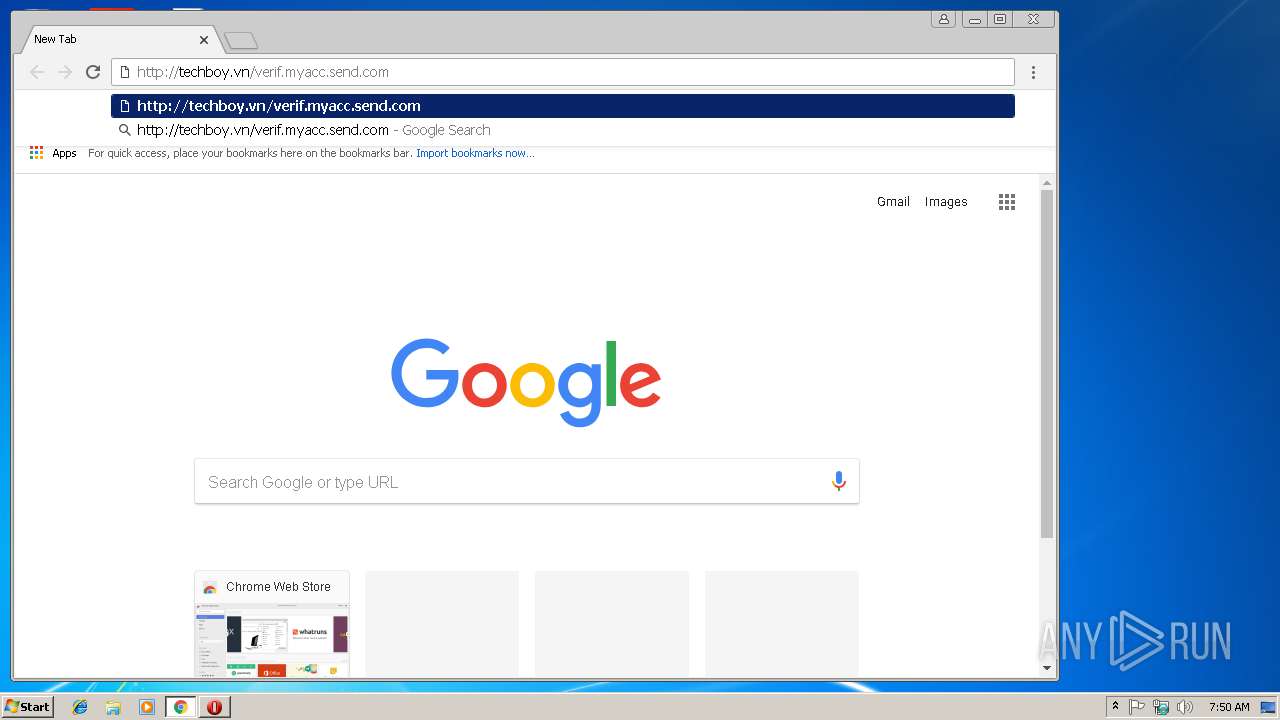
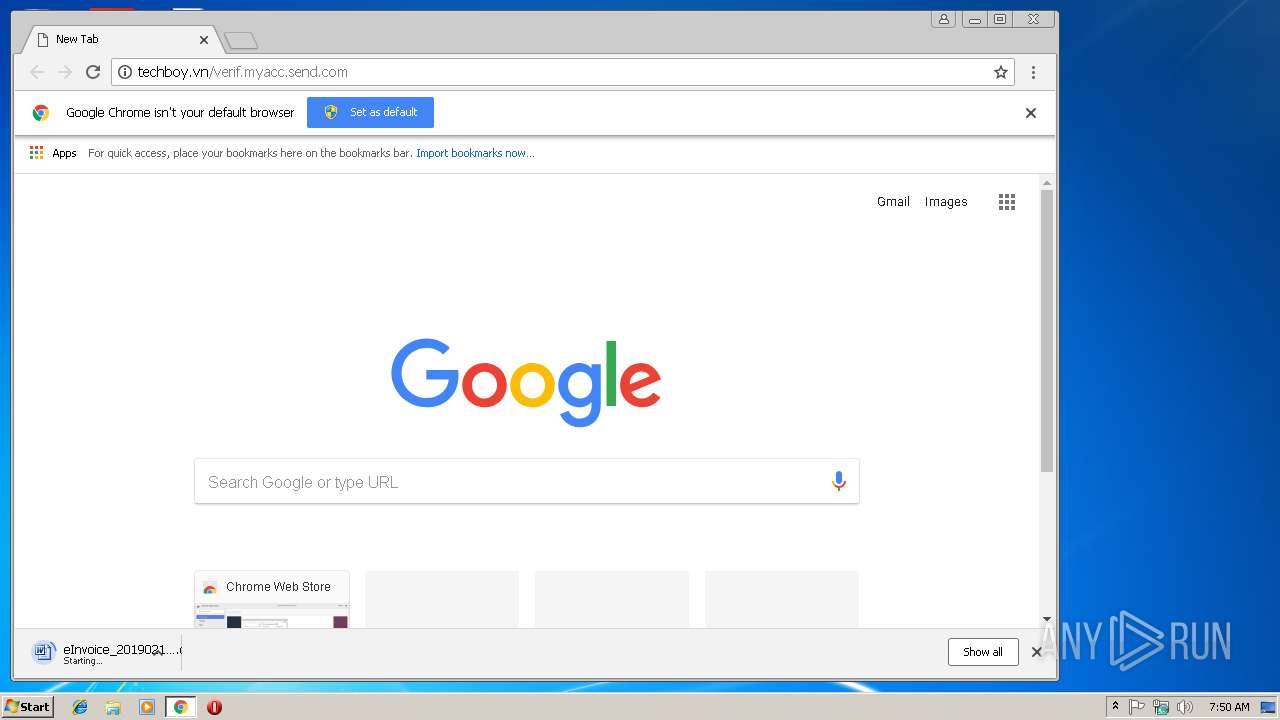
3060 | chrome.exe | GET | 200 | 35.198.196.245:80 | http://techboy.vn/verif.myacc.send.com/ | US | document | 180 Kb | malicious |
3060 | chrome.exe | GET | 301 | 35.198.196.245:80 | http://techboy.vn/verif.myacc.send.com | US | html | 247 b | malicious |
3792 | powersheLl.exe | GET | 301 | 45.252.248.16:80 | http://tongdailyson.com/xep5fMwX | VN | html | 617 b | malicious |
2628 | wabmetagen.exe | GET | — | 209.159.244.240:443 | http://209.159.244.240:443/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3060 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
3060 | chrome.exe | 172.217.22.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3060 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3060 | chrome.exe | 35.198.196.245:80 | techboy.vn | Google Inc. | US | malicious |
2628 | wabmetagen.exe | 88.225.226.91:443 | — | Turk Telekom | TR | malicious |
3792 | powersheLl.exe | 45.252.248.16:80 | tongdailyson.com | AZDIGI Corporation | VN | malicious |
2628 | wabmetagen.exe | 208.180.246.147:80 | — | Suddenlink Communications | US | malicious |
2628 | wabmetagen.exe | 189.251.40.71:8080 | — | Uninet S.A. de C.V. | MX | malicious |
2628 | wabmetagen.exe | 70.24.147.245:443 | — | Bell Canada | CA | malicious |
2628 | wabmetagen.exe | 209.159.244.240:443 | — | Clarity Telecom LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.it |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3792 | powersheLl.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3792 | powersheLl.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3792 | powersheLl.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2628 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2628 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2628 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2628 | wabmetagen.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
2628 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
4 ETPRO signatures available at the full report