| File name: | api |
| Full analysis: | https://app.any.run/tasks/a95b6d0f-ae9b-4a31-8c52-40aa610aea86 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 09:22:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7C77C0DA0680925A5C81689610D94DAE |
| SHA1: | 1D2D2928B692A8D035E6CD638B8FA63549278674 |
| SHA256: | A6A2083DD4127D8100A77640FC30EAECE25A97D3F398E7C8B58775C263DE1541 |
| SSDEEP: | 393216:WBj1a4rJzX03OesdJxzVF4/WWAz70GLJsv6tWKFdu9C9QUearRAVuHw/Pg:Wp/rJT03Oes+/WWAzRAVuuY |
MALICIOUS
Loads the Task Scheduler DLL interface
- api.exe (PID: 2340)
Loads the Task Scheduler COM API
- api.exe (PID: 2340)
SUSPICIOUS
Low-level read access rights to disk partition
- api.exe (PID: 2340)
Creates files in the program directory
- api.exe (PID: 2340)
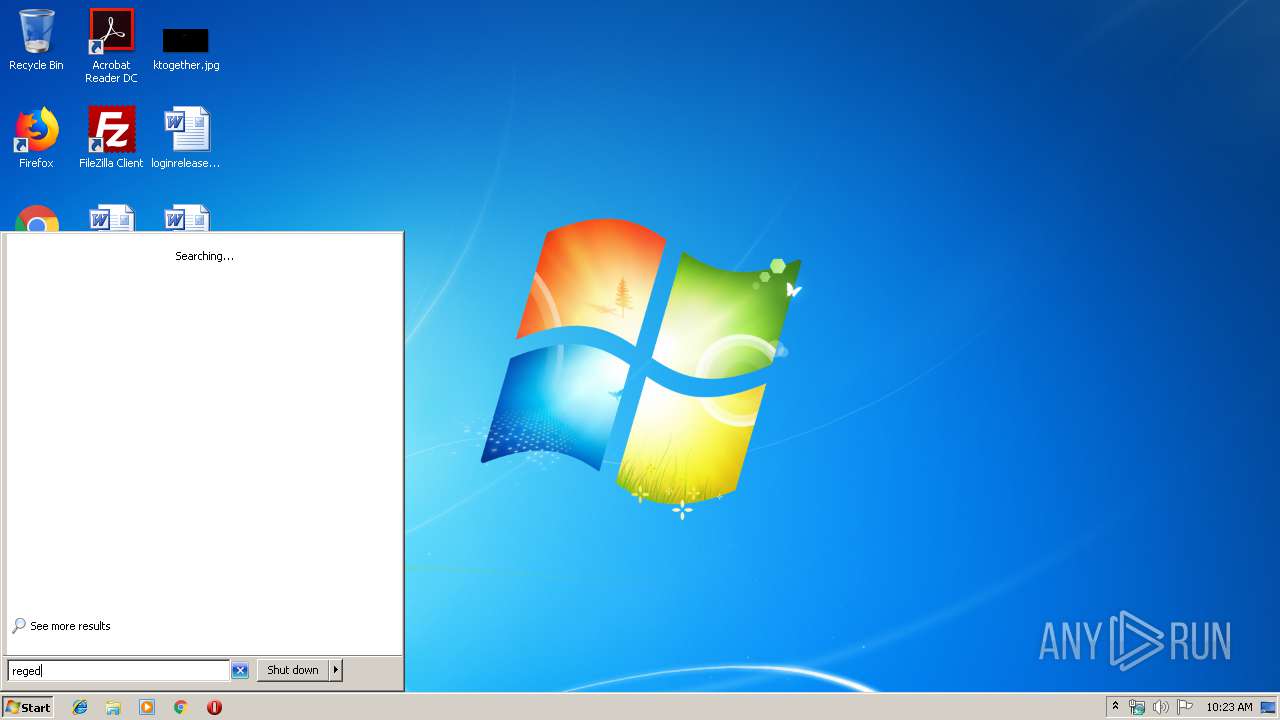
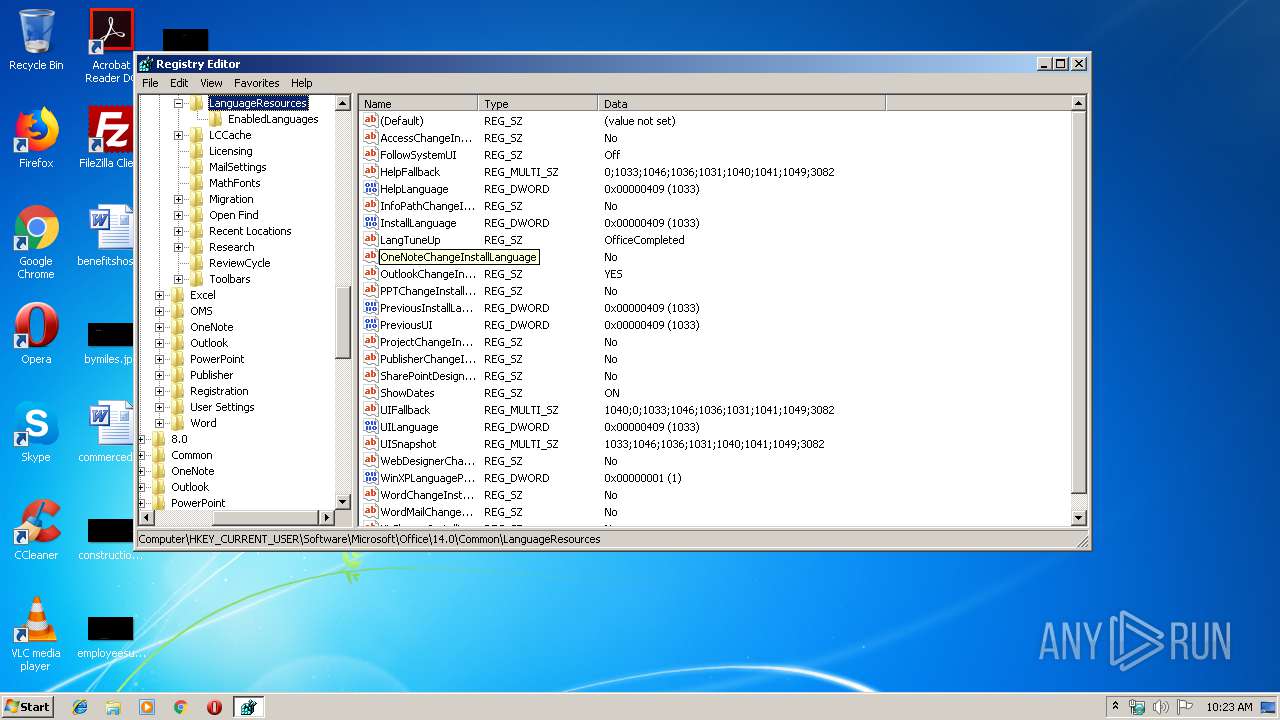
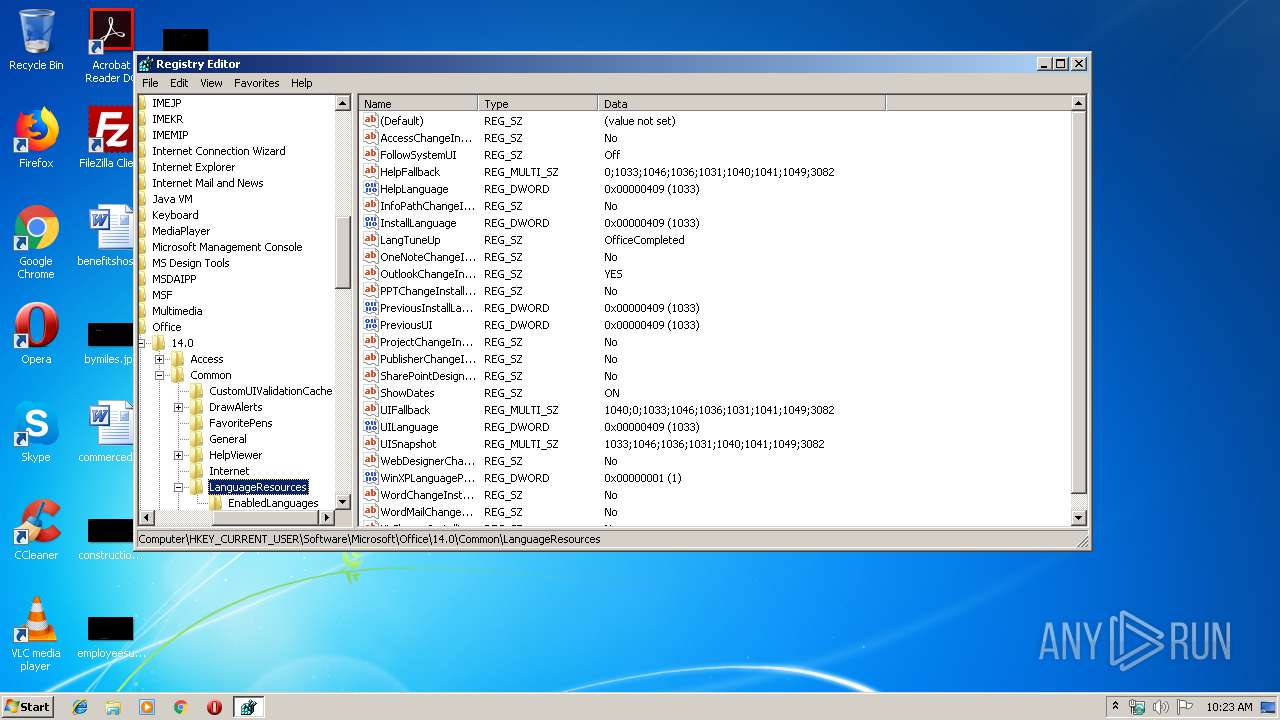
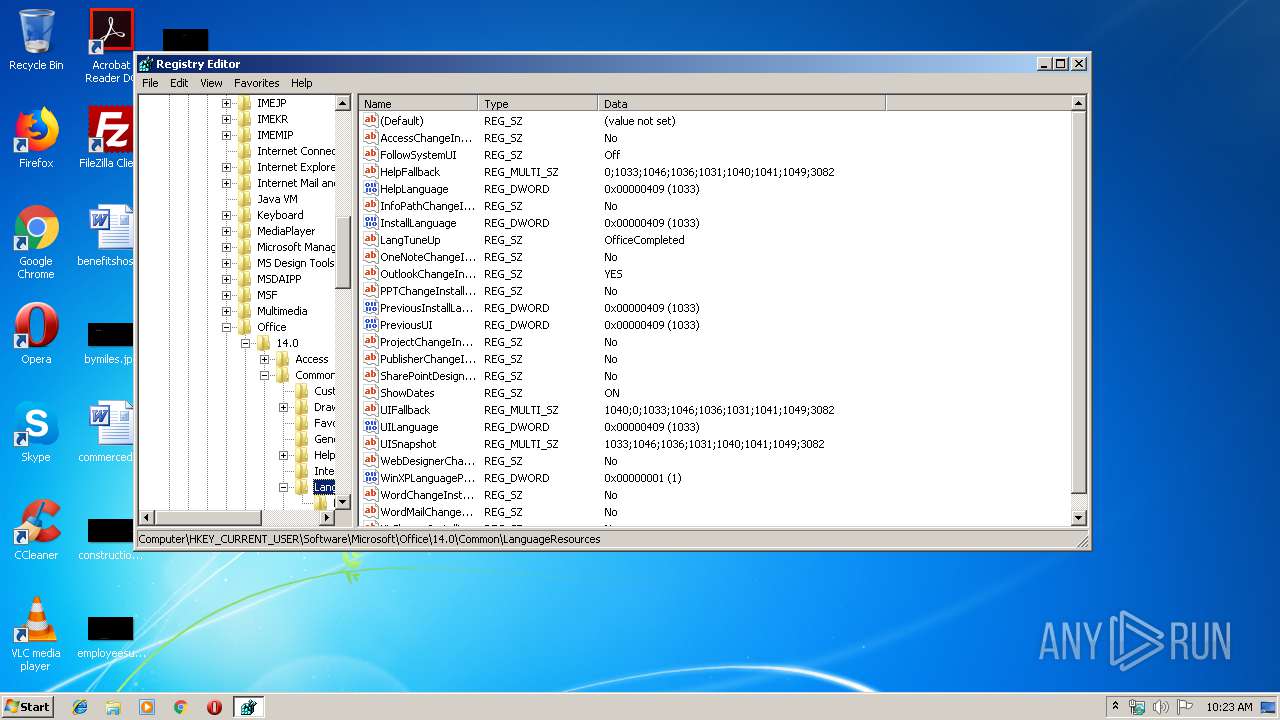
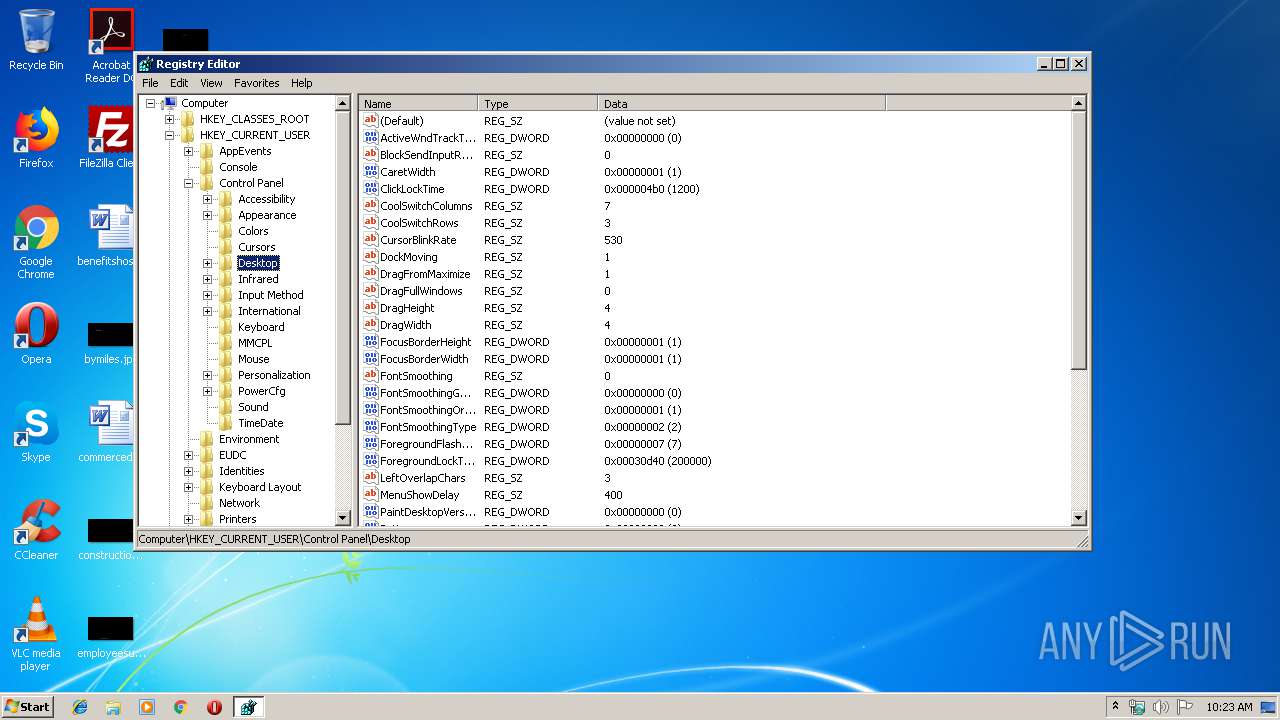
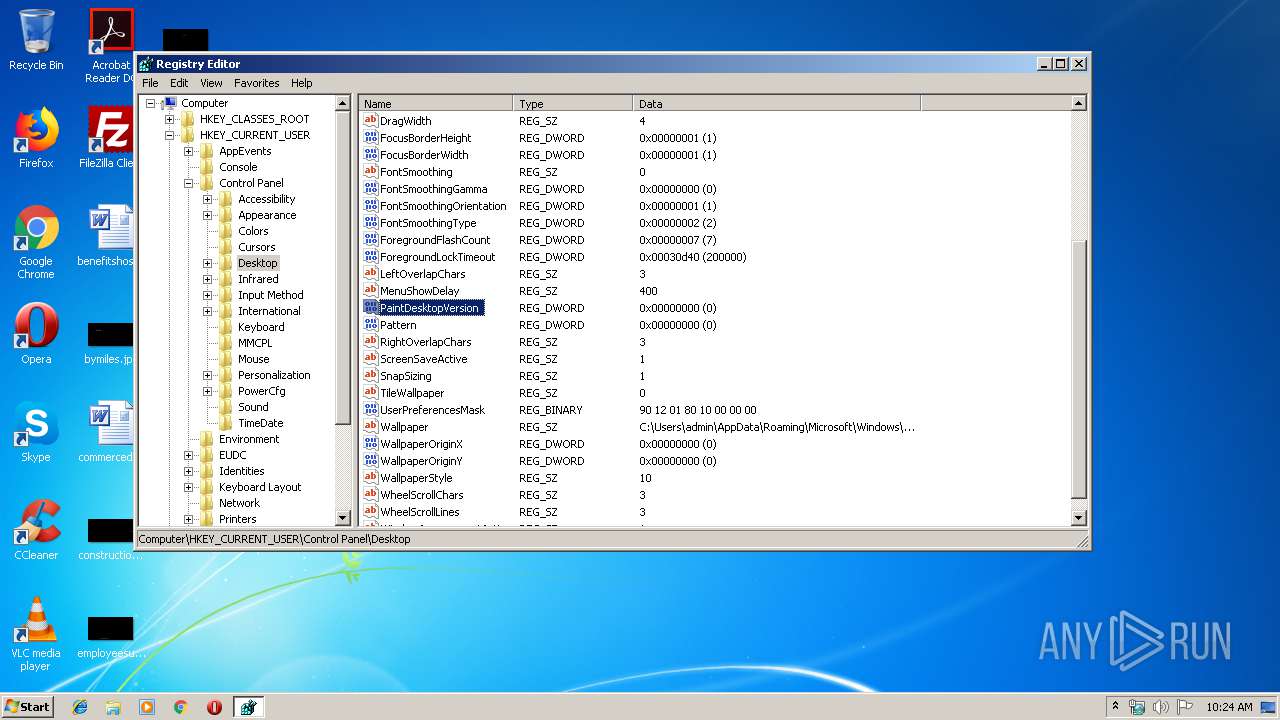
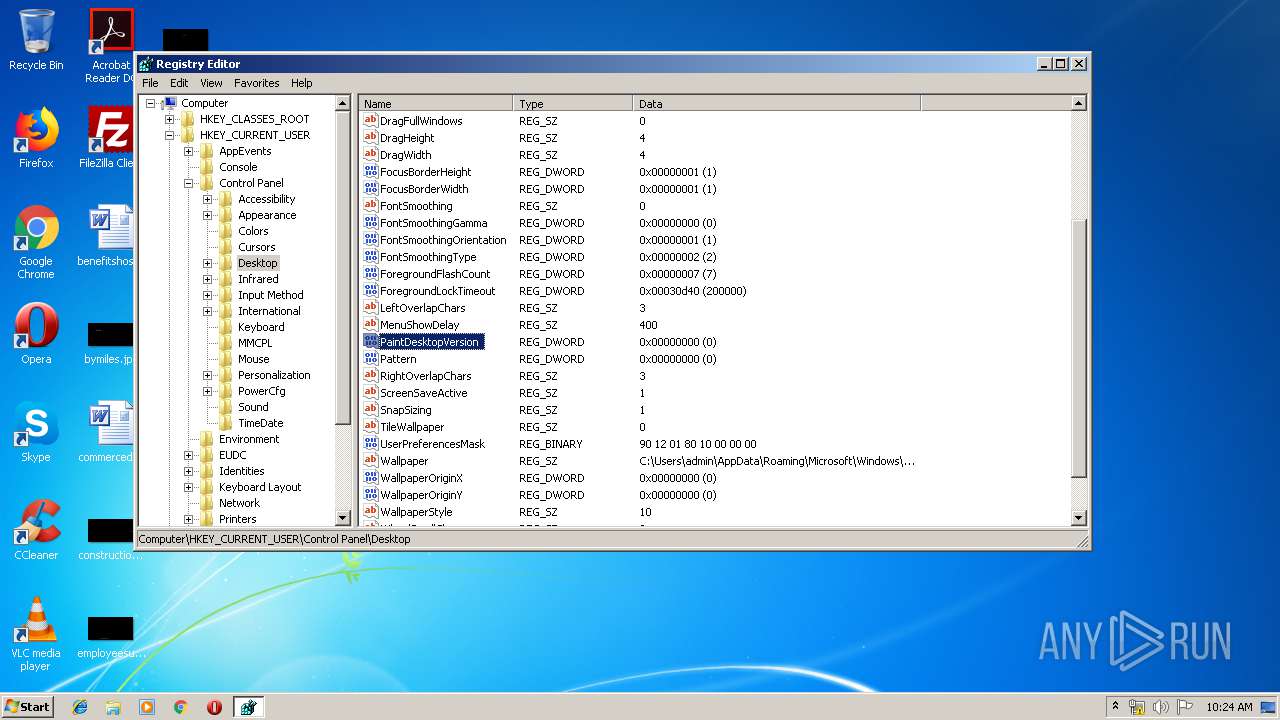
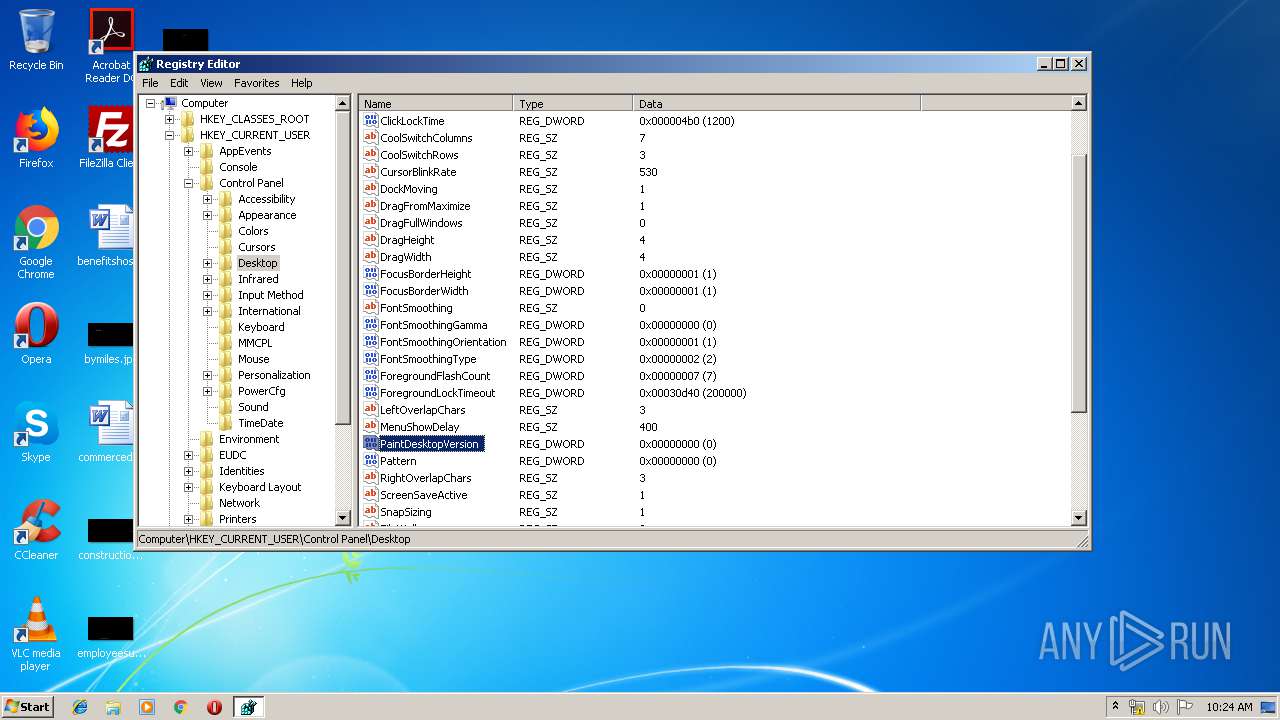
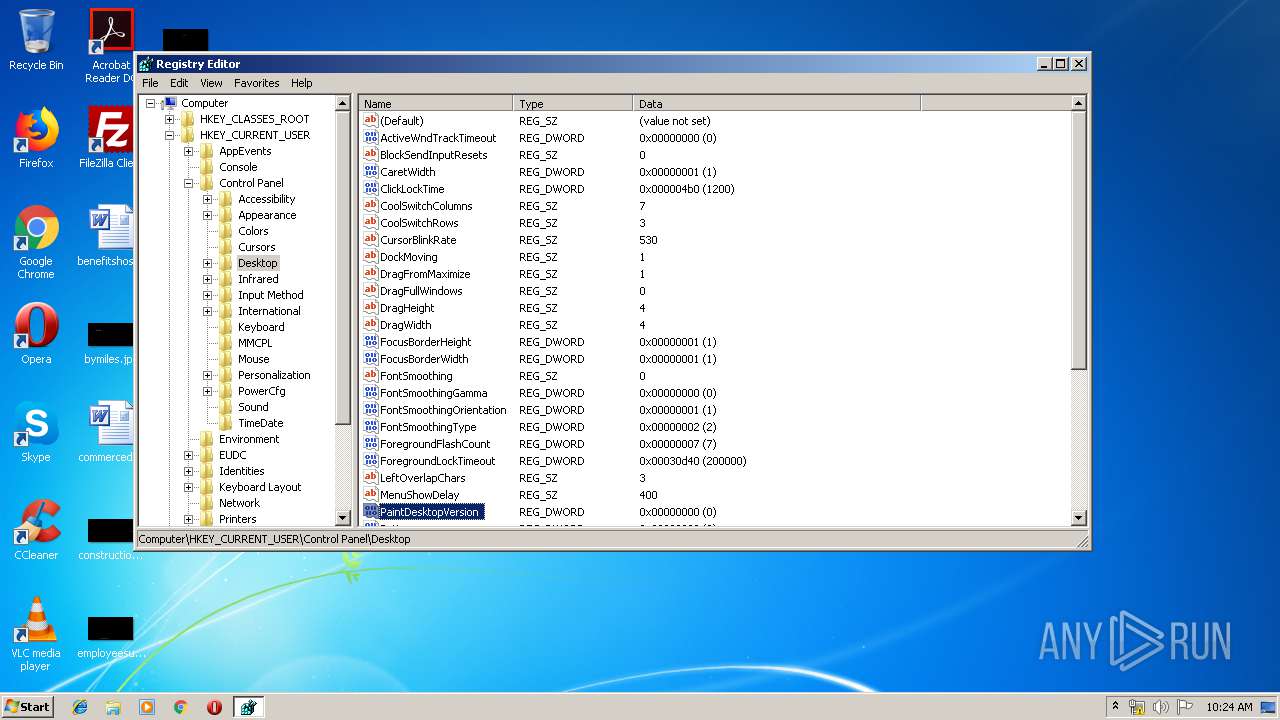
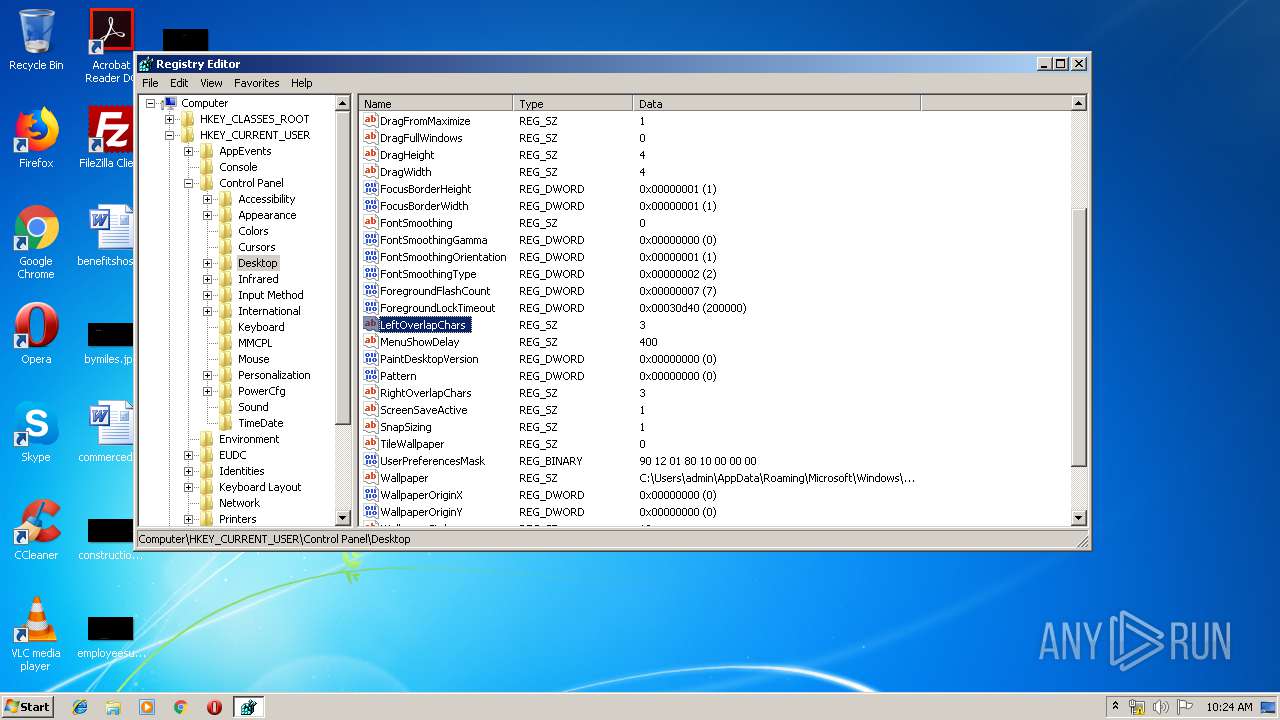
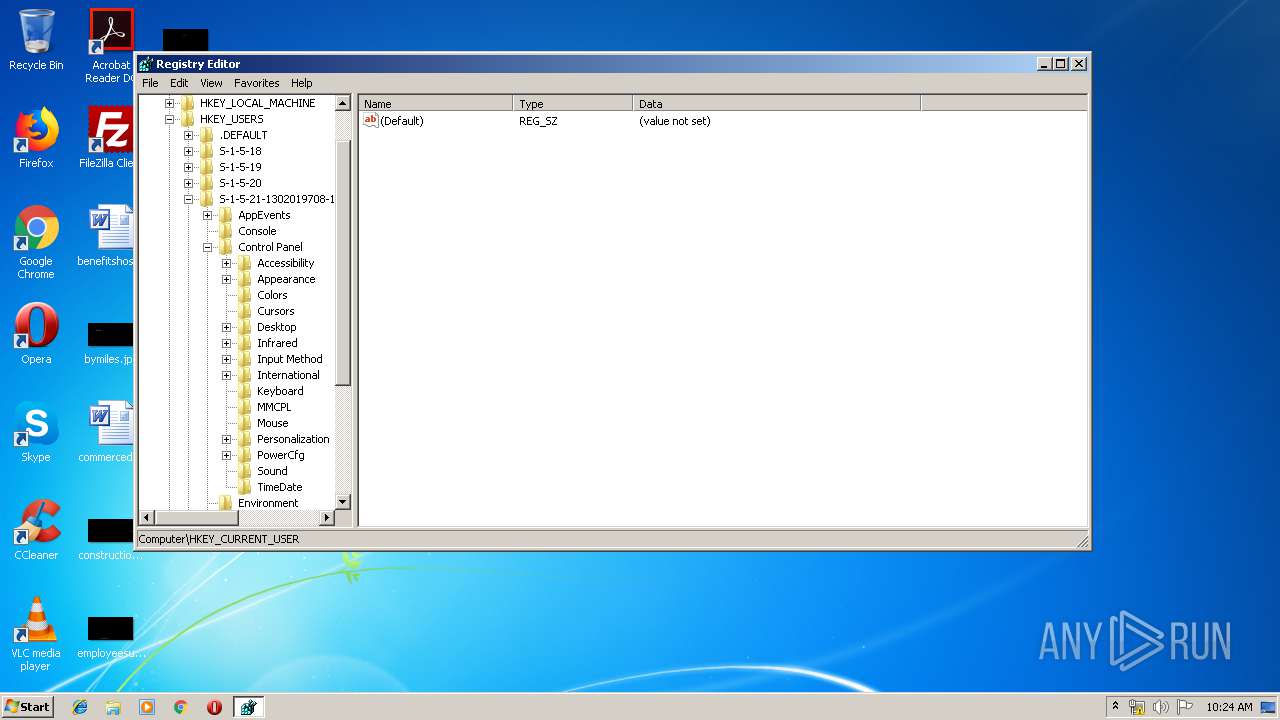
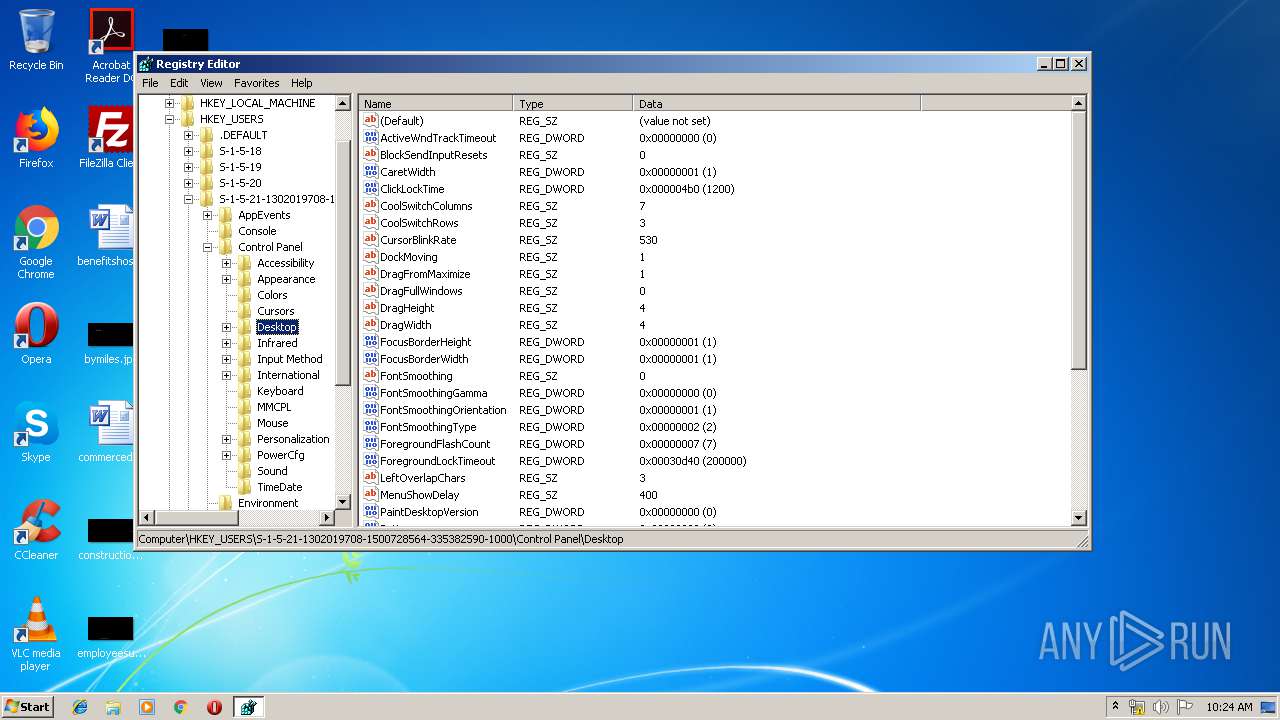
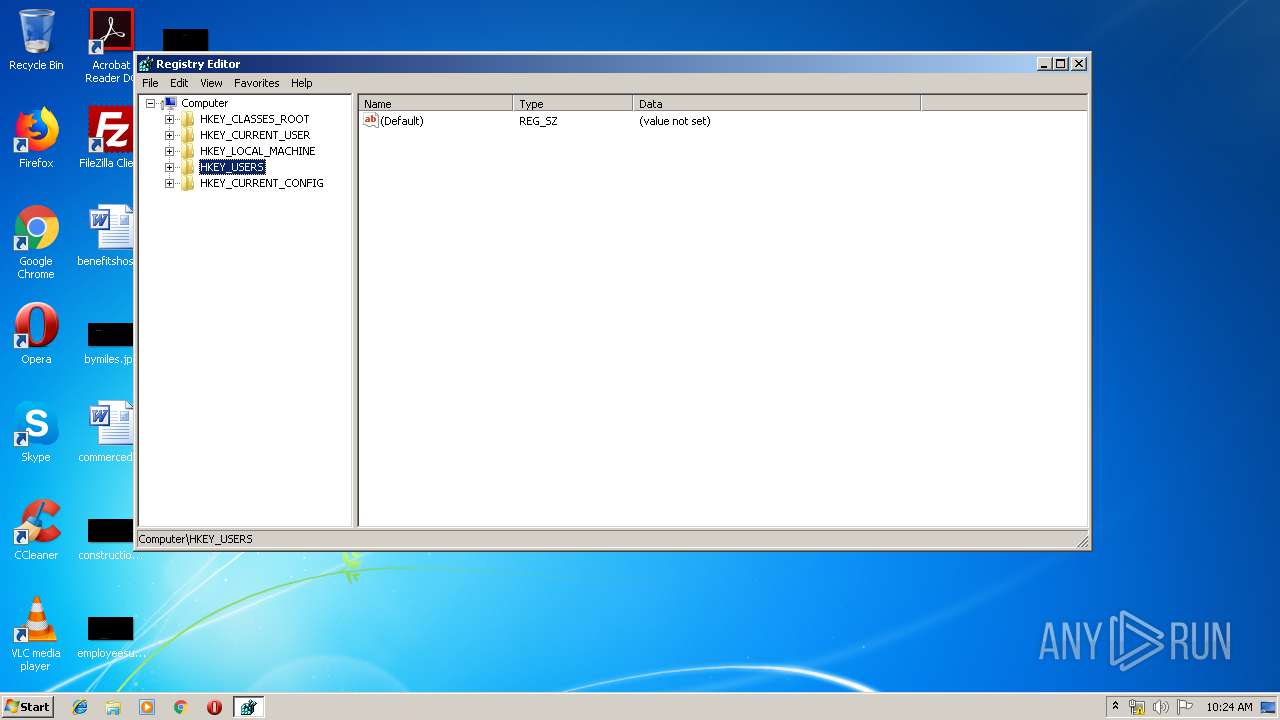
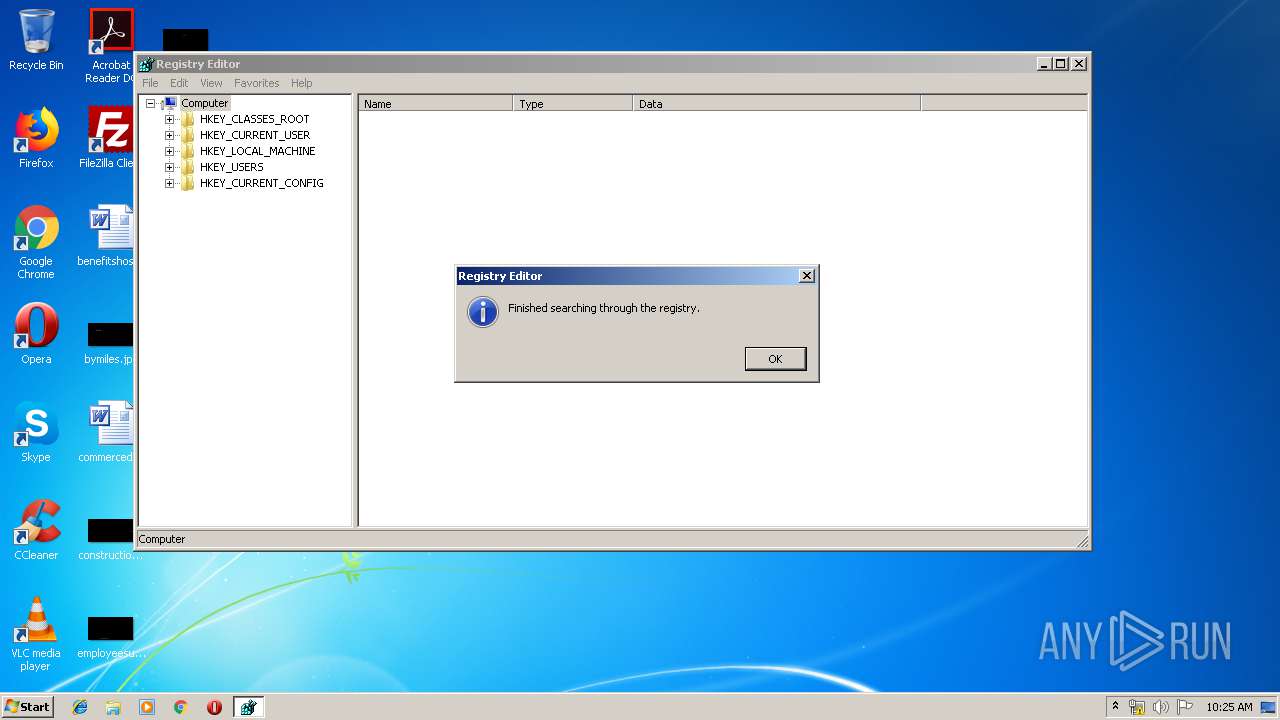
Reads Internet Cache Settings
- regedit.exe (PID: 2788)
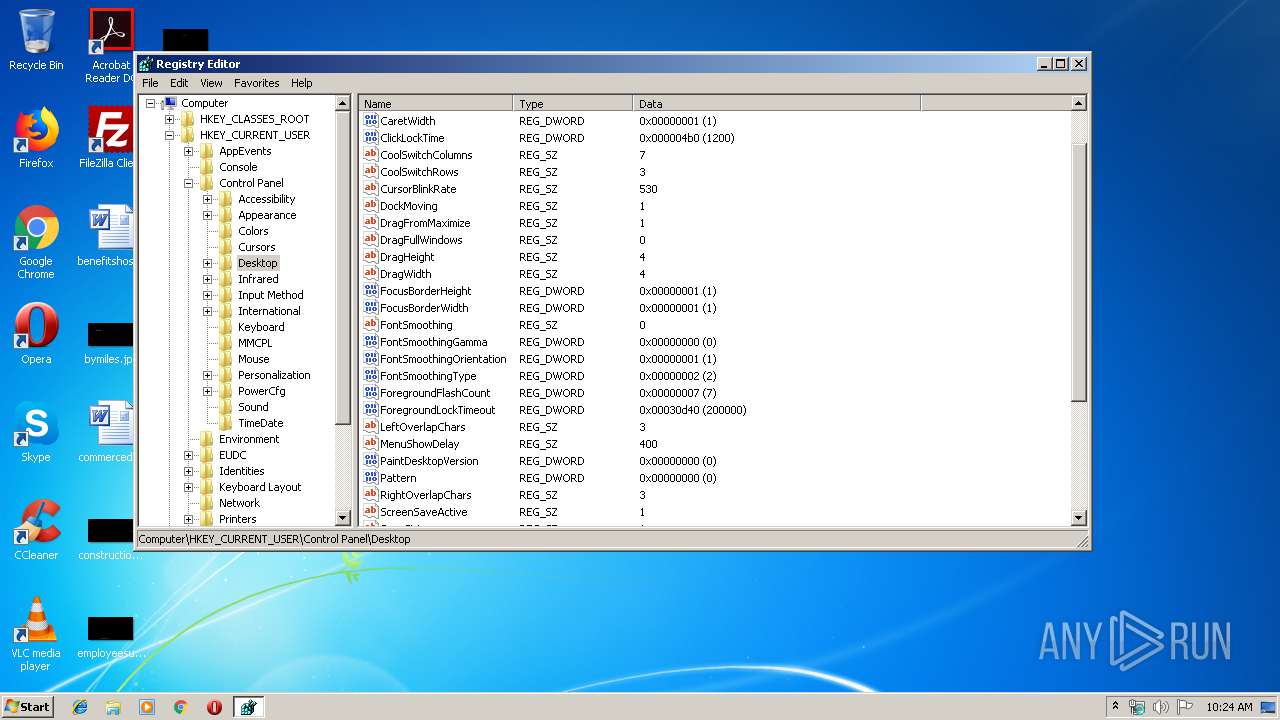
Reads Windows Product ID
- regedit.exe (PID: 2788)
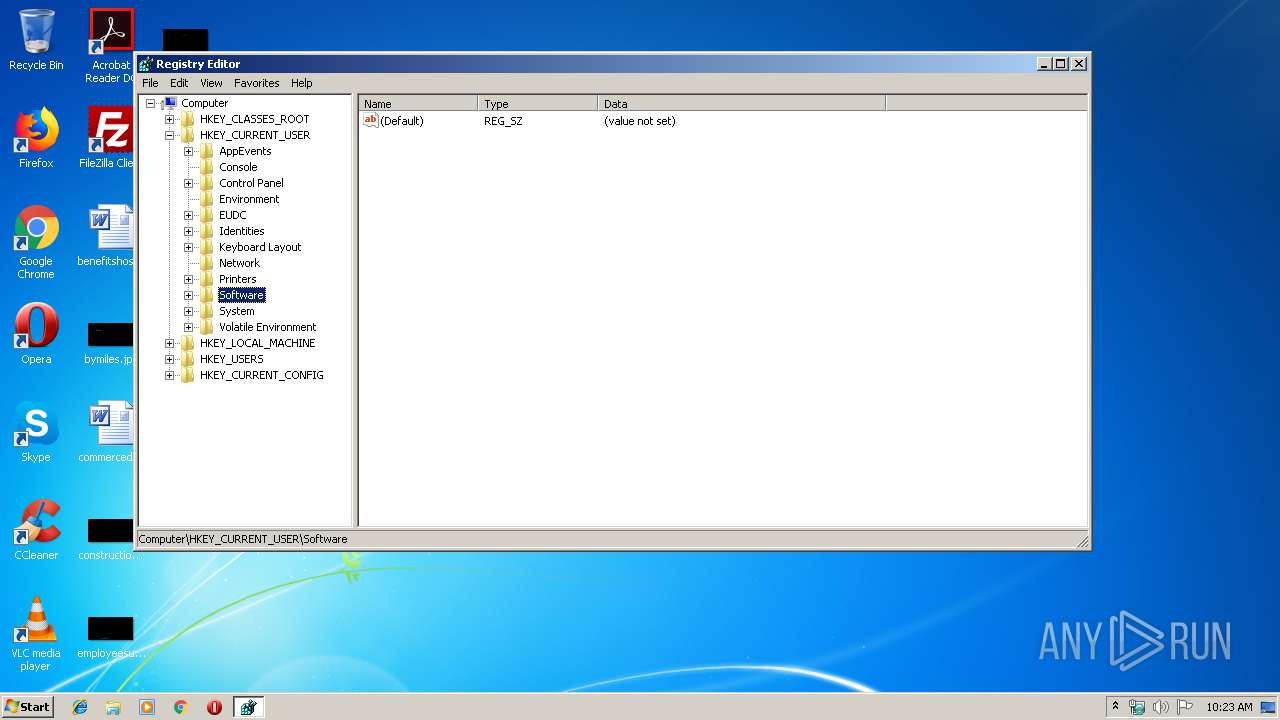
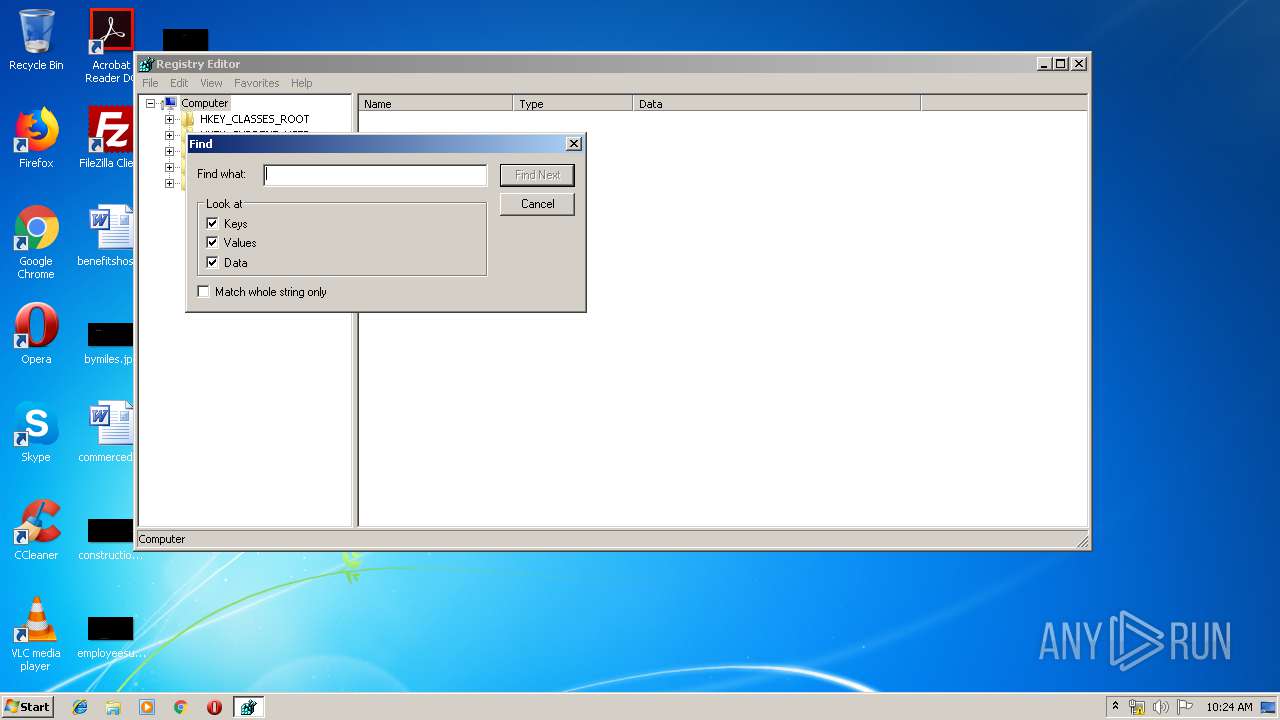
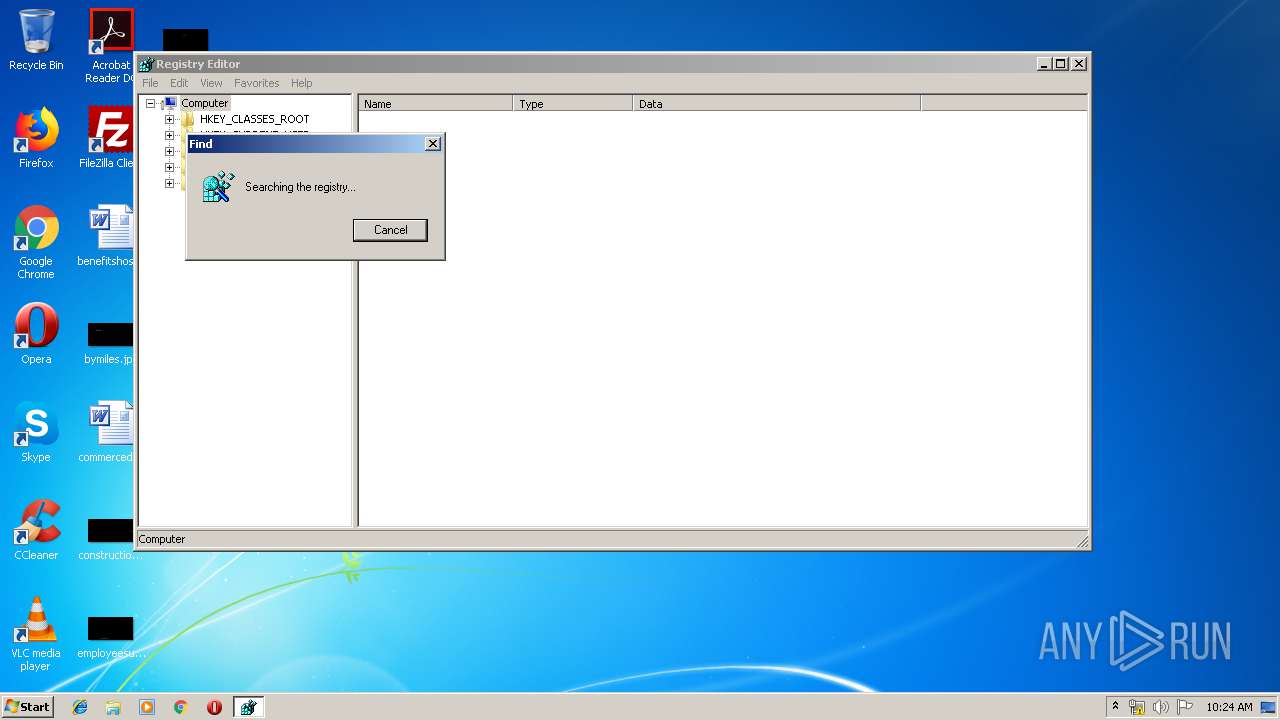
Searches for installed software
- regedit.exe (PID: 2788)
Reads default file associations for system extensions
- regedit.exe (PID: 2788)
INFO
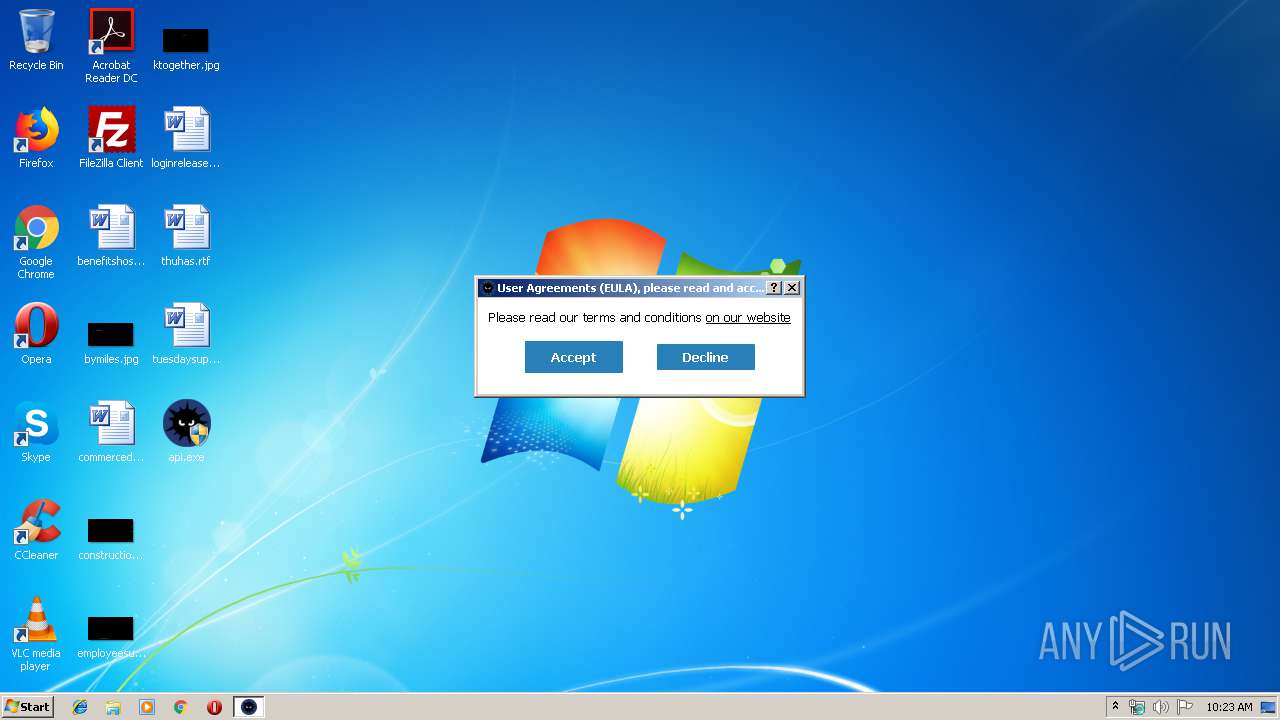
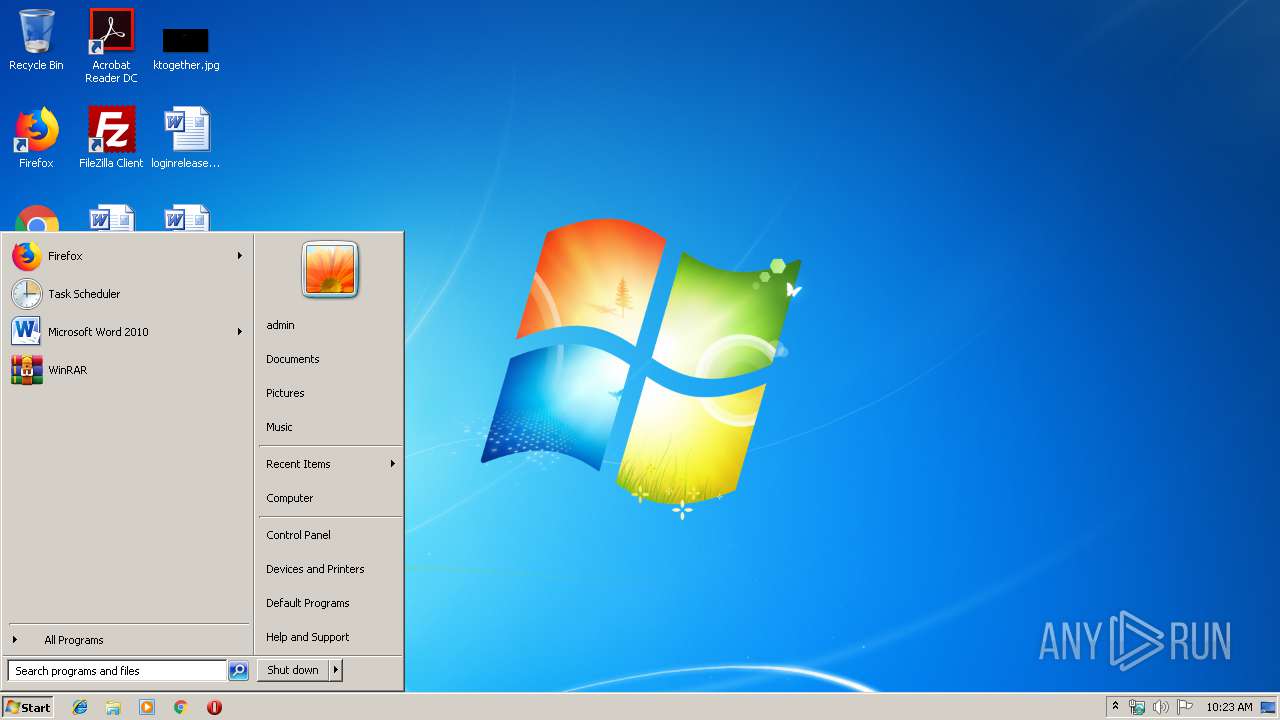
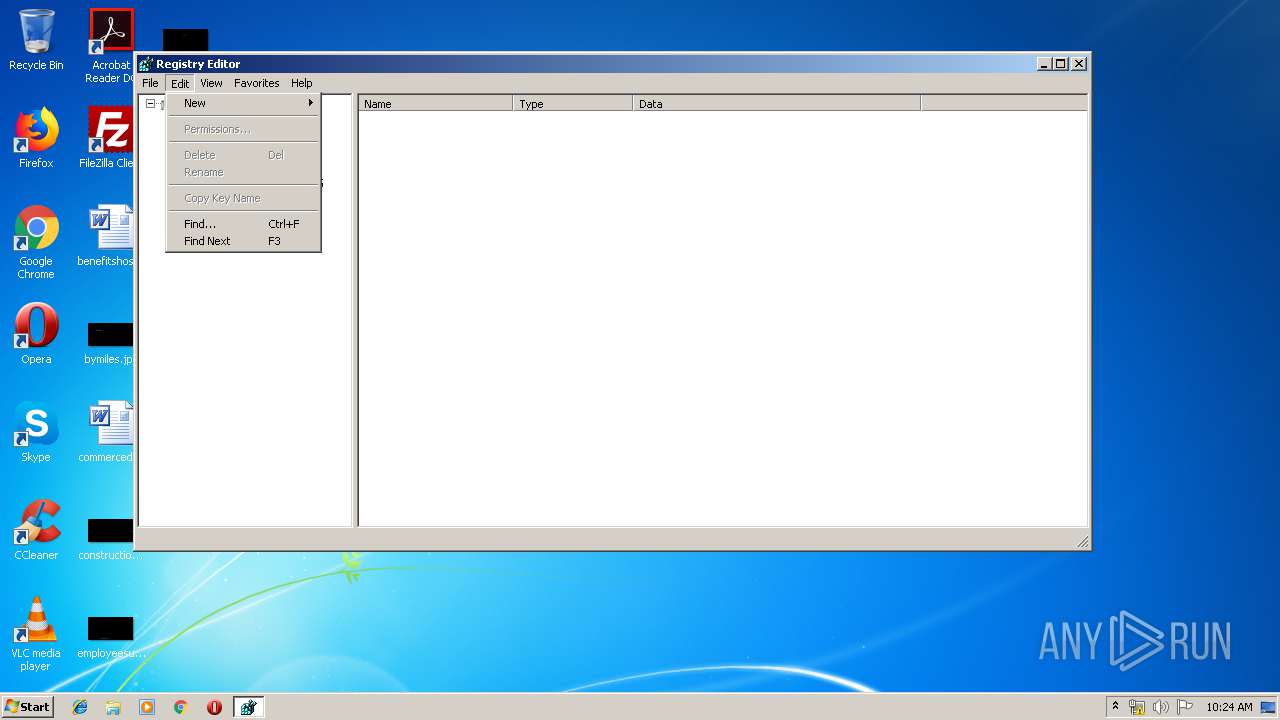
Manual execution by user
- regedit.exe (PID: 2788)
- regedit.exe (PID: 964)
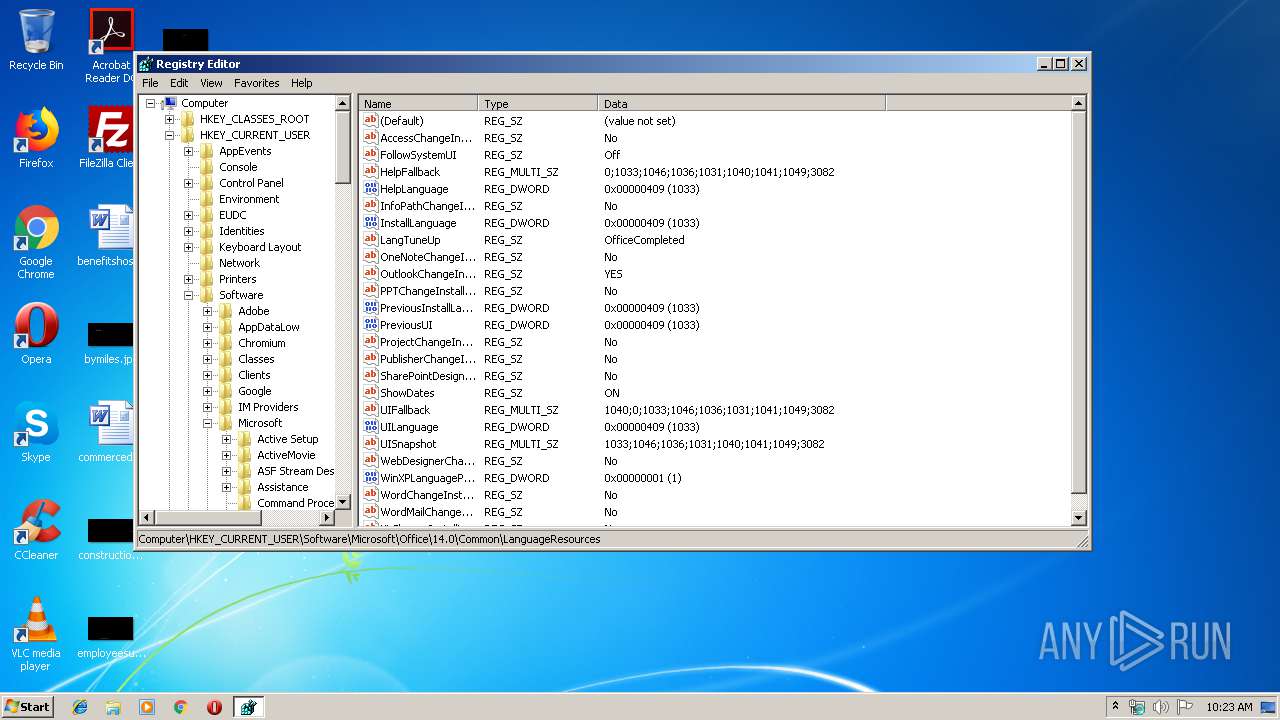
Reads Microsoft Office registry keys
- regedit.exe (PID: 2788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:10 18:48:37+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 16878080 |
| InitializedDataSize: | 11647488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd592e4 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 13.5.3.0 |
| ProductVersionNumber: | 13.5.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Adlice Software |
| FileDescription: | Anti-Malware Scan and Removal |
| FileVersion: | 13.5.3.0 |
| InternalName: | RogueKiller Anti-Malware |
| LegalCopyright: | Copyright Adlice Software(C) 2019 |
| LegalTrademarks1: | Adlice Software |
| LegalTrademarks2: | Adlice Software |
| OriginalFileName: | RogueKiller Anti-Malware |
| ProductName: | RogueKiller Anti-Malware |
| ProductVersion: | 13.5.3.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Oct-2019 16:48:37 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Adlice Software |
| FileDescription: | Anti-Malware Scan and Removal |
| FileVersion: | 13.5.3.0 |
| InternalName: | RogueKiller Anti-Malware |
| LegalCopyright: | Copyright Adlice Software(C) 2019 |
| LegalTrademarks1: | Adlice Software |
| LegalTrademarks2: | Adlice Software |
| OriginalFilename: | RogueKiller Anti-Malware |
| ProductName: | RogueKiller Anti-Malware |
| ProductVersion: | 13.5.3.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000160 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 10-Oct-2019 16:48:37 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x010189E0 | 0x01018A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60262 |
.rdata | 0x0101A000 | 0x004E6B6C | 0x004E6C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.35074 |
.data | 0x01501000 | 0x00052440 | 0x00031400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.89859 |
.tls | 0x01554000 | 0x0000000D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.qtmetadL\x02 | 0x01555000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.15593 |
.gfids | 0x01556000 | 0x00000770 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.98218 |
_RDATA | 0x01557000 | 0x00000124 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.51793 |
.rsrc | 0x01558000 | 0x00533D50 | 0x00533E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.88516 |
.reloc | 0x01A8C000 | 0x000AD824 | 0x000ADA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64741 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21878 | 667 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.08492 | 296 | UNKNOWN | English - United States | RT_ICON |
3 | 4.32673 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 4.69 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 4.96085 | 1384 | UNKNOWN | English - United States | RT_ICON |
6 | 7.96471 | 21897 | UNKNOWN | English - United States | RT_ICON |
7 | 3.53747 | 16936 | UNKNOWN | English - United States | RT_ICON |
8 | 3.87766 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 4.07378 | 6760 | UNKNOWN | English - United States | RT_ICON |
10 | 4.36584 | 4264 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
OPENGL32.dll |
PSAPI.DLL |
Total processes
45
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 964 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\Desktop\api.exe" | C:\Users\admin\Desktop\api.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967295 Modules
| |||||||||||||||
| 2408 | "C:\Users\admin\Desktop\api.exe" | C:\Users\admin\Desktop\api.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2788 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 898
Read events
7 875
Write events
22
Delete events
1
Modification events
| (PID) Process: | (2340) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2340) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2340) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2340) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2340) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2340) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2340) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2340) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2340) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2340) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
1
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2340 | api.exe | C:\ProgramData\RogueKiller\Debug\RogueKiller Anti-Malware_debug.log | text | |
MD5:— | SHA256:— | |||
| 2340 | api.exe | C:\ProgramData\RogueKiller\advert | text | |
MD5:— | SHA256:— | |||
| 2340 | api.exe | C:\ProgramData\RogueKiller\scheduler | text | |
MD5:— | SHA256:— | |||
| 2340 | api.exe | C:\ProgramData\RogueKiller\config.ini | binary | |
MD5:63C5385BB4EBD97837CE7257C397728C | SHA256:9D6AB3186C01D89B932AAE80B728154928A09240107893AD4ED4B97AAC177764 | |||
| 2340 | api.exe | C:\ProgramData\RogueKiller\vt.cache | text | |
MD5:FABA9D79BCEED5EC3D3F5C3AAE8B1E30 | SHA256:5D10EA790B9458C94384FF5EB4BFE04069053BACC87347CC0E831950F7EB931B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2340 | api.exe | 178.33.106.117:443 | download.adlice.com | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.adlice.com |
| whitelisted |
adflux.adlice.com |
| whitelisted |