| File name: | Unlock-r-MOD-1.2.7-MODBIBO.apk |
| Full analysis: | https://app.any.run/tasks/5db2d8dc-2240-4bff-902c-53eb5d0fec4c |
| Verdict: | Malicious activity |
| Analysis date: | February 23, 2026, 22:04:18 |
| OS: | Android 14 |
| Tags: | |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with APK Signing Block |
| MD5: | 18108C4E94B57C6A2E5086EE002112F5 |
| SHA1: | 138E54BA66DE1D076CF21183038E709E6D571267 |
| SHA256: | A69A34A045C93669C9072DDBCC73DE6908A4FD163622731395C9DCCFCFF9FC25 |
| SSDEEP: | 98304:dFfg1SCpck885HA6lBhyVBQwa21lsmAz+ZAVIWHrYWglOBe2LjCIPgoR1q5zUt+o:zc1ECRM9OfuqESkY |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes dynamic code using class loader
- app_process64 (PID: 2847)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2847)
Accesses system-level resources
- app_process64 (PID: 2847)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2847)
Establishing a connection
- app_process64 (PID: 2847)
Uses encryption API functions
- app_process64 (PID: 2847)
Retrieves Android OS build information
- app_process64 (PID: 2847)
Retrieves the MCC and MNC of the SIM card operator
- app_process64 (PID: 2847)
Potential Corporate Privacy Violation
- app_process64 (PID: 2847)
Accesses external device storage files
- app_process64 (PID: 2847)
Launches a new activity
- app_process64 (PID: 2847)
INFO
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2847)
Dynamically registers broadcast event listeners
- app_process64 (PID: 2847)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 2847)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2847)
Retrieves the value of a secure system setting
- app_process64 (PID: 2847)
Dynamically loads a class in Java
- app_process64 (PID: 2847)
Stores data using SQLite database
- app_process64 (PID: 2847)
Returns elapsed time since boot
- app_process64 (PID: 2847)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2847)
Drops script file
- app_process64 (PID: 2847)
Gets file name without full path
- app_process64 (PID: 2847)
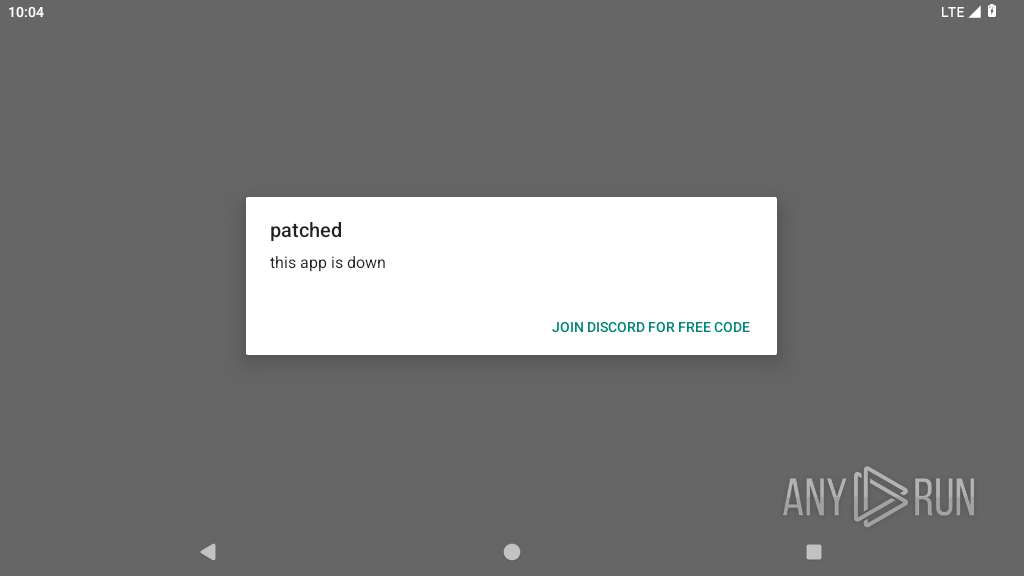
Attempting to use instant messaging service
- app_process64 (PID: 3216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (73.9) |
|---|---|---|
| .jar | | | Java Archive (20.4) |
| .zip | | | ZIP compressed archive (5.6) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:27 10:56:06 |
| ZipCRC: | 0x1f2ca912 |
| ZipCompressedSize: | 3777 |
| ZipUncompressedSize: | 19252 |
| ZipFileName: | AndroidManifest.xml |
Total processes
138
Monitored processes
12
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2847 | me.tito.unlocker | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2971 | com.android.webview:webview_service | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2972 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3024 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3090 | com.android.webview:webview_apk | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3216 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3287 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3311 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 9 | ||||
| 3312 | org.chromium.chrome:privileged_process0 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3385 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
35
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2847 | app_process64 | /storage/emulated/0/Android/data/me.tito.unlocker/cache/crash.txt | text | |
MD5:— | SHA256:— | |||
| 2847 | app_process64 | /data/user/0/me.tito.unlocker/cache/xz.apk | compressed | |
MD5:— | SHA256:— | |||
| 2847 | app_process64 | /data/user/0/me.tito.unlocker/shared_prefs/CBGr2.xml | xml | |
MD5:— | SHA256:— | |||
| 2847 | app_process64 | /data/user/0/me.tito.unlocker/app_webview/last-exit-info | text | |
MD5:— | SHA256:— | |||
| 2847 | app_process64 | /data/user/0/me.tito.unlocker/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2847 | app_process64 | /data/user/0/me.tito.unlocker/app_webview/Default/Web Data-journal | binary | |
MD5:— | SHA256:— | |||
| 2847 | app_process64 | /data/user/0/me.tito.unlocker/cache/WebView/Default/HTTP Cache/Code Cache/js/index | binary | |
MD5:— | SHA256:— | |||
| 2847 | app_process64 | /data/user/0/me.tito.unlocker/cache/WebView/Default/HTTP Cache/Code Cache/wasm/index | binary | |
MD5:— | SHA256:— | |||
| 2847 | app_process64 | /data/user/0/me.tito.unlocker/app_webview/Default/Shared Dictionary/cache/index | binary | |
MD5:— | SHA256:— | |||
| 2847 | app_process64 | /data/user/0/me.tito.unlocker/app_webview/Default/Shared Dictionary/cache/index-dir/temp-index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
143
TCP/UDP connections
73
DNS requests
32
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
822 | app_process64 | GET | 204 | 142.251.127.105:443 | https://www.google.com/generate_204 | unknown | — | — | whitelisted |
822 | app_process64 | GET | 204 | 142.251.140.163:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
— | — | GET | 204 | 142.251.127.99:80 | http://www.google.com/gen_204 | unknown | — | — | whitelisted |
2847 | app_process64 | POST | 200 | 188.114.97.3:443 | https://log-report.com/report | unknown | text | 48 b | unknown |
2847 | app_process64 | POST | 200 | 188.114.97.3:443 | https://log-report.com/report | unknown | text | 48 b | unknown |
2847 | app_process64 | GET | 200 | 172.247.0.106:443 | https://strongwill100.com/jd?a=53acdd351da24a600000242d50cf1f9f&av=1.2.7&cv=23&d=4b22c8d55aadcc6f&lang=en&p=me.tito.unlocker®ion=US&v=0&vc=50 | unknown | text | 253 b | unknown |
2847 | app_process64 | GET | 200 | 107.148.236.156:443 | https://360mixup.com/feature/config?api_version=1&app_id=53acdd351da24a600000242d50cf1f9f&app_version=2.3&device_code=4b22c8d55aadcc6f&lang=en&platform=2®ion=US&version_code=23 | unknown | text | 509 b | unknown |
1756 | app_process64 | POST | 200 | 142.251.168.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:fetchEekChain | unknown | binary | 778 b | whitelisted |
1756 | app_process64 | POST | 200 | 142.251.168.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:signCertificates?challenge=AAABnIyIXIsBILStY3SXO3_uYnBqi_7J5beAEEE=&request_id=5f15c90c-e72b-49c2-a320-4d1bc2a4884b | unknown | binary | 11.8 Kb | whitelisted |
2971 | app_process32 | GET | 200 | 216.58.206.35:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=android_webview&milestone=137 | unknown | compressed | 13.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
443 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 142.251.127.99:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.251.127.105:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.251.140.163:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
2847 | app_process64 | 104.19.31.141:443 | — | CLOUDFLARENET | US | whitelisted |
2847 | app_process64 | 172.64.203.72:443 | — | CLOUDFLARENET | US | whitelisted |
2847 | app_process64 | 172.64.197.29:443 | — | CLOUDFLARENET | US | whitelisted |
2847 | app_process64 | 162.159.38.227:443 | — | CLOUDFLARENET | US | whitelisted |
2847 | app_process64 | 104.19.82.128:443 | — | CLOUDFLARENET | US | whitelisted |
2847 | app_process64 | 162.159.243.215:443 | — | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google.com |
| whitelisted |
log-report.com |
| whitelisted |
strongwill100.com |
| unknown |
360mixup.com |
| unknown |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
822 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
2847 | app_process64 | Potential Corporate Privacy Violation | ET INFO Android Dalvik Executable File Download |
3216 | app_process64 | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
3216 | app_process64 | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
3216 | app_process64 | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
3216 | app_process64 | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
339 | netd | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
3216 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Request to load WebAssembly module |